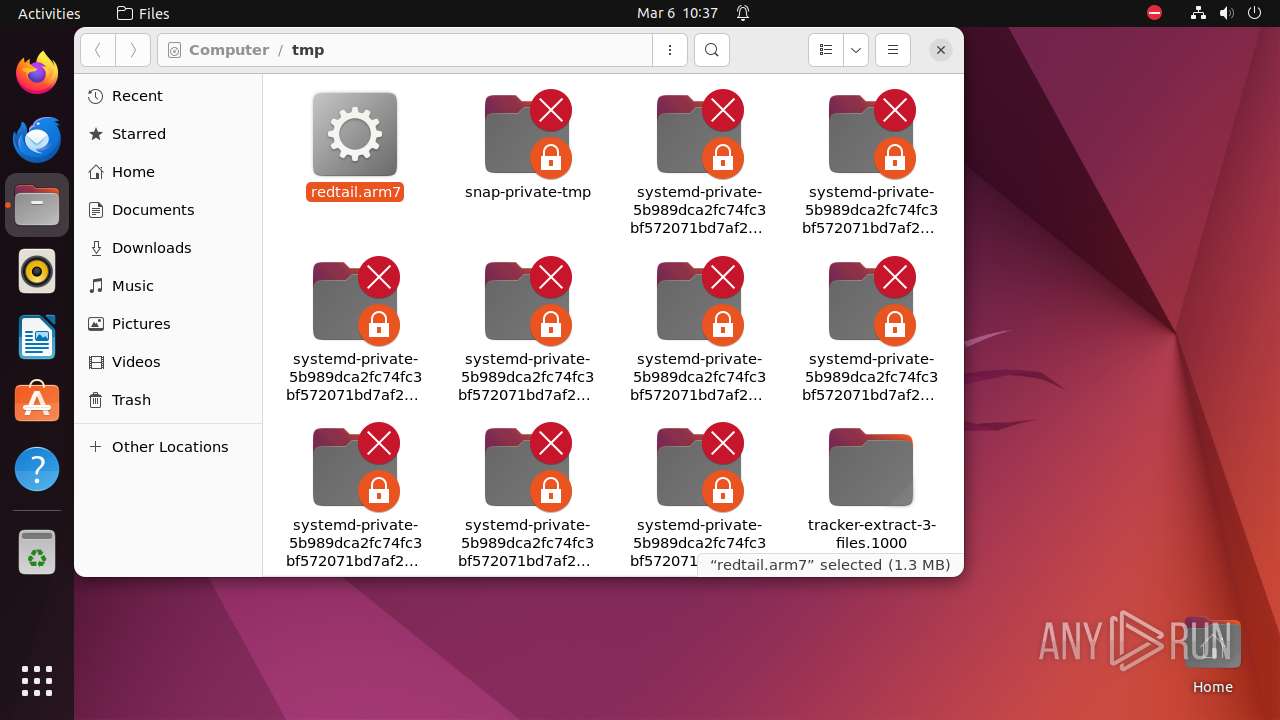
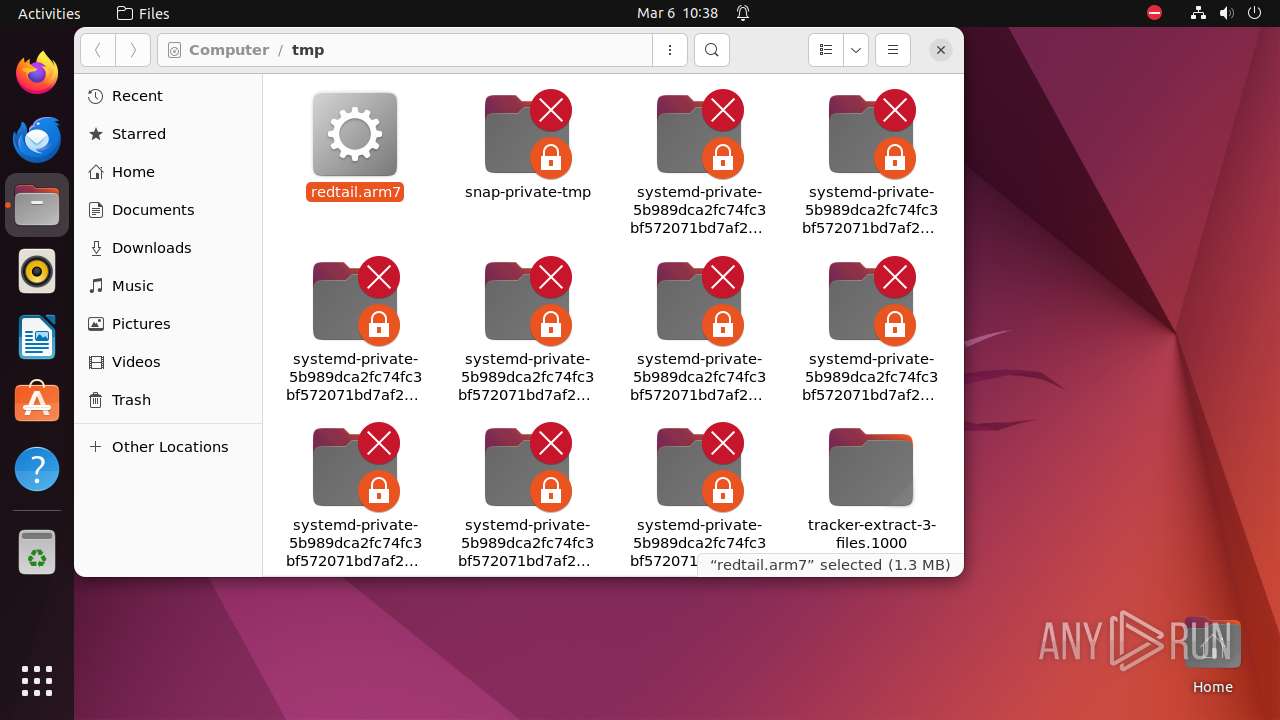
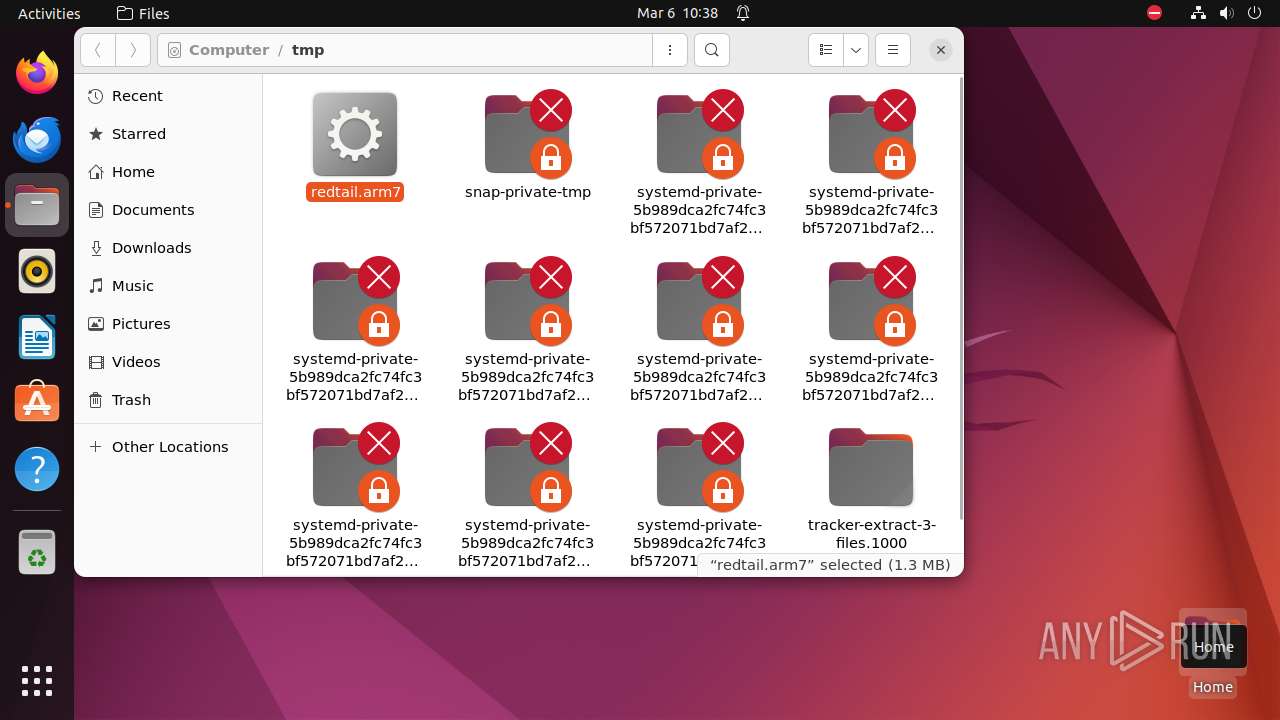
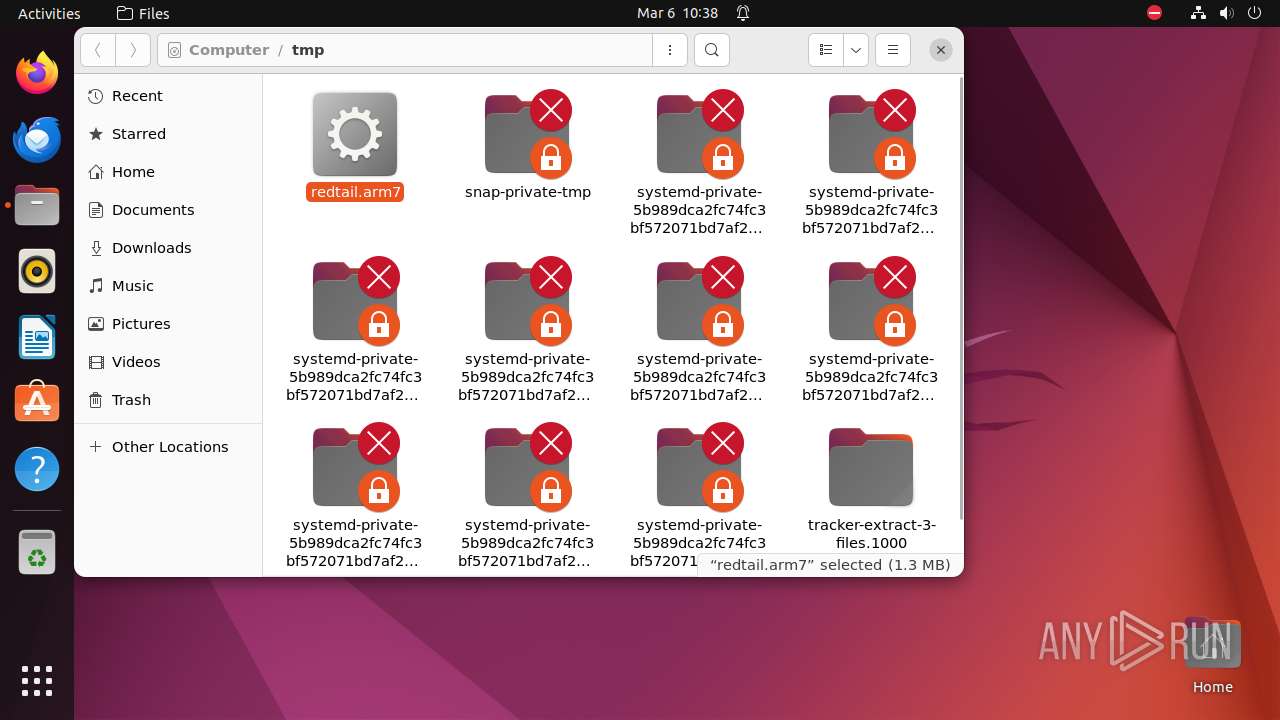
| download: | /download/redtail.arm7 |
| Full analysis: | https://app.any.run/tasks/07f750d8-71c7-4841-8d40-c065c6660e3c |
| Verdict: | Malicious activity |
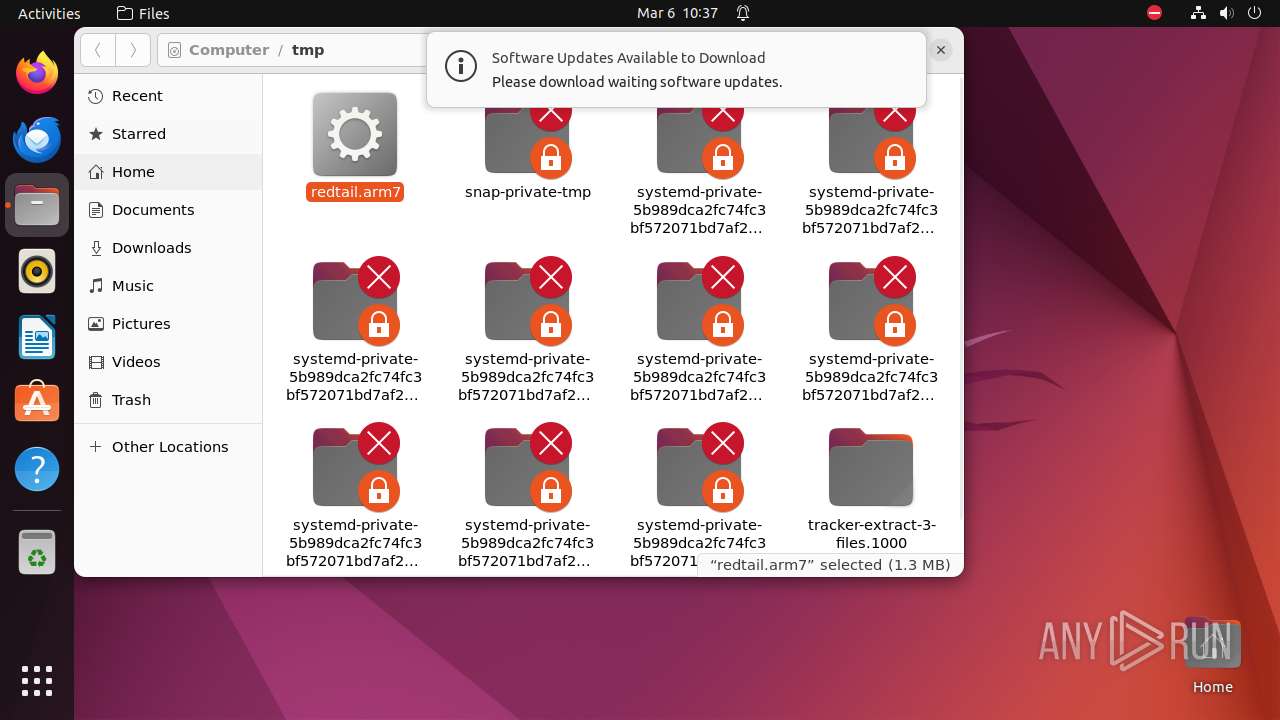
| Analysis date: | March 06, 2024, 10:37:35 |
| OS: | Ubuntu 22.04.2 |
| MIME: | application/x-sharedlib |
| File info: | ELF 32-bit LSB shared object, ARM, EABI5 version 1 (GNU/Linux), statically linked, stripped |
| MD5: | EE0C1CC1BD2875068FDA036E1CA8502A |
| SHA1: | 49FAE78A5BE266576E708AE2E68E475B5F75CA47 |
| SHA256: | F8C18B7511E27D5431752C8CB521BEA3B4048841F331A89E773918BF5E635CFD |
| SSDEEP: | 49152:d0uenCSWUyS97VYgLvoV93CUwR9KiVDnEF7DZFbAI2NrX4qEmA+Anjmo69UcO/M3:2uezWxoY0e933wR9KiVDnExjsI2lIqEA |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes commands using command-line interpreter
- nautilus (PID: 9329)
- nautilus (PID: 9333)
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 9321)
INFO
Manipulating modules (likely to execute programs on system boot)
- modprobe (PID: 9331)
- modprobe (PID: 9335)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .o | | | ELF Executable and Linkable format (generic) (100) |
|---|
EXIF
EXE
| CPUArchitecture: | 32 bit |
|---|---|
| CPUByteOrder: | Little endian |
| ObjectFileType: | Shared object file |
| CPUType: | Unknown (40) |
Total processes
233
Monitored processes
11
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
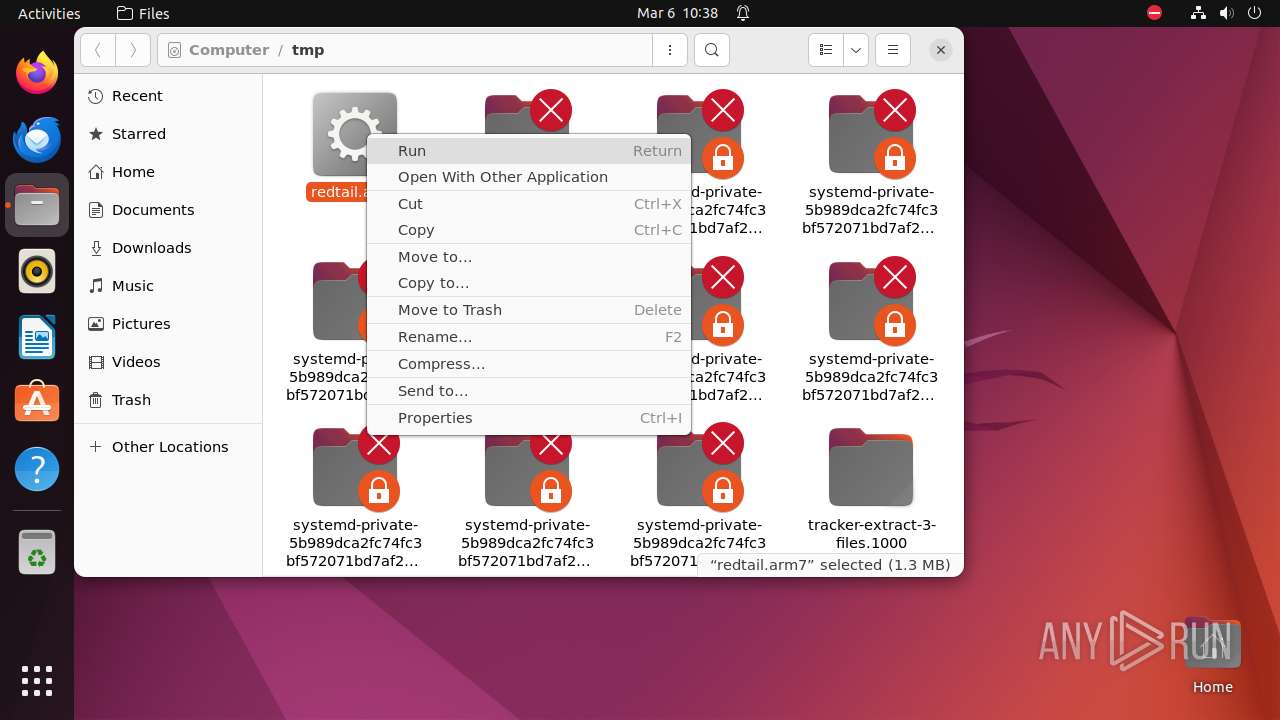
| 9302 | /bin/sh -c "DISPLAY=:0 sudo -iu user nautilus \"/tmp/redtail\.arm7\" " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9303 | sudo -iu user nautilus /tmp/redtail.arm7 | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9304 | nautilus /tmp/redtail.arm7 | /usr/bin/nautilus | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9305 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9321 | /lib/systemd/systemd-hostnamed | /lib/systemd/systemd-hostnamed | — | systemd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9329 | nautilus /tmp/redtail.arm7 | /usr/bin/nautilus | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 1214 | ||||
| 9330 | /bin/sh -e -u -c "export GIO_LAUNCHED_DESKTOP_FILE_PID=\$\$; exec \"\$@\"" sh /tmp/redtail.arm7 | /bin/sh | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 1214 | ||||
| 9331 | /sbin/modprobe -q -- binfmt-464c | /sbin/modprobe | — | u8:4-writeback |
User: root Integrity Level: UNKNOWN Exit code: 1214 | ||||
| 9333 | nautilus /tmp/redtail.arm7 | /usr/bin/nautilus | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 1214 | ||||
| 9334 | /bin/sh -e -u -c "export GIO_LAUNCHED_DESKTOP_FILE_PID=\$\$; exec \"\$@\"" sh /tmp/redtail.arm7 | /bin/sh | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 1214 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 9304 | nautilus | /home/user/.local/share/nautilus/tags/meta.db-wal | — | |
MD5:— | SHA256:— | |||
| 9304 | nautilus | /home/user/.local/share/nautilus/tags/meta.db-shm | — | |
MD5:— | SHA256:— | |||
| 9304 | nautilus | /home/user/.local/share/nautilus/tags/.meta.isrunning | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
9
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.49:80 | — | Canonical Group Limited | GB | unknown |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 195.181.170.19:443 | — | Datacamp Limited | DE | unknown |
— | — | 212.102.56.182:443 | — | Datacamp Limited | DE | unknown |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
119.100.168.192.in-addr.arpa |
| unknown |
api.snapcraft.io |
| unknown |