| File name: | f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a |
| Full analysis: | https://app.any.run/tasks/b4ceb635-1234-40fa-86b1-8f33fb732864 |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2022, 22:45:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 3553F31B0FC2377321C3532697676270 |
| SHA1: | 2028DEE9DDBA6616F4B48539CAA17E515524E122 |
| SHA256: | F8FB4FB205E65D957E0AB4BF568C394AE3AF6186EEE90751161D6DF85F0D840A |
| SSDEEP: | 6144:fZM93Txzh+w+m/AKm9E9RCtRwZfrz4rZD4V:fq9jFhlIS9QzMY4V |
MALICIOUS
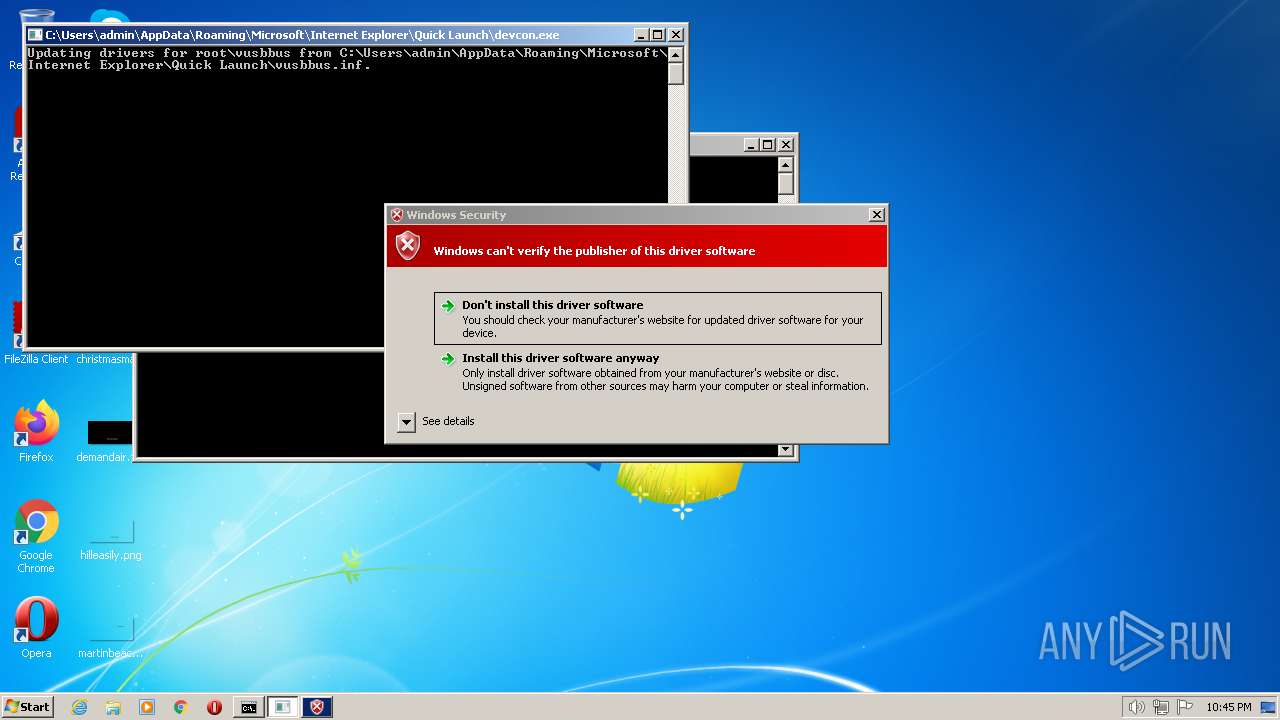
Drops the executable file immediately after the start
- f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe (PID: 1756)
- devcon.exe (PID: 1936)
Application was dropped or rewritten from another process
- devcon.exe (PID: 1284)
- devcon.exe (PID: 3036)
- devcon.exe (PID: 2008)
- devcon.exe (PID: 2800)
- devcon.exe (PID: 2276)
- devcon.exe (PID: 1936)
SUSPICIOUS
Drops a file with too old compile date
- f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe (PID: 1756)
- devcon.exe (PID: 1936)
- DrvInst.exe (PID: 1280)
- DrvInst.exe (PID: 3080)
Executable content was dropped or overwritten
- f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe (PID: 1756)
- devcon.exe (PID: 1936)
INFO
Drops a file that was compiled in debug mode
- f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe (PID: 1756)
- devcon.exe (PID: 1936)
- DrvInst.exe (PID: 1280)
- DrvInst.exe (PID: 3080)
Drops the executable file immediately after the start
- DrvInst.exe (PID: 1280)
- DrvInst.exe (PID: 3080)
Executable content was dropped or overwritten
- DrvInst.exe (PID: 1280)
- DrvInst.exe (PID: 3080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2007-Aug-19 08:31:03 |
| Detected languages: |
|
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 3 |
| TimeDateStamp: | 2007-Aug-19 08:31:03 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 4096 | 94208 | 0 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
UPX1 | 98304 | 45056 | 41984 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.88506 |
.rsrc | 143360 | 4096 | 4096 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.5121 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.85097 | 2216 | UNKNOWN | English - United States | RT_ICON |
2 | 7.61532 | 2216 | UNKNOWN | English - United States | RT_ICON |
8001 | 1.81924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
8002 | 4.32193 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
1 (#2) | 5.00605 | 695 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
56
Monitored processes
15
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1060 | "C:\Windows\regedit.exe" /s 0000EA30.reg | C:\Windows\regedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1280 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{2496fcec-86e9-4706-c488-7e79283a6b56}\vusbbus.inf" "0" "67ff6bedb" "0000058C" "WinSta0\Default" "00000568" "208" "c:\users\admin\appdata\roaming\microsoft\internet explorer\quick launch" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1284 | devcon remove root\vusbbus | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\devcon.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Setup API Exit code: 3221226540 Version: 5.1.2600.1106 (xpsp1.020828-1920) Modules
| |||||||||||||||
| 1756 | "C:\Users\admin\AppData\Local\Temp\f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe" | C:\Users\admin\AppData\Local\Temp\f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1936 | "C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\devcon.exe" install vusbbus.inf root\vusbbus | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\devcon.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 5.1.2600.1106 (xpsp1.020828-1920) Modules
| |||||||||||||||
| 2008 | "C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\devcon.exe" remove root\vusbbus | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\devcon.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 5.1.2600.1106 (xpsp1.020828-1920) Modules
| |||||||||||||||
| 2276 | "C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\devcon.exe" install vusbbus.inf root\vusbbus | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\devcon.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Setup API Exit code: 3221226540 Version: 5.1.2600.1106 (xpsp1.020828-1920) Modules
| |||||||||||||||
| 2400 | "C:\Windows\regedit.exe" /s 0000EA30.reg | C:\Windows\regedit.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2800 | devcon install vusbbus.inf root\vusbbus | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\devcon.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Setup API Exit code: 3221226540 Version: 5.1.2600.1106 (xpsp1.020828-1920) Modules
| |||||||||||||||
| 3036 | "C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\devcon.exe" remove root\vusbbus | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\devcon.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Setup API Exit code: 3221226540 Version: 5.1.2600.1106 (xpsp1.020828-1920) Modules
| |||||||||||||||
Total events
2 876
Read events
2 665
Write events
211
Delete events
0
Modification events
| (PID) Process: | (1756) f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1756) f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1756) f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1756) f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3136) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3136) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3136) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3136) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1936) devcon.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (1936) devcon.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
Executable files
8
Suspicious files
17
Text files
12
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1756 | f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe | C:\Users\admin\AppData\Local\Temp\FP34C.tmp | text | |
MD5:— | SHA256:— | |||
| 1756 | f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\install.bat | text | |
MD5:— | SHA256:— | |||
| 1756 | f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\vusbbus.inf | binary | |
MD5:— | SHA256:— | |||
| 1756 | f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\0000EA30.REG | text | |
MD5:— | SHA256:— | |||
| 1756 | f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\remove.bat | text | |
MD5:— | SHA256:— | |||
| 1280 | DrvInst.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1756 | f8fb4fb205e65d957e0ab4bf568c394ae3af6186eee90751161d6df85f0d840a.exe | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\VUsbBus.sys | executable | |
MD5:— | SHA256:— | |||
| 1936 | devcon.exe | C:\Windows\INF\setupapi.dev.log | ini | |
MD5:— | SHA256:— | |||
| 1936 | devcon.exe | C:\Windows\INF\setupapi.app.log | ini | |
MD5:— | SHA256:— | |||
| 1936 | devcon.exe | C:\Users\admin\AppData\Local\Temp\{2496fcec-86e9-4706-c488-7e79283a6b56}\SETD50.tmp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
regedit.exe | REGEDIT: CreateFile failed, GetLastError() = 2
|