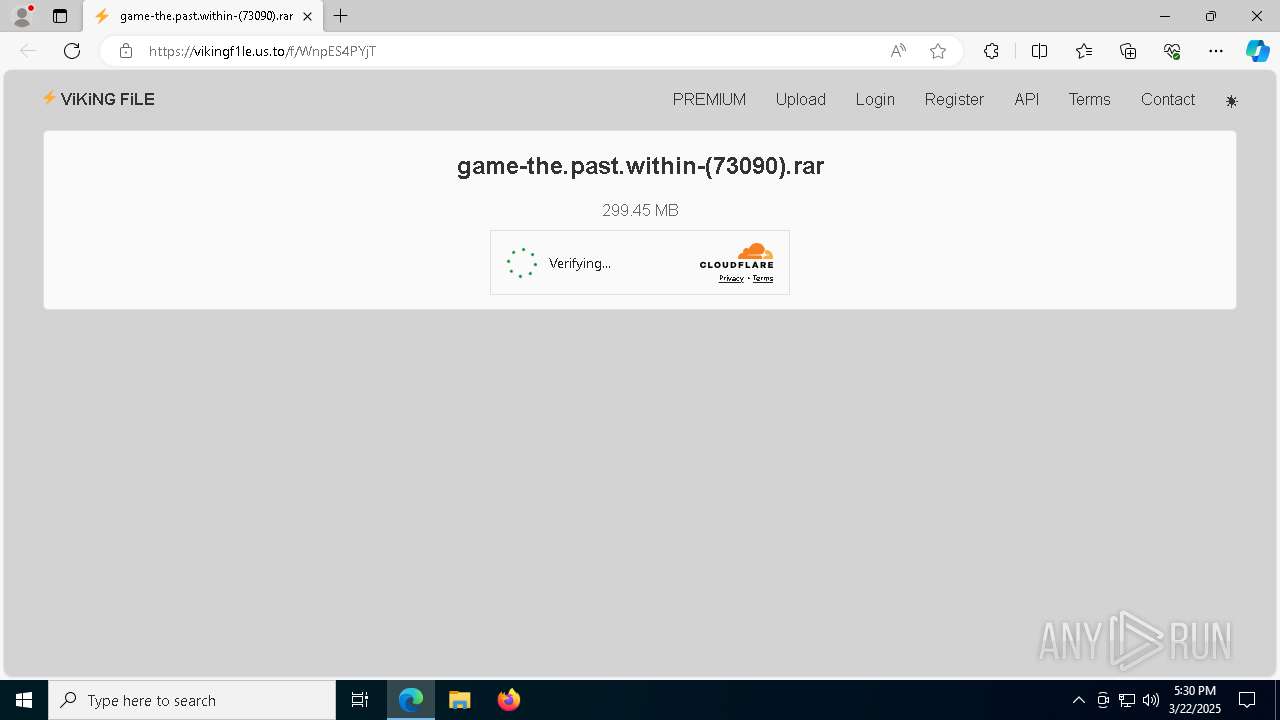
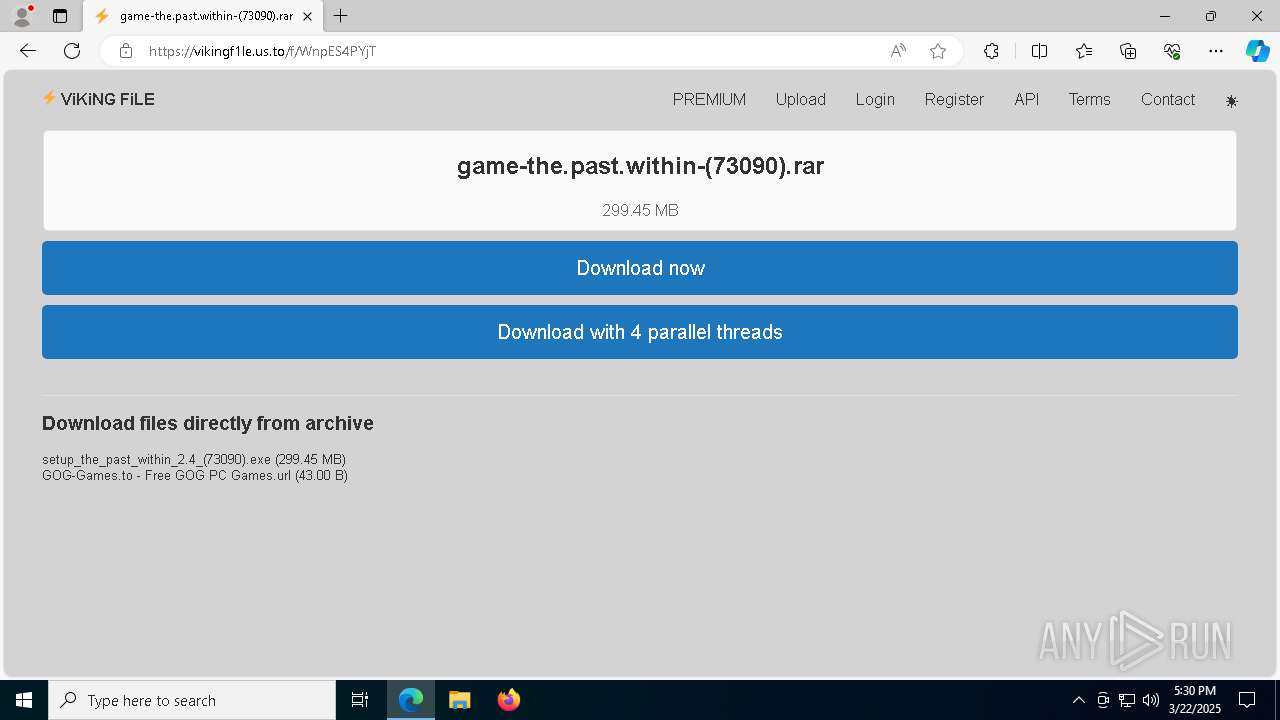
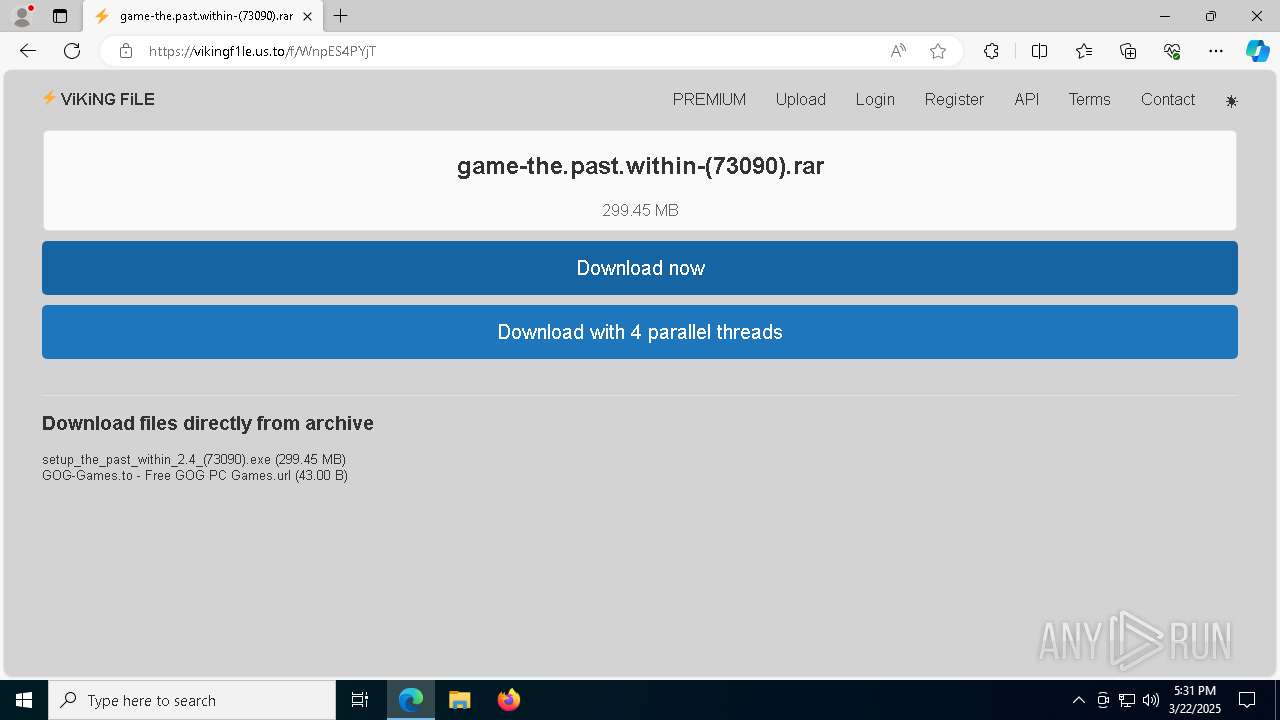
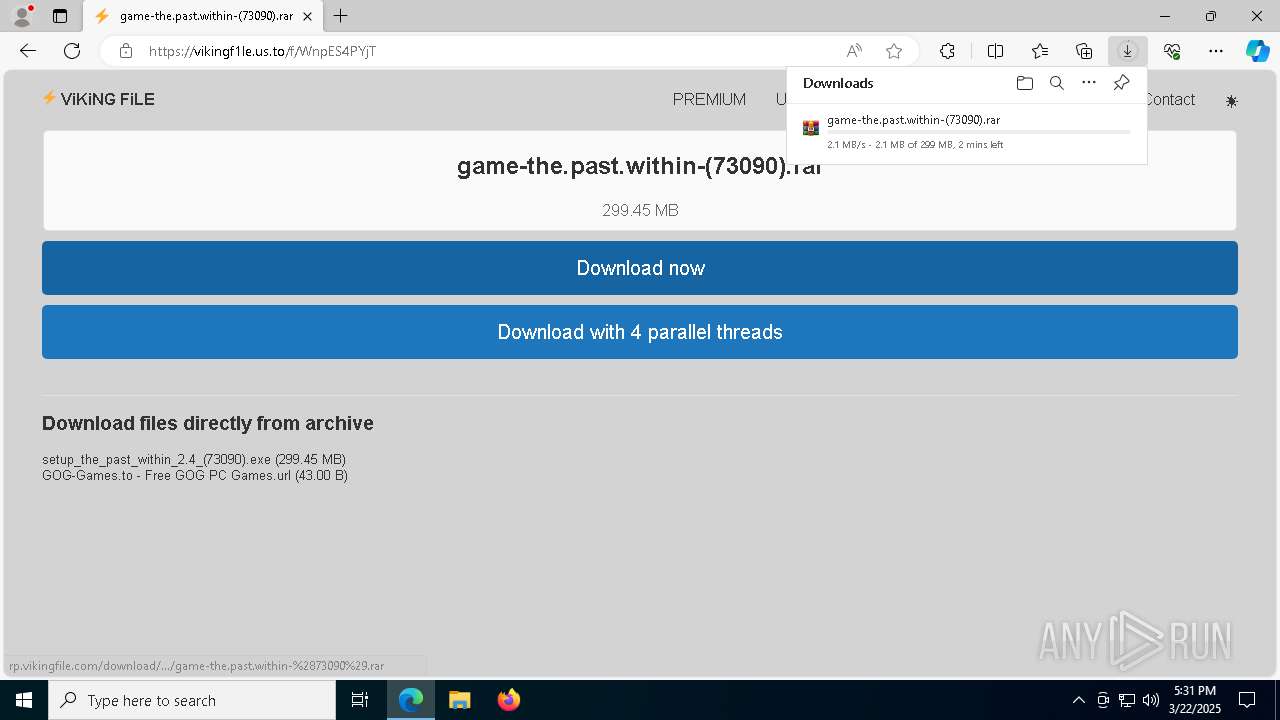
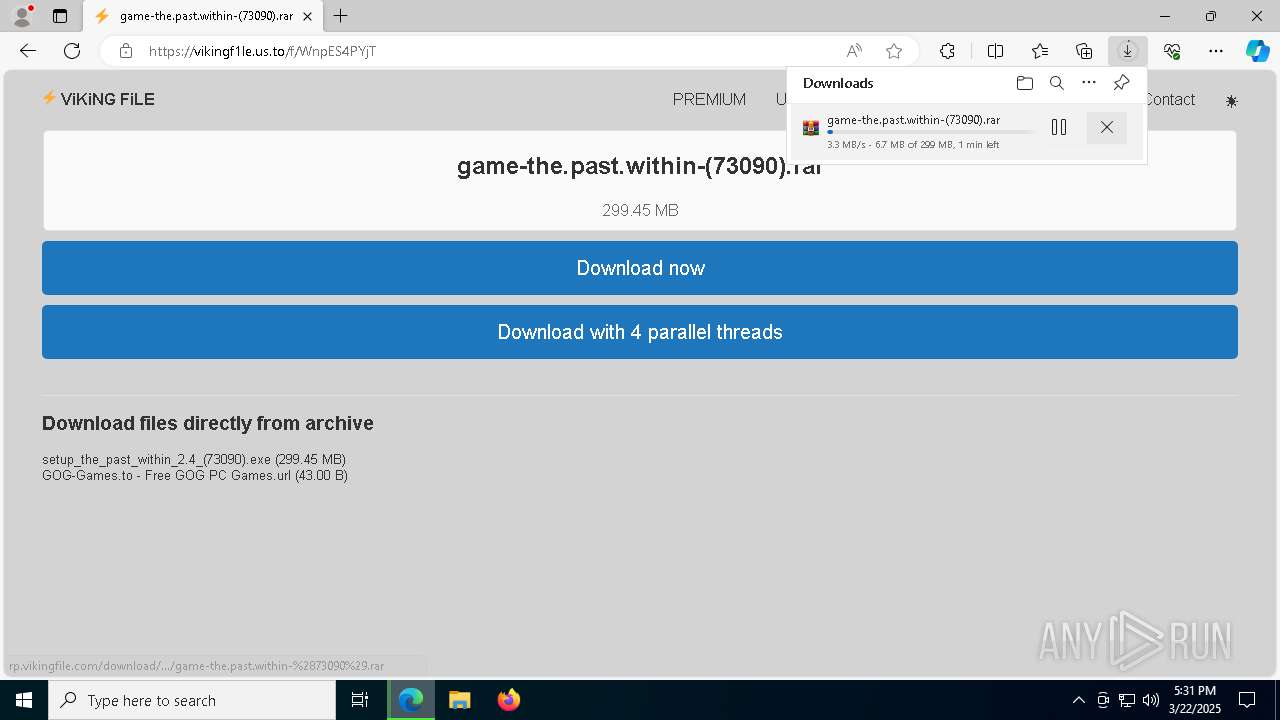
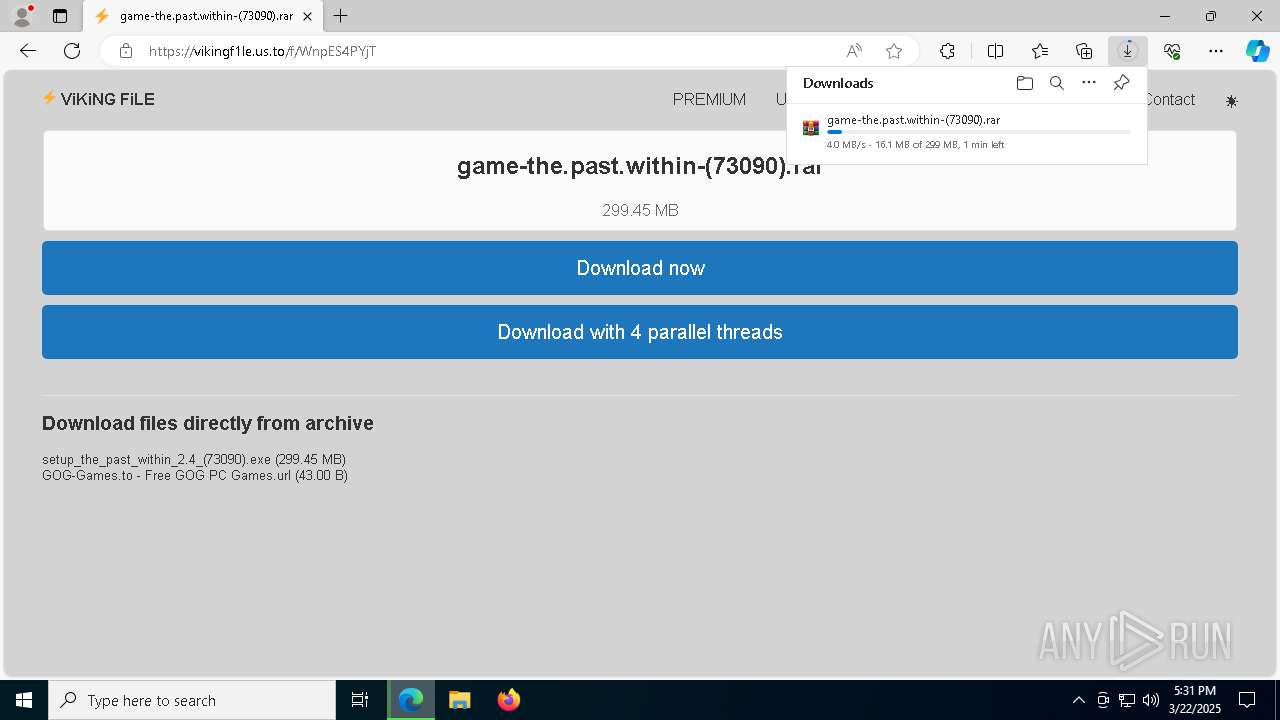
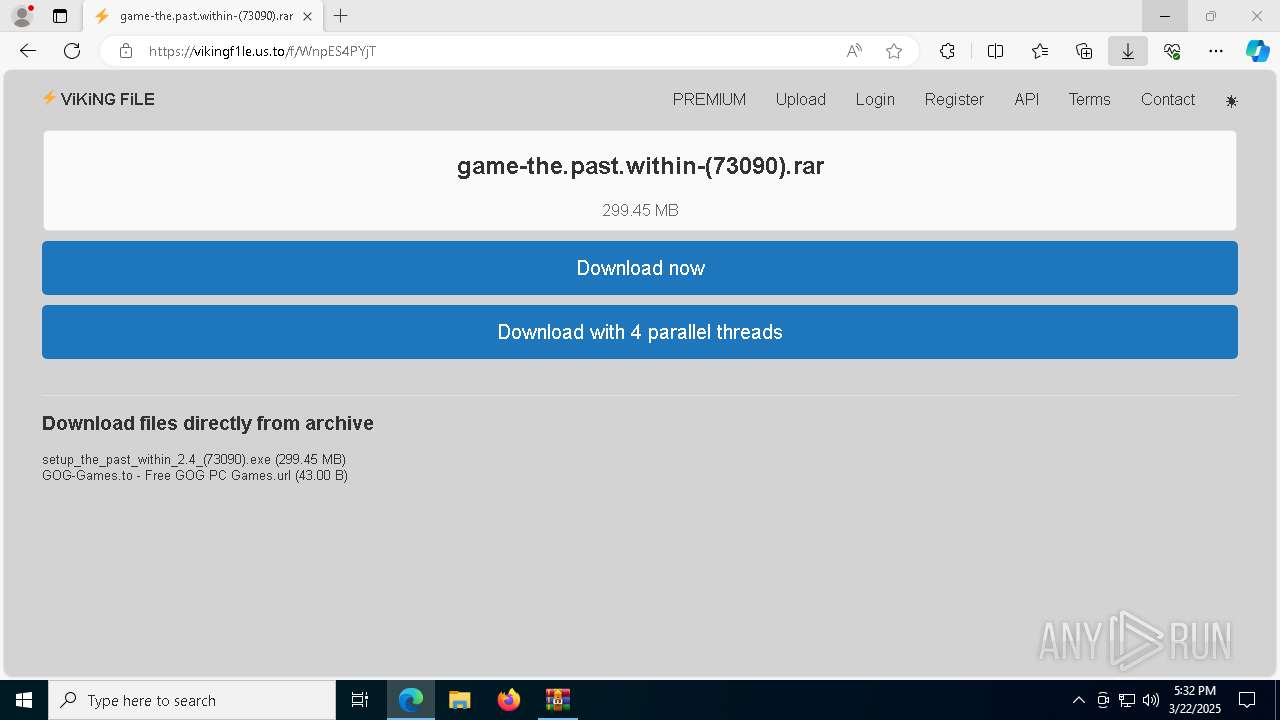
| URL: | https://vikingf1le.us.to/f/WnpES4PYjT |
| Full analysis: | https://app.any.run/tasks/a5d2af7a-c708-400e-9606-e1d74ba92a3f |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2025, 17:30:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
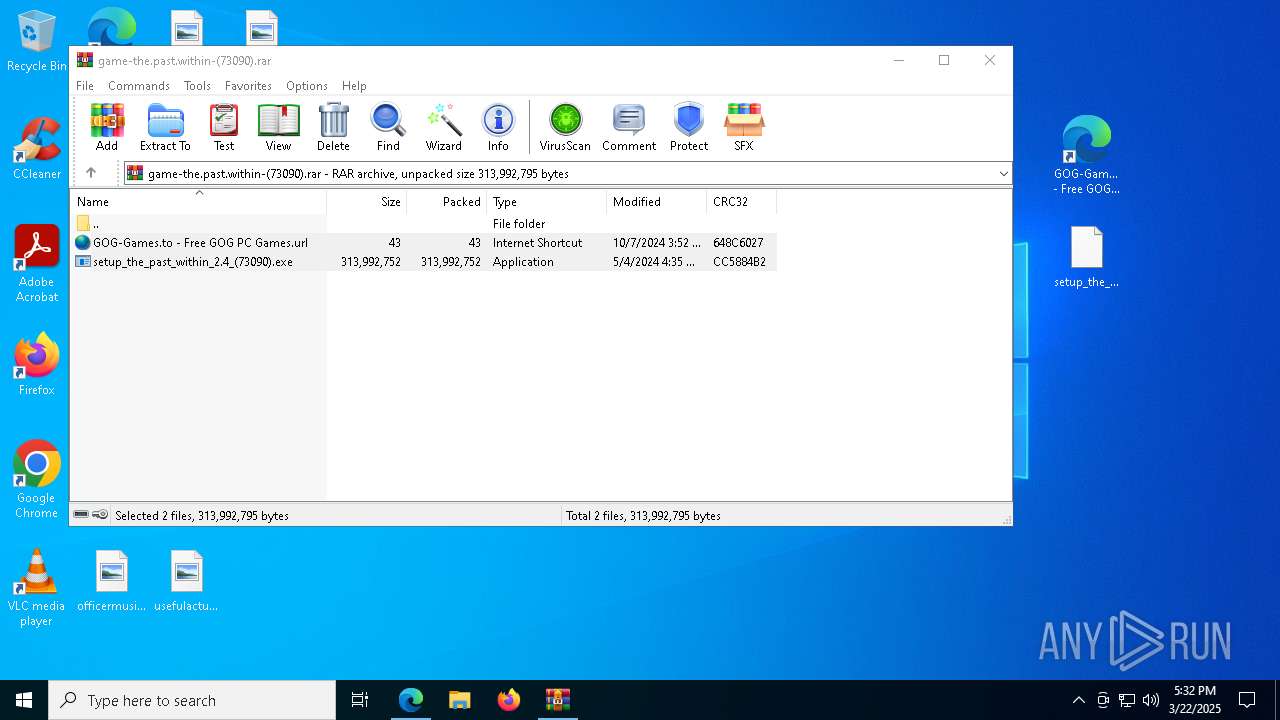
| MD5: | 7154D985726B0E7936C3948EC2C858E2 |
| SHA1: | CED924A53DFFC4B950C1297763C6901745DA31FC |
| SHA256: | F8C698CCBE0478C867D2E1121BD7587F409964D7B9A7EC01F3C07F81D238312B |
| SSDEEP: | 3:N8BMdOjrWyLK2a:2BM0jr1Ra |
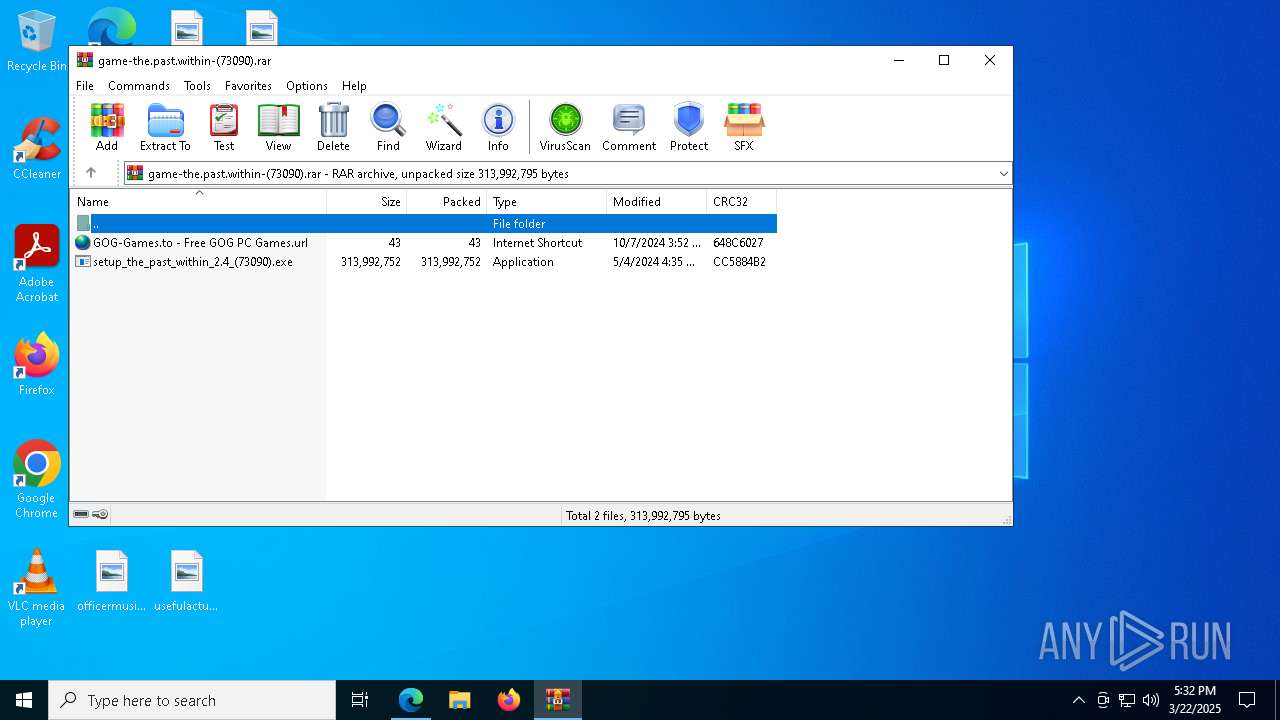
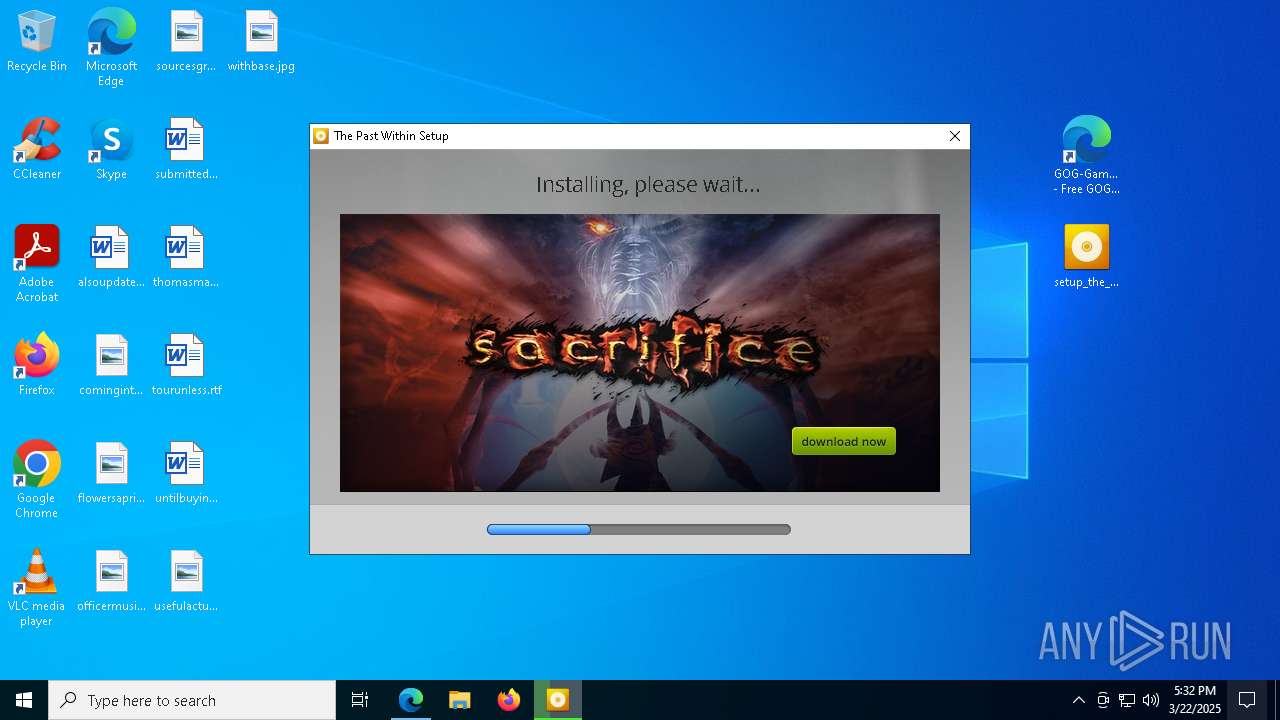
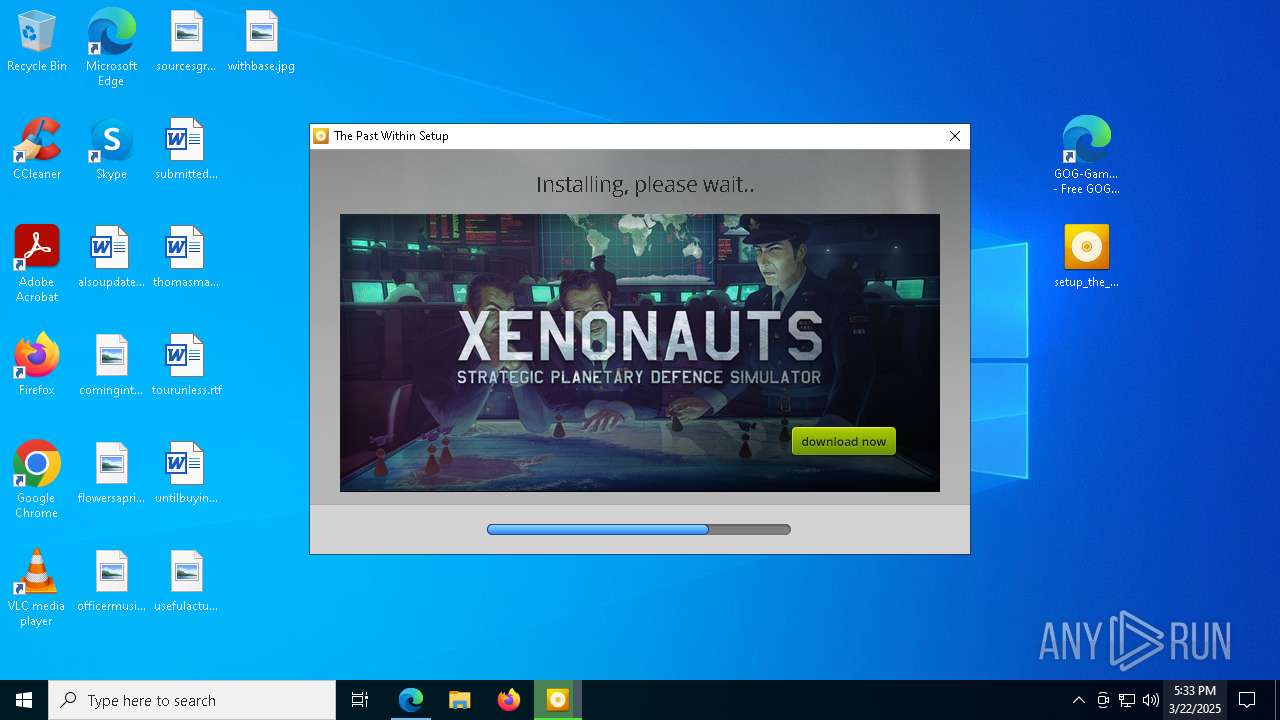
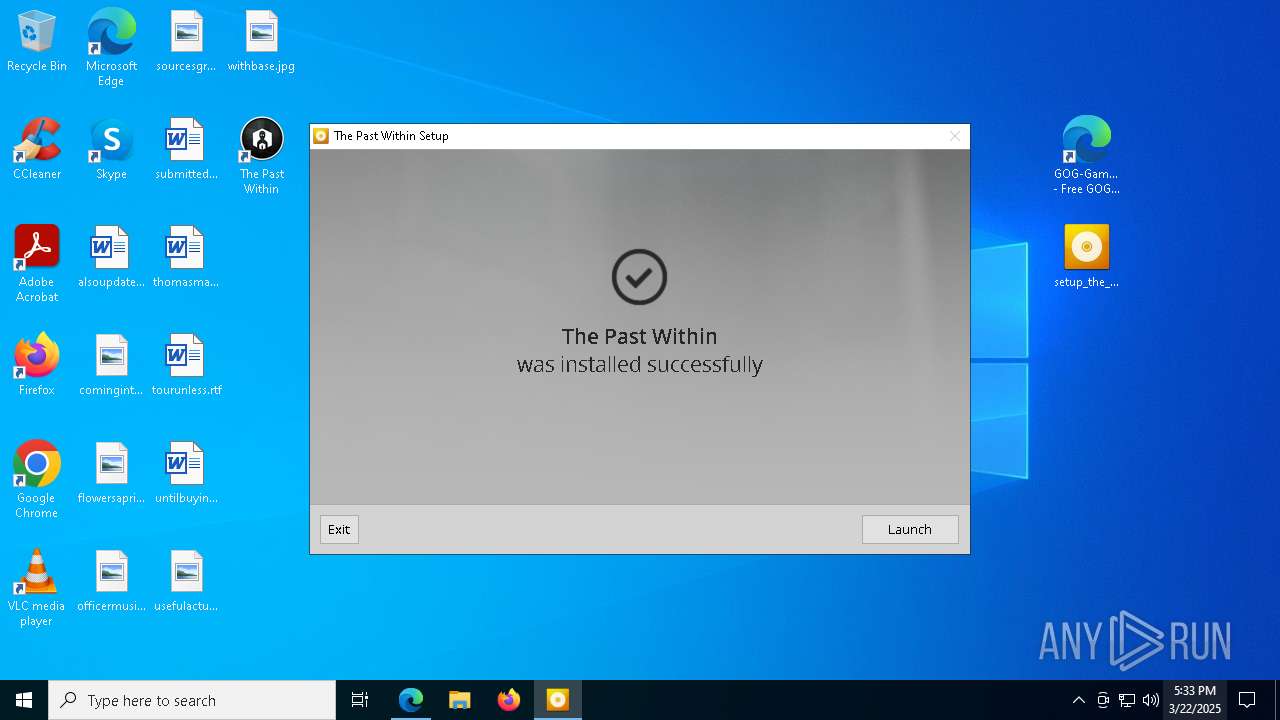
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7384)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8512)
- setup_the_past_within_2.4_(73090).tmp (PID: 960)
- setup_the_past_within_2.4_(73090).tmp (PID: 6712)
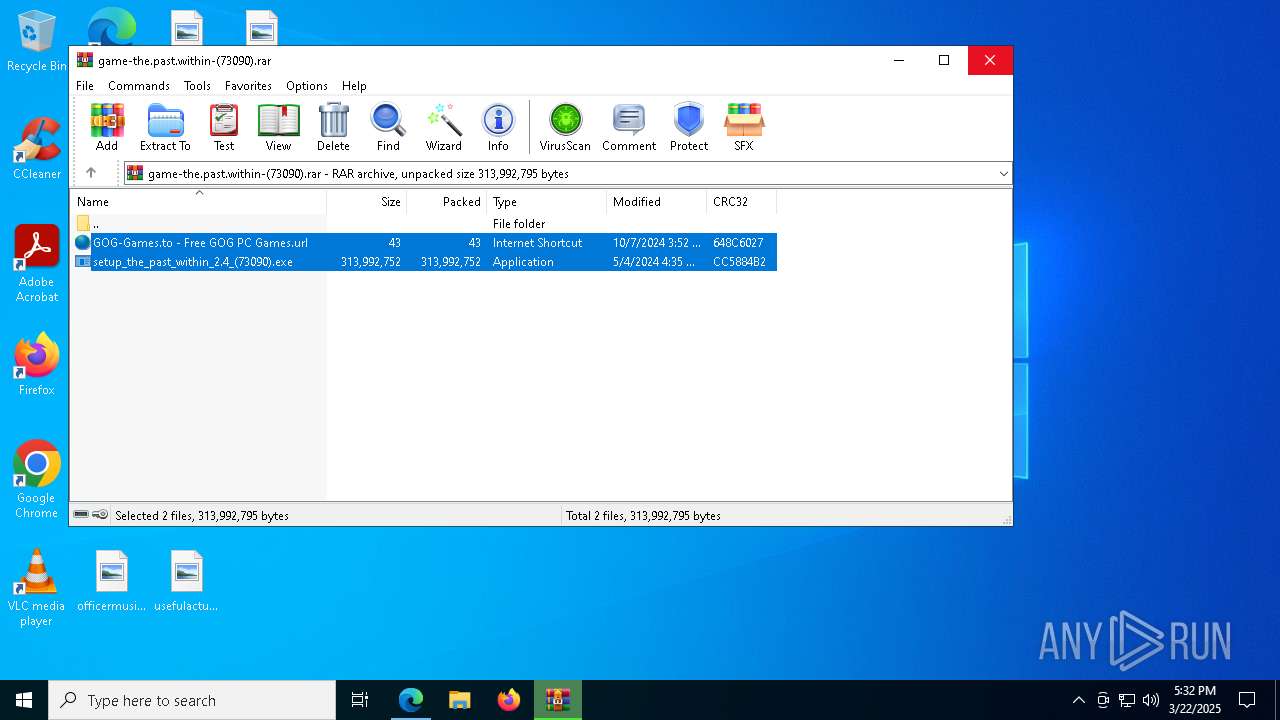
Executable content was dropped or overwritten
- setup_the_past_within_2.4_(73090).exe (PID: 4268)
- setup_the_past_within_2.4_(73090).exe (PID: 664)
- setup_the_past_within_2.4_(73090).tmp (PID: 960)
- scriptinterpreter.exe (PID: 3176)
- scriptInterpreter.tmp (PID: 8392)
Reads the Windows owner or organization settings
- setup_the_past_within_2.4_(73090).tmp (PID: 960)
- scriptInterpreter.tmp (PID: 8392)
There is functionality for taking screenshot (YARA)
- setup_the_past_within_2.4_(73090).tmp (PID: 960)
The process creates files with name similar to system file names
- setup_the_past_within_2.4_(73090).tmp (PID: 960)
Searches for installed software
- scriptInterpreter.tmp (PID: 8392)
Adds/modifies Windows certificates
- The Past Within.exe (PID: 8040)
INFO
Reads the computer name
- identity_helper.exe (PID: 9096)
- setup_the_past_within_2.4_(73090).tmp (PID: 6712)
- setup_the_past_within_2.4_(73090).tmp (PID: 960)
- scriptInterpreter.tmp (PID: 8392)
- The Past Within.exe (PID: 8040)
Reads the software policy settings
- slui.exe (PID: 8368)
- slui.exe (PID: 5776)
- The Past Within.exe (PID: 8040)
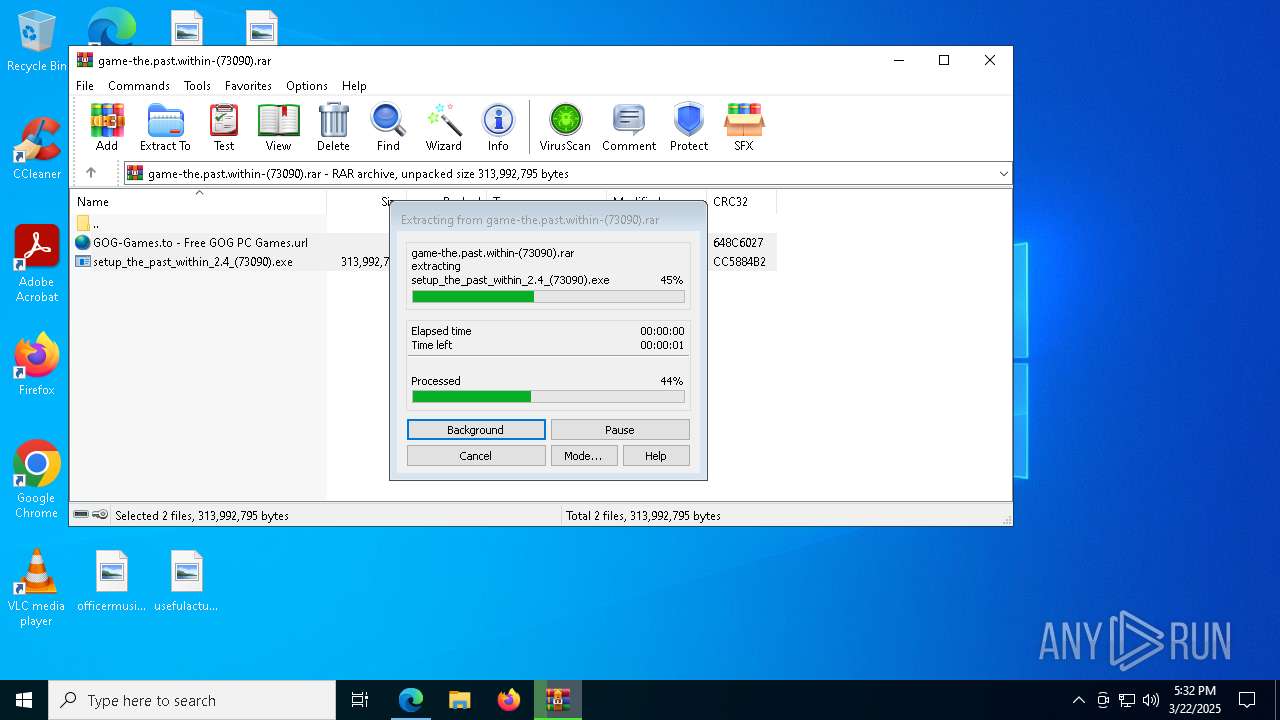
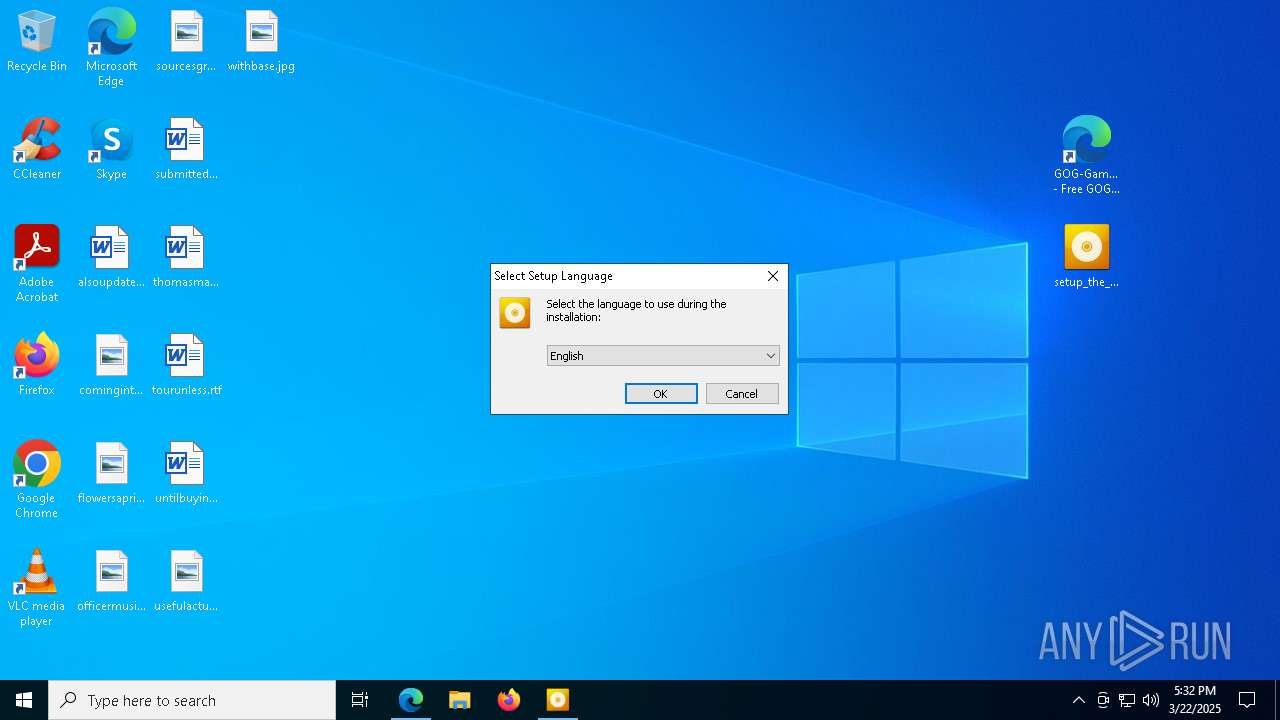
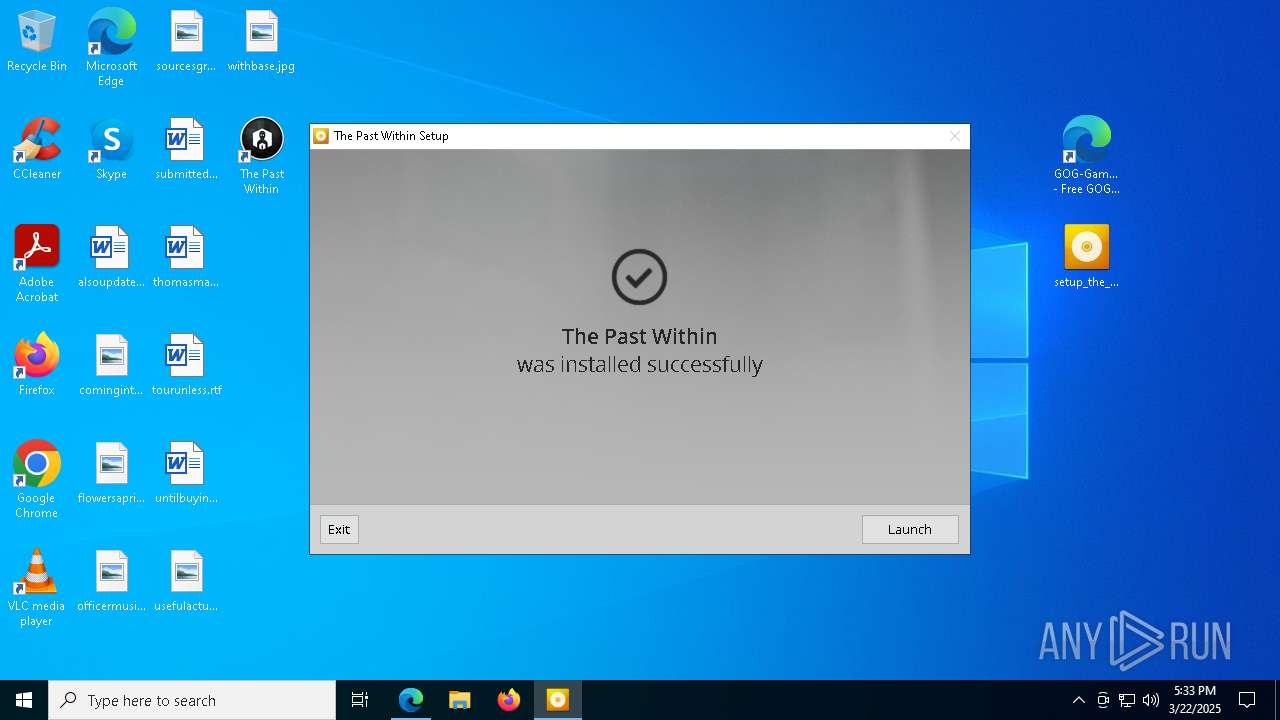
Manual execution by a user
- setup_the_past_within_2.4_(73090).exe (PID: 4268)
Checks supported languages
- identity_helper.exe (PID: 9096)
- setup_the_past_within_2.4_(73090).exe (PID: 4268)
- setup_the_past_within_2.4_(73090).exe (PID: 664)
- setup_the_past_within_2.4_(73090).tmp (PID: 6712)
- setup_the_past_within_2.4_(73090).tmp (PID: 960)
- scriptinterpreter.exe (PID: 3176)
- scriptInterpreter.tmp (PID: 8392)
- The Past Within.exe (PID: 8040)
- UnityCrashHandler64.exe (PID: 9052)
Process checks computer location settings
- setup_the_past_within_2.4_(73090).tmp (PID: 6712)
- setup_the_past_within_2.4_(73090).tmp (PID: 960)
Create files in a temporary directory
- setup_the_past_within_2.4_(73090).exe (PID: 664)
- setup_the_past_within_2.4_(73090).exe (PID: 4268)
- setup_the_past_within_2.4_(73090).tmp (PID: 960)
- scriptInterpreter.tmp (PID: 8392)
- scriptinterpreter.exe (PID: 3176)
- The Past Within.exe (PID: 8040)
Reads Environment values
- identity_helper.exe (PID: 9096)
- The Past Within.exe (PID: 8040)
Reads Microsoft Office registry keys
- msedge.exe (PID: 4200)
Local mutex for internet shortcut management
- WinRAR.exe (PID: 8512)
Application launched itself
- msedge.exe (PID: 4200)
The sample compiled with english language support
- setup_the_past_within_2.4_(73090).tmp (PID: 960)
- scriptInterpreter.tmp (PID: 8392)
- msedge.exe (PID: 8504)
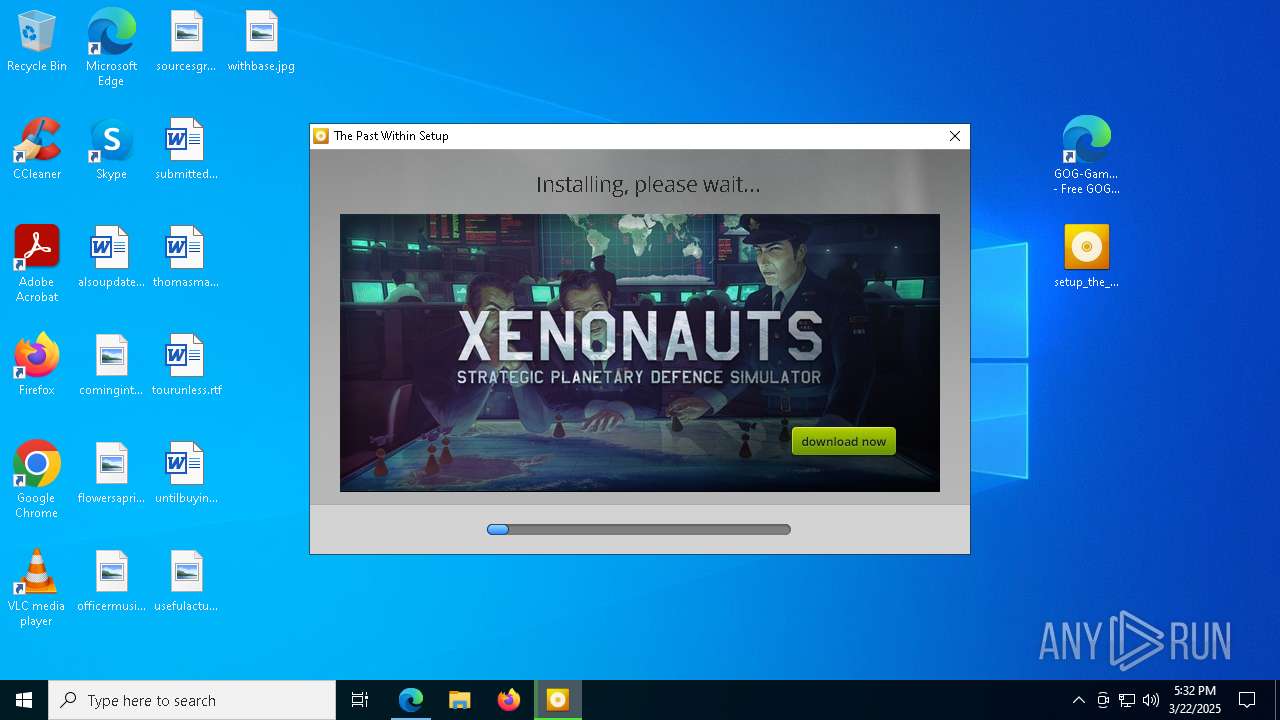
Detects InnoSetup installer (YARA)
- setup_the_past_within_2.4_(73090).tmp (PID: 6712)
- setup_the_past_within_2.4_(73090).exe (PID: 664)
- setup_the_past_within_2.4_(73090).exe (PID: 4268)
- setup_the_past_within_2.4_(73090).tmp (PID: 960)
The sample compiled with russian language support
- setup_the_past_within_2.4_(73090).tmp (PID: 960)
Compiled with Borland Delphi (YARA)
- setup_the_past_within_2.4_(73090).tmp (PID: 6712)
- setup_the_past_within_2.4_(73090).tmp (PID: 960)
- setup_the_past_within_2.4_(73090).exe (PID: 664)
- setup_the_past_within_2.4_(73090).exe (PID: 4268)
Checks proxy server information
- slui.exe (PID: 5776)
- The Past Within.exe (PID: 8040)
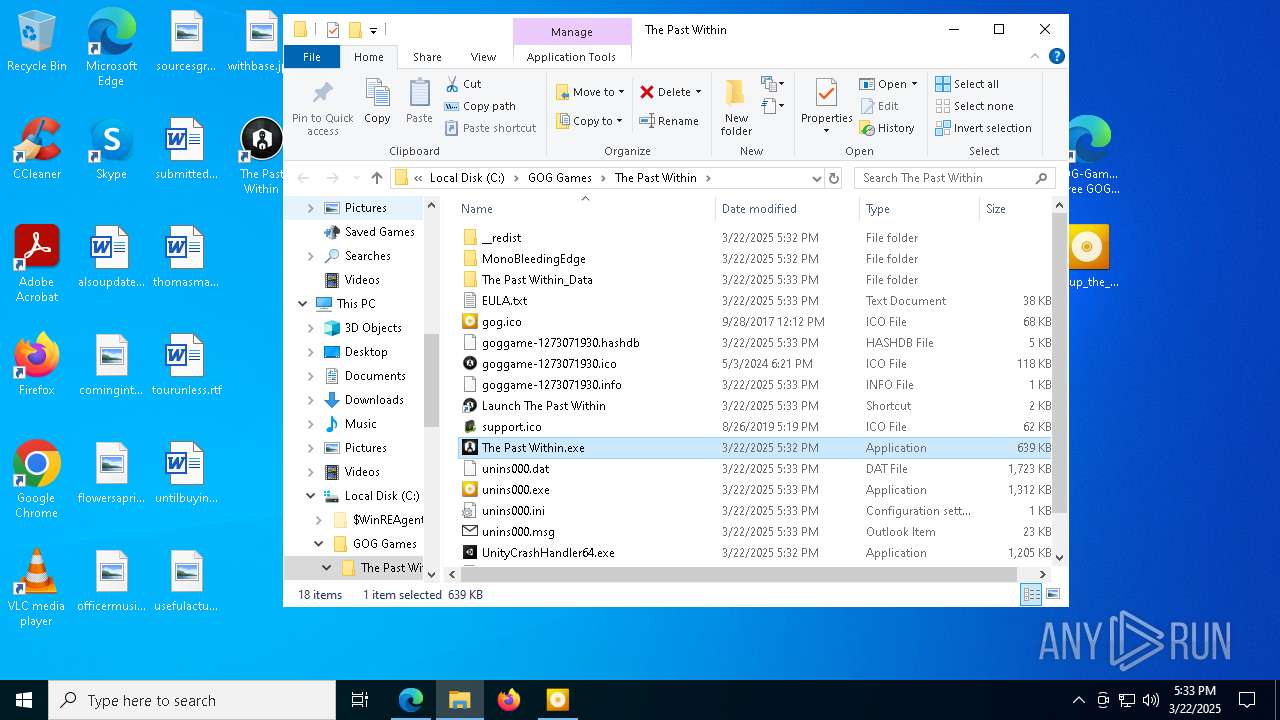
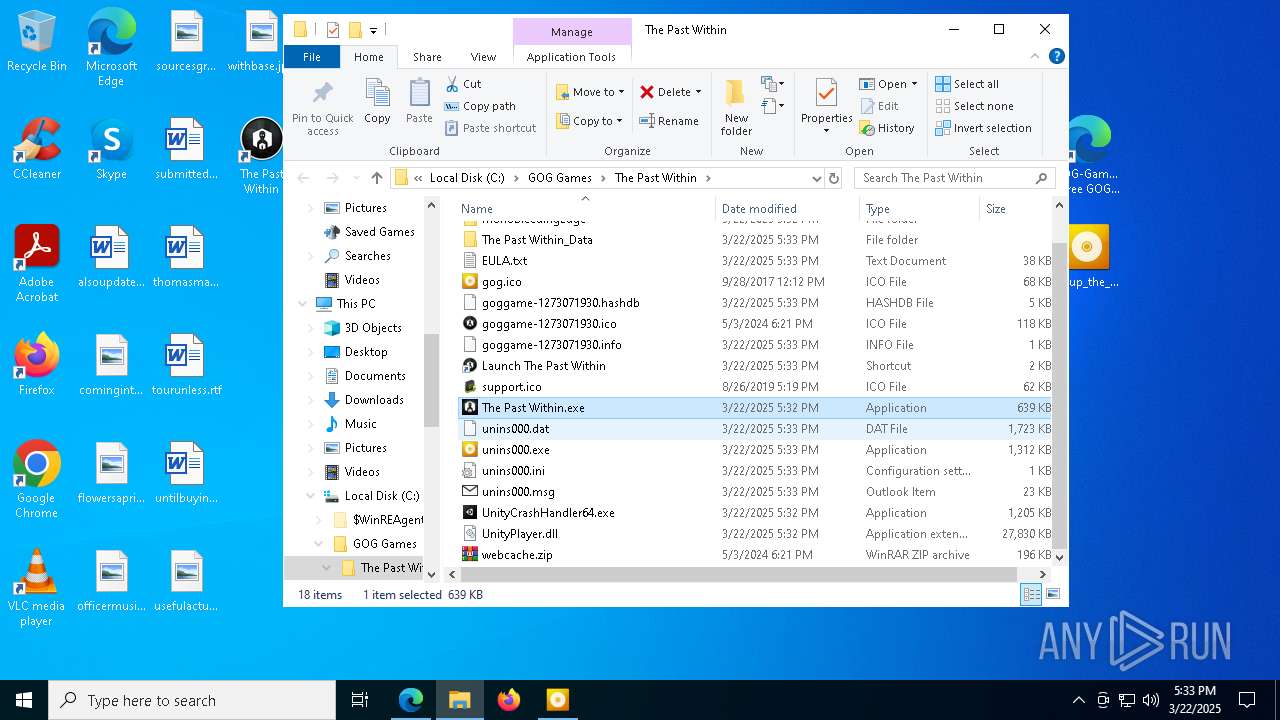
Creates files in the program directory
- setup_the_past_within_2.4_(73090).tmp (PID: 960)
- scriptInterpreter.tmp (PID: 8392)
Creates a software uninstall entry
- scriptInterpreter.tmp (PID: 8392)
- setup_the_past_within_2.4_(73090).tmp (PID: 960)
Reads CPU info
- The Past Within.exe (PID: 8040)
Creates files or folders in the user directory
- The Past Within.exe (PID: 8040)
Reads the time zone
- The Past Within.exe (PID: 8040)
Reads the machine GUID from the registry
- The Past Within.exe (PID: 8040)
Executable content was dropped or overwritten
- msedge.exe (PID: 8504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
218
Monitored processes
73
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Users\admin\Desktop\setup_the_past_within_2.4_(73090).exe" /SPAWNWND=$B014C /NOTIFYWND=$D02DE | C:\Users\admin\Desktop\setup_the_past_within_2.4_(73090).exe | setup_the_past_within_2.4_(73090).tmp | ||||||||||||
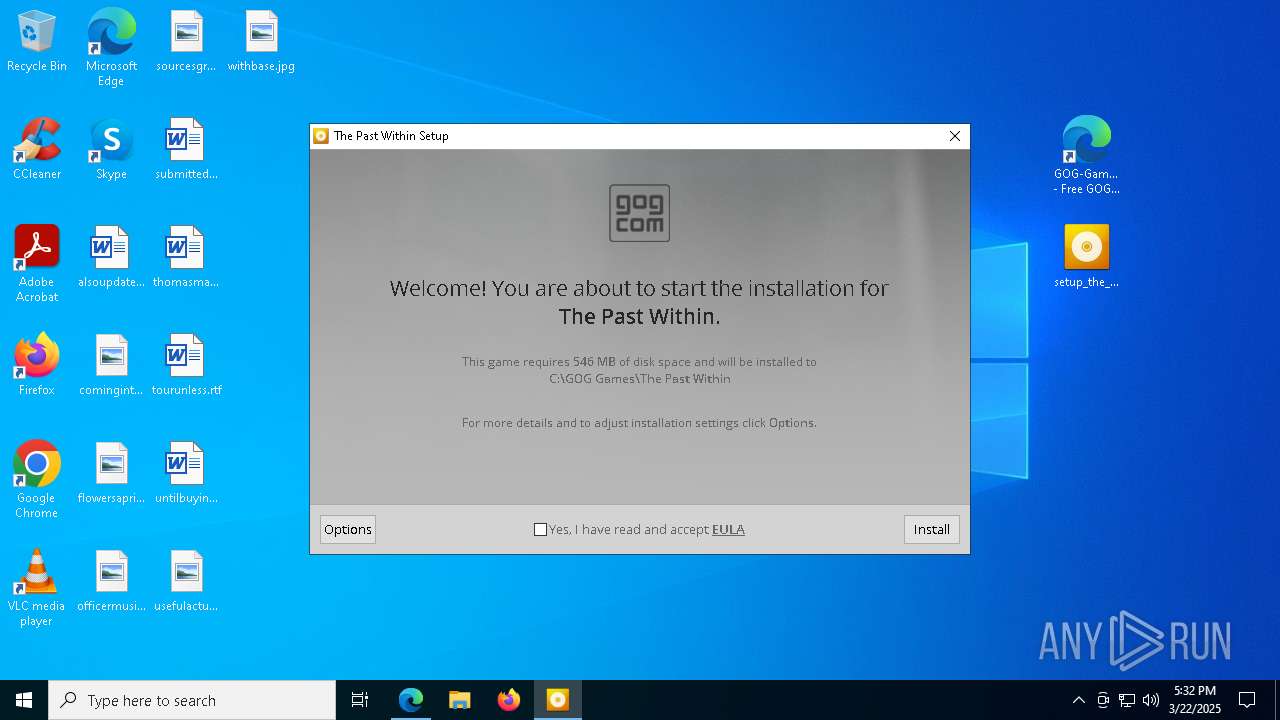
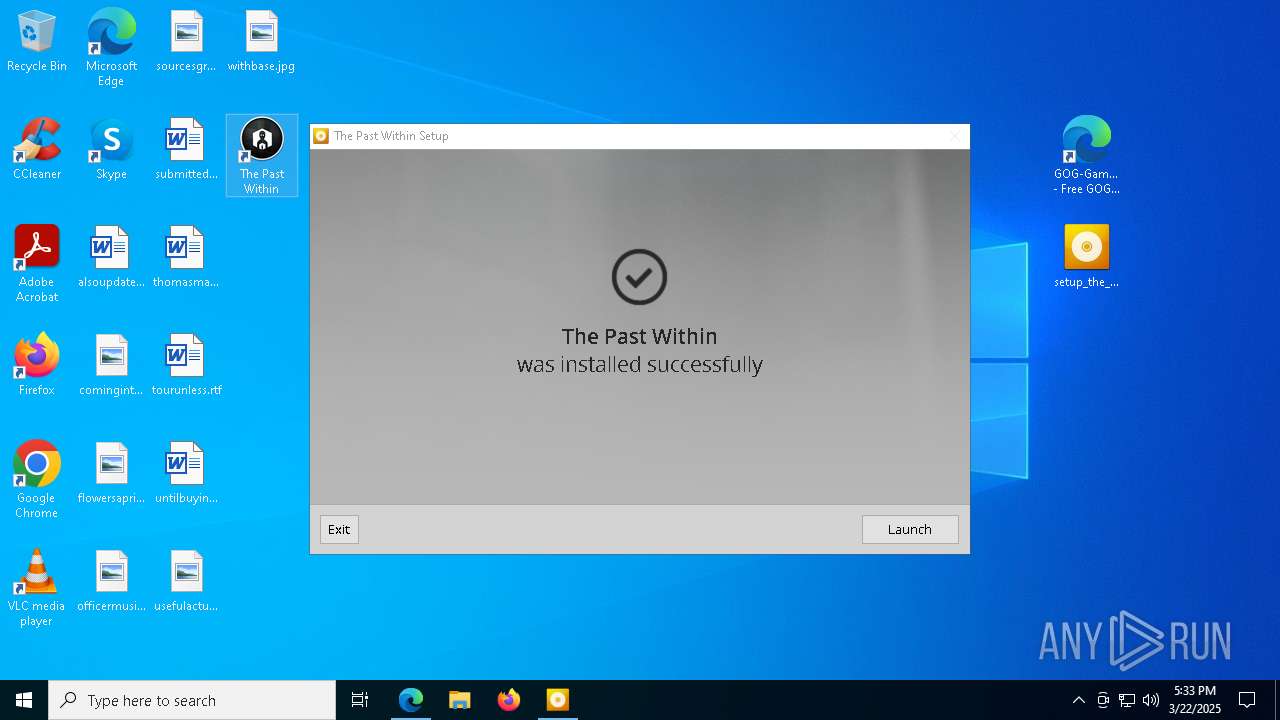
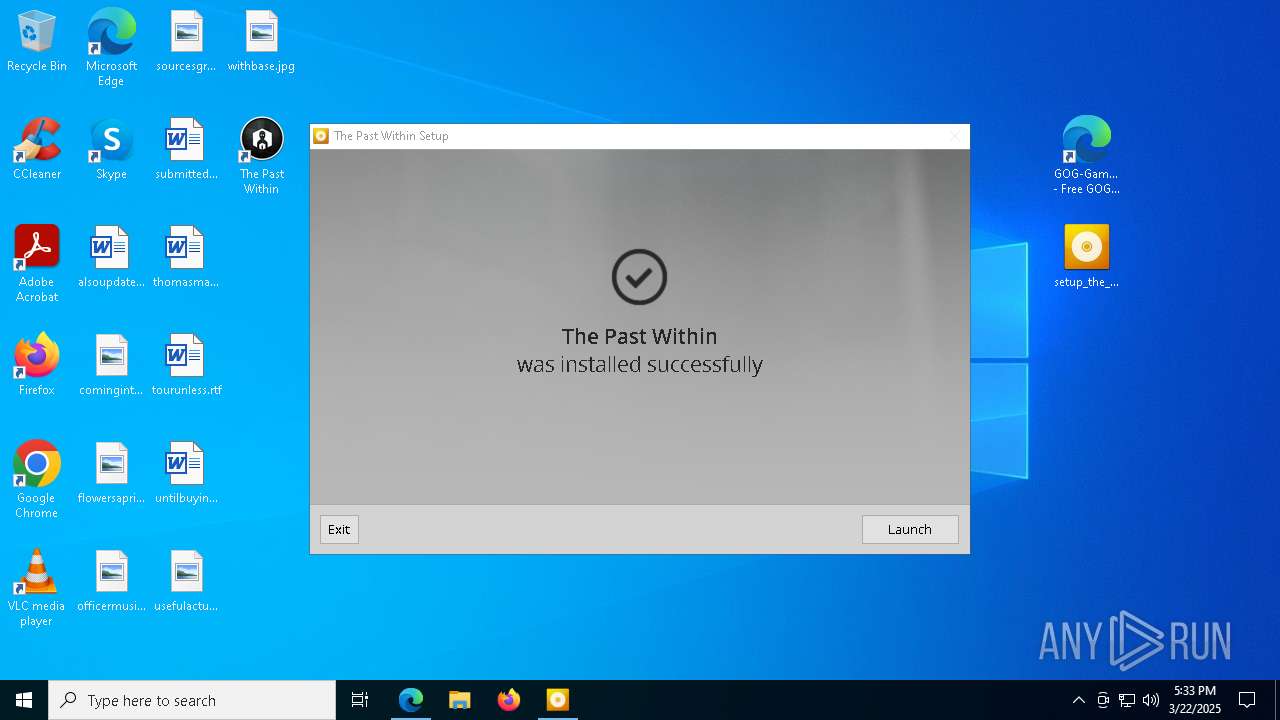
User: admin Company: GOG.com Integrity Level: HIGH Description: The Past Within Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=5496 --field-trial-handle=2516,i,12323661511826064046,16746950033219497387,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6544 --field-trial-handle=2516,i,12323661511826064046,16746950033219497387,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 960 | "C:\Users\admin\AppData\Local\Temp\is-9IJUV.tmp\setup_the_past_within_2.4_(73090).tmp" /SL5="$B0304,313413114,192512,C:\Users\admin\Desktop\setup_the_past_within_2.4_(73090).exe" /SPAWNWND=$B014C /NOTIFYWND=$D02DE | C:\Users\admin\AppData\Local\Temp\is-9IJUV.tmp\setup_the_past_within_2.4_(73090).tmp | setup_the_past_within_2.4_(73090).exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6084 --field-trial-handle=2516,i,12323661511826064046,16746950033219497387,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2284 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --mojo-platform-channel-handle=7144 --field-trial-handle=2516,i,12323661511826064046,16746950033219497387,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2552 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=28 --mojo-platform-channel-handle=3988 --field-trial-handle=2516,i,12323661511826064046,16746950033219497387,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2960 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --mojo-platform-channel-handle=4244 --field-trial-handle=2516,i,12323661511826064046,16746950033219497387,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3176 | "C:\GOG Games\The Past Within\__redist\ISI\scriptInterpreter.exe" /verysilent /supportDir="C:\GOG Games\The Past Within\__support" /SUPPRESSMSGBOXES /NORESTART /DIR="C:\GOG Games\The Past Within" /productId="1273071930" /buildId="57537024706944916" /versionName="2.4" /Language="English" /LANG="english" | C:\GOG Games\The Past Within\__redist\ISI\scriptinterpreter.exe | setup_the_past_within_2.4_(73090).tmp | ||||||||||||
User: admin Company: GOG.com Integrity Level: HIGH Description: GOG.com, scriptIntepreter Exit code: 0 Version: 0.1.2.538 Modules
| |||||||||||||||
| 3896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=6072 --field-trial-handle=2516,i,12323661511826064046,16746950033219497387,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
14 366
Read events
14 198
Write events
159
Delete events
9
Modification events
| (PID) Process: | (4200) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F6169703888F2F00 | |||
| (PID) Process: | (4200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262792 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E8E71046-22C9-4806-B05E-E91A677DD121} | |||
| (PID) Process: | (4200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4200) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BCBC6603888F2F00 | |||
| (PID) Process: | (4200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (4200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
| (PID) Process: | (4200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262792 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {025C4981-6647-4832-BCE7-DE7BD0B0C996} | |||
Executable files
102
Suspicious files
750
Text files
149
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c14e.TMP | — | |
MD5:— | SHA256:— | |||
| 4200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c13e.TMP | — | |
MD5:— | SHA256:— | |||
| 4200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c16d.TMP | — | |
MD5:— | SHA256:— | |||
| 4200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c17d.TMP | — | |
MD5:— | SHA256:— | |||
| 4200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c1fa.TMP | — | |
MD5:— | SHA256:— | |||
| 4200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
94
DNS requests
122
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
9004 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
9004 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3140 | svchost.exe | HEAD | 200 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743003060&P2=404&P3=2&P4=h0kh7%2b%2fmYE%2f1YodWzCGa2NPJV4EPbVqmieKprT9i9XOknEc9MTkazw6FbHTq%2f5z7565QN0r%2flg2Yk%2b81vETZ7A%3d%3d | unknown | — | — | whitelisted |
3140 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743003060&P2=404&P3=2&P4=h0kh7%2b%2fmYE%2f1YodWzCGa2NPJV4EPbVqmieKprT9i9XOknEc9MTkazw6FbHTq%2f5z7565QN0r%2flg2Yk%2b81vETZ7A%3d%3d | unknown | — | — | whitelisted |
3140 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743003060&P2=404&P3=2&P4=h0kh7%2b%2fmYE%2f1YodWzCGa2NPJV4EPbVqmieKprT9i9XOknEc9MTkazw6FbHTq%2f5z7565QN0r%2flg2Yk%2b81vETZ7A%3d%3d | unknown | — | — | whitelisted |
3140 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743003060&P2=404&P3=2&P4=h0kh7%2b%2fmYE%2f1YodWzCGa2NPJV4EPbVqmieKprT9i9XOknEc9MTkazw6FbHTq%2f5z7565QN0r%2flg2Yk%2b81vETZ7A%3d%3d | unknown | — | — | whitelisted |
3140 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743003060&P2=404&P3=2&P4=h0kh7%2b%2fmYE%2f1YodWzCGa2NPJV4EPbVqmieKprT9i9XOknEc9MTkazw6FbHTq%2f5z7565QN0r%2flg2Yk%2b81vETZ7A%3d%3d | unknown | — | — | whitelisted |
3140 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743003060&P2=404&P3=2&P4=h0kh7%2b%2fmYE%2f1YodWzCGa2NPJV4EPbVqmieKprT9i9XOknEc9MTkazw6FbHTq%2f5z7565QN0r%2flg2Yk%2b81vETZ7A%3d%3d | unknown | — | — | whitelisted |
3140 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743003060&P2=404&P3=2&P4=h0kh7%2b%2fmYE%2f1YodWzCGa2NPJV4EPbVqmieKprT9i9XOknEc9MTkazw6FbHTq%2f5z7565QN0r%2flg2Yk%2b81vETZ7A%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6476 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4200 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7384 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7384 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7384 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7384 | msedge.exe | 13.107.246.60:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
vikingf1le.us.to |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7384 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
7384 | msedge.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.us .to Domain |
7384 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
7384 | msedge.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.us .to Domain |
7384 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain by CrossDomain (vikingfile .com) |
7384 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain by CrossDomain (vikingfile .com) |
7384 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7384 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
7384 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
7384 | msedge.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.us .to Domain |