| File name: | Run Burp Suite Professional Edition [ ViP ].exe |
| Full analysis: | https://app.any.run/tasks/9e9396eb-8997-46bb-ab93-f93c8be6fa0e |
| Verdict: | Malicious activity |
| Analysis date: | August 06, 2021, 05:24:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DCD54272C49372A7130346FD7C419F3D |
| SHA1: | 4AC48B6380137677BDB911A20F7F54F22834312E |
| SHA256: | F8F79CE67015DBD0CFCCA4BFF40E4C65A600FDC36C17ECBA49C98EFDB4AC08EA |
| SSDEEP: | 24576:/AHnh+eWsN3skA4RV1Hom2KXMmHak7M5:ih+ZkldoPK8Yakm |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- cmd.exe (PID: 3896)
- Run Burp Suite Professional Edition [ ViP ].exe (PID: 376)
Starts CMD.EXE for commands execution
- Run Burp Suite Professional Edition [ ViP ].exe (PID: 376)
Reads the computer name
- Run Burp Suite Professional Edition [ ViP ].exe (PID: 376)
Reads mouse settings
- Run Burp Suite Professional Edition [ ViP ].exe (PID: 376)
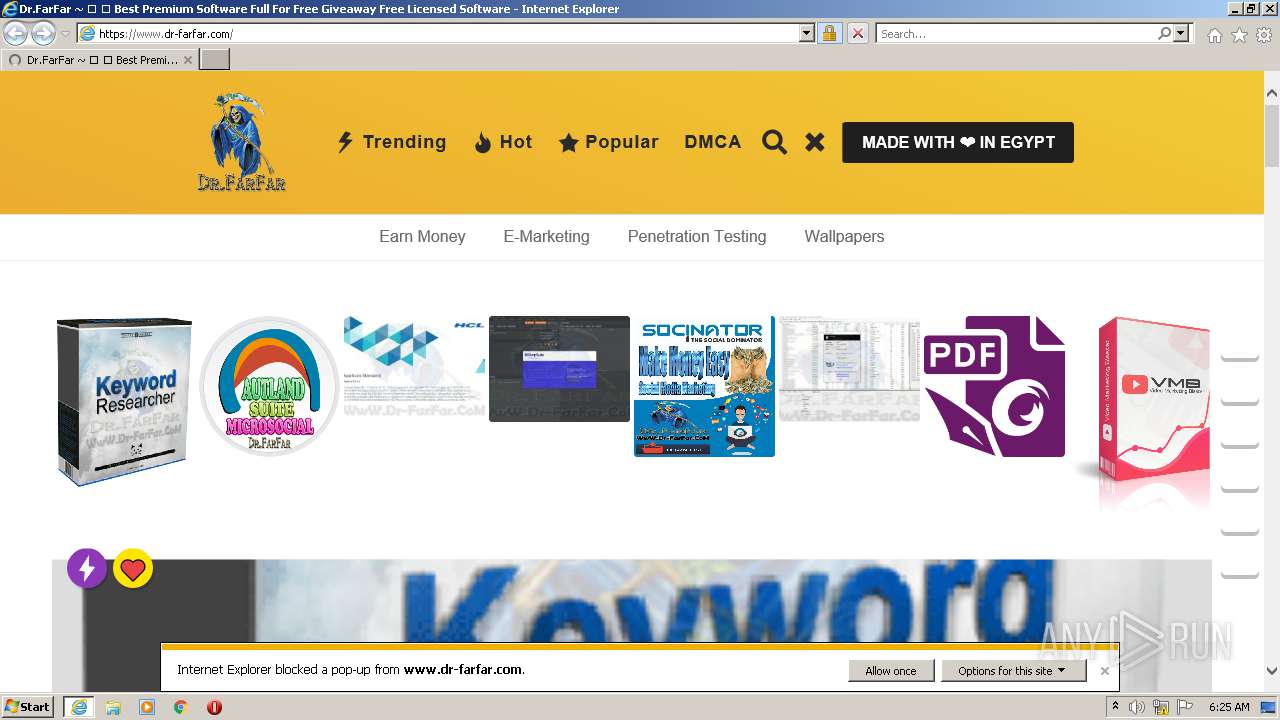
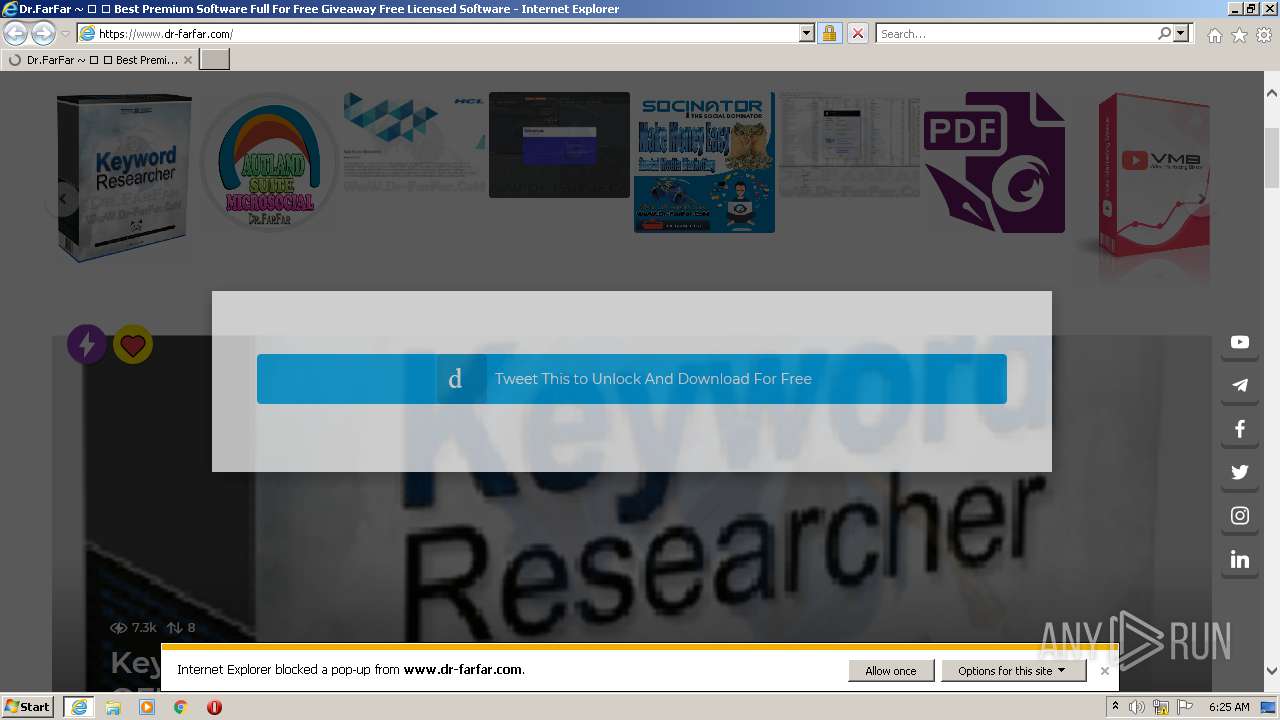
Starts Internet Explorer
- Run Burp Suite Professional Edition [ ViP ].exe (PID: 376)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2292)
INFO
Checks supported languages
- iexplore.exe (PID: 932)
- iexplore.exe (PID: 2292)
Reads the computer name
- iexplore.exe (PID: 932)
- iexplore.exe (PID: 2292)
Application launched itself
- iexplore.exe (PID: 932)
Changes internet zones settings
- iexplore.exe (PID: 932)
Reads settings of System Certificates
- iexplore.exe (PID: 2292)
- iexplore.exe (PID: 932)
Checks Windows Trust Settings
- iexplore.exe (PID: 932)
- iexplore.exe (PID: 2292)
Reads internet explorer settings
- iexplore.exe (PID: 2292)
Changes settings of System certificates
- iexplore.exe (PID: 2292)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2292)
Creates files in the user directory
- iexplore.exe (PID: 2292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| AssemblyVersion: | 1337 |
|---|---|
| ProductVersion: | 1337 |
| ProductName: | Burp Suite Professional Edition [ ViP ] |
| OriginalFileName: | Burp Suite Professional Edition.exe |
| LegalTrademarks: | Burp Suite Professional Edition [ ViP ] |
| LegalCopyright: | Copyright © Dr.FarFar |
| InternalName: | Burp Suite Professional Edition.exe |
| FileVersion: | 1337 |
| FileDescription: | Burp Suite Professional Edition [ ViP ] |
| CompanyName: | Dr.FarFar | www.Dr-FarFar.com |
| Comments: | www.Dr-FarFar.com |
| CharacterSet: | Unicode |
| LanguageCode: | English (British) |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.3.3.7 |
| FileVersionNumber: | 1.3.3.7 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x2800a |
| UninitializedDataSize: | - |
| InitializedDataSize: | 277504 |
| CodeSize: | 581632 |
| LinkerVersion: | 12 |
| PEType: | PE32 |
| TimeStamp: | 2020:07:24 05:51:34+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Jul-2020 03:51:34 |
| Detected languages: |
|
| Comments: | www.Dr-FarFar.com |
| CompanyName: | Dr.FarFar | www.Dr-FarFar.com |
| FileDescription: | Burp Suite Professional Edition [ ViP ] |
| FileVersion: | 1337 |
| InternalName: | Burp Suite Professional Edition.exe |
| LegalCopyright: | Copyright © Dr.FarFar |
| LegalTrademarks: | Burp Suite Professional Edition [ ViP ] |
| OriginalFilename: | Burp Suite Professional Edition.exe |
| ProductName: | Burp Suite Professional Edition [ ViP ] |
| ProductVersion: | 1337 |
| Assembly Version: | 1337 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Jul-2020 03:51:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008DFDD | 0x0008E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67525 |
.rdata | 0x0008F000 | 0x0002FD8E | 0x0002FE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76324 |
.data | 0x000BF000 | 0x00008F74 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.19638 |
.rsrc | 0x000C8000 | 0x00007881 | 0x00007A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.50338 |
.reloc | 0x000D0000 | 0x00007134 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78396 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.33385 | 1629 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 4.83428 | 1128 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 4.65785 | 4264 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 4.5407 | 9640 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
11 | 3.26322 | 1628 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
12 | 3.25812 | 1126 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
42
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | "C:\Users\admin\AppData\Local\Temp\Run Burp Suite Professional Edition [ ViP ].exe" | C:\Users\admin\AppData\Local\Temp\Run Burp Suite Professional Edition [ ViP ].exe | Explorer.EXE | ||||||||||||
User: admin Company: Dr.FarFar | www.Dr-FarFar.com Integrity Level: HIGH Description: Burp Suite Professional Edition [ ViP ] Exit code: 3221225547 Version: 1337 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.dr-farfar.com/ | C:\Program Files\Internet Explorer\iexplore.exe | Run Burp Suite Professional Edition [ ViP ].exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1796 | "C:\Users\admin\AppData\Local\Temp\Run Burp Suite Professional Edition [ ViP ].exe" | C:\Users\admin\AppData\Local\Temp\Run Burp Suite Professional Edition [ ViP ].exe | — | Explorer.EXE | |||||||||||
User: admin Company: Dr.FarFar | www.Dr-FarFar.com Integrity Level: MEDIUM Description: Burp Suite Professional Edition [ ViP ] Exit code: 3221226540 Version: 1337 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:932 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3896 | C:\Windows\system32\cmd.exe /C Loader.jar | C:\Windows\system32\cmd.exe | — | Run Burp Suite Professional Edition [ ViP ].exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
20 568
Read events
20 411
Write events
157
Delete events
0
Modification events
| (PID) Process: | (932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30902915 | |||
| (PID) Process: | (932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30902915 | |||
| (PID) Process: | (932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
26
Text files
295
Unknown types
84
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2292 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9FF67FB3141440EED32363089565AE60_72EF4AD29CF40BA3DEE76AFA6BC61263 | der | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\SBF6NVH6.htm | html | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\9ja3p[1].css | text | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\9ja3o[1].css | text | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\9ja3o[1].css | text | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\9ja3p[1].js | text | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
118
DNS requests
42
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2292 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
2292 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2292 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAawPwIzCvpK6KKdRuE24AU%3D | US | der | 279 b | whitelisted |
2292 | iexplore.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
2292 | iexplore.exe | GET | 200 | 195.138.255.11:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | DE | der | 1.16 Kb | whitelisted |
2292 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2292 | iexplore.exe | GET | 200 | 195.138.255.18:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgNfzT7LrK9QNf0UmFOyDDiiUg%3D%3D | DE | der | 503 b | shared |
2292 | iexplore.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCH2WZ7Jwl83h | US | der | 1.74 Kb | whitelisted |
2292 | iexplore.exe | GET | 200 | 195.138.255.18:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgQX6EvayU3iZ0Y6rih7obV72g%3D%3D | DE | der | 503 b | shared |
2292 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2292 | iexplore.exe | 149.154.167.99:443 | telegram.org | Telegram Messenger LLP | GB | malicious |
2292 | iexplore.exe | 104.18.225.52:443 | cdn.onesignal.com | Cloudflare Inc | US | malicious |
2292 | iexplore.exe | 142.250.186.142:443 | drive.google.com | Google Inc. | US | whitelisted |
2292 | iexplore.exe | 192.0.76.3:443 | stats.wp.com | Automattic, Inc | US | suspicious |
2292 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
2292 | iexplore.exe | 192.124.249.24:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
2292 | iexplore.exe | 142.250.185.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2292 | iexplore.exe | 104.21.58.182:443 | www.mrfog.com | Cloudflare Inc | US | unknown |
2292 | iexplore.exe | 104.21.34.60:443 | www.3zdl.com | Cloudflare Inc | US | unknown |
2292 | iexplore.exe | 172.64.99.12:443 | www.dr-farfar.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dr-farfar.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
c0.wp.com |
| whitelisted |
drive.google.com |
| shared |
telegram.org |
| whitelisted |
cdn.onesignal.com |
| whitelisted |