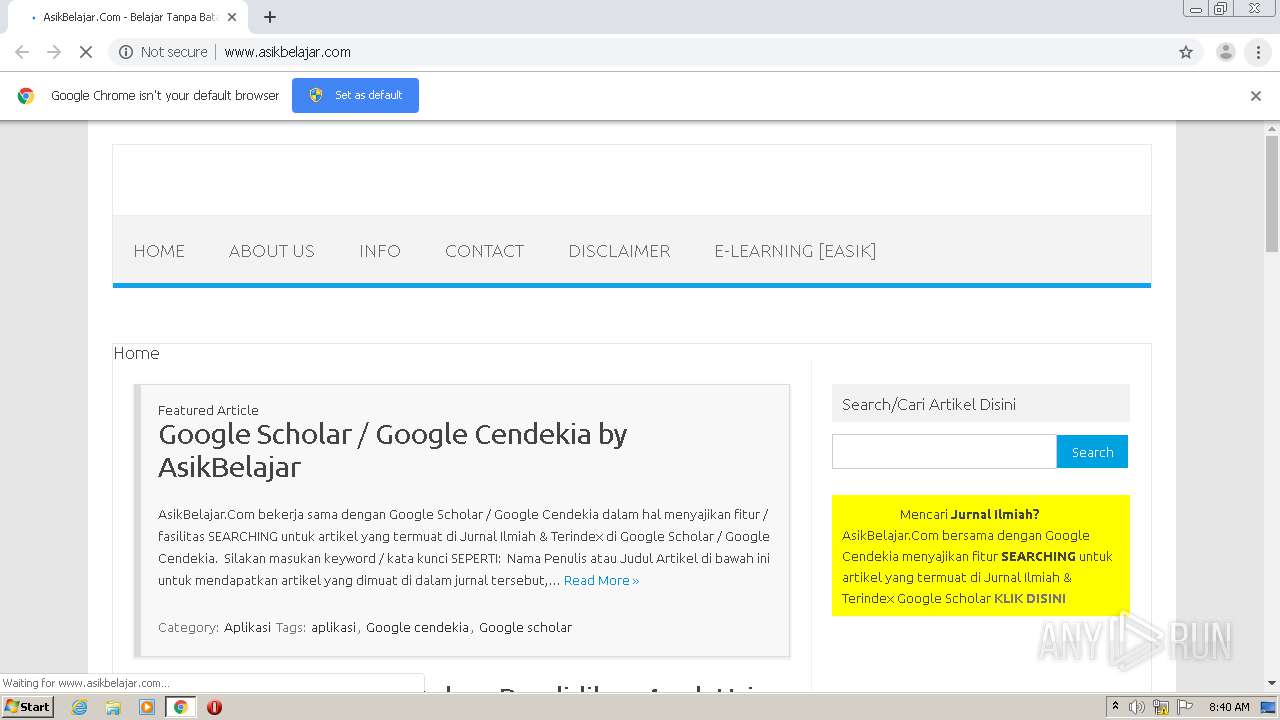
| URL: | http://asikbelajar.com |
| Full analysis: | https://app.any.run/tasks/8e56dd91-d9ef-48fa-8e28-d6310d584ec4 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 07:40:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5139F283D6162B329586AE97BCB57A3E |
| SHA1: | D08342FAEA2D453B730686D5116FAA951400AEE3 |
| SHA256: | F8D638DA844432958AEEFFF1830F34497DCFC1B4D818B027E5B4B0C2485FCC48 |
| SSDEEP: | 3:N1Kf6Hl8m:Ckum |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2488)
- chrome.exe (PID: 1864)
Application launched itself
- chrome.exe (PID: 2488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
17
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,15561802358066178949,6344156754844541703,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12921517427741993707 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3552 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,15561802358066178949,6344156754844541703,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10811987451309356196 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,15561802358066178949,6344156754844541703,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=928131100726803052 --mojo-platform-channel-handle=3476 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,15561802358066178949,6344156754844541703,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12209533222061857785 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1956 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,15561802358066178949,6344156754844541703,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7852304699670547827 --mojo-platform-channel-handle=1600 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c57a9d0,0x6c57a9e0,0x6c57a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2480 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,15561802358066178949,6344156754844541703,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17246465648474511999 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3580 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://asikbelajar.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,15561802358066178949,6344156754844541703,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=517767666831669153 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3672 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
588
Read events
520
Write events
64
Delete events
4
Modification events
| (PID) Process: | (2488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1944) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2488-13247653221405750 |
Value: 259 | |||
| (PID) Process: | (2488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2488) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
83
Text files
75
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E9466-9B8.pma | — | |
MD5:— | SHA256:— | |||
| 2488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cbdbd236-1954-4441-be57-f02b7b9d8e48.tmp | — | |
MD5:— | SHA256:— | |||
| 2488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d41a1.TMP | text | |
MD5:— | SHA256:— | |||
| 2488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2d41a1.TMP | text | |
MD5:— | SHA256:— | |||
| 2488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 2488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF2d422e.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
92
DNS requests
58
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1864 | chrome.exe | GET | 200 | 202.52.146.121:80 | http://www.asikbelajar.com/ | ID | html | 8.79 Kb | suspicious |
1864 | chrome.exe | GET | 200 | 52.85.32.16:80 | http://compasscdn.adop.cc/js/adop_collapse_1.1.8.min.js | US | text | 5.39 Kb | malicious |
1864 | chrome.exe | GET | 200 | 54.230.183.55:80 | http://compass.adop.cc/assets/js/adop/adopJ.js?v=10 | US | text | 1.89 Kb | shared |
1864 | chrome.exe | GET | 200 | 52.85.32.24:80 | http://get.optad360.io/sf/33f7b45a-5f31-11e8-b929-06048607e8f8/plugin.min.js | US | text | 62.9 Kb | shared |
1864 | chrome.exe | GET | 200 | 202.52.146.121:80 | http://www.asikbelajar.com/wp-content/themes/iconic-one/custom.css?ver=5.5.1 | ID | text | 69 b | suspicious |
1864 | chrome.exe | GET | 200 | 202.52.146.121:80 | http://www.asikbelajar.com/wp-includes/css/dist/block-library/style.min.css?ver=5.5.1 | ID | text | 9.40 Kb | suspicious |
1864 | chrome.exe | GET | 200 | 202.52.146.121:80 | http://www.asikbelajar.com/wp-content/themes/iconic-one/js/selectnav.js?ver=1.0 | ID | html | 1.60 Kb | suspicious |
1864 | chrome.exe | GET | 200 | 202.52.146.121:80 | http://www.asikbelajar.com/wp-content/plugins/advanced-random-posts-widget/assets/css/arpw-frontend.css?ver=5.5.1 | ID | text | 275 b | suspicious |
1864 | chrome.exe | GET | 200 | 13.125.190.115:80 | http://data.adop.cc/collect.php?data=eyJkdCI6IjIwMjAxMDIwMDc0MDQ2IiwiY3RyeSI6IkxUIiwiYWNpZCI6IkxULTIwMTAyMDA3NDA0Ni1mYjA4YjA4NDk3NmU0YmFkIiwibmV0IjoiR29vZ2xlIEFkIE1hbmFnZXIiLCJ3Z3QiOiIxMDAiLCJvcmQiOiIxLzMiLCJ6aWQiOiJhMmZmMGRkZi1hOTgxLTQwOWQtOTljZC1hNjk5NDQ0YTEwOGQiLCJ1YSI6Ik1vemlsbGEvNS4wIChXaW5kb3dzIE5UIDYuMSkgQXBwbGVXZWJLaXQvNTM3LjM2IChLSFRNTCwgbGlrZSBHZWNrbykgQ2hyb21lLzc1LjAuMzc3MC4xMDAgU2FmYXJpLzUzNy4zNiIsImJyb3ciOiJDaHJvbWUiLCJkZXYiOiJkZXNrdG9wIiwib3MiOiJXaW5kb3dzIiwiaXAiOiI4NS4yMDYuMTc1LjIxOSIsImZsb2MiOiJodHRwOi8vd3d3LmFzaWtiZWxhamFyLmNvbS8iLCJjZHQiOiIyMDEwMjAwNzQwNDYiLCJkaXIiOiJ2IiwidyI6IjMwMCIsImgiOiIyNTAiLCJsYW5nIjoiZW4tdXMiLCJzY3IiOiIxMjgweDcyMCIsInZwIjoiMzAweDI1MCIsInBhdGgiOiIvIiwidHAiOiJyZSIsInJlZiI6IiIsInRpdGxlIjoiQXNpa0JlbGFqYXIuQ29tJTIwLSUyMEJlbGFqYXIlMjBUYW5wYSUyMEJhdGFzIiwicGwiOiJXaW4zMiIsIndkIjoibi9hIiwicGIiOiJOIiwicHQiOiJodHRwIiwibG9nIjoiYmFzaWMifQ%3D%3D | KR | text | 2 b | whitelisted |
1864 | chrome.exe | GET | 200 | 13.125.190.115:80 | http://data.adop.cc/collect.php?log=com_imp&dt=20201020074046&aid=e40fbcdc-cb58-4dc7-9297-1beef6781898&zid=a2ff0ddf-a981-409d-99cd-a699444a108d&r=YImp | KR | text | 2 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1864 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1864 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1864 | chrome.exe | 202.52.146.121:80 | asikbelajar.com | Global Media Teknologi, PT | ID | suspicious |
1864 | chrome.exe | 172.217.18.2:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
1864 | chrome.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1864 | chrome.exe | 172.217.16.130:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
1864 | chrome.exe | 216.58.205.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1864 | chrome.exe | 202.52.146.121:443 | asikbelajar.com | Global Media Teknologi, PT | ID | suspicious |
1864 | chrome.exe | 52.85.32.16:80 | compasscdn.adop.cc | Amazon.com, Inc. | US | unknown |
1864 | chrome.exe | 216.58.205.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
asikbelajar.com |
| suspicious |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.asikbelajar.com |
| suspicious |
securepubads.g.doubleclick.net |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
compasscdn.adop.cc |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |