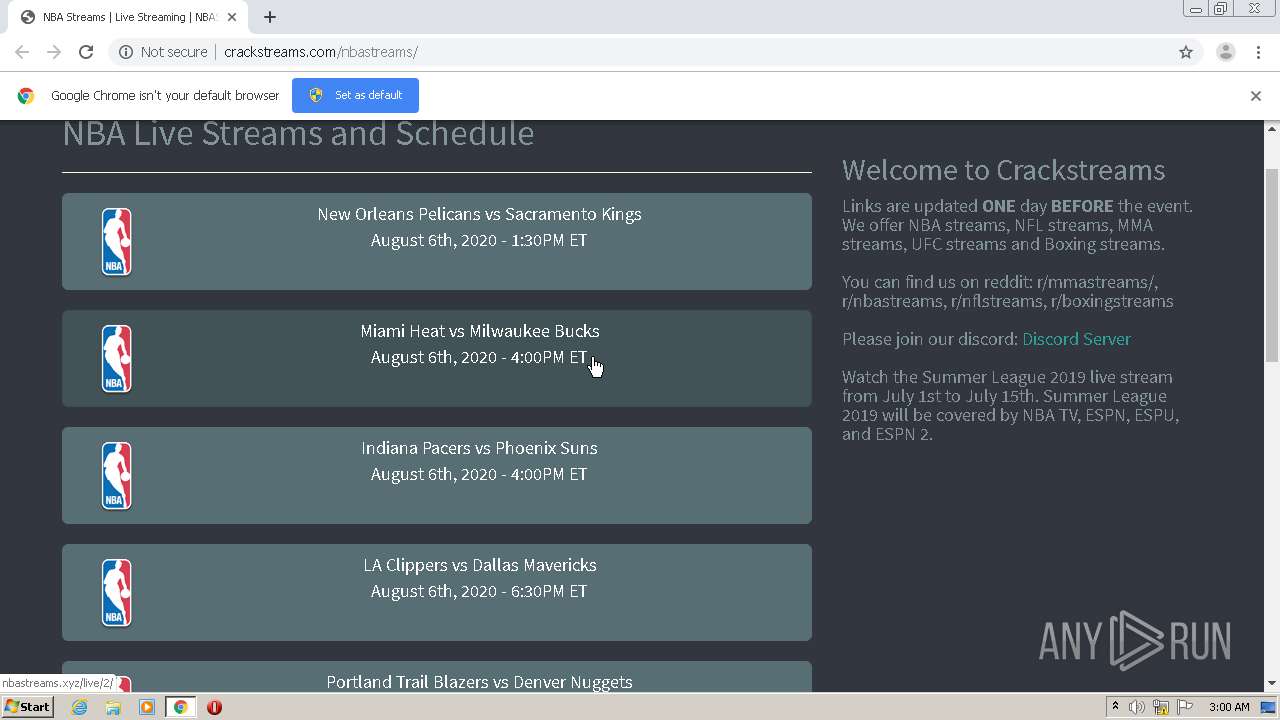
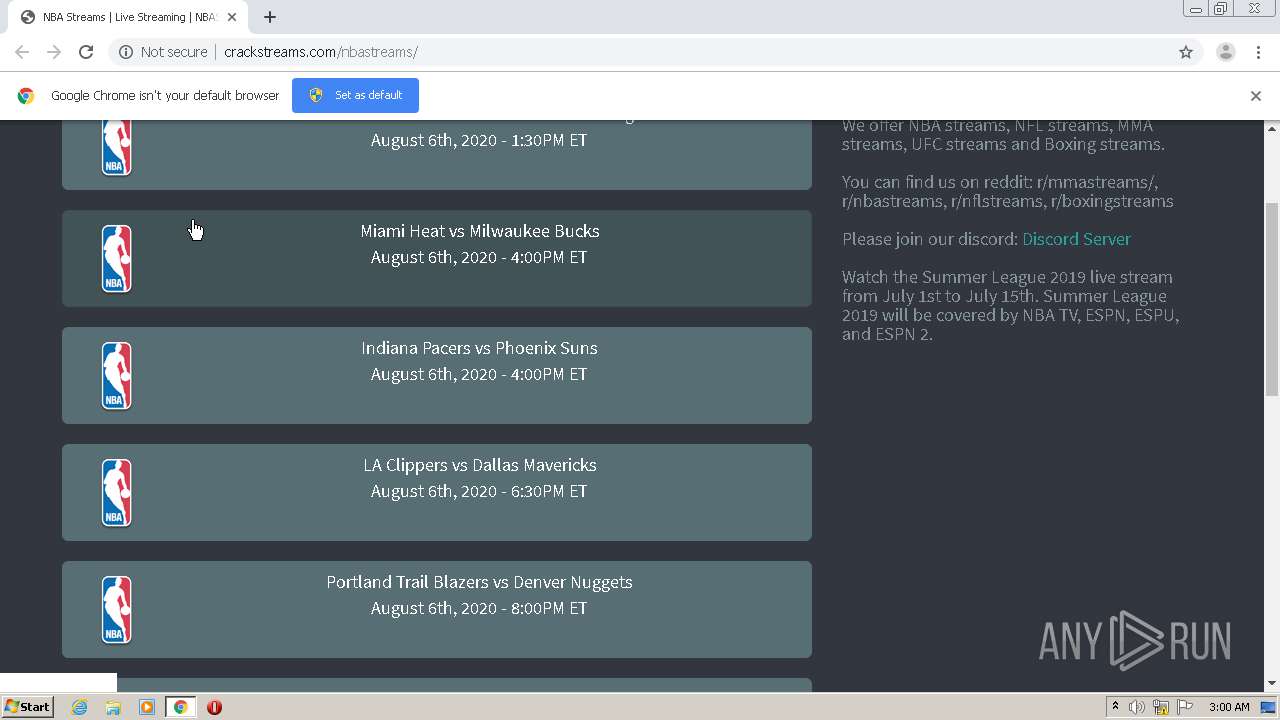
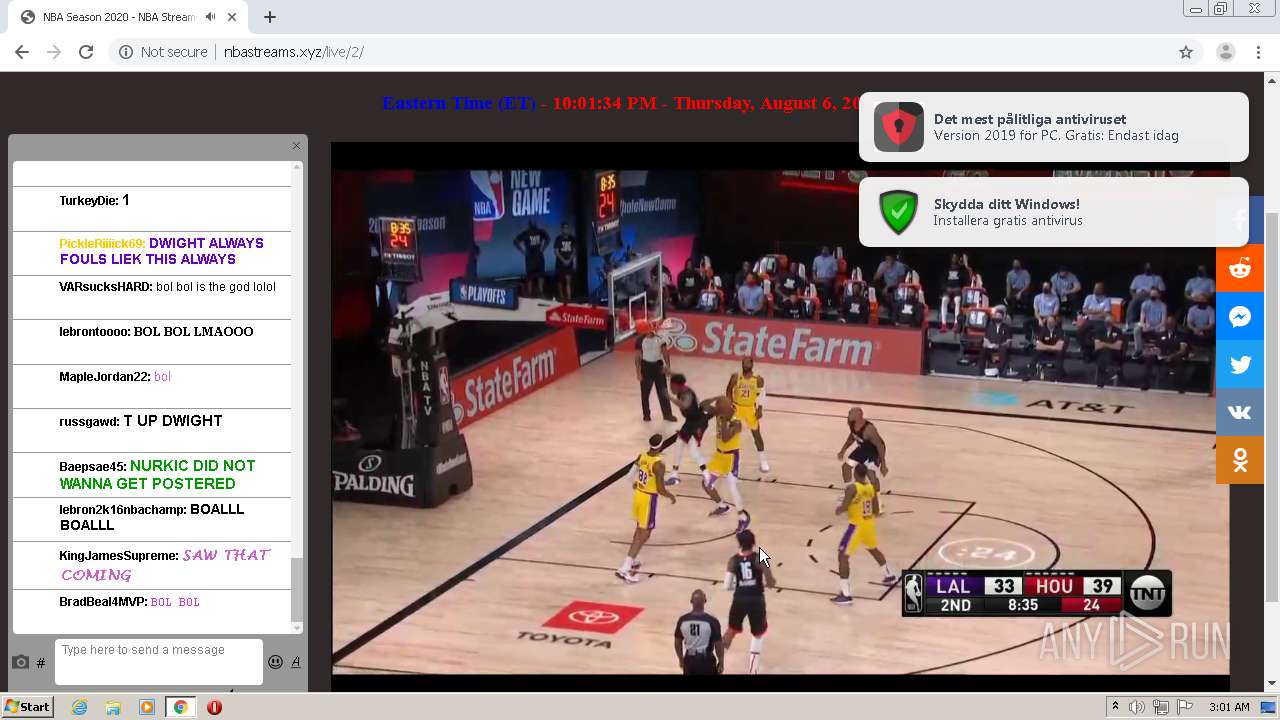
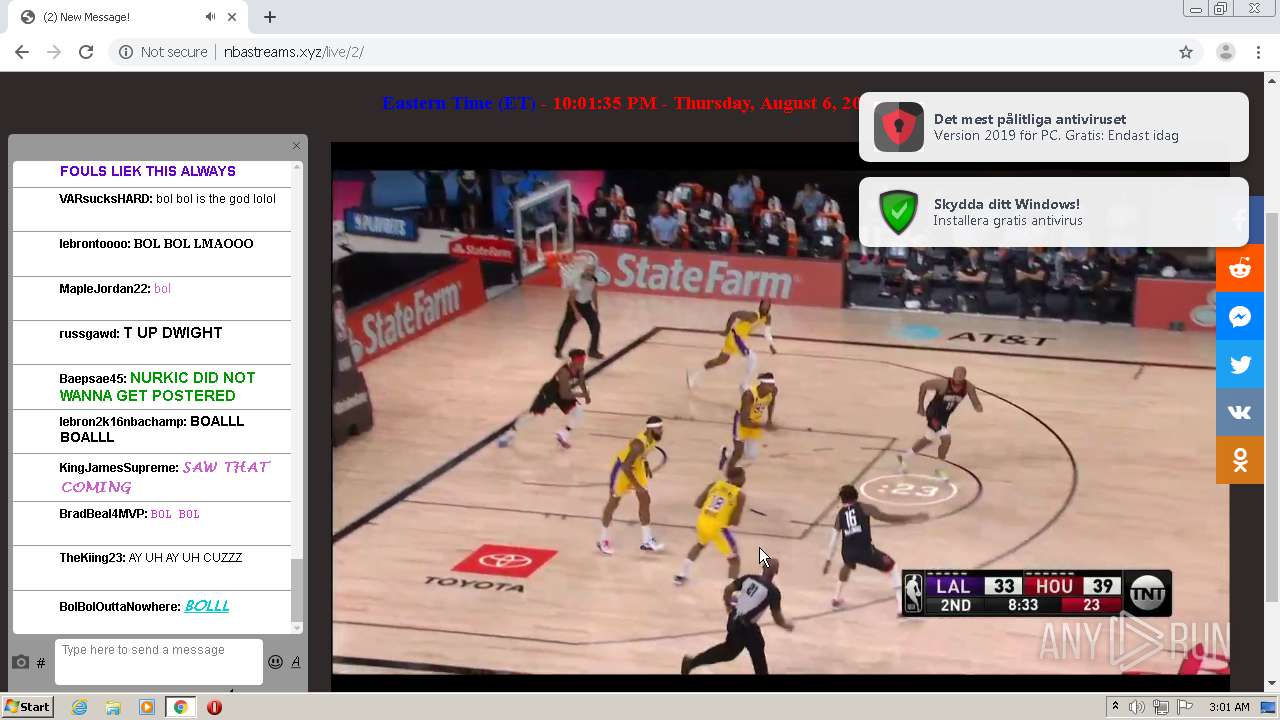
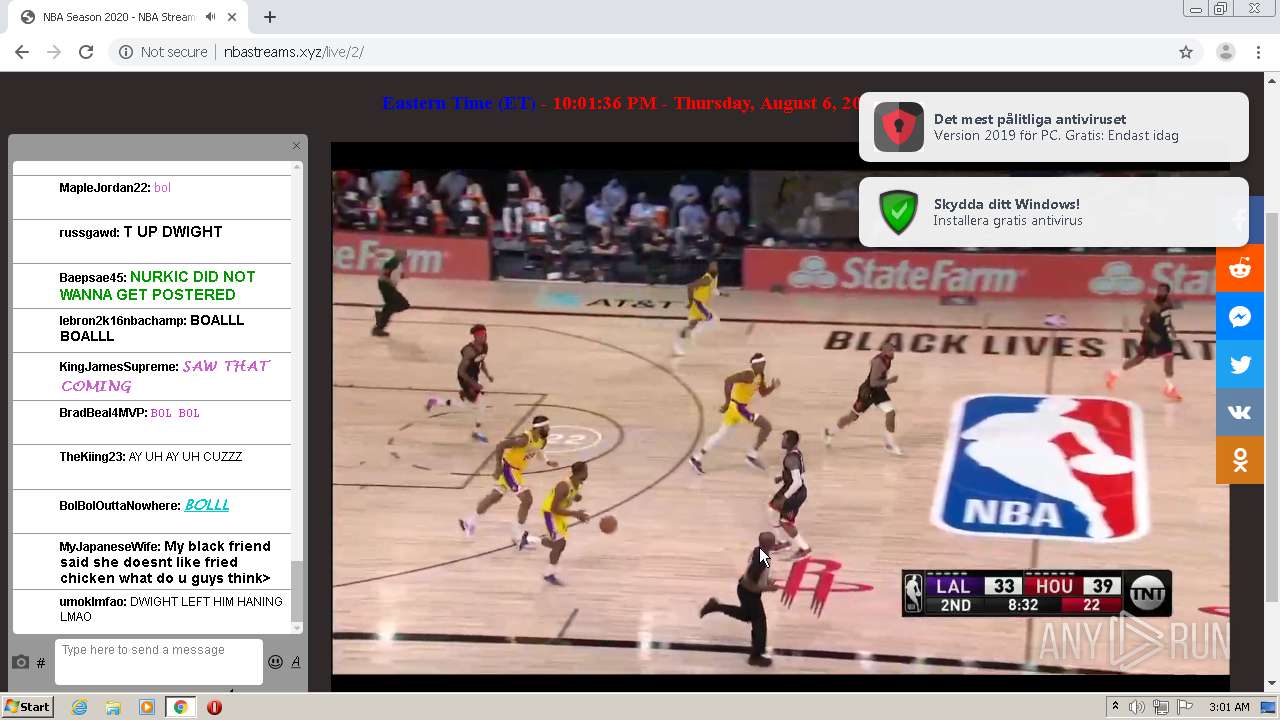
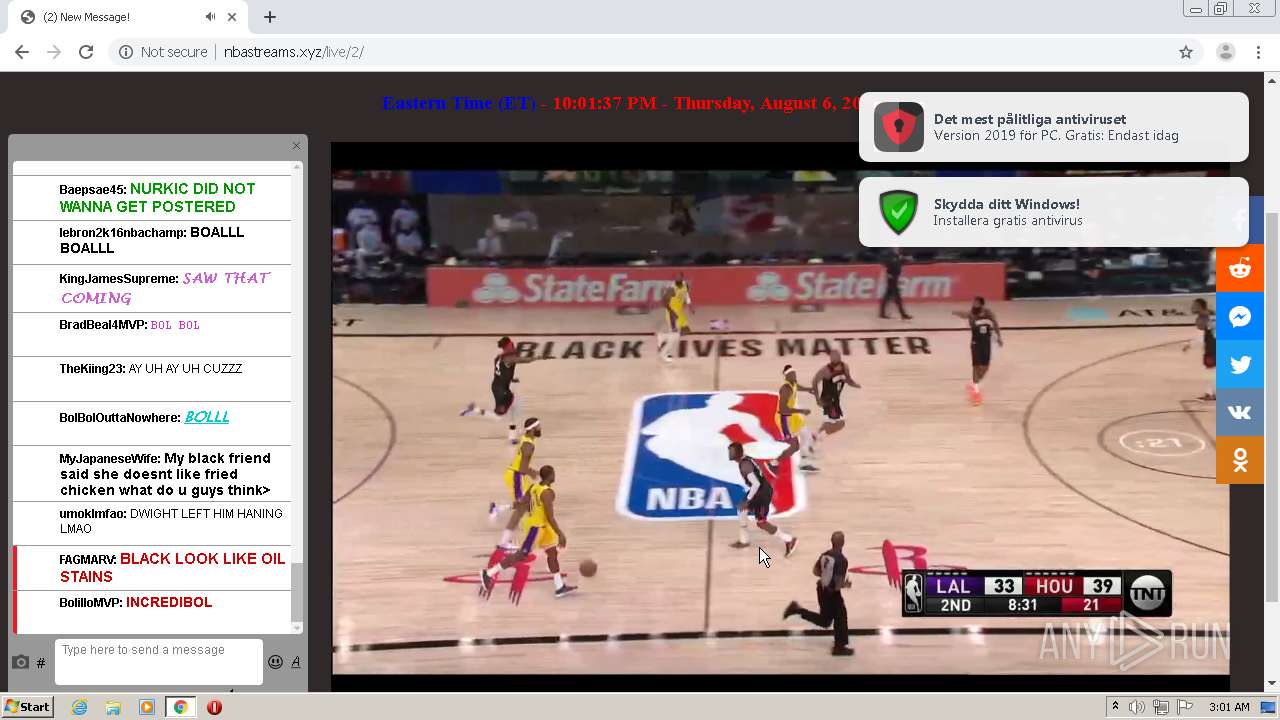
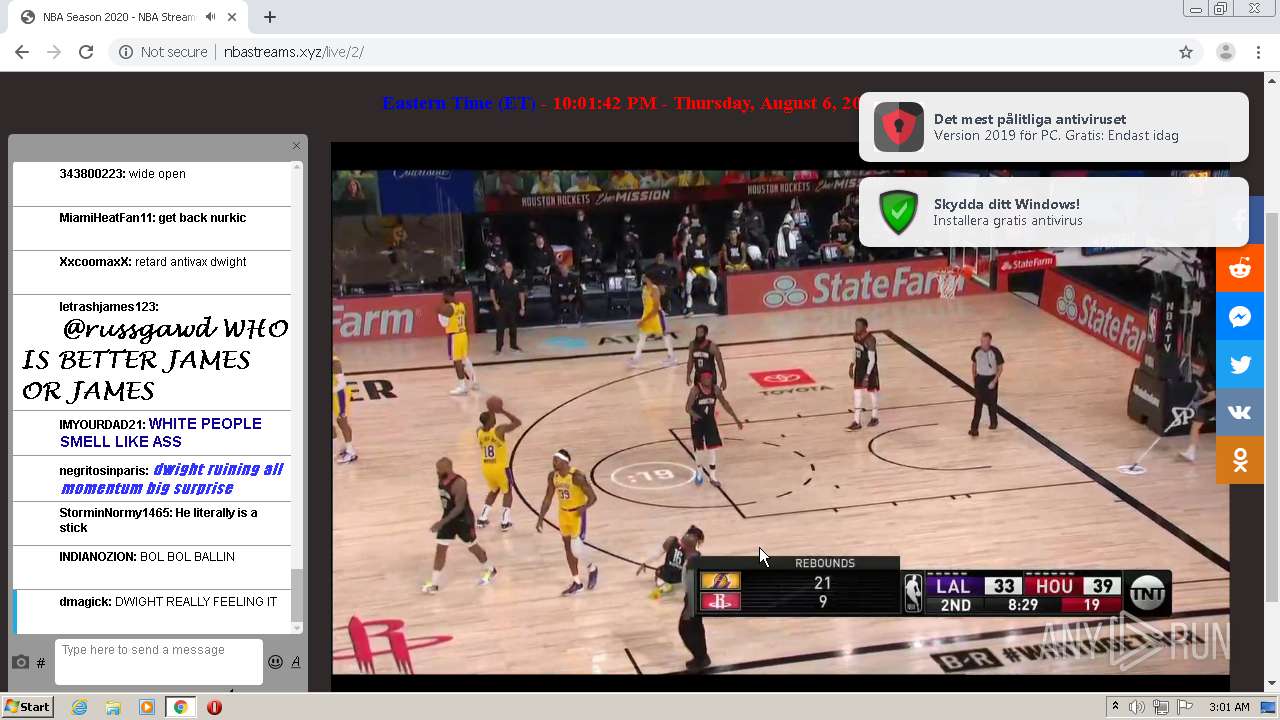
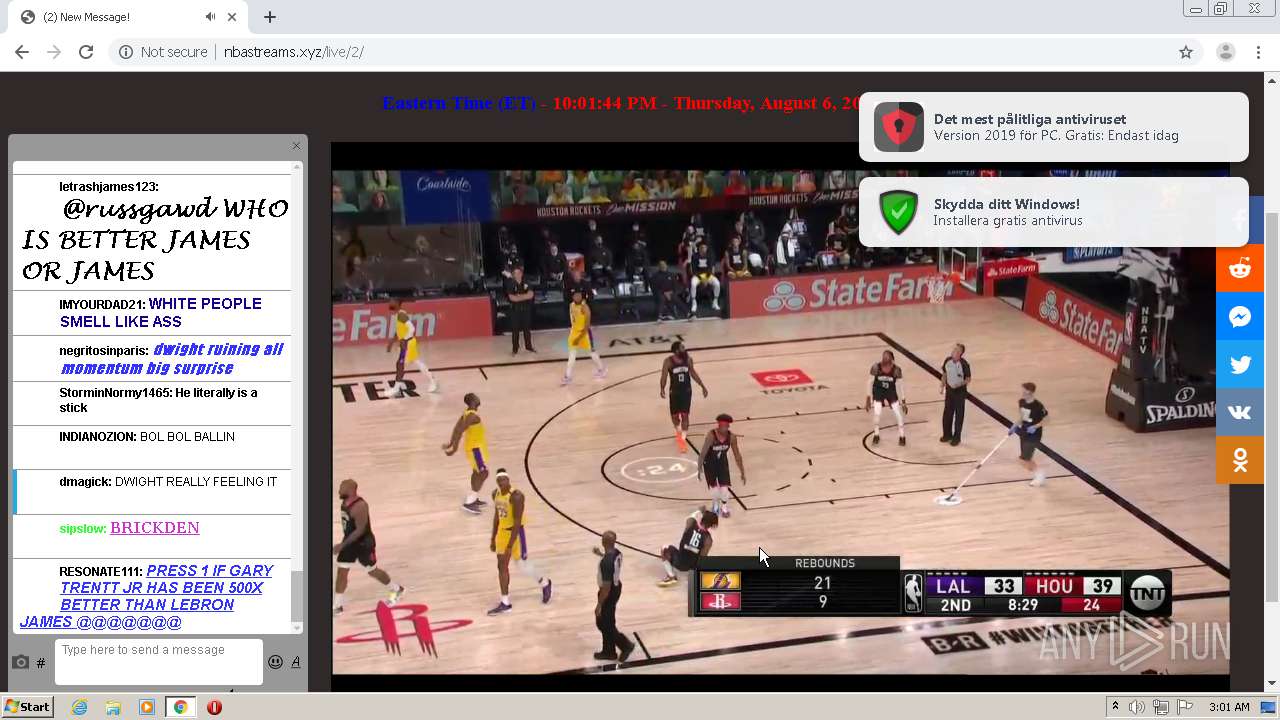
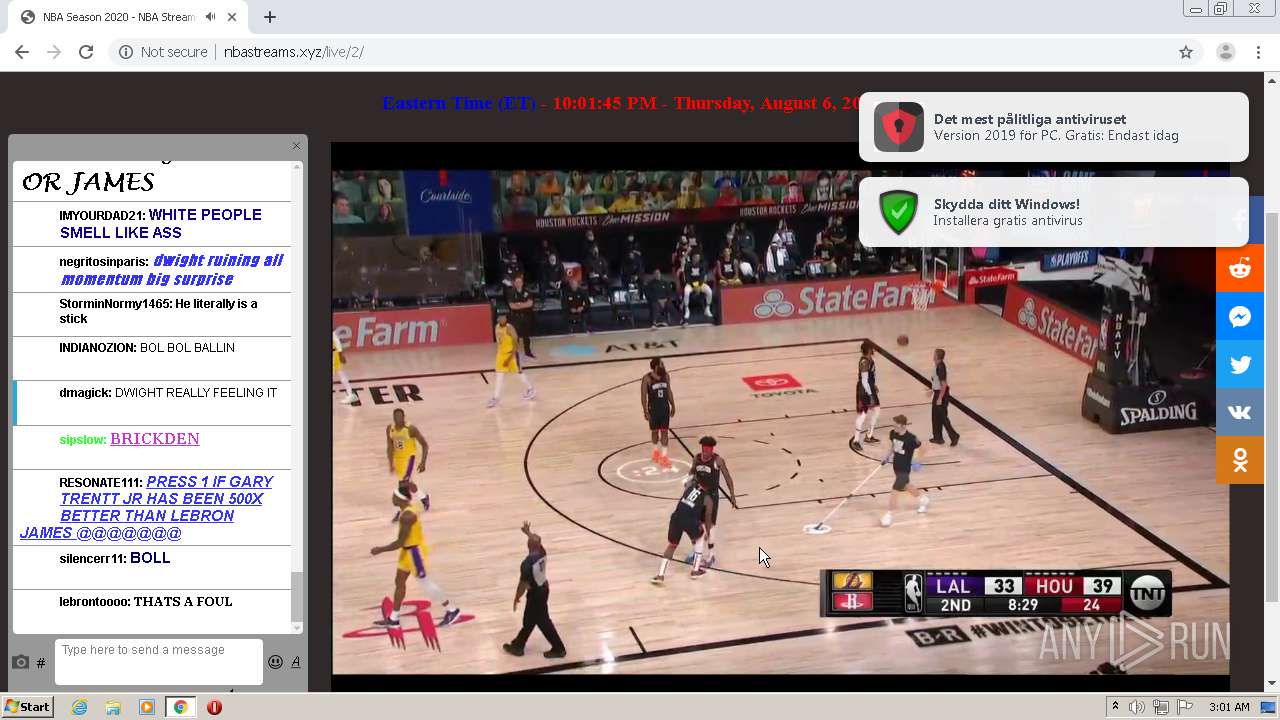
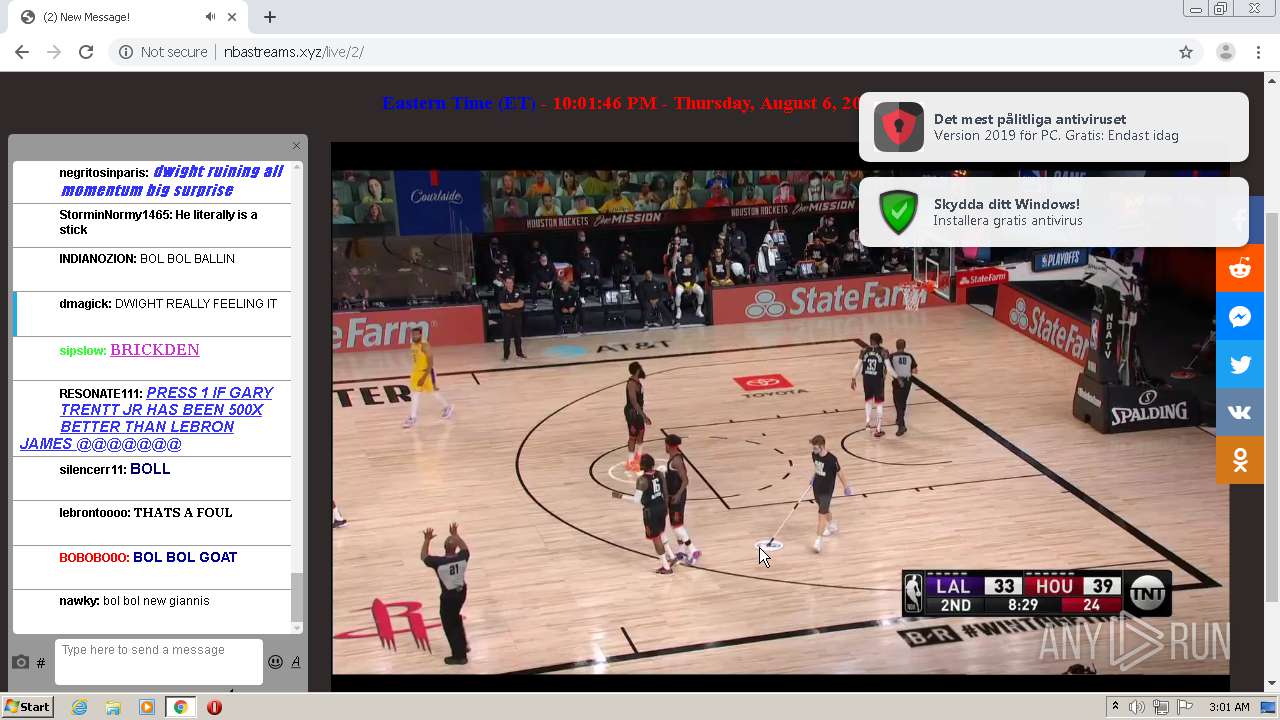
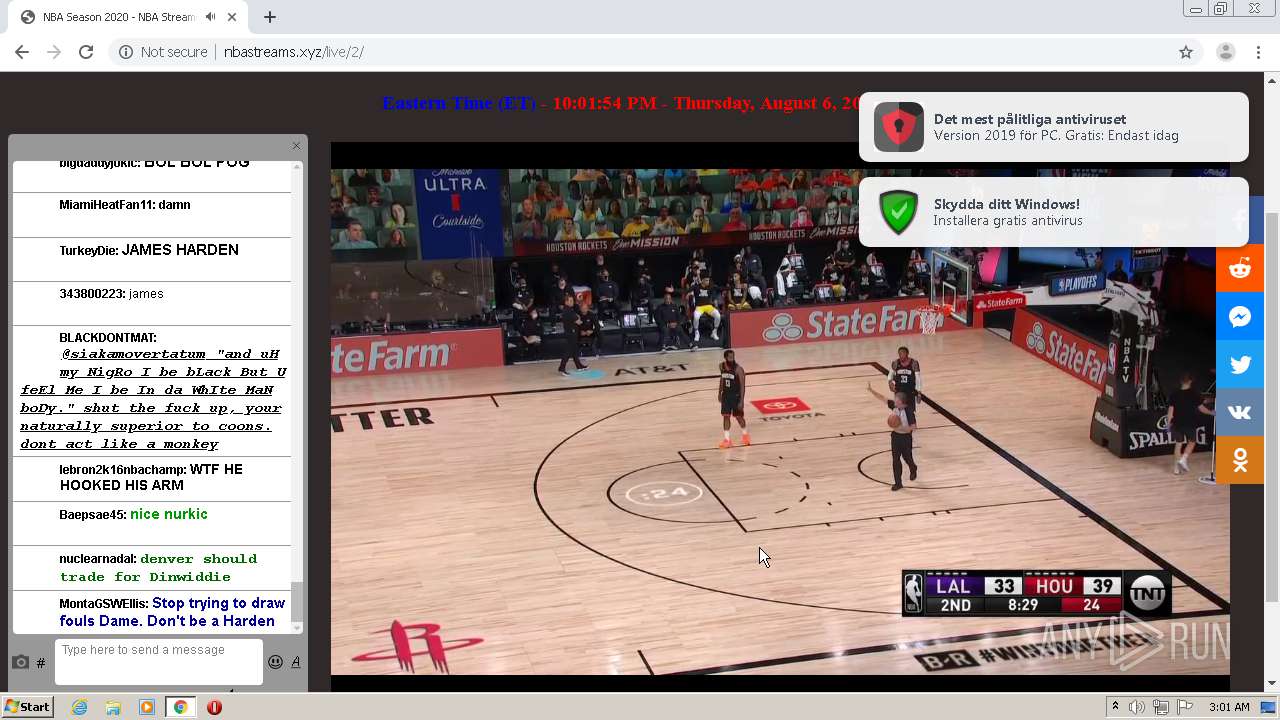
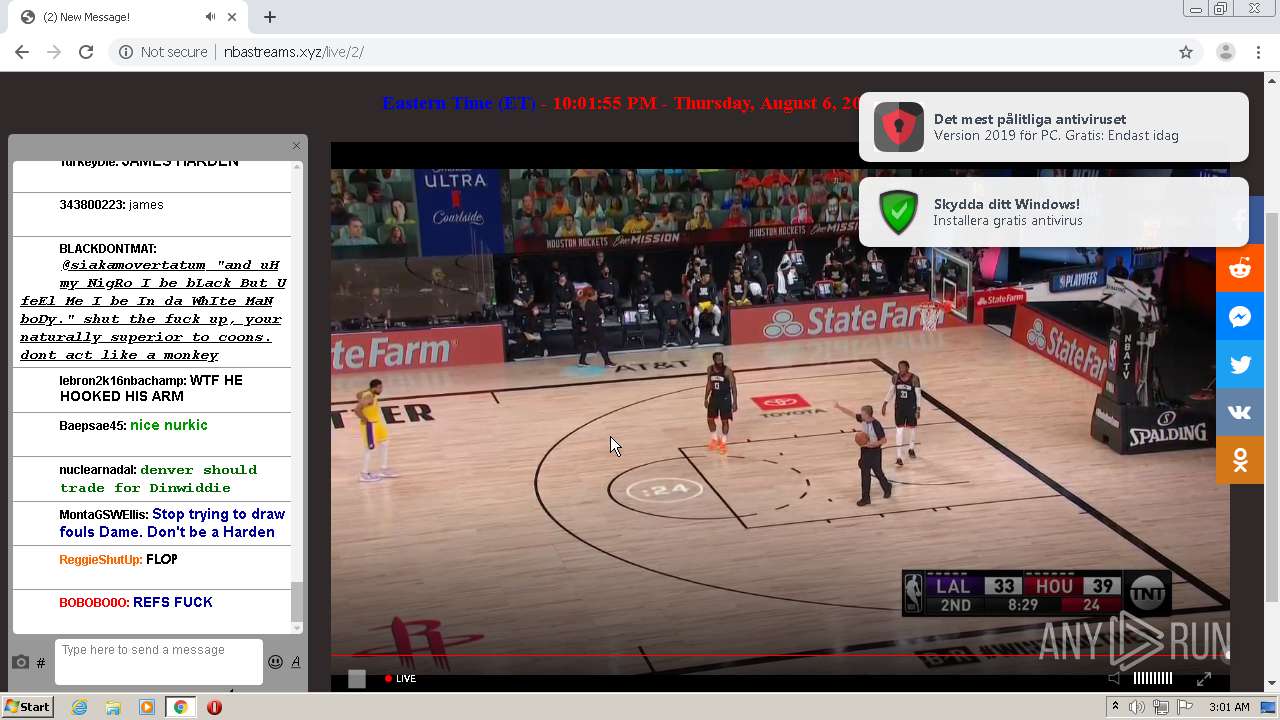
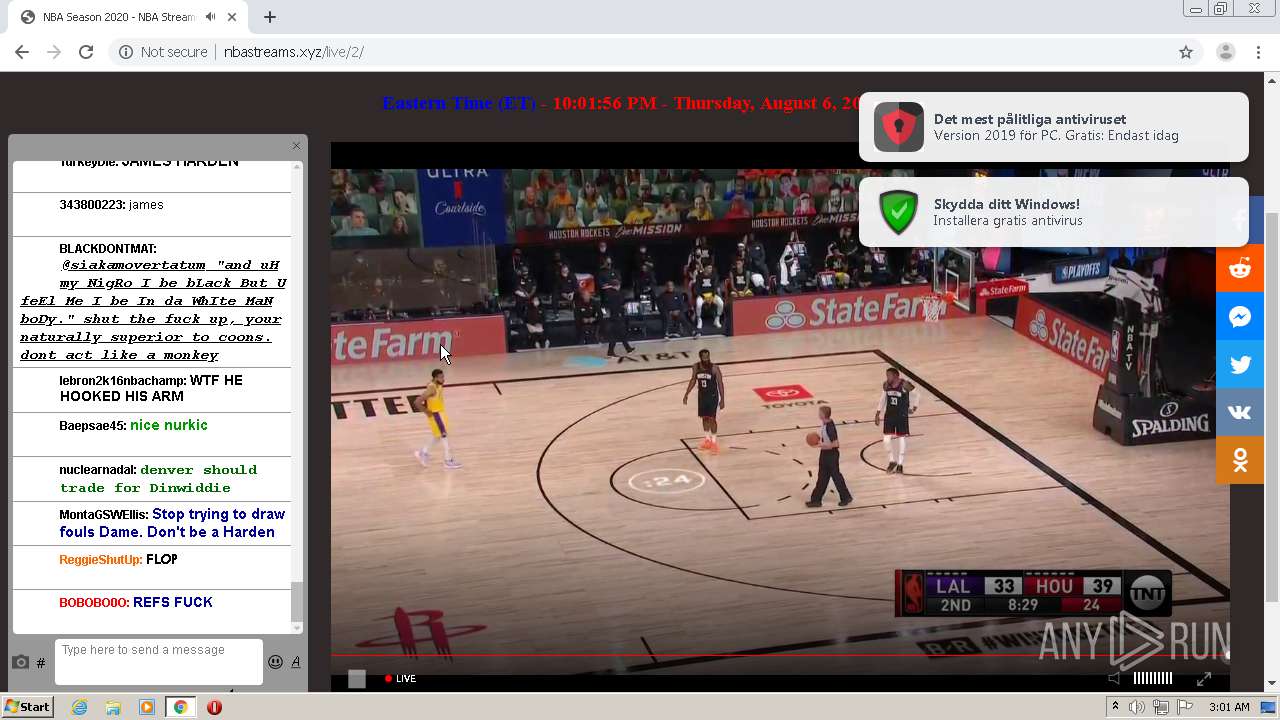
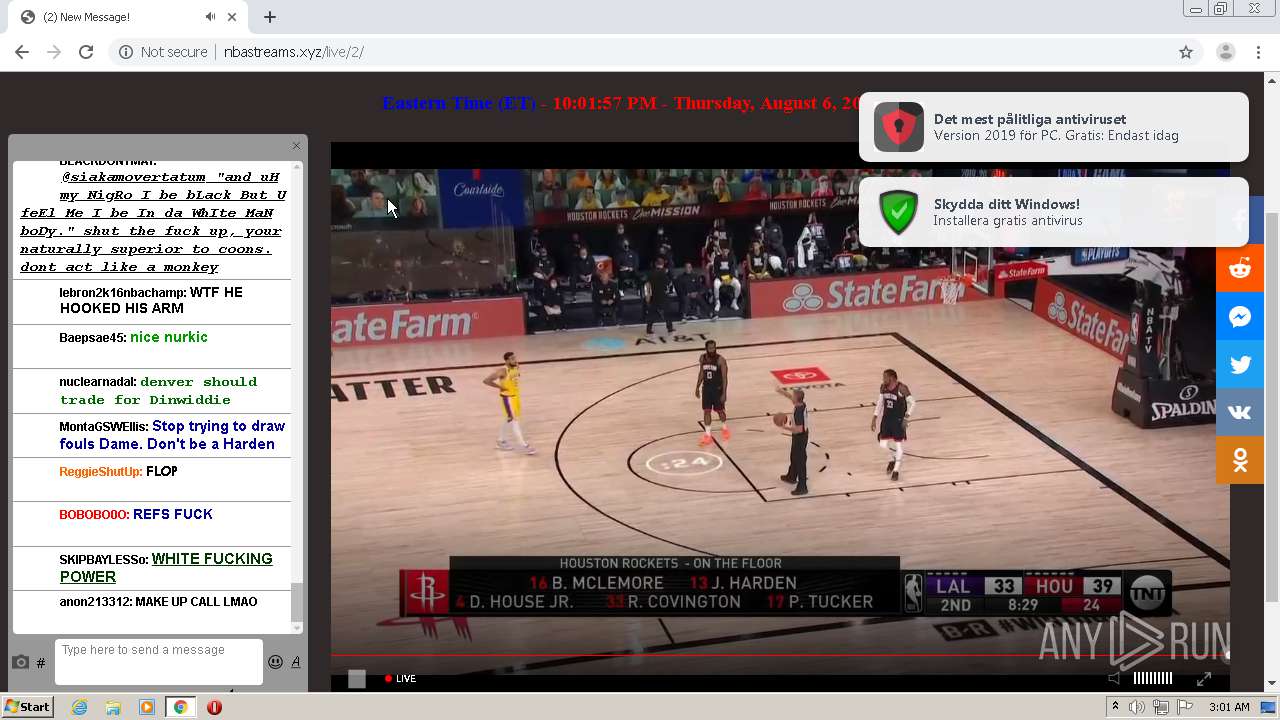
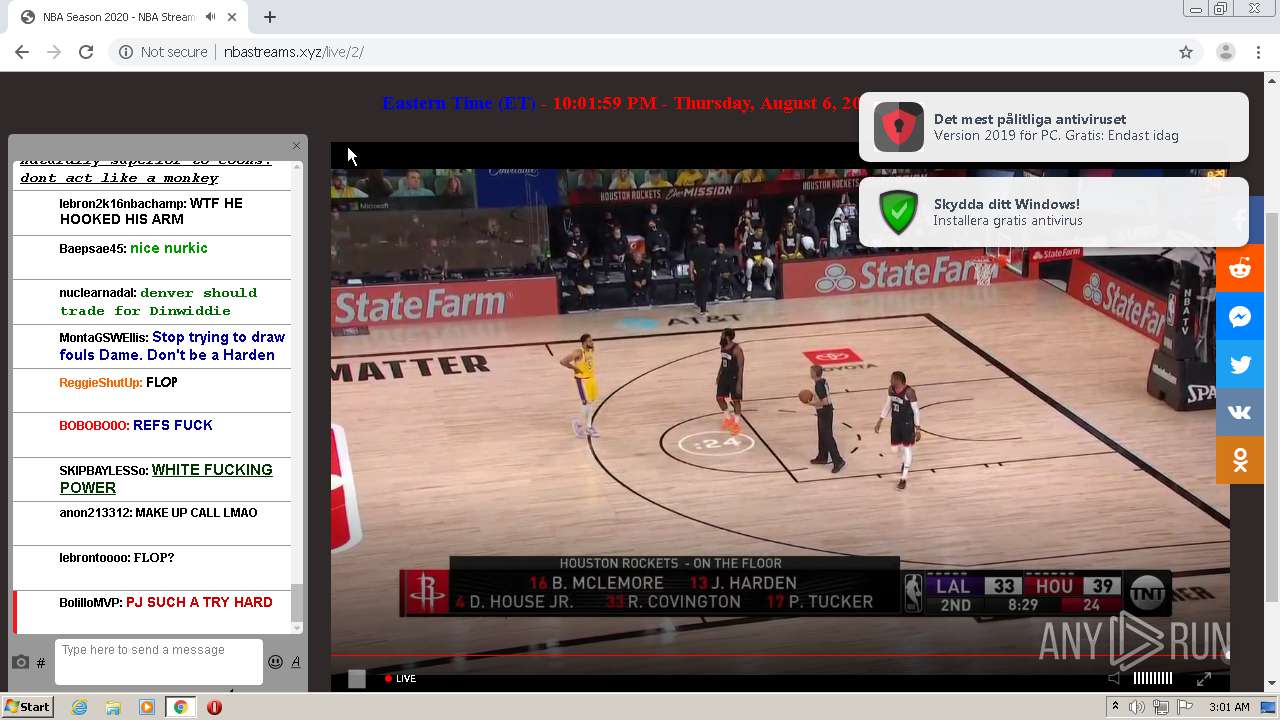
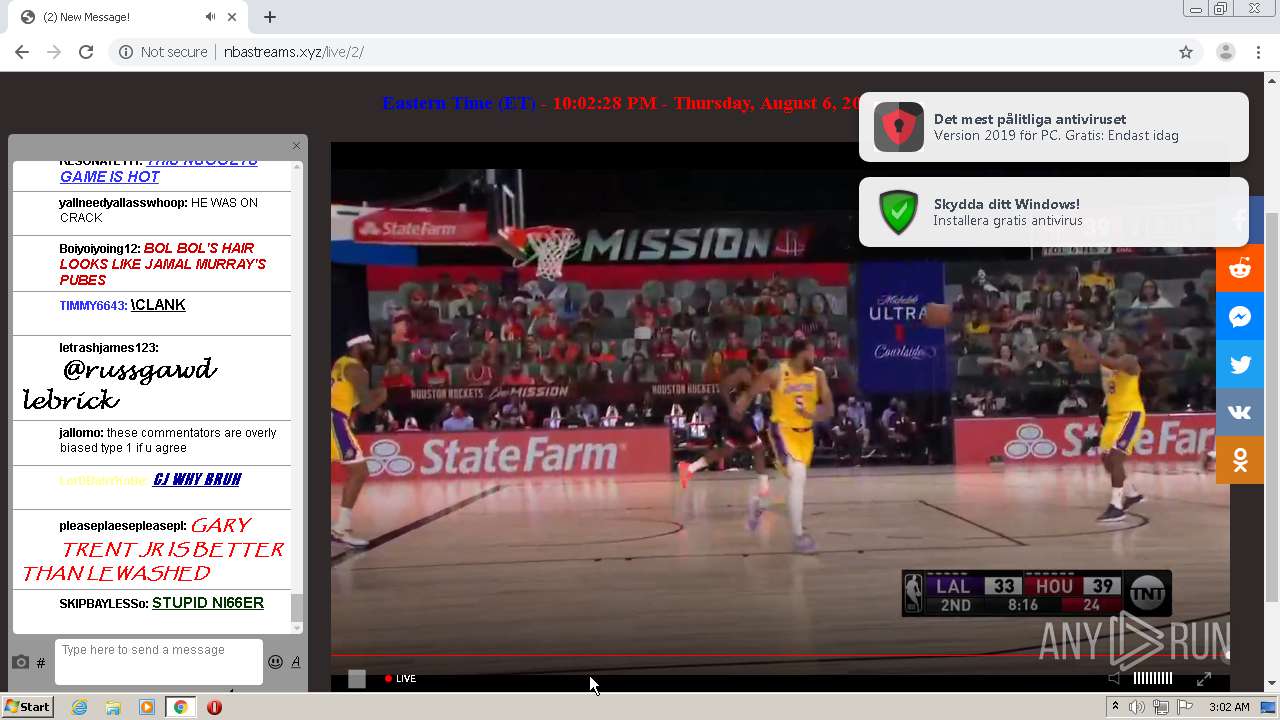
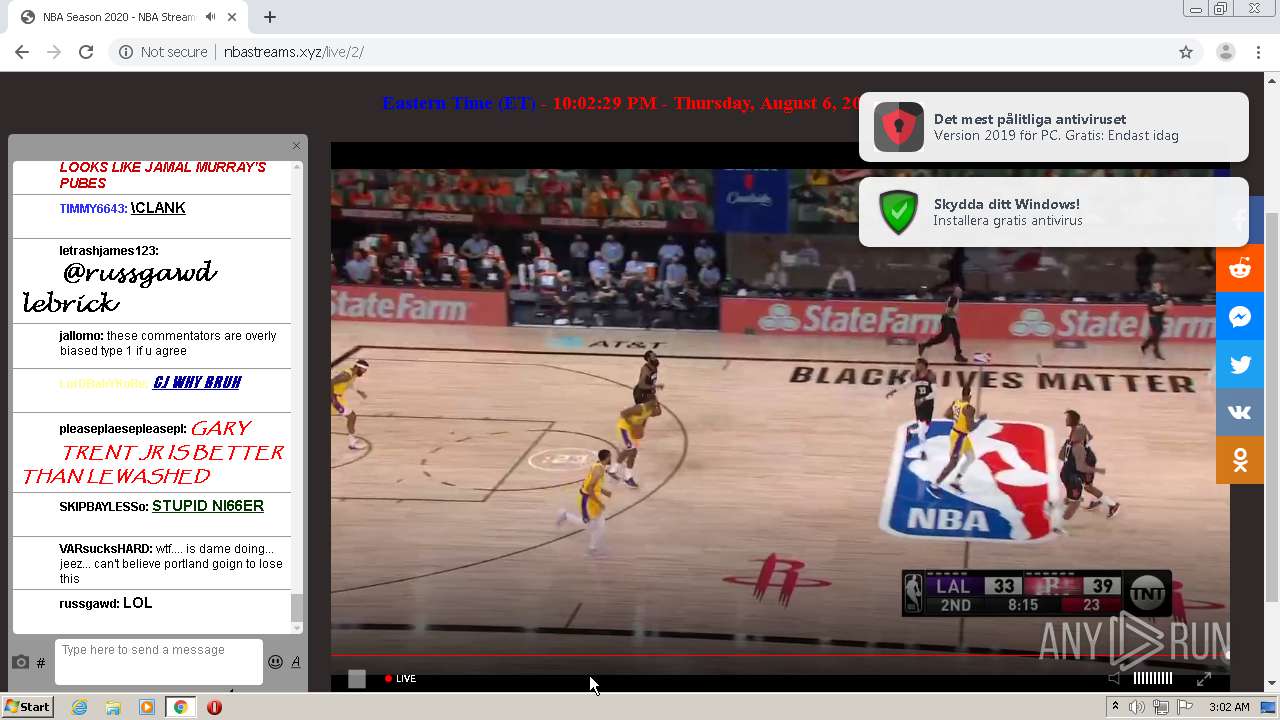
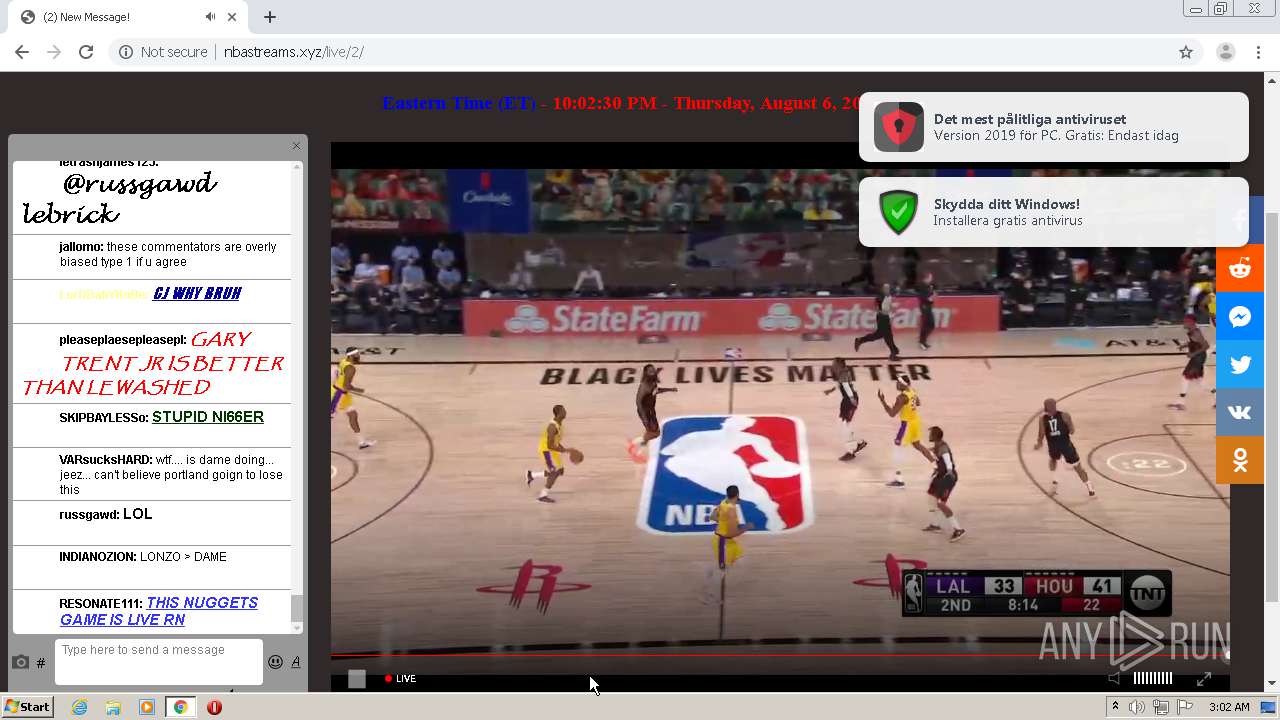
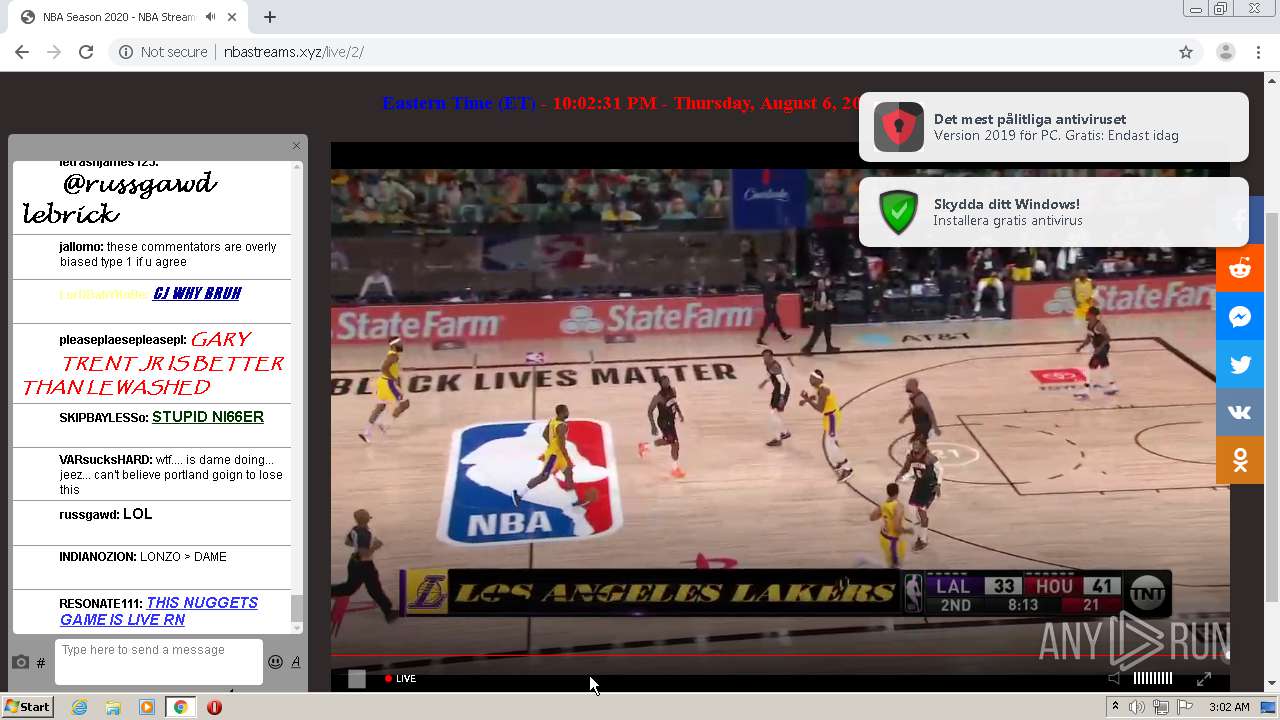
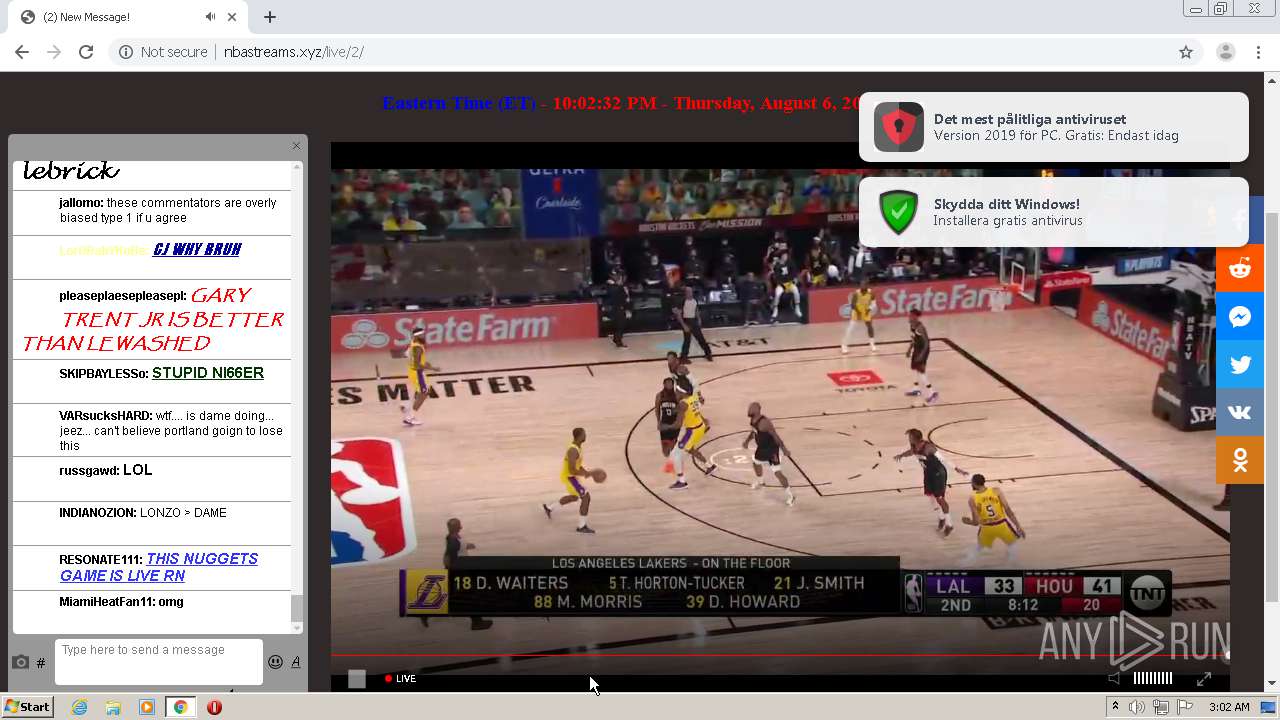
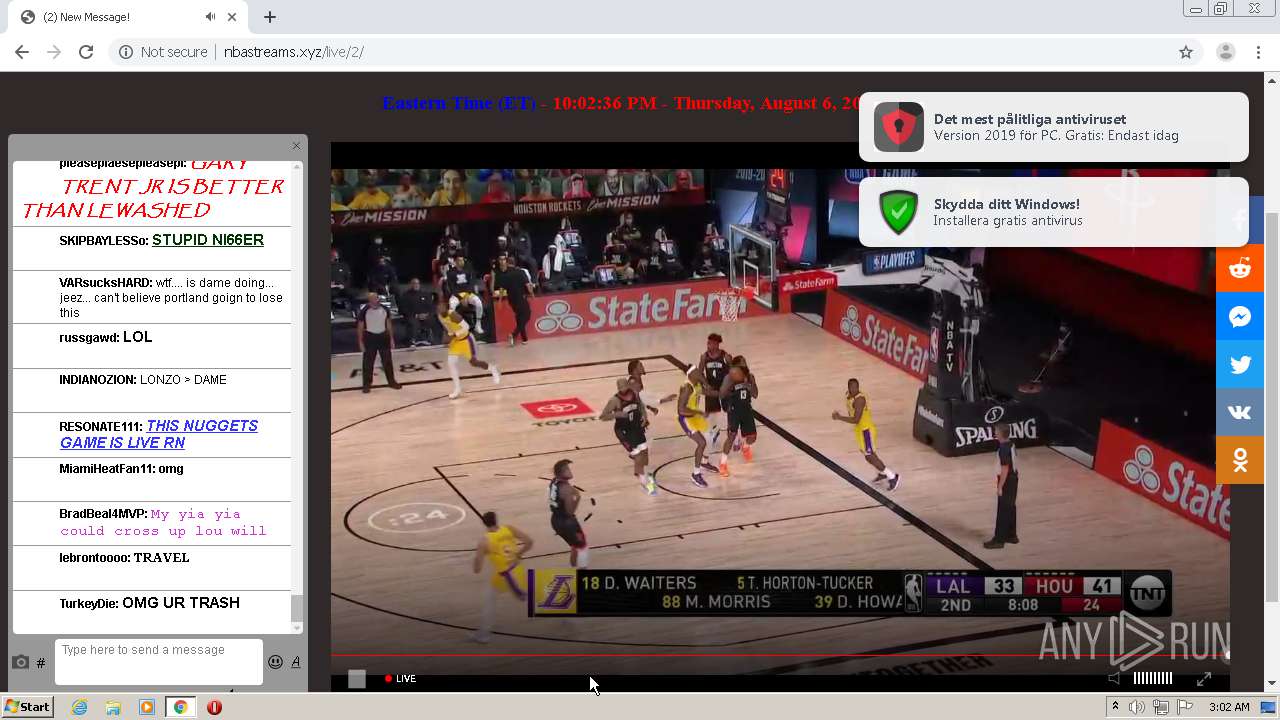
| URL: | http://nbastreams123.xyz/nba/nop/1.php |
| Full analysis: | https://app.any.run/tasks/6721a7f6-d5af-4f0b-b9ca-e78c3d2f6c00 |
| Verdict: | Malicious activity |
| Analysis date: | August 07, 2020, 02:00:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F2C59E38692F7890020378AF5DDC13C8 |
| SHA1: | 6D8B9747E37619B2A4A90E1EEA5164B28BBDFD15 |
| SHA256: | F8A544952533102B1A648FE7EB3A1216717750F356D34C4A39DEC864C0CFBEEA |
| SSDEEP: | 3:N1KQfRQEAX4zehHn:CQfTAXln |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 940)
- chrome.exe (PID: 2692)
Reads settings of System Certificates
- chrome.exe (PID: 940)
Application launched itself
- chrome.exe (PID: 2692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
27
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,5947886978515144041,9045694695603436,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11714970462886032893 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2660 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,5947886978515144041,9045694695603436,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16988585265482736037 --mojo-platform-channel-handle=1648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,5947886978515144041,9045694695603436,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14842337268171428121 --mojo-platform-channel-handle=2264 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,5947886978515144041,9045694695603436,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=588560199573758165 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2540 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,5947886978515144041,9045694695603436,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8616867173630147707 --mojo-platform-channel-handle=3124 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,5947886978515144041,9045694695603436,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15646405713982378248 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,5947886978515144041,9045694695603436,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6899591942966568493 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,5947886978515144041,9045694695603436,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10893034017907246563 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,5947886978515144041,9045694695603436,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17872061711031934686 --mojo-platform-channel-handle=996 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,5947886978515144041,9045694695603436,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2714647324013951133 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2756 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
772
Read events
662
Write events
105
Delete events
5
Modification events
| (PID) Process: | (2692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2692-13241239240328375 |
Value: 259 | |||
| (PID) Process: | (2692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2692) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
86
Text files
106
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b95d3652-a48b-43f4-ad7b-1e0564eec667.tmp | — | |
MD5:— | SHA256:— | |||
| 2692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF18f018.TMP | text | |
MD5:— | SHA256:— | |||
| 2692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF18f027.TMP | text | |
MD5:— | SHA256:— | |||
| 2692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF18f066.TMP | text | |
MD5:— | SHA256:— | |||
| 2692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
234
DNS requests
79
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
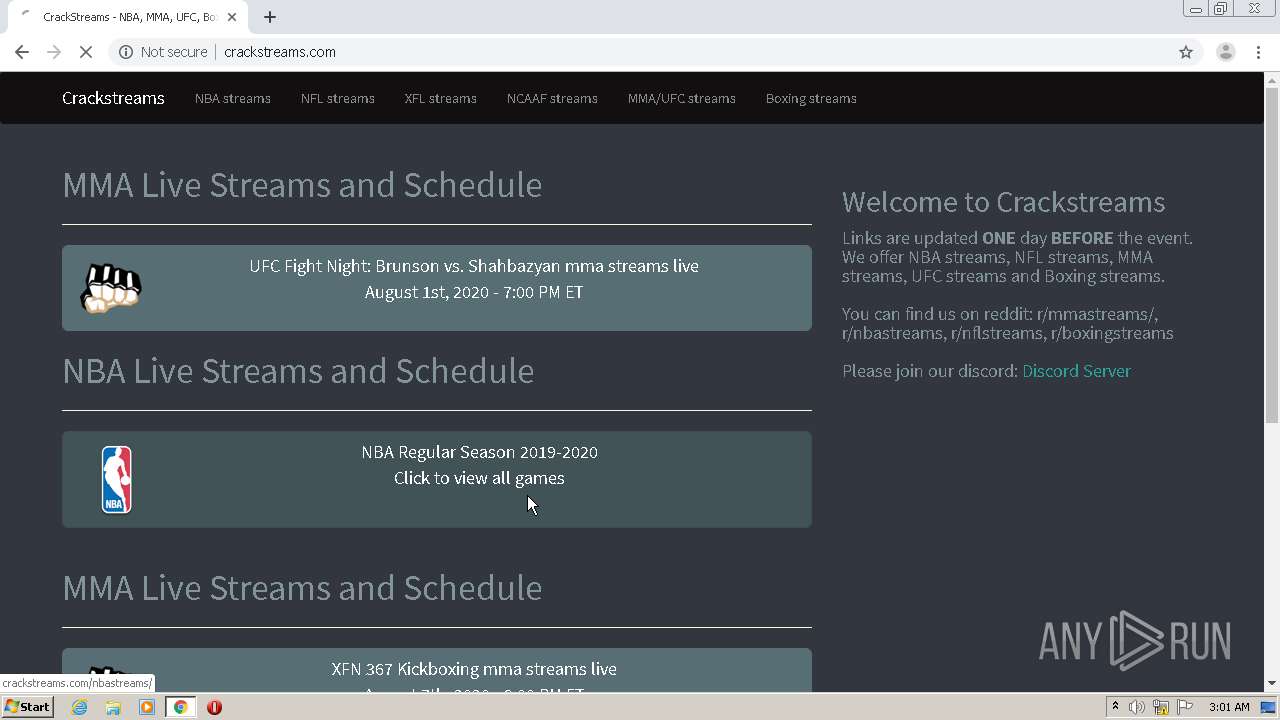
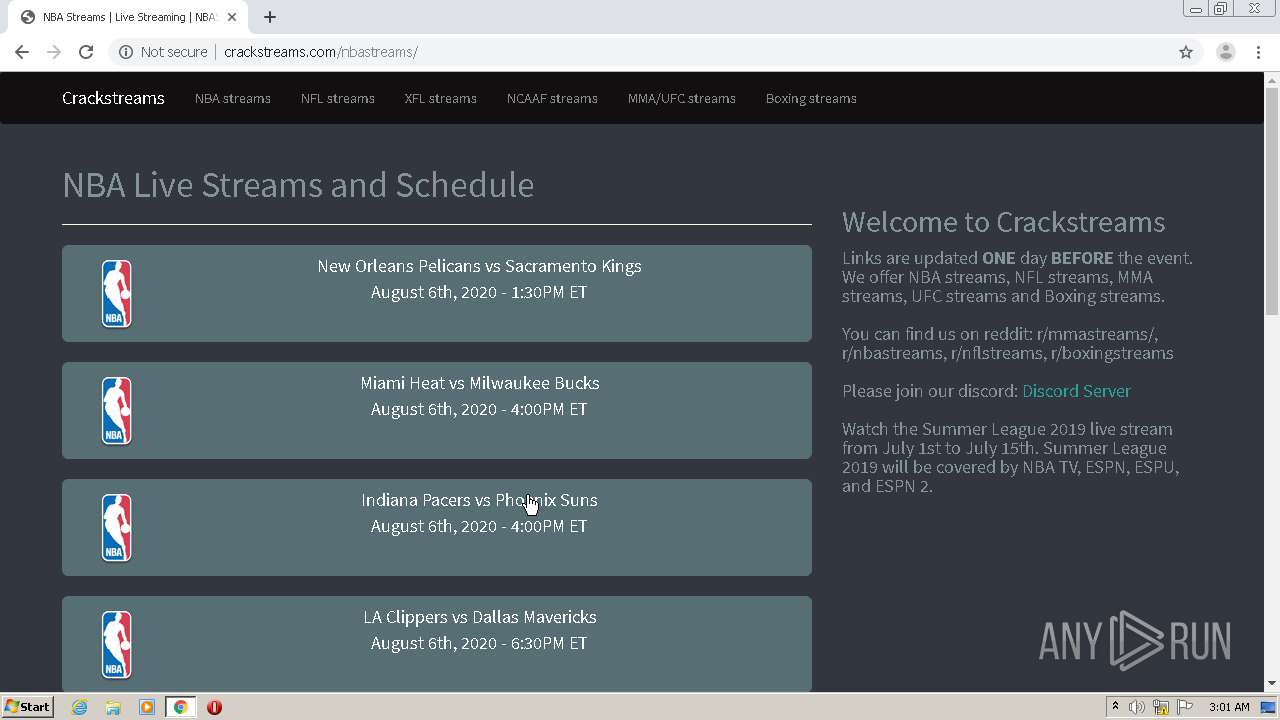
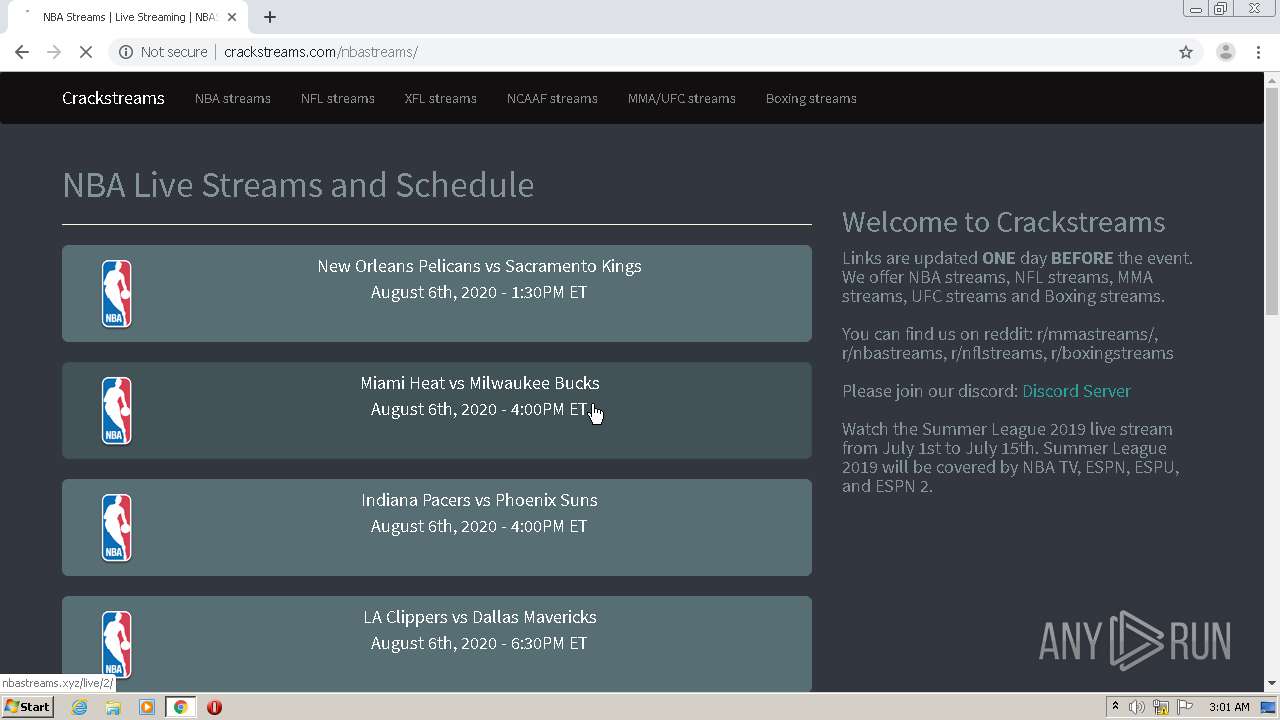
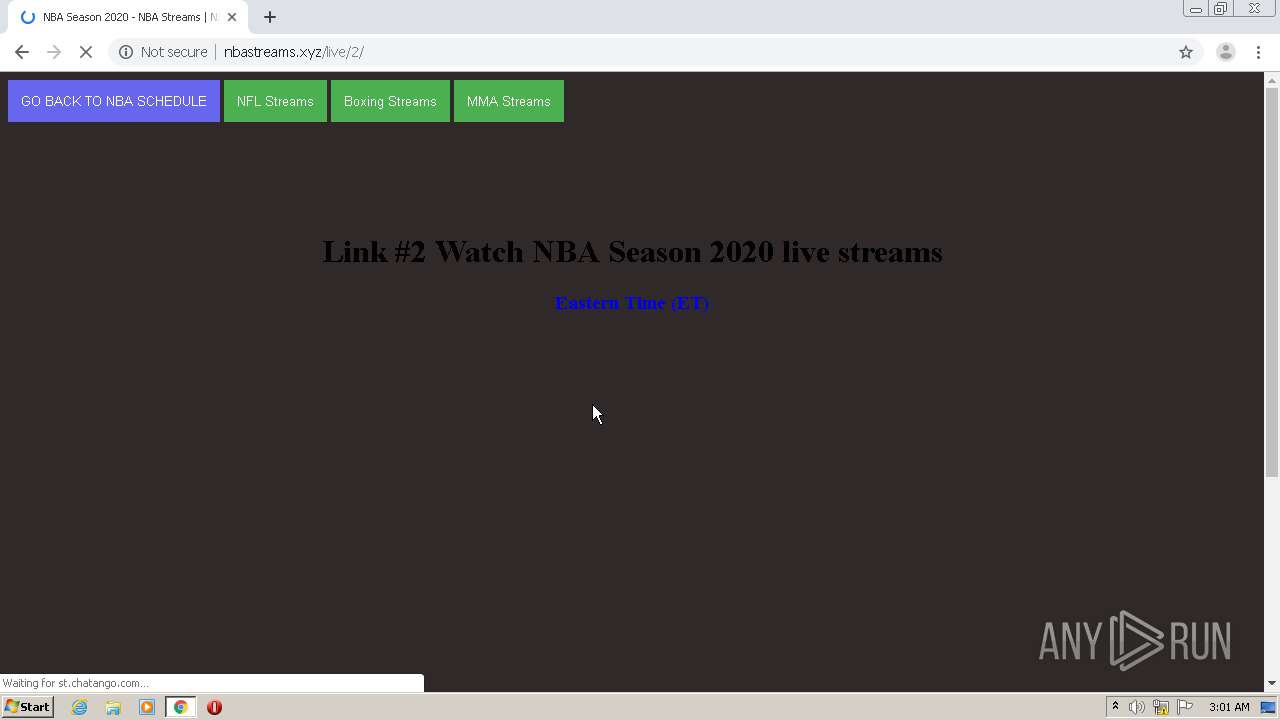
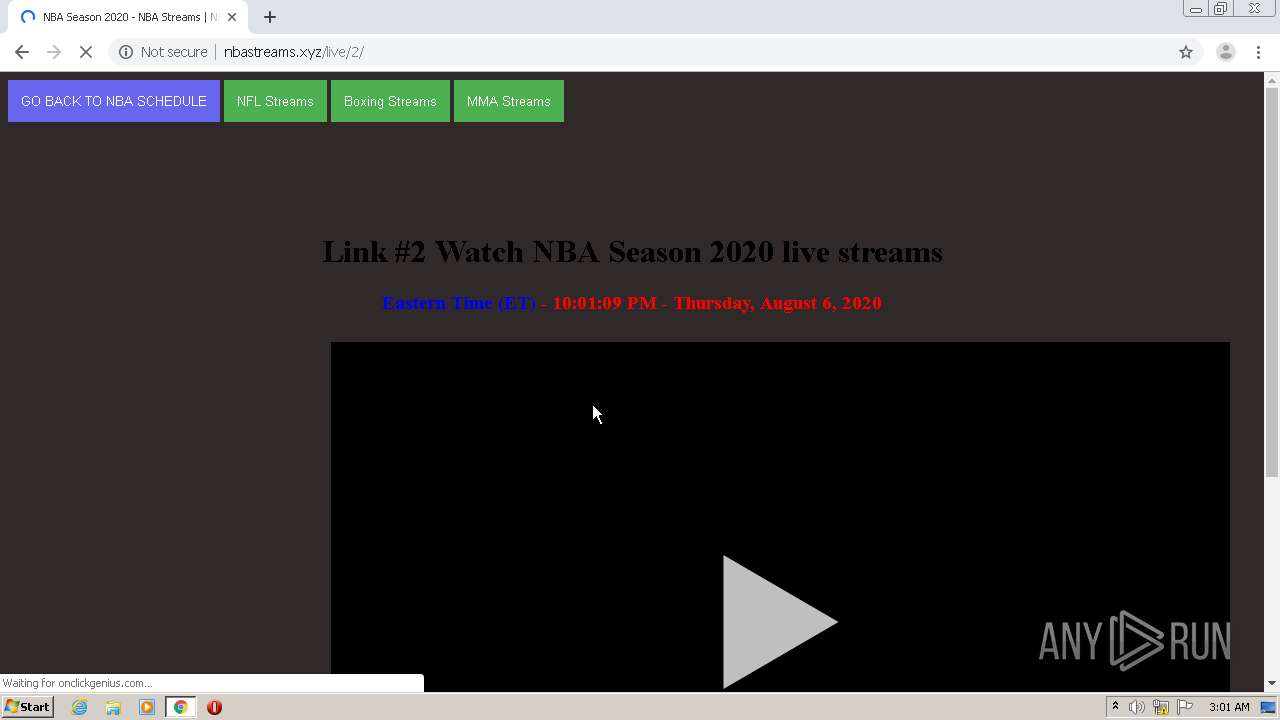
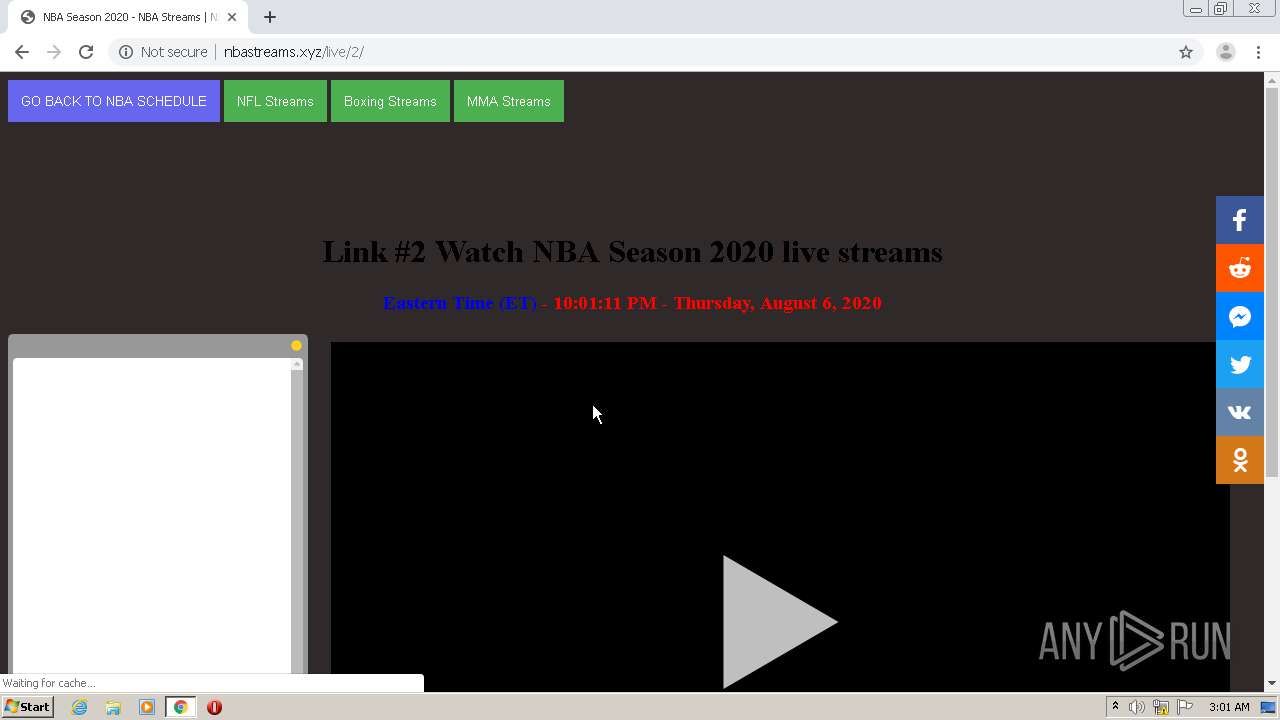
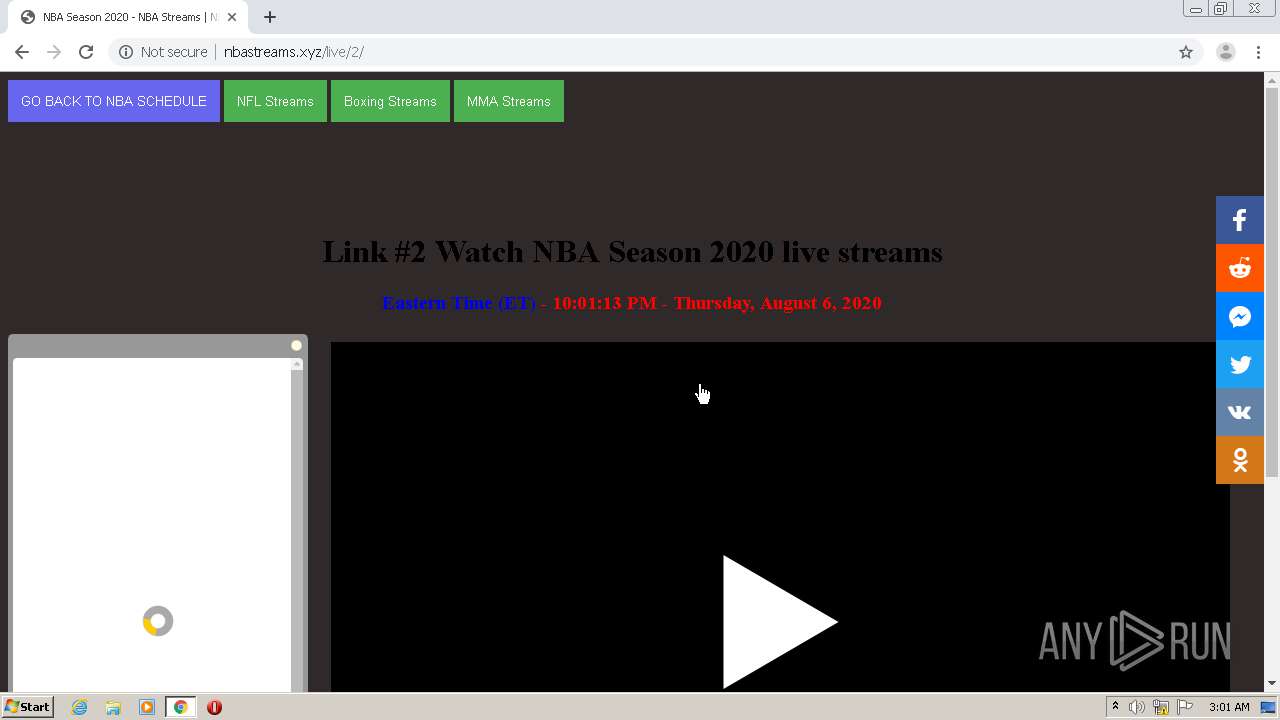
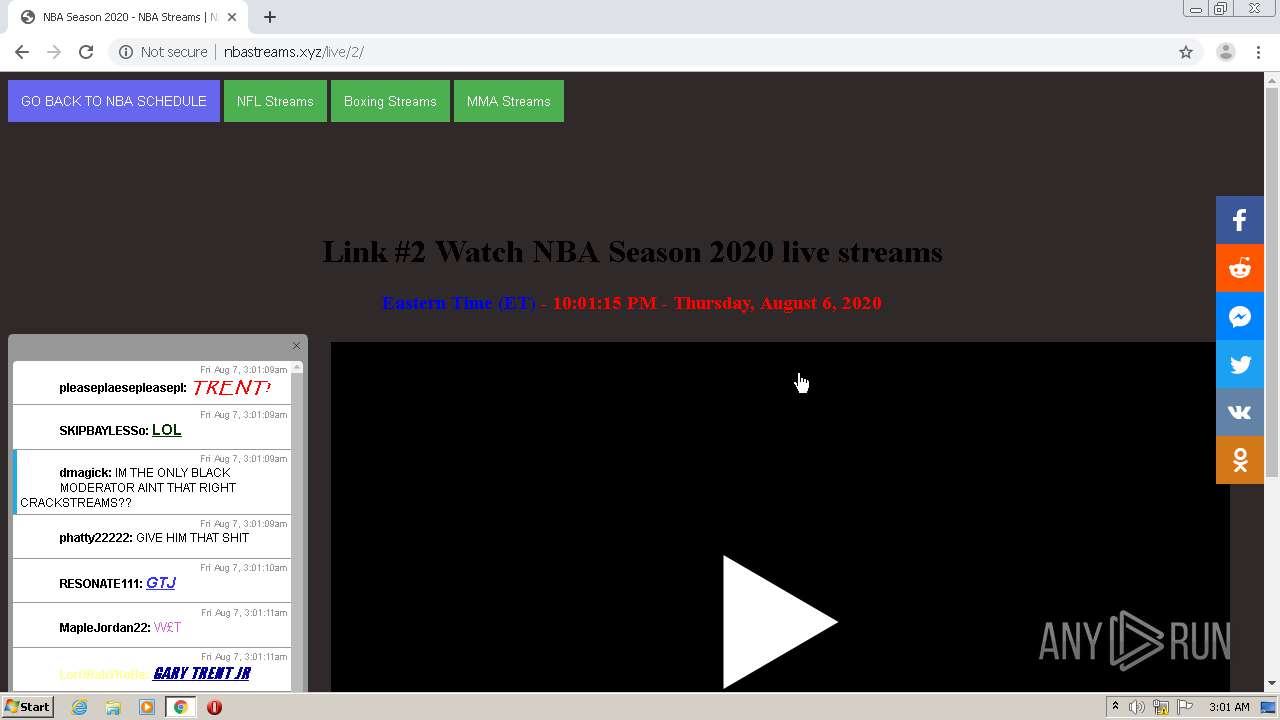
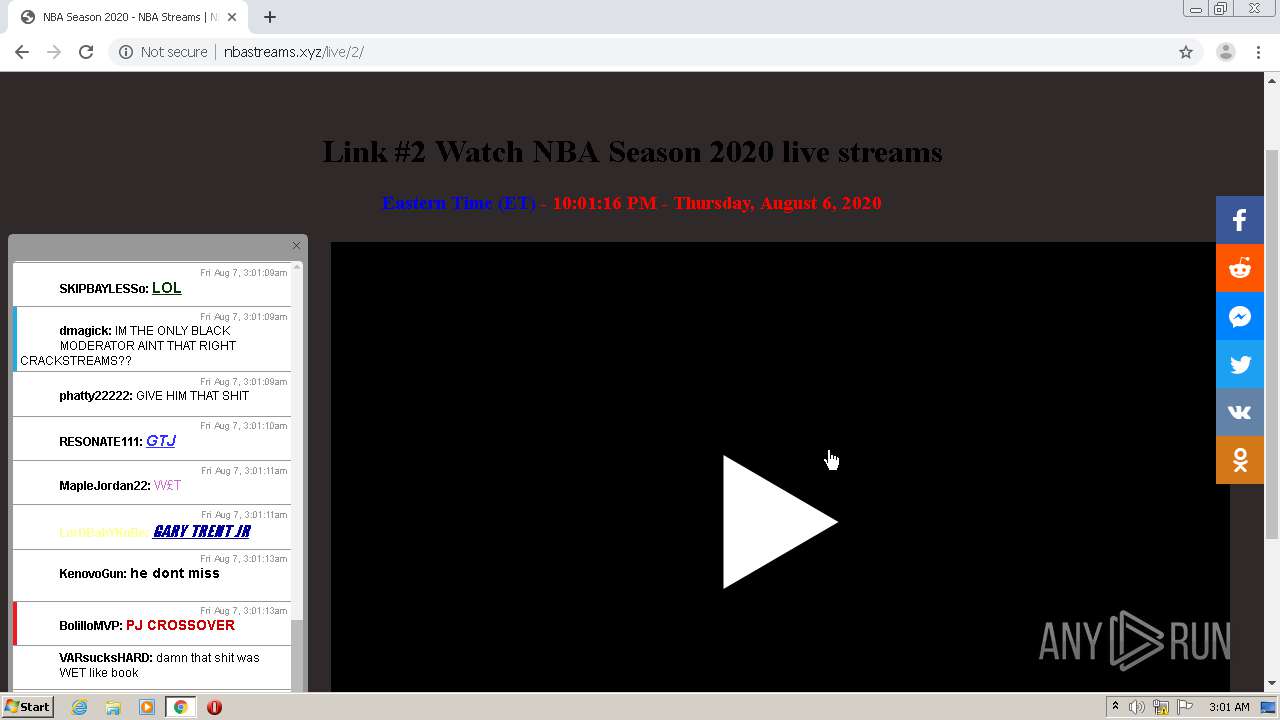
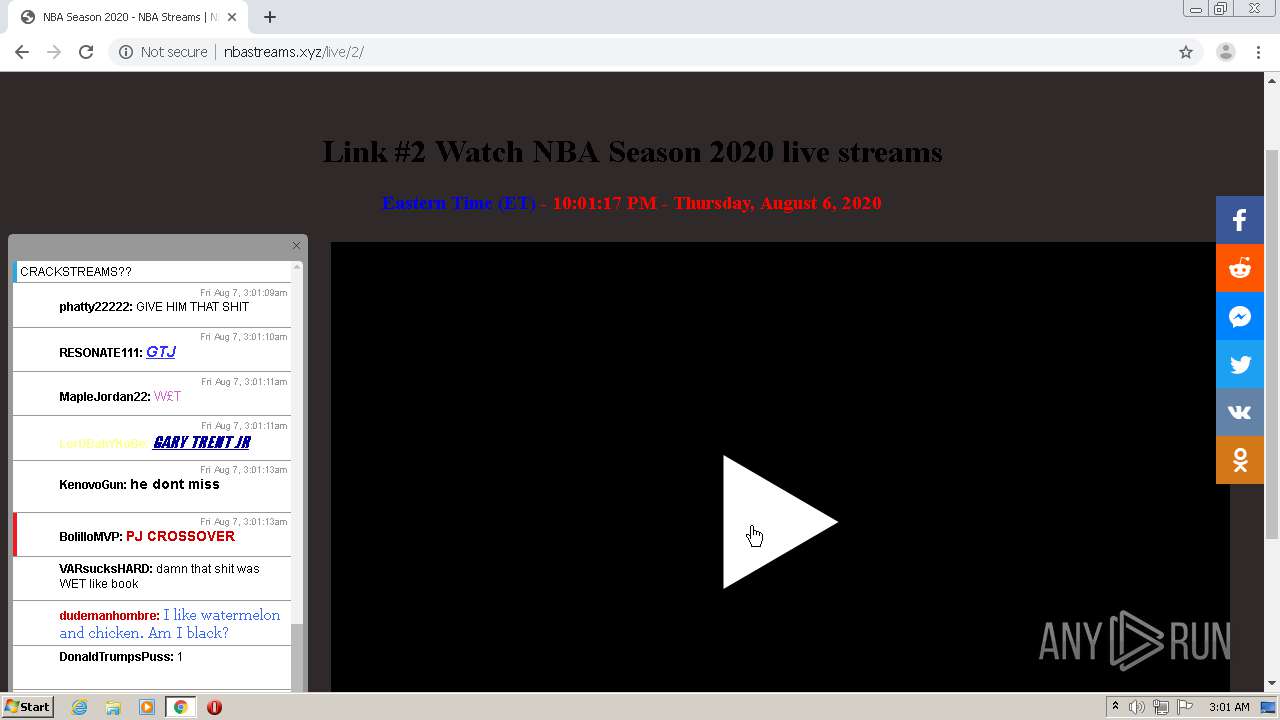
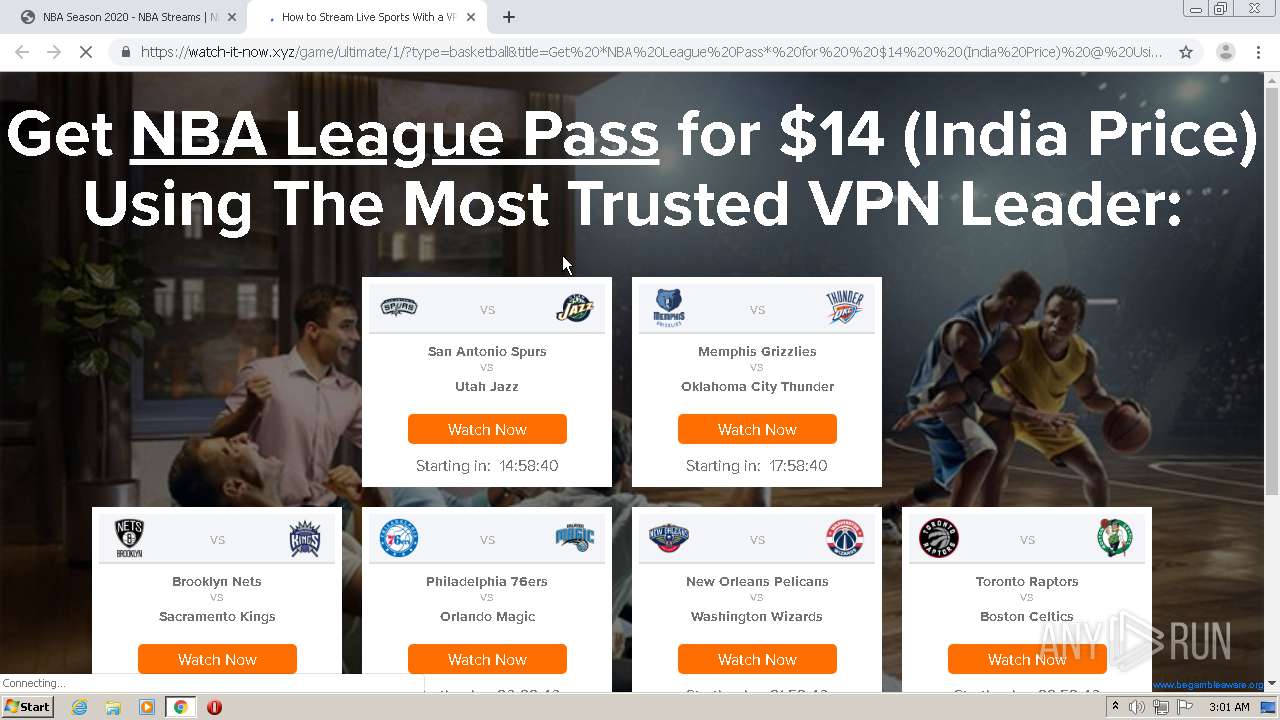
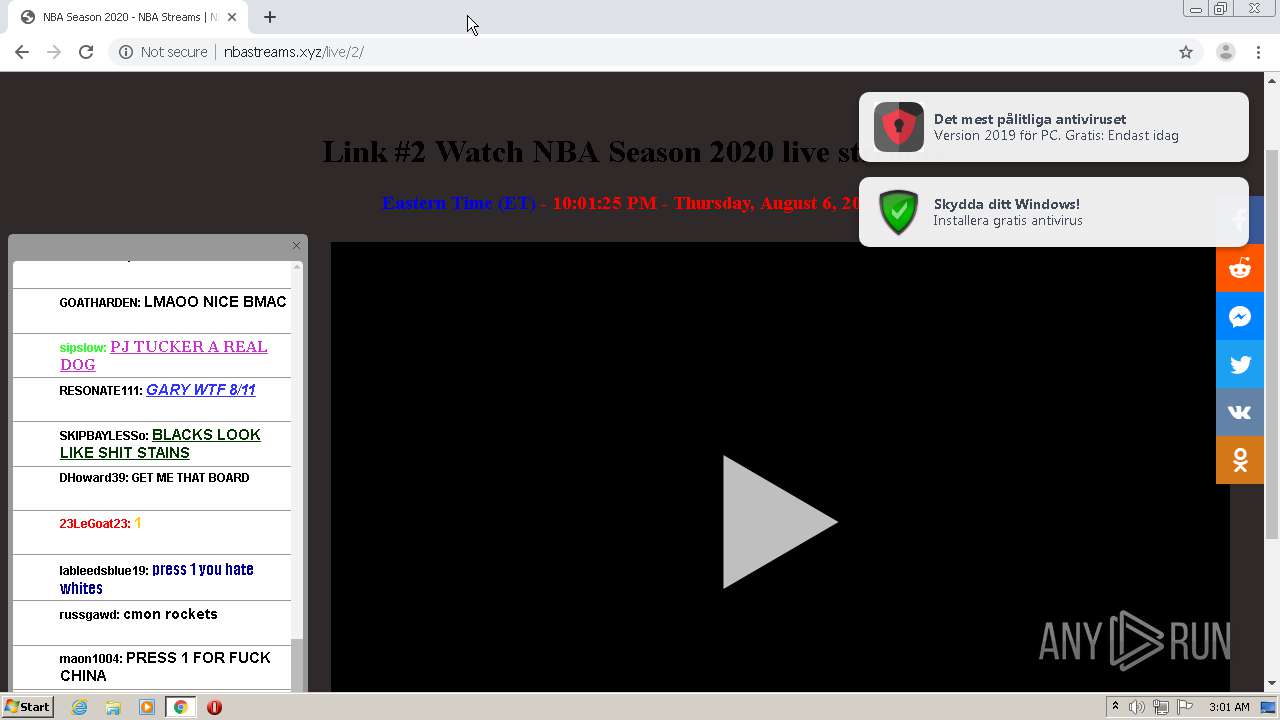
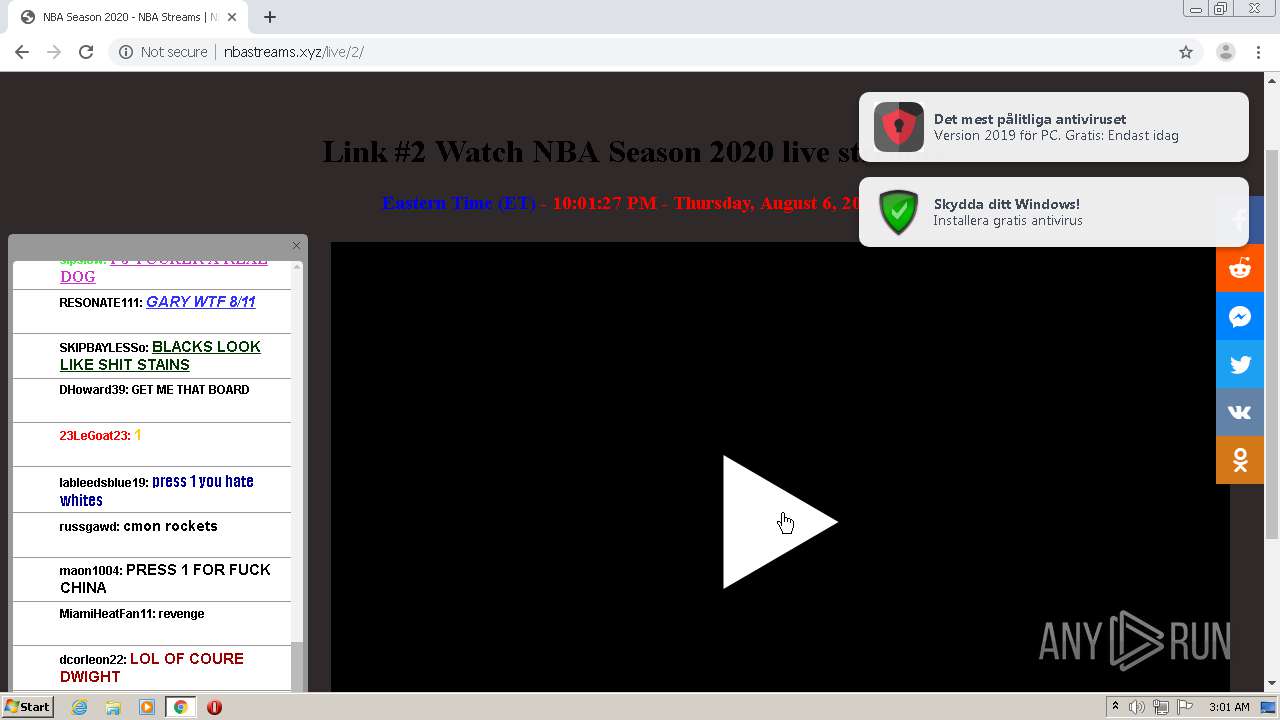
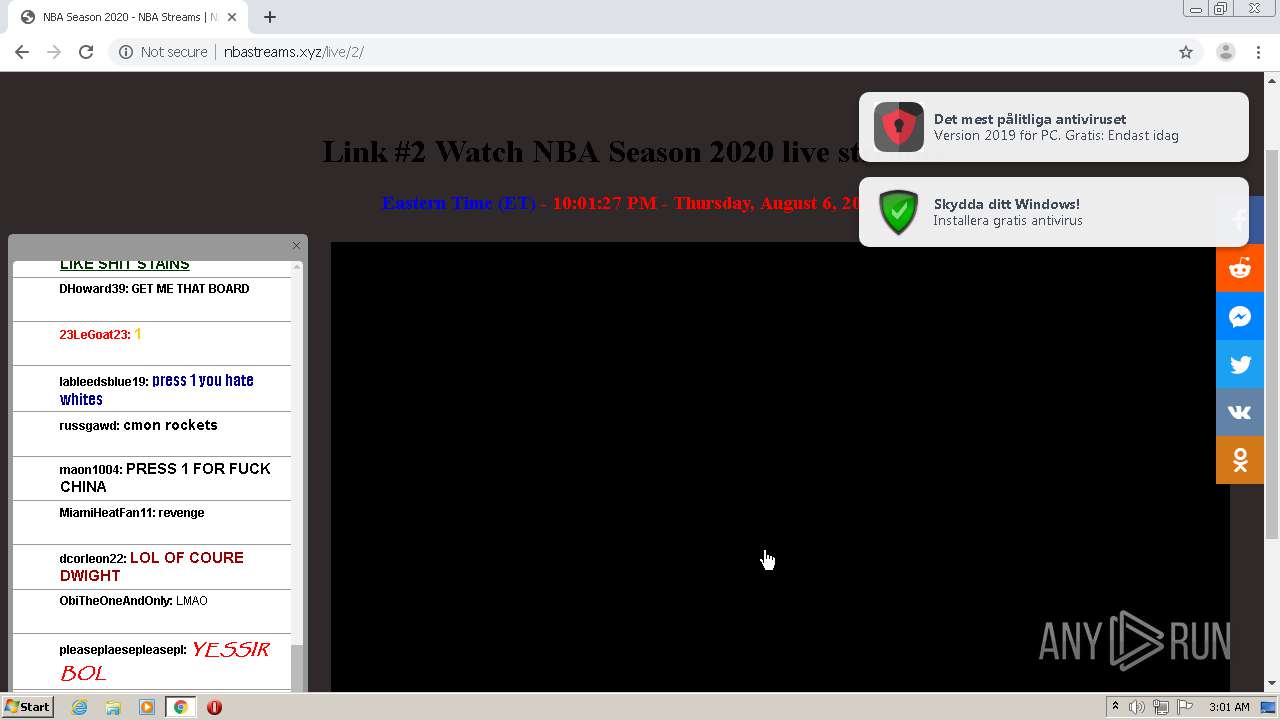
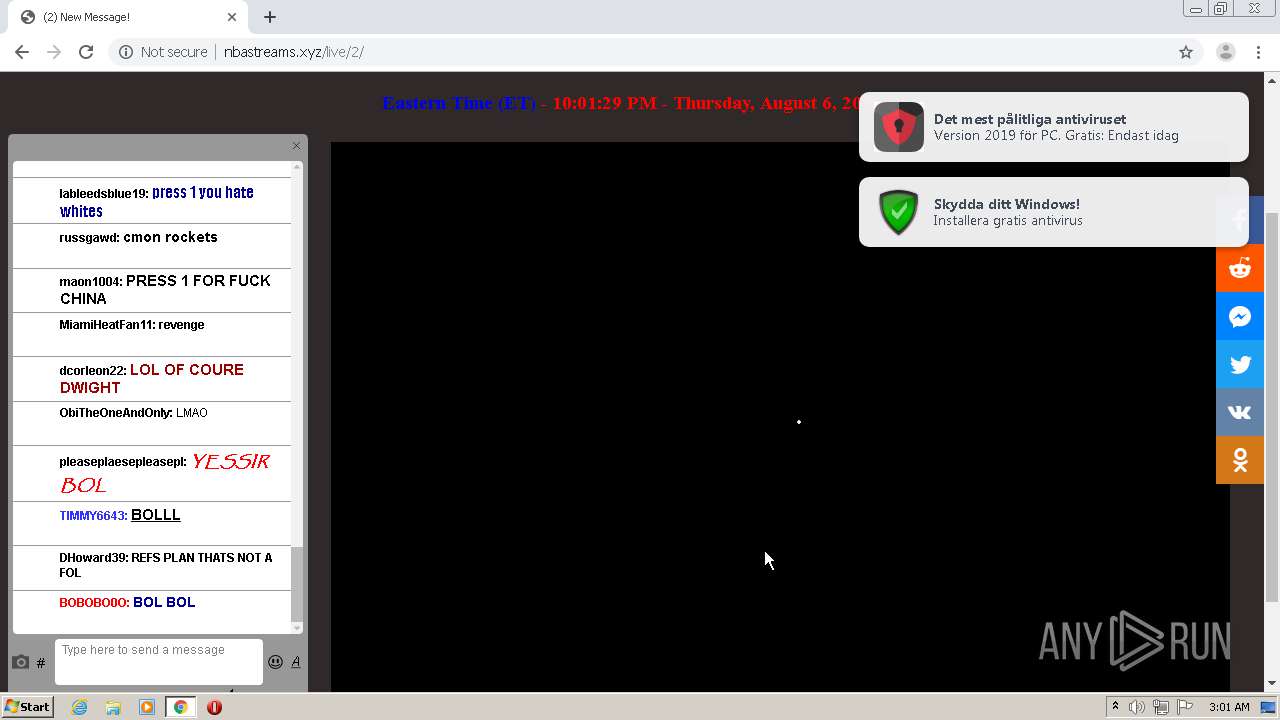
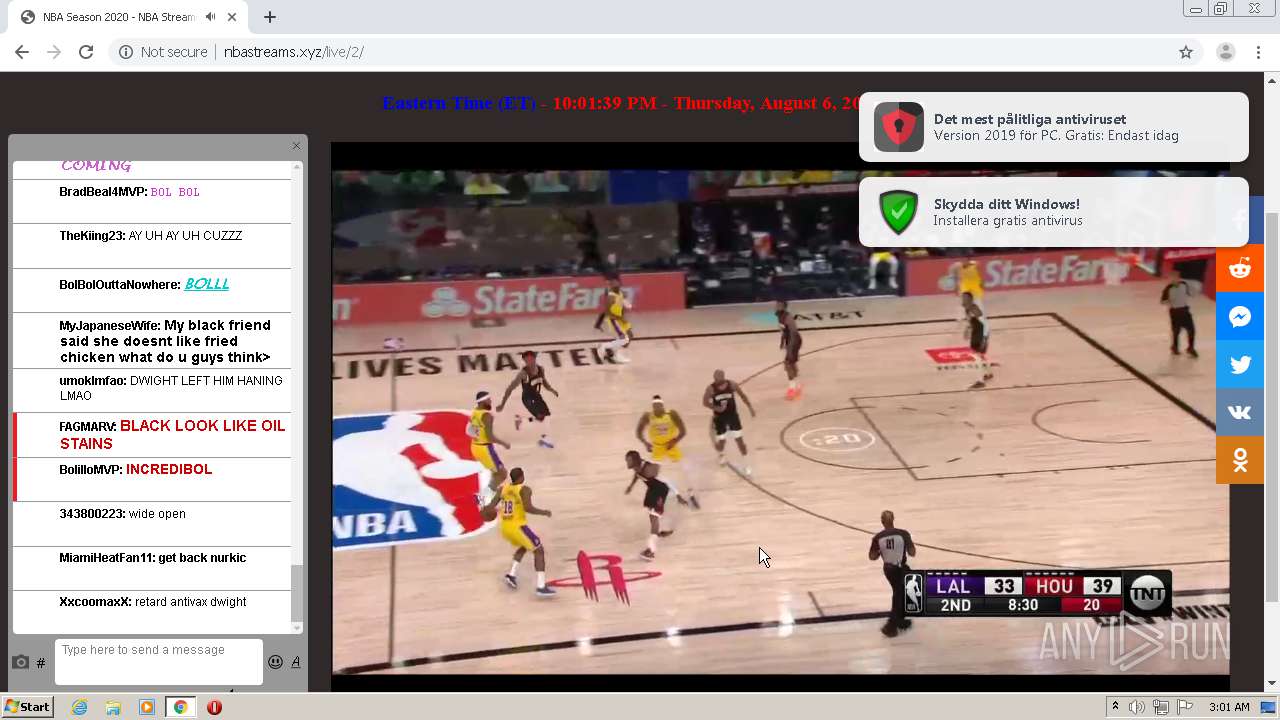
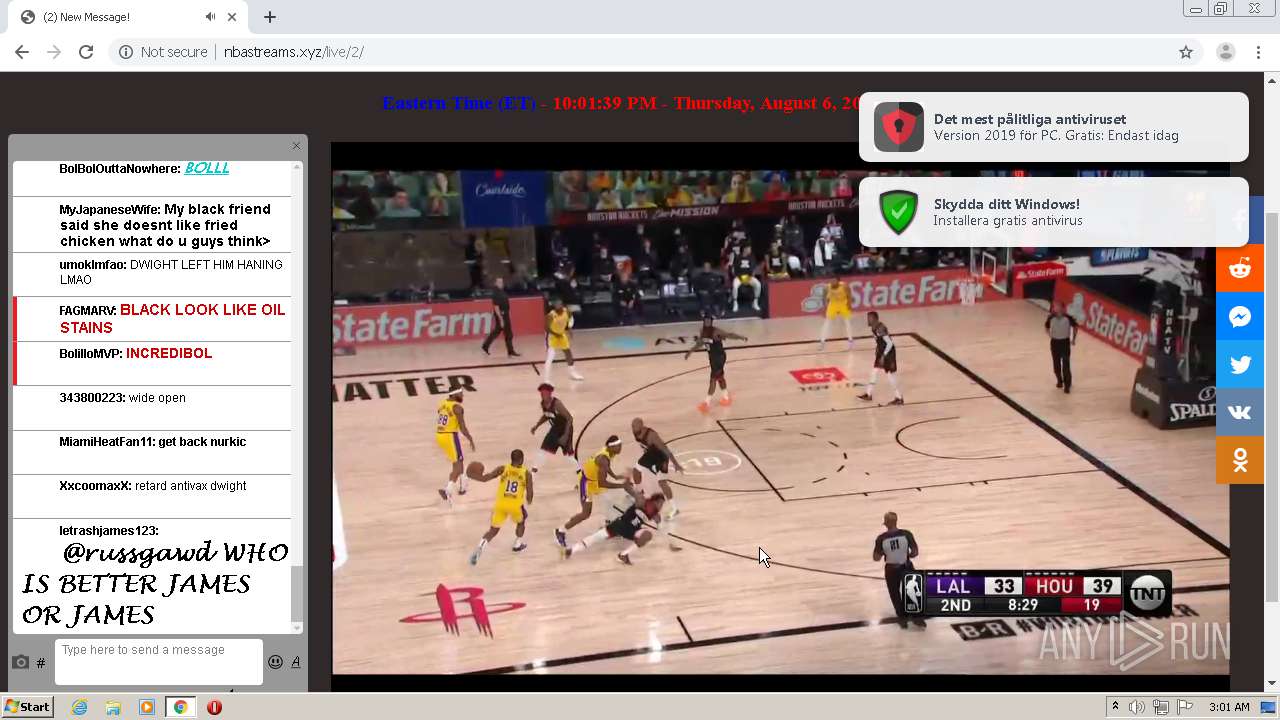
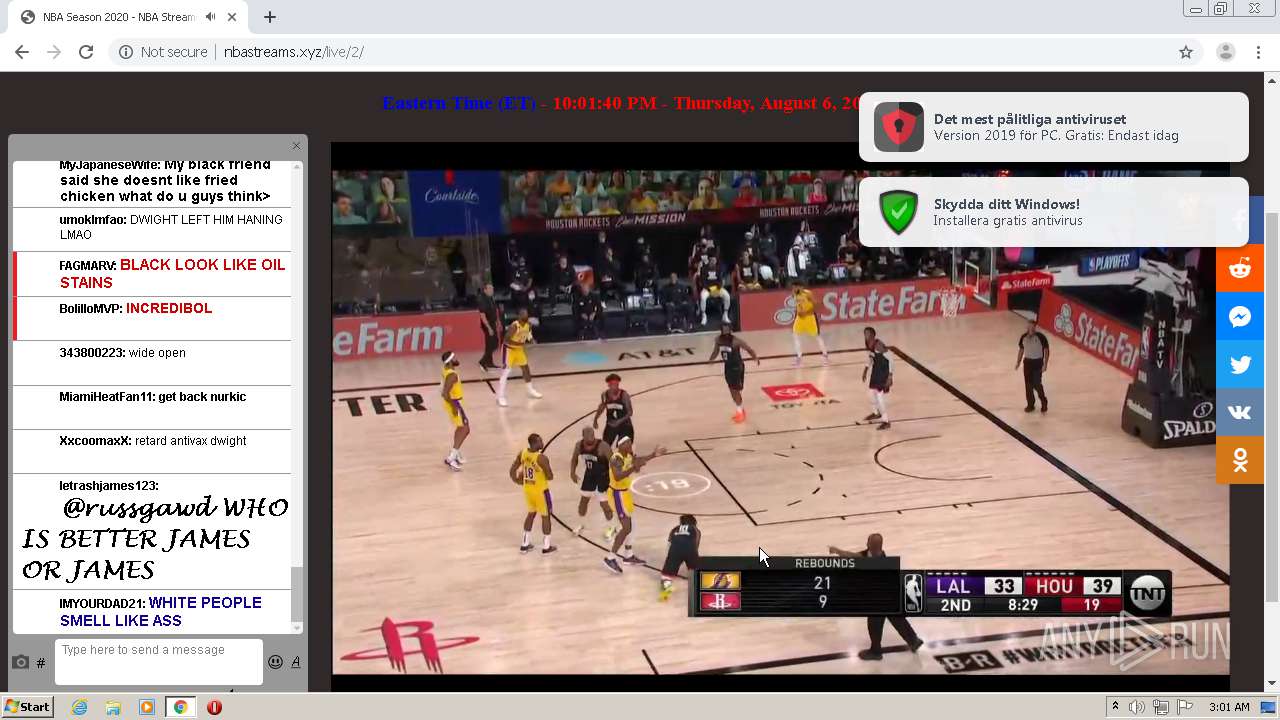
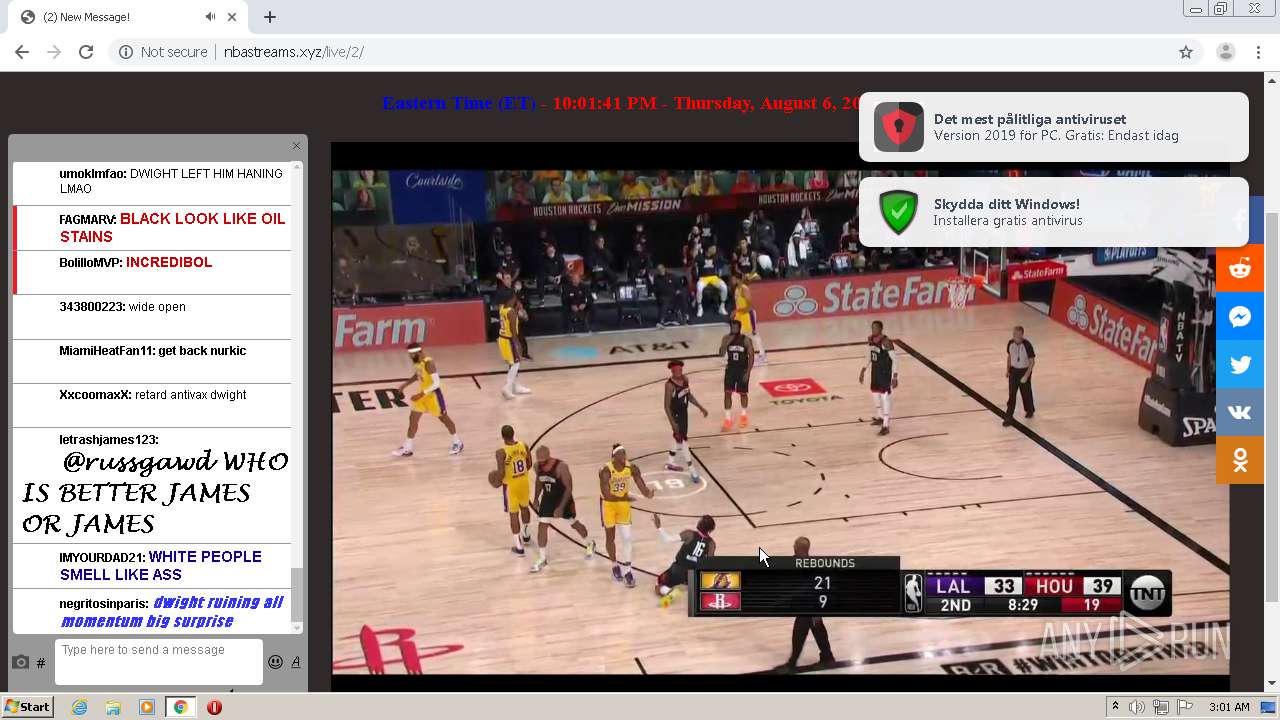
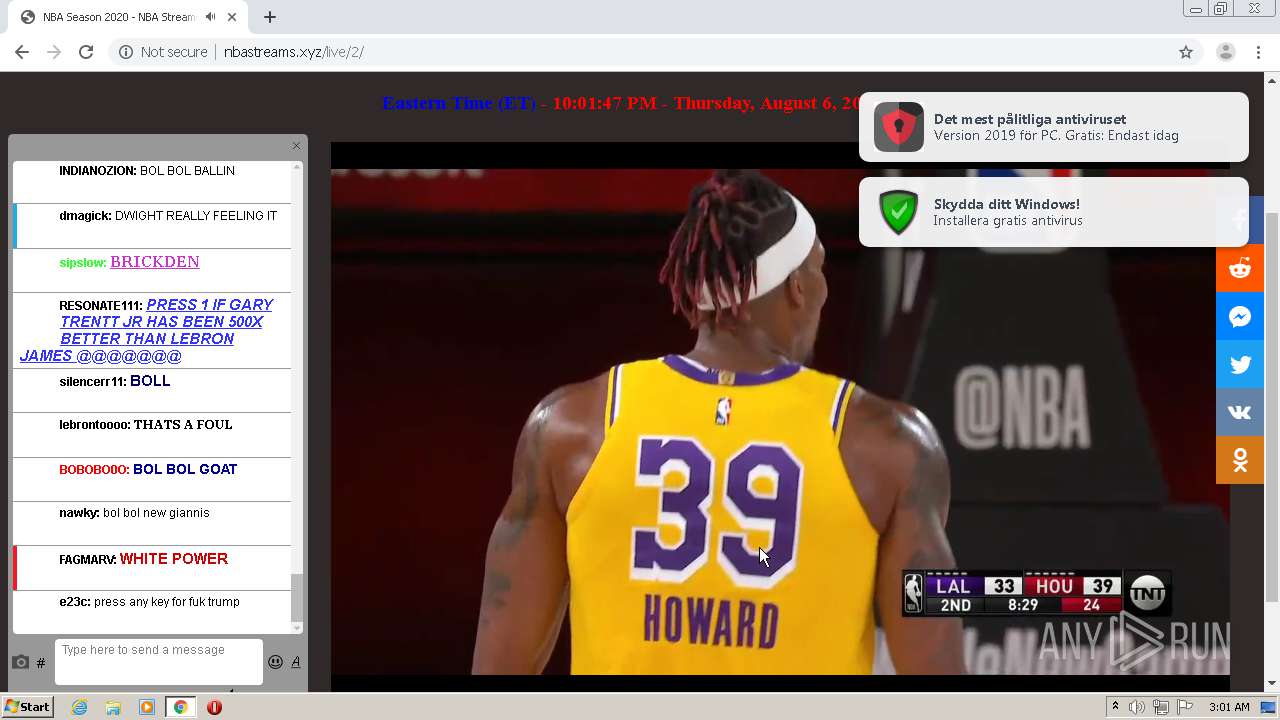
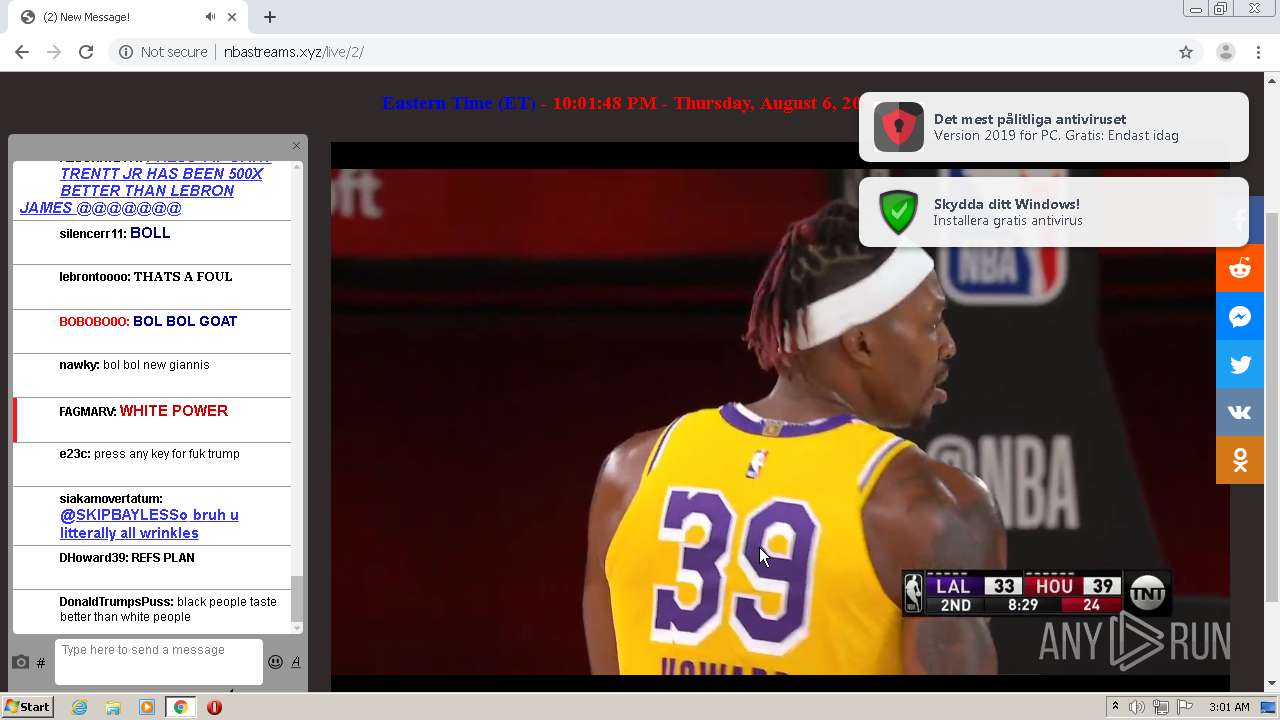
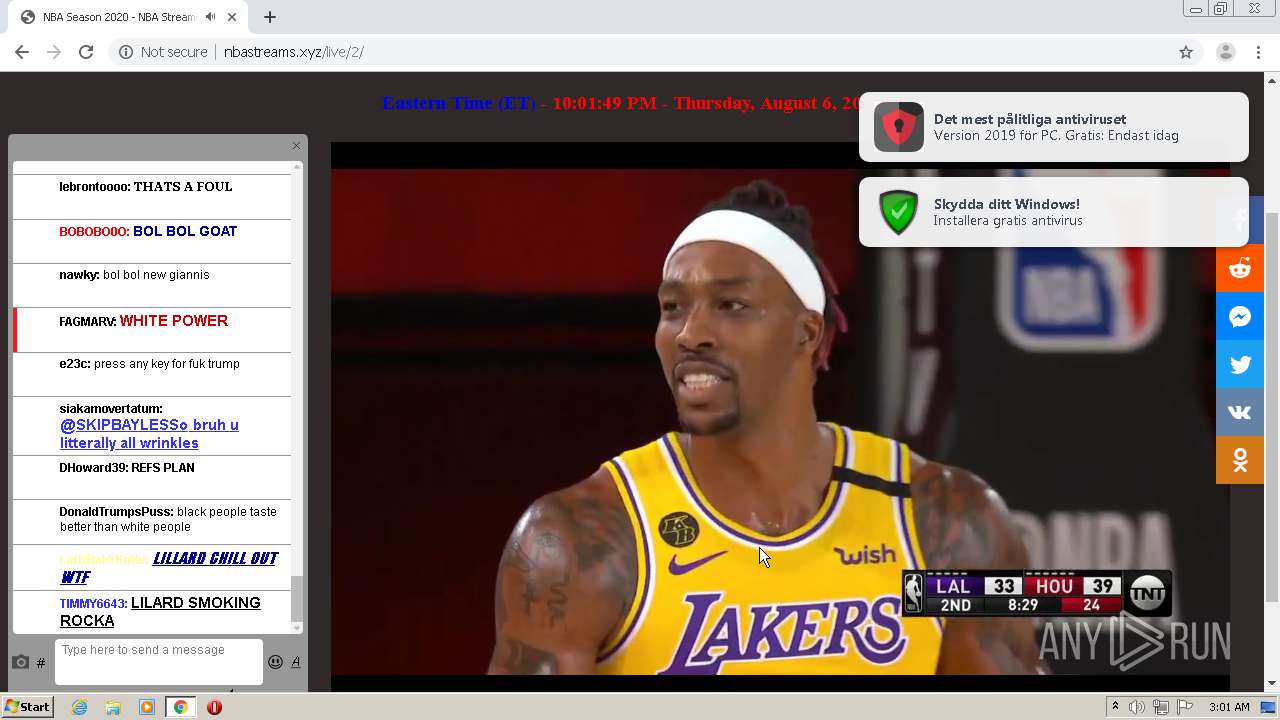
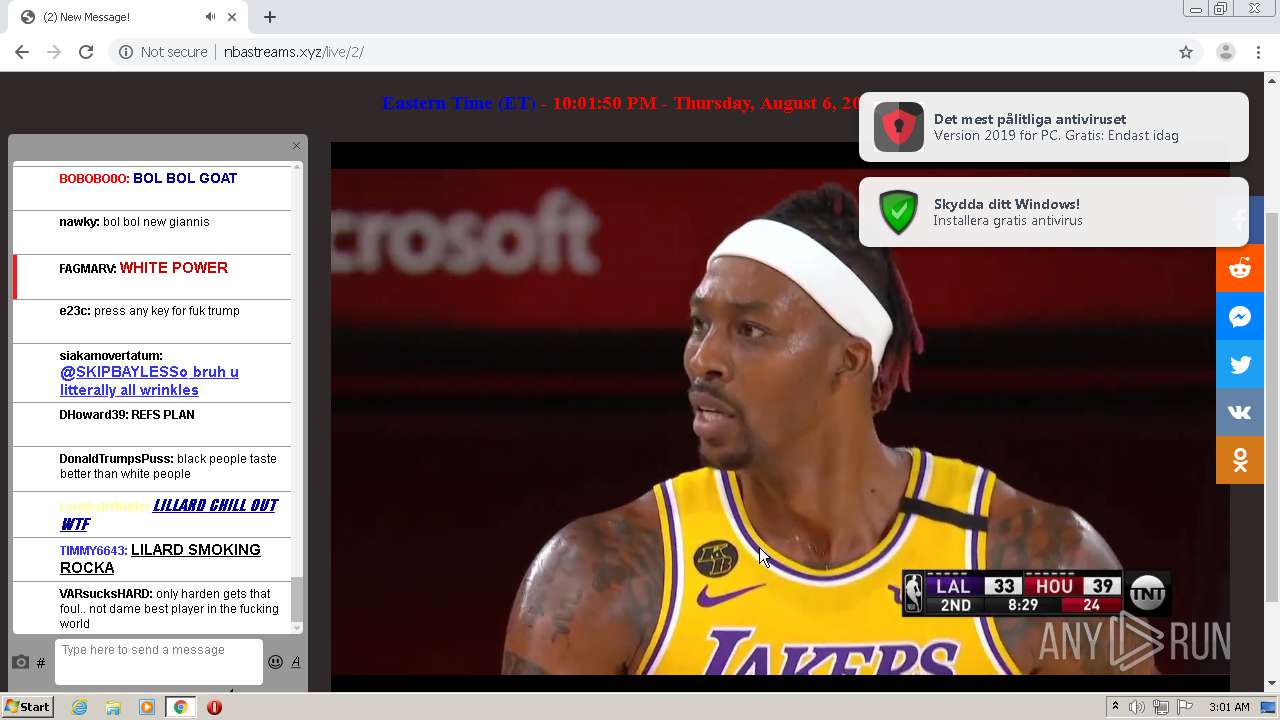
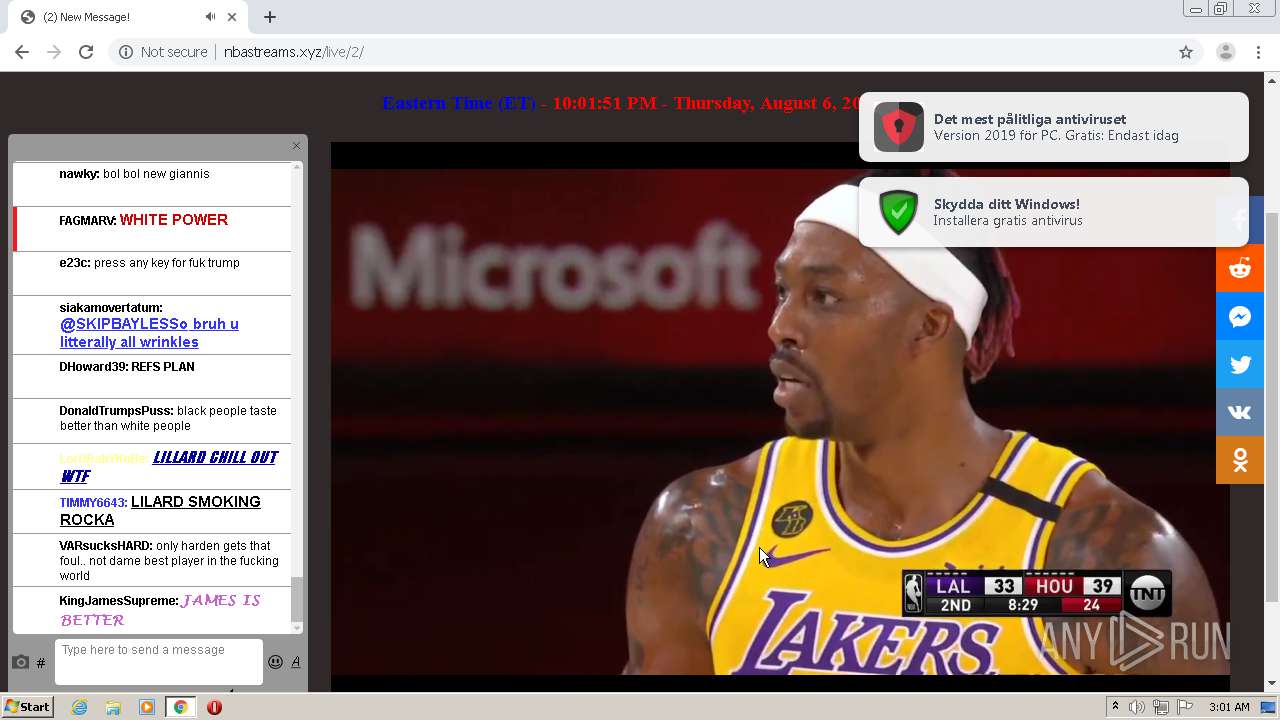
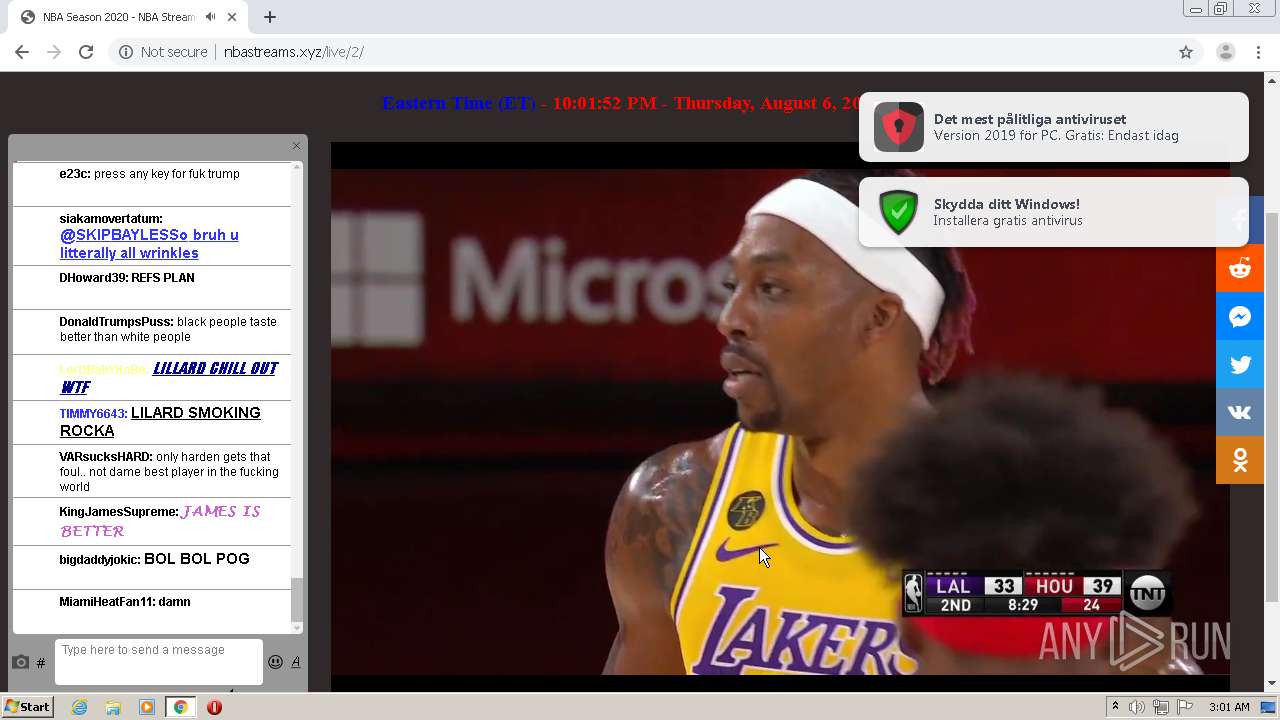
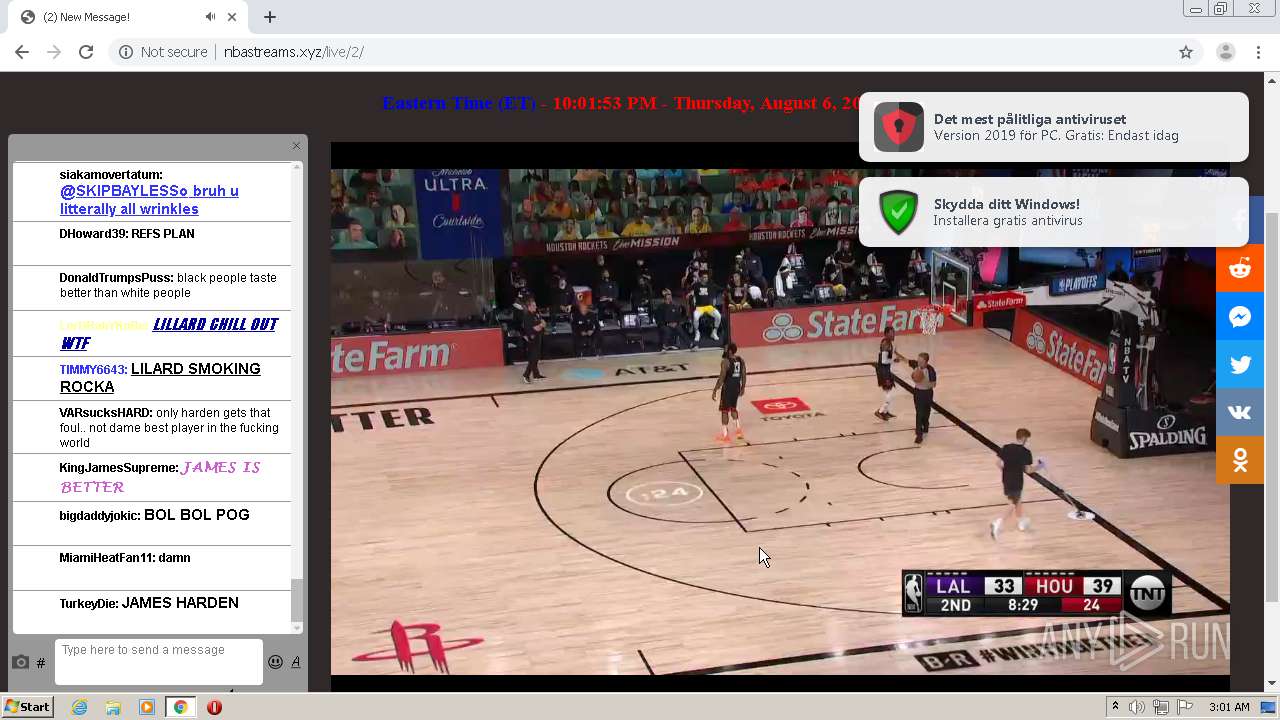
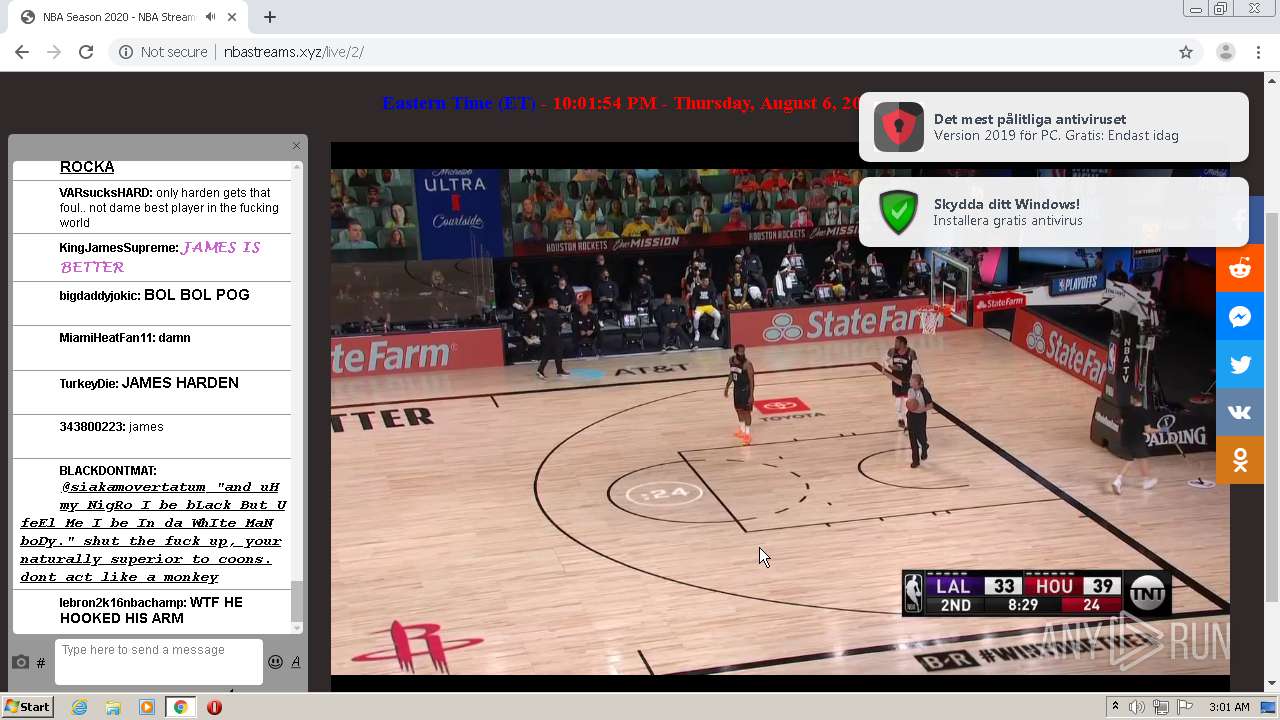
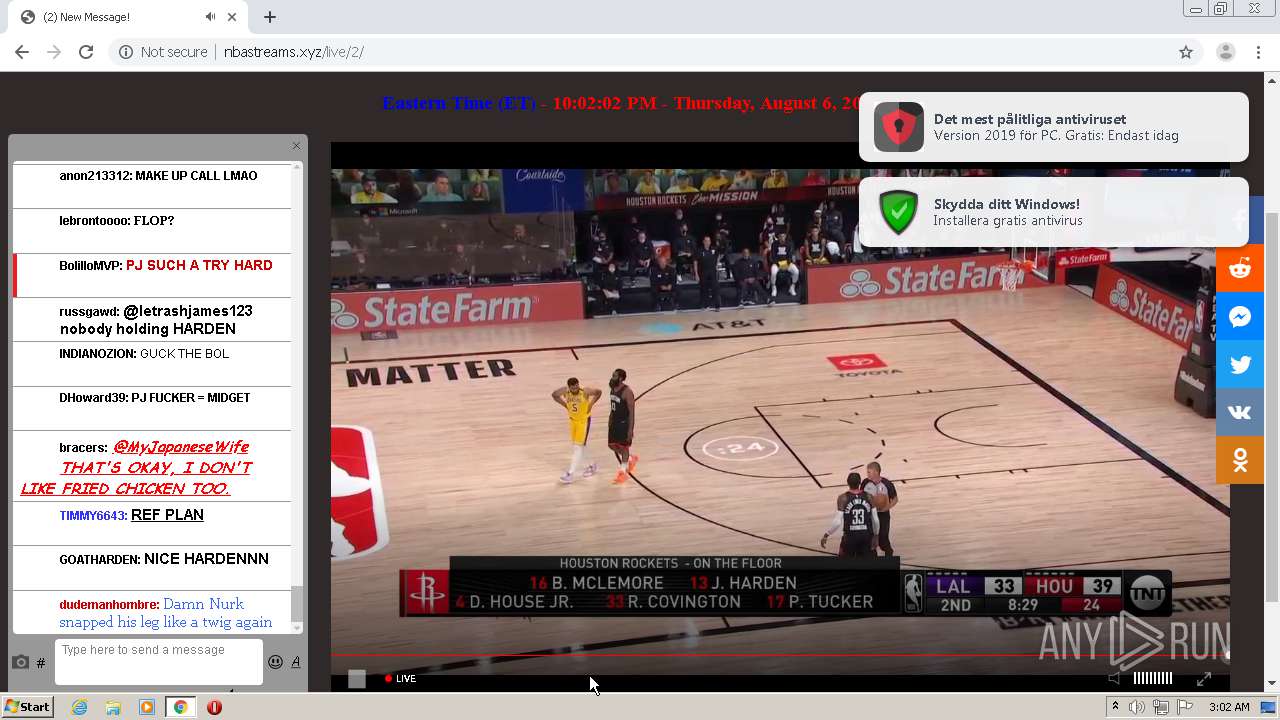
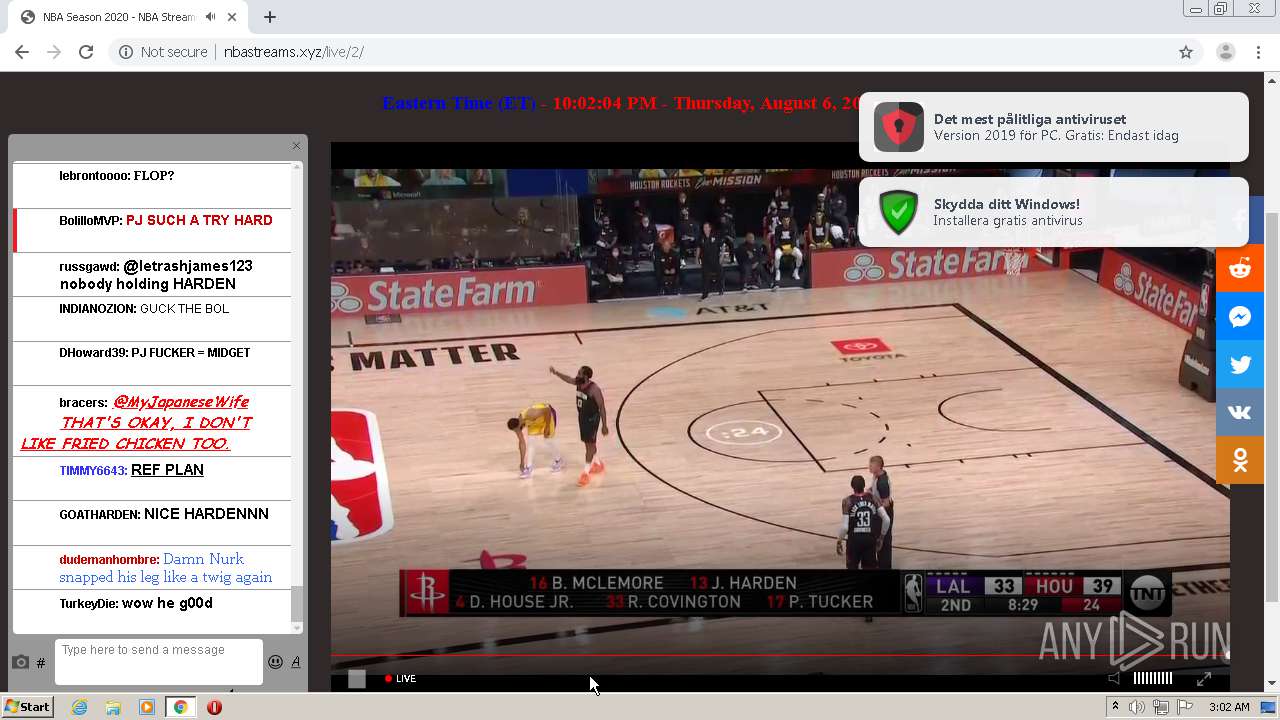
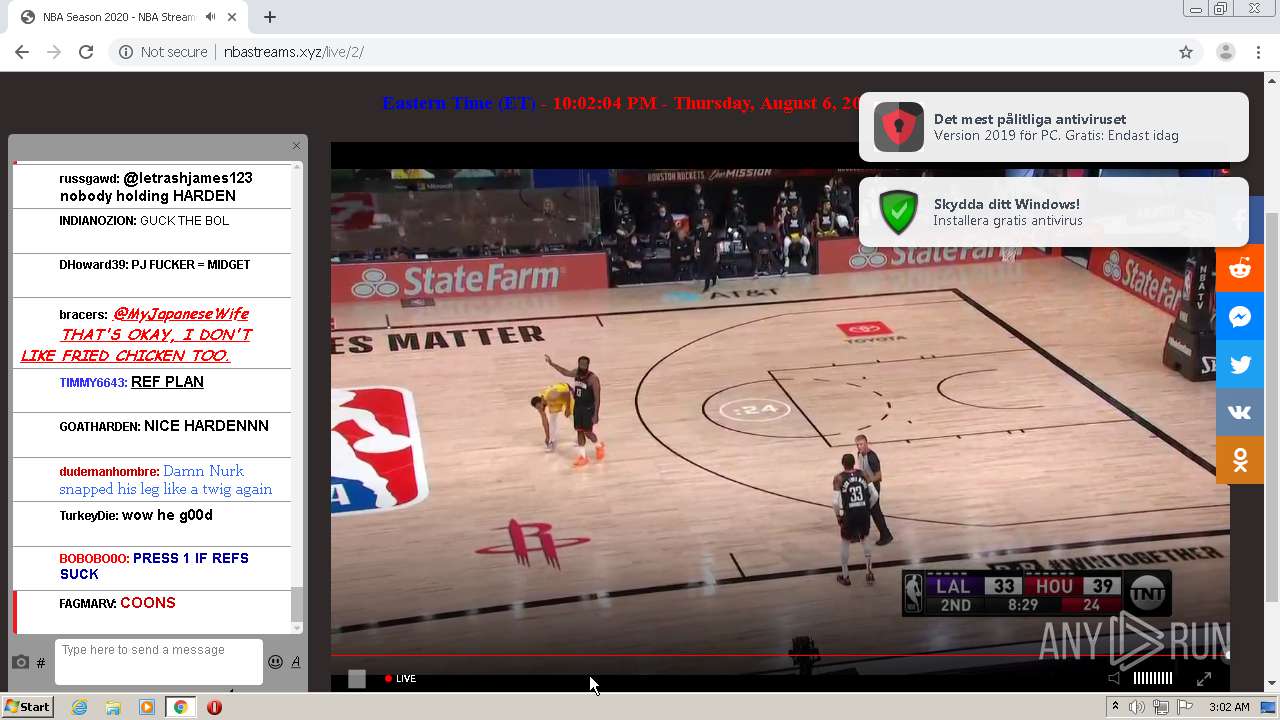
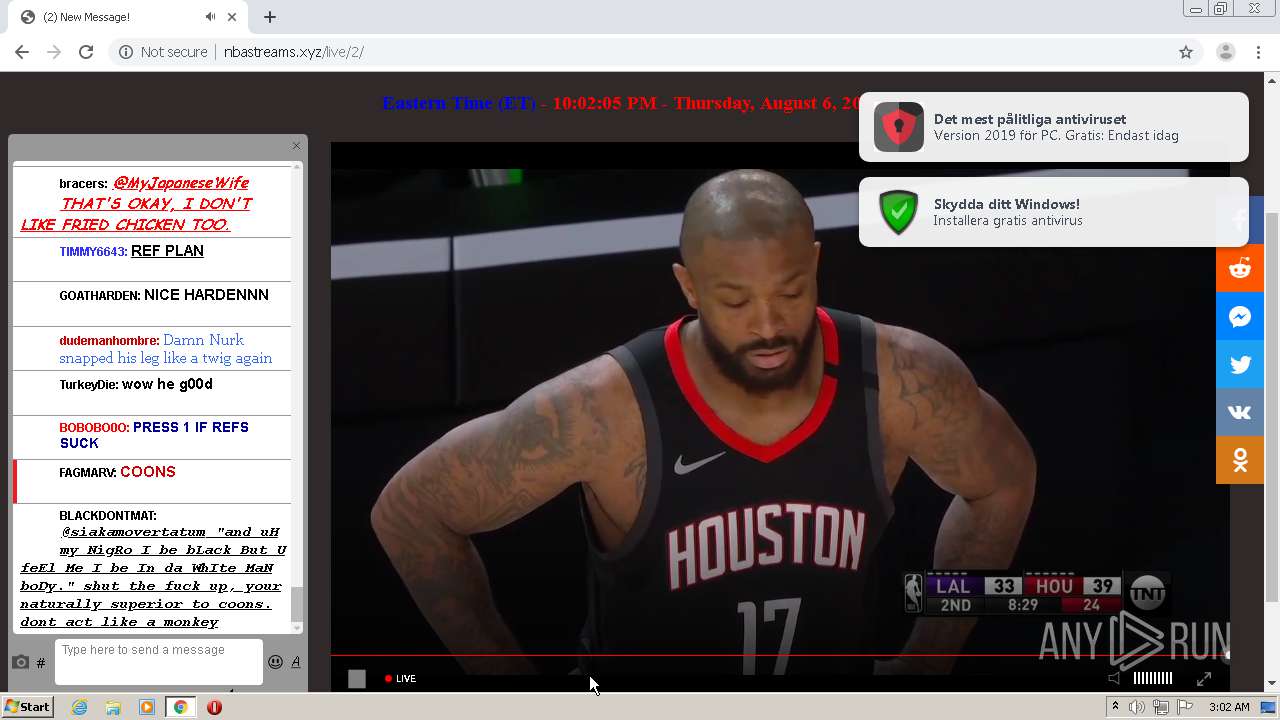
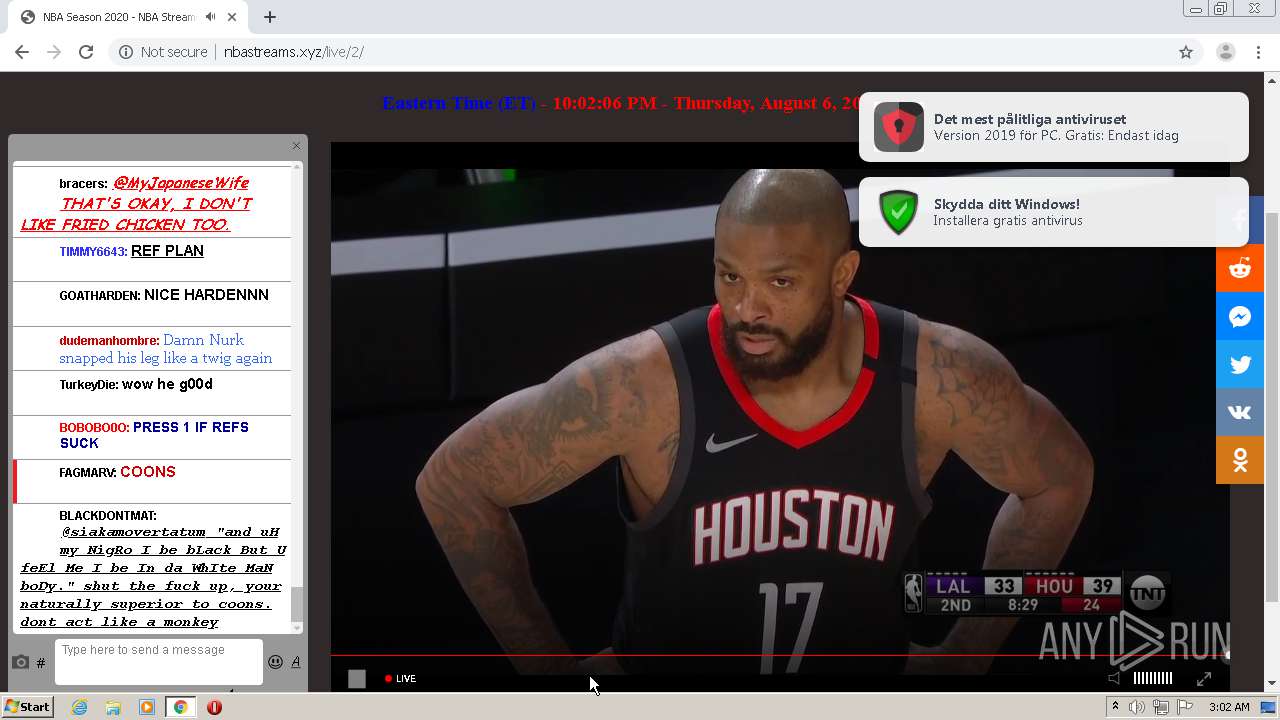
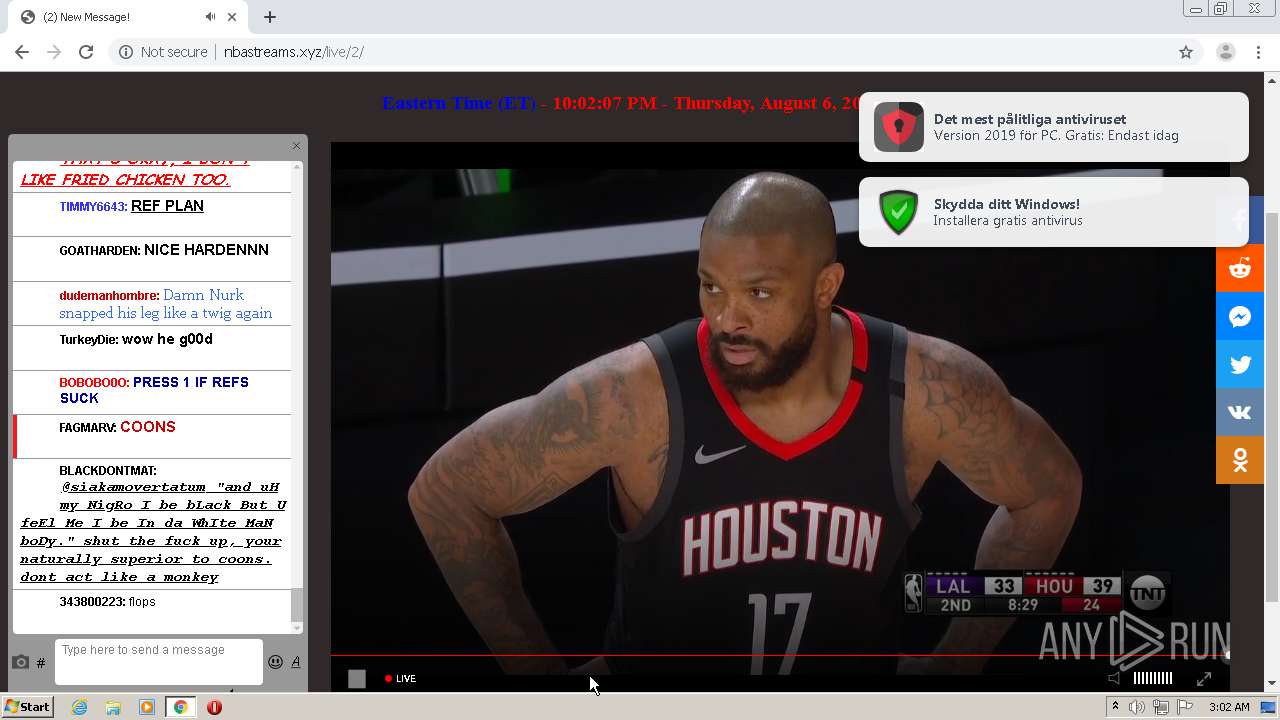
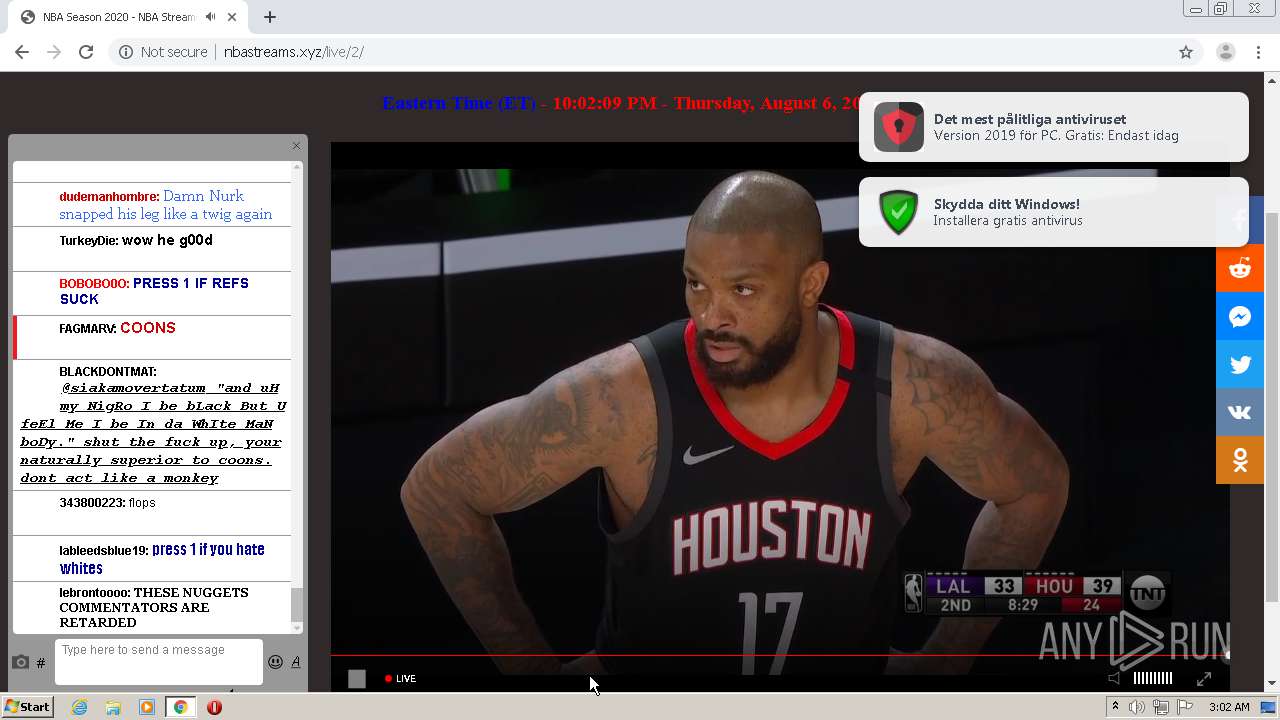
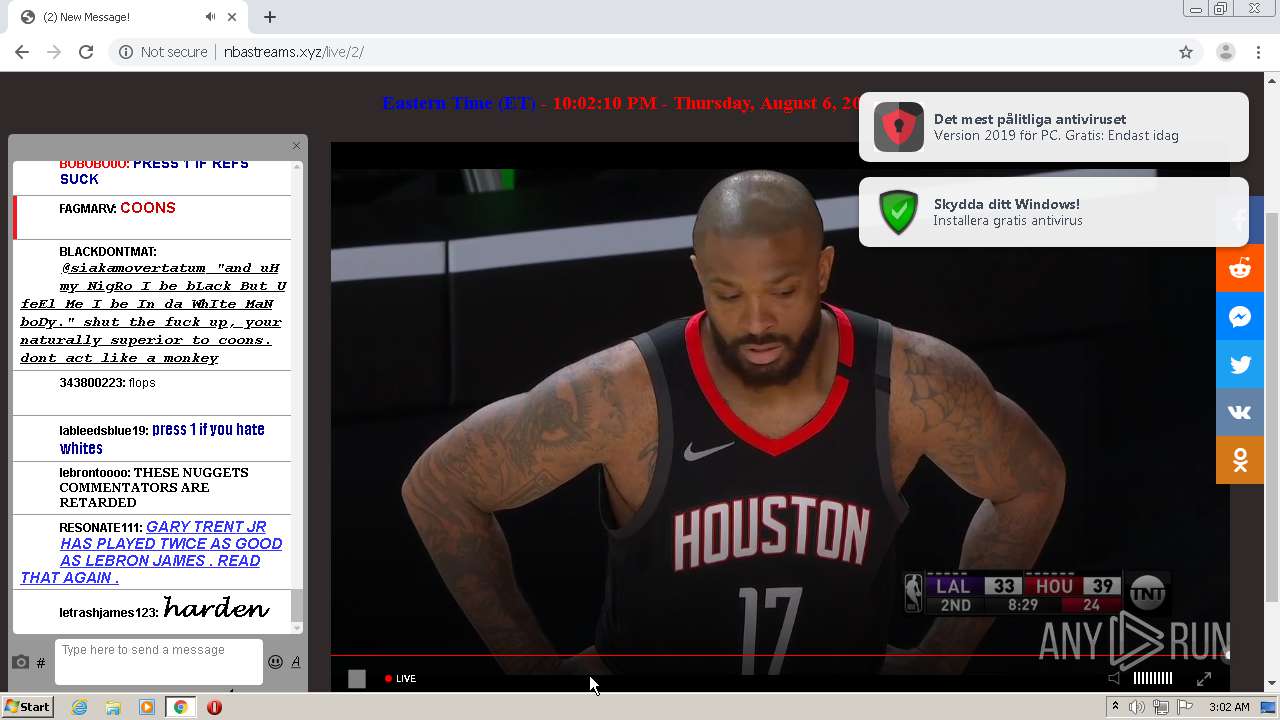
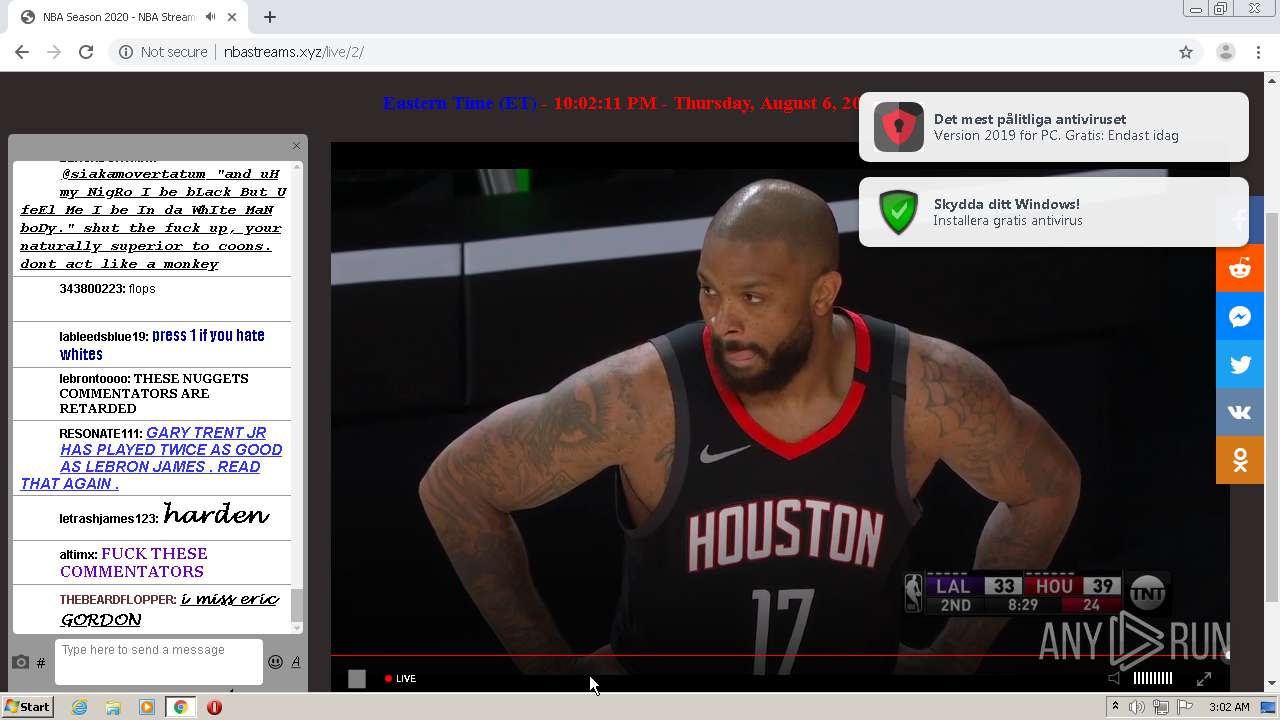
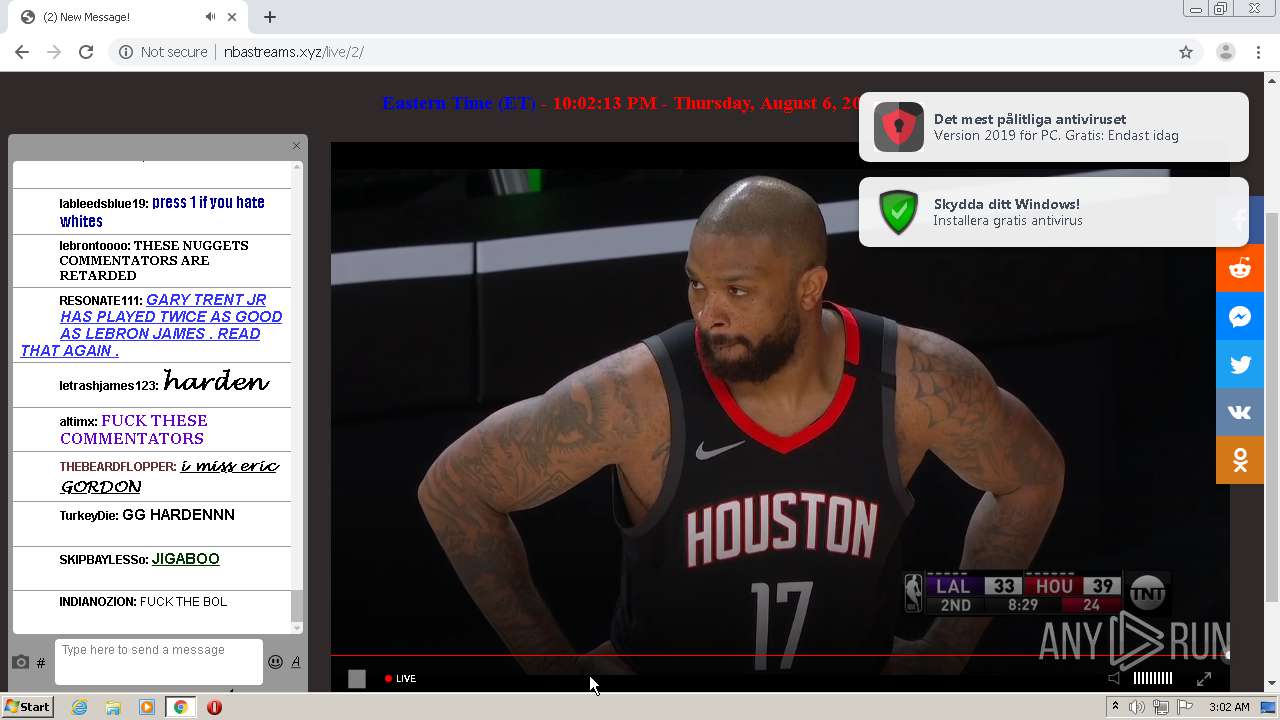
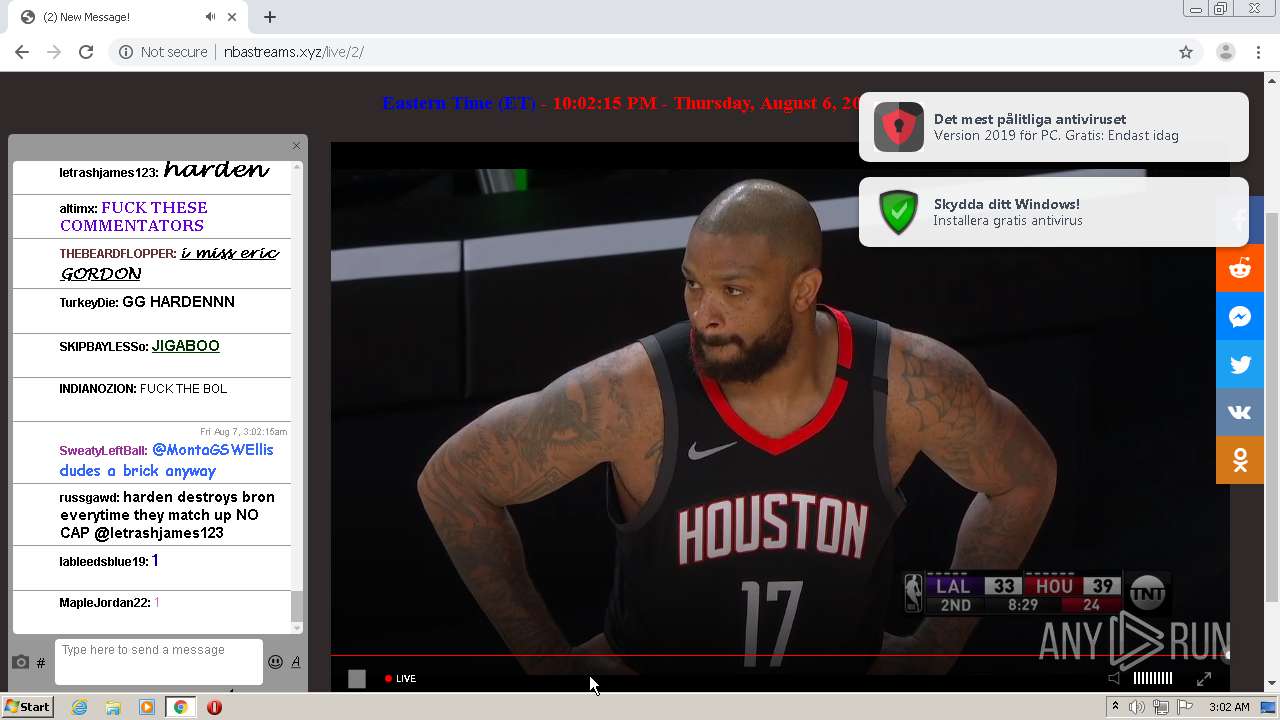
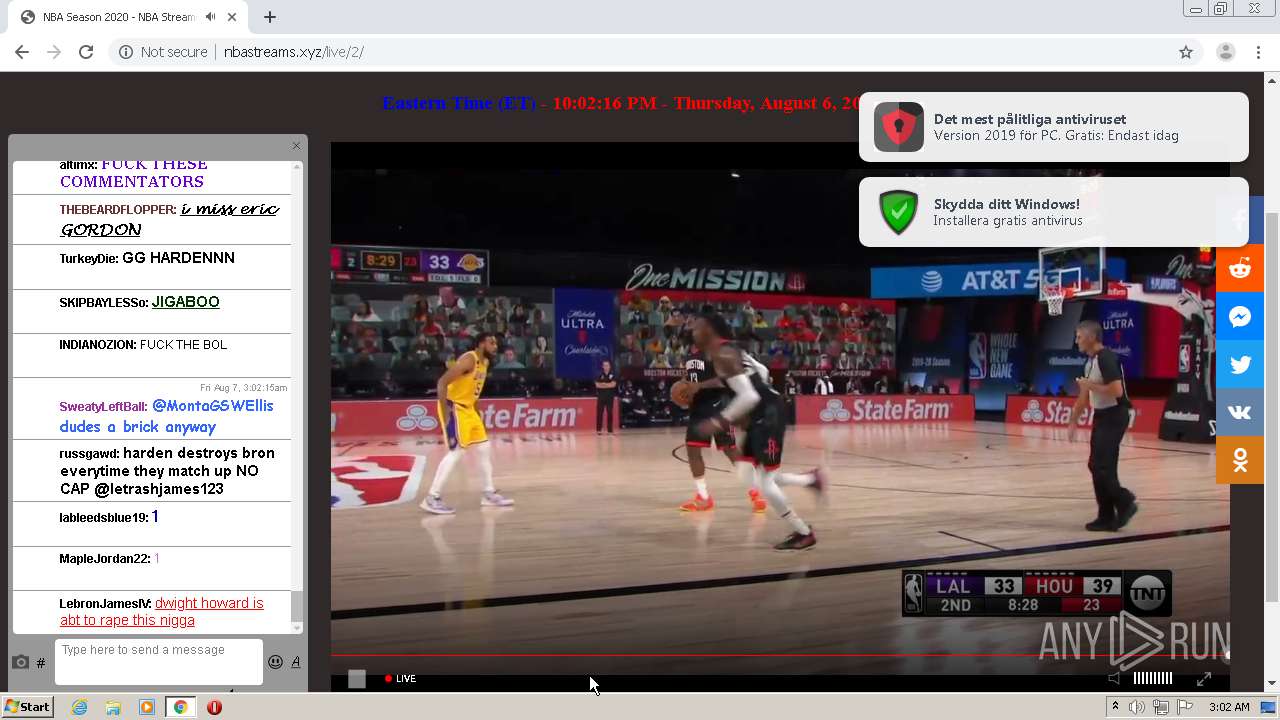
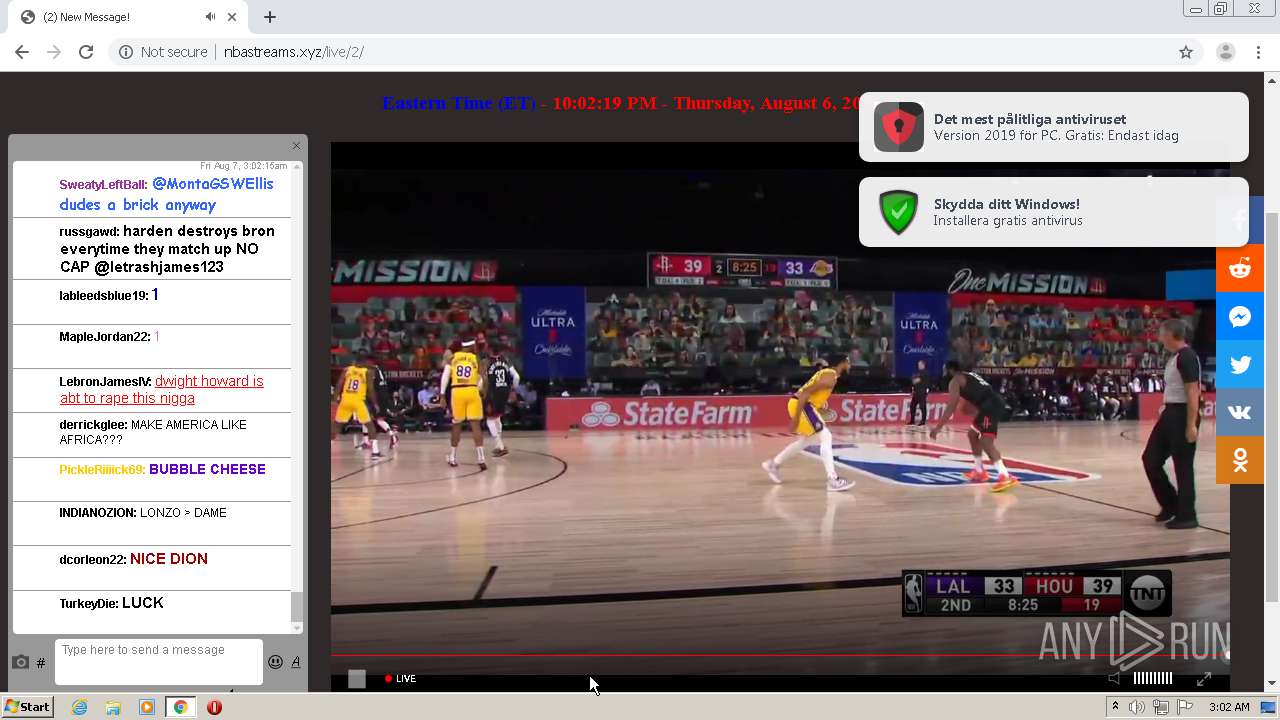
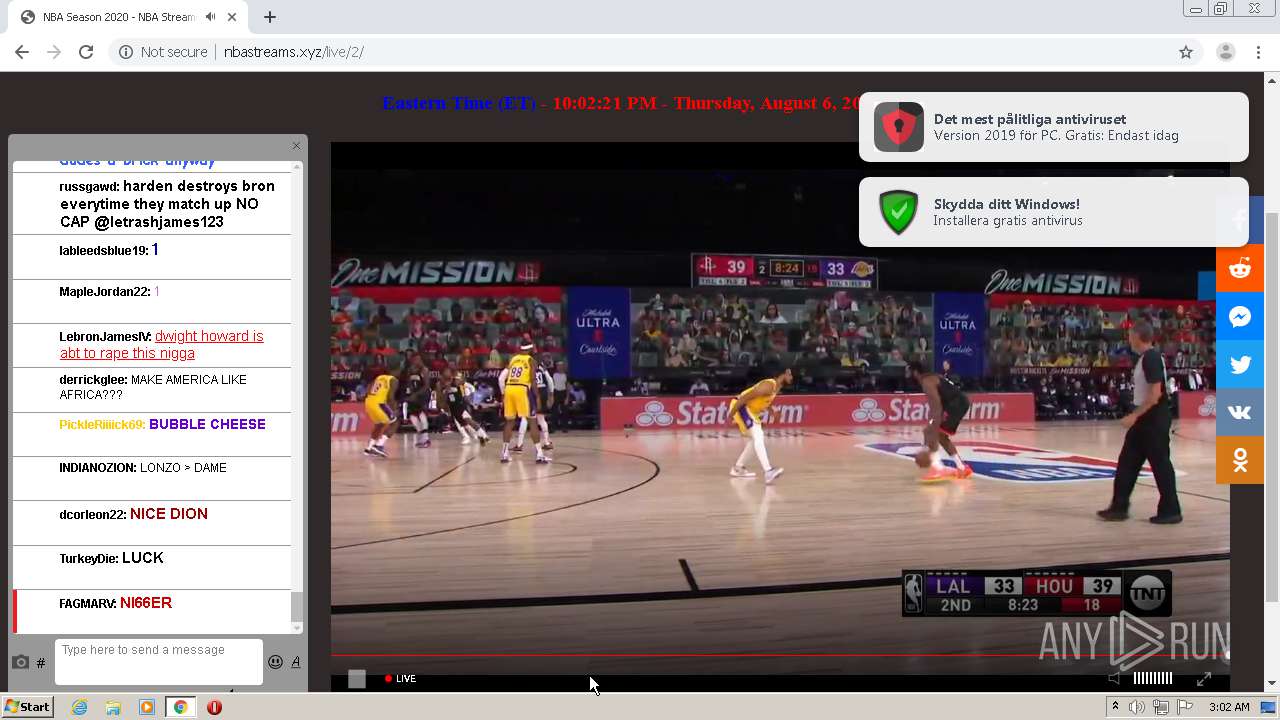
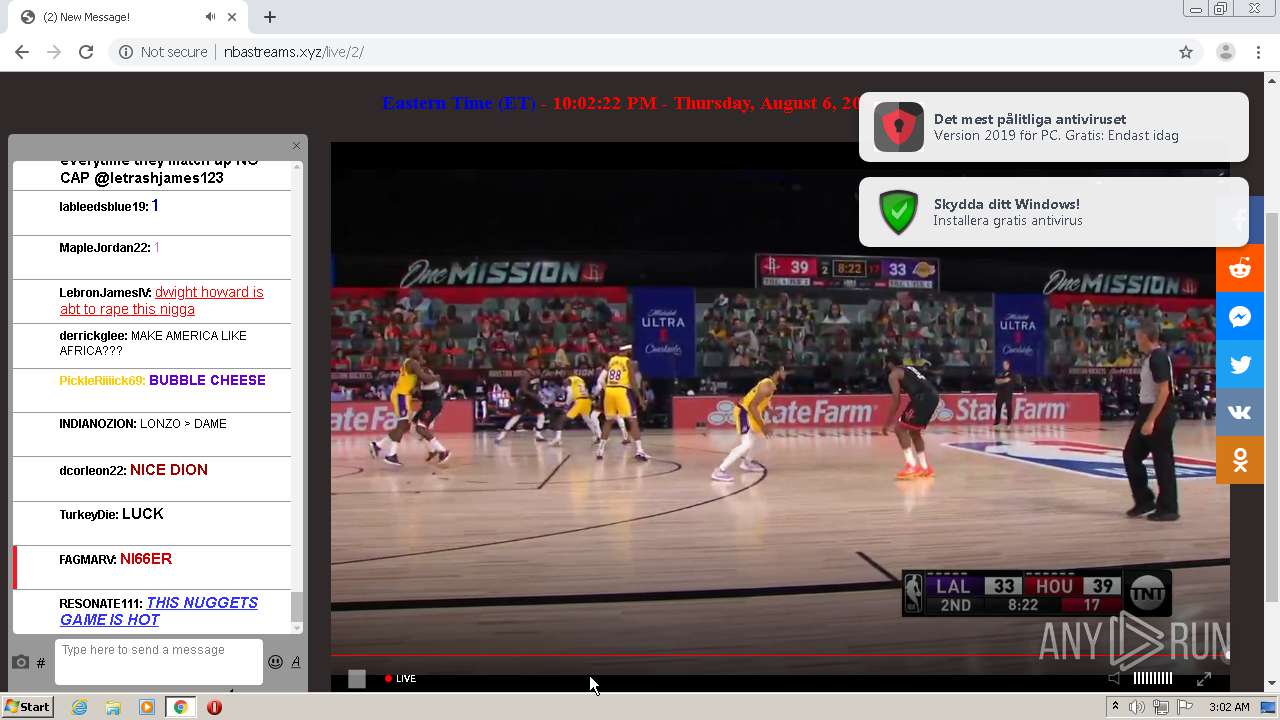
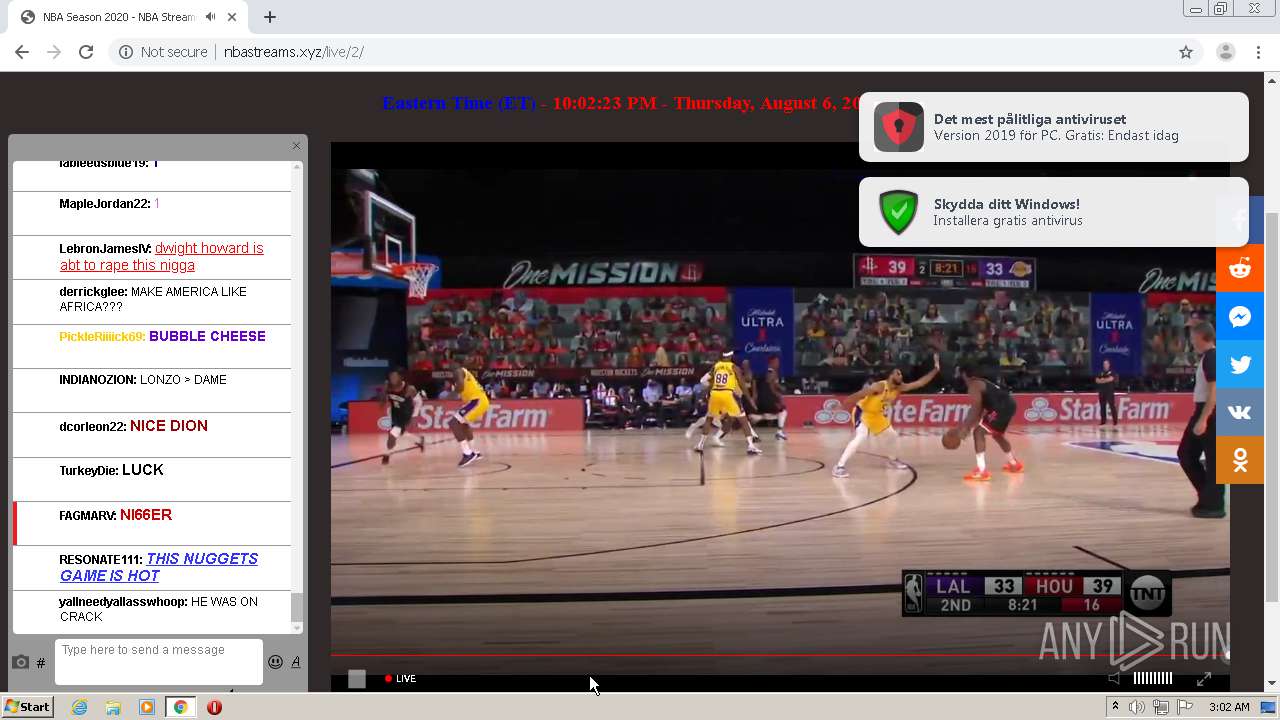
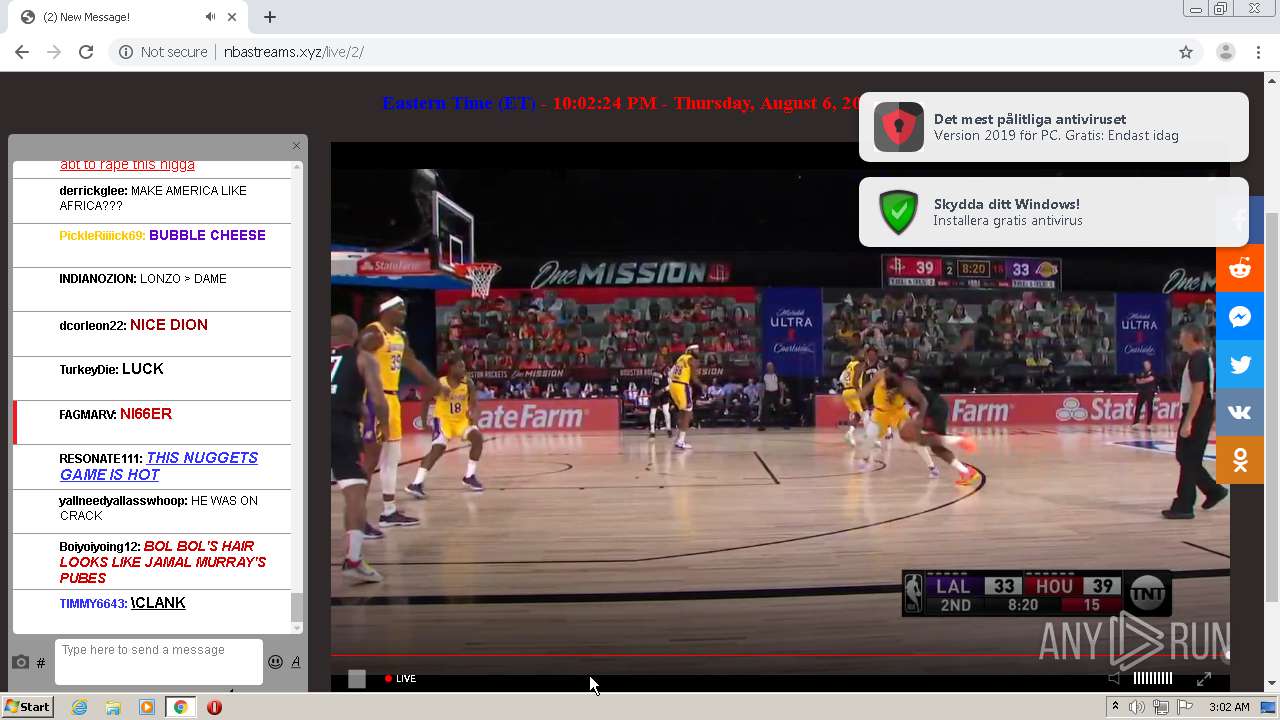
940 | chrome.exe | GET | 200 | 172.64.195.14:80 | http://nbastreams.xyz/live/2/ | US | html | 2.37 Kb | malicious |
940 | chrome.exe | GET | 200 | 172.64.195.14:80 | http://nbastreams.xyz/crack_stream1.js | US | text | 2.29 Kb | malicious |
940 | chrome.exe | GET | 200 | 172.64.140.2:80 | http://nbastreams123.xyz/nba/nop/1.php | US | html | 733 b | malicious |
940 | chrome.exe | GET | 200 | 172.67.205.2:80 | http://w.24timezones.com/l.js | US | text | 7.60 Kb | suspicious |
940 | chrome.exe | GET | 200 | 208.93.230.28:80 | http://st.chatango.com/js/gz/emb.js | US | text | 24.0 Kb | whitelisted |
940 | chrome.exe | GET | 200 | 172.217.21.226:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 42.0 Kb | whitelisted |
940 | chrome.exe | GET | 200 | 172.64.195.14:80 | http://nbastreams.xyz/config.json | US | text | 112 b | malicious |
940 | chrome.exe | GET | 200 | 104.17.173.62:80 | http://velocecdn.com/script/chrome.js | US | text | 11.1 Kb | shared |
940 | chrome.exe | GET | 403 | 139.45.195.59:80 | http://cdn.betgorebysson.club/apu.php?zoneid=3473429 | US | text | 382 b | malicious |
940 | chrome.exe | GET | 200 | 172.64.140.2:80 | http://nbastreams123.xyz/nba/tnt/1.php | US | html | 647 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
940 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
940 | chrome.exe | 172.64.140.2:80 | nbastreams123.xyz | Cloudflare Inc | US | shared |
940 | chrome.exe | 104.16.133.229:443 | ajax.cloudflare.com | Cloudflare Inc | US | suspicious |
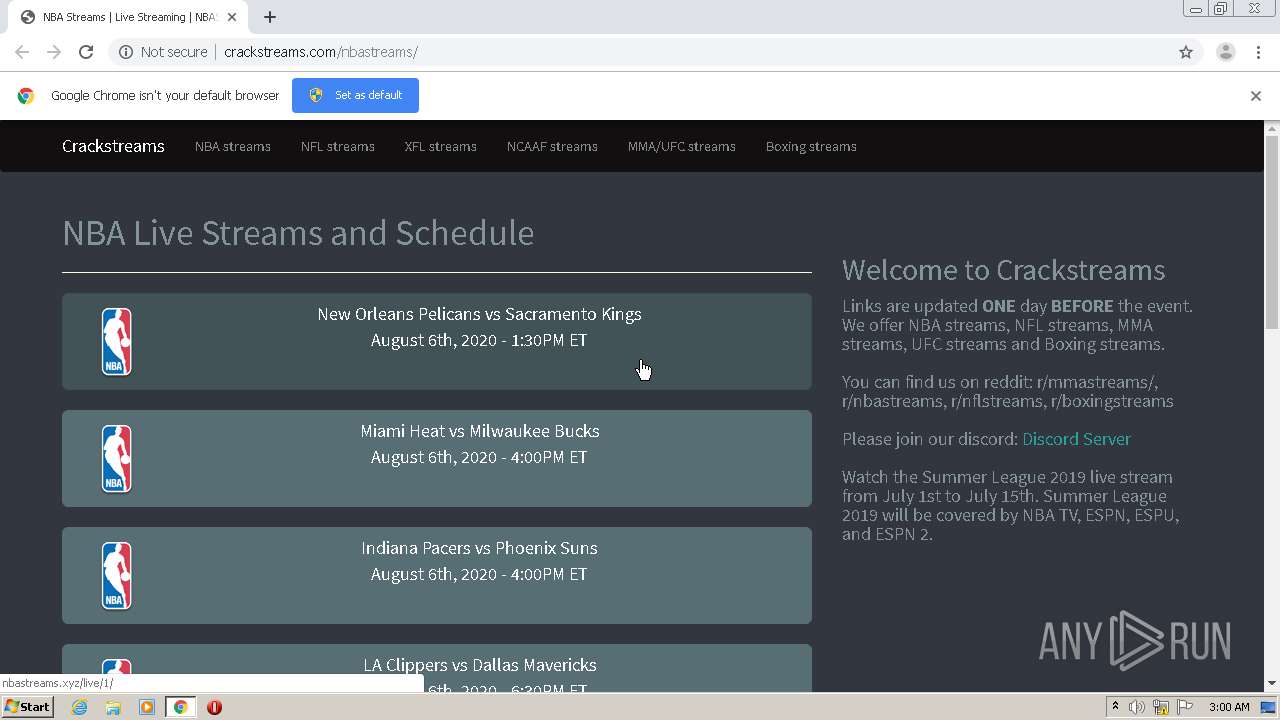
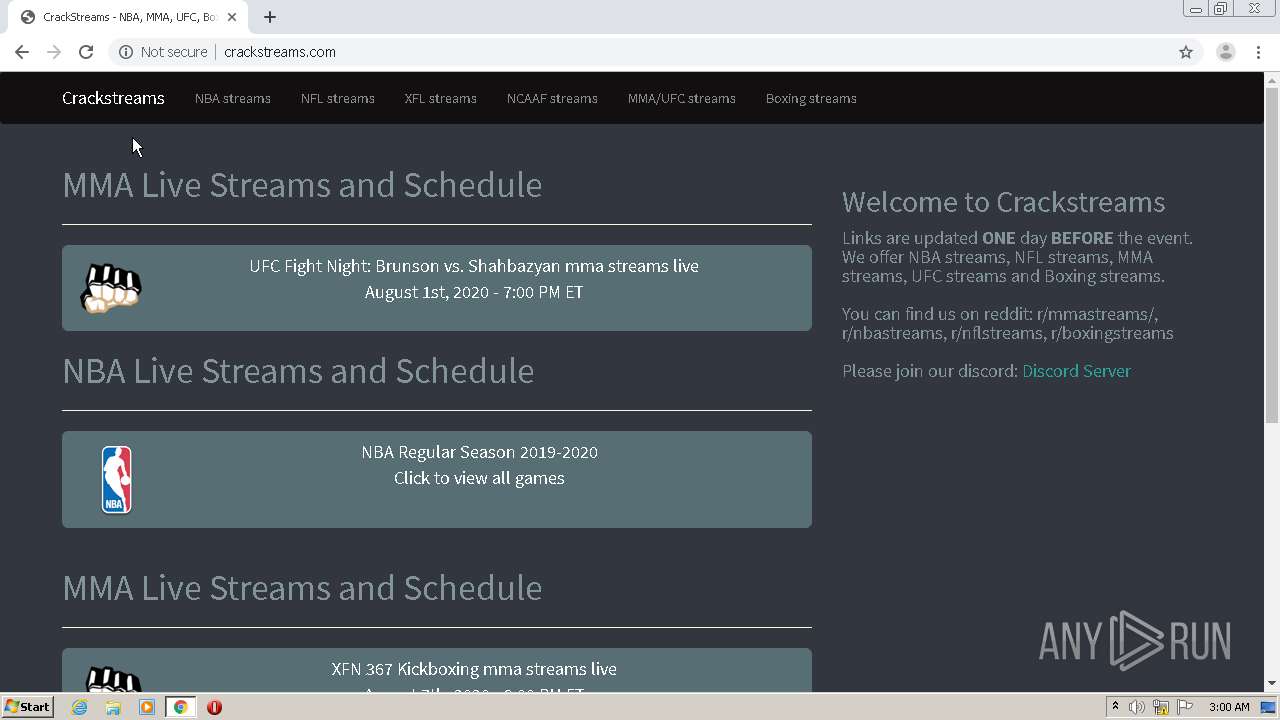
940 | chrome.exe | 172.64.167.5:80 | crackstreams.com | Cloudflare Inc | US | shared |
940 | chrome.exe | 172.217.23.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
940 | chrome.exe | 172.217.16.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
940 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
940 | chrome.exe | 172.64.195.14:80 | nbastreams.xyz | Cloudflare Inc | US | suspicious |
940 | chrome.exe | 139.45.196.10:80 | inpagepush.com | — | US | unknown |
940 | chrome.exe | 172.67.205.2:80 | w.24timezones.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nbastreams123.xyz |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
cdn.jsdelivr.net |
| whitelisted |
crackstreams.com |
| malicious |
ajax.cloudflare.com |
| whitelisted |
discord.gg |
| whitelisted |
nbastreams.xyz |
| malicious |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
940 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
940 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
940 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
940 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
940 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
940 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
940 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
940 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
940 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
940 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1 ETPRO signatures available at the full report