| File name: | redirect |
| Full analysis: | https://app.any.run/tasks/65688c67-b85c-441c-ac59-e96b5b201410 |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 20:05:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | F22923B6643239F83B158250E787B6FA |
| SHA1: | DF0BDC2252E0D356CC45C954C02110B94A4B890F |
| SHA256: | F8D837D52CA0435FA8F11BE3557BFFCCC840B3F63558C235BD840B8AE8A3BD8F |
| SSDEEP: | 768:bi66kR/VfOJkjPv5KHj5kNGv2ZnRzuK+0F+fXD7pliuIr1dAXk:qkjX50kNGcnRg0FMU |
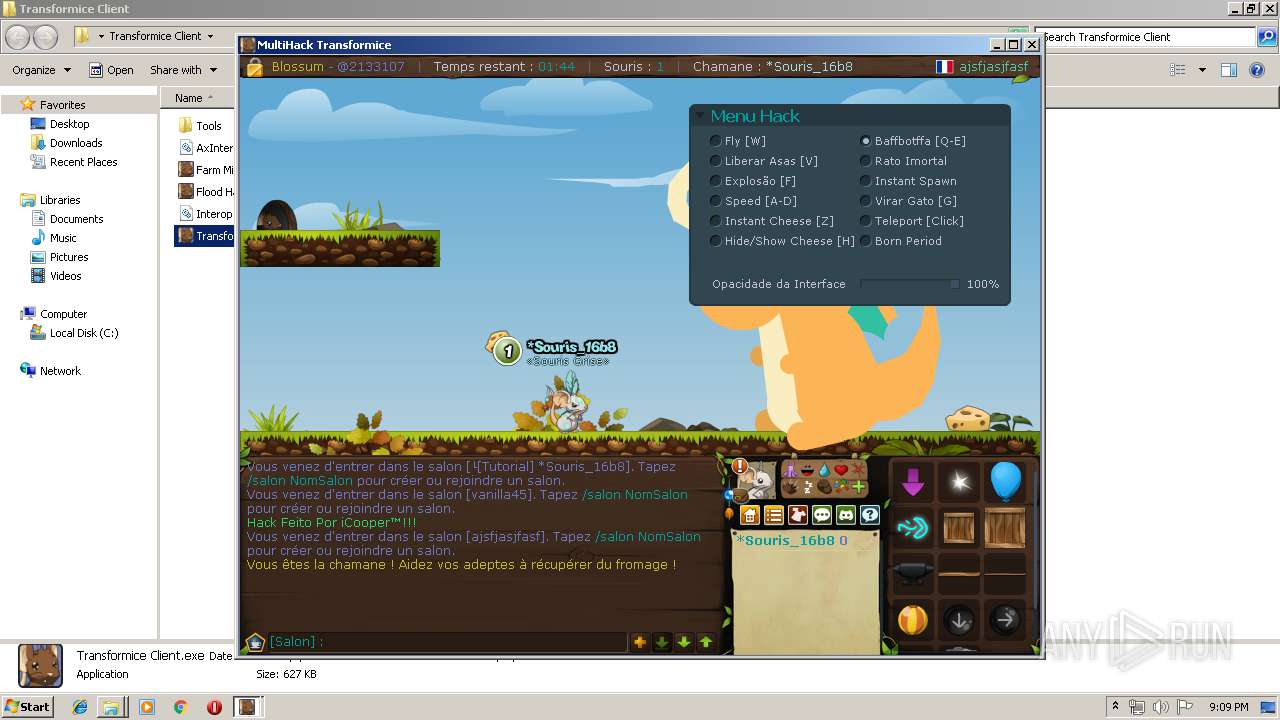
MALICIOUS
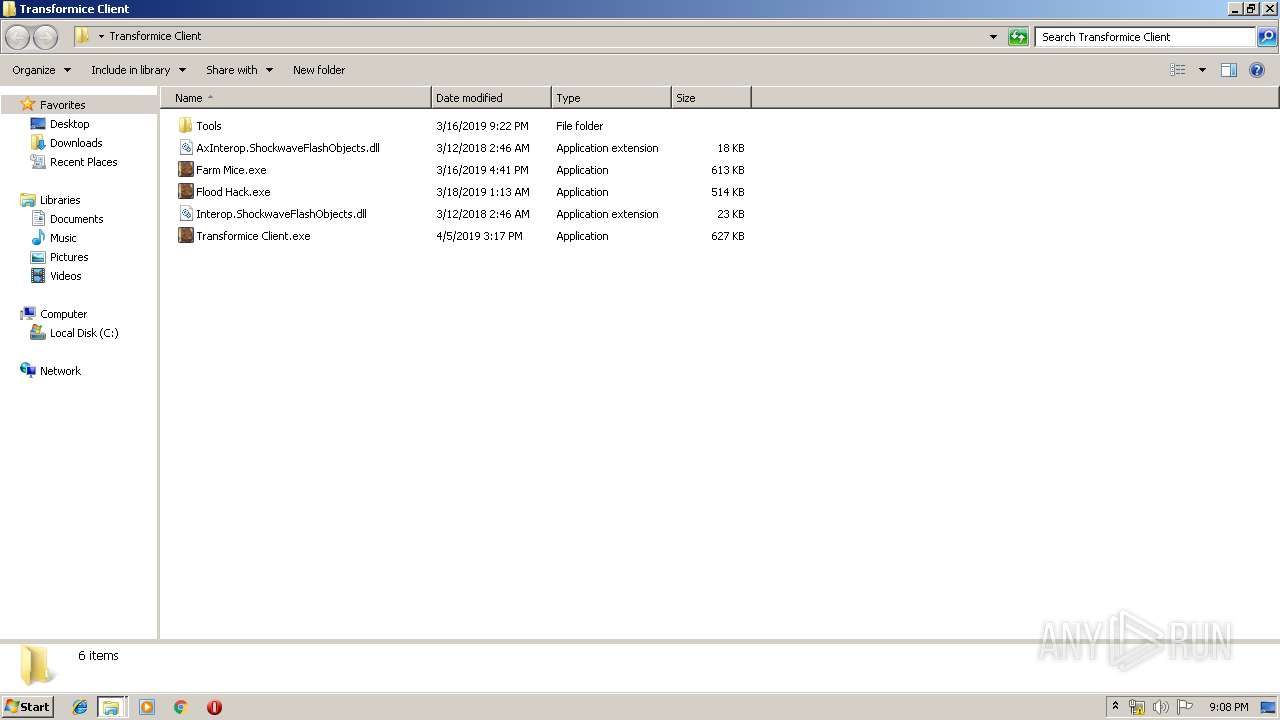
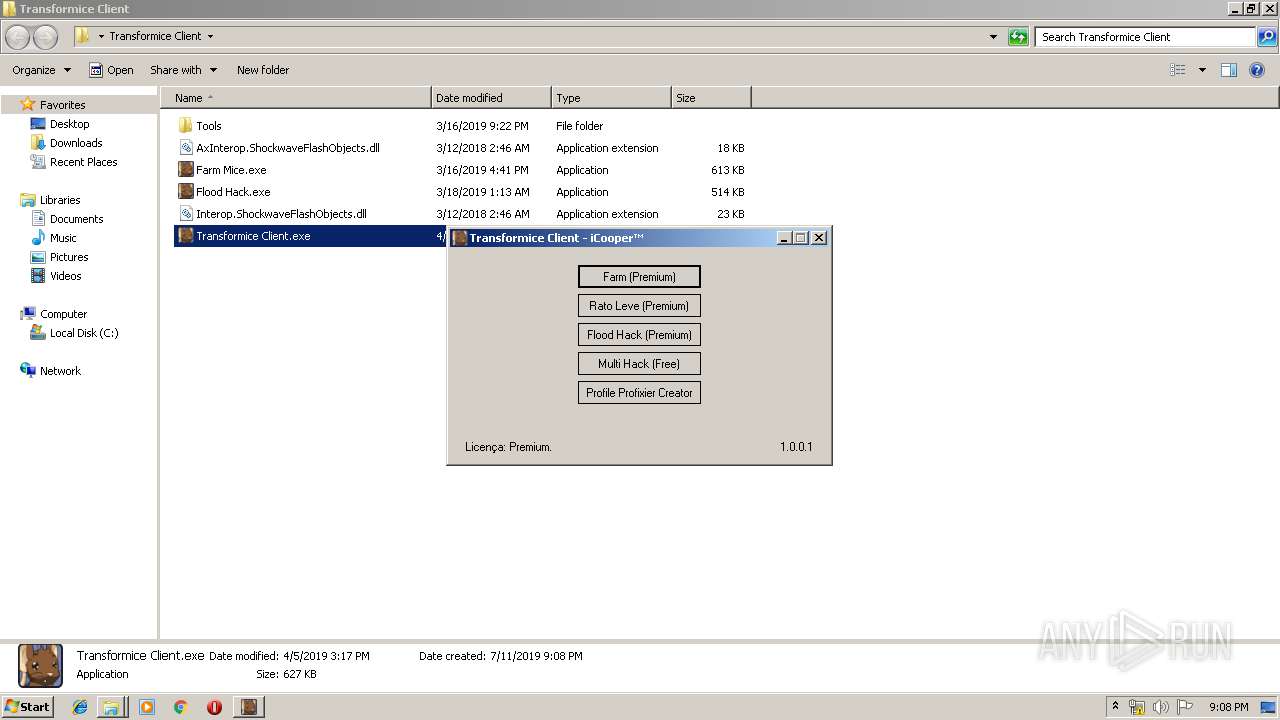
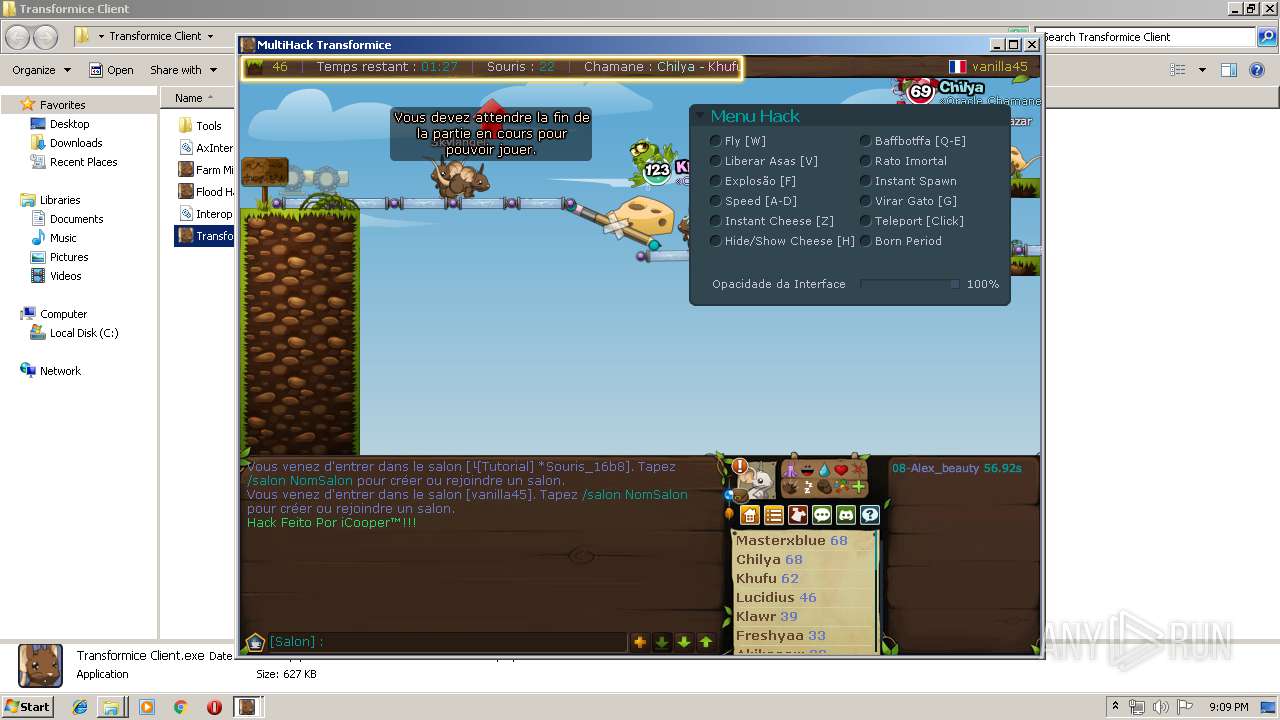
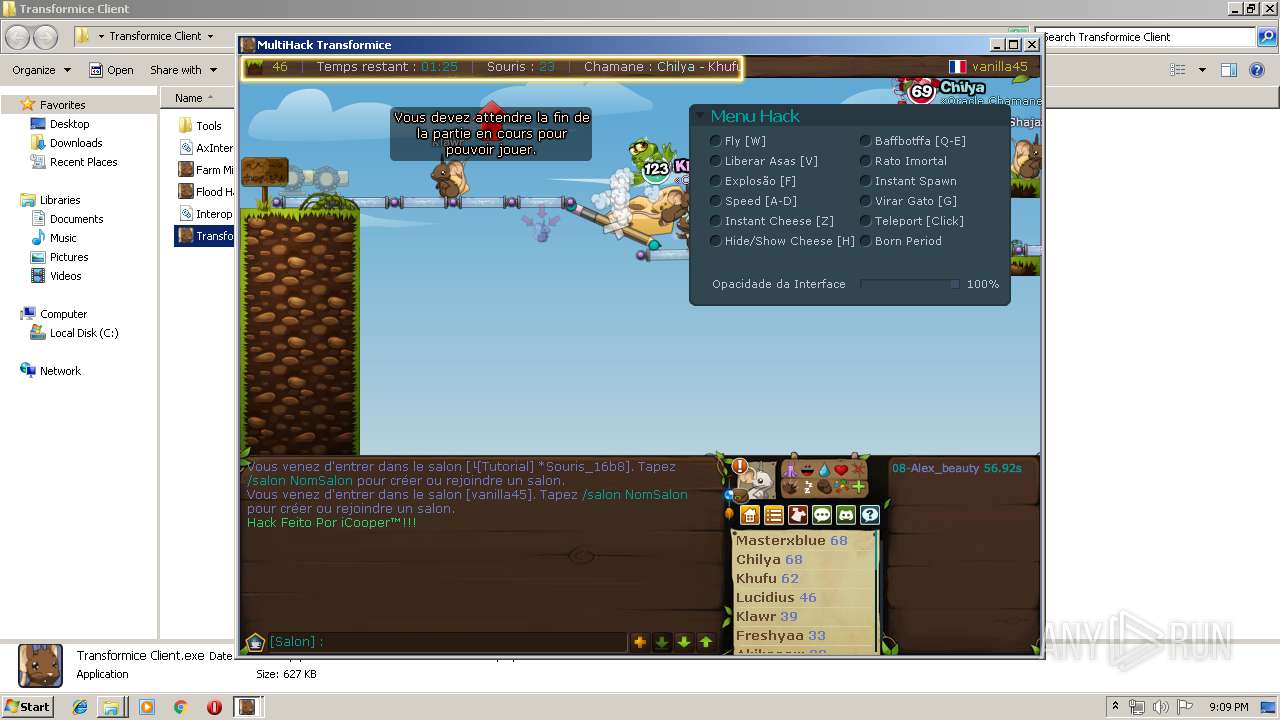
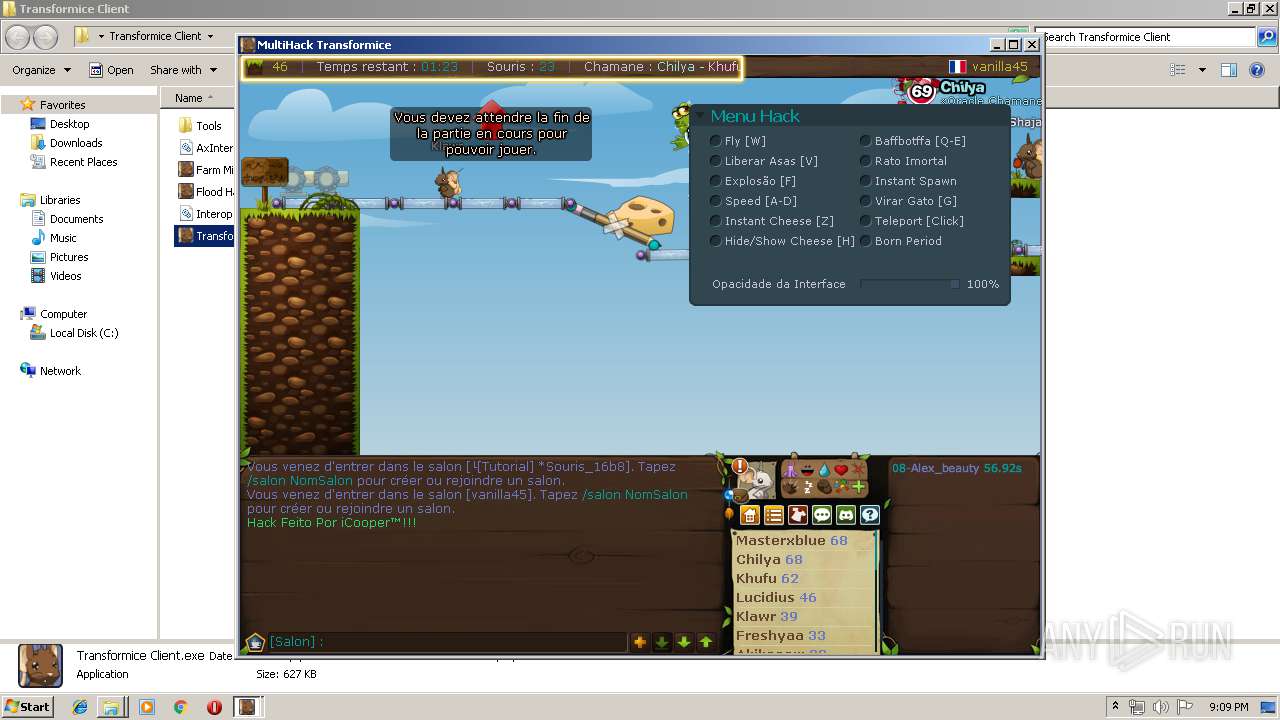
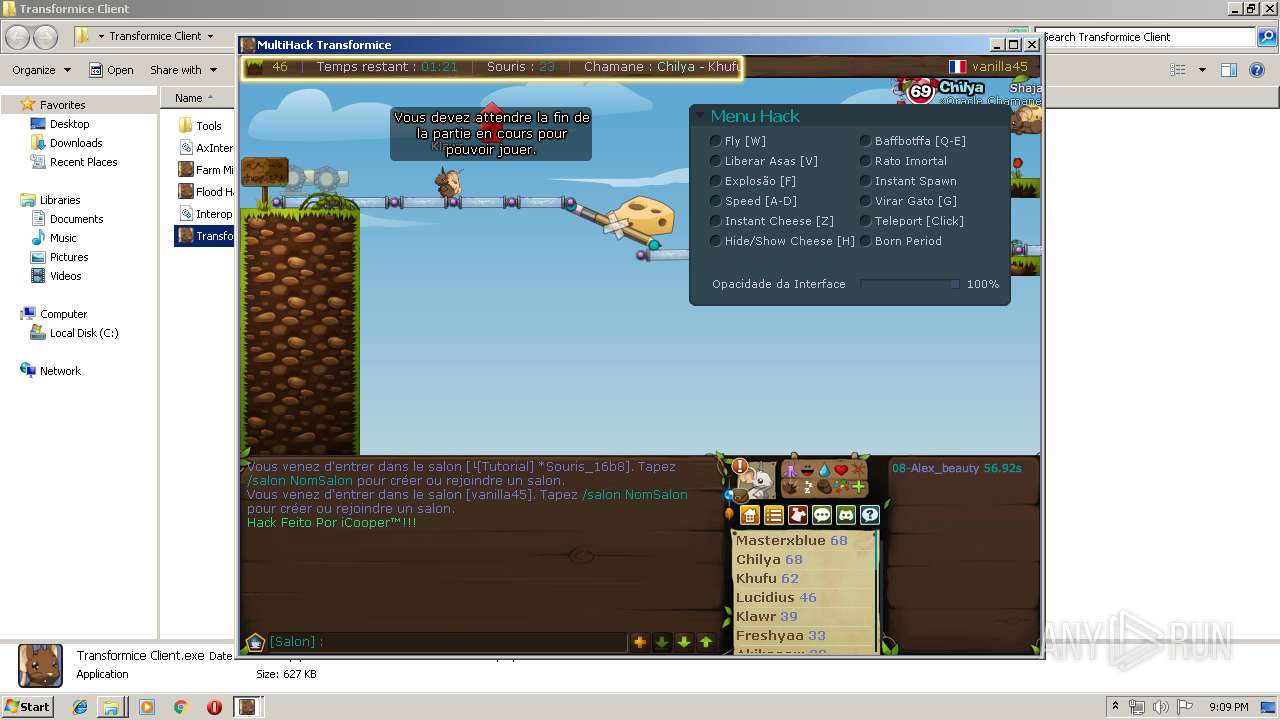
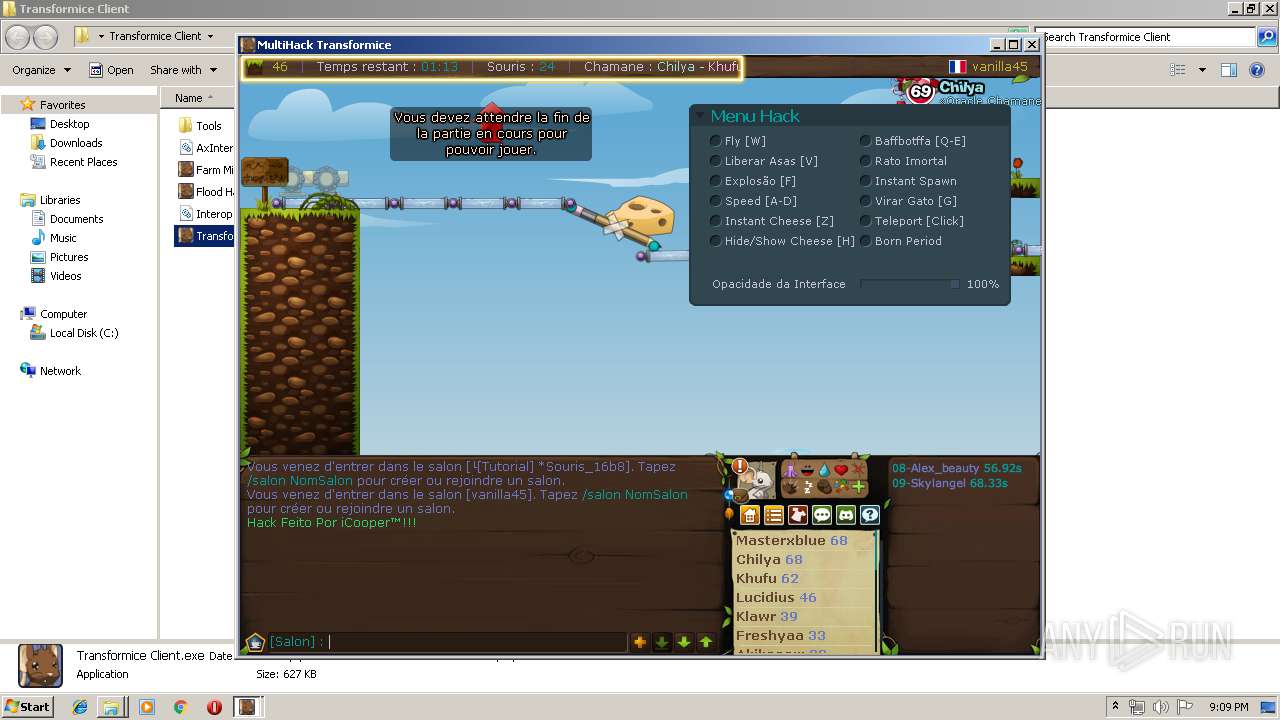
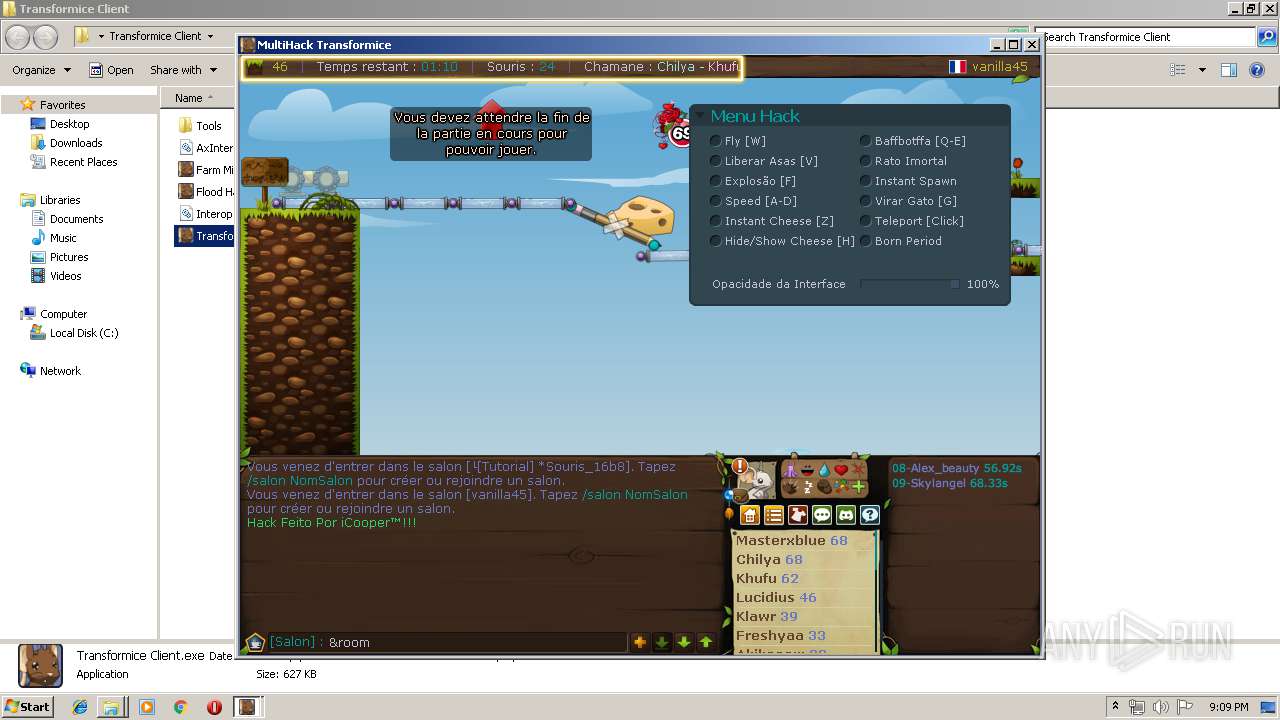
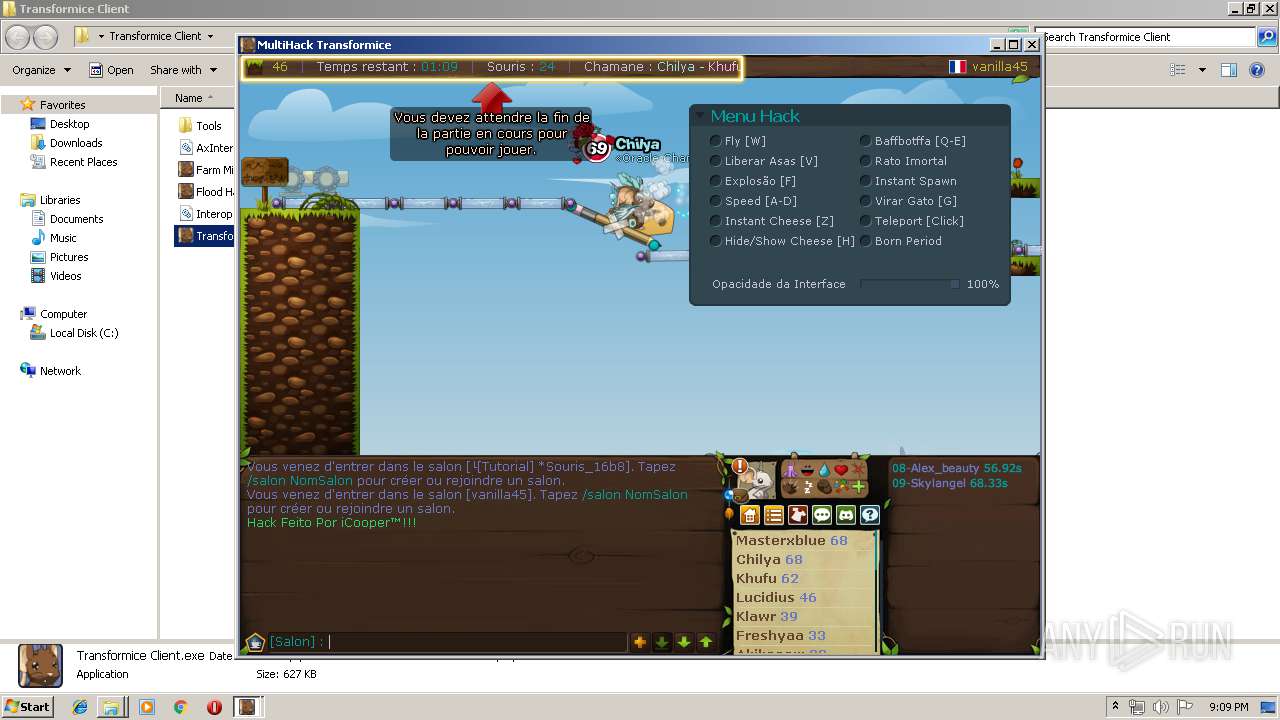
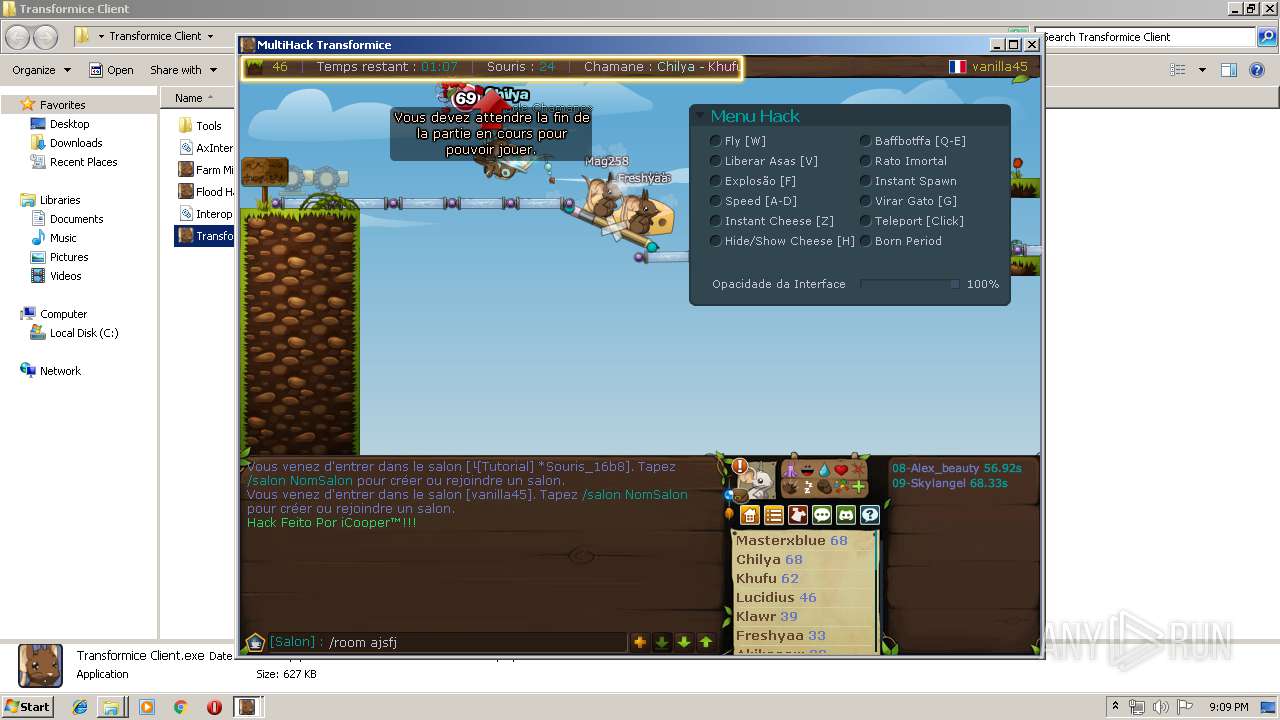
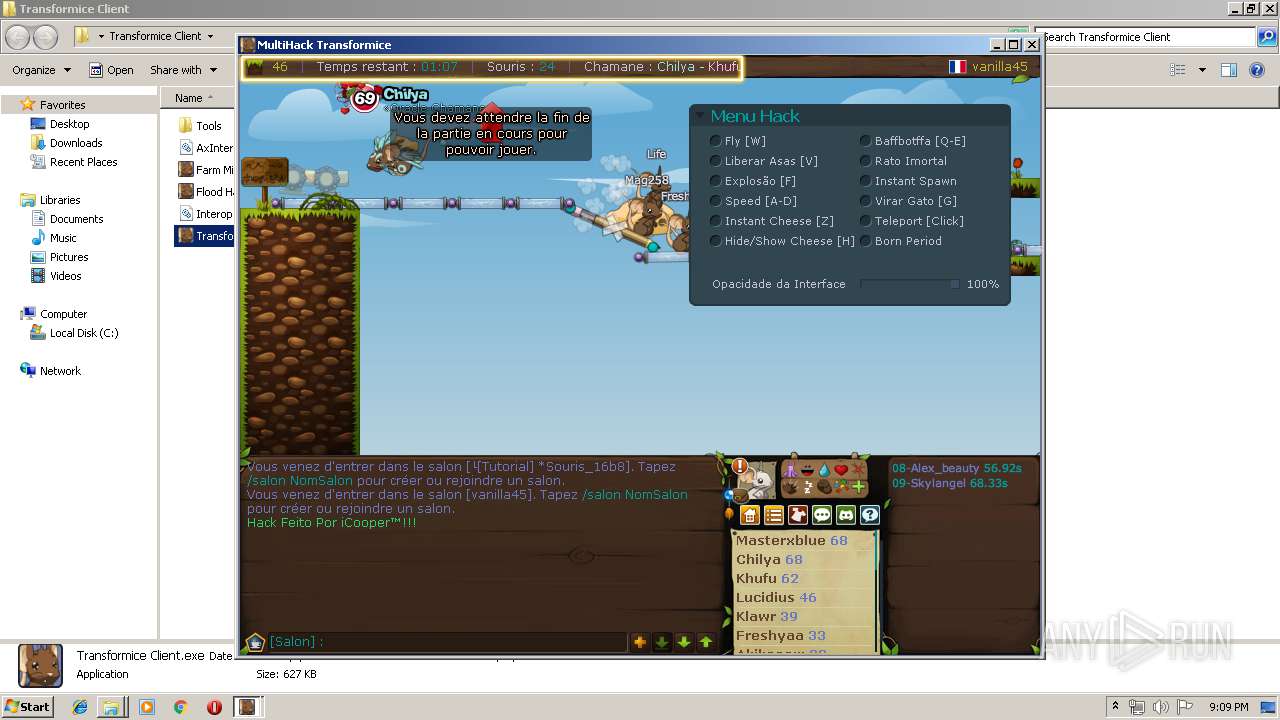
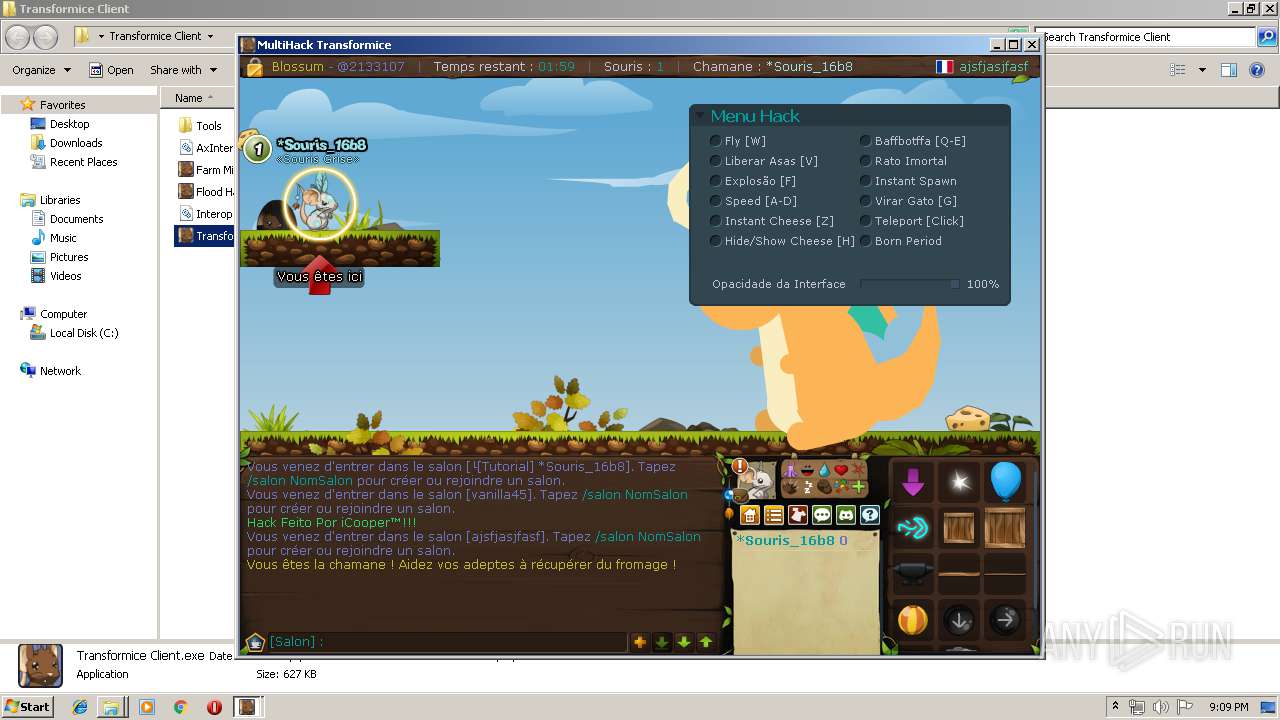
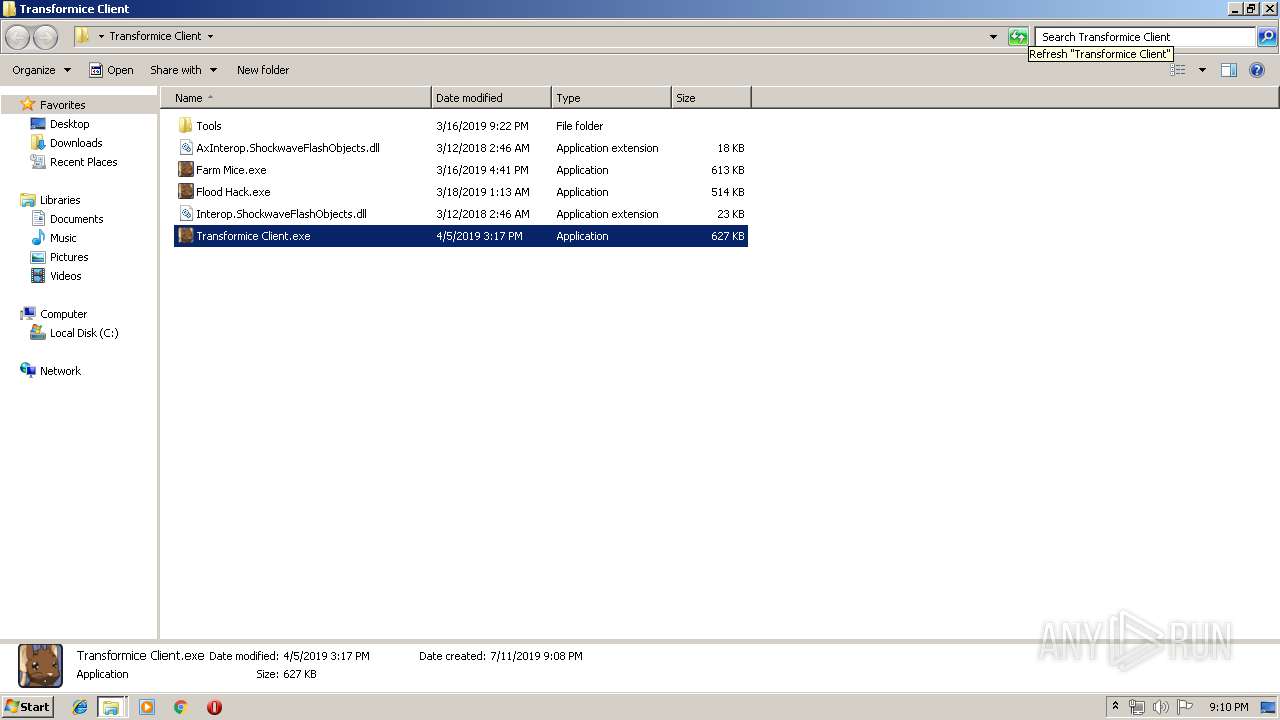
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3328)
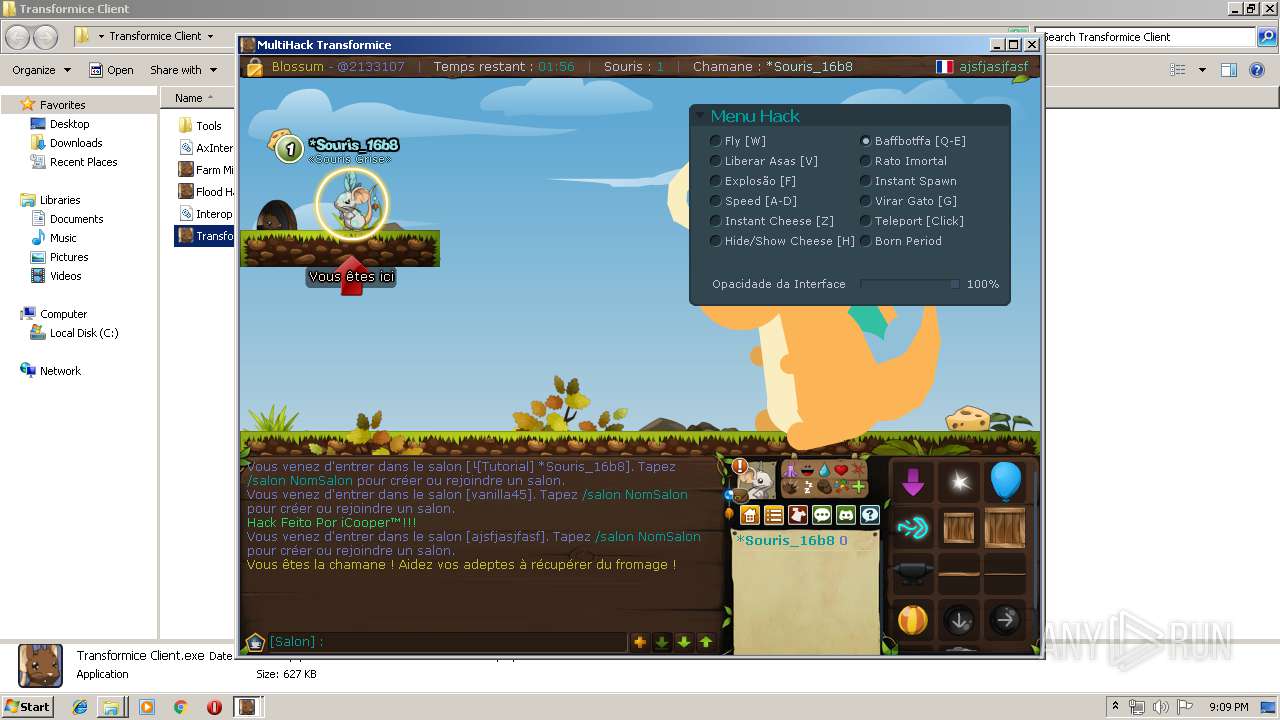
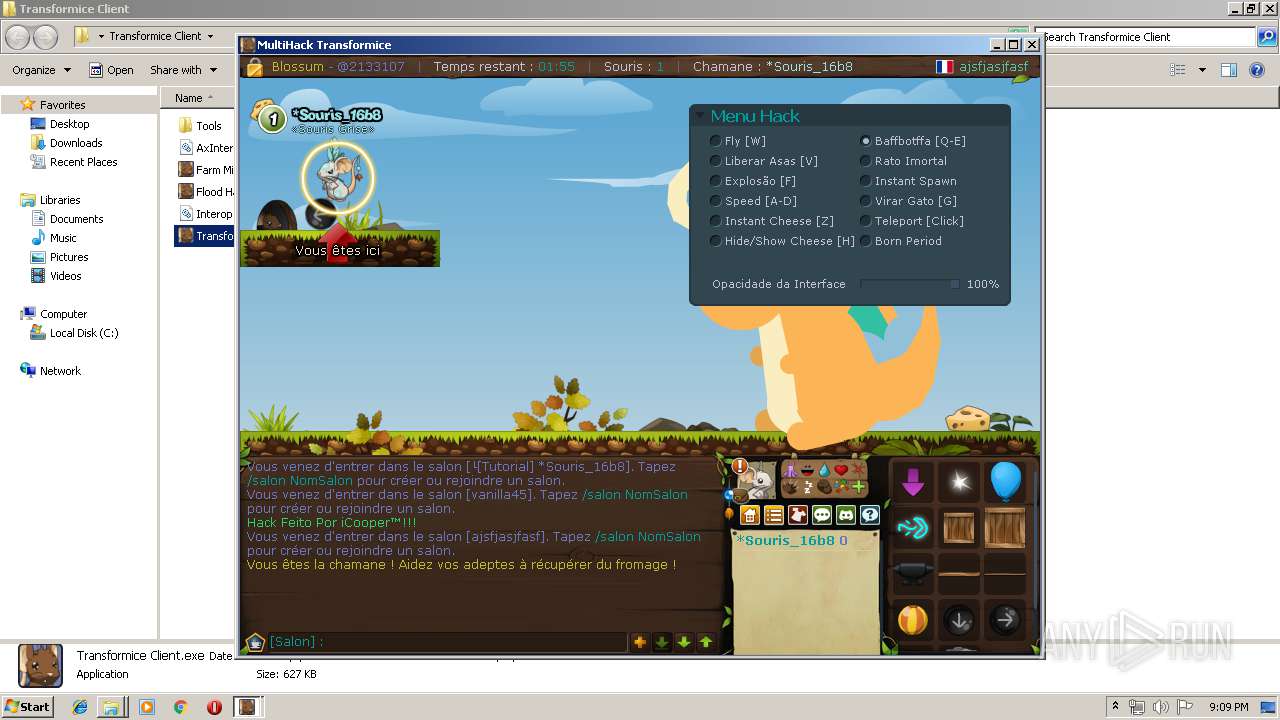
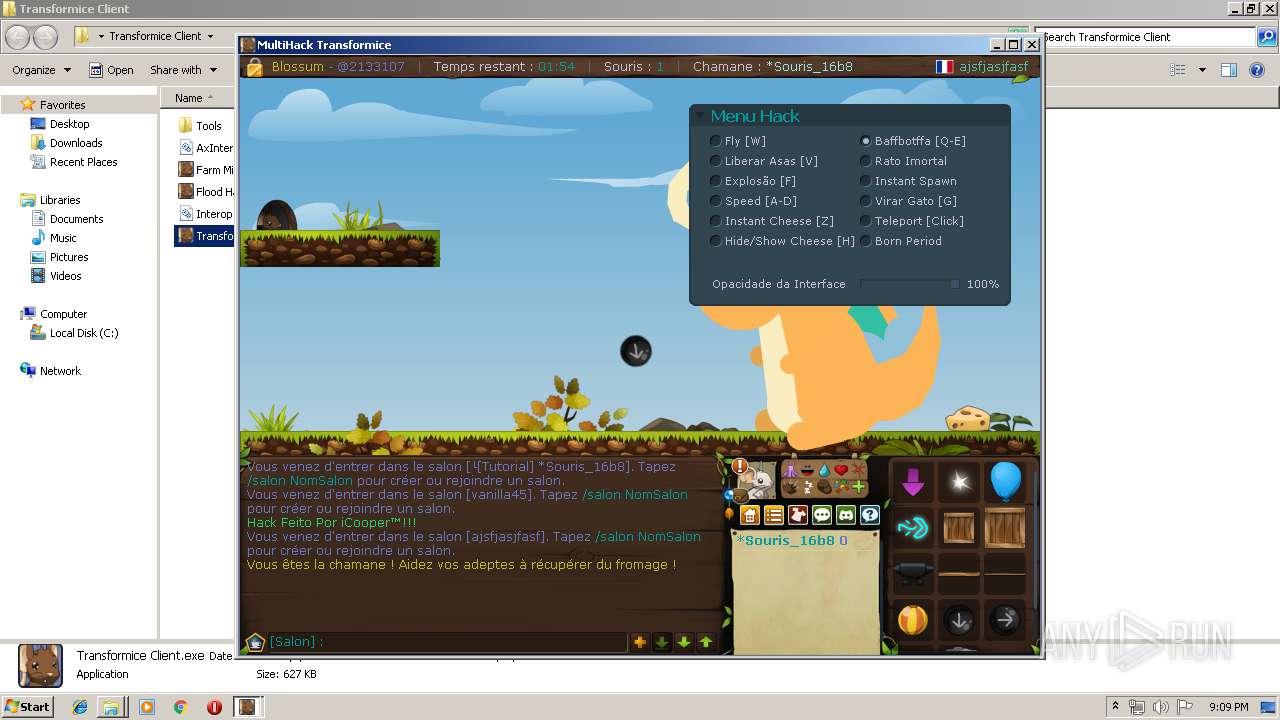
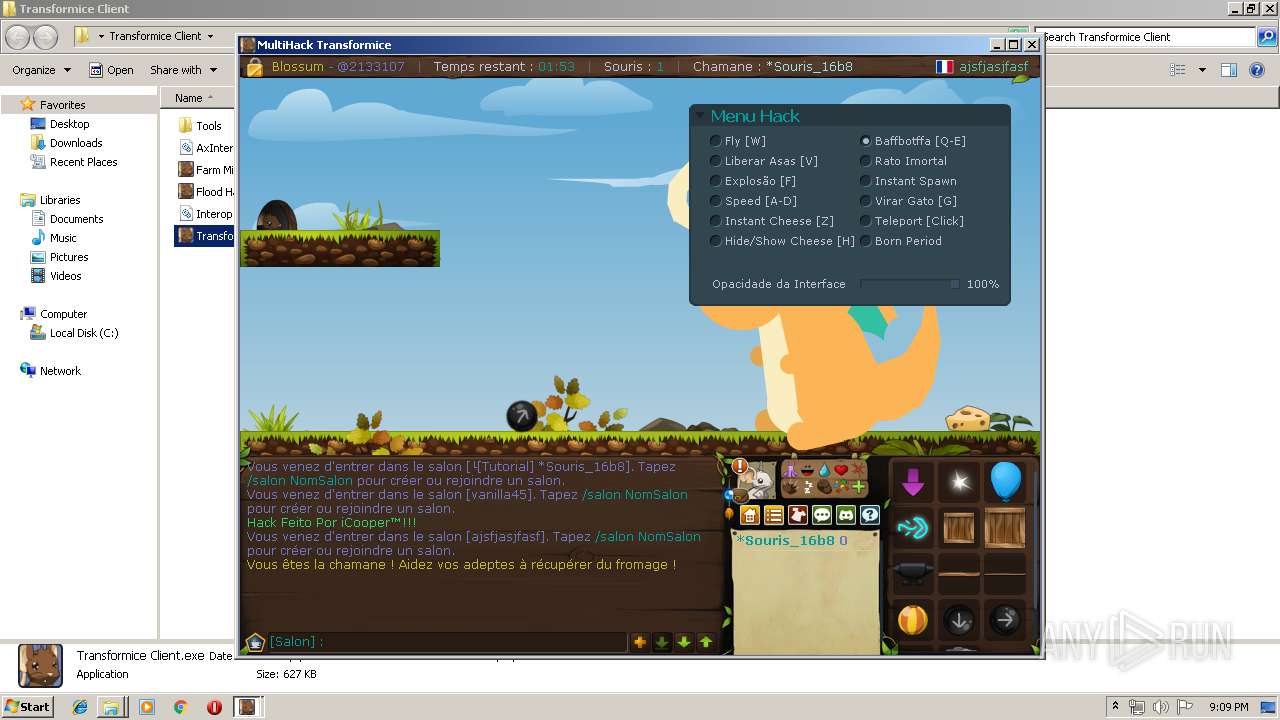
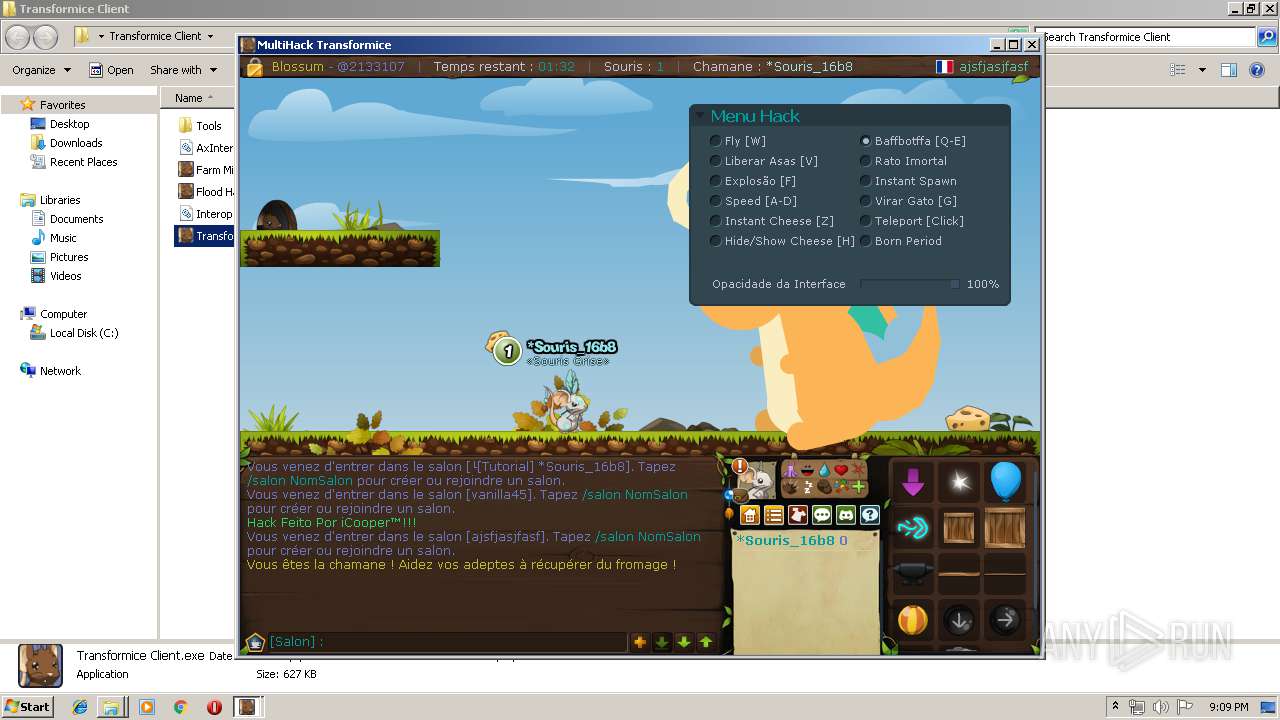
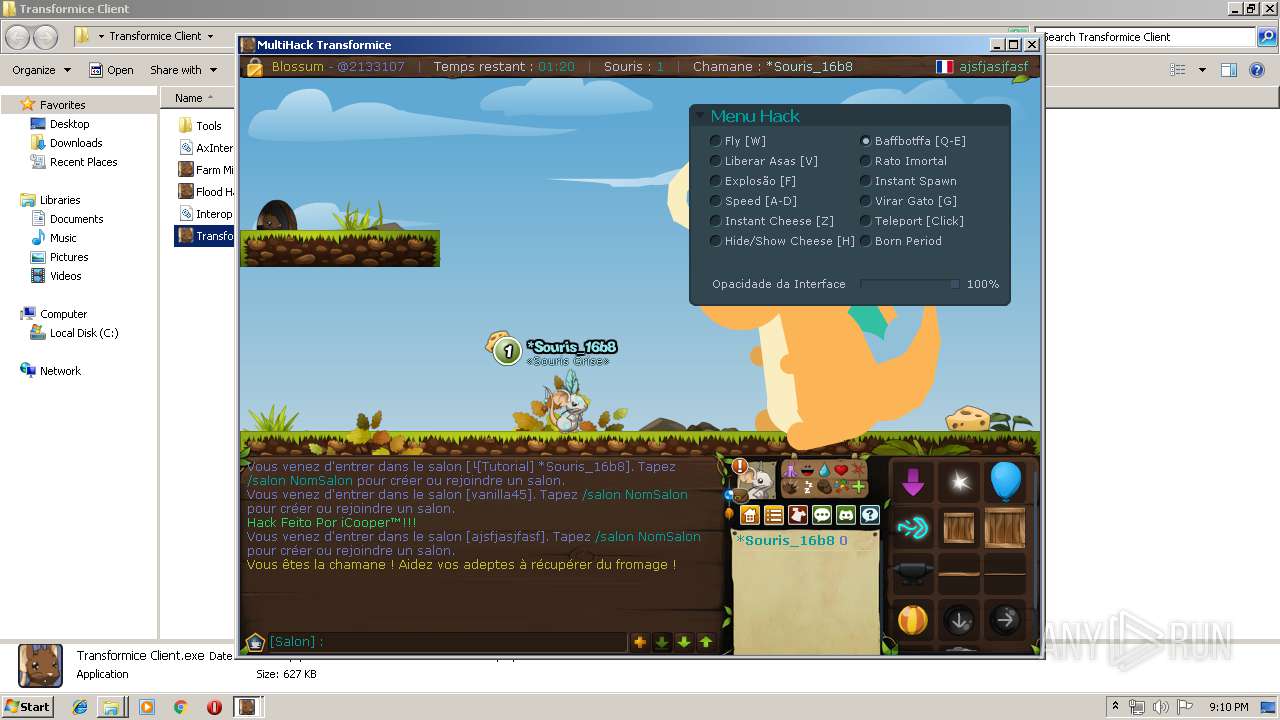
- Transformice Client.exe (PID: 3824)
- abcexport.exe (PID: 2376)
- abcexport.exe (PID: 3312)
- abcreplace.exe (PID: 3364)
Application was dropped or rewritten from another process
- abcexport.exe (PID: 3312)
- abcexport.exe (PID: 2376)
- rabcasm.exe (PID: 3980)
- abcreplace.exe (PID: 3364)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3804)
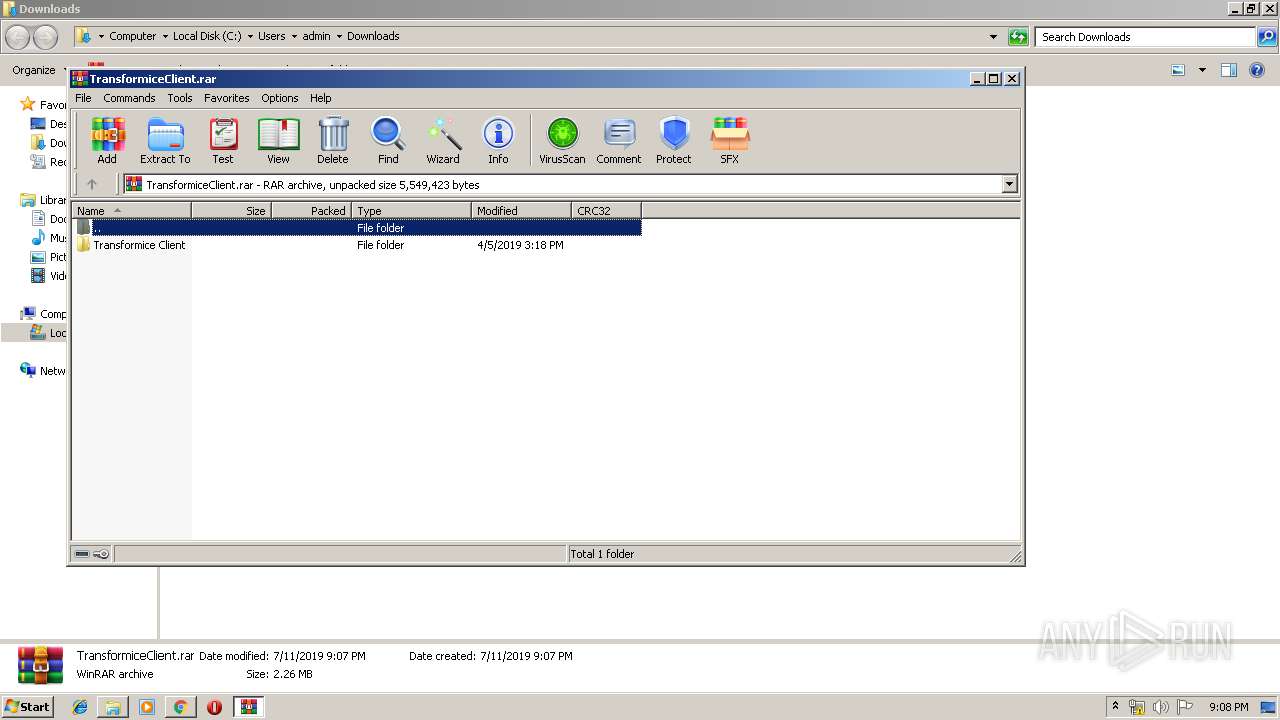
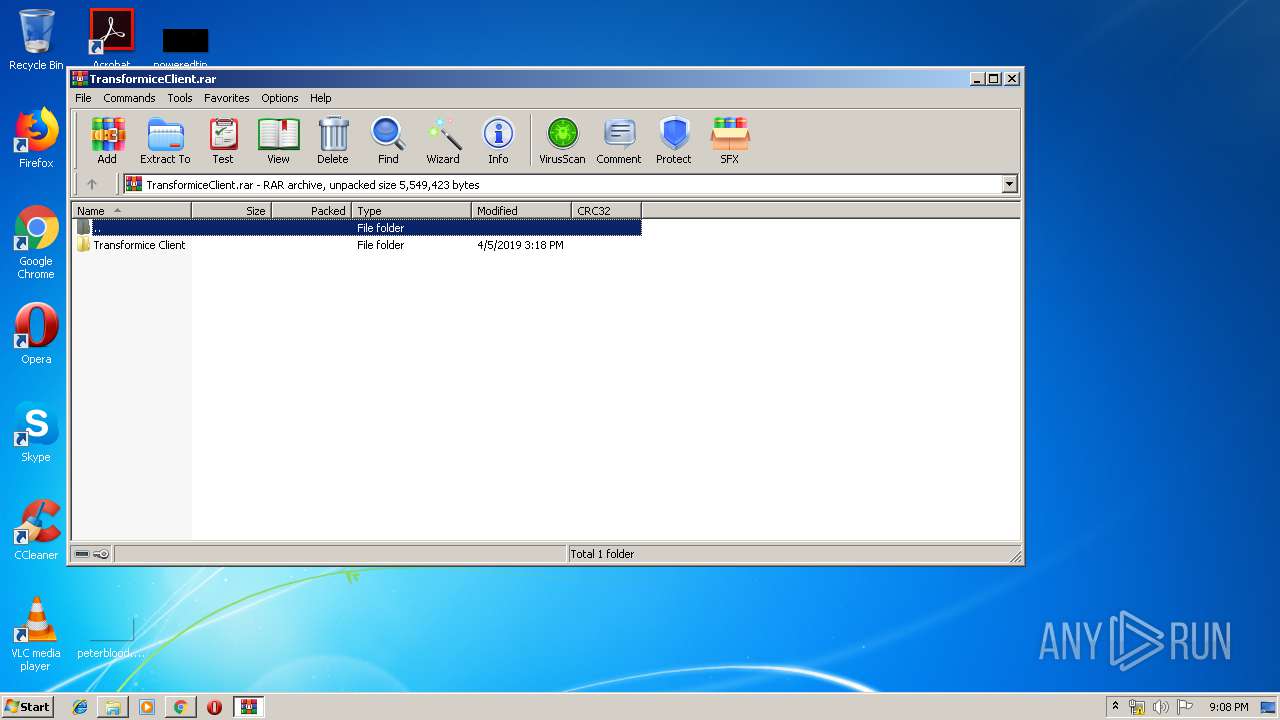
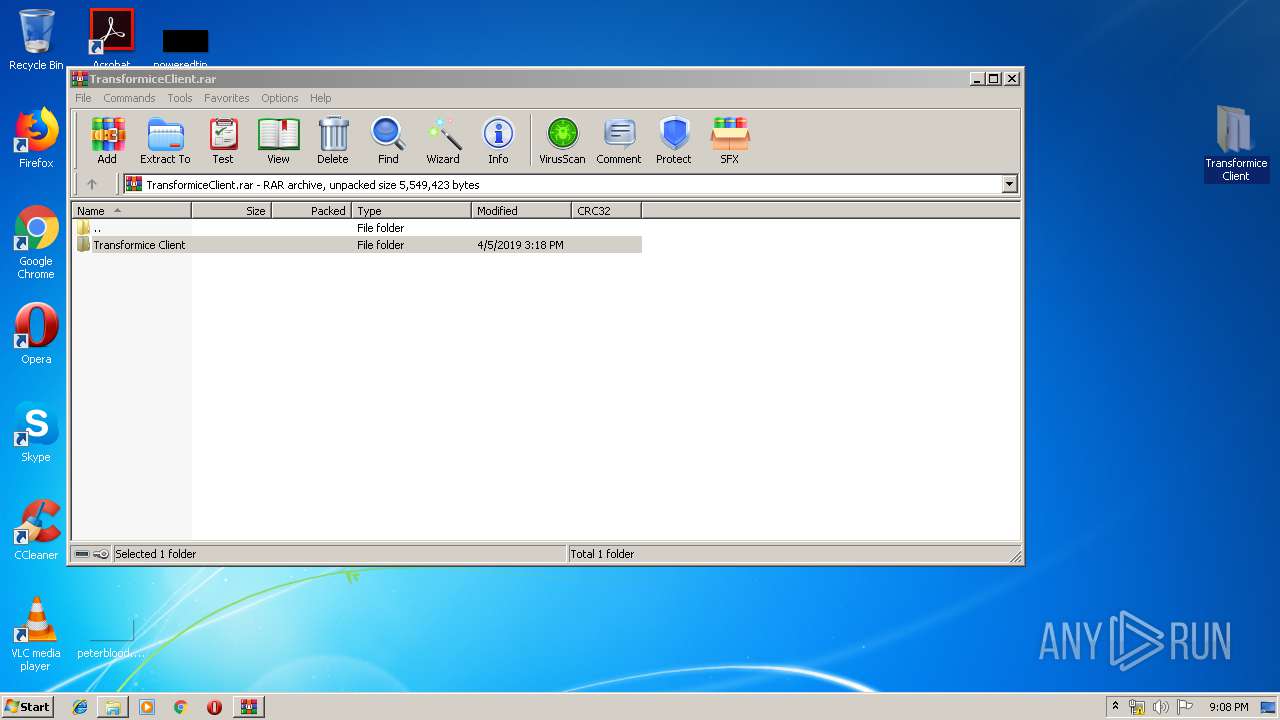
Executable content was dropped or overwritten
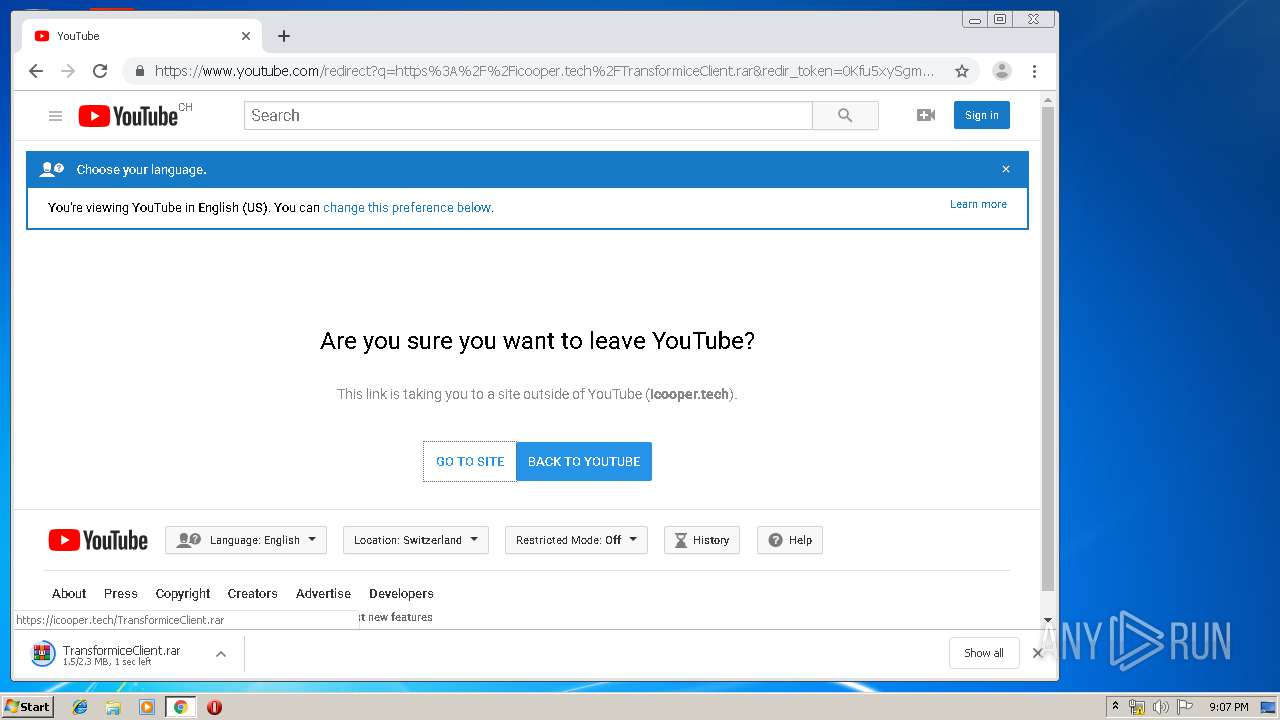
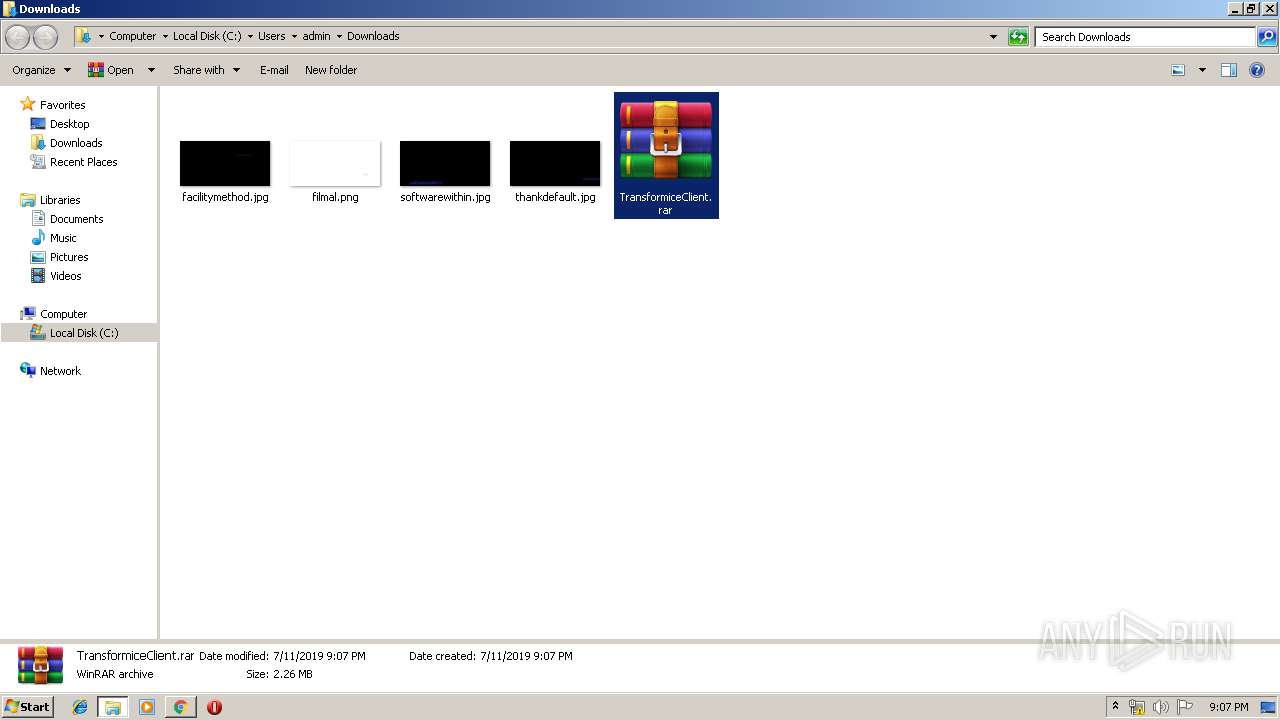
- WinRAR.exe (PID: 2912)
Reads internet explorer settings
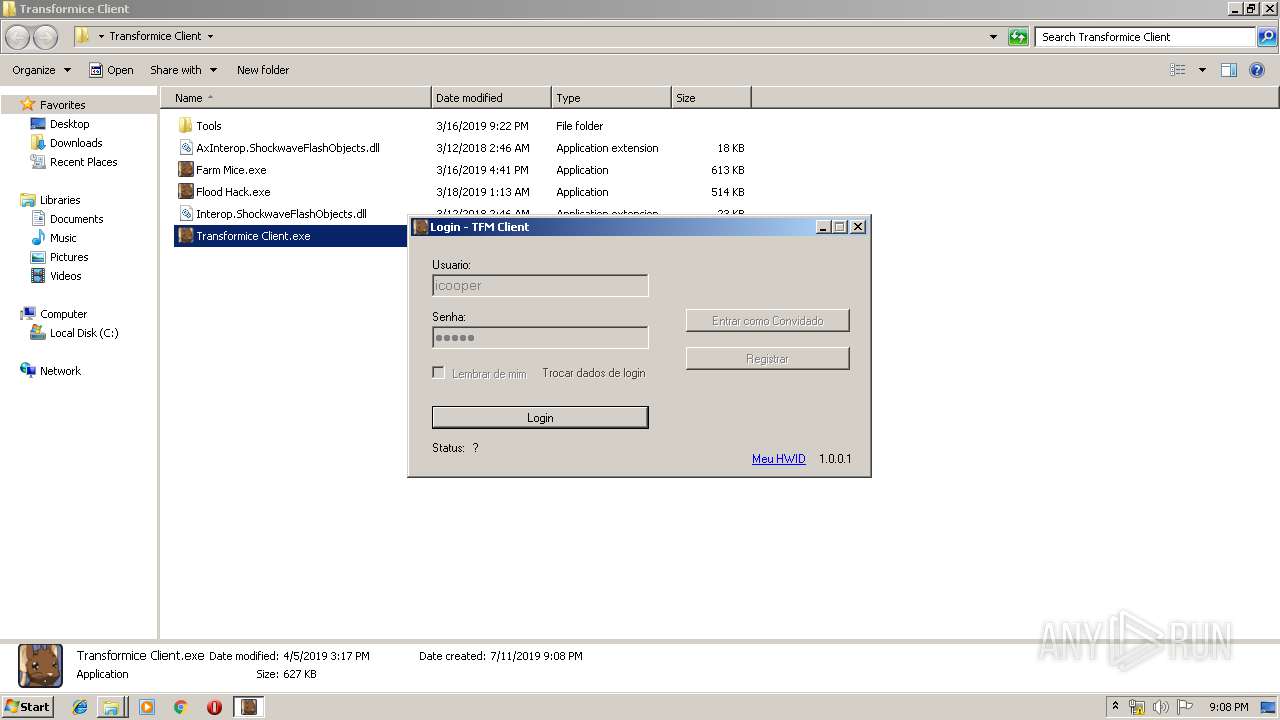
- Transformice Client.exe (PID: 3824)
Creates files in the user directory
- abcexport.exe (PID: 3312)
- abcexport.exe (PID: 2376)
- Transformice Client.exe (PID: 3824)
- rabcasm.exe (PID: 3980)
- rabcdasm.exe (PID: 988)
- rabcdasm.exe (PID: 3392)
Reads Internet Cache Settings
- Transformice Client.exe (PID: 3824)
INFO
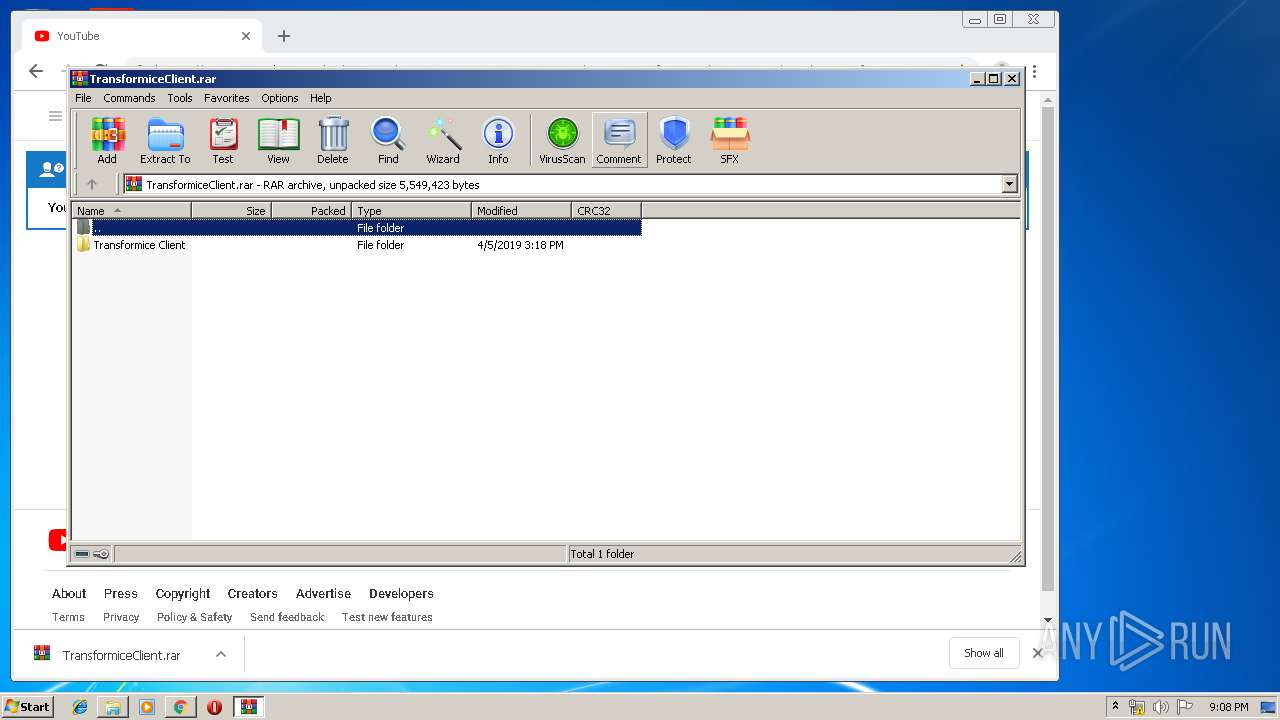
Manual execution by user
- chrome.exe (PID: 3804)
- WinRAR.exe (PID: 2912)
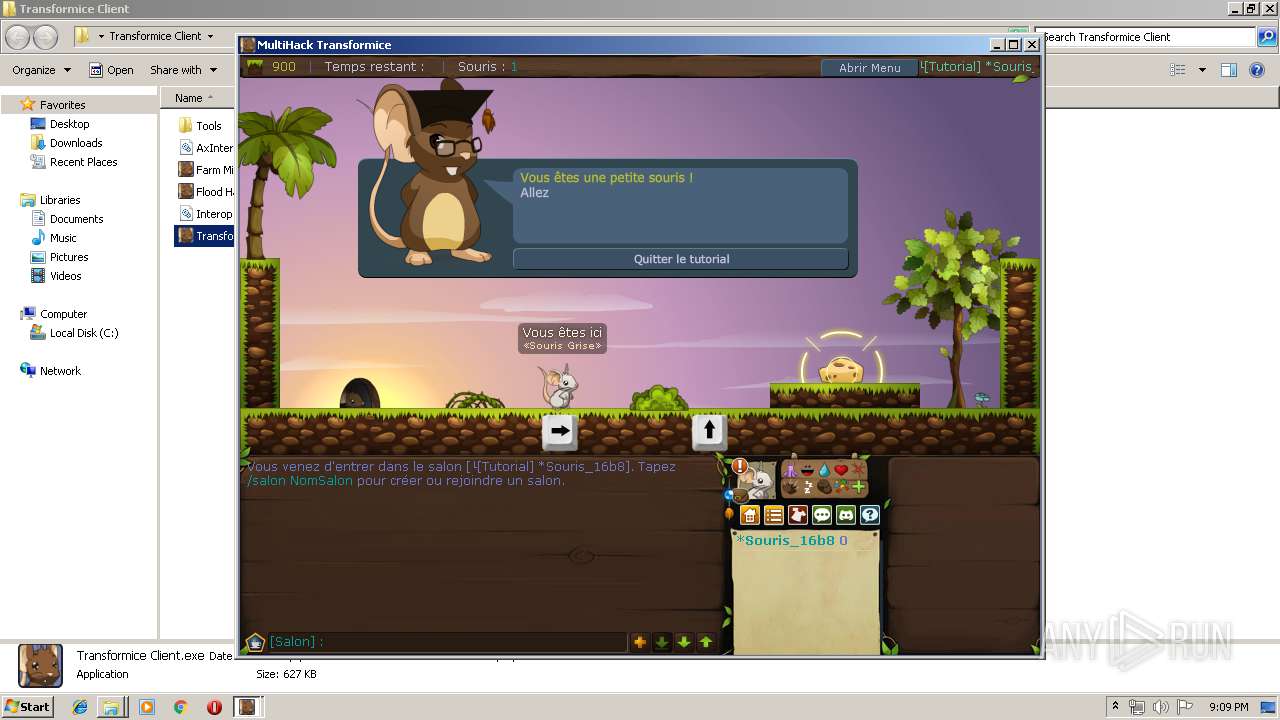
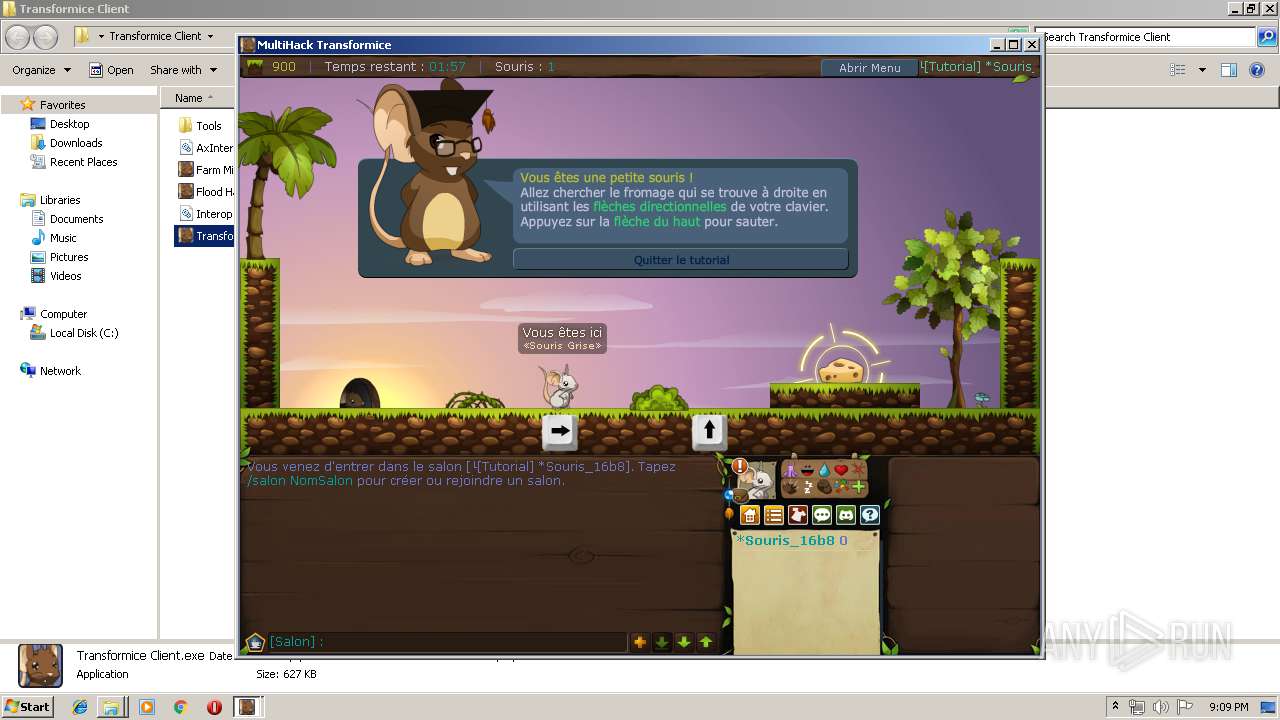
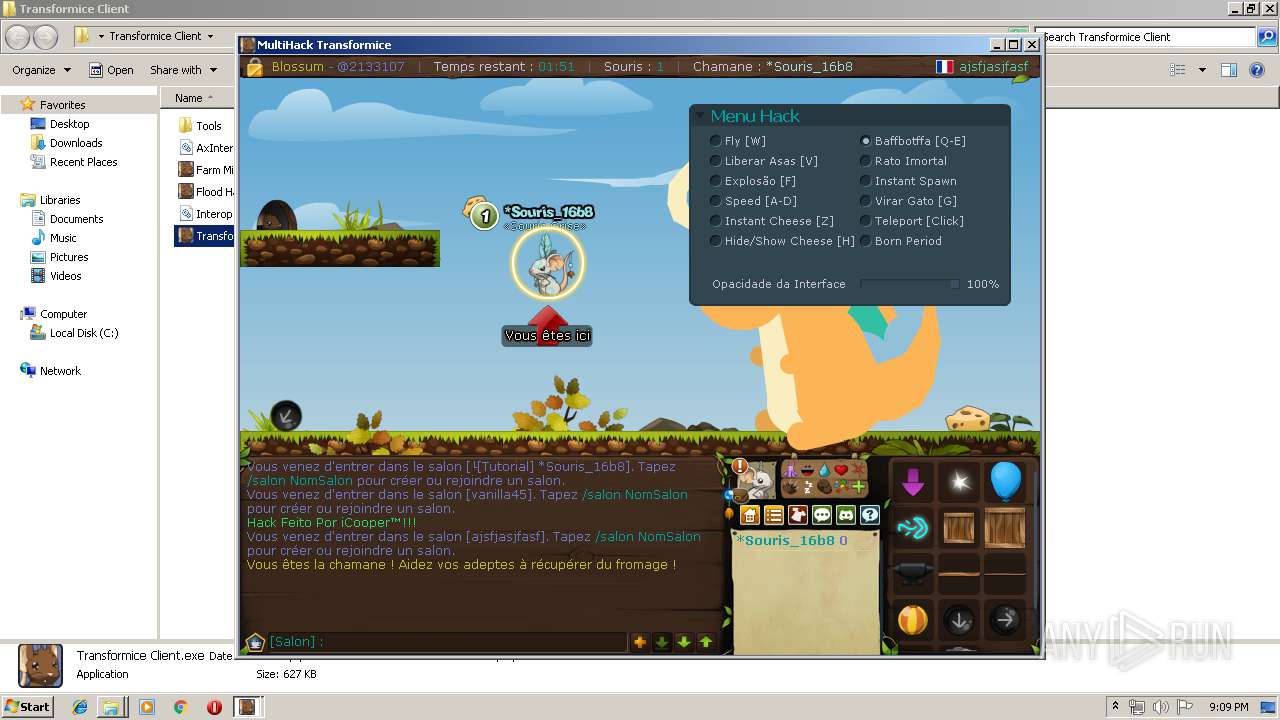
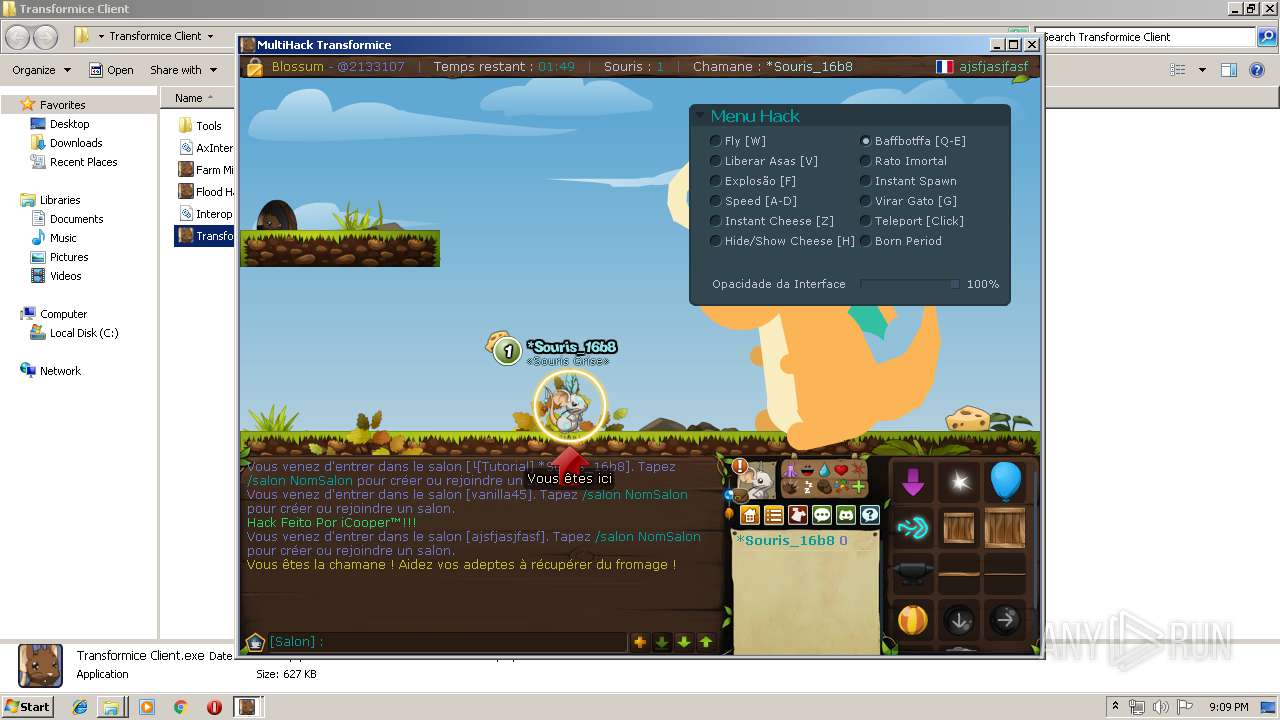
- Transformice Client.exe (PID: 3824)
Reads Internet Cache Settings
- chrome.exe (PID: 3804)
Application launched itself
- chrome.exe (PID: 3804)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2912)
Reads settings of System Certificates
- Transformice Client.exe (PID: 3824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
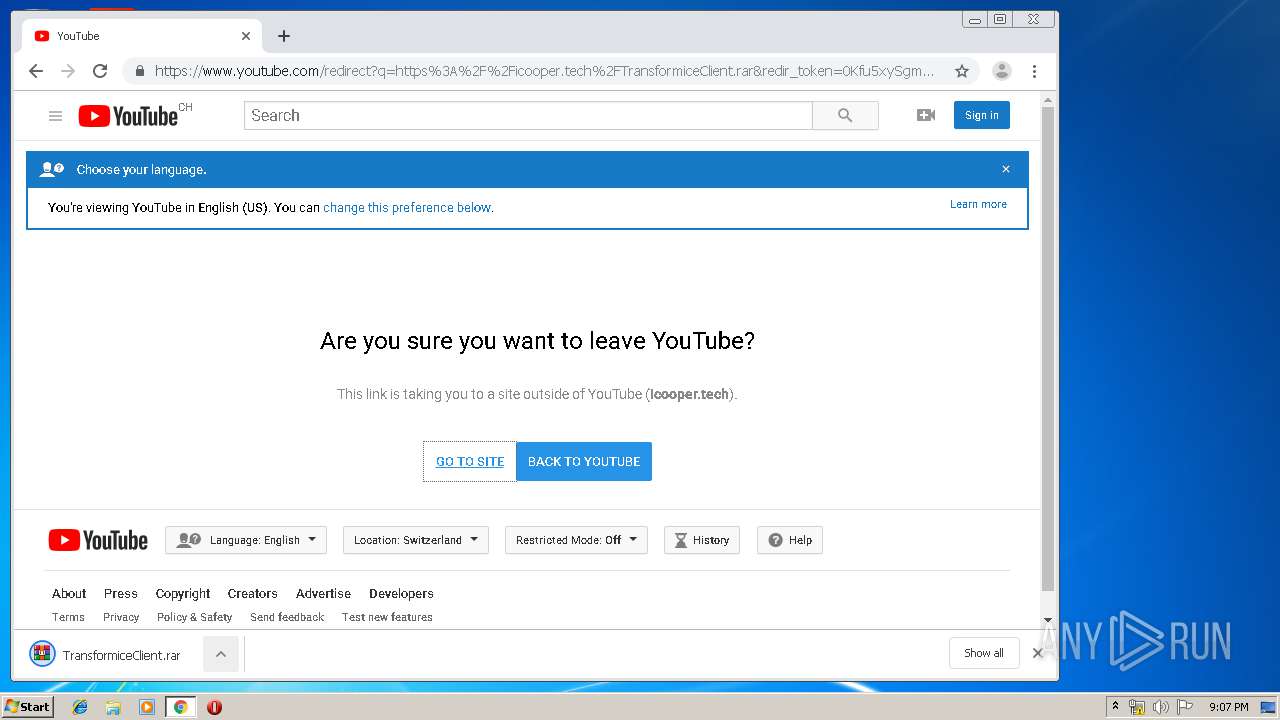
| HTTPEquivXUACompatible: | IE=edge |
|---|---|
| Title: | YouTube |
| Description: | Enjoy the videos and music you love, upload original content and share it all with friends, family and the world on YouTube. |
| Keywords: | video, sharing, camera phone, video phone, free, upload |
| themeColor: | #ff0000 |
Total processes
89
Monitored processes
42
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1964678696054584948,4319392242170944286,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1554650485042089959 --mojo-platform-channel-handle=2892 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | "C:\Users\admin\Desktop\Transformice Client\Tools\rabcdasm.exe" Chargeur-0.abc | C:\Users\admin\Desktop\Transformice Client\Tools\rabcdasm.exe | — | Transformice Client.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,1964678696054584948,4319392242170944286,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13852397744178821483 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2604 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1964678696054584948,4319392242170944286,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7771456082737186301 --mojo-platform-channel-handle=2432 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,1964678696054584948,4319392242170944286,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11419429621290237735 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2440 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1964678696054584948,4319392242170944286,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12135441577917831162 --mojo-platform-channel-handle=3116 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2100 | "swfdump.exe" -a "C:\Users\admin\AppData\Roaming\iCooper\Multi\Transformice.swf" | C:\Users\admin\Desktop\Transformice Client\Tools\swfdump.exe | — | swfdecript.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1964678696054584948,4319392242170944286,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9600178898199000039 --mojo-platform-channel-handle=1224 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1964678696054584948,4319392242170944286,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17052332718582625990 --mojo-platform-channel-handle=2780 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1964678696054584948,4319392242170944286,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15781186419321103794 --mojo-platform-channel-handle=3292 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 967
Read events
1 799
Write events
163
Delete events
5
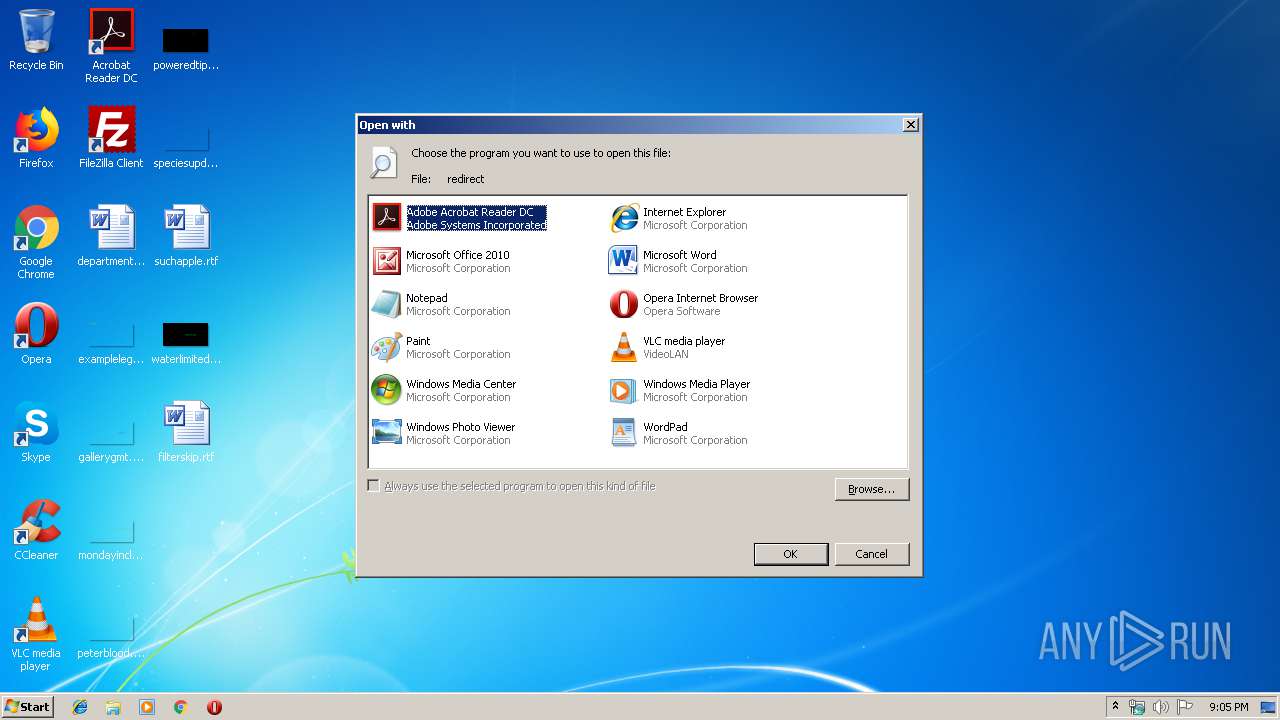
Modification events
| (PID) Process: | (3092) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
| (PID) Process: | (3092) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (3092) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (3092) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
| (PID) Process: | (3092) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (3092) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (3092) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (3092) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (3092) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (3092) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
Executable files
8
Suspicious files
48
Text files
2 913
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8f1ef15f-5d4b-4b97-9aa4-91c164c74f31.tmp | — | |
MD5:— | SHA256:— | |||
| 3804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF108167.TMP | text | |
MD5:— | SHA256:— | |||
| 3804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1080f9.TMP | text | |
MD5:— | SHA256:— | |||
| 3804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF108128.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
40
DNS requests
25
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3824 | Transformice Client.exe | GET | 200 | 51.75.128.119:80 | http://transformice.com/Transformice.swf | GB | swf | 1.99 Mb | whitelisted |
2848 | chrome.exe | GET | 302 | 216.58.207.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
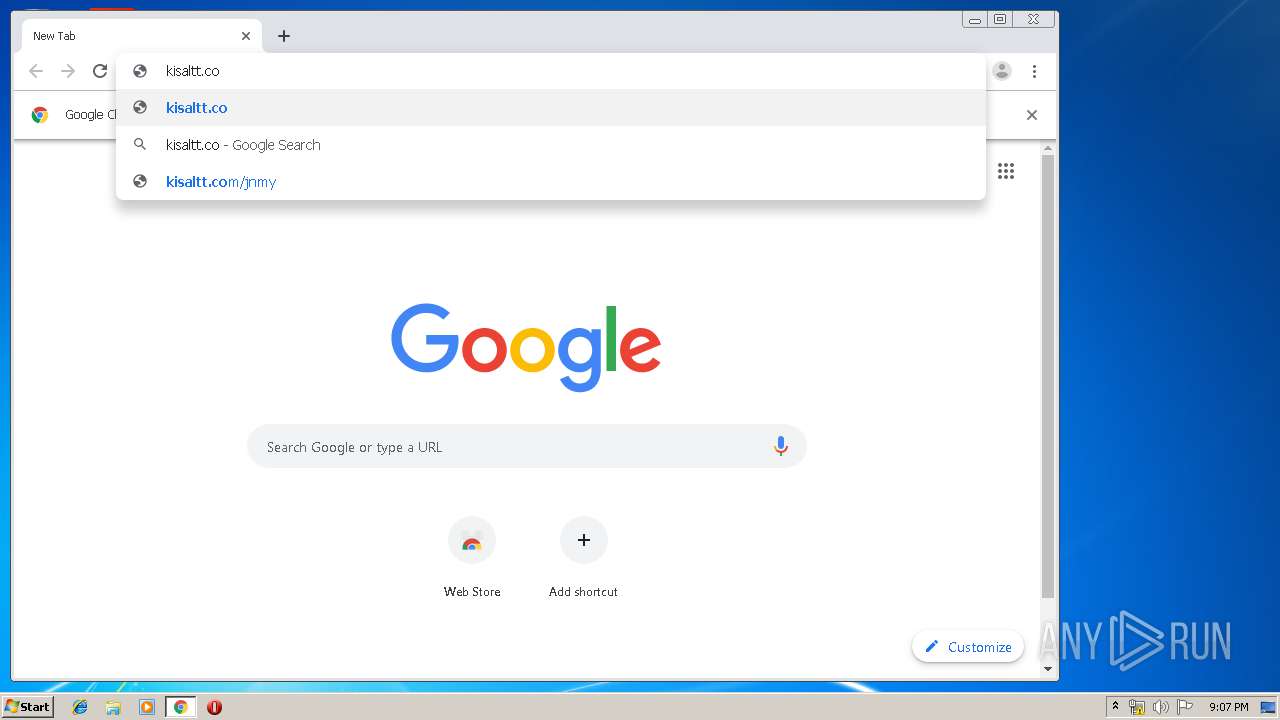
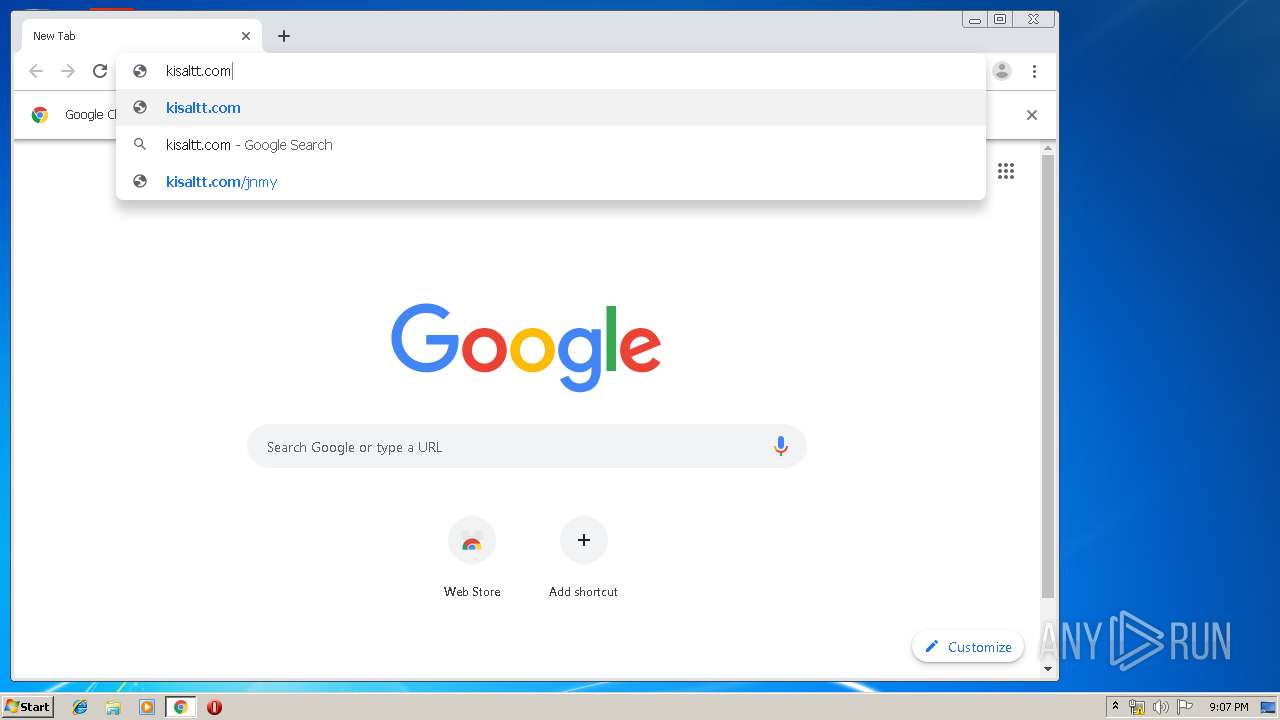
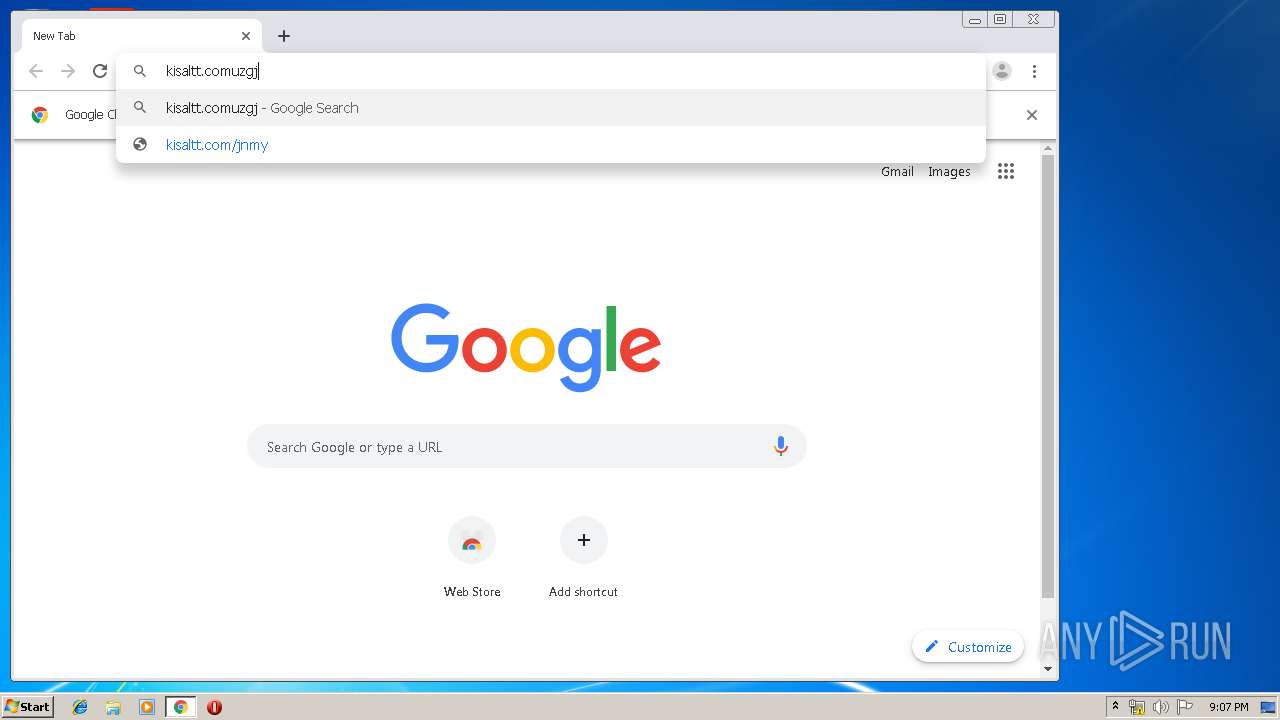
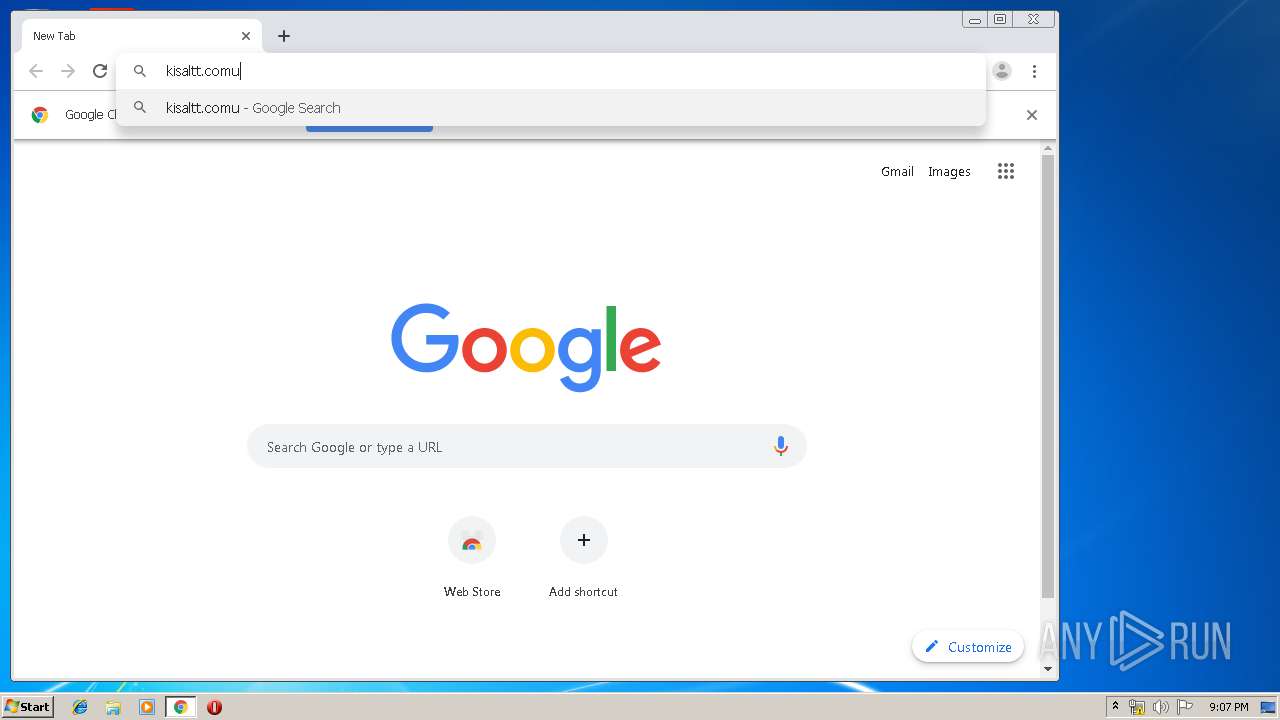
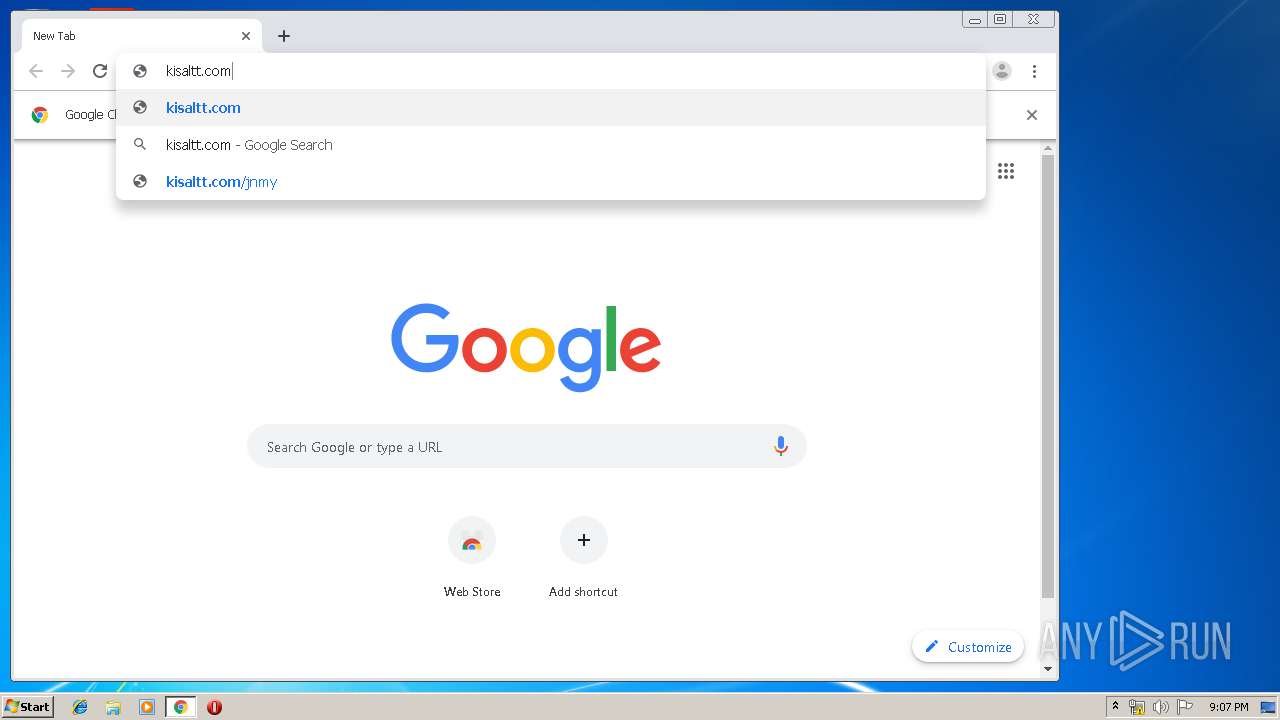
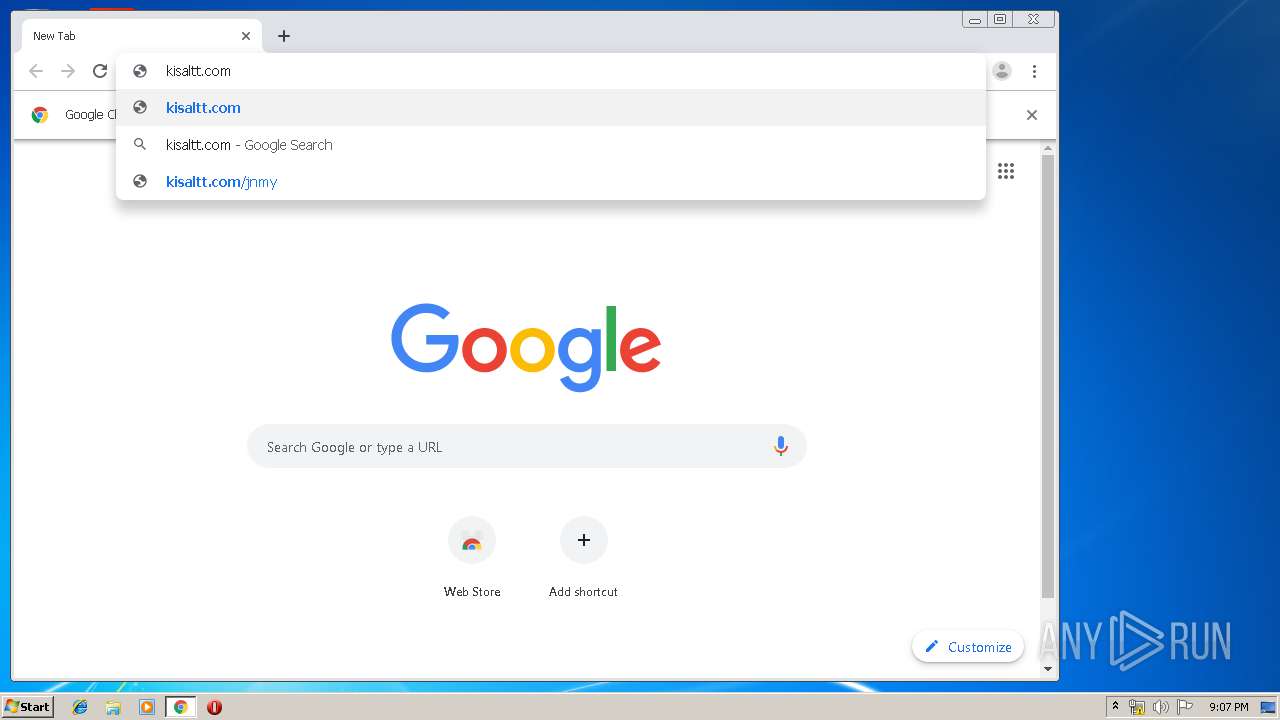
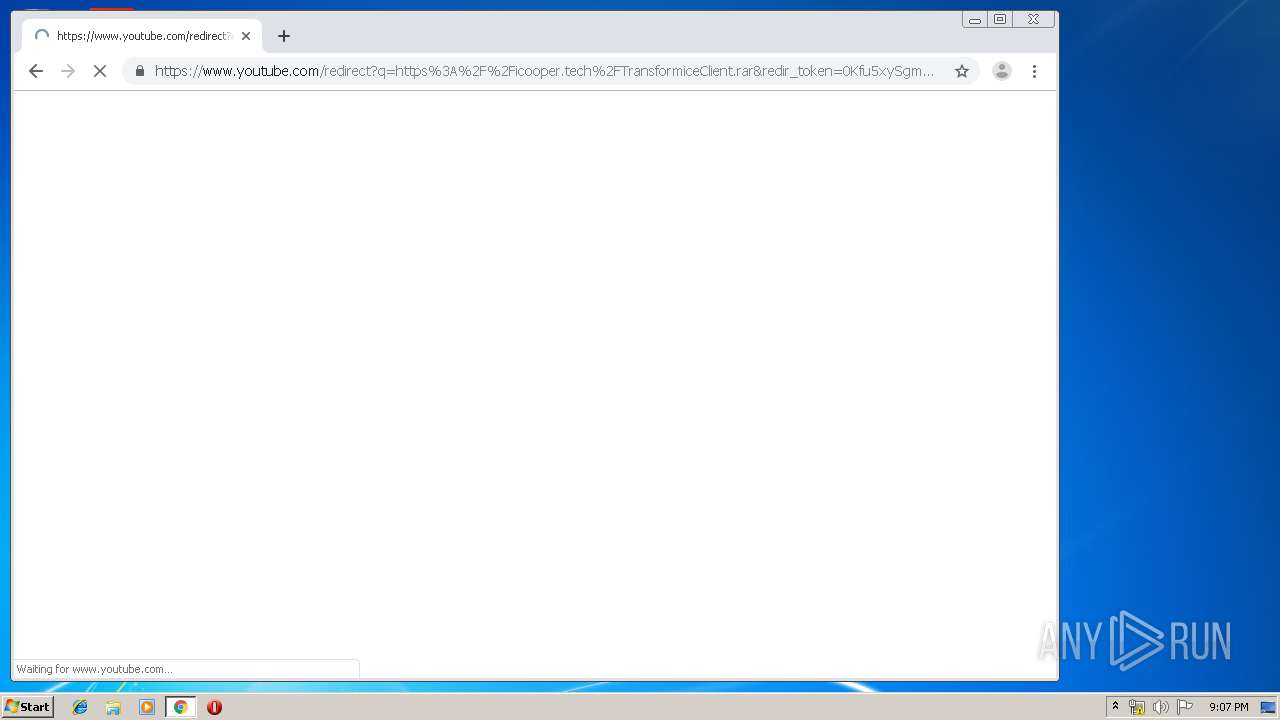
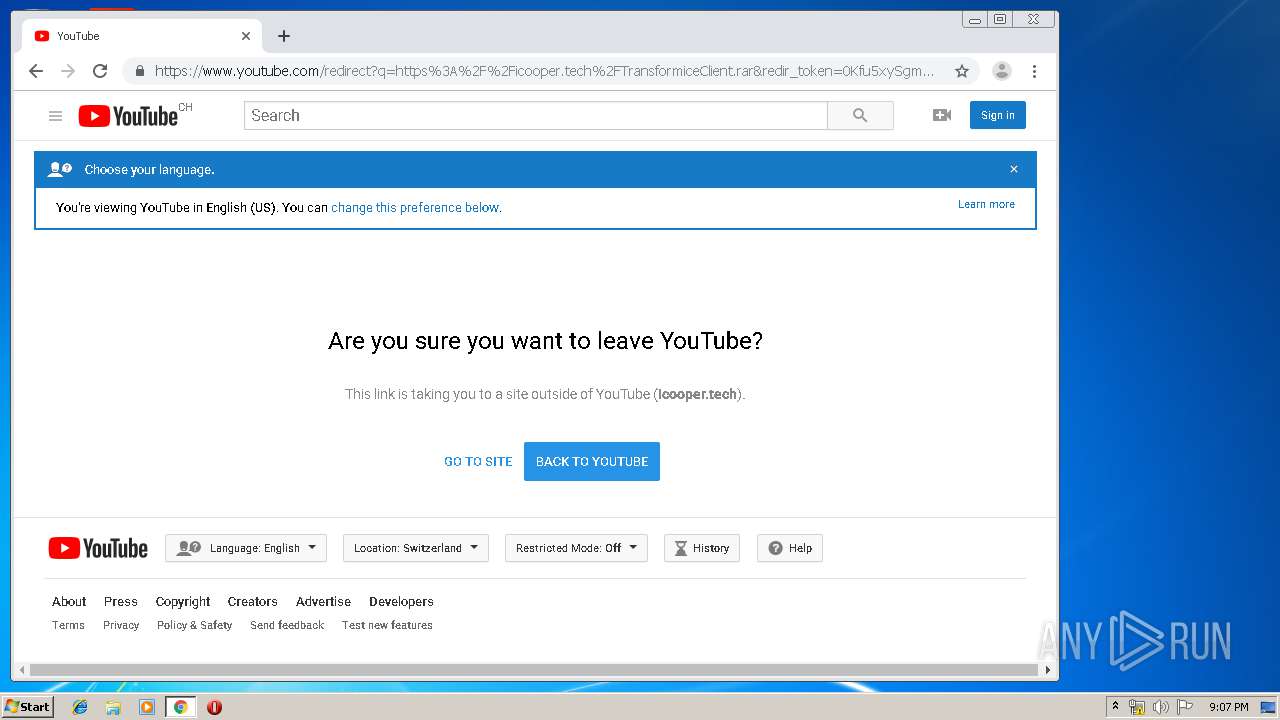
2848 | chrome.exe | GET | 302 | 95.173.170.161:80 | http://kisaltt.com/uzgjd | TR | html | 321 b | unknown |
3824 | Transformice Client.exe | GET | 200 | 145.239.9.124:80 | http://www.transformice.com/images/x_bibliotheques/x_fourrures3.swf?d=528.94?d=528 | FR | swf | 236 Kb | suspicious |
3824 | Transformice Client.exe | GET | 200 | 145.239.9.124:80 | http://www.transformice.com/langues/tfz_fr?d=94 | FR | pz | 35.4 Kb | suspicious |
3824 | Transformice Client.exe | GET | 200 | 145.239.9.124:80 | http://www.transformice.com/images/x_bibliotheques/x_pictos_editeur.swf?d=528.94?d=528 | FR | swf | 218 Kb | suspicious |
3824 | Transformice Client.exe | GET | 200 | 145.239.9.124:80 | http://www.transformice.com/images/x_transformice/x_aventure/x_banniere/x_21.jpg?d=94 | FR | image | 6.96 Kb | suspicious |
3824 | Transformice Client.exe | GET | 200 | 145.239.9.124:80 | http://www.transformice.com/images/x_bibliotheques/x_fourrures.swf?d=528.94?d=528 | FR | swf | 153 Kb | suspicious |
3824 | Transformice Client.exe | GET | 200 | 145.239.9.124:80 | http://www.transformice.com/images/x_bibliotheques/x_meli_costumes.swf?d=528.94?d=528 | FR | swf | 398 Kb | suspicious |
3824 | Transformice Client.exe | GET | 200 | 145.239.9.124:80 | http://www.transformice.com/images/musiques/tfm_0.mp3 | FR | mp3 | 931 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2848 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.18.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.16.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.22.78:443 | apis.google.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.18.110:443 | ogs.google.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.18.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.21.195:443 | www.google.ch | Google Inc. | US | whitelisted |
2848 | chrome.exe | 216.58.210.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
www.google.ch |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3824 | Transformice Client.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |
3824 | Transformice Client.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |