| File name: | file.exe |
| Full analysis: | https://app.any.run/tasks/a4e673f7-996f-40fe-a940-adfe359dab5b |
| Verdict: | Malicious activity |
| Analysis date: | April 17, 2026, 17:14:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 4 sections |
| MD5: | 2DA285B6DA2E4848042B79011F56F291 |
| SHA1: | 081344B4DBE0844201196FB6836F4AE751F5B23A |
| SHA256: | F8BBE59A29302484EF064B7154D596CC27444DCC017702E88C9BAFE8A15C5A2D |
| SSDEEP: | 1536:imr1zQgnmW/1estc6gAGjhuOc7IAf6zG7SP:imrhQdkwstc6gRjhu4AfAG7S |
MALICIOUS
DUCDUN has been detected (YARA)
- file.exe (PID: 2576)
- file.exe (PID: 2456)
SUSPICIOUS
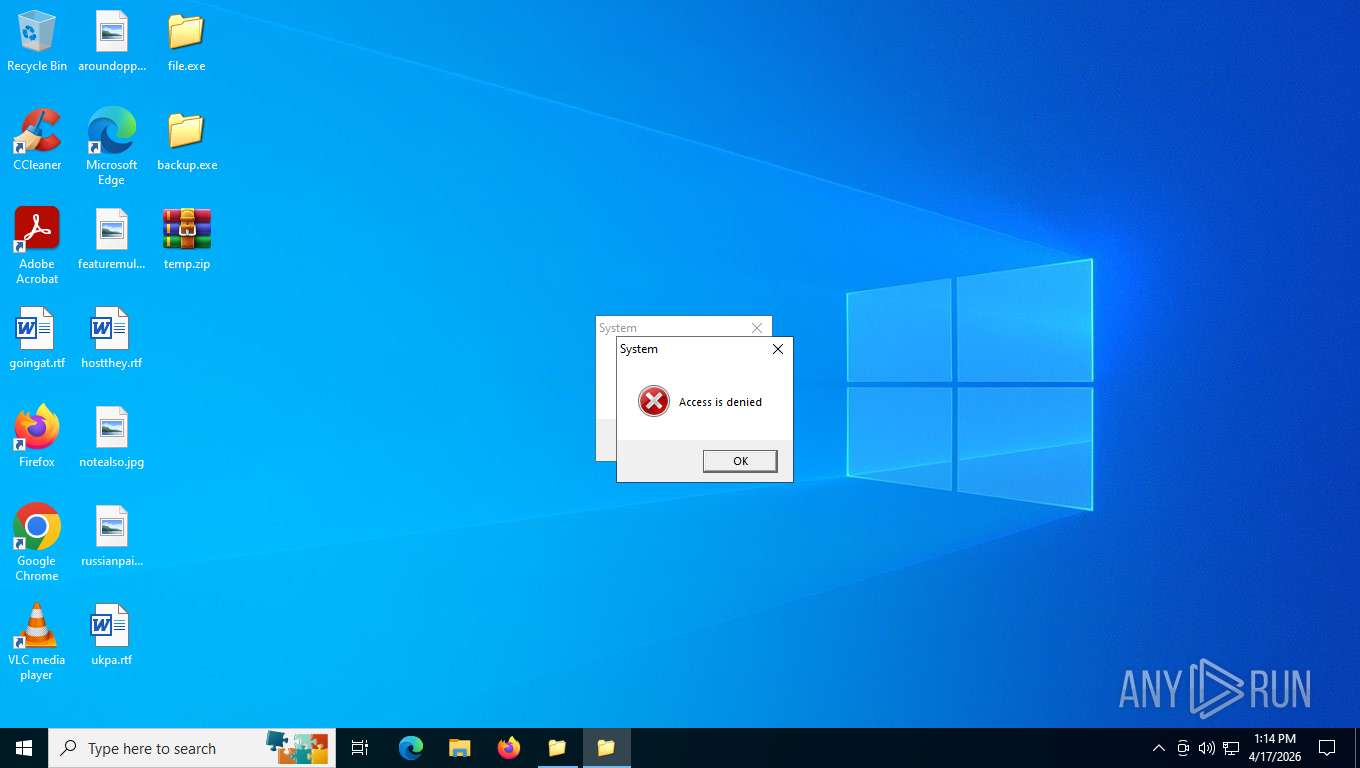
Executable content was dropped or overwritten
- file.exe (PID: 2576)
- file.exe (PID: 2456)
Creates file in the systems drive root
- file.exe (PID: 2576)
- file.exe (PID: 2456)
INFO
Reads the computer name
- file.exe (PID: 2576)
- file.exe (PID: 2456)
Checks supported languages
- file.exe (PID: 2576)
- file.exe (PID: 2456)
Create files in a temporary directory
- file.exe (PID: 2576)
- file.exe (PID: 2456)
The sample compiled with english language support
- file.exe (PID: 2576)
- file.exe (PID: 2456)
Manual execution by a user
- file.exe (PID: 2456)
UPX packer has been detected
- file.exe (PID: 2576)
- file.exe (PID: 2456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (56.4) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (19) |
| .exe | | | UPX compressed Win32 Executable (18.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Generic Win/DOS Executable (1.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:01:06 04:02:14+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 16384 |
| InitializedDataSize: | 24576 |
| UninitializedDataSize: | 65536 |
| EntryPoint: | 0x1150 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.57 |
| ProductVersionNumber: | 1.0.0.57 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | SBC |
| ProductName: | Microsoft Windows |
| FileVersion: | 1.00.0057 |
| ProductVersion: | 1.00.0057 |
| InternalName: | musicvn |
| OriginalFileName: | musicvn.exe |
Total processes
138
Monitored processes
2
Malicious processes
2
Suspicious processes
0
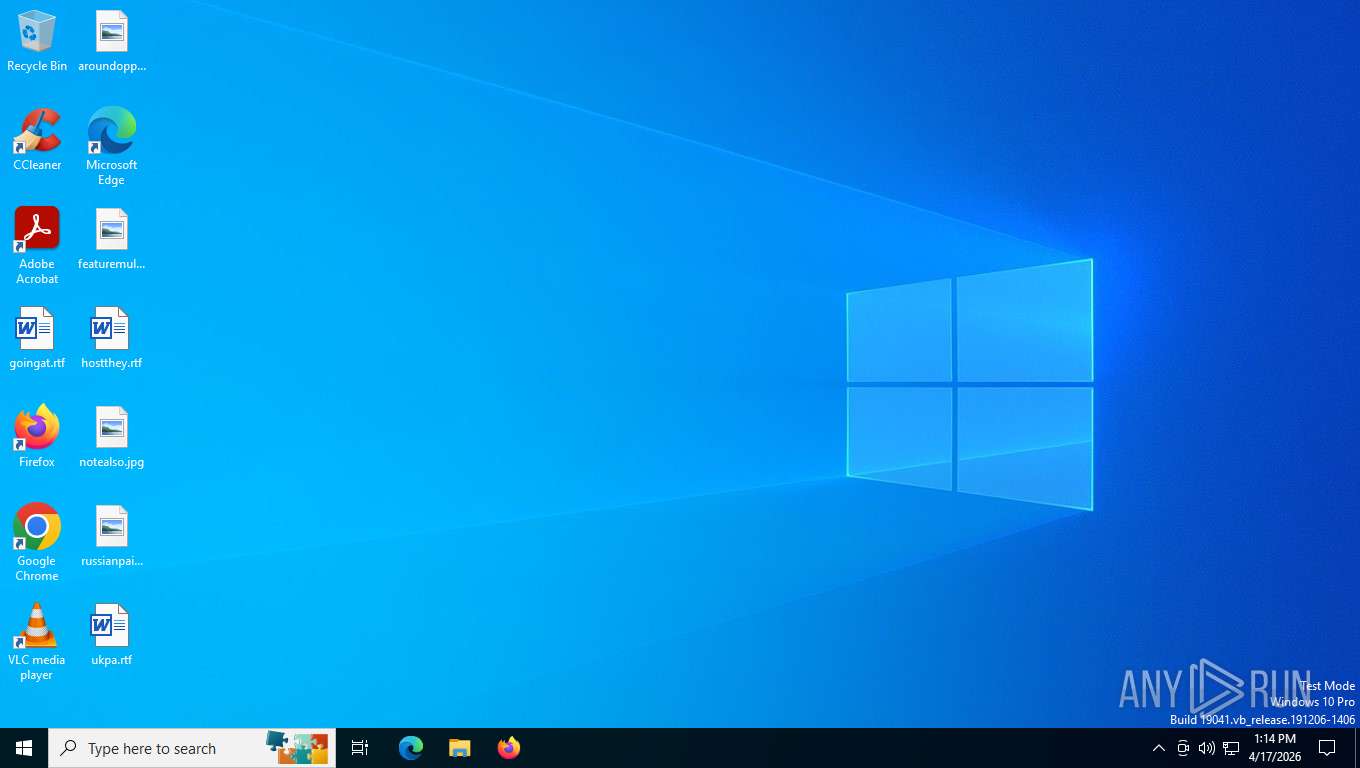
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2456 | "C:\Users\admin\Desktop\file.exe" | C:\Users\admin\Desktop\file.exe | explorer.exe | ||||||||||||
User: admin Company: SBC Integrity Level: MEDIUM Version: 1.00.0057 Modules
| |||||||||||||||
| 2576 | "C:\Users\admin\AppData\Local\Temp\file.exe" | C:\Users\admin\AppData\Local\Temp\file.exe | explorer.exe | ||||||||||||
User: admin Company: SBC Integrity Level: MEDIUM Version: 1.00.0057 Modules
| |||||||||||||||
Total events
419
Read events
415
Write events
2
Delete events
2
Modification events
| (PID) Process: | (2576) file.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoFolderOptions |
Value: 1 | |||
| (PID) Process: | (2576) file.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Streams |
| Operation: | delete value | Name: | Settings |
Value: | |||
| (PID) Process: | (2456) file.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoFolderOptions |
Value: 1 | |||
| (PID) Process: | (2456) file.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Streams |
| Operation: | delete value | Name: | Settings |
Value: | |||
Executable files
2
Suspicious files
12
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2576 | file.exe | C:\Users\admin\AppData\Local\Temp\backup.exe | executable | |
MD5:C03B5682490603E45FC17029928029D3 | SHA256:F2F7429D76D62AA5F2300FD63C08D38FA5FA97A5683D774DCF533800E7C1BB88 | |||
| 2576 | file.exe | C:\Users\admin\AppData\Local\Temp\temp.zip | compressed | |
MD5:76CDB2BAD9582D23C1F6F4D868218D6C | SHA256:8739C76E681F900923B900C9DF0EF75CF421D39CABB54650C4B9AD19B6A76D85 | |||
| 2576 | file.exe | C:\Users\admin\AppData\Local\Temp\temp.zip~RFdfbc5.TMP | compressed | |
MD5:76CDB2BAD9582D23C1F6F4D868218D6C | SHA256:8739C76E681F900923B900C9DF0EF75CF421D39CABB54650C4B9AD19B6A76D85 | |||
| 2456 | file.exe | C:\Users\admin\Desktop\temp.zip | compressed | |
MD5:76CDB2BAD9582D23C1F6F4D868218D6C | SHA256:8739C76E681F900923B900C9DF0EF75CF421D39CABB54650C4B9AD19B6A76D85 | |||
| 2576 | file.exe | C:\Users\admin\AppData\Local\Temp\T3a05616 | compressed | |
MD5:FDF8A396257F9E3FC4D15F30EBBCD048 | SHA256:FD12E412FA1952712EB9CF9CEEE37D1474CD823DDC5E1AE3160362FFB1BB9637 | |||
| 2576 | file.exe | C:\Users\admin\AppData\Local\Temp\file.zip | compressed | |
MD5:BA2D6B1EEB3C4590229436A2C7BA76FA | SHA256:9B71B89DD2E43E50F392D0968DBB8CEC95618B1367E81C7A1BBFE593049B8CAA | |||
| 2576 | file.exe | C:\Users\admin\AppData\Local\Temp\file.dat | binary | |
MD5:FE5DE2F2BC22AC01839B0DF6EA71AC24 | SHA256:BFAF5AA667E151C68D22CEDC0E05AC068037F64151FDC64E4FF775465BD619D7 | |||
| 2456 | file.exe | C:\Users\admin\Desktop\temp.zip~RFe18f2.TMP | compressed | |
MD5:76CDB2BAD9582D23C1F6F4D868218D6C | SHA256:8739C76E681F900923B900C9DF0EF75CF421D39CABB54650C4B9AD19B6A76D85 | |||
| 2456 | file.exe | C:\Users\admin\AppData\Local\Temp\SMa03580 | compressed | |
MD5:4AD0A21A860E9D128A3D03F28574413A | SHA256:9C4D851B98FF360FBCEA7CCDEE439509E1193F6628388BD0C196F60B8D5CC6B0 | |||
| 2456 | file.exe | C:\Users\admin\Desktop\backup.exe | executable | |
MD5:FB9AF1D0D568A2427719A8978E201466 | SHA256:892C4A05CED051C3BA4D9504282A0C939415FBAB808E5C50F34CF68B2CFD5AF2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
24
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
4712 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
5532 | SearchApp.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | NL | binary | 312 b | whitelisted |
4712 | SIHClient.exe | GET | 200 | 74.179.77.164:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
4712 | SIHClient.exe | GET | 200 | 74.179.77.204:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
4712 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
5532 | SearchApp.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 959 b | whitelisted |
5316 | svchost.exe | POST | 200 | 20.190.160.22:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | whitelisted |
5484 | svchost.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
5316 | svchost.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | NL | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5484 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5484 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5484 | svchost.exe | 23.216.77.34:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5484 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3428 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | SearchApp.exe | 2.16.204.145:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5484 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |