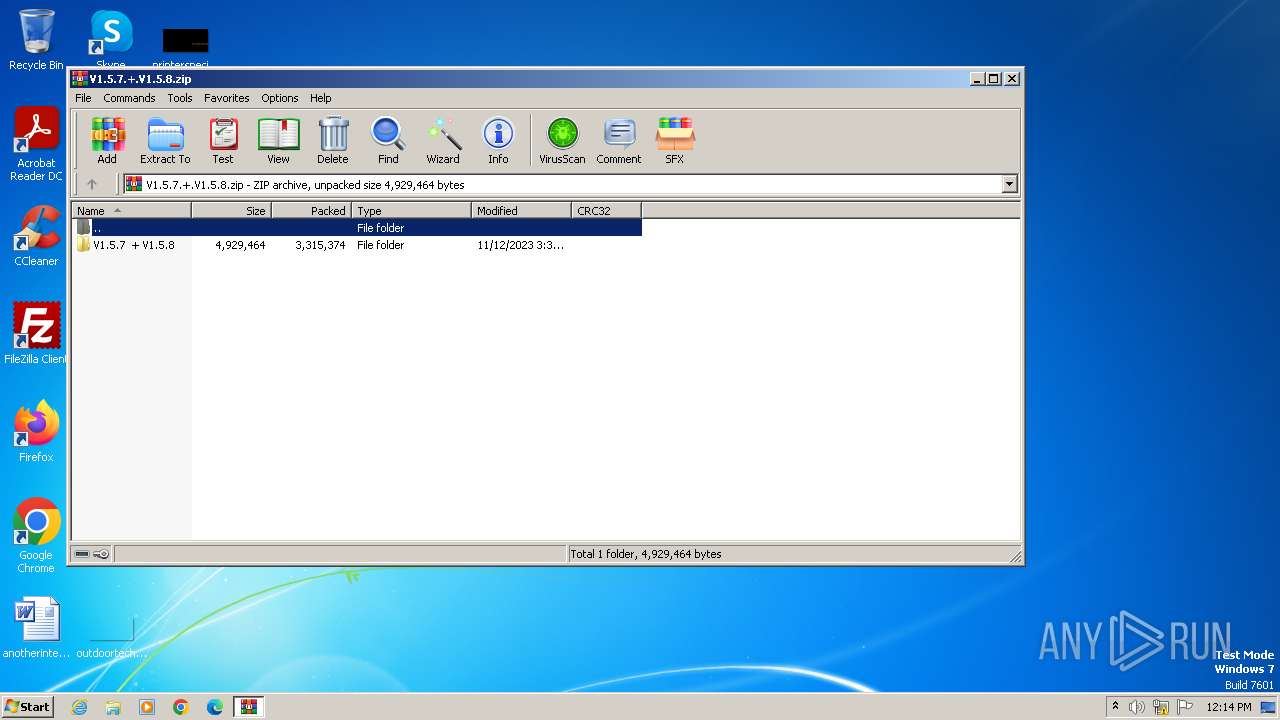
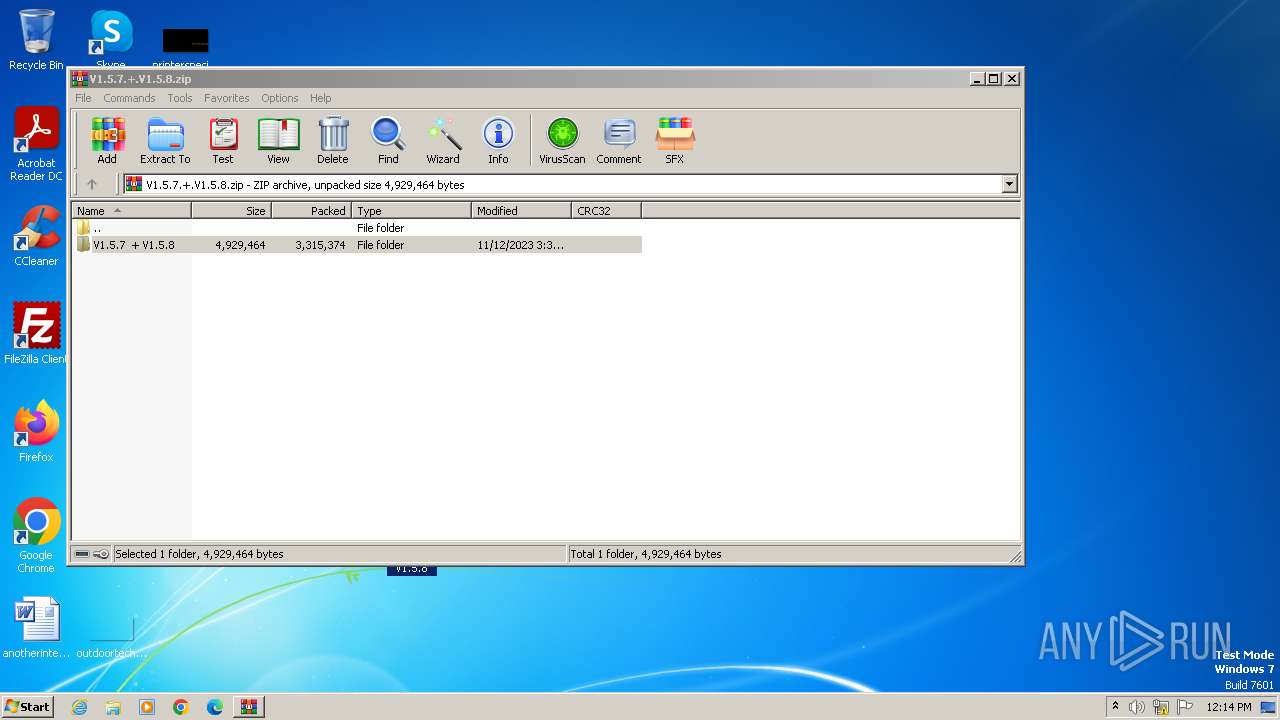
| File name: | V1.5.7.+.V1.5.8.zip |
| Full analysis: | https://app.any.run/tasks/773e3a84-87d8-4a3c-86b7-c1b91c28027f |
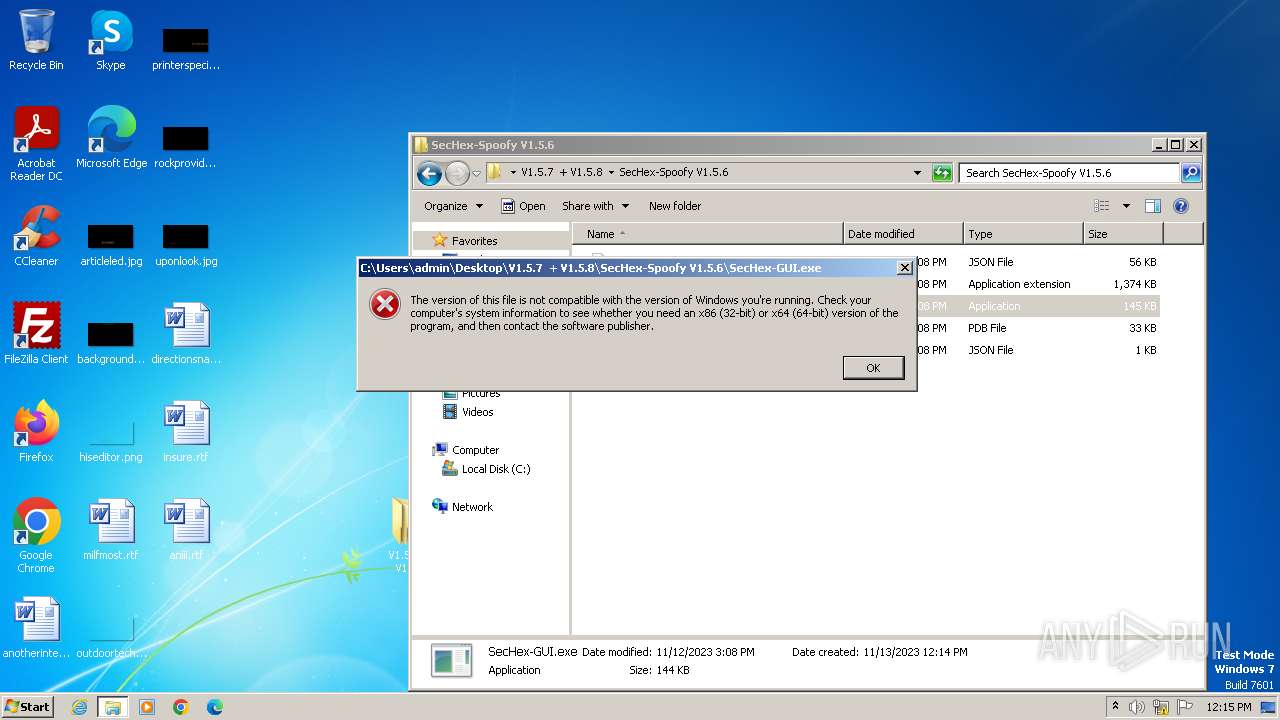
| Verdict: | Malicious activity |
| Analysis date: | November 13, 2023, 12:14:07 |
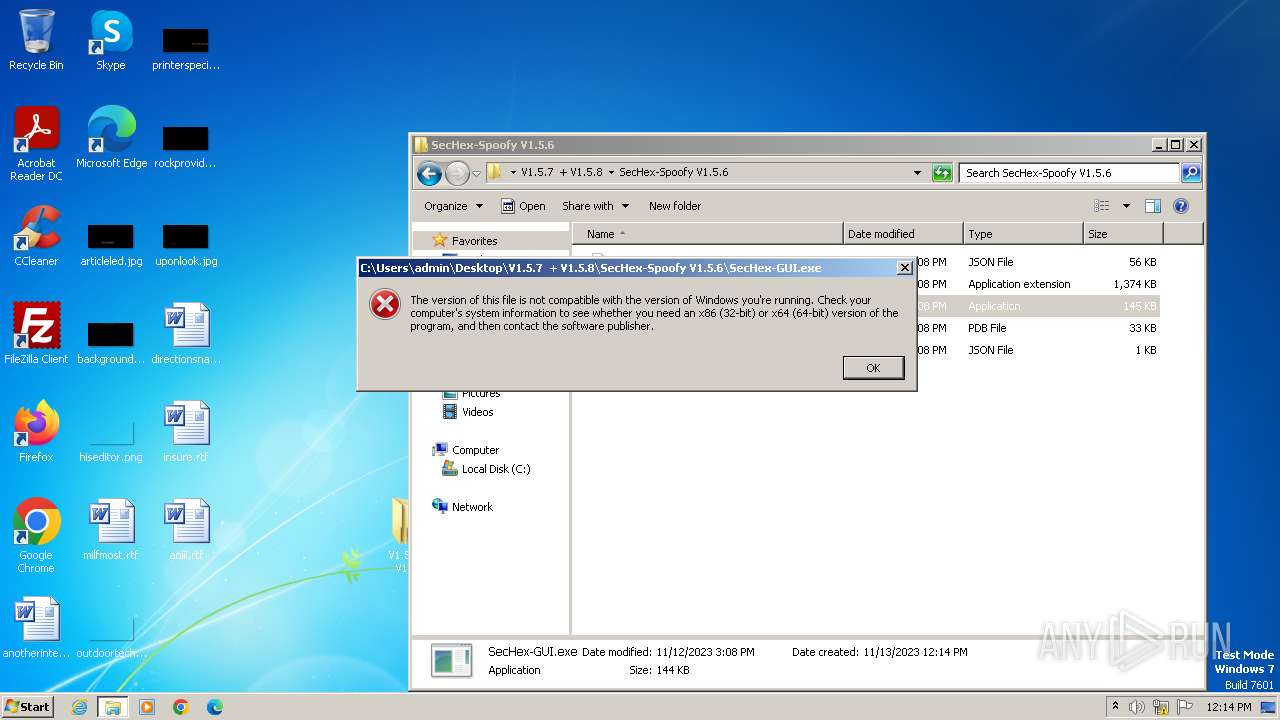
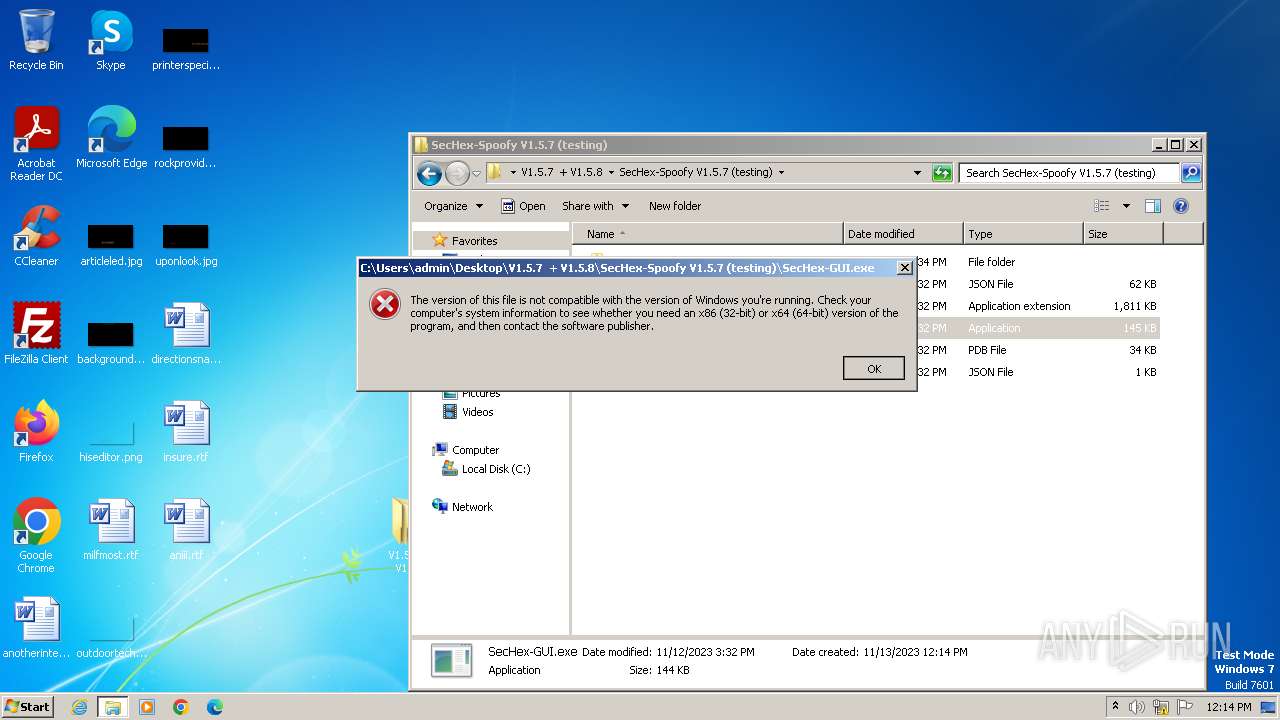
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 350F7A333F78A4F8080D5EA05E6CDF1A |
| SHA1: | DBC1C327C13147BF20BA4FE9AD915C208BBDED8D |
| SHA256: | F8E1404B46C51AB281F124FFECA7984231D2068E7F09A5EF28149DB4FC229B8A |
| SSDEEP: | 98304:AoIzQRvnws9JTeDQ72Y3Hlb4nQiqzI1k2vgvTb0qFHc31+PQPxVtBDagA8faKLW2:bB0Br |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 3448)
INFO
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:11:12 16:34:18 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
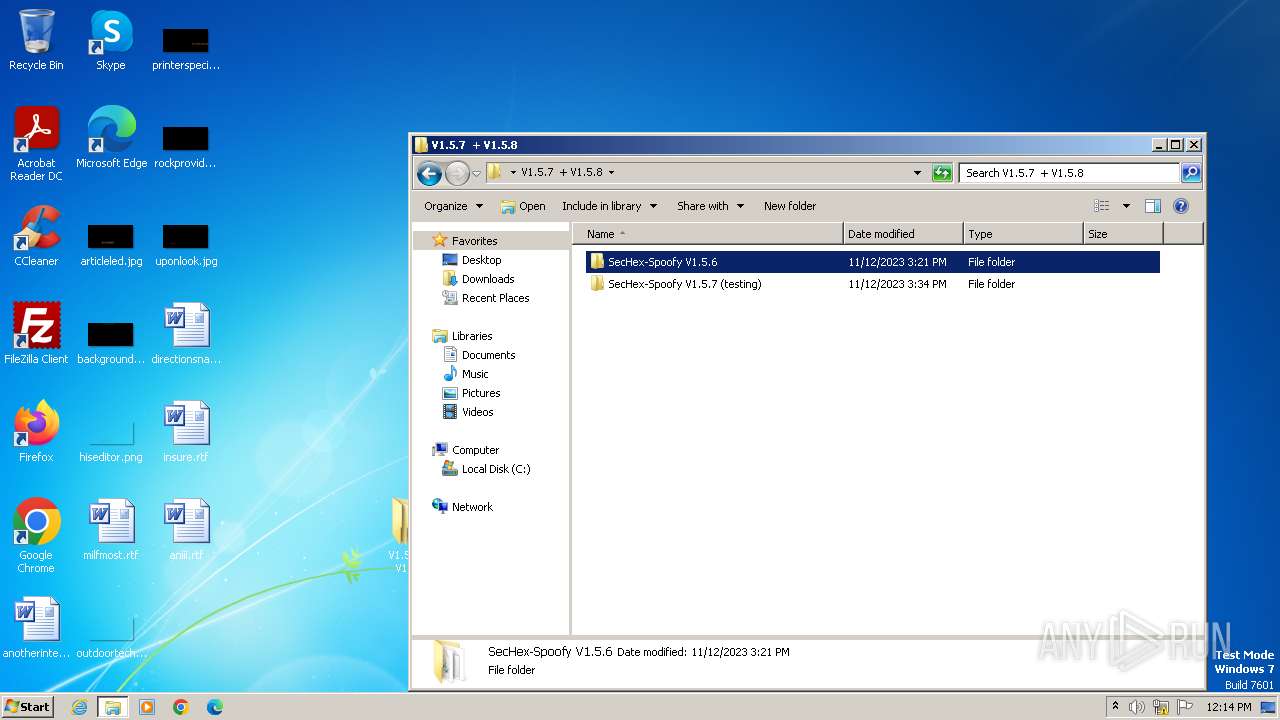
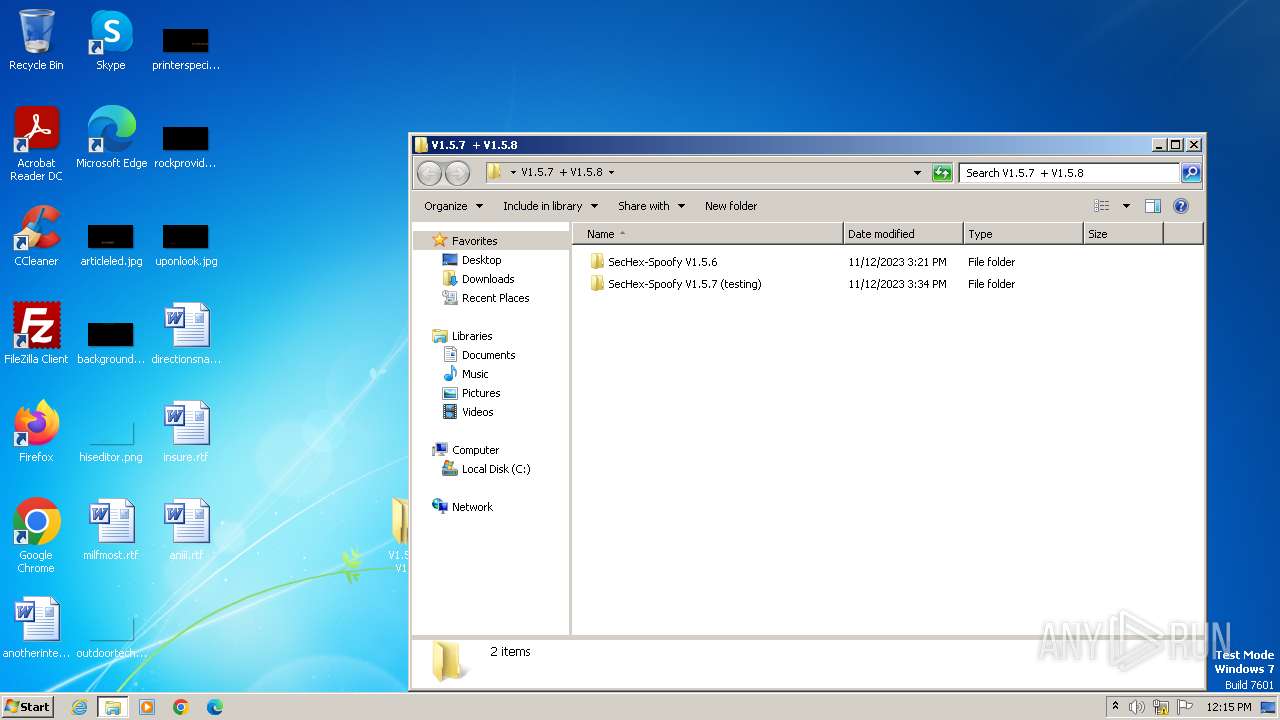
| ZipFileName: | V1.5.7 + V1.5.8/ |
Total processes
42
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
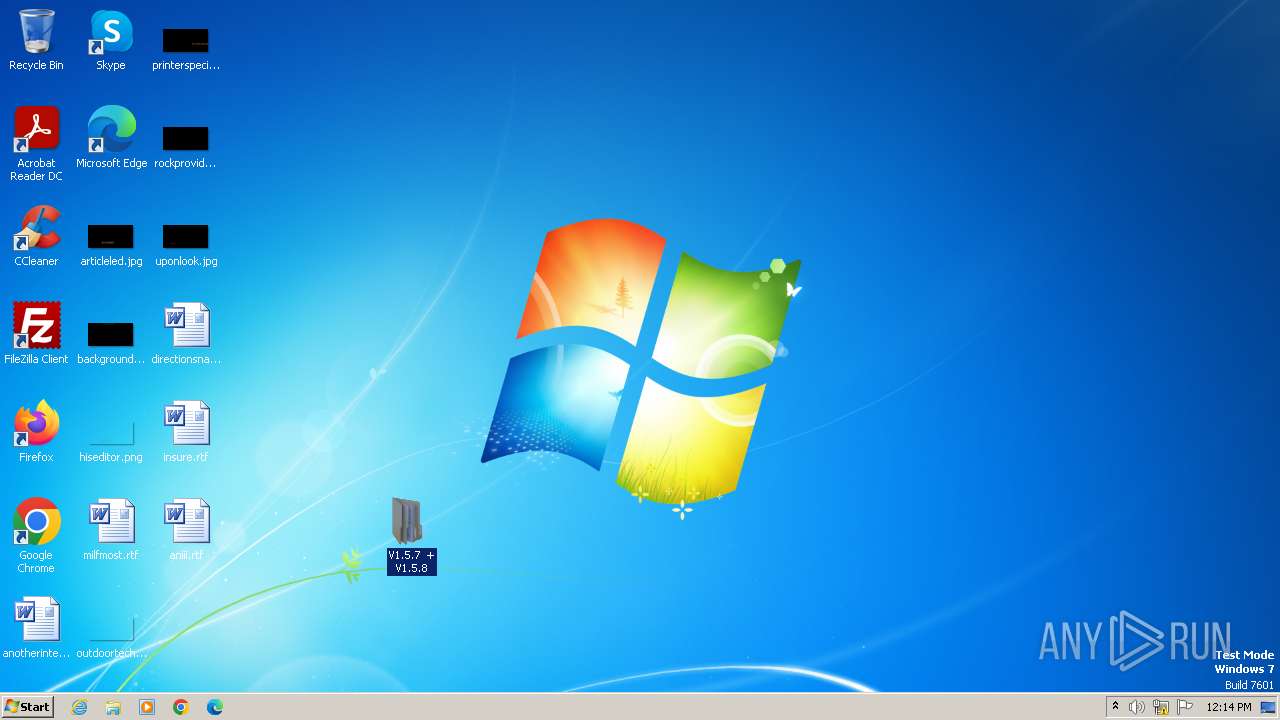
| 3448 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\V1.5.7.+.V1.5.8.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
928
Read events
909
Write events
19
Delete events
0
Modification events
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
9
Suspicious files
6
Text files
0
Unknown types
0
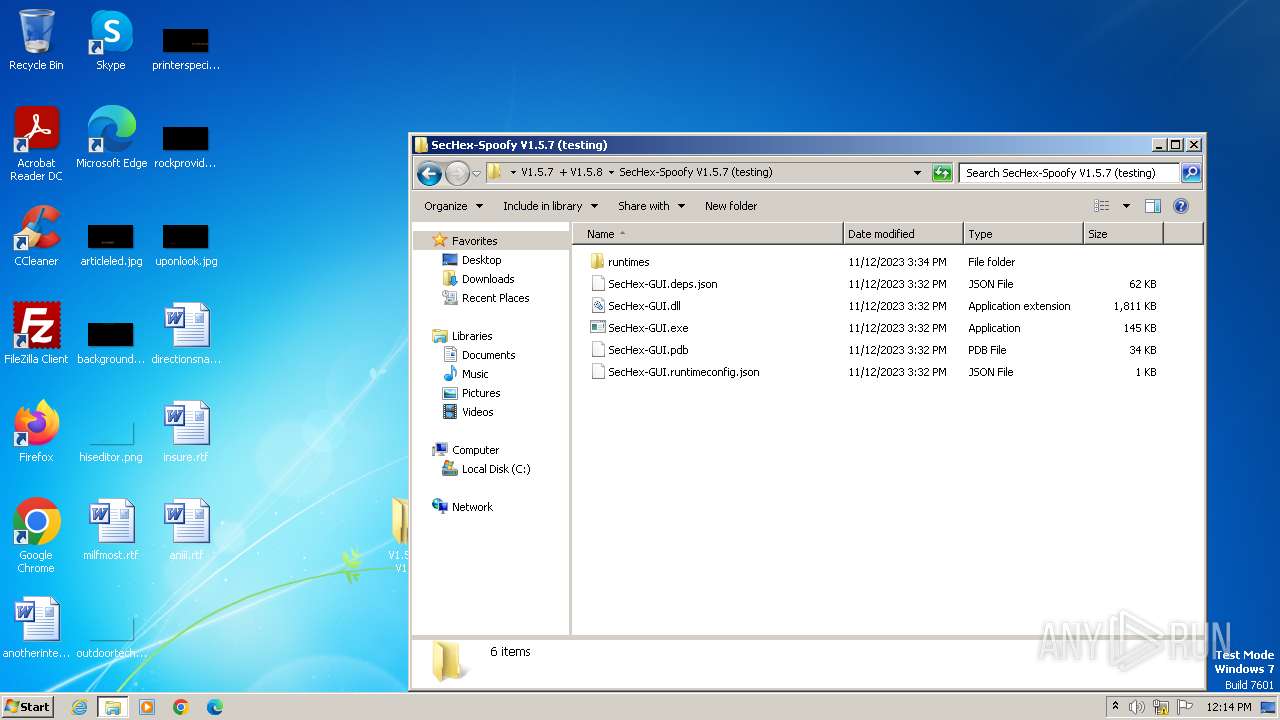
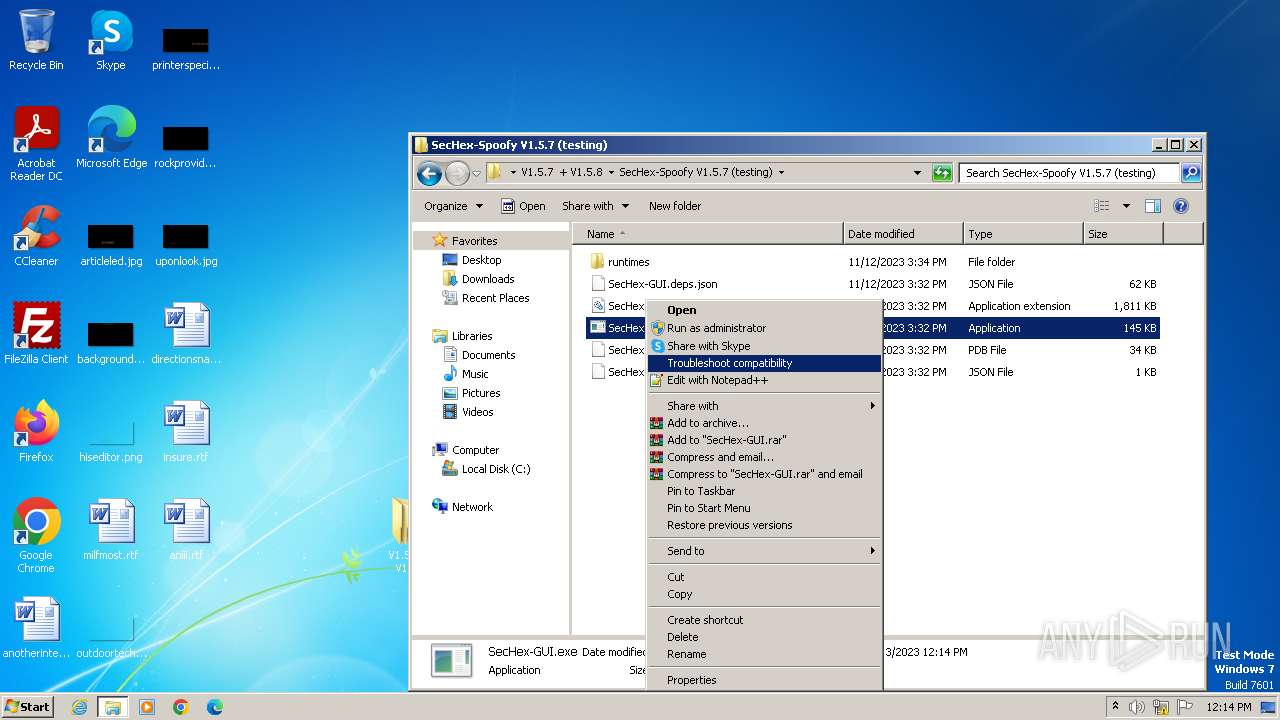
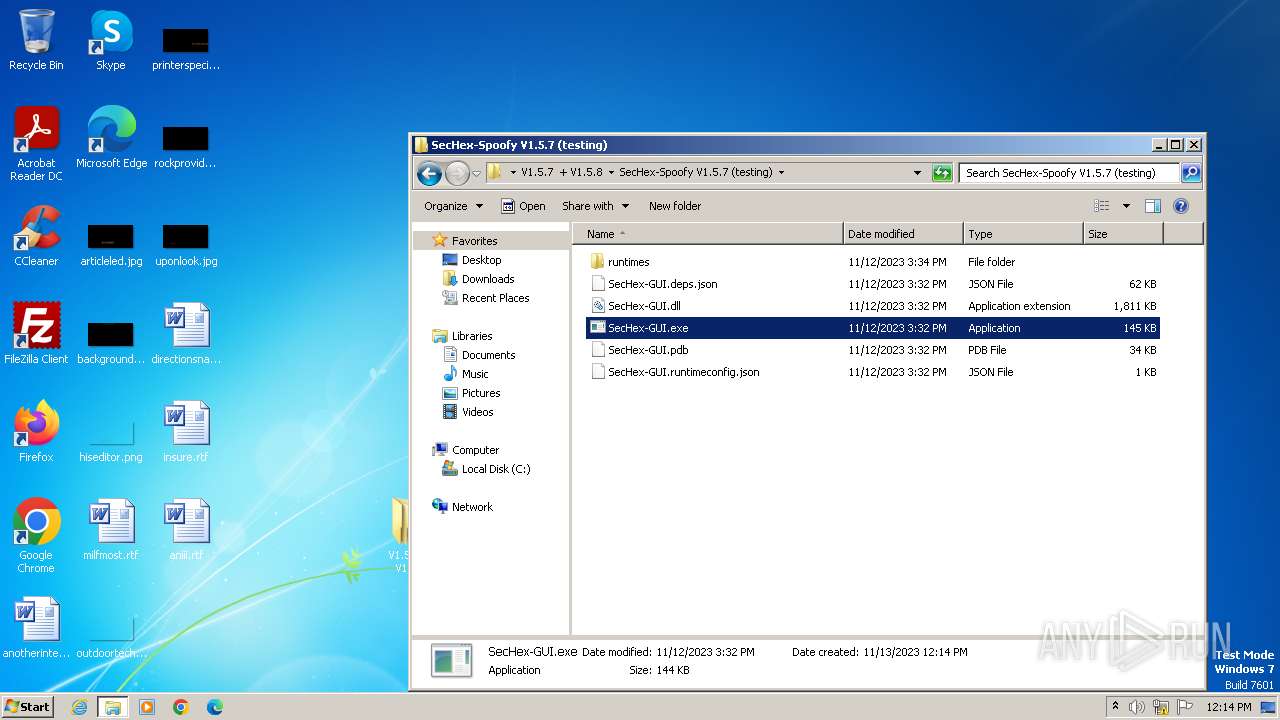
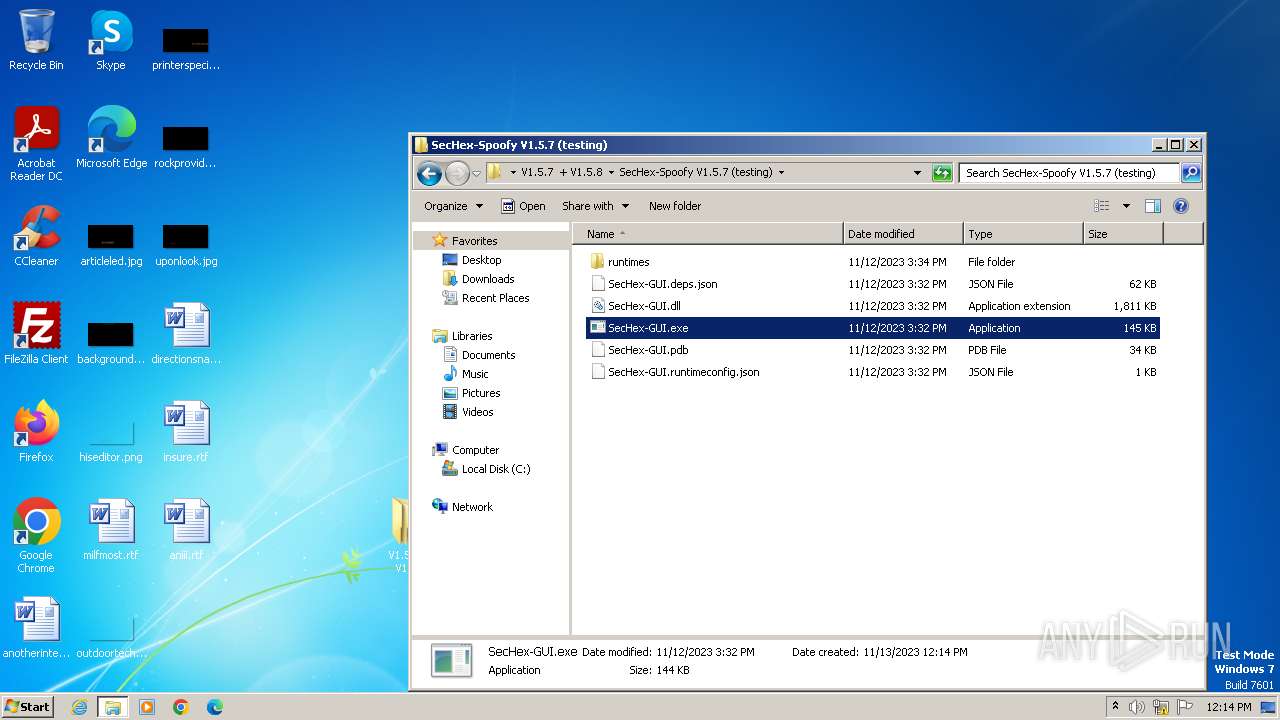
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
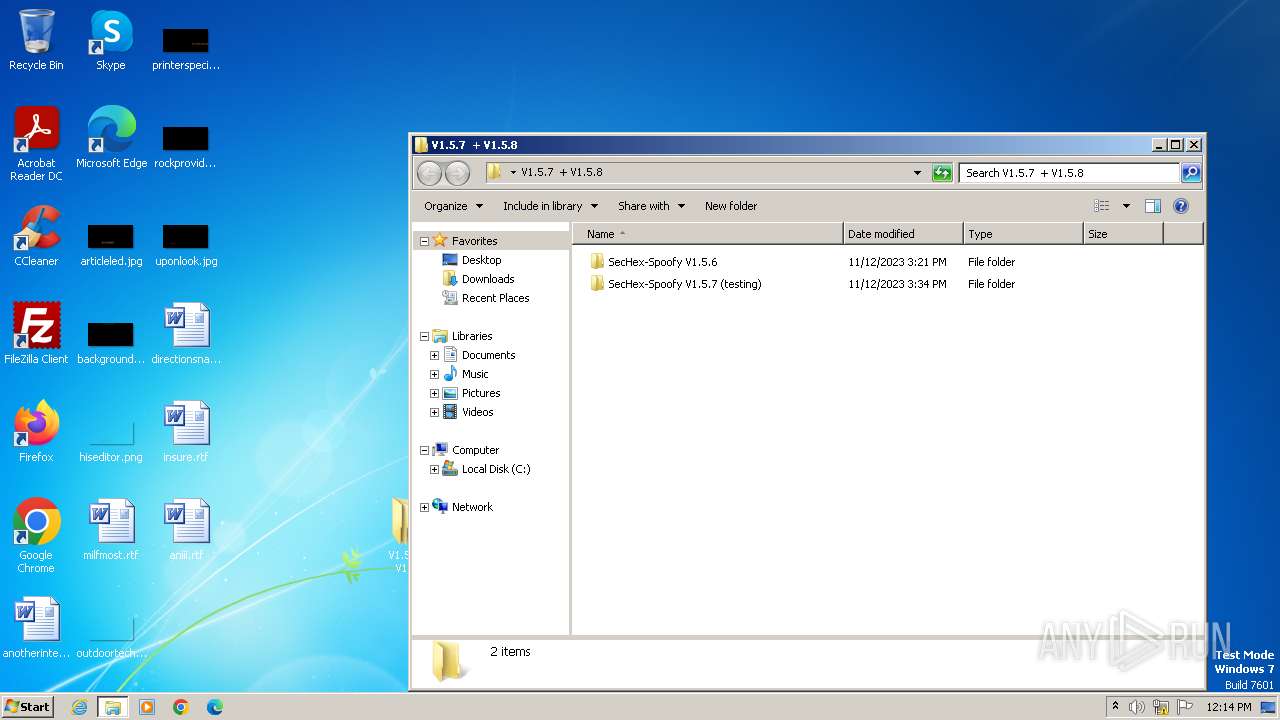
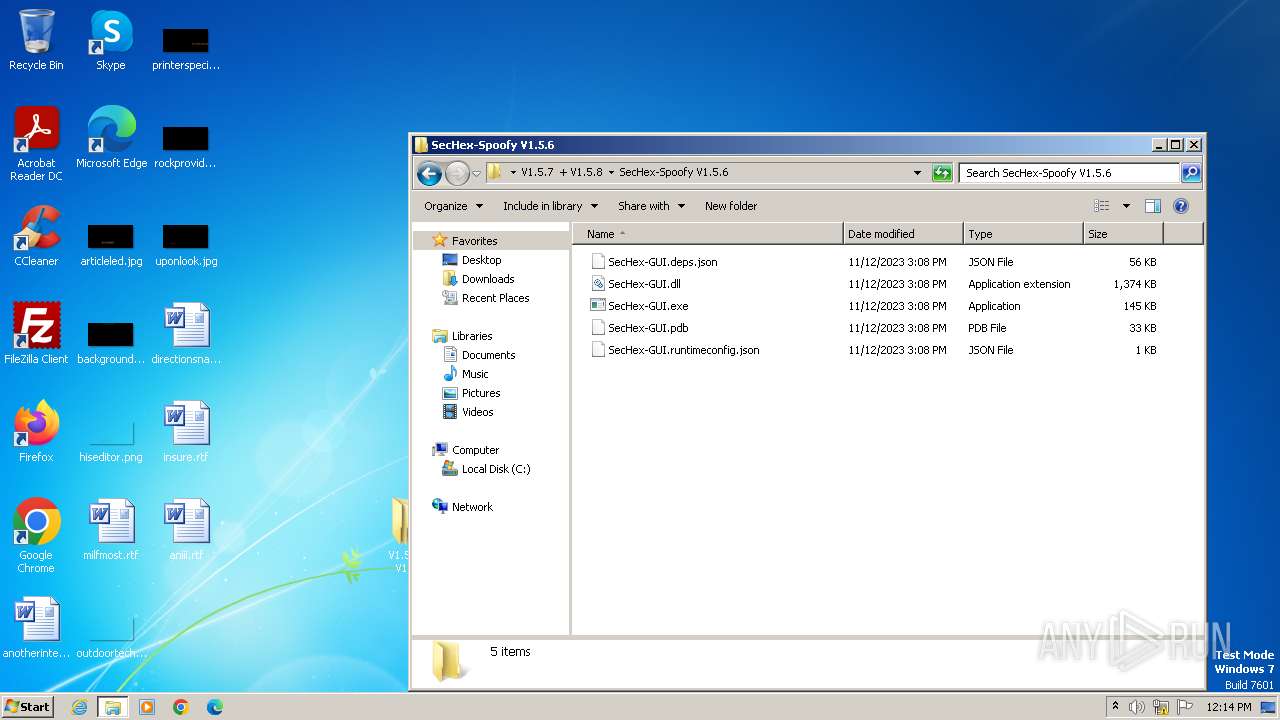
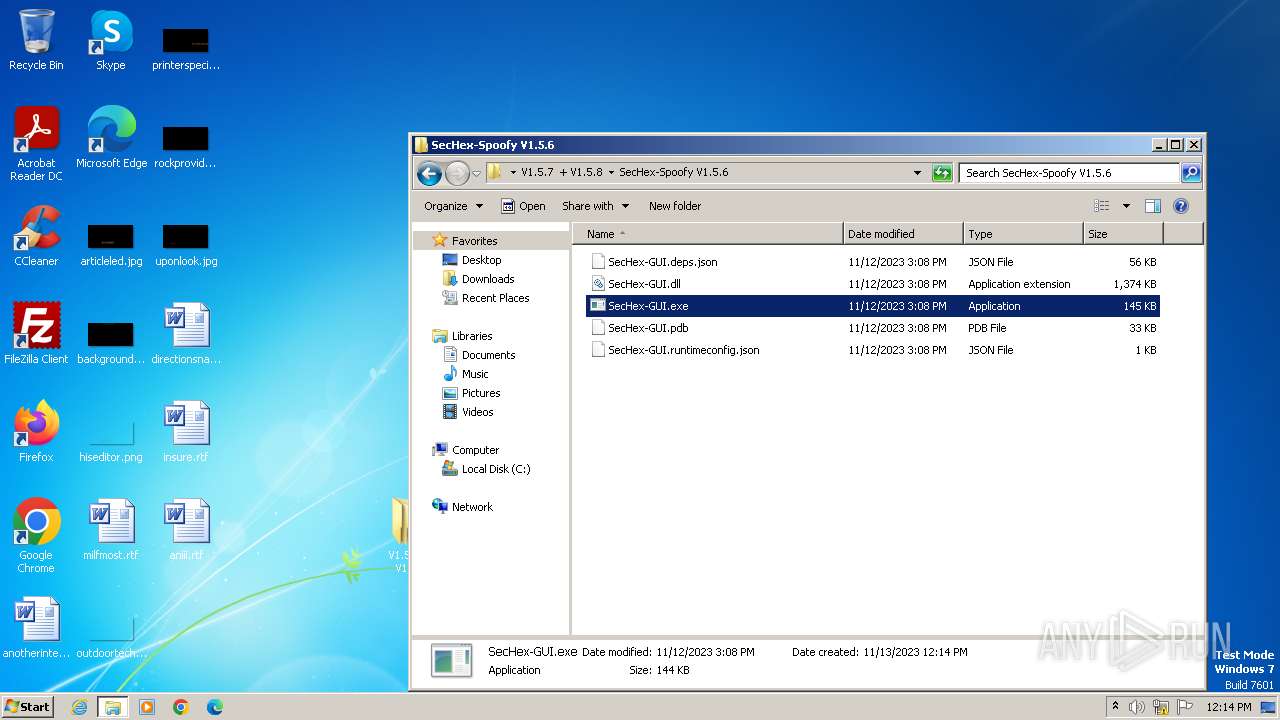
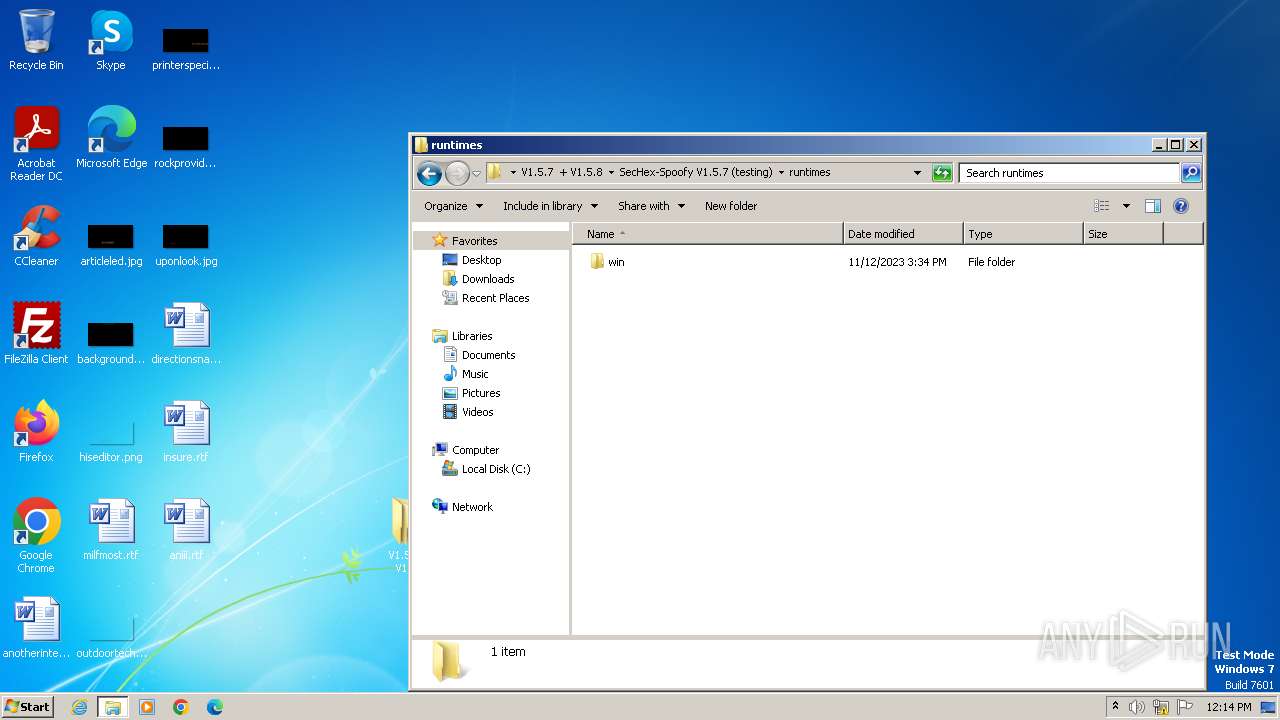
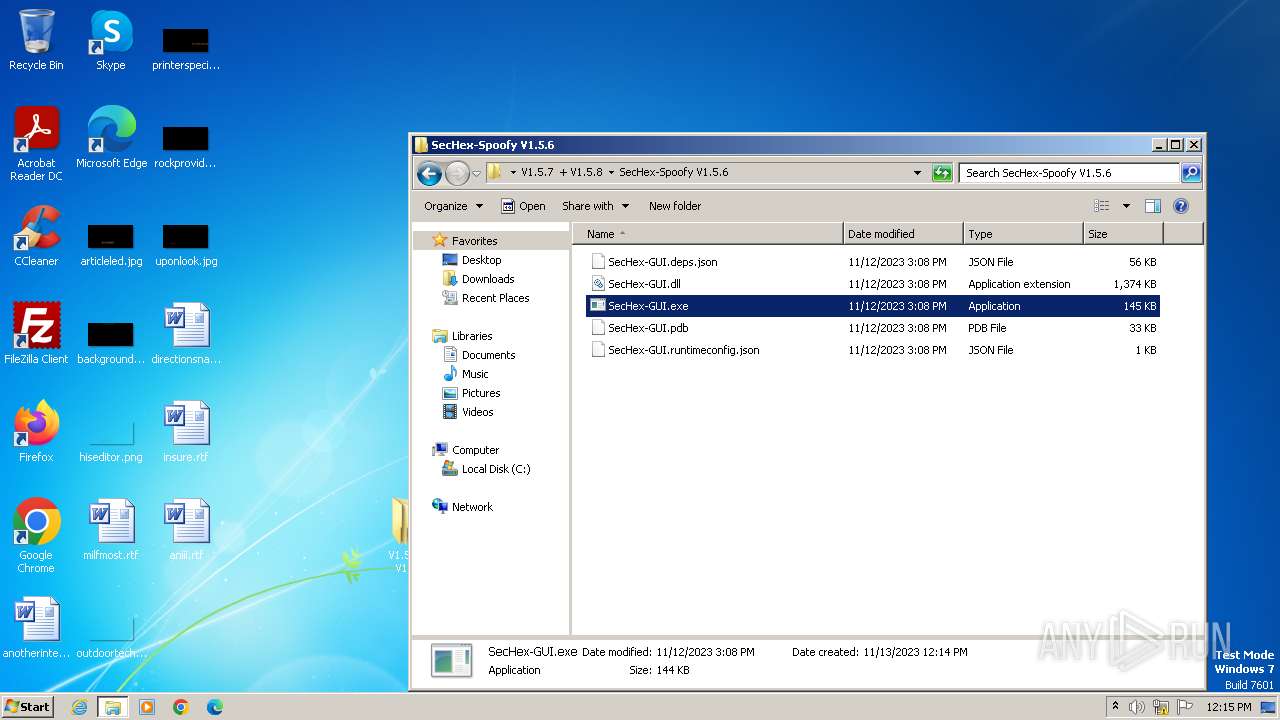
| 3448 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3448.14590\V1.5.7 + V1.5.8\SecHex-Spoofy V1.5.6\SecHex-GUI.dll | executable | |
MD5:AD714EE48D2E829C5012C65DE6166C05 | SHA256:7D32D13D123871650794A1E172ADC70BC8DAFBDB762F49D889F813844D532B20 | |||
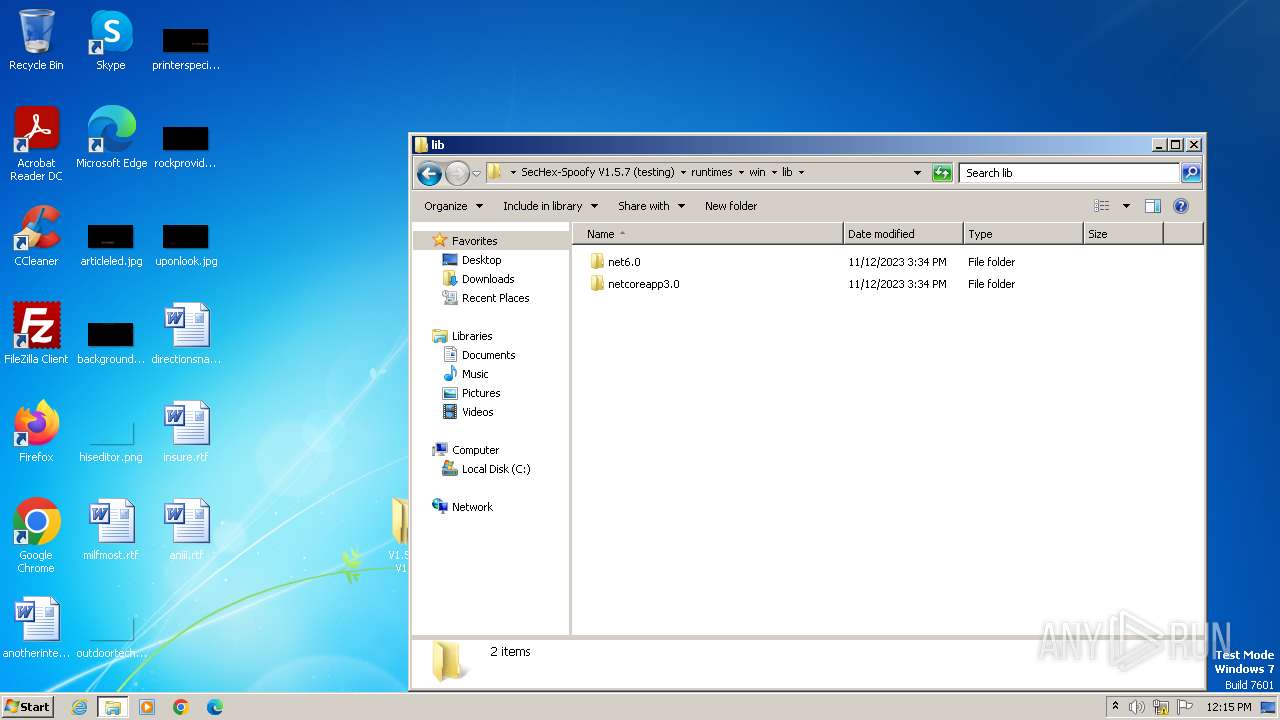
| 3448 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3448.14590\V1.5.7 + V1.5.8\SecHex-Spoofy V1.5.7 (testing)\runtimes\win\lib\net6.0\System.Diagnostics.EventLog.Messages.dll | executable | |
MD5:286F0A973CF2332FBDED81CF541FFF06 | SHA256:3A2EA792755BBE4674F349D7870AEB917494AC39F96A9E5D9625D4AC68DC3EC5 | |||
| 3448 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3448.14590\V1.5.7 + V1.5.8\SecHex-Spoofy V1.5.7 (testing)\runtimes\win\lib\net6.0\System.Diagnostics.EventLog.dll | executable | |
MD5:62C63C04C6083330D020CF855C85002C | SHA256:FAC816CA0BD5D9C4A17693B37575A5ABA901D993133B61D7344B597472FA0C26 | |||
| 3448 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3448.14590\V1.5.7 + V1.5.8\SecHex-Spoofy V1.5.7 (testing)\runtimes\win\lib\net6.0\System.ServiceProcess.ServiceController.dll | executable | |
MD5:1C710EF8481E54352A4E1F66A8F7AD8C | SHA256:D11B97C114101961BCC7ACB0BB17E536708593C0321B6107942FBA20CB430C65 | |||
| 3448 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3448.14590\V1.5.7 + V1.5.8\SecHex-Spoofy V1.5.6\SecHex-GUI.exe | executable | |
MD5:A3A73BB0B21C4C4C0771D4FDA37AD34A | SHA256:9C04CA4639650F2707E817C8852BF8E128AB328FA4EF790ABA96F8EC17AD5316 | |||
| 3448 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3448.14590\V1.5.7 + V1.5.8\SecHex-Spoofy V1.5.6\SecHex-GUI.deps.json | binary | |
MD5:33784D40D169FA2AD9BFA73EDA3EA7EF | SHA256:2FC1A3F36E616CBC3CD8BE04F8BF7ED49F927B69B4DC14E8A21ED65FE262EB08 | |||
| 3448 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3448.14590\V1.5.7 + V1.5.8\SecHex-Spoofy V1.5.7 (testing)\runtimes\win\lib\netcoreapp3.0\System.Runtime.WindowsRuntime.dll | executable | |
MD5:0198A79063C865ED21C95B7400DDD9FC | SHA256:BE26699765F700A29C3928E10F6D1E02A297DFF3BA6EB7AFB6EC41003CB3D665 | |||
| 3448 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3448.14590\V1.5.7 + V1.5.8\SecHex-Spoofy V1.5.6\SecHex-GUI.runtimeconfig.json | binary | |
MD5:D720176A229E9D969B40FABEB0BAF62E | SHA256:321B4E463BBACD6113AA337511BDEBF5E7356E9971744346B28424607C7B483A | |||
| 3448 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3448.14590\V1.5.7 + V1.5.8\SecHex-Spoofy V1.5.7 (testing)\SecHex-GUI.pdb | binary | |
MD5:629565872D2B14CF9AF1EDCF06F3F367 | SHA256:97502B5792ACB1EA7C640560AE7E9A53568C77002D5B10F3B4D4EFCC8EE6B16F | |||
| 3448 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3448.14590\V1.5.7 + V1.5.8\SecHex-Spoofy V1.5.7 (testing)\runtimes\win\lib\netcoreapp3.0\System.Runtime.WindowsRuntime.UI.Xaml.dll | executable | |
MD5:7141C72E54FE9A7ED39EF89814DE67D9 | SHA256:884442E44BCEF27D917E5DE5B69CBD4A297830E0B98B84495C7AB7486FA47332 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |