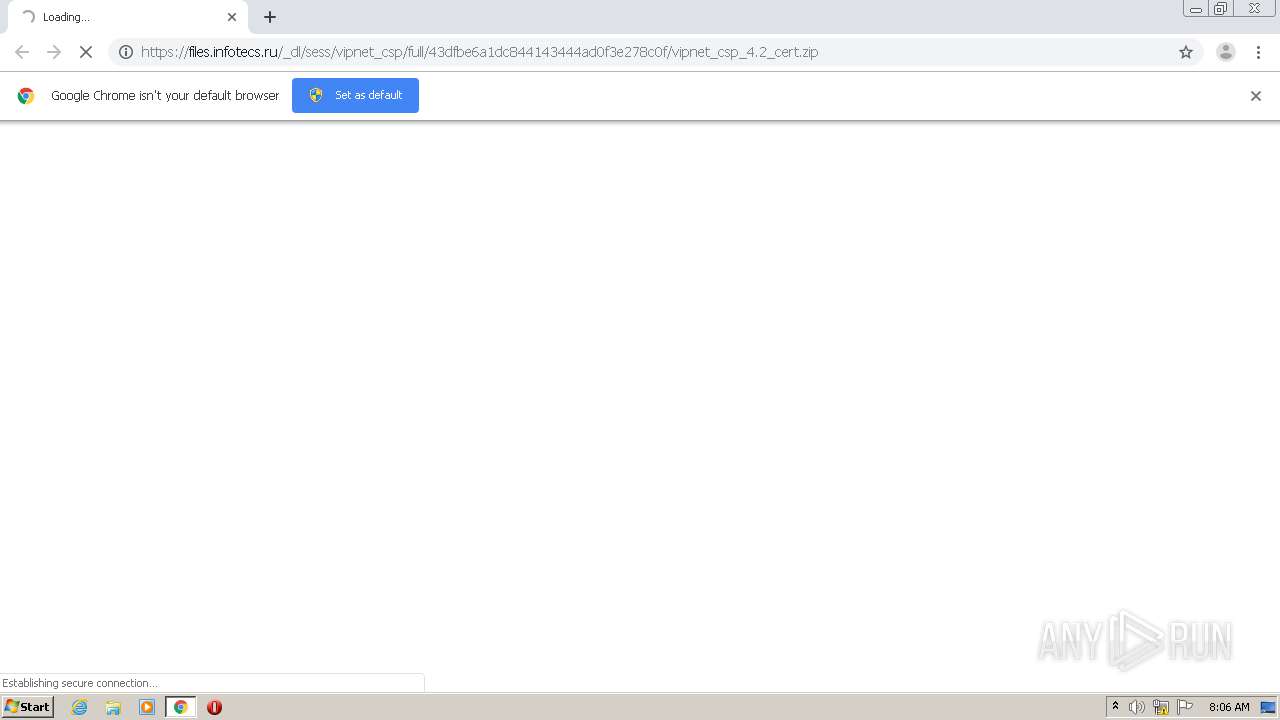
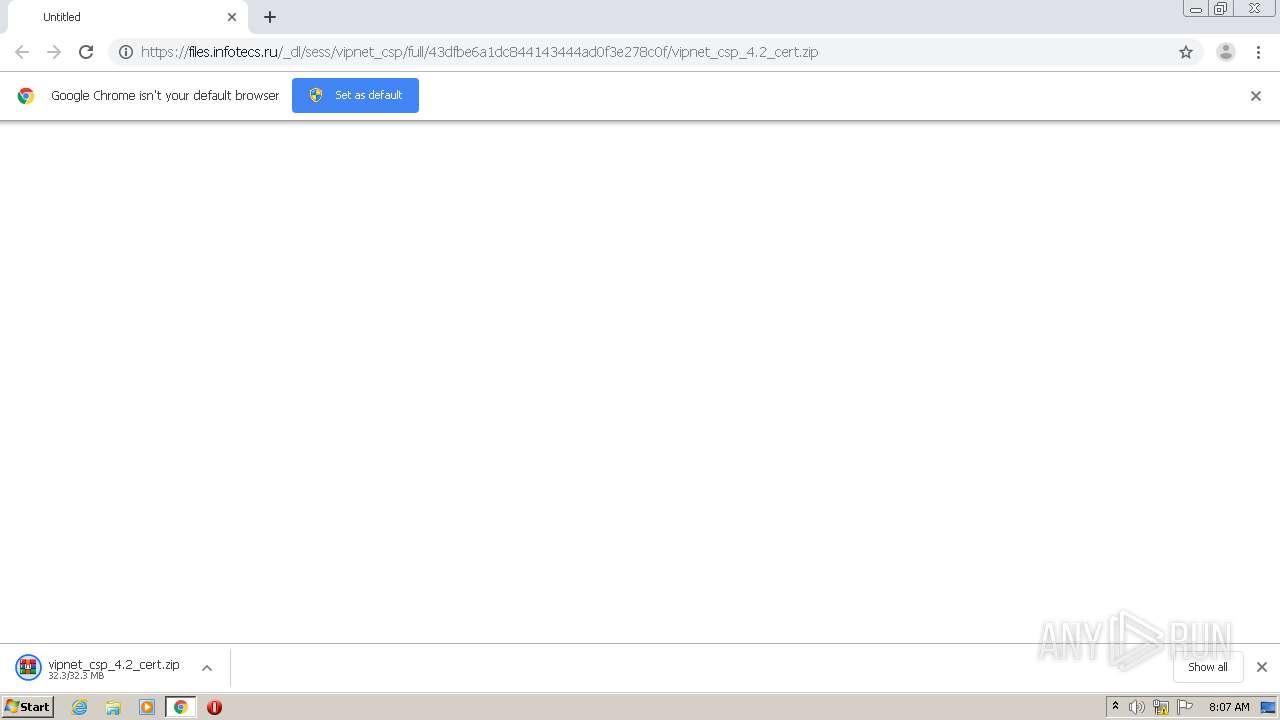
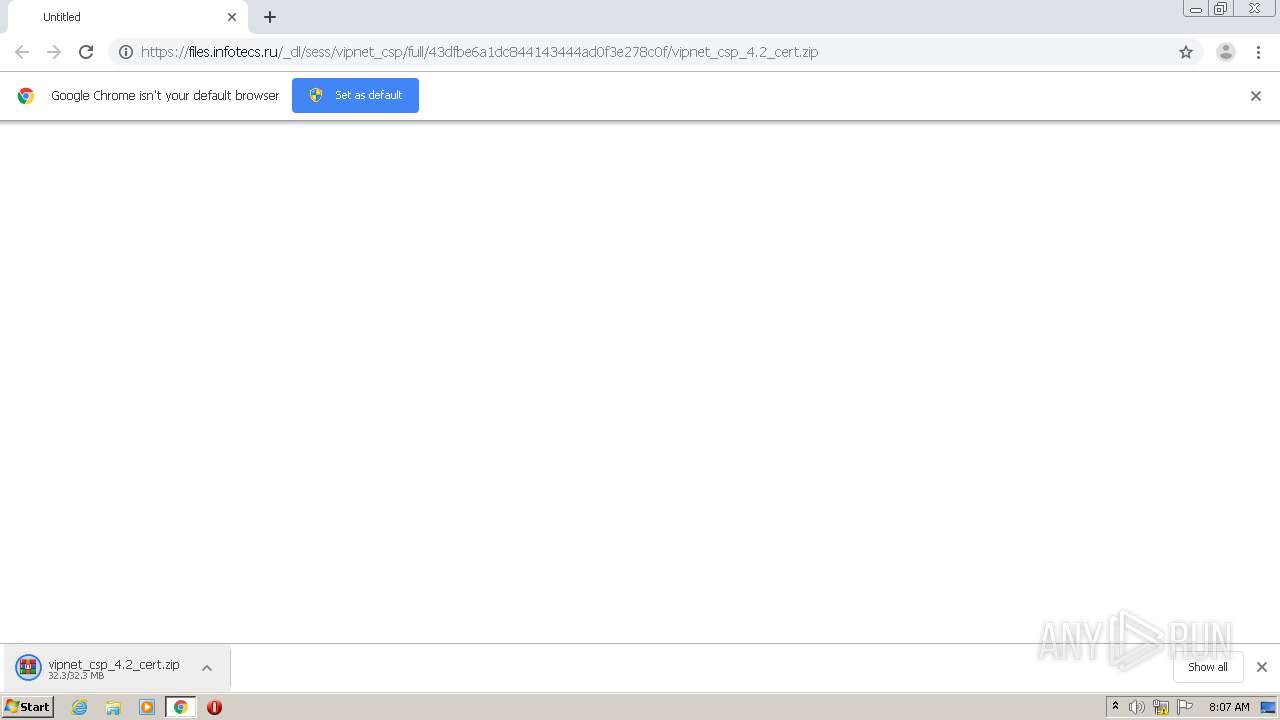
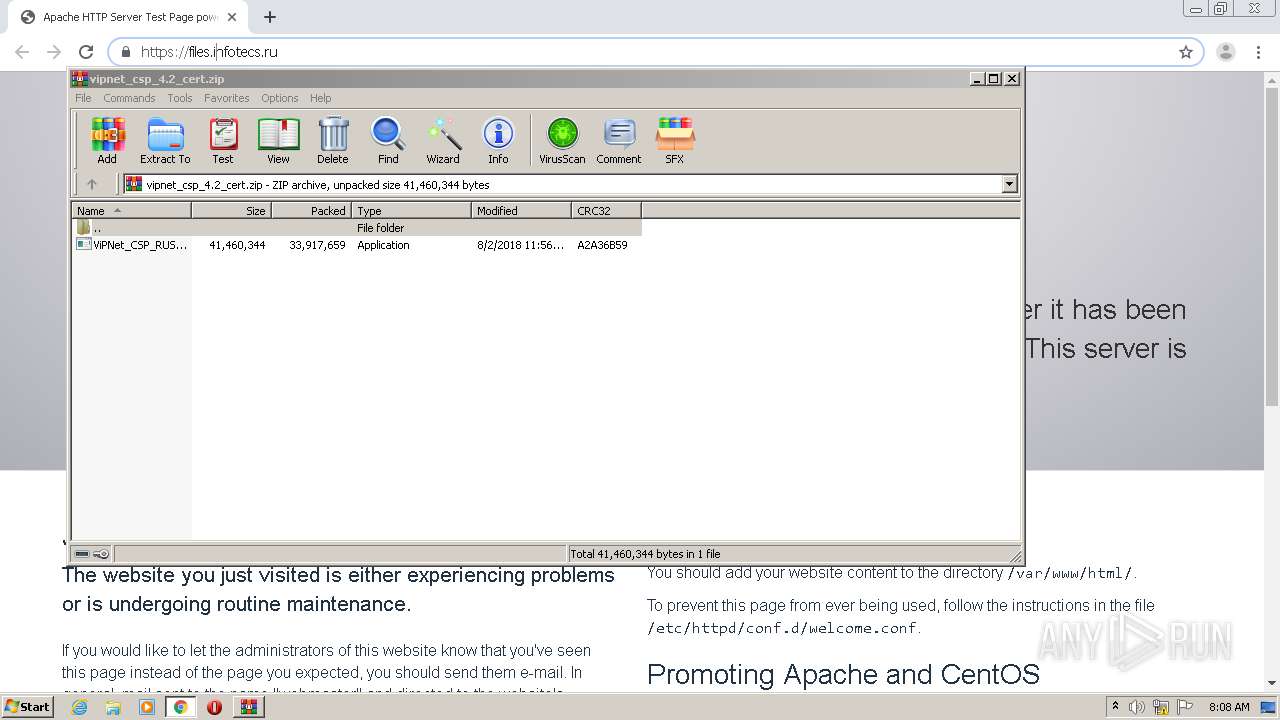
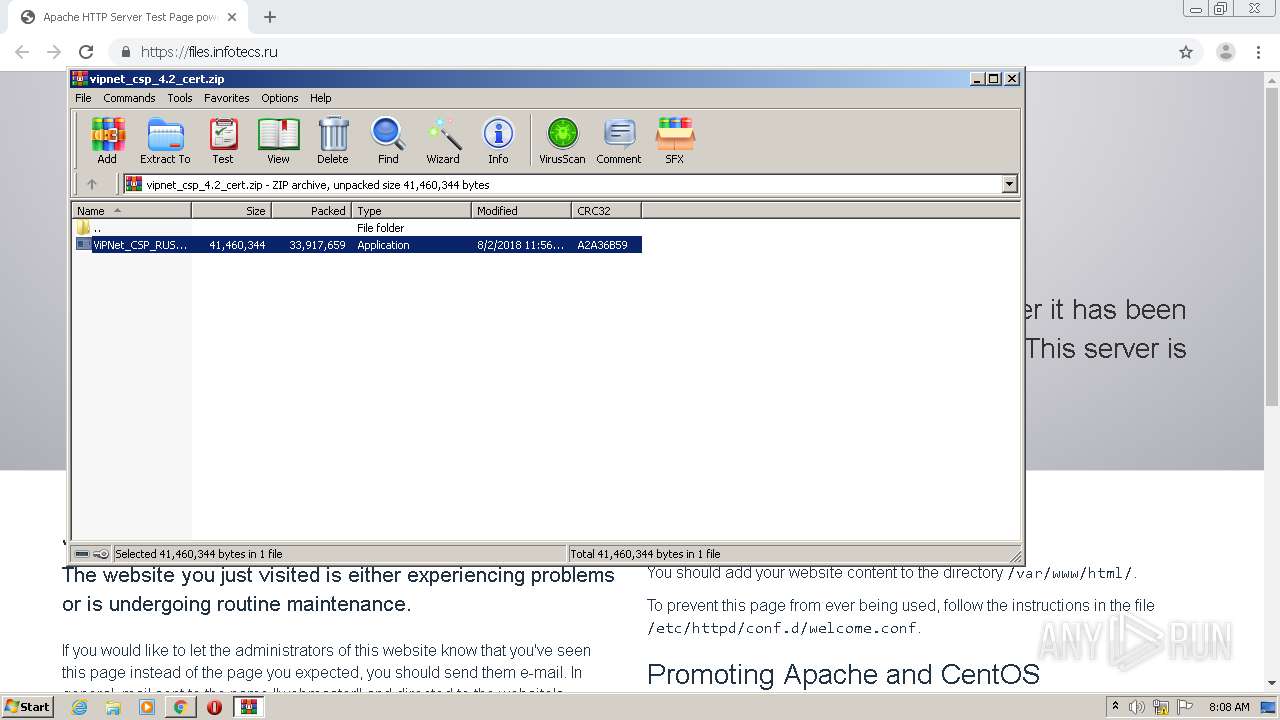
| URL: | https://files.infotecs.ru/_dl/sess/vipnet_csp/full/43dfbe6a1dc844143444ad0f3e278c0f/vipnet_csp_4.2_cert.zip |
| Full analysis: | https://app.any.run/tasks/ef91ae3c-d01d-4295-b5b1-99df3753269c |
| Verdict: | Suspicious activity |
| Analysis date: | August 24, 2020, 07:06:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B1BB56C472174434CEC60A03CD6CB4D0 |
| SHA1: | A89802E3CBBE1E46366B0376AE3A0FA4D389AF81 |
| SHA256: | F8E8A2EB57AE695CFE1866E127C8905AB7511613E4D699A7234478464ADB857E |
| SSDEEP: | 3:N8MQLAhBIWBWsfTEUQF3IKAXSdGVUU0i9XRYV:2MeAhqWBWsfIUaAXbUzib4 |
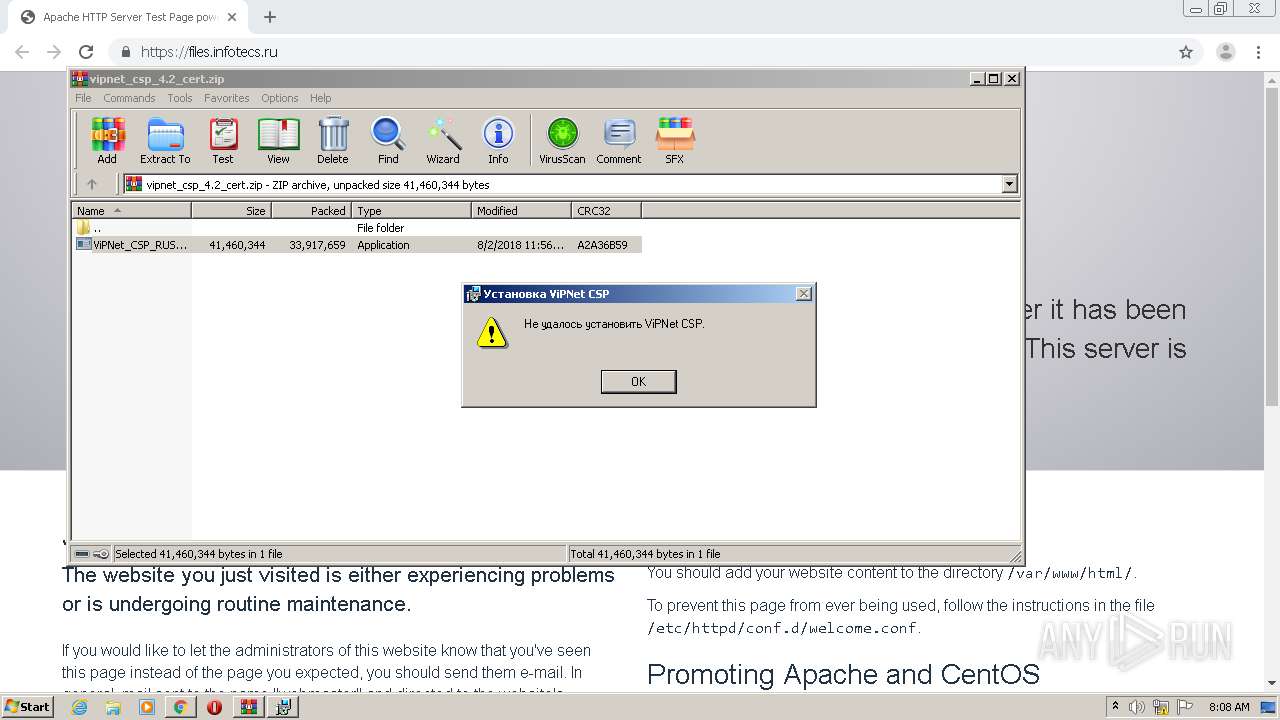
MALICIOUS
Changes settings of System certificates
- ViPNet_CSP_RUS_4.2.8.51670.exe (PID: 656)
Application was dropped or rewritten from another process
- MSI22AC.tmp (PID: 3196)
- itcsetupstdtool.exe (PID: 3084)
SUSPICIOUS
Creates files in the program directory
- ViPNet_CSP_RUS_4.2.8.51670.exe (PID: 656)
- msiexec.exe (PID: 2584)
- MSI22AC.tmp (PID: 3196)
- itcsetupstdtool.exe (PID: 3084)
Adds / modifies Windows certificates
- ViPNet_CSP_RUS_4.2.8.51670.exe (PID: 656)
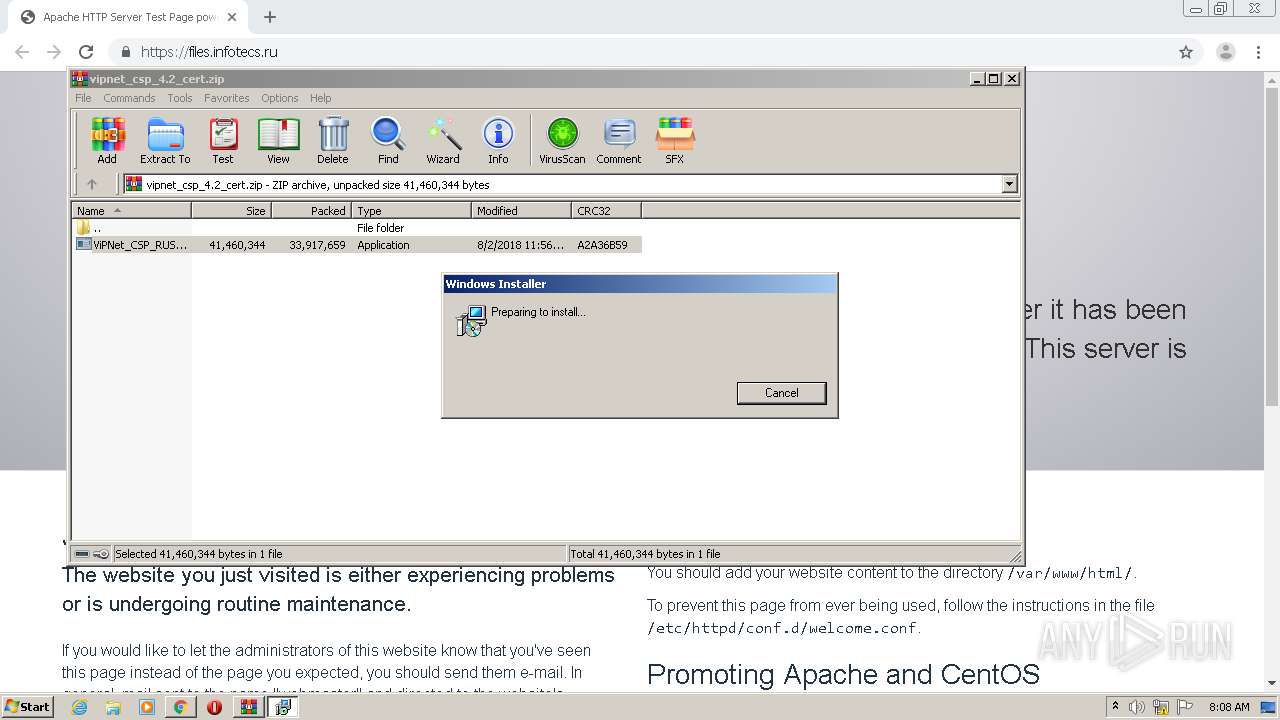
Starts Microsoft Installer
- ViPNet_CSP_RUS_4.2.8.51670.exe (PID: 656)
Starts application with an unusual extension
- msiexec.exe (PID: 2584)
Executable content was dropped or overwritten
- ViPNet_CSP_RUS_4.2.8.51670.exe (PID: 656)
- msiexec.exe (PID: 2584)
Executed via COM
- DllHost.exe (PID: 4064)
INFO
Application launched itself
- chrome.exe (PID: 2400)
Reads the hosts file
- chrome.exe (PID: 2400)
- chrome.exe (PID: 2636)
Reads settings of System Certificates
- chrome.exe (PID: 2636)
Reads Internet Cache Settings
- chrome.exe (PID: 2400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
73
Monitored processes
21
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9547617406017294490,14709065289480501797,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8440318165164466052 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
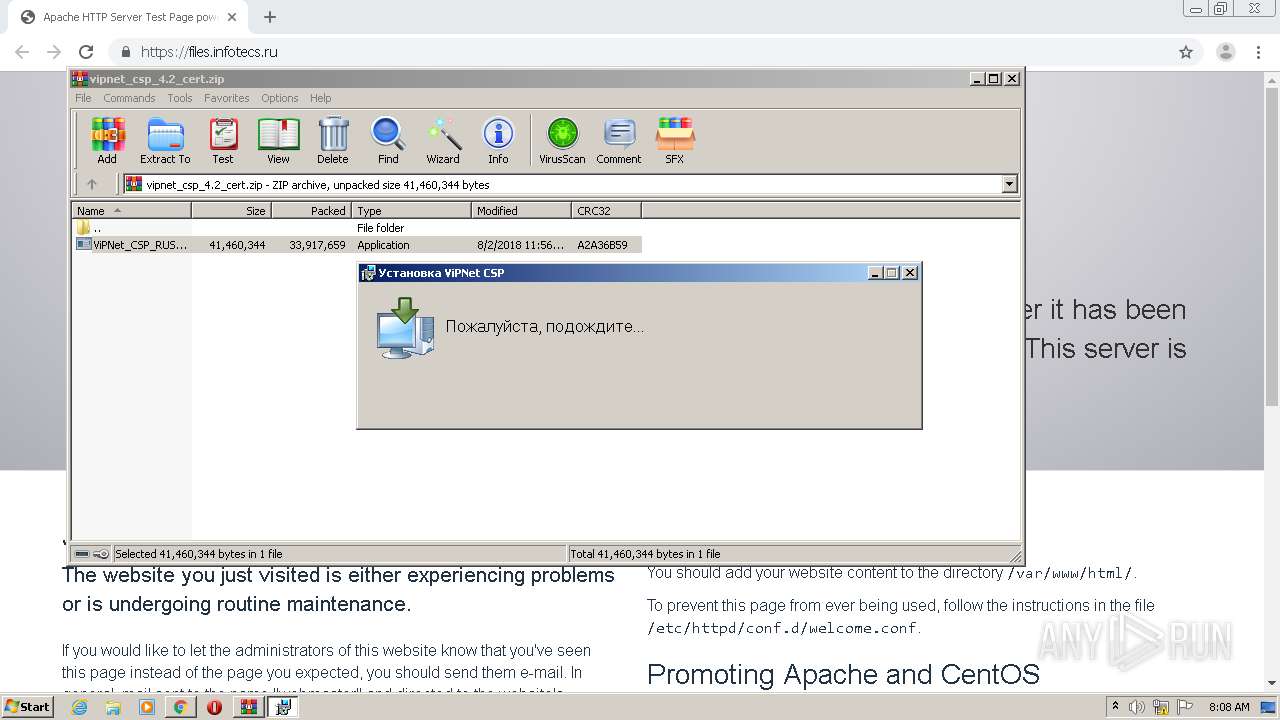
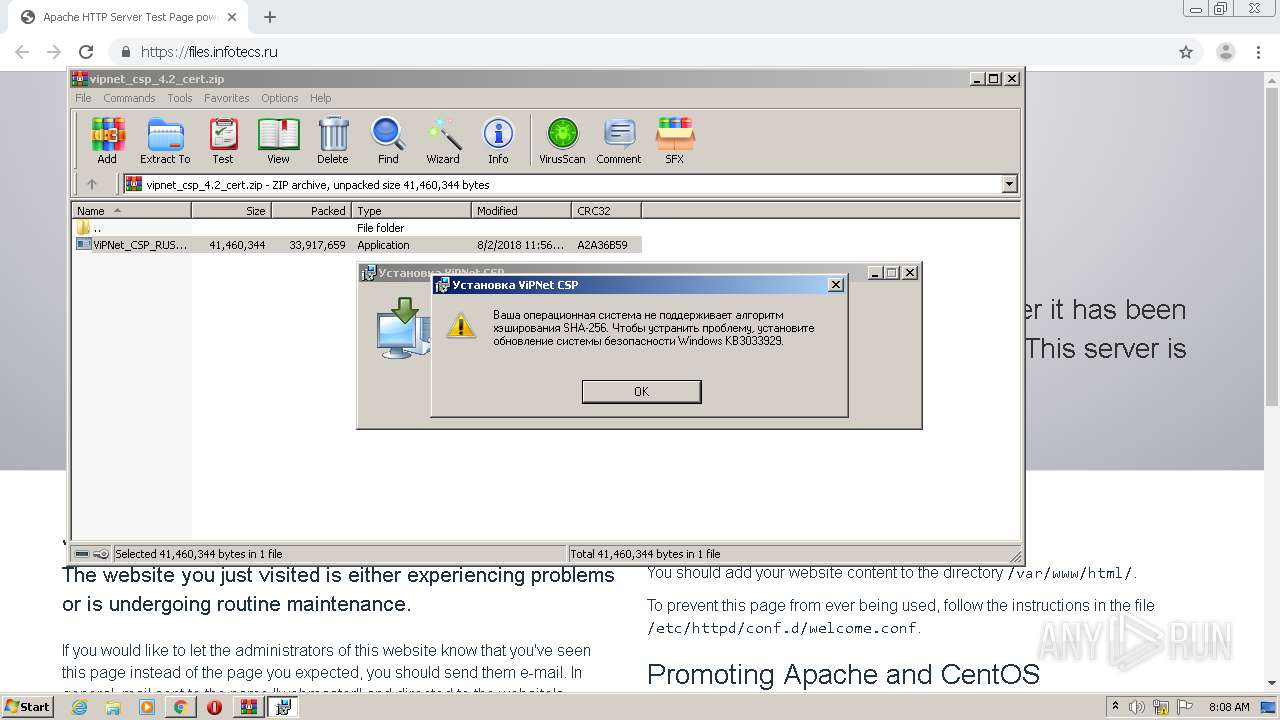
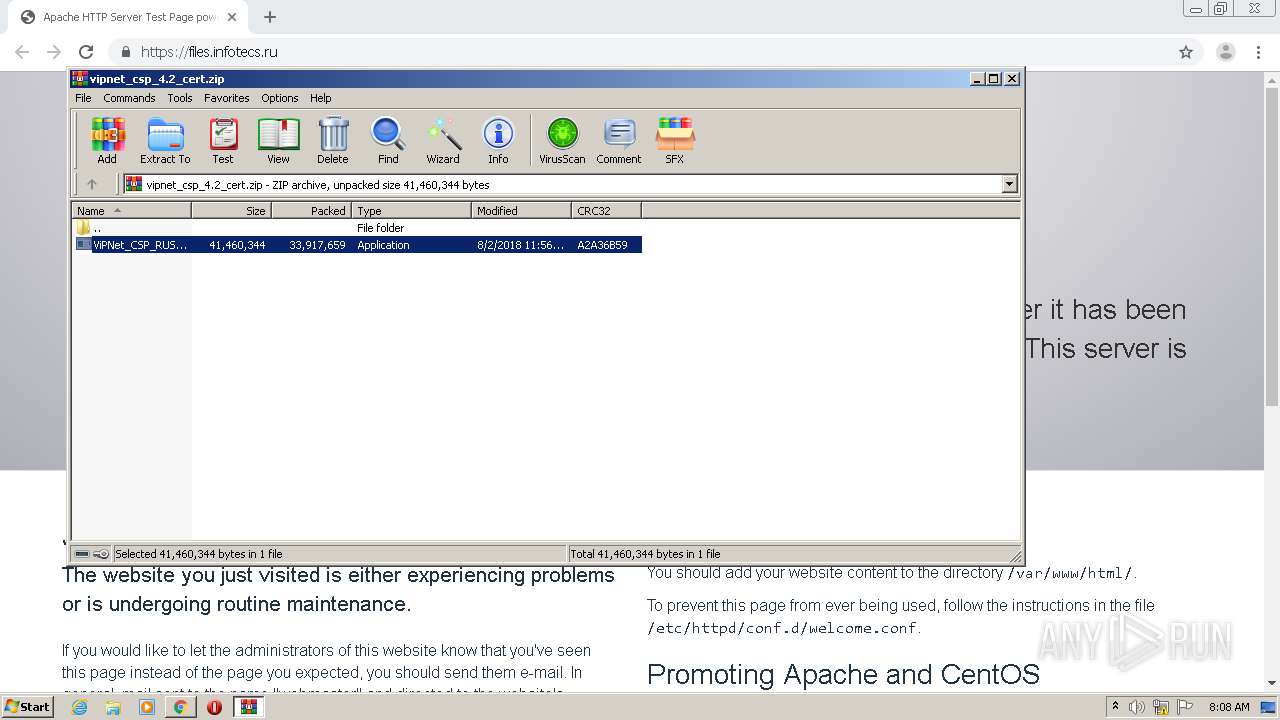
| 656 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa876.23072\ViPNet_CSP_RUS_4.2.8.51670.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa876.23072\ViPNet_CSP_RUS_4.2.8.51670.exe | WinRAR.exe | ||||||||||||
User: admin Company: InfoTeCS Integrity Level: HIGH Description: ViPNet setup Exit code: 3221225547 Version: 4.2.8.51670 Modules
| |||||||||||||||
| 700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,9547617406017294490,14709065289480501797,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4576728018287179777 --mojo-platform-channel-handle=2012 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 876 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\vipnet_csp_4.2_cert.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 972 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa876.23072\ViPNet_CSP_RUS_4.2.8.51670.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa876.23072\ViPNet_CSP_RUS_4.2.8.51670.exe | — | WinRAR.exe | |||||||||||
User: admin Company: InfoTeCS Integrity Level: MEDIUM Description: ViPNet setup Exit code: 3221226540 Version: 4.2.8.51670 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,9547617406017294490,14709065289480501797,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15755981235237750314 --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,9547617406017294490,14709065289480501797,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17152024546174676220 --mojo-platform-channel-handle=1272 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9547617406017294490,14709065289480501797,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11197242167822699975 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://files.infotecs.ru/_dl/sess/vipnet_csp/full/43dfbe6a1dc844143444ad0f3e278c0f/vipnet_csp_4.2_cert.zip" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,9547617406017294490,14709065289480501797,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13284975256692064789 --mojo-platform-channel-handle=3068 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 716
Read events
1 589
Write events
123
Delete events
4
Modification events
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2400-13242726395594632 |
Value: 259 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
4
Suspicious files
127
Text files
257
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cf7b36ee-c804-4e05-9377-2845de056e53.tmp | — | |
MD5:— | SHA256:— | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF157c00.TMP | text | |
MD5:— | SHA256:— | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF157df4.TMP | — | |
MD5:— | SHA256:— | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
53
DNS requests
30
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2636 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2636 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
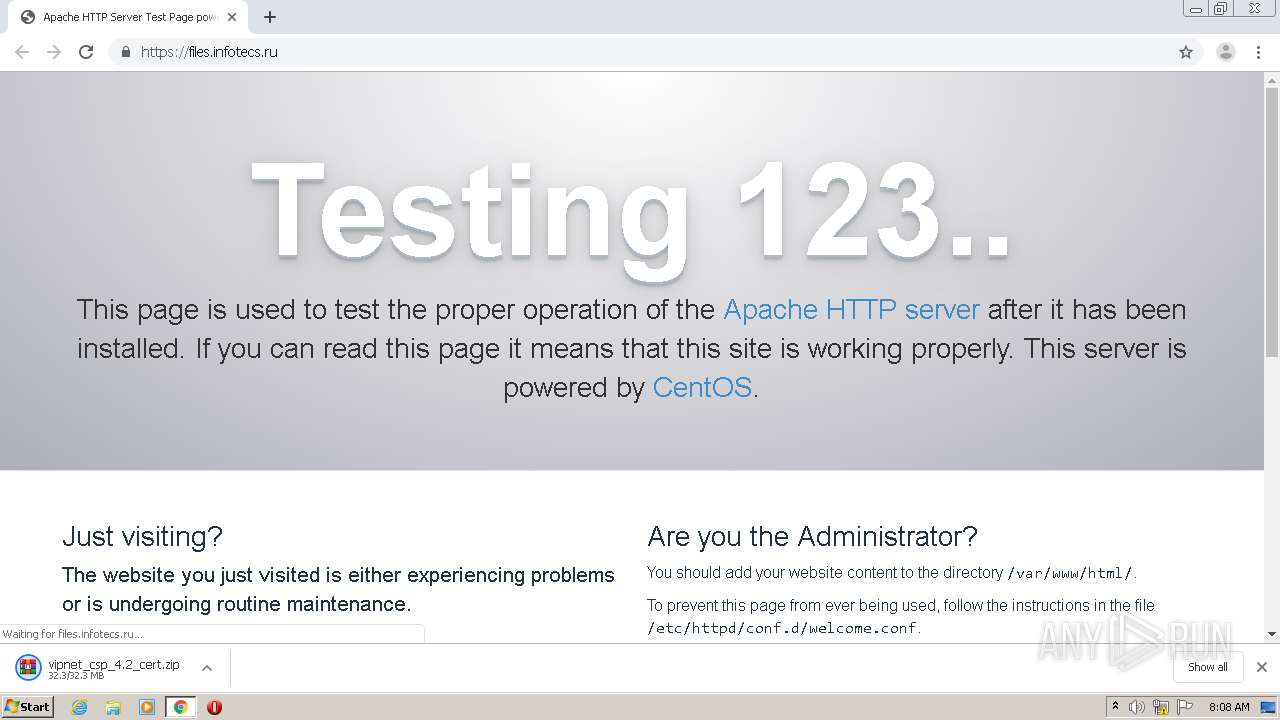
2636 | chrome.exe | 89.108.121.3:443 | files.infotecs.ru | Domain names registrar REG.RU, Ltd | RU | unknown |
2636 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
2636 | chrome.exe | 172.217.22.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
— | — | 216.58.210.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
2636 | chrome.exe | 216.58.207.46:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2636 | chrome.exe | 172.217.23.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2636 | chrome.exe | 77.88.21.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
files.infotecs.ru |
| unknown |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.google.fr |
| whitelisted |