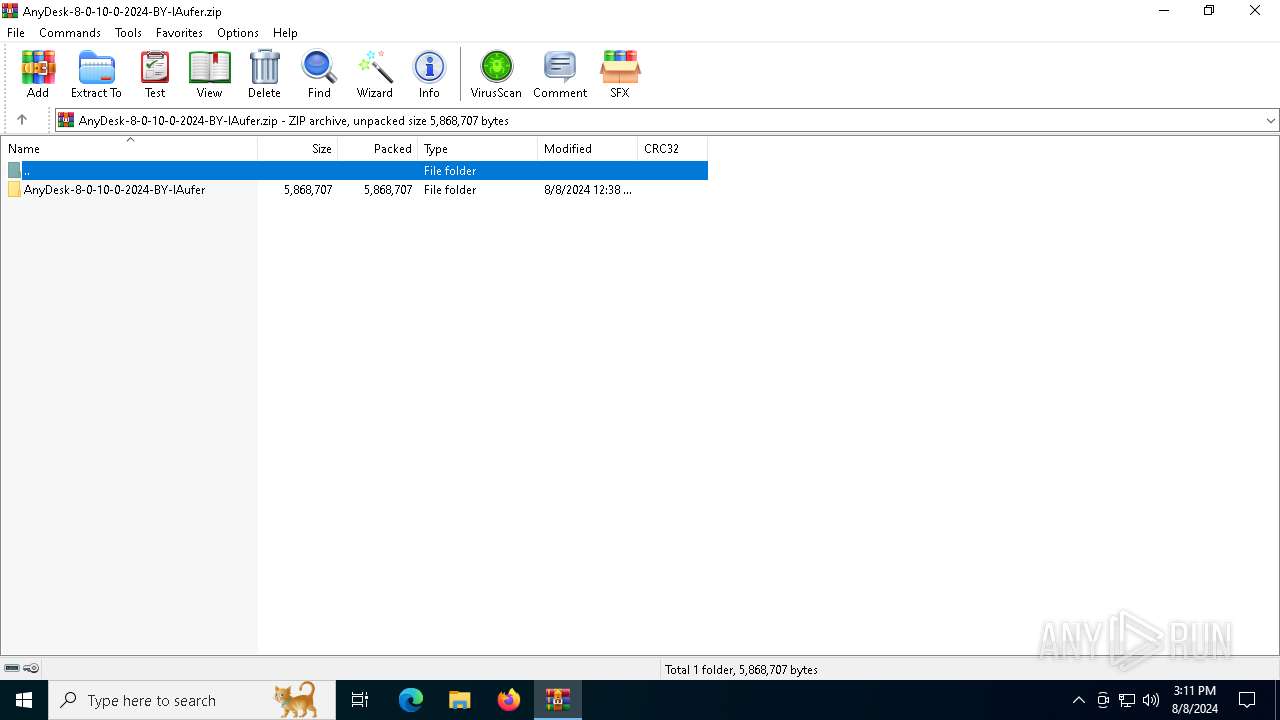
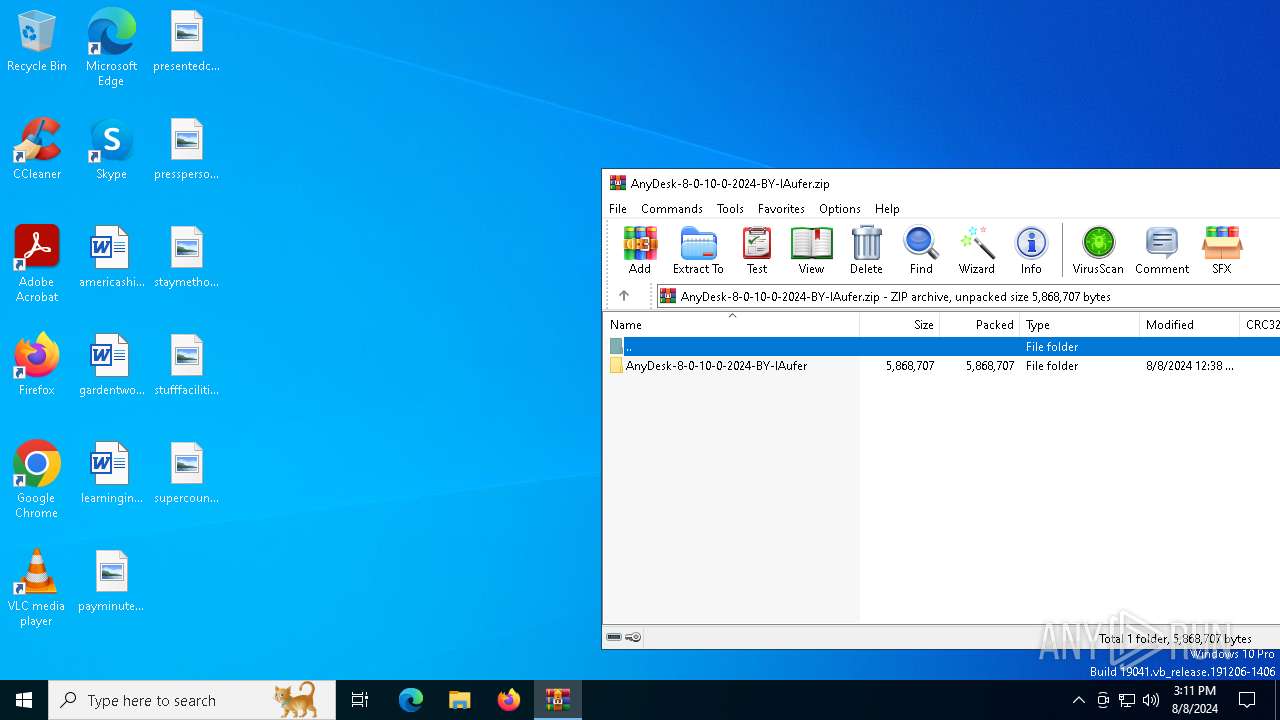
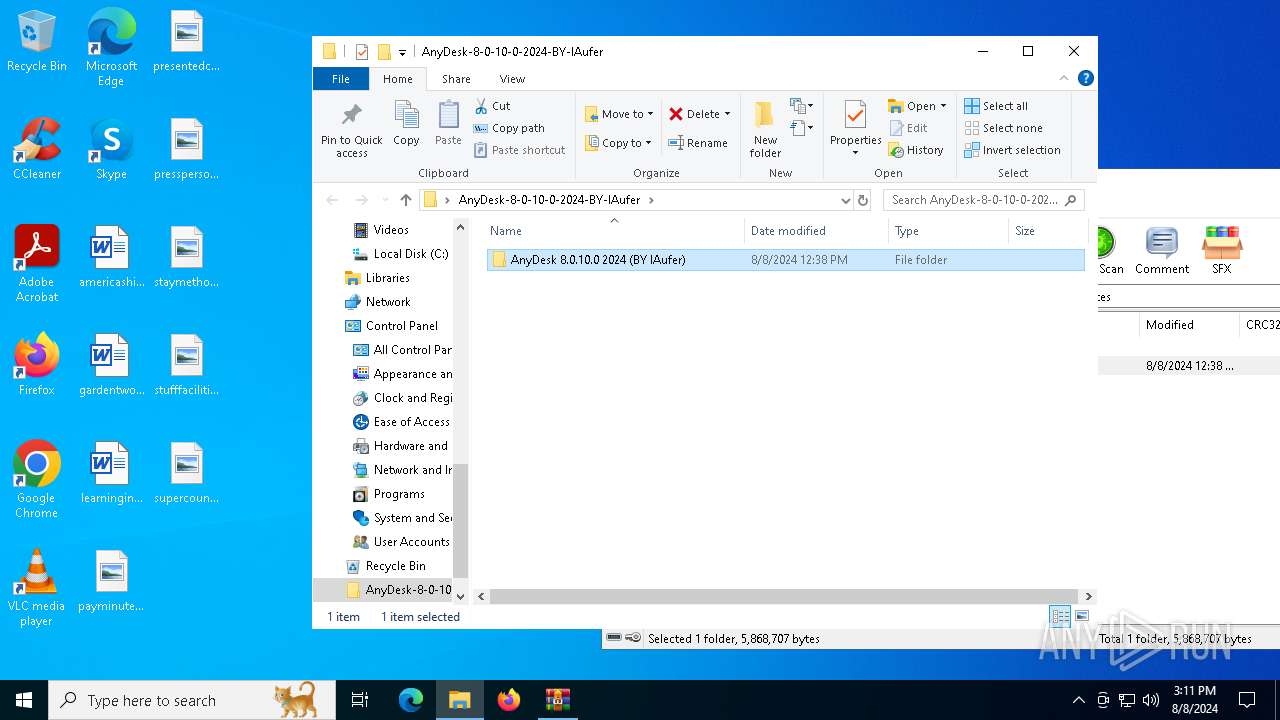
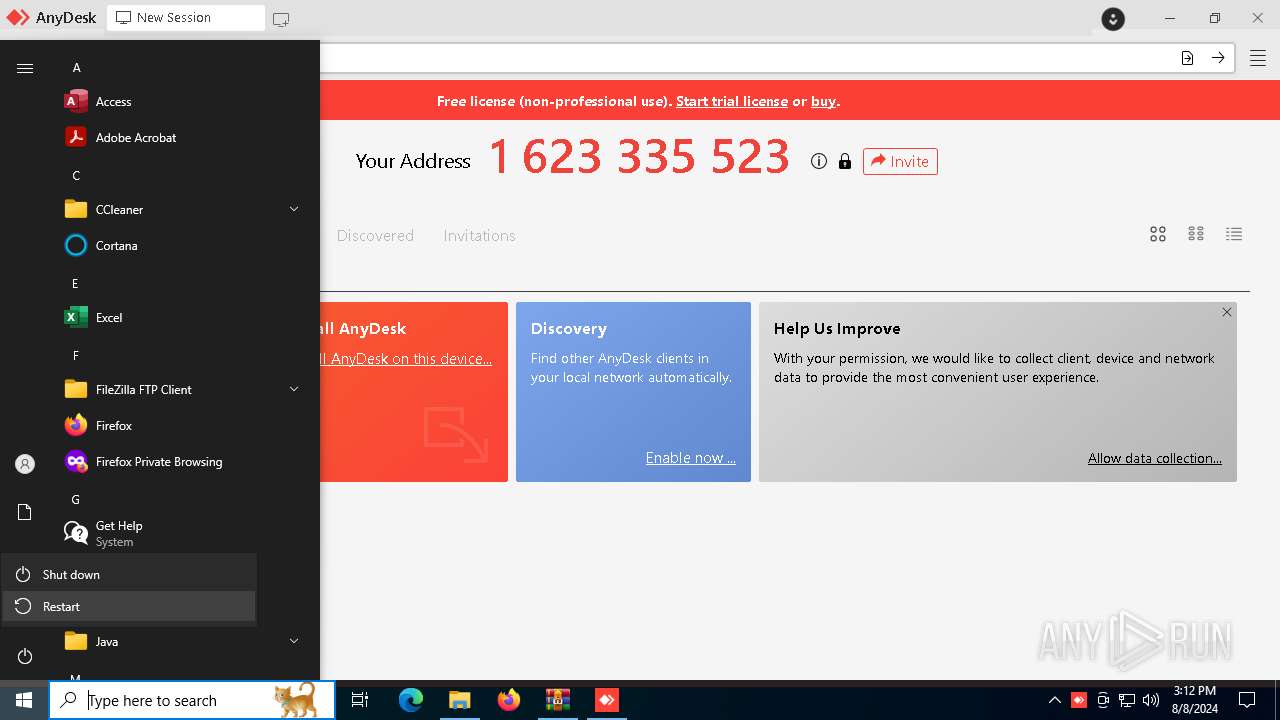
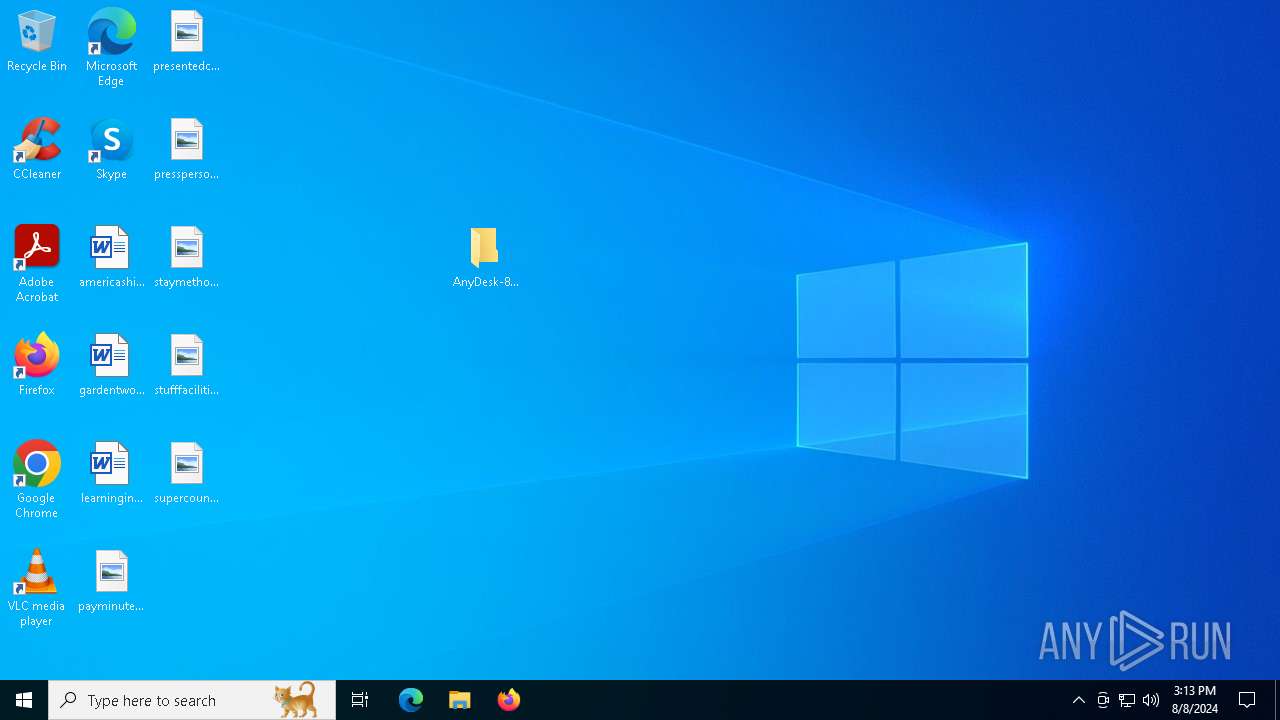
| File name: | AnyDesk-8-0-10-0-2024-BY-lAufer.zip |
| Full analysis: | https://app.any.run/tasks/80e4873f-91a3-4cad-afae-89667d51001a |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2024, 15:11:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | E2D6BEB90B4EE16CDE884B01BF590D17 |
| SHA1: | ECC81CFFEDA95137F218267E983CF4BC49FB3160 |
| SHA256: | F8F319208670D83A68A015B9D43D52F76EE6F372E6A837158D49FE46AF9603FF |
| SSDEEP: | 98304:bf4bAtLvz+qHVZ+eMR4YAPkW/PvNuaiXxKCGpIPahlhYjHiKloGshfz+D+yR6daW:mnxbeqNfk |
MALICIOUS
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 2228)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 2228)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 2228)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 2228)
SUSPICIOUS
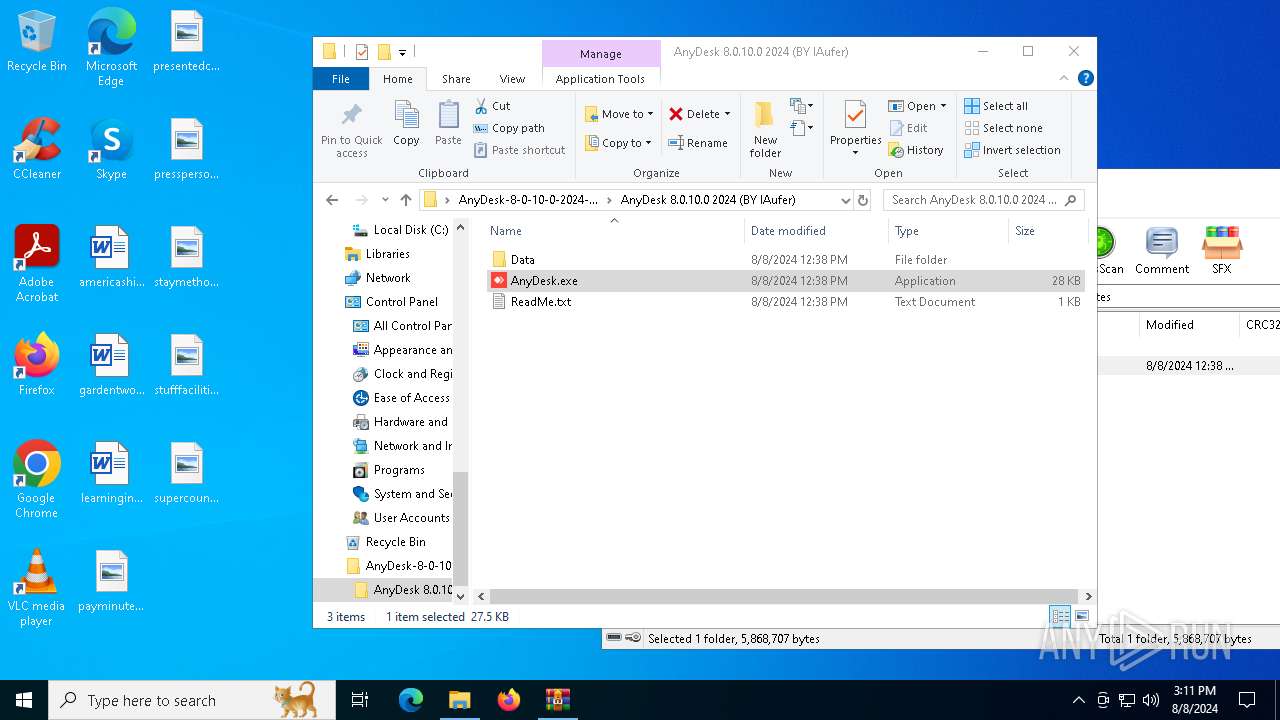
Checks Windows Trust Settings
- AnyDesk.exe (PID: 7108)
Executing commands from a ".bat" file
- AnyDesk.exe (PID: 7108)
- cmd.exe (PID: 2872)
Reads security settings of Internet Explorer
- AnyDesk.exe (PID: 7108)
Reads the date of Windows installation
- AnyDesk.exe (PID: 7108)
Application launched itself
- cmd.exe (PID: 2872)
- Classic.exe (PID: 3864)
- powershell.exe (PID: 2228)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2872)
- AnyDesk.exe (PID: 7108)
Allows hiding code in an environment variable
- cmd.exe (PID: 5908)
- cmd.exe (PID: 5980)
- cmd.exe (PID: 1948)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 4296)
- cmd.exe (PID: 2336)
- cmd.exe (PID: 4016)
- cmd.exe (PID: 2008)
- cmd.exe (PID: 2204)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2872)
- powershell.exe (PID: 2228)
Executable content was dropped or overwritten
- Classic.exe (PID: 2852)
Cryptography encrypted command line is found
- cmd.exe (PID: 3032)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2228)
Drops the executable file immediately after the start
- Classic.exe (PID: 2852)
- WinRAR.exe (PID: 304)
Potential Corporate Privacy Violation
- Classic.exe (PID: 2852)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 1064)
Process checks specific path in scheduled tasks
- powershell.exe (PID: 5468)
Probably obfuscated PowerShell command line is found
- powershell.exe (PID: 2228)
INFO
Reads the machine GUID from the registry
- AnyDesk.exe (PID: 7108)
- Classic.exe (PID: 2852)
Checks proxy server information
- AnyDesk.exe (PID: 7108)
- Classic.exe (PID: 7076)
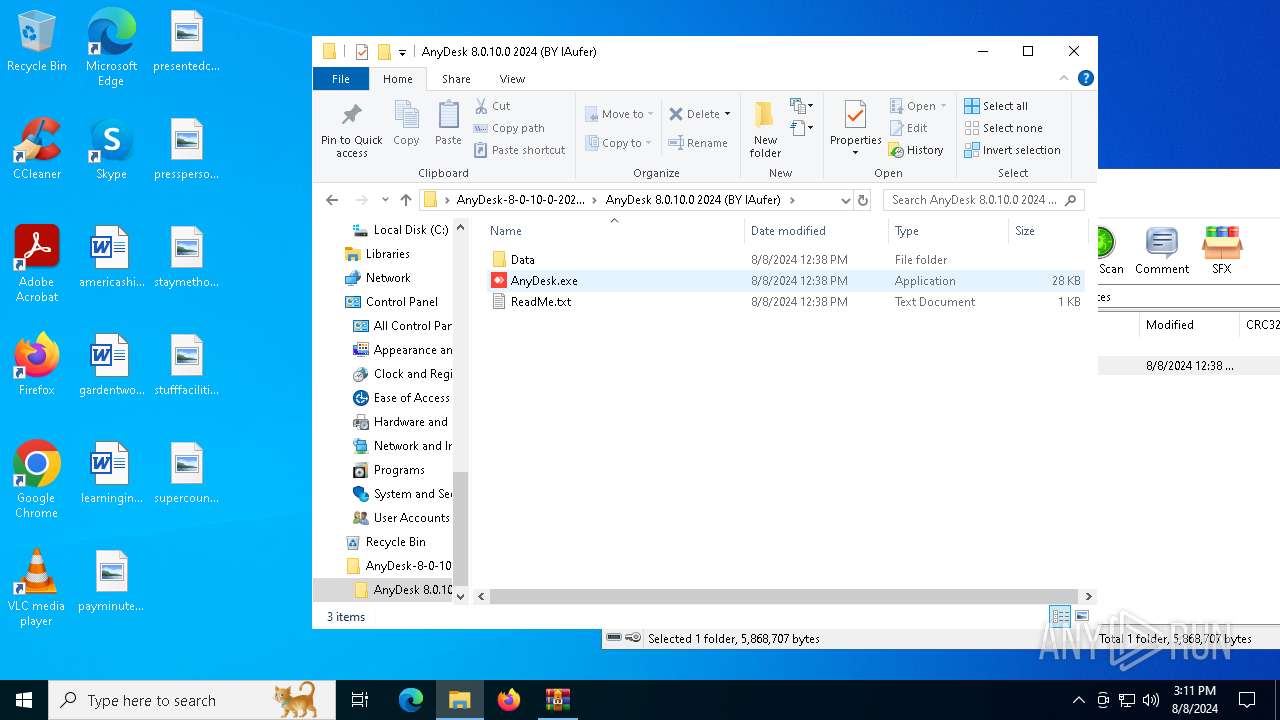
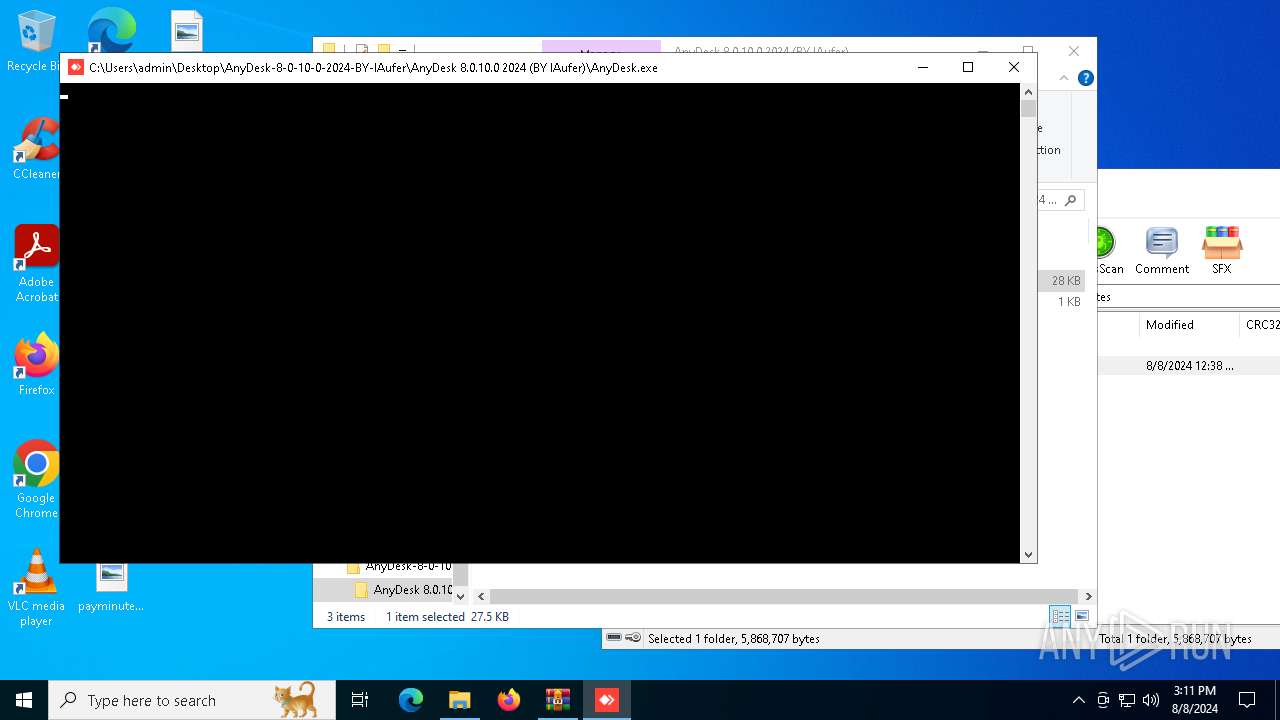
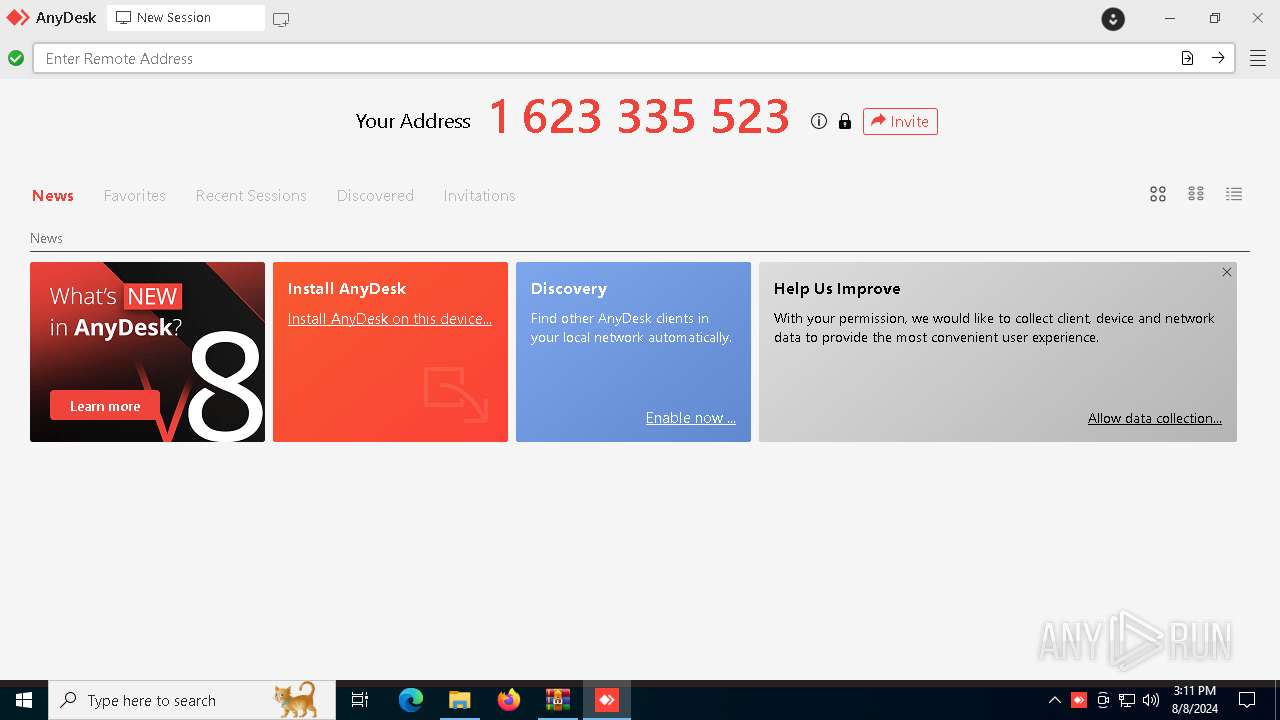
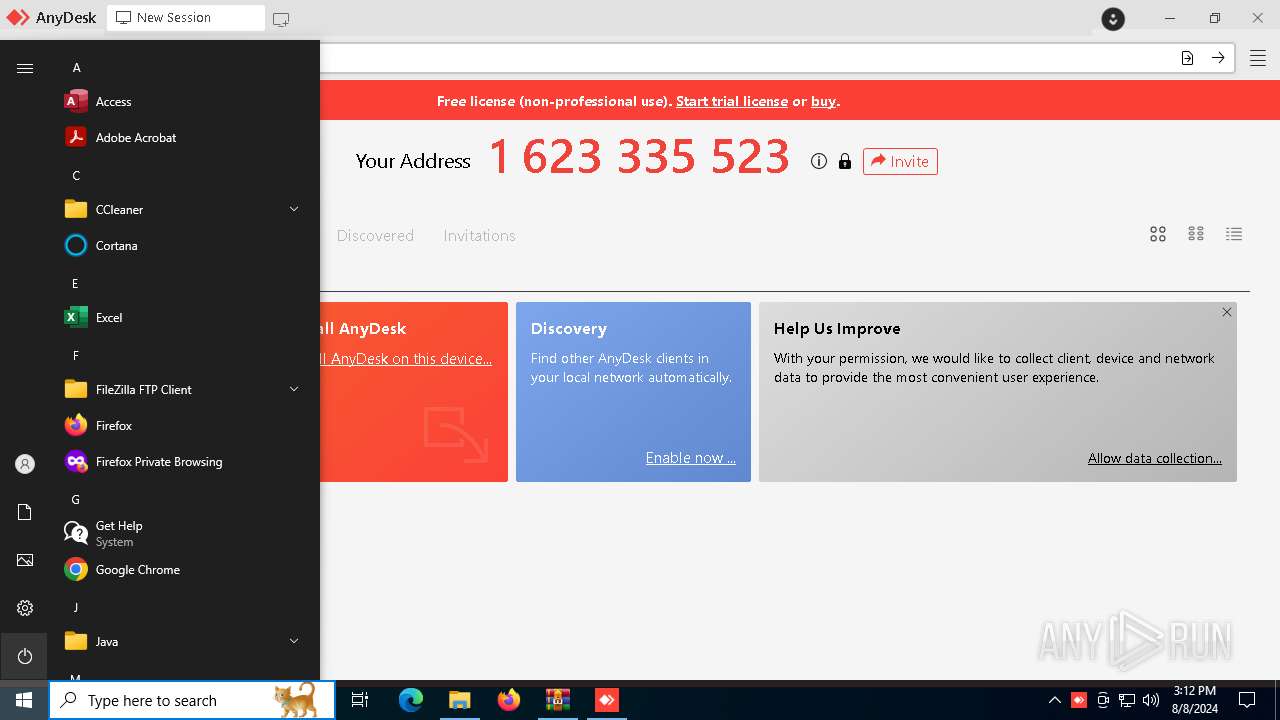
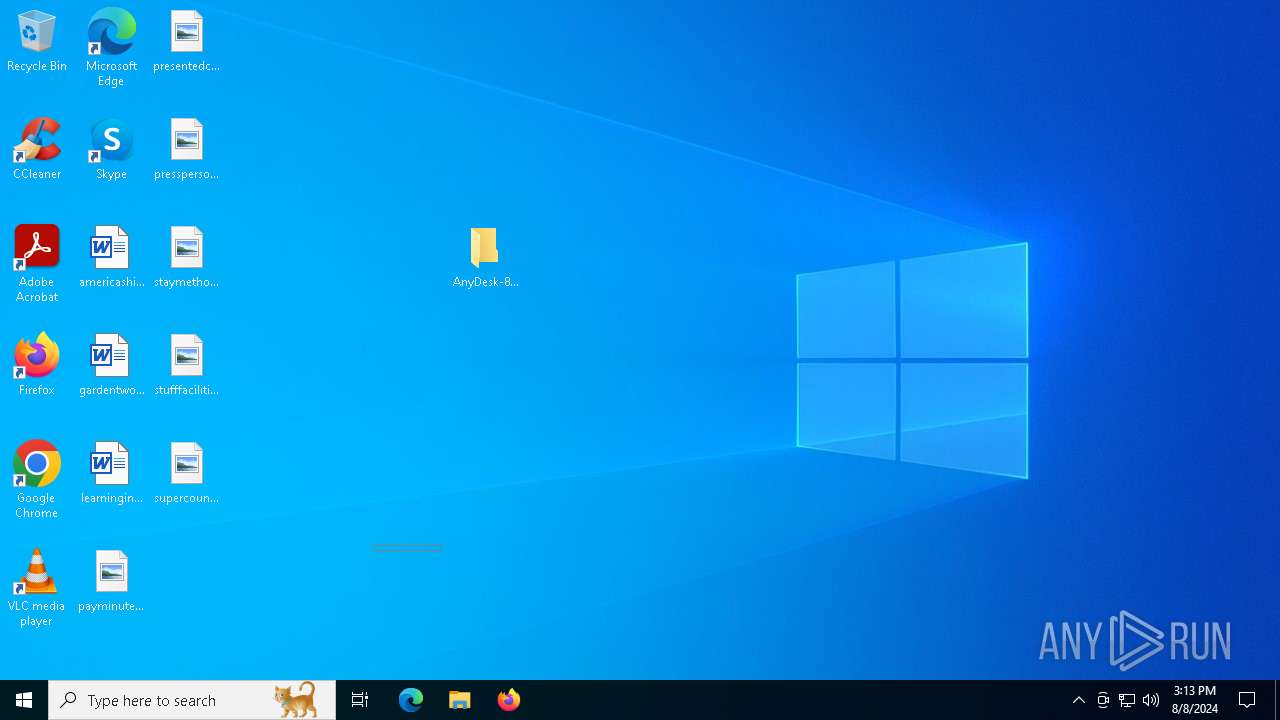
Manual execution by a user
- AnyDesk.exe (PID: 7108)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 304)
Reads the computer name
- Classic.exe (PID: 3864)
- Classic.exe (PID: 2852)
- Classic.exe (PID: 7076)
- TextInputHost.exe (PID: 6392)
- AnyDesk.exe (PID: 7108)
- PLUGScheduler.exe (PID: 1064)
Checks supported languages
- AnyDesk.exe (PID: 7108)
- Classic.exe (PID: 3864)
- TextInputHost.exe (PID: 6392)
- PLUGScheduler.exe (PID: 1064)
- Classic.exe (PID: 2852)
- Classic.exe (PID: 7076)
Reads the software policy settings
- AnyDesk.exe (PID: 7108)
Checks if a key exists in the options dictionary (POWERSHELL)
- AnyDesk.exe (PID: 7108)
Process checks whether UAC notifications are on
- Classic.exe (PID: 3864)
Create files in a temporary directory
- AnyDesk.exe (PID: 7108)
Reads Environment values
- AnyDesk.exe (PID: 7108)
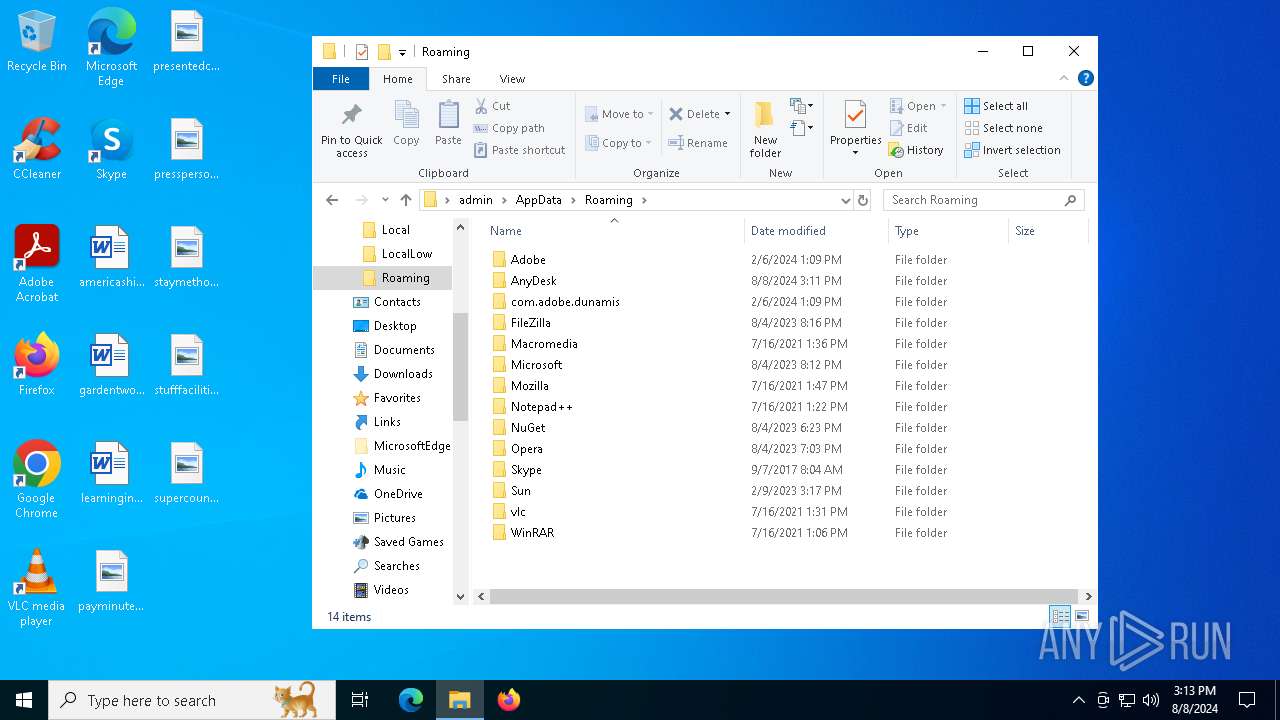
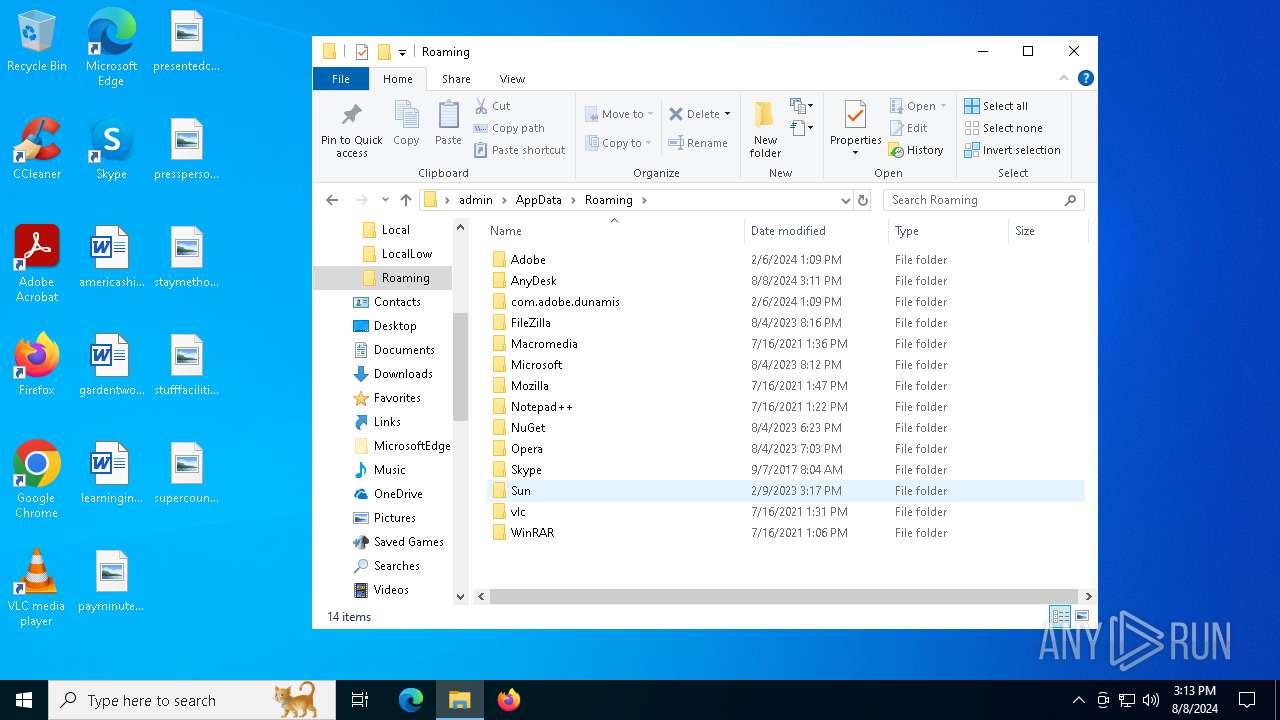
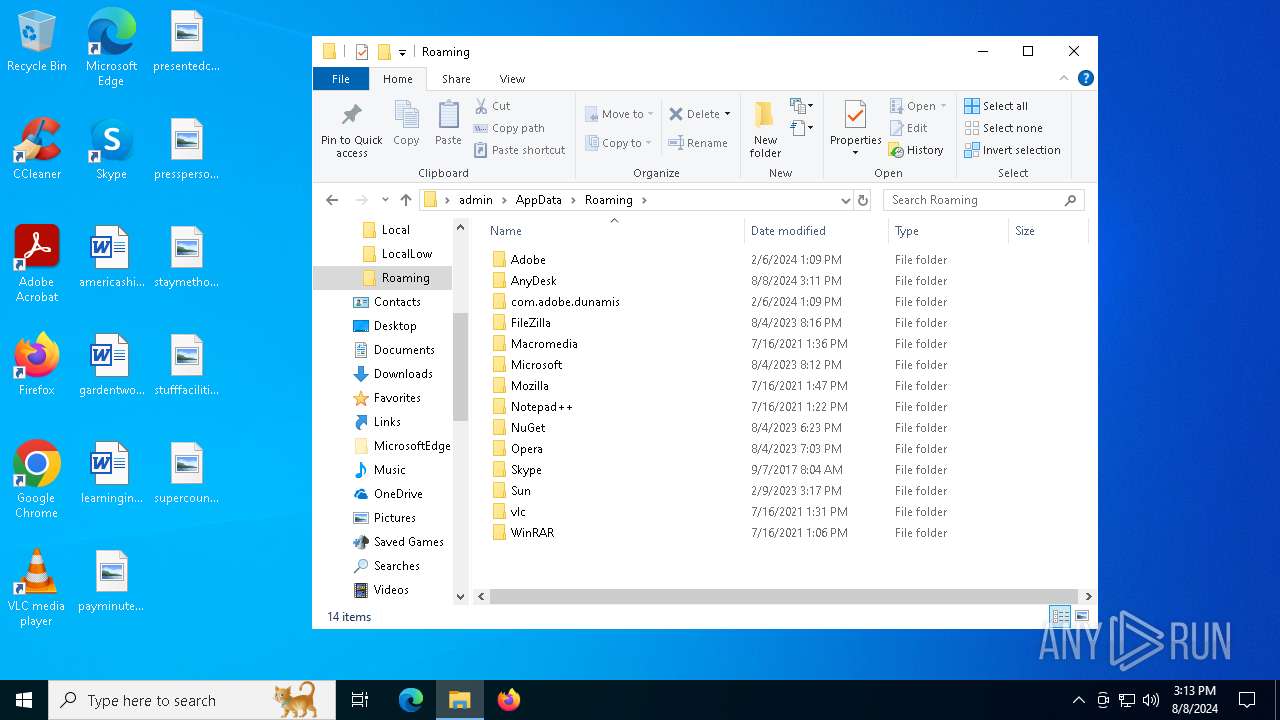
Creates files or folders in the user directory
- AnyDesk.exe (PID: 7108)
- Classic.exe (PID: 3864)
Process checks computer location settings
- AnyDesk.exe (PID: 7108)
- Classic.exe (PID: 2852)
- Classic.exe (PID: 7076)
Reads CPU info
- Classic.exe (PID: 3864)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 2228)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 2228)
Checks current location (POWERSHELL)
- powershell.exe (PID: 2228)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2228)
Creates files in the program directory
- PLUGScheduler.exe (PID: 1064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:08:08 14:38:54 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
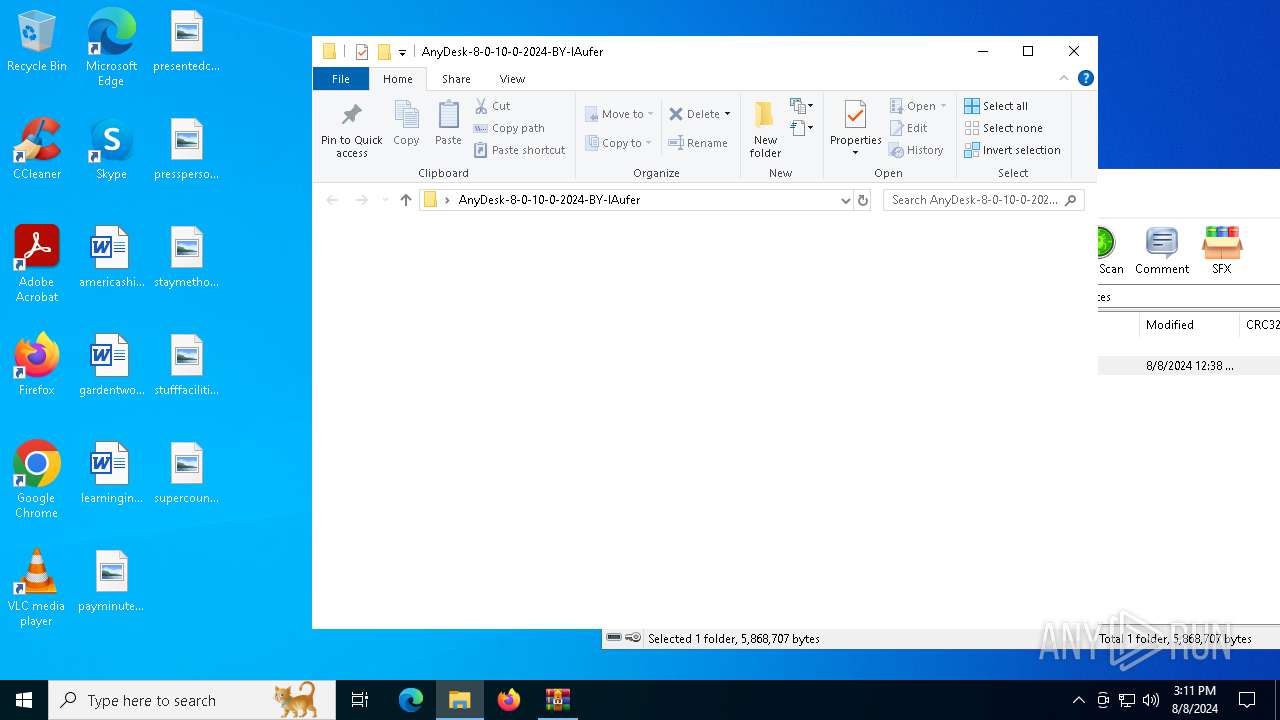
| ZipFileName: | AnyDesk-8-0-10-0-2024-BY-lAufer/ |
Total processes
262
Monitored processes
24
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\AnyDesk-8-0-10-0-2024-BY-lAufer.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1073807364 Version: 5.91.0 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1948 | cmd /c "set __=^&rem" | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | cmd /c "set __=^&rem" | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2204 | cmd /c "set __=^&rem" | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2228 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1073807364 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2336 | cmd /c "set __=^&rem" | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2852 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\Desktop\AnyDesk-8-0-10-0-2024-BY-lAufer\AnyDesk 8.0.10.0 2024 (BY lAufer)\Data\Classic.exe" --local-service | C:\Users\admin\Desktop\AnyDesk-8-0-10-0-2024-BY-lAufer\AnyDesk 8.0.10.0 2024 (BY lAufer)\Data\Classic.exe | Classic.exe | ||||||||||||
User: admin Company: AnyDesk Software GmbH Integrity Level: MEDIUM Description: AnyDesk Exit code: 1073807364 Version: 8.0.10 Modules
| |||||||||||||||
Total events
28 128
Read events
28 102
Write events
26
Delete events
0
Modification events
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\AnyDesk-8-0-10-0-2024-BY-lAufer.zip | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7108) AnyDesk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7108) AnyDesk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
4
Suspicious files
17
Text files
16
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3864 | Classic.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\75fdacd8330bac18.customDestinations-ms | binary | |
MD5:7C625E96678EB15DF307F4186CB8003C | SHA256:A79CBE456B82FF14339DCACA43CA66E8664BB90B064A51205058403CB81EC5DF | |||
| 7108 | AnyDesk.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nmejhcht.bgh.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2852 | Classic.exe | C:\Users\admin\AppData\Roaming\AnyDesk\service.conf | text | |
MD5:072F9D80C61F1BC912D6D0145B2E5027 | SHA256:79D52BC97A54EE687229929FEF3805FF5359D09741462381B2037E157AB32A97 | |||
| 2228 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_t15ewq5a.5y4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 304 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa304.21515\AnyDesk-8-0-10-0-2024-BY-lAufer\AnyDesk 8.0.10.0 2024 (BY lAufer)\AnyDesk.exe | executable | |
MD5:F5ECF2EB39C378971BF78F7A7A92CE8B | SHA256:4506BAAA1B8B9284E432B1396D35D6157EC10109EA0A0ADD7B4E08E7110284FA | |||
| 7108 | AnyDesk.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\FE17BEC2A573BC9AE36869D0274FFA19_6DA81F04C5F9EAD2CD0268808FCE61E1 | binary | |
MD5:C67694744018B32AC849460D1FE2DF1C | SHA256:8415841FB684C9A2458CB6EFEC18E0B5275D84F4D1575712001021D0207221D5 | |||
| 304 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa304.21515\AnyDesk-8-0-10-0-2024-BY-lAufer\AnyDesk 8.0.10.0 2024 (BY lAufer)\Data\setup.dll | text | |
MD5:50666591FB42D9E912A11CAA2DED4ADD | SHA256:652A740A2B4C79E78D301A64229E3712639BBD4B9E9668E30C907F7B27D3B2CC | |||
| 7108 | AnyDesk.exe | C:\Users\admin\AppData\Local\Temp\setup.bat | text | |
MD5:50666591FB42D9E912A11CAA2DED4ADD | SHA256:652A740A2B4C79E78D301A64229E3712639BBD4B9E9668E30C907F7B27D3B2CC | |||
| 7108 | AnyDesk.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\248DDD9FCF61002E219645695E3FFC98_B65931808D21CEA247CFE7AD8A5650BC | binary | |
MD5:F344DEB4F1E4C912FB4436901B23490C | SHA256:C0A72E1B8E1417D63DB48EA2DBE774FA6067AF02475C2BBFCD46D2FF206C72D4 | |||
| 7108 | AnyDesk.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_u5js521o.woa.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
78
DNS requests
30
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7108 | AnyDesk.exe | GET | 200 | 52.6.97.148:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSoEwb5tith0jIBy9frSyNGB1lsAAQUNr1J%2FzEs669qQP6ZwBbtuvxI3V8CEC5PS6JcFeO7CIfoudHuK%2F8%3D | unknown | — | — | whitelisted |
6348 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 52.6.97.148:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQg3SSkKA74hABkhmlBtJTz8w3hlAQU%2BWC71OPVNPa49QaAJadz20ZpqJ4CEEJLalPOx2YUHCpjsaUcQQQ%3D | unknown | — | — | whitelisted |
2852 | Classic.exe | POST | 200 | 18.245.86.105:80 | http://api.playanext.com/httpapi | unknown | — | — | unknown |
6316 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4620 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2928 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
532 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5336 | SearchApp.exe | 104.126.37.139:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
ocsps.ssl.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2852 | Classic.exe | Potential Corporate Privacy Violation | ET USER_AGENTS AnyDesk Remote Desktop Software User-Agent |