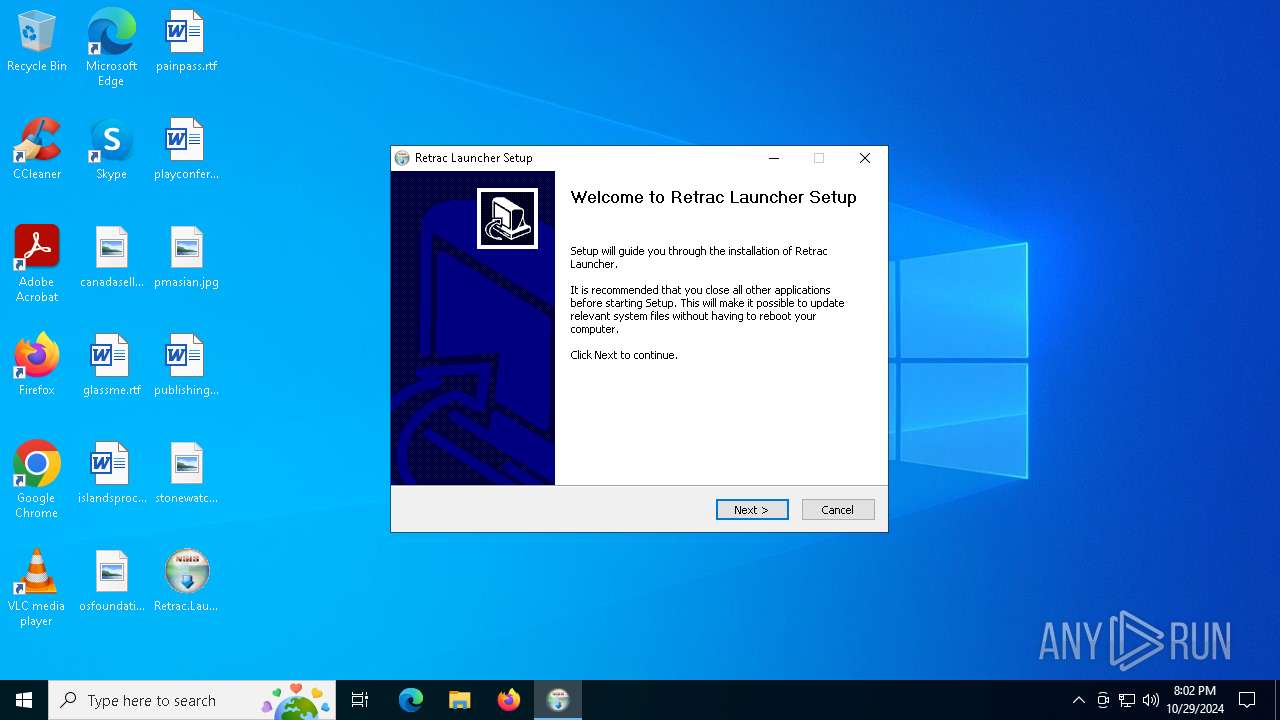
| File name: | Retrac.Launcher_1.0.13_x64-setup.exe |
| Full analysis: | https://app.any.run/tasks/130d3591-84a3-461a-b57b-5420be5a1cd7 |
| Verdict: | Malicious activity |
| Analysis date: | October 29, 2024, 20:02:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 6E607913C153F9315BB5BD7480461B0F |
| SHA1: | E8B0F014D538A54D1174EB383A6A93009761A7F5 |
| SHA256: | F8FB5C2357192ABDBE1821A6A9F14F23F4D7EC6FF786E30E41D29AFCD67B7D01 |
| SSDEEP: | 98304:9J8C/rP1gcCLb2D58EeX+2qkJGv04mAdjUr3NplKXBYPPmdosnxT3nAGSx6Iwsua:9dVQ2whQ7YHpdU12 |
MALICIOUS
No malicious indicators.SUSPICIOUS
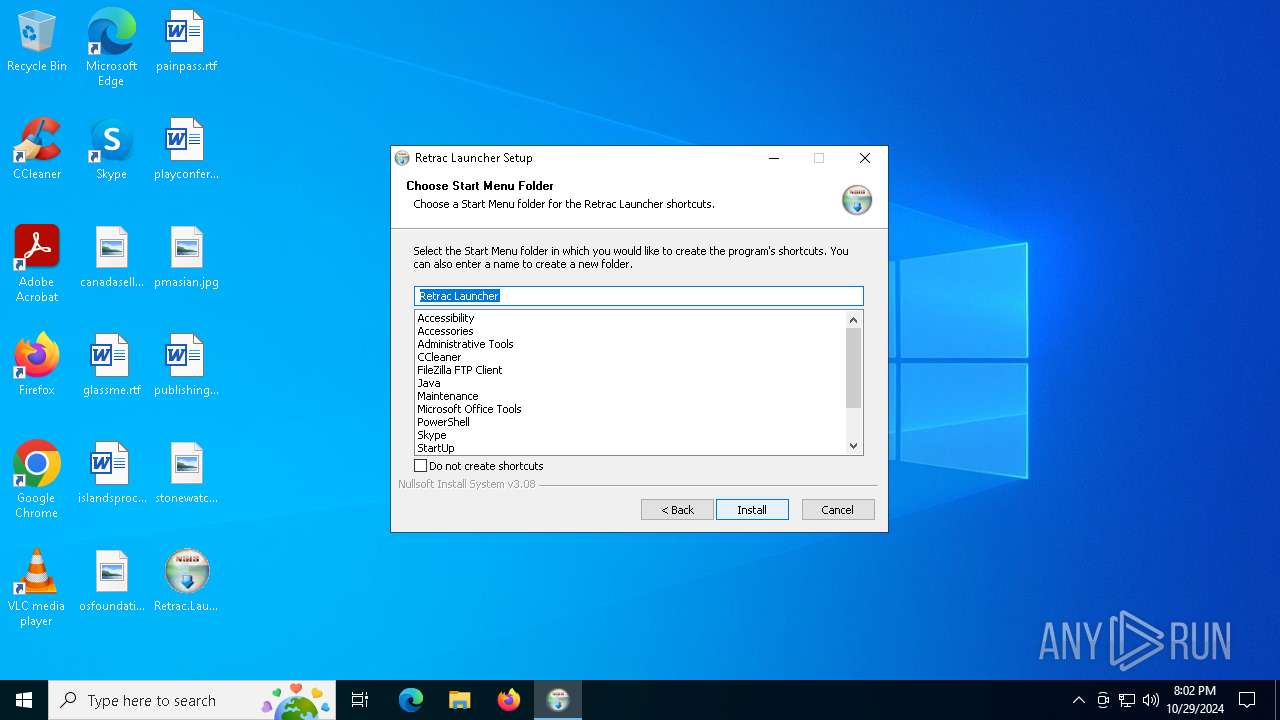
The process creates files with name similar to system file names
- Retrac.Launcher_1.0.13_x64-setup.exe (PID: 1160)
Malware-specific behavior (creating "System.dll" in Temp)
- Retrac.Launcher_1.0.13_x64-setup.exe (PID: 1160)
Searches for installed software
- Retrac.Launcher_1.0.13_x64-setup.exe (PID: 1160)
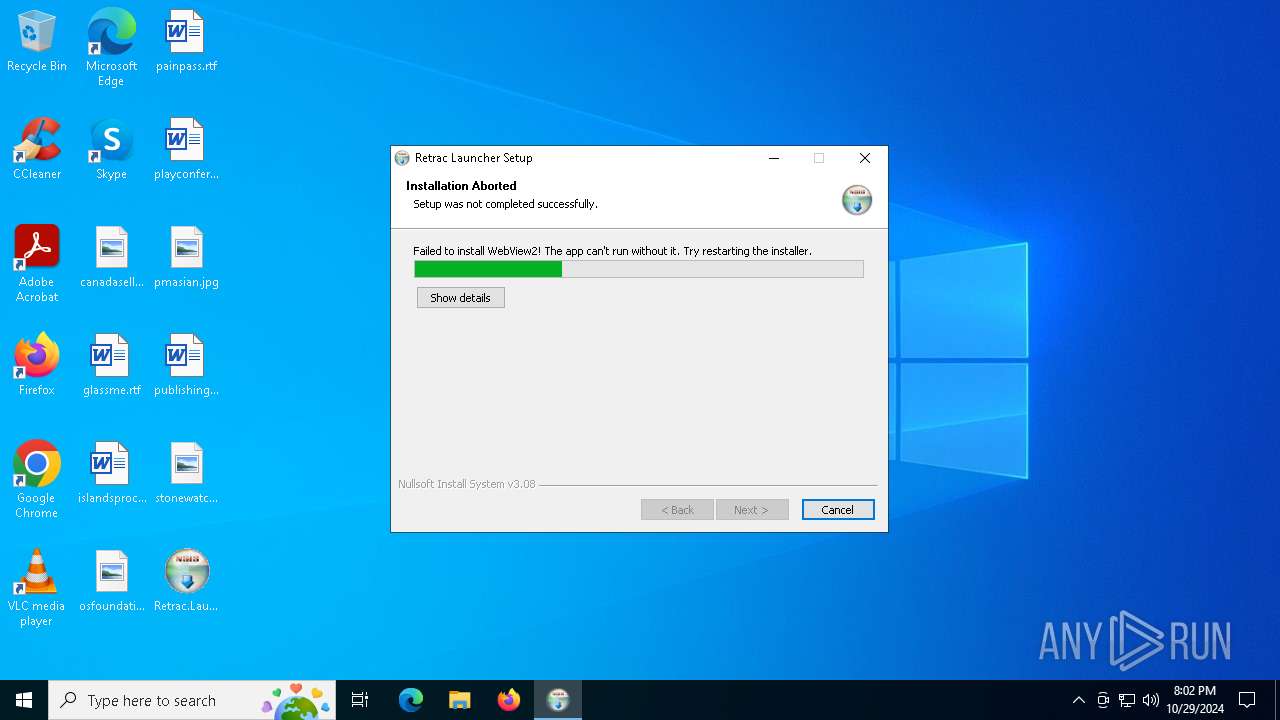
Executable content was dropped or overwritten
- Retrac.Launcher_1.0.13_x64-setup.exe (PID: 1160)
INFO
Checks supported languages
- Retrac.Launcher_1.0.13_x64-setup.exe (PID: 1160)
Reads the computer name
- Retrac.Launcher_1.0.13_x64-setup.exe (PID: 1160)
Create files in a temporary directory
- Retrac.Launcher_1.0.13_x64-setup.exe (PID: 1160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:56:47+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3640 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.13.0 |
| ProductVersionNumber: | 1.0.13.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | Retrac Launcher |
| FileVersion: | 1.0.13 |
| LegalCopyright: | - |
| ProductName: | Retrac Launcher |
| ProductVersion: | 1.0.13 |
Total processes
126
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1160 | "C:\Users\admin\Desktop\Retrac.Launcher_1.0.13_x64-setup.exe" | C:\Users\admin\Desktop\Retrac.Launcher_1.0.13_x64-setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Retrac Launcher Version: 1.0.13 Modules
| |||||||||||||||
Total events
516
Read events
516
Write events
0
Delete events
0
Modification events
Executable files
4
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1160 | Retrac.Launcher_1.0.13_x64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsiC222.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 1160 | Retrac.Launcher_1.0.13_x64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsiC222.tmp\nsis_tauri_utils.dll | executable | |
MD5:0BA06473CEC3F0E72FC6865D870B6BD9 | SHA256:2B454443F12806D9E531E18BF19933C0AAD1CD8AE397C71B99E814566E6BB5FD | |||
| 1160 | Retrac.Launcher_1.0.13_x64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsiC222.tmp\System.dll | executable | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
| 1160 | Retrac.Launcher_1.0.13_x64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsiC222.tmp\StartMenu.dll | executable | |
MD5:D070F3275DF715BF3708BEFF2C6C307D | SHA256:42DD4DDA3249A94E32E20F76EAFFAE784A5475ED00C60EF0197C8A2C1CCD2FB7 | |||
| 1160 | Retrac.Launcher_1.0.13_x64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsiC222.tmp\nsDialogs.dll | executable | |
MD5:6C3F8C94D0727894D706940A8A980543 | SHA256:56B96ADD1978B1ABBA286F7F8982B0EFBE007D4A48B3DED6A4D408E01D753FE2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
22
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1752 | RUXIMICS.exe | GET | 200 | 2.16.164.83:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 2.16.164.83:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.83:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1752 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1752 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1752 | RUXIMICS.exe | 2.16.164.83:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
6944 | svchost.exe | 2.16.164.83:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.164.83:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1752 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |