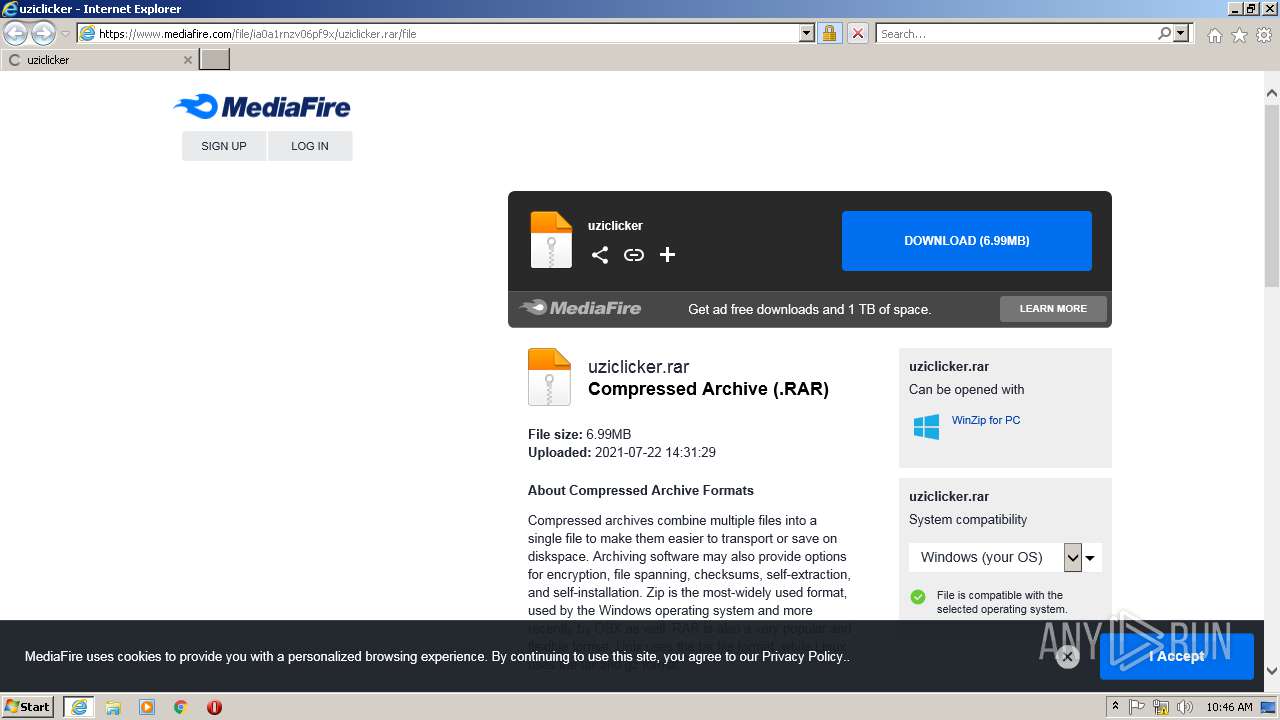
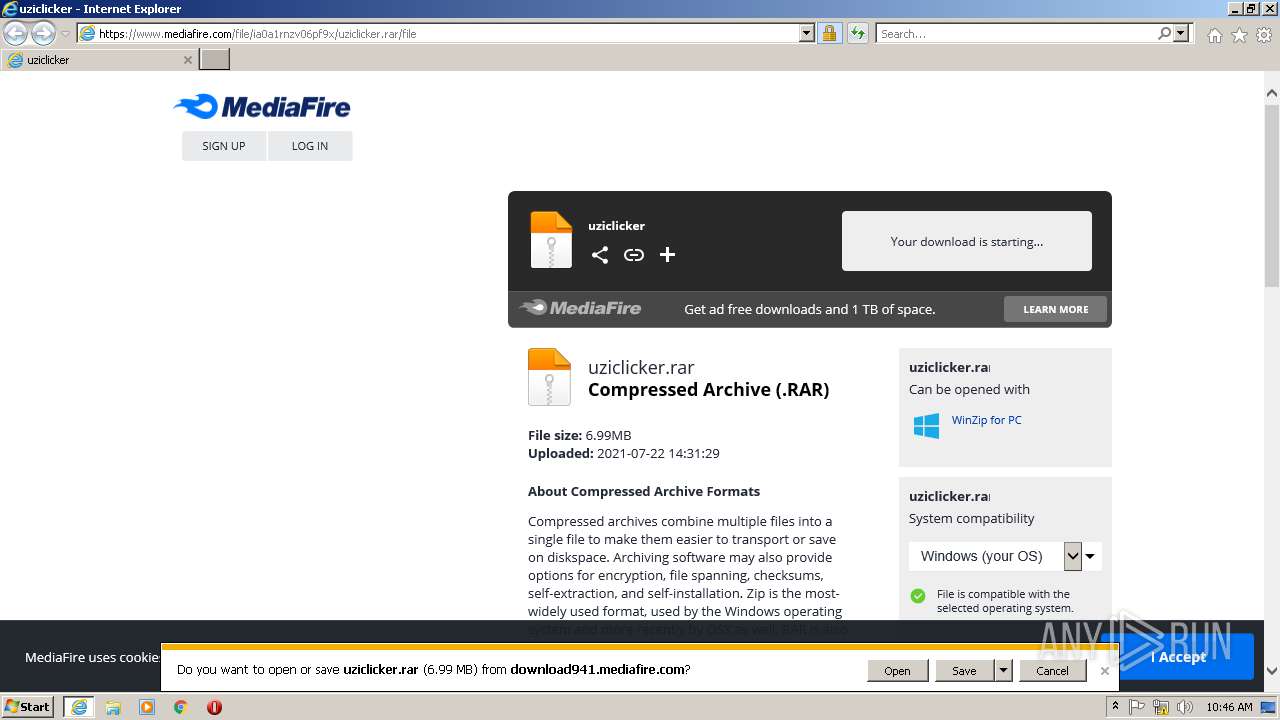
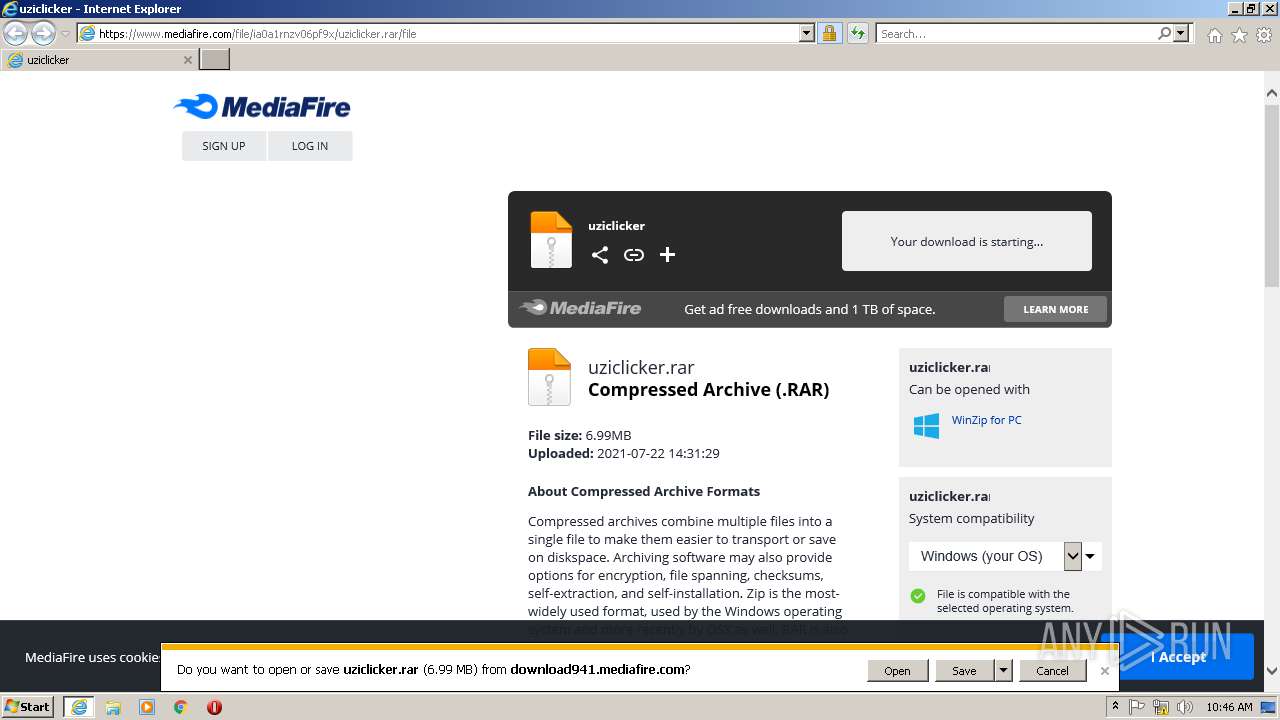
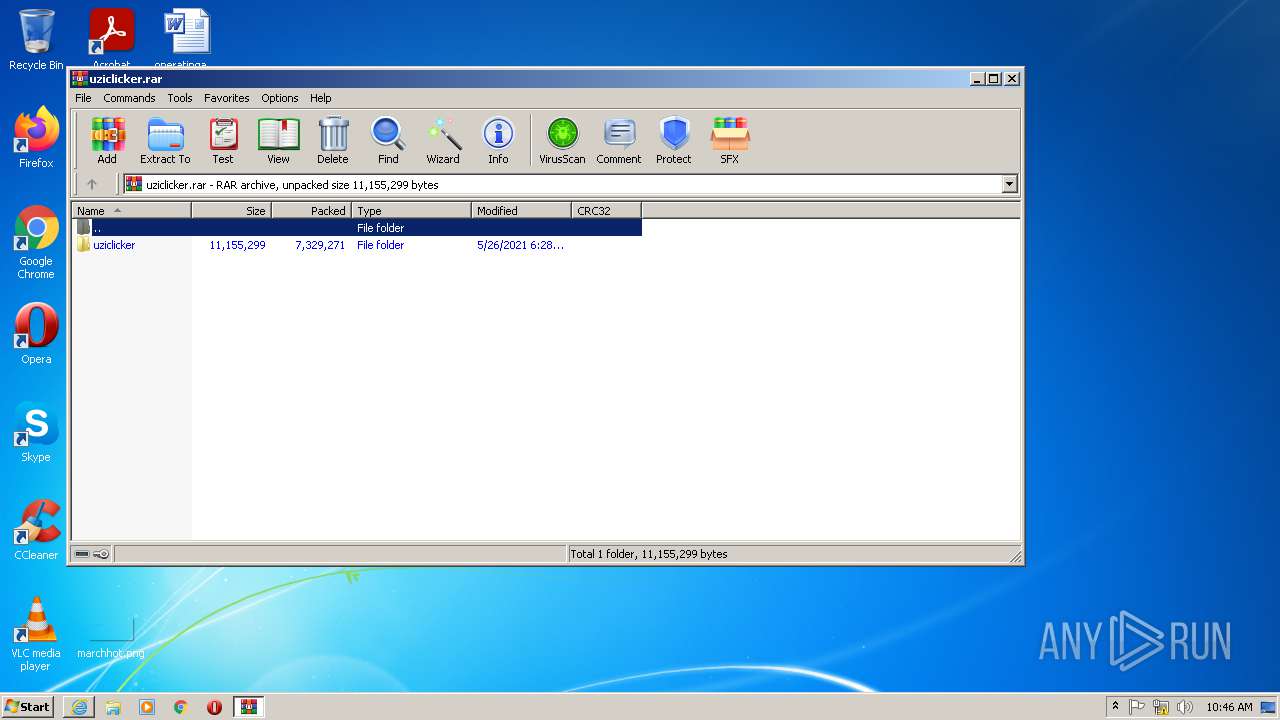
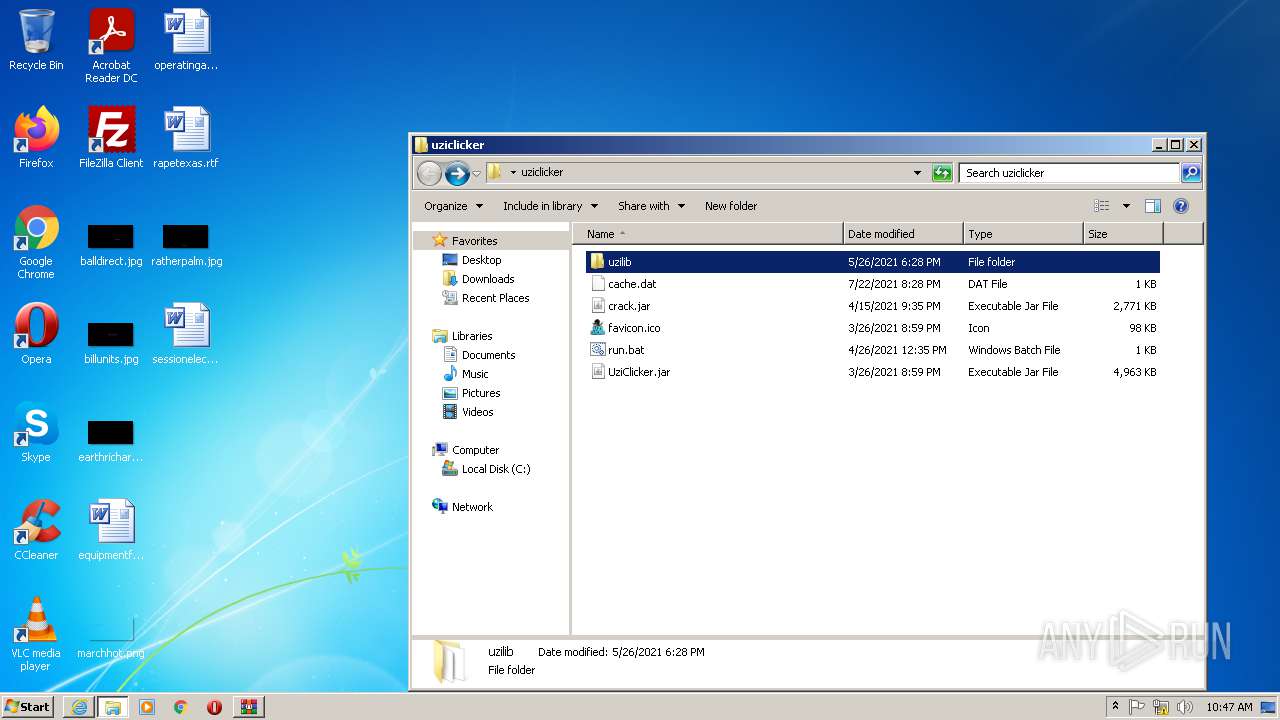
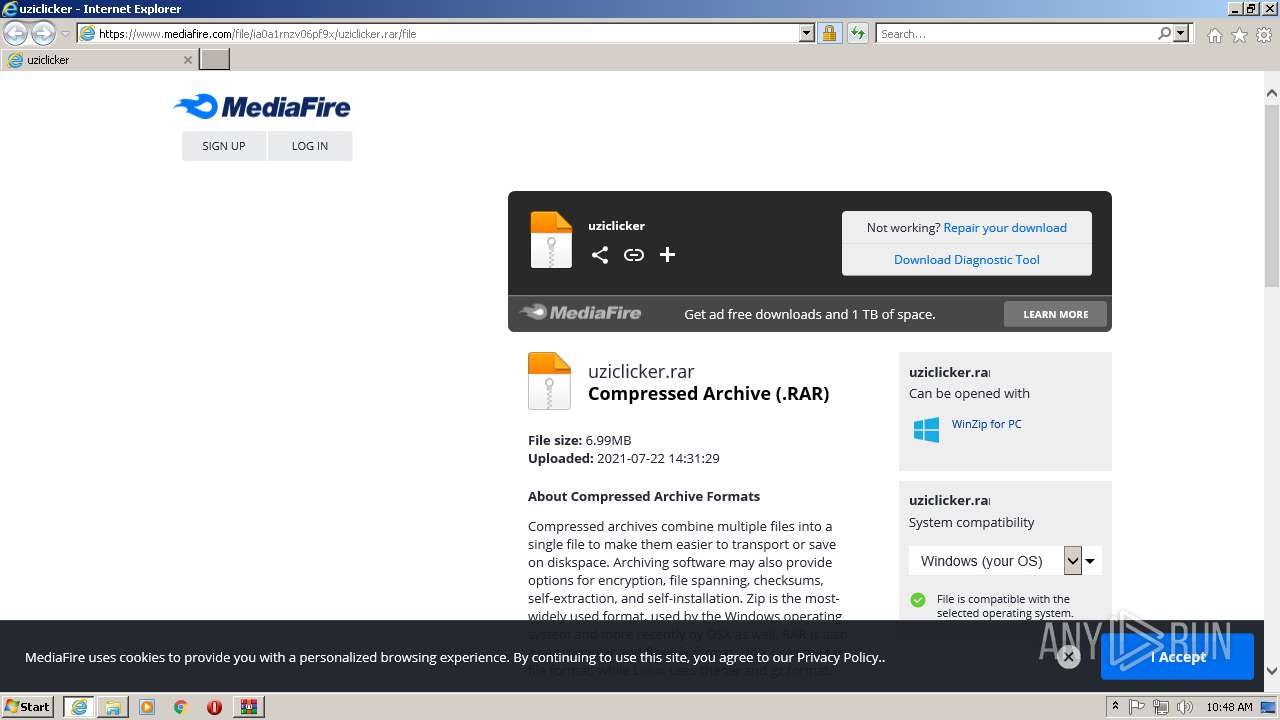
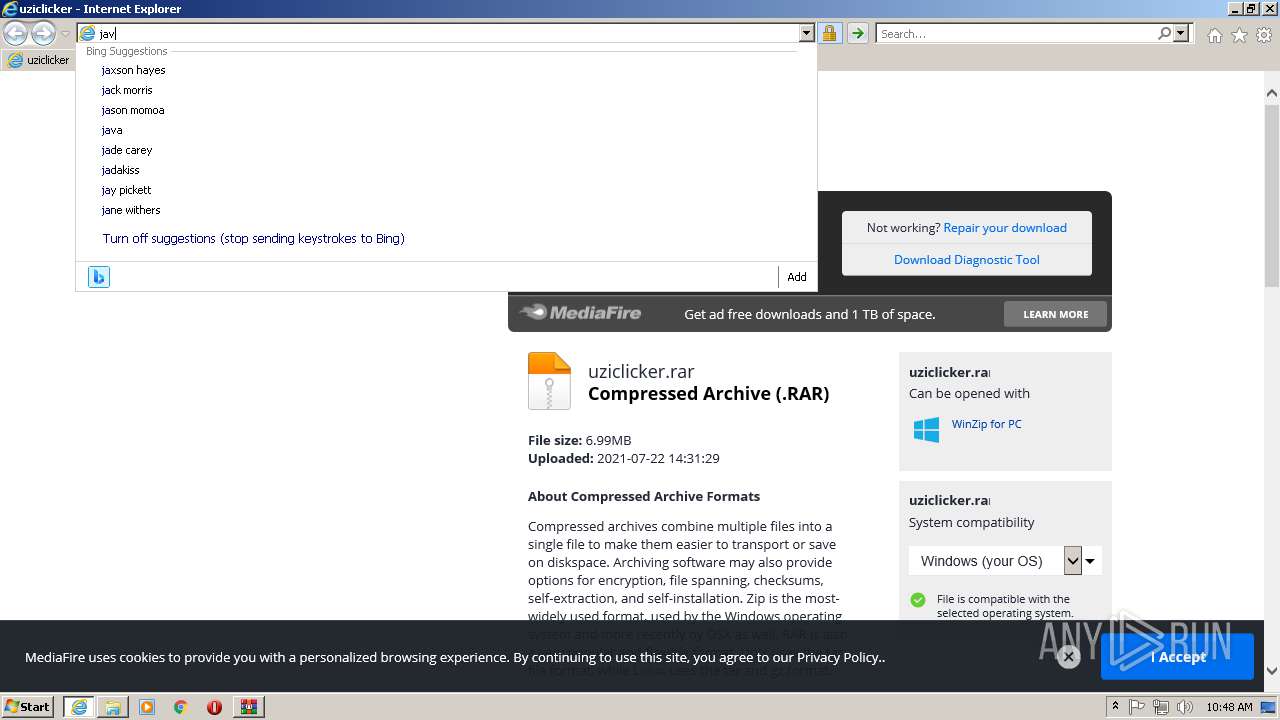
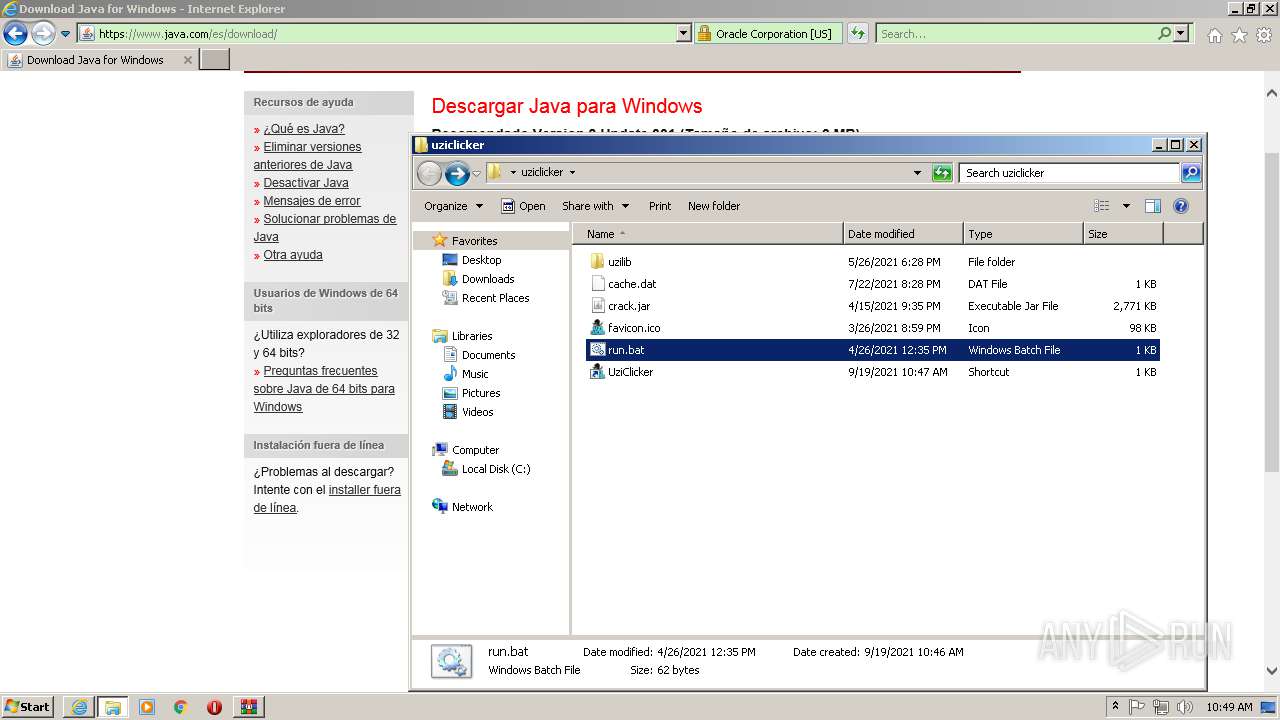
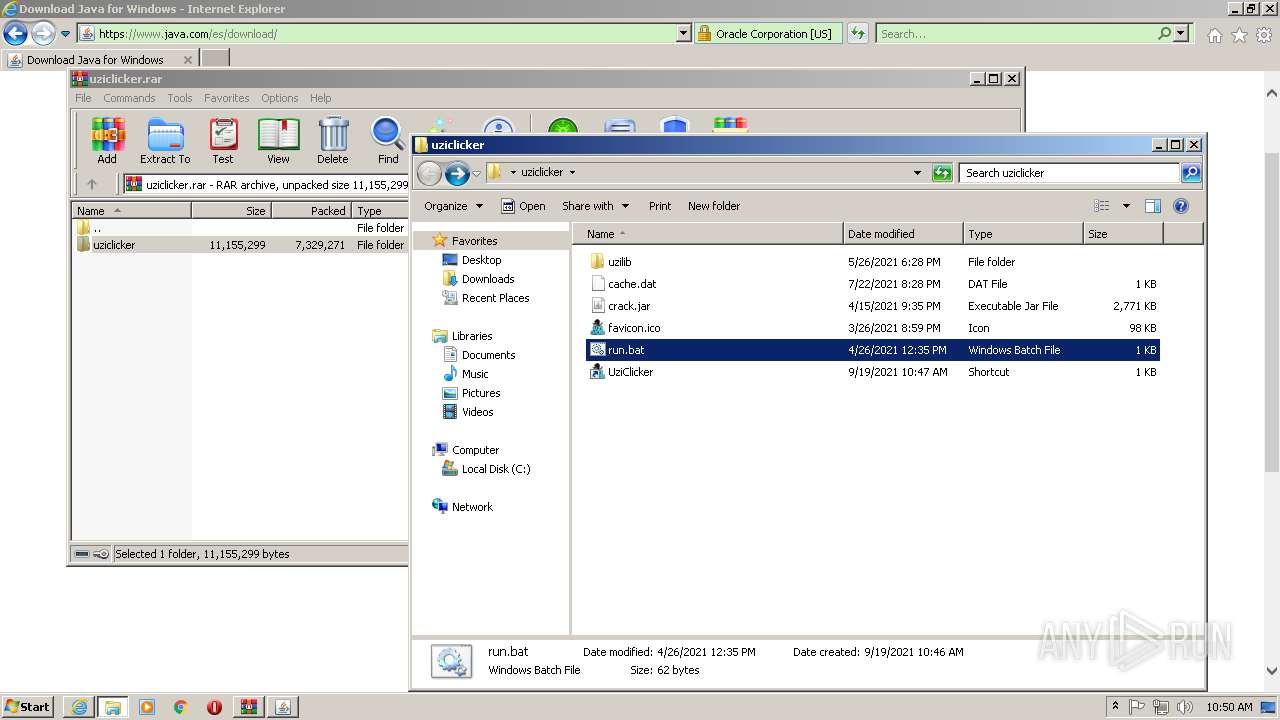
| URL: | https://www.mediafire.com/file/ia0a1rnzv06pf9x/uziclicker.rar/file |
| Full analysis: | https://app.any.run/tasks/74ad9f83-a6e4-453b-970f-9eb33cfa7fac |
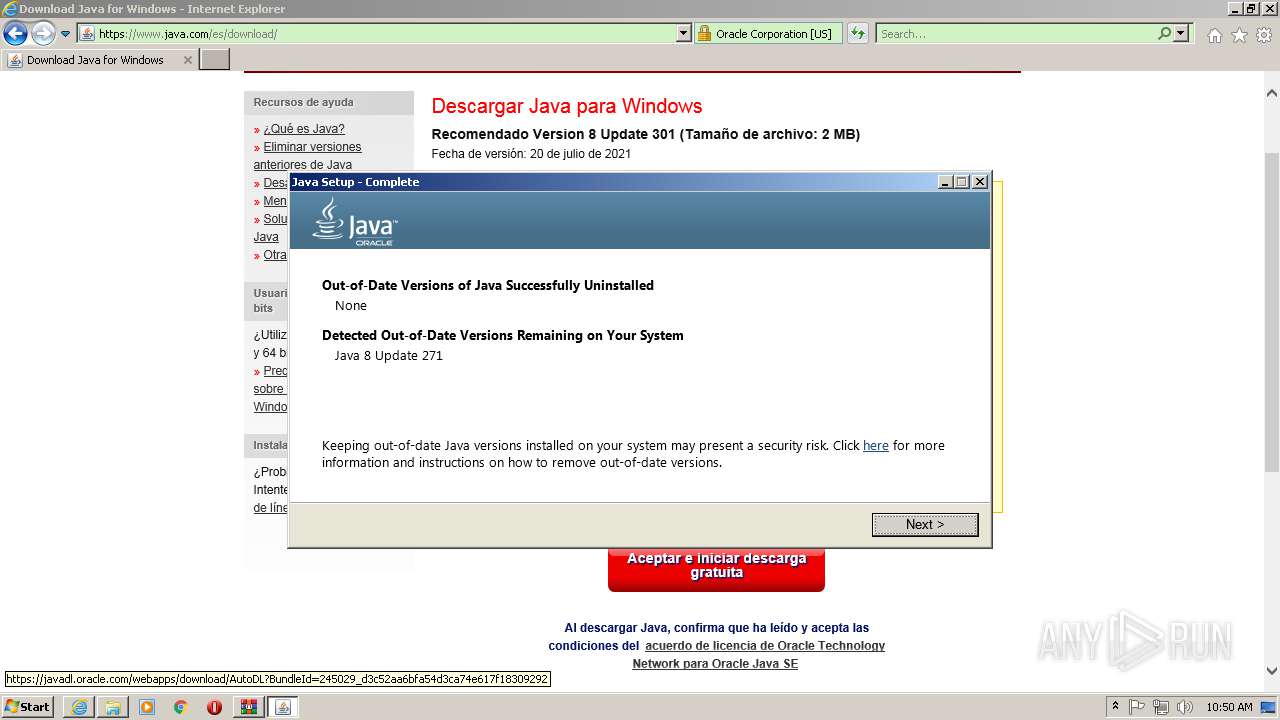
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2021, 09:46:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 207DEFF43048600206E27543B68AE073 |
| SHA1: | 5165B1768144883474A2B0843E1562B07164C215 |
| SHA256: | F8A30BFDEC9CF7BD277761FC370D15ACE55E02C045CF6ABA187249A1395F4AB2 |
| SSDEEP: | 3:N8DSLw3eGUoFuMZDEkGCZyjKA:2OLw3eGQM+kGCZ3A |
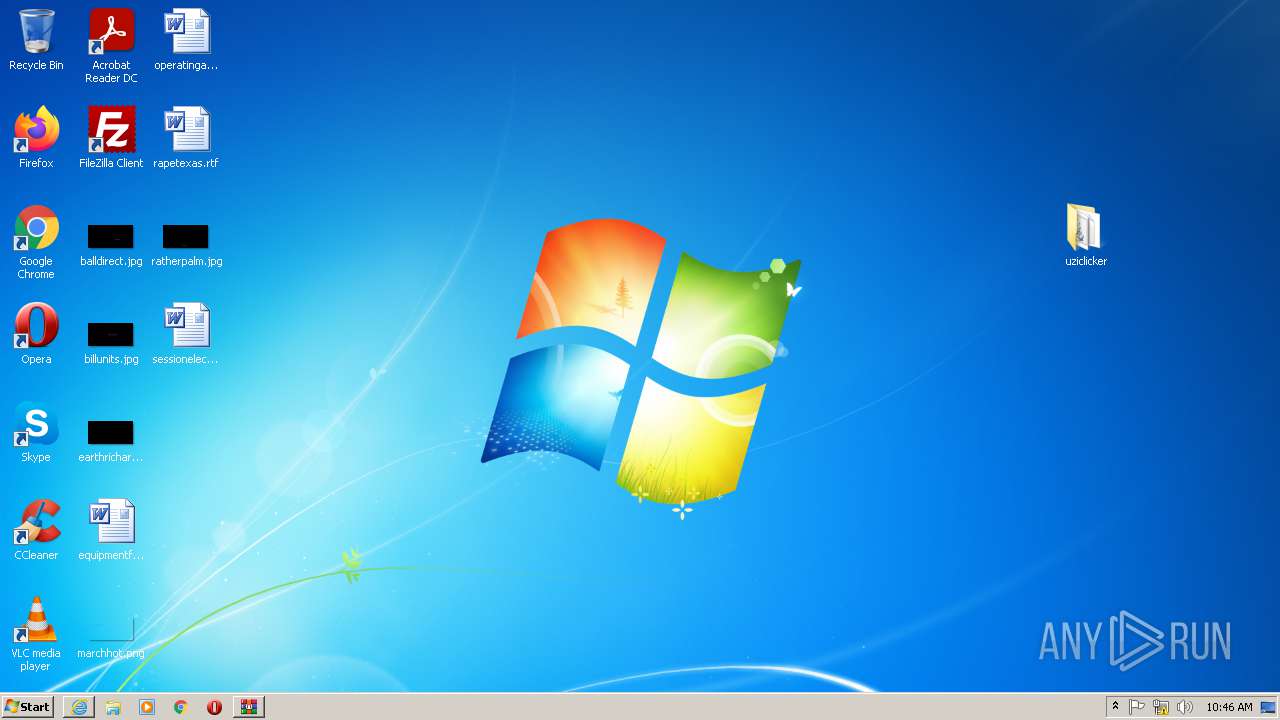
MALICIOUS
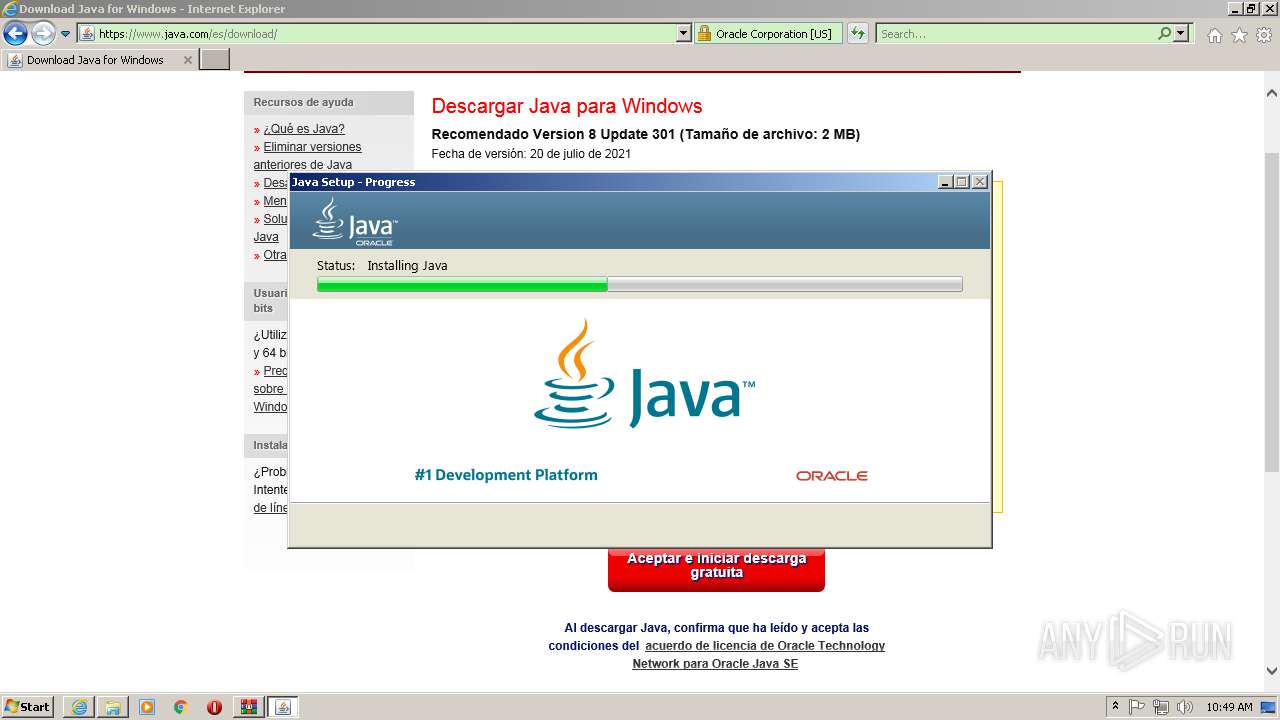
Loads dropped or rewritten executable
- Explorer.EXE (PID: 1668)
- SearchProtocolHost.exe (PID: 1616)
- MsiExec.exe (PID: 3992)
- unpack200.exe (PID: 2732)
- unpack200.exe (PID: 2688)
- unpack200.exe (PID: 3444)
- unpack200.exe (PID: 3660)
- java.exe (PID: 3036)
- unpack200.exe (PID: 4004)
- java.exe (PID: 276)
- unpack200.exe (PID: 2532)
- installer.exe (PID: 3612)
- javaw.exe (PID: 796)
- unpack200.exe (PID: 3840)
- ssvagent.exe (PID: 888)
- svchost.exe (PID: 868)
- jp2launcher.exe (PID: 3868)
- MsiExec.exe (PID: 2784)
- jp2launcher.exe (PID: 3196)
- MsiExec.exe (PID: 2992)
- MsiExec.exe (PID: 1632)
Application was dropped or rewritten from another process
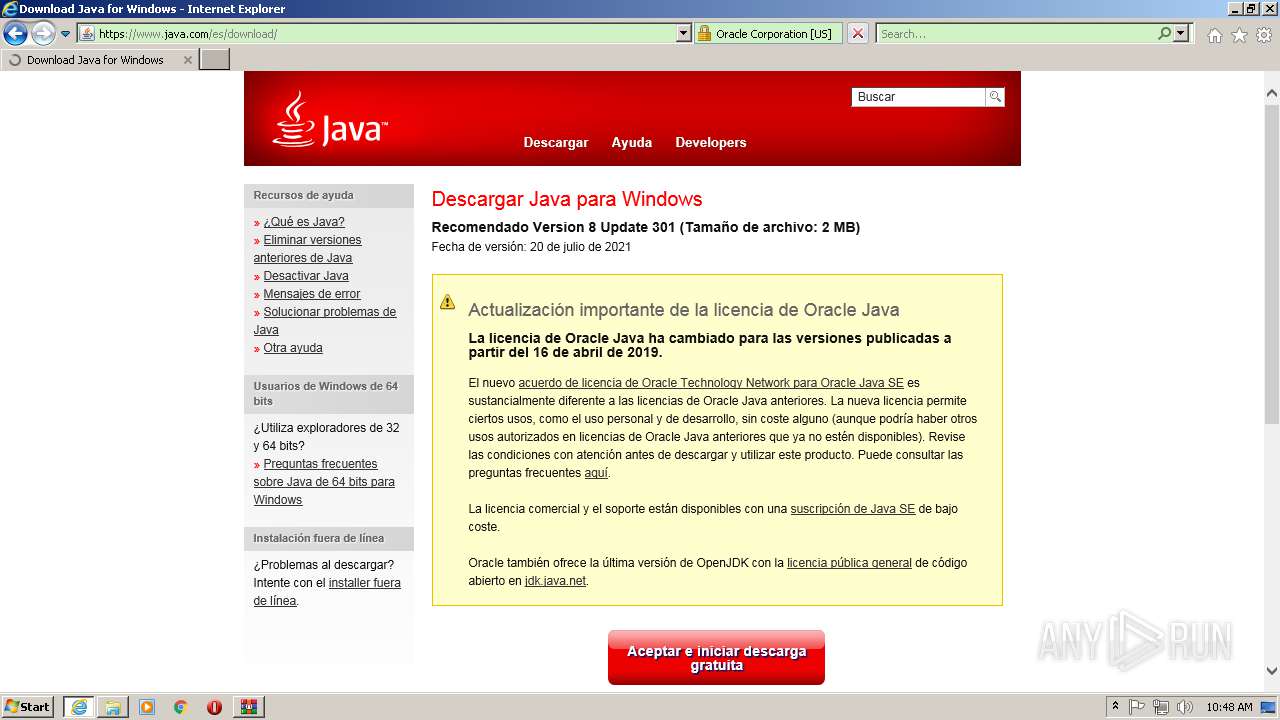
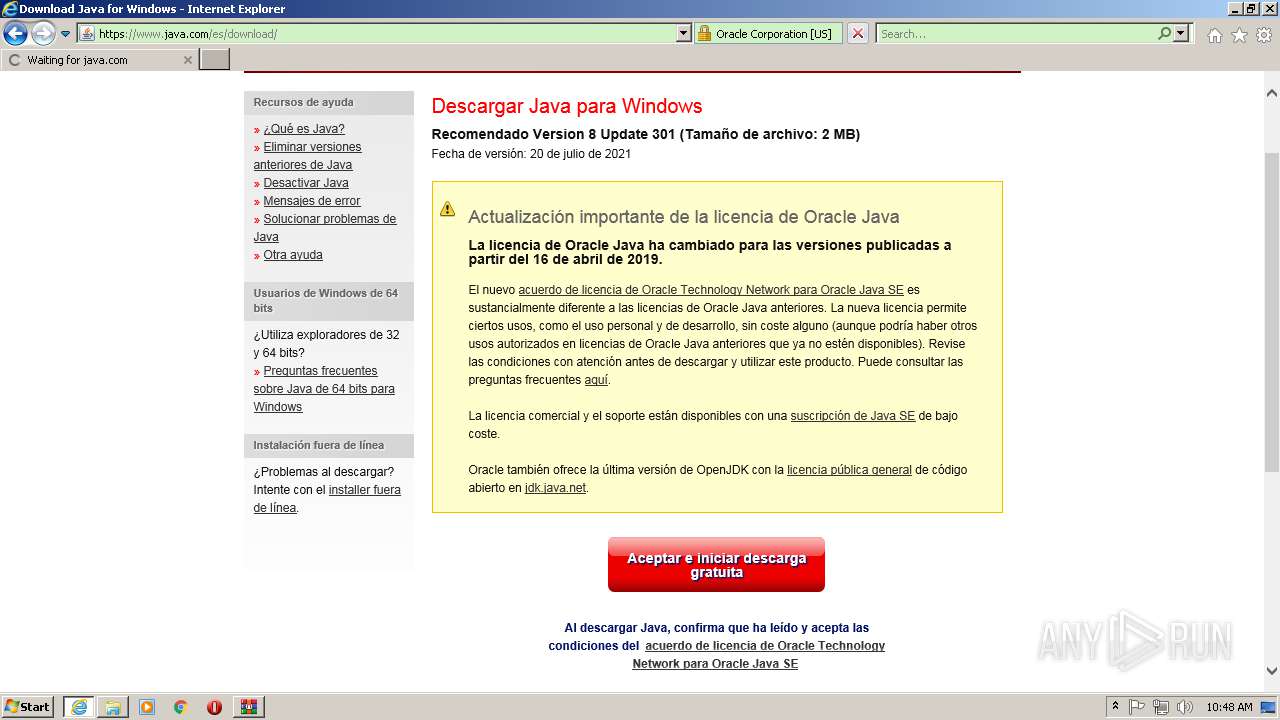
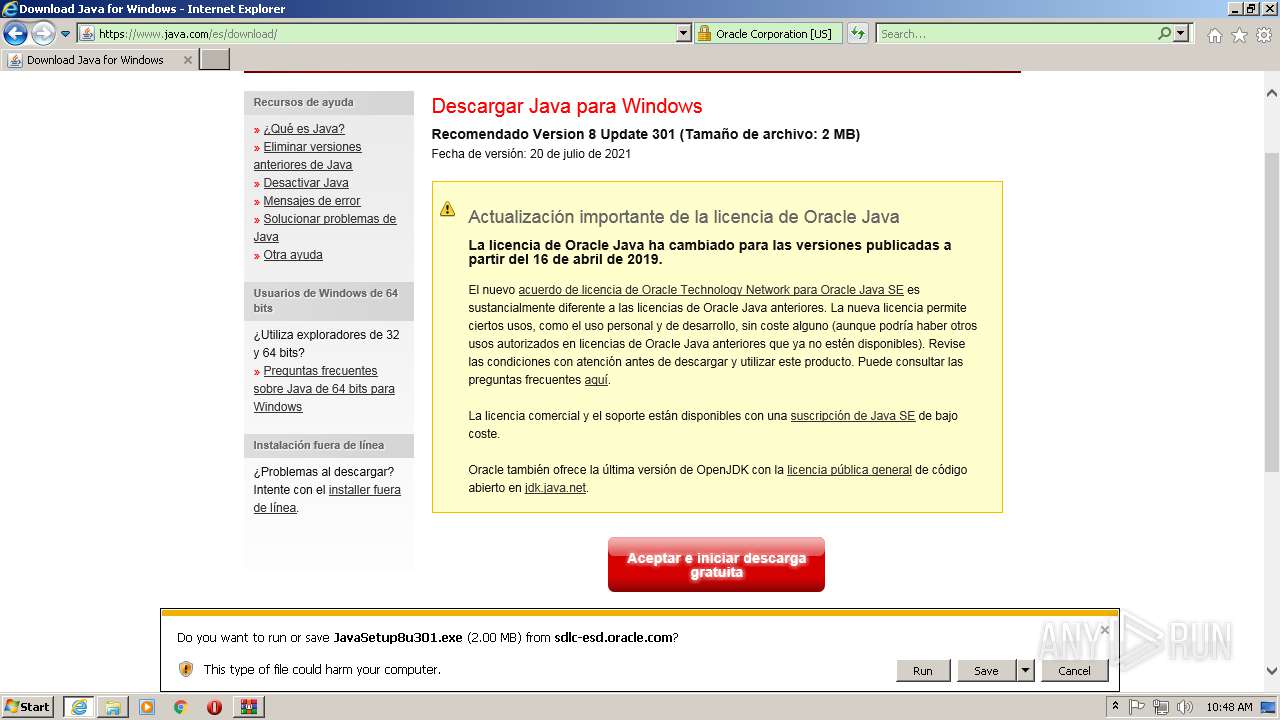
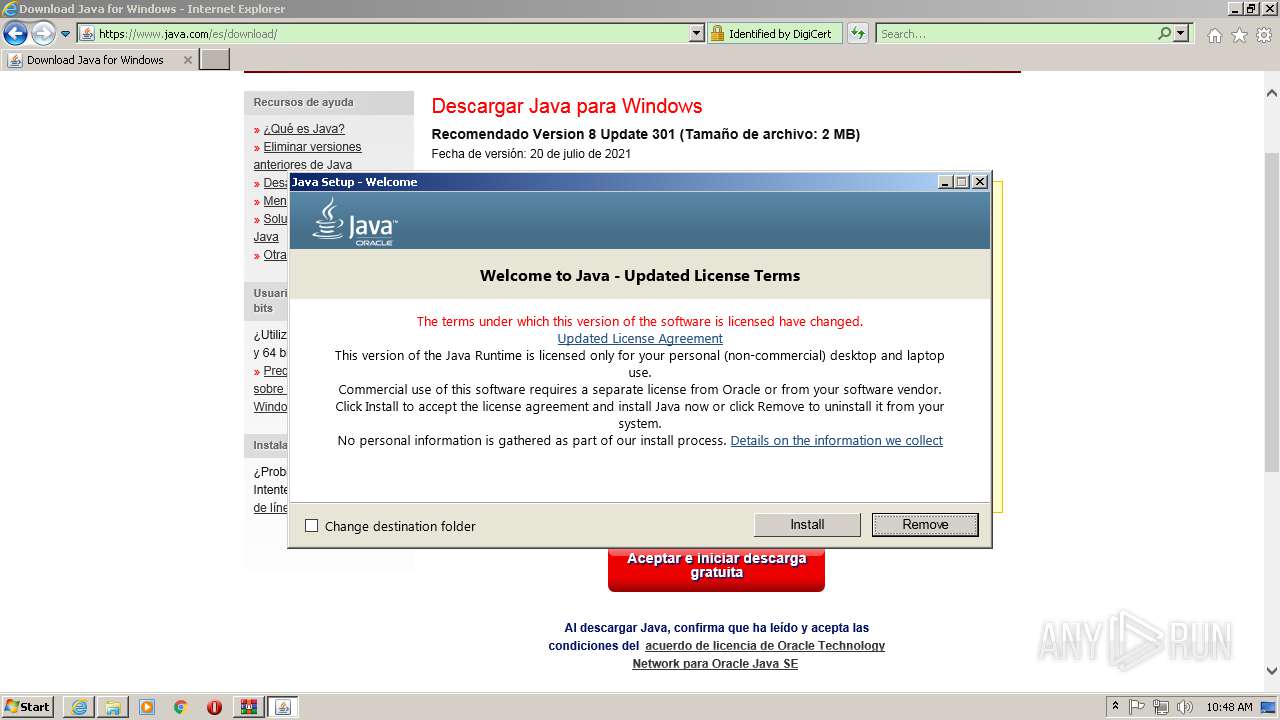
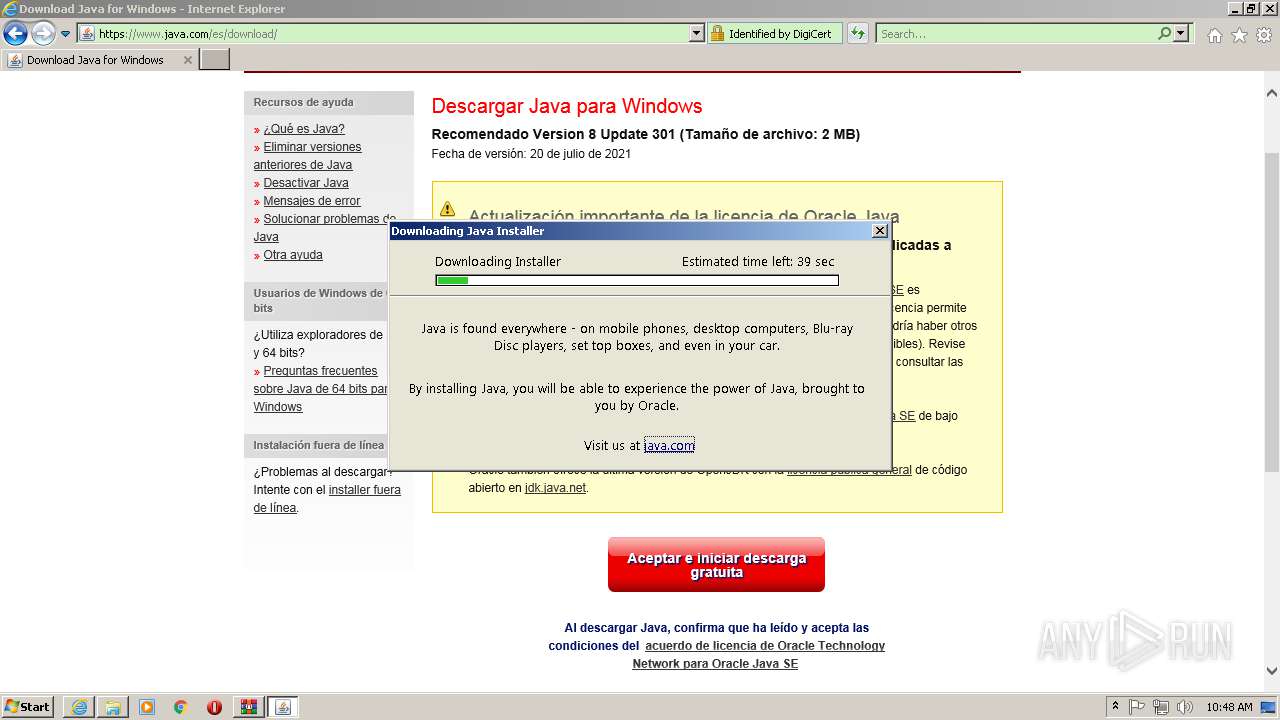
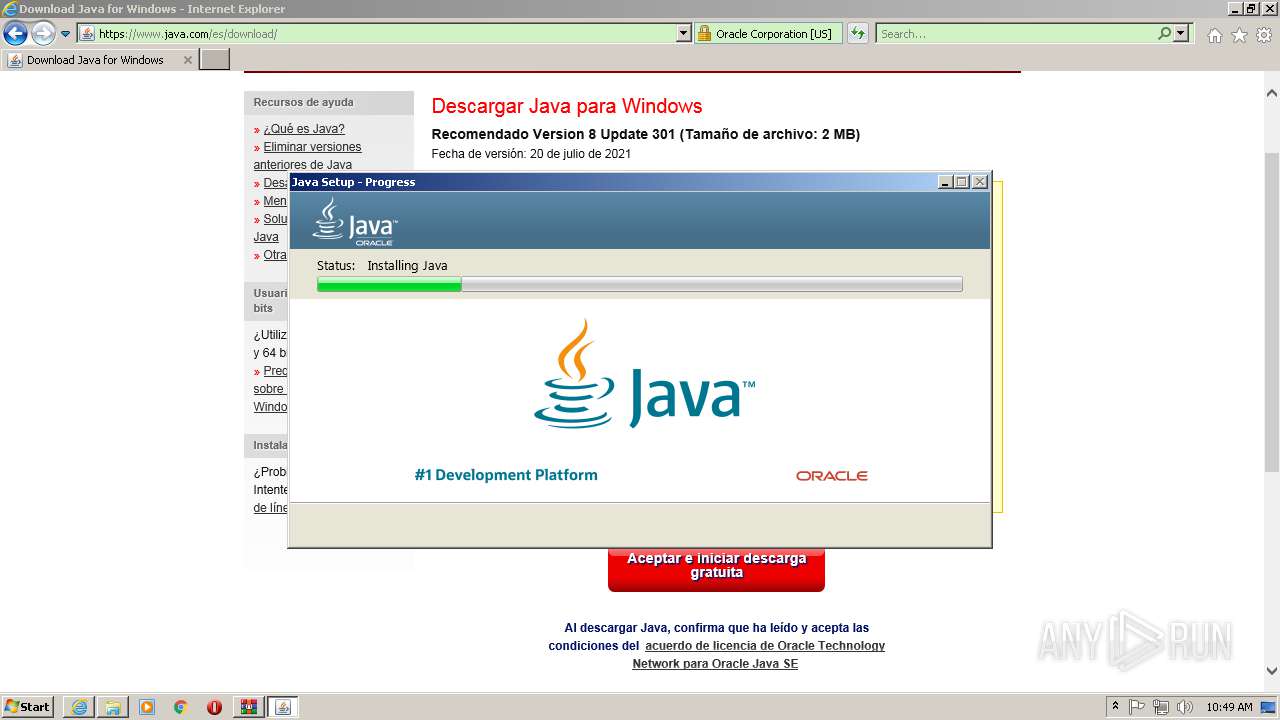
- JavaSetup8u301.exe (PID: 3524)
- JavaSetup8u301.exe (PID: 2132)
- JavaSetup8u301.exe (PID: 2508)
- LZMA_EXE (PID: 296)
- LZMA_EXE (PID: 2480)
- bspatch.exe (PID: 3204)
- unpack200.exe (PID: 2732)
- unpack200.exe (PID: 2688)
- unpack200.exe (PID: 3444)
- unpack200.exe (PID: 4004)
- unpack200.exe (PID: 3840)
- unpack200.exe (PID: 3660)
- javaw.exe (PID: 796)
- ssvagent.exe (PID: 888)
- unpack200.exe (PID: 2532)
- javaws.exe (PID: 2352)
- jp2launcher.exe (PID: 3868)
- jp2launcher.exe (PID: 3196)
- javaws.exe (PID: 4088)
- java.exe (PID: 1880)
Drops executable file immediately after starts
- JavaSetup8u301.exe (PID: 2132)
- installer.exe (PID: 3612)
Loads the Task Scheduler COM API
- MsiExec.exe (PID: 2992)
Changes the autorun value in the registry
- msiexec.exe (PID: 372)
SUSPICIOUS
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1008)
- installer.exe (PID: 3612)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1556)
- iexplore.exe (PID: 2576)
- JavaSetup8u301.exe (PID: 2508)
Reads the computer name
- WinRAR.exe (PID: 1008)
- java.exe (PID: 276)
- java.exe (PID: 3036)
- JavaSetup8u301.exe (PID: 2132)
- JavaSetup8u301.exe (PID: 2508)
- installer.exe (PID: 3612)
- javaws.exe (PID: 2352)
- jp2launcher.exe (PID: 3868)
- javaws.exe (PID: 4088)
- jp2launcher.exe (PID: 3196)
Checks supported languages
- WinRAR.exe (PID: 1008)
- cmd.exe (PID: 3960)
- java.exe (PID: 276)
- java.exe (PID: 3036)
- JavaSetup8u301.exe (PID: 2132)
- JavaSetup8u301.exe (PID: 2508)
- cmd.exe (PID: 3320)
- java.exe (PID: 1476)
- cmd.exe (PID: 2388)
- java.exe (PID: 552)
- LZMA_EXE (PID: 2480)
- LZMA_EXE (PID: 296)
- java.exe (PID: 3932)
- cmd.exe (PID: 3756)
- java.exe (PID: 3180)
- cmd.exe (PID: 2408)
- java.exe (PID: 1876)
- installer.exe (PID: 3612)
- bspatch.exe (PID: 3204)
- unpack200.exe (PID: 2732)
- unpack200.exe (PID: 2688)
- unpack200.exe (PID: 3660)
- unpack200.exe (PID: 3444)
- java.exe (PID: 3708)
- cmd.exe (PID: 1924)
- unpack200.exe (PID: 4004)
- unpack200.exe (PID: 3840)
- javaw.exe (PID: 796)
- unpack200.exe (PID: 2532)
- jp2launcher.exe (PID: 3868)
- javaws.exe (PID: 4088)
- cmd.exe (PID: 3644)
- ssvagent.exe (PID: 888)
- javaws.exe (PID: 2352)
- jp2launcher.exe (PID: 3196)
- cmd.exe (PID: 2848)
- java.exe (PID: 1880)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1008)
- iexplore.exe (PID: 1556)
- iexplore.exe (PID: 2576)
- JavaSetup8u301.exe (PID: 2132)
- JavaSetup8u301.exe (PID: 2508)
- LZMA_EXE (PID: 2480)
- msiexec.exe (PID: 372)
- installer.exe (PID: 3612)
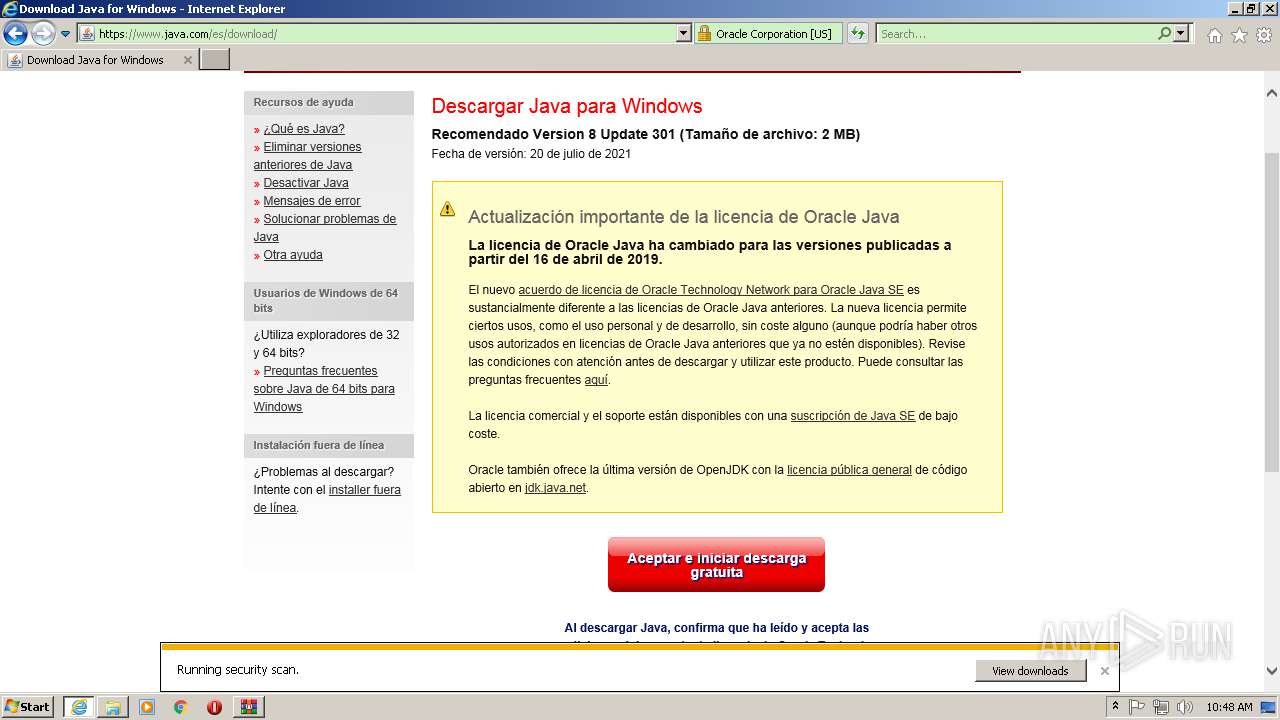
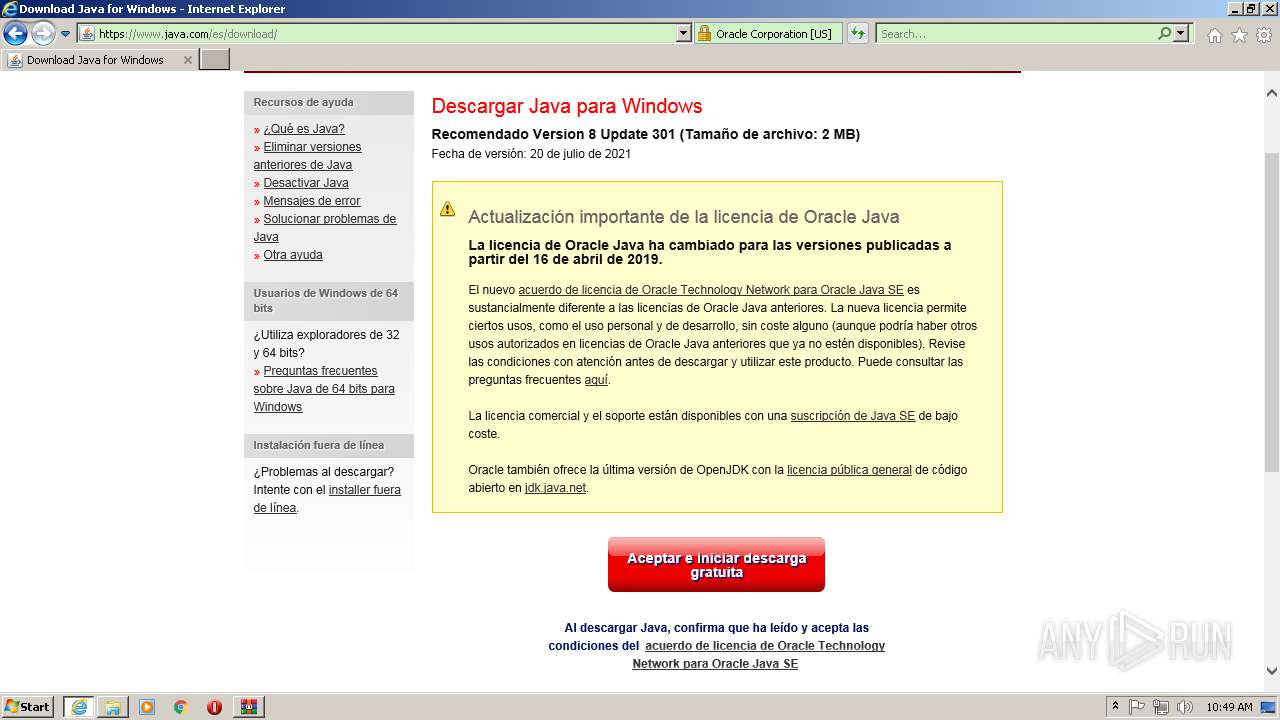
Starts Internet Explorer
- Explorer.EXE (PID: 1668)
Reads default file associations for system extensions
- Explorer.EXE (PID: 1668)
- SearchProtocolHost.exe (PID: 1616)
Starts CMD.EXE for commands execution
- Explorer.EXE (PID: 1668)
Uses ICACLS.EXE to modify access control list
- java.exe (PID: 276)
Creates files in the program directory
- java.exe (PID: 276)
- msiexec.exe (PID: 372)
- installer.exe (PID: 3612)
- unpack200.exe (PID: 2732)
- bspatch.exe (PID: 3204)
- unpack200.exe (PID: 2688)
- unpack200.exe (PID: 3660)
- unpack200.exe (PID: 3444)
- unpack200.exe (PID: 4004)
- unpack200.exe (PID: 3840)
- javaw.exe (PID: 796)
- unpack200.exe (PID: 2532)
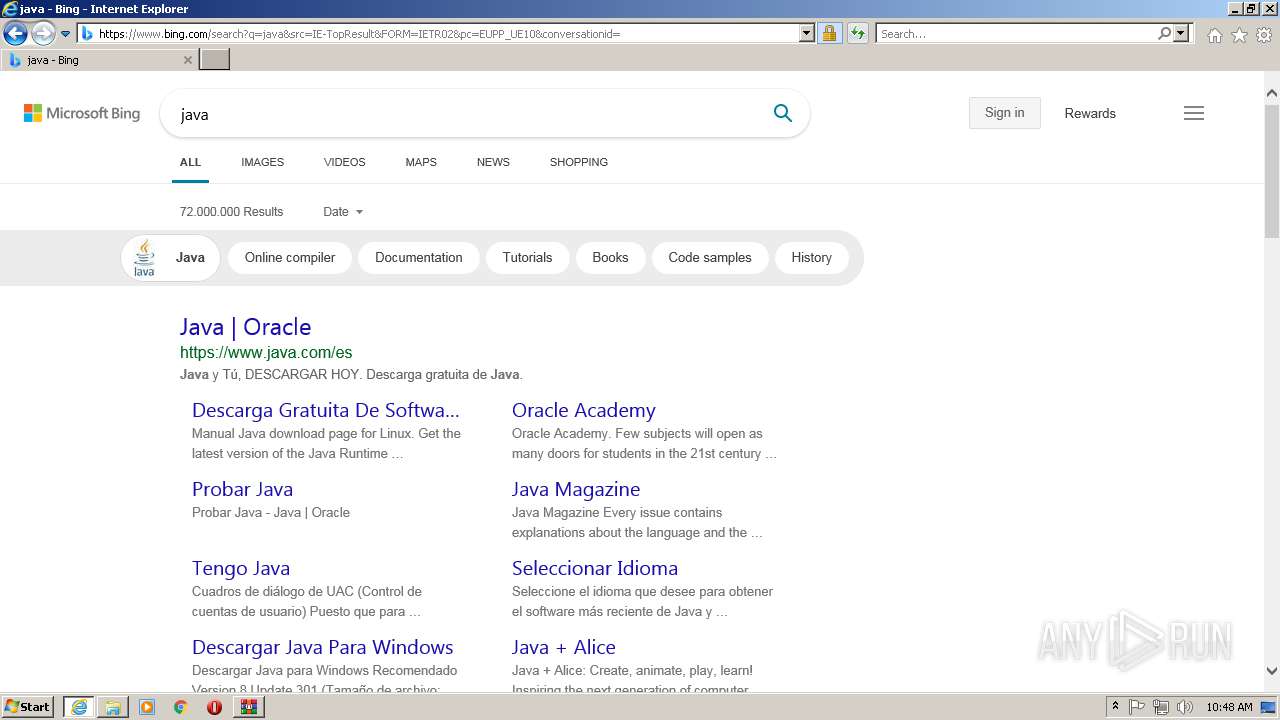
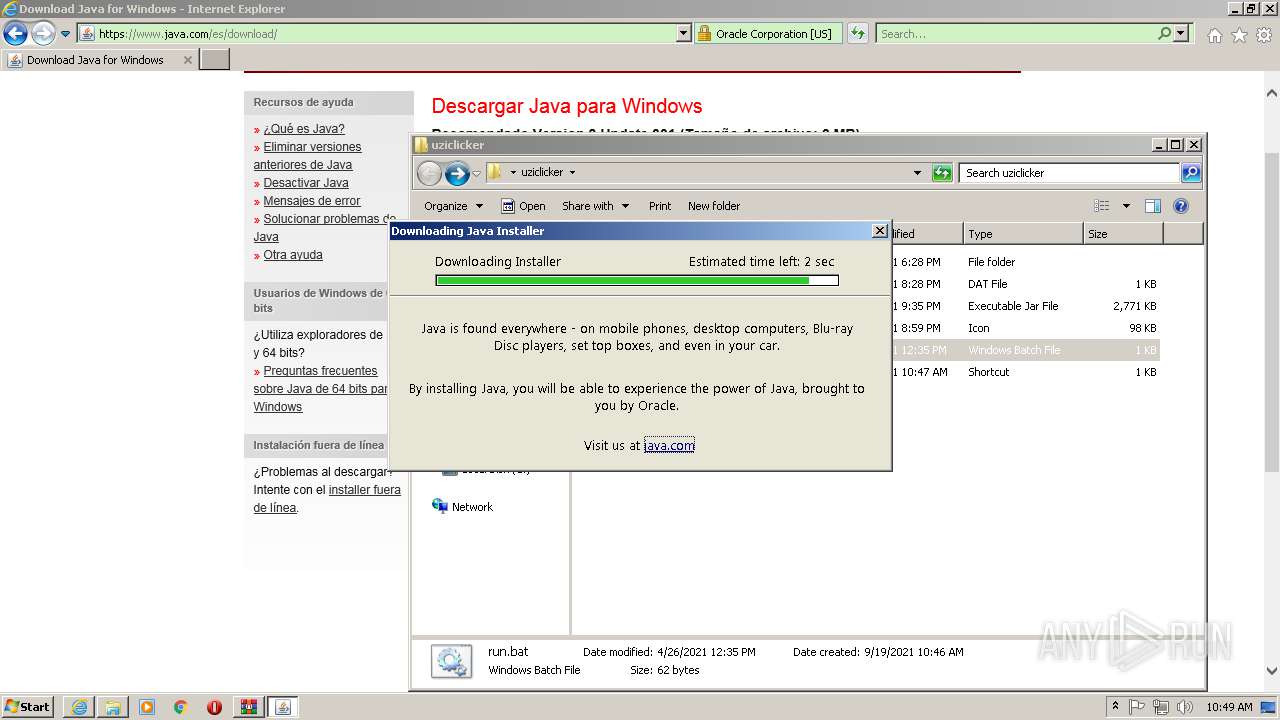
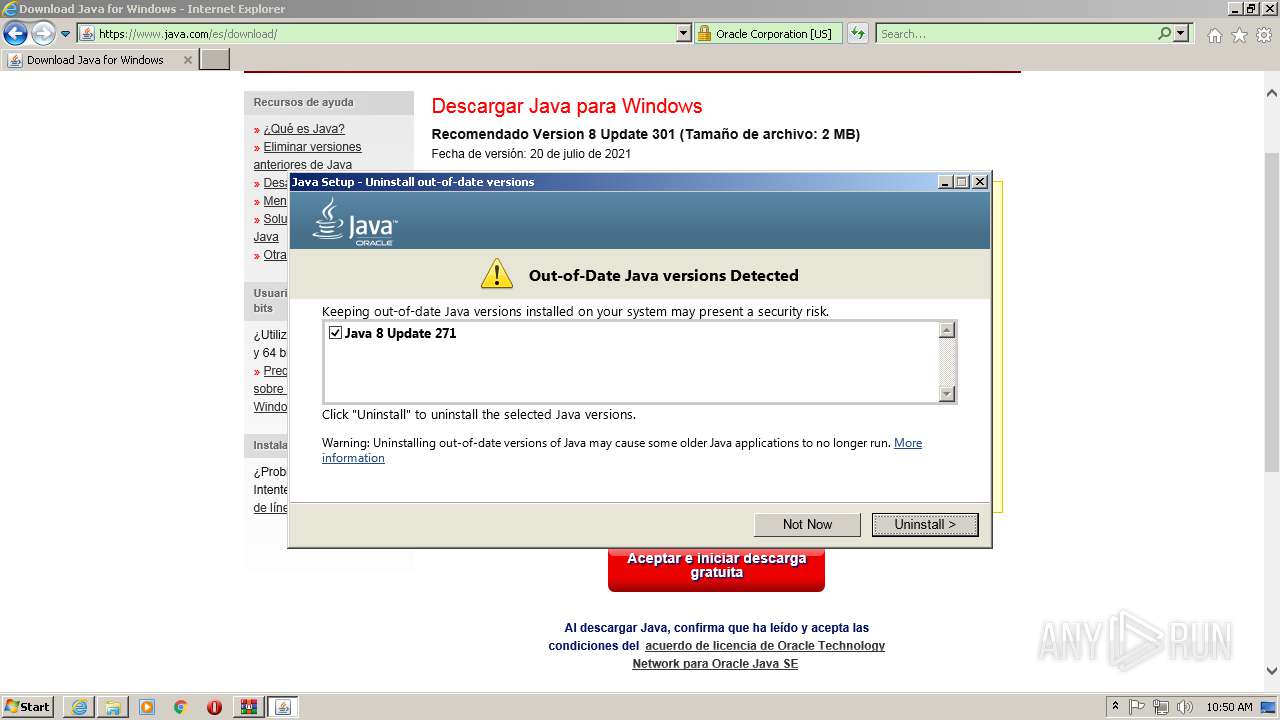
Check for Java to be installed
- java.exe (PID: 276)
- java.exe (PID: 3036)
- installer.exe (PID: 3612)
- jp2launcher.exe (PID: 3868)
- ssvagent.exe (PID: 888)
- jp2launcher.exe (PID: 3196)
- JavaSetup8u301.exe (PID: 2508)
Application launched itself
- java.exe (PID: 276)
- msiexec.exe (PID: 372)
Creates files in the user directory
- java.exe (PID: 276)
- java.exe (PID: 3036)
- JavaSetup8u301.exe (PID: 2508)
Reads internet explorer settings
- JavaSetup8u301.exe (PID: 2508)
Starts application with an unusual extension
- JavaSetup8u301.exe (PID: 2508)
Executed as Windows Service
- msiexec.exe (PID: 372)
Reads Windows owner or organization settings
- msiexec.exe (PID: 372)
Creates a directory in Program Files
- msiexec.exe (PID: 372)
- installer.exe (PID: 3612)
Reads the Windows organization settings
- msiexec.exe (PID: 372)
Creates a software uninstall entry
- msiexec.exe (PID: 372)
Drops a file with too old compile date
- installer.exe (PID: 3612)
Drops a file with a compile date too recent
- installer.exe (PID: 3612)
Executes JAVA applets
- installer.exe (PID: 3612)
Changes default file association
- installer.exe (PID: 3612)
Removes files from Windows directory
- installer.exe (PID: 3612)
Creates files in the Windows directory
- installer.exe (PID: 3612)
Creates/Modifies COM task schedule object
- ssvagent.exe (PID: 888)
- installer.exe (PID: 3612)
Searches for installed software
- msiexec.exe (PID: 372)
INFO
Checks supported languages
- iexplore.exe (PID: 2576)
- iexplore.exe (PID: 1556)
- icacls.exe (PID: 1540)
- msiexec.exe (PID: 372)
- MsiExec.exe (PID: 3992)
- MsiExec.exe (PID: 2784)
- MsiExec.exe (PID: 1632)
- MsiExec.exe (PID: 2992)
- MsiExec.exe (PID: 1860)
- MsiExec.exe (PID: 2740)
Reads the computer name
- iexplore.exe (PID: 2576)
- iexplore.exe (PID: 1556)
- icacls.exe (PID: 1540)
- msiexec.exe (PID: 372)
- MsiExec.exe (PID: 3992)
- MsiExec.exe (PID: 1632)
- MsiExec.exe (PID: 2784)
- MsiExec.exe (PID: 2992)
- MsiExec.exe (PID: 2740)
- MsiExec.exe (PID: 1860)
Changes internet zones settings
- iexplore.exe (PID: 2576)
Checks Windows Trust Settings
- iexplore.exe (PID: 1556)
- iexplore.exe (PID: 2576)
- JavaSetup8u301.exe (PID: 2508)
- msiexec.exe (PID: 372)
Reads settings of System Certificates
- iexplore.exe (PID: 2576)
- iexplore.exe (PID: 1556)
- JavaSetup8u301.exe (PID: 2508)
- msiexec.exe (PID: 372)
Application launched itself
- iexplore.exe (PID: 2576)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2576)
Reads internet explorer settings
- iexplore.exe (PID: 1556)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 1008)
Creates files in the user directory
- iexplore.exe (PID: 1556)
- iexplore.exe (PID: 2576)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2576)
Changes settings of System certificates
- iexplore.exe (PID: 2576)
Reads CPU info
- msiexec.exe (PID: 372)
Check for Java to be installed
- msiexec.exe (PID: 372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
114
Monitored processes
51
Malicious processes
20
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
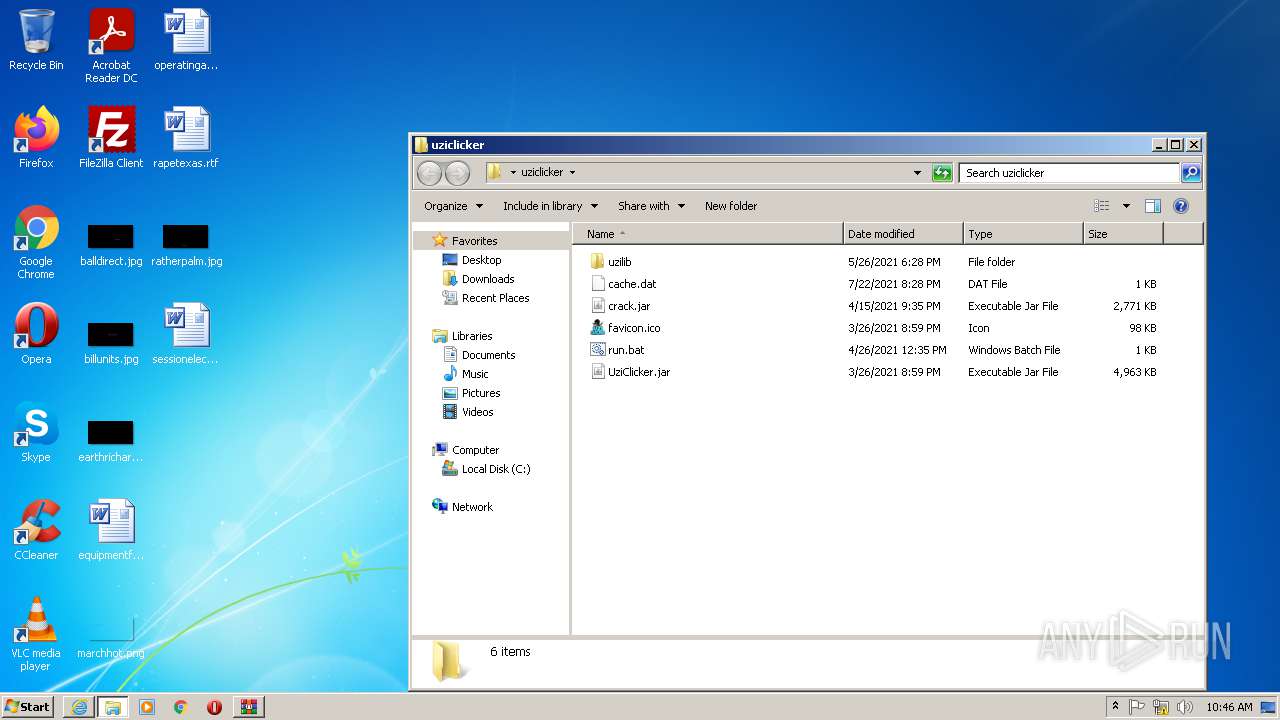
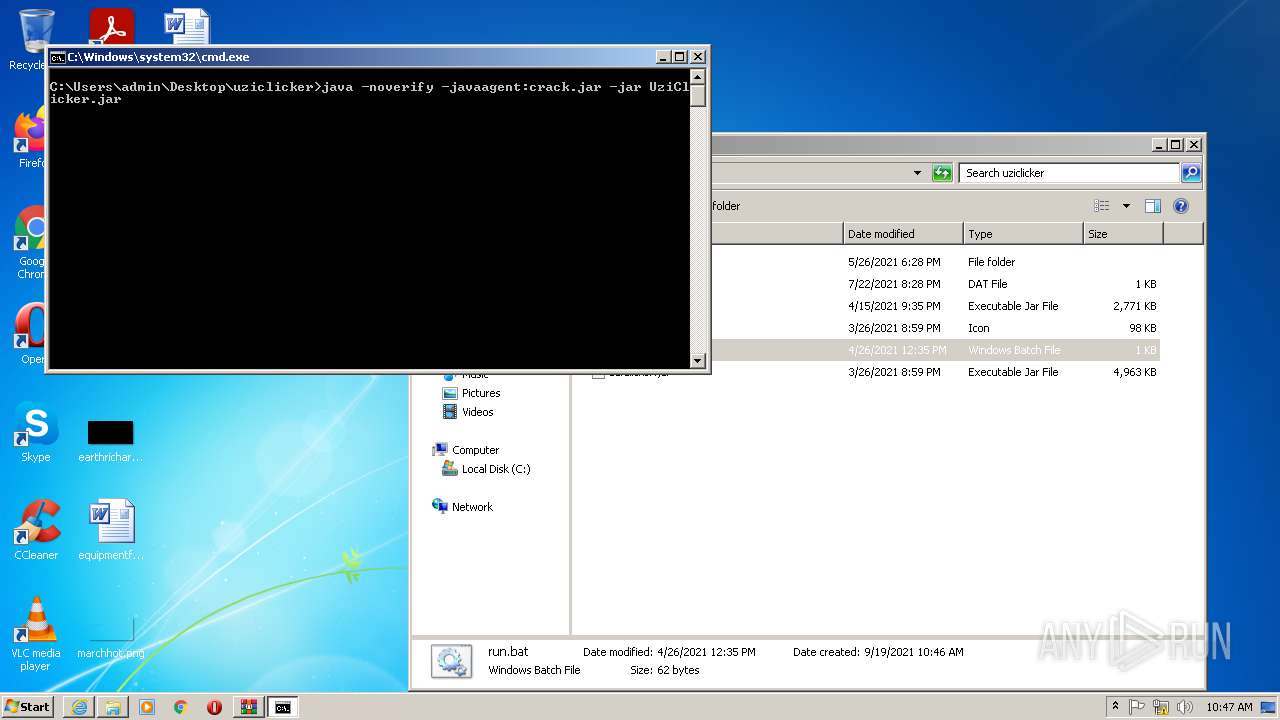
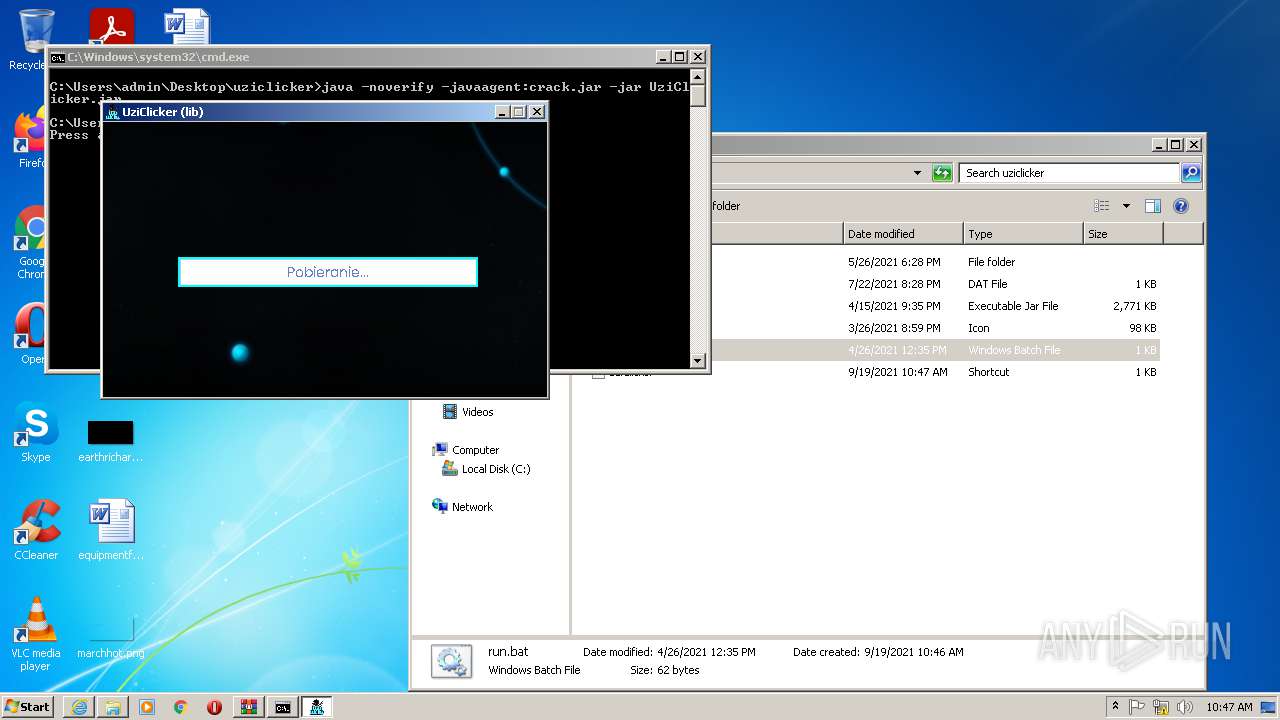
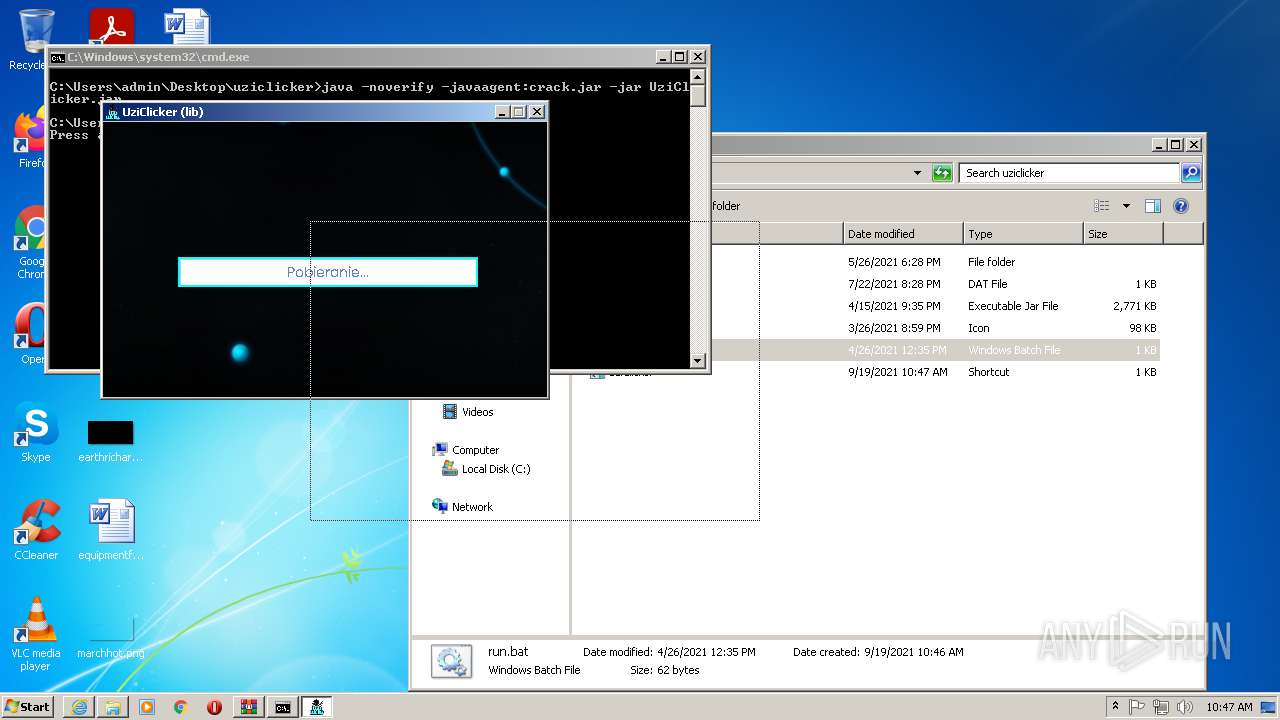
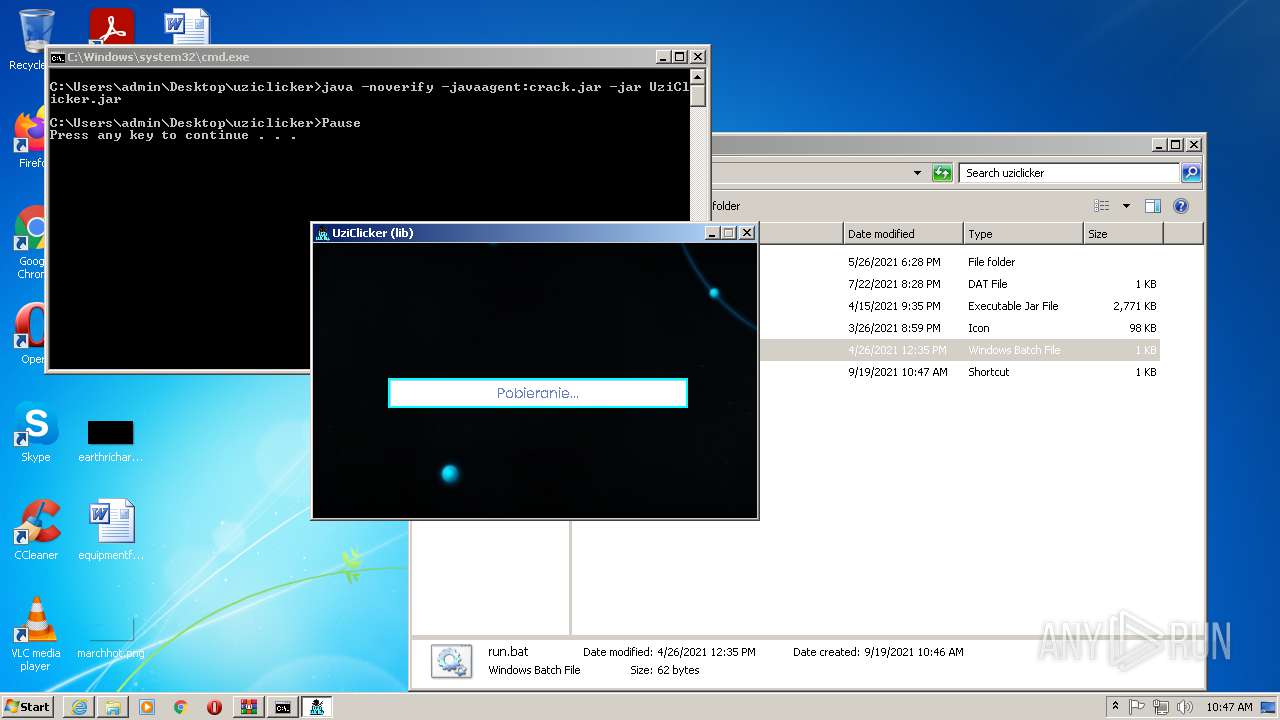
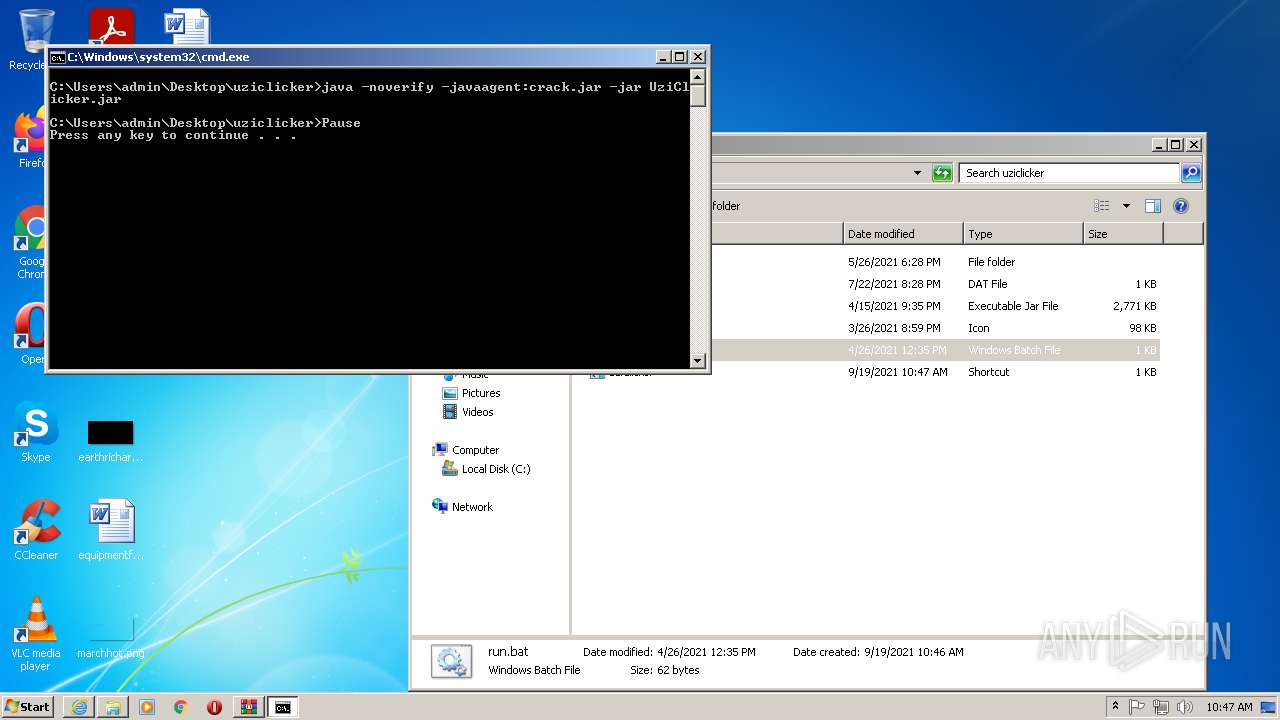
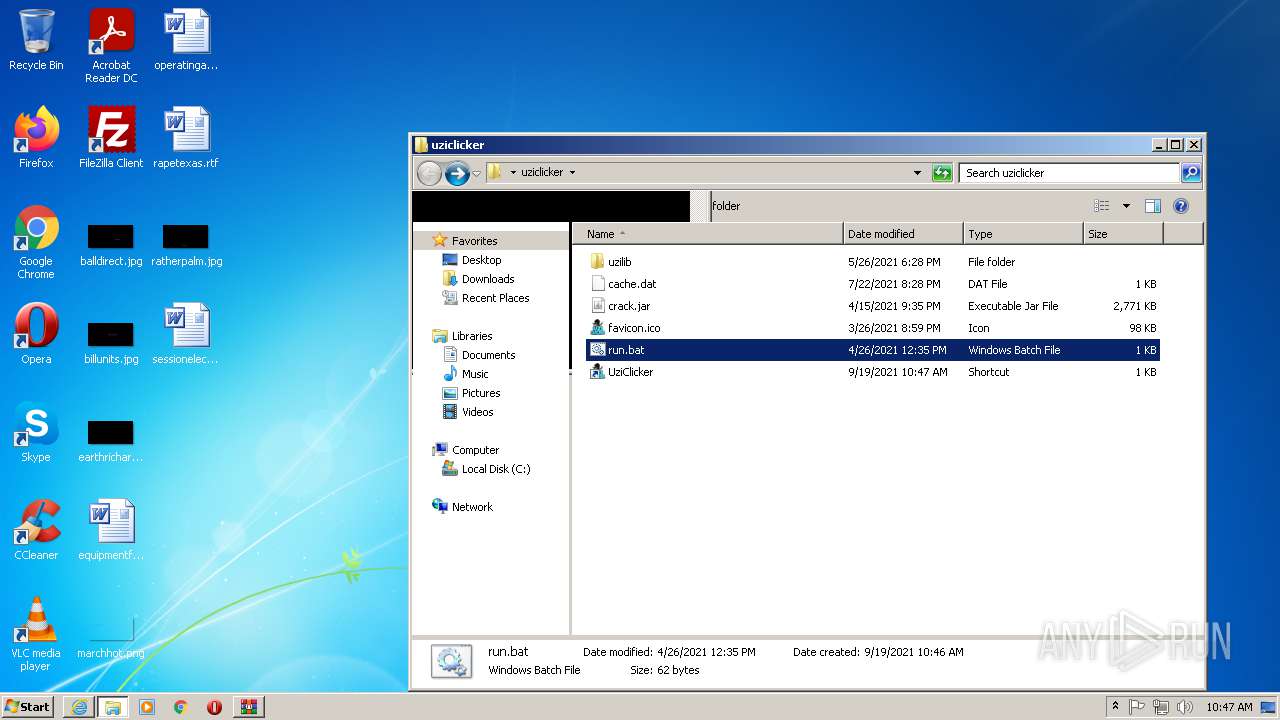
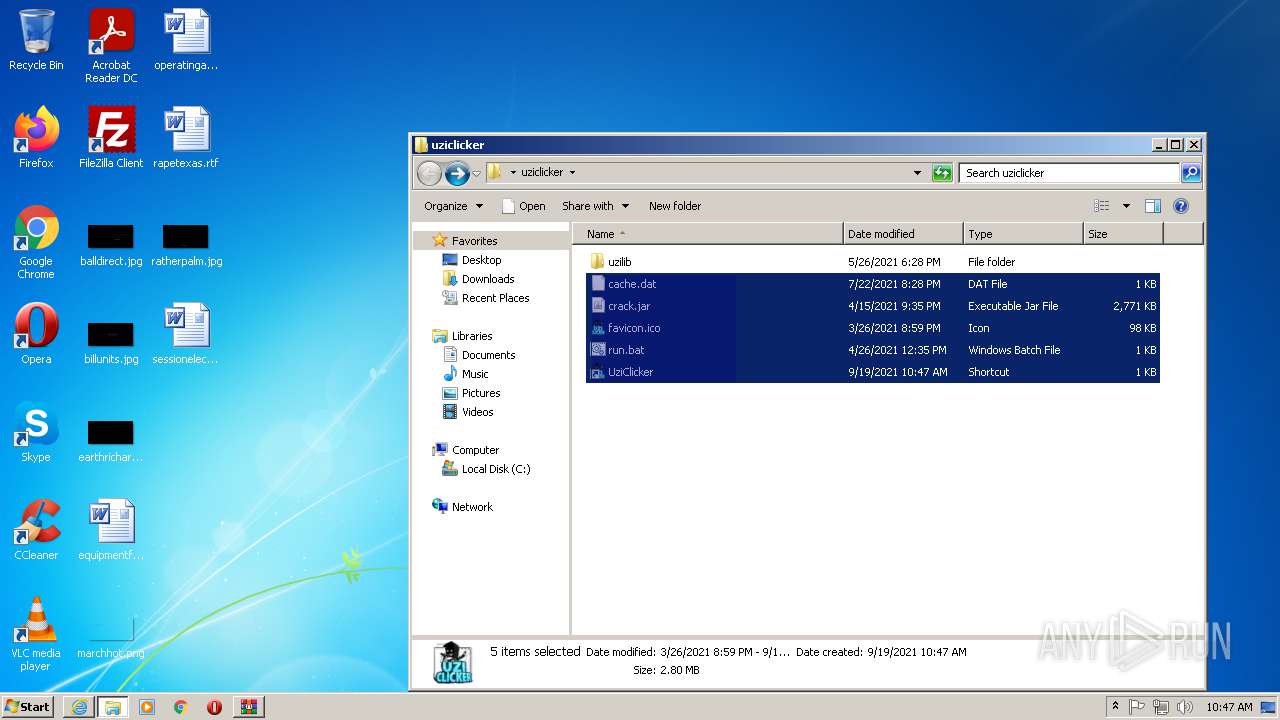
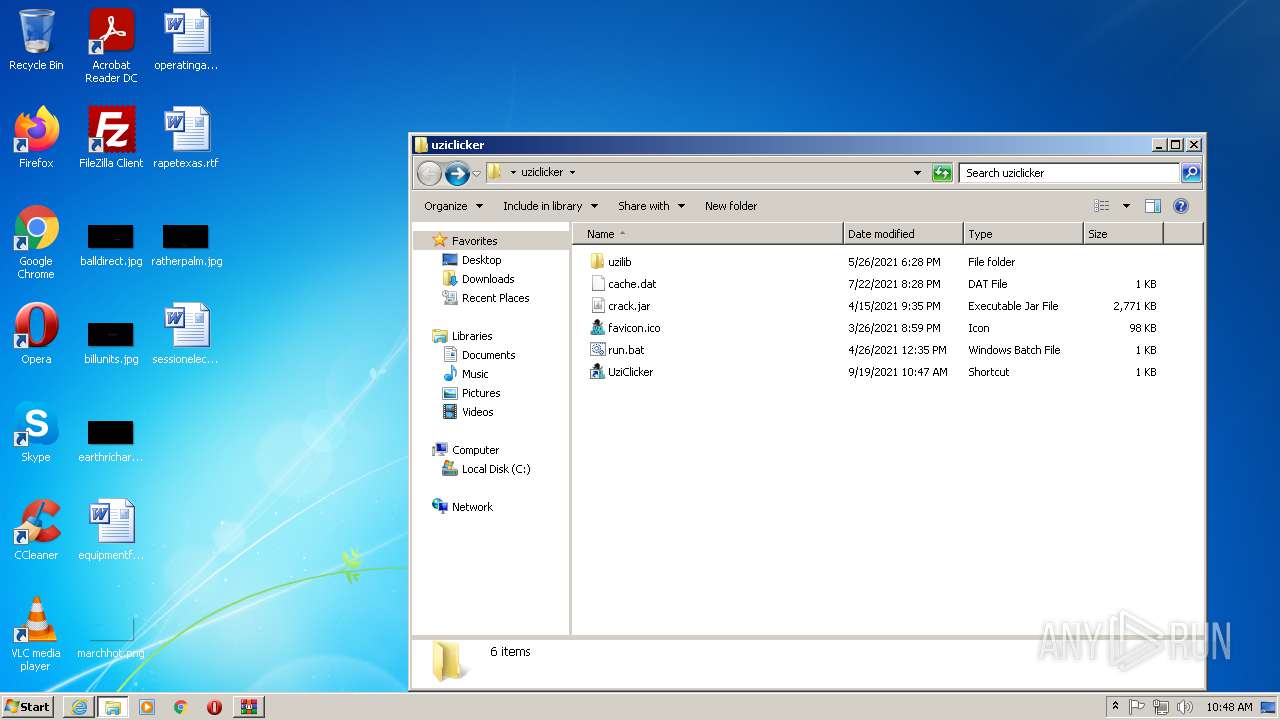
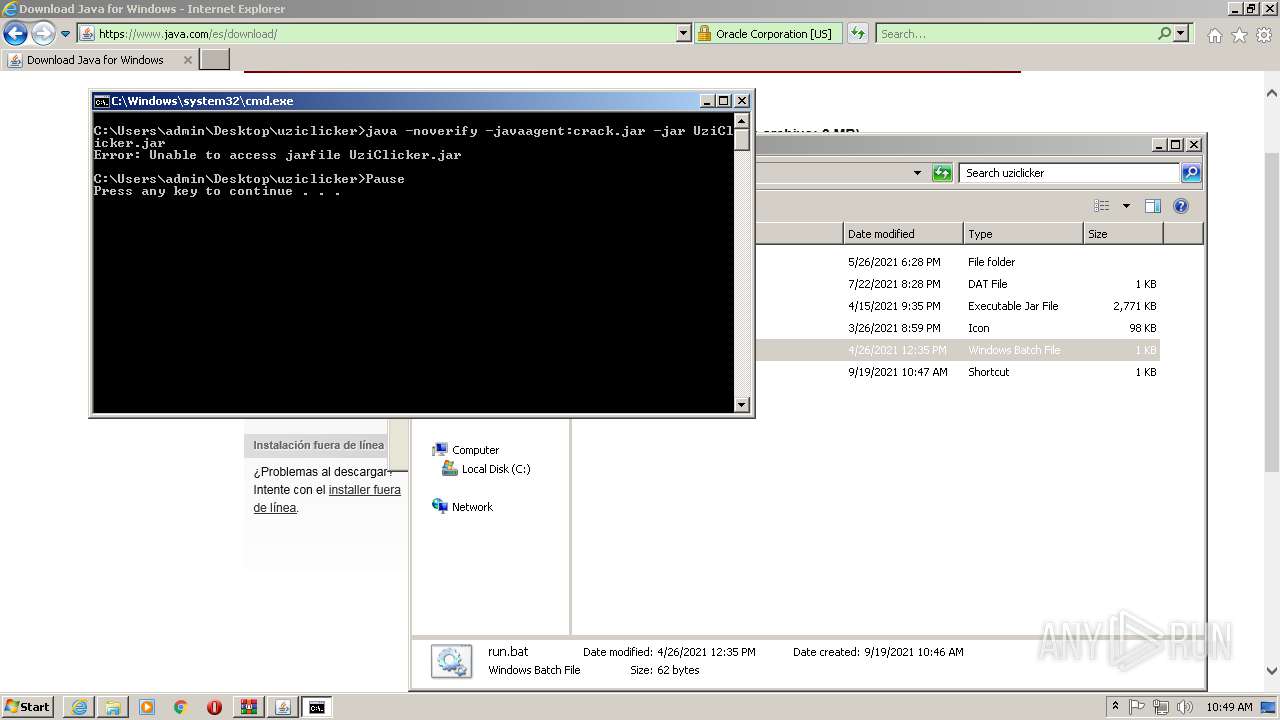
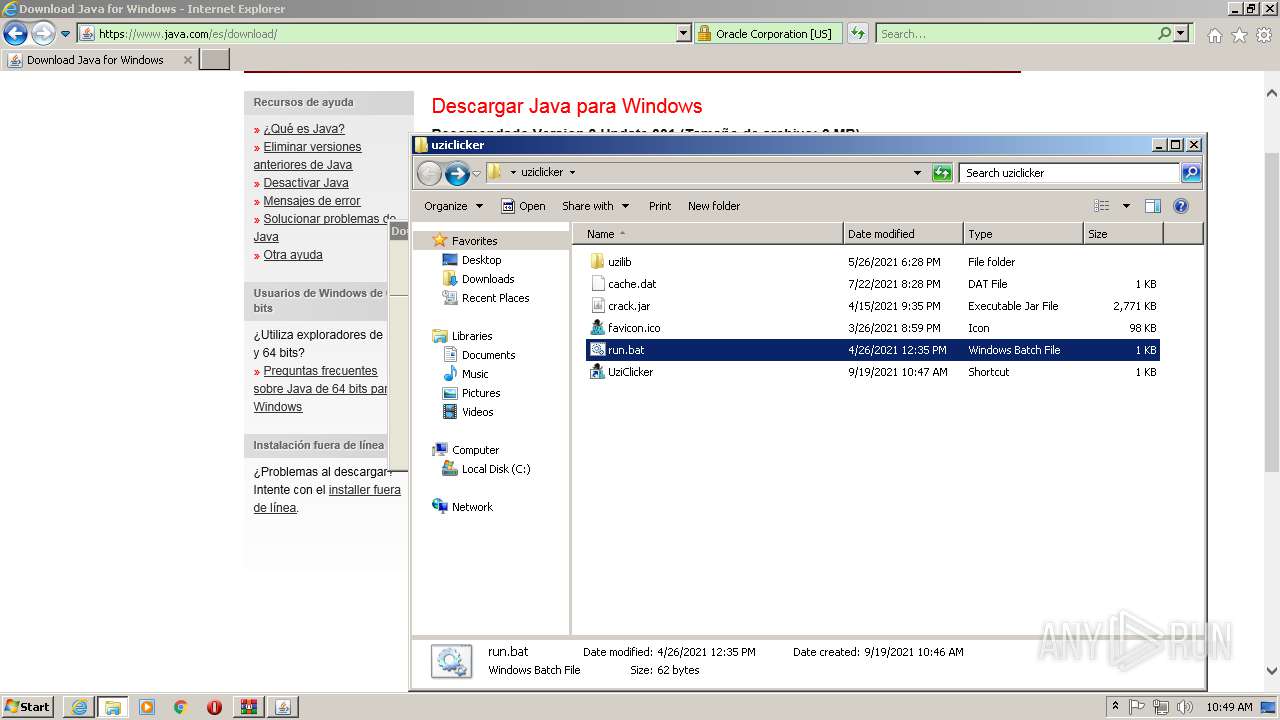
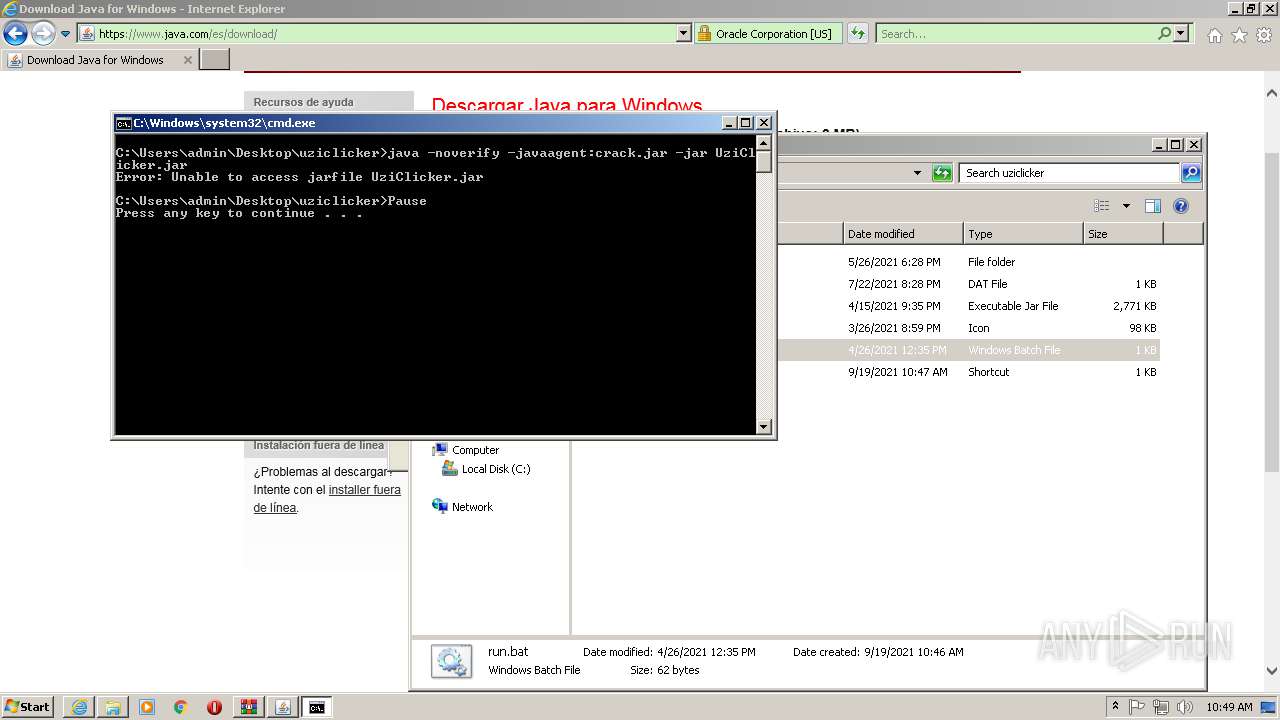
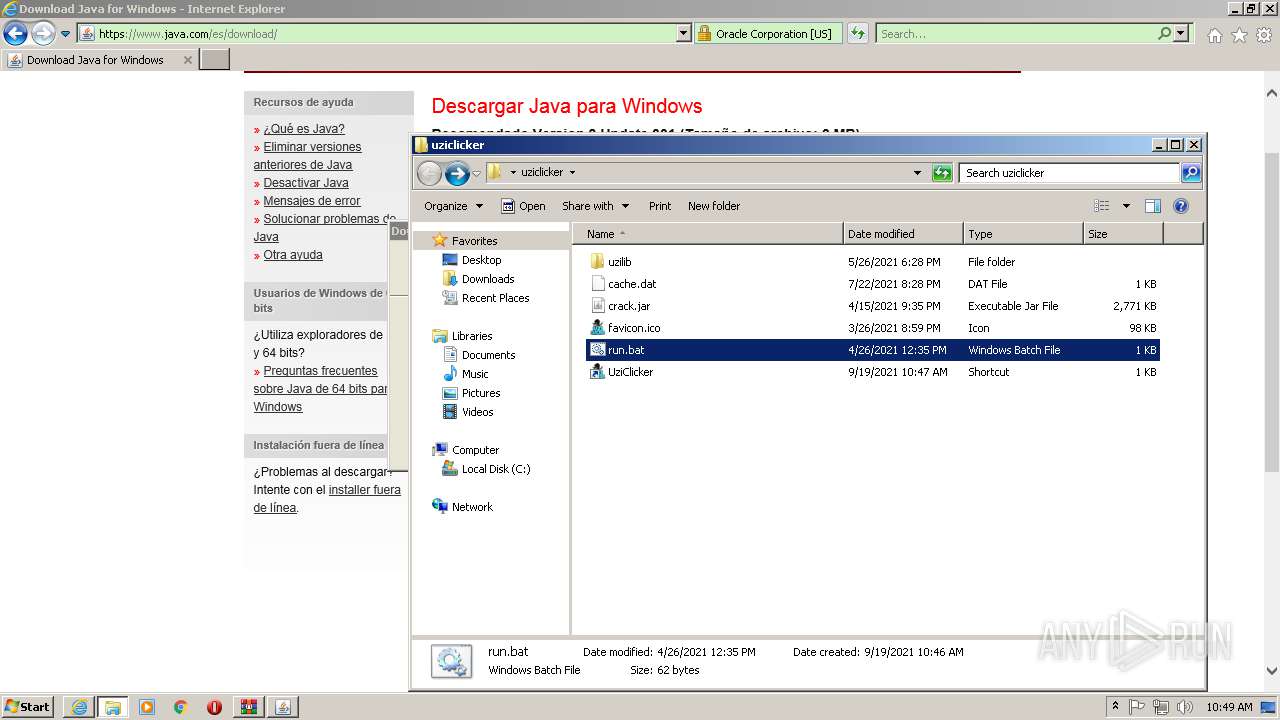
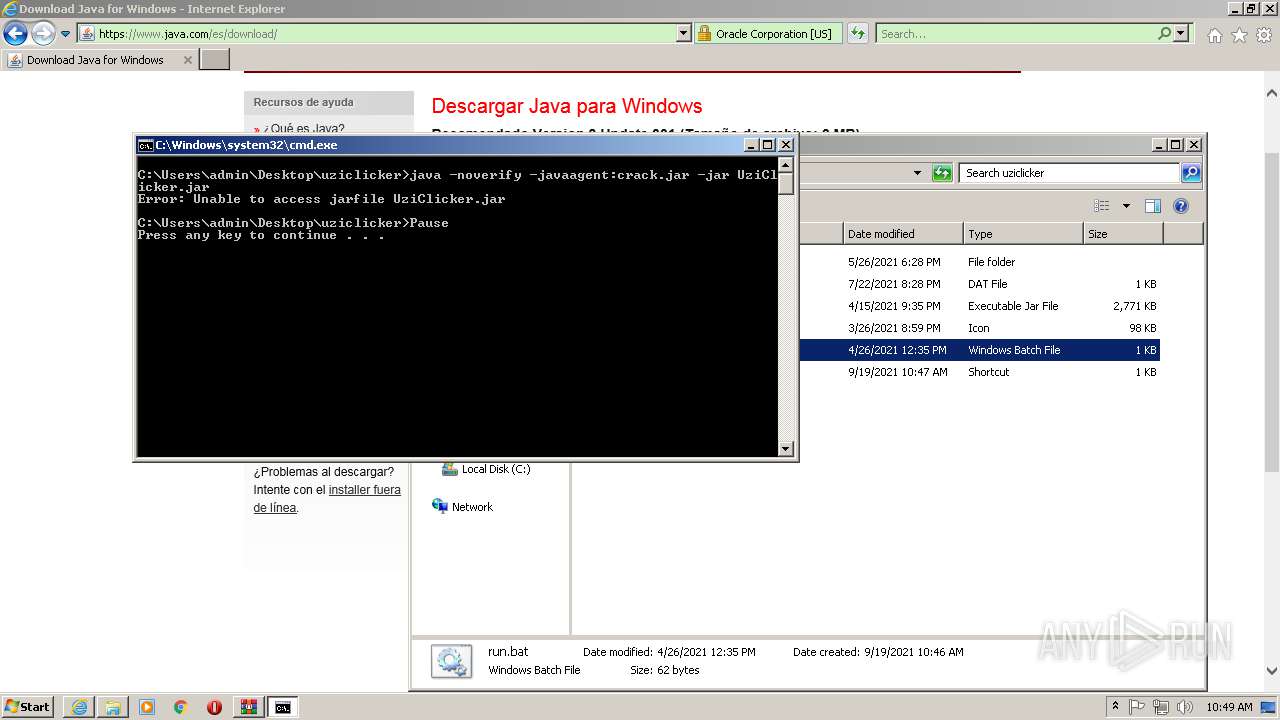
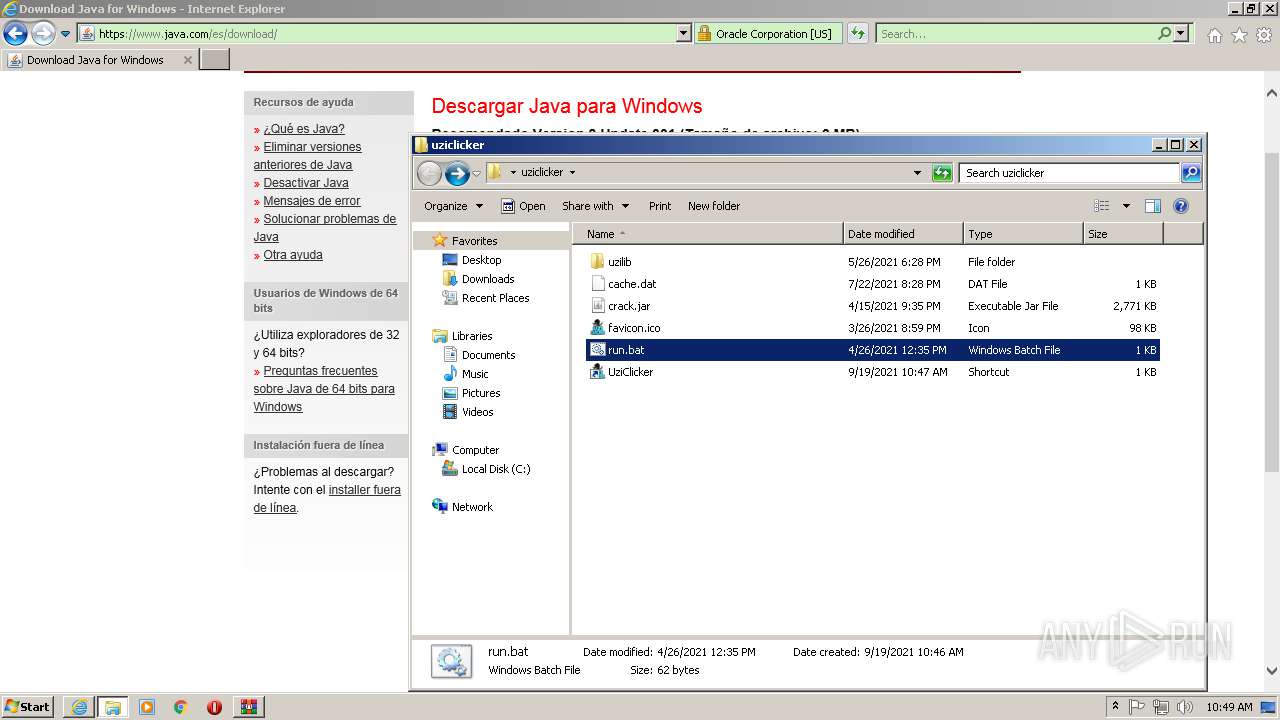
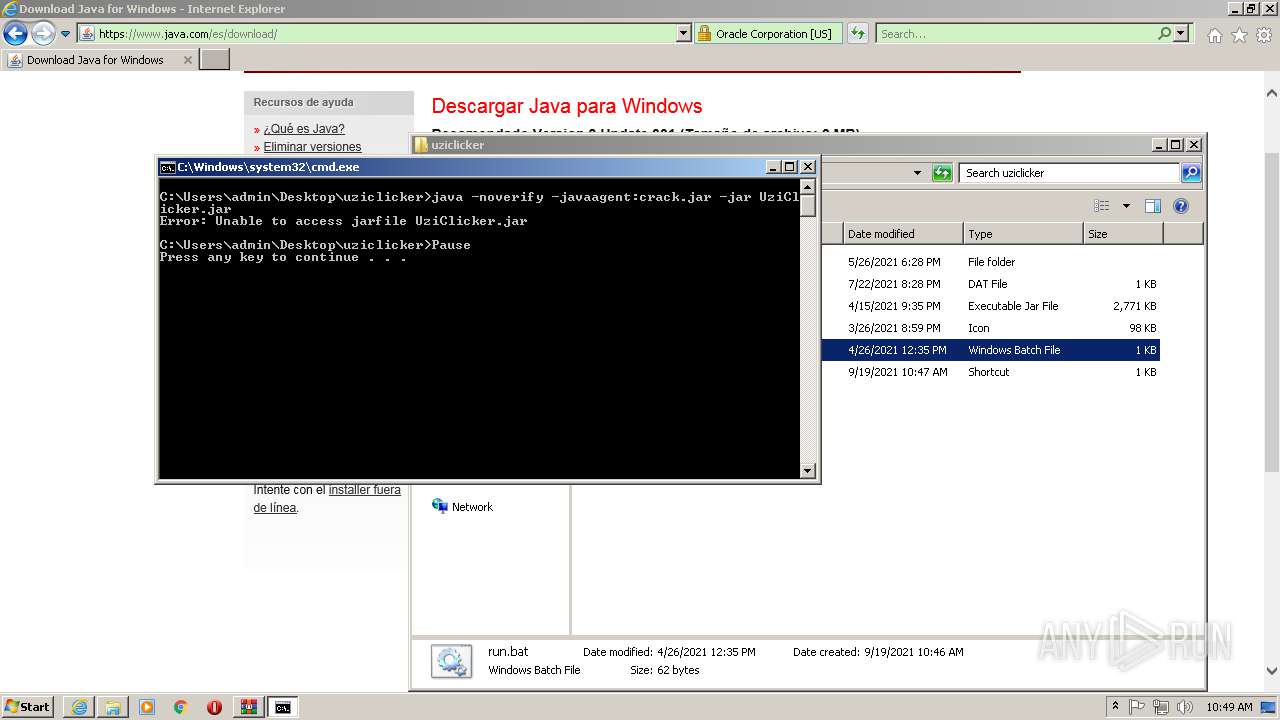
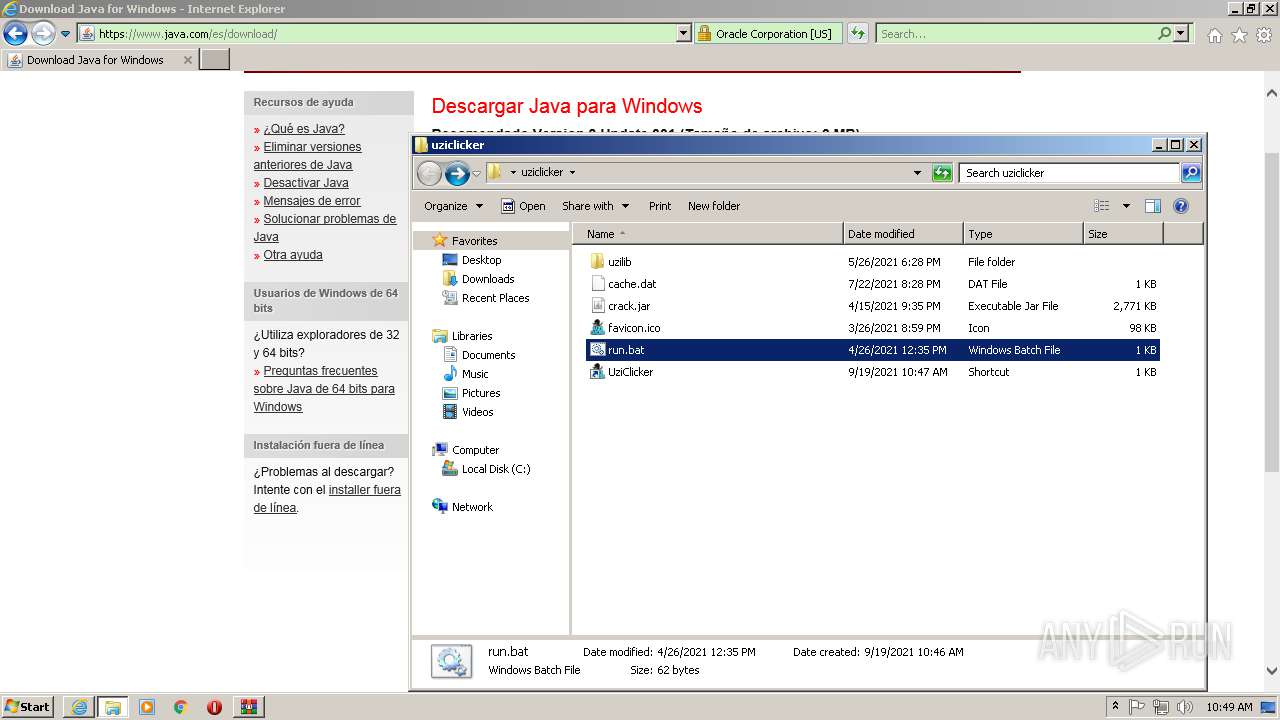
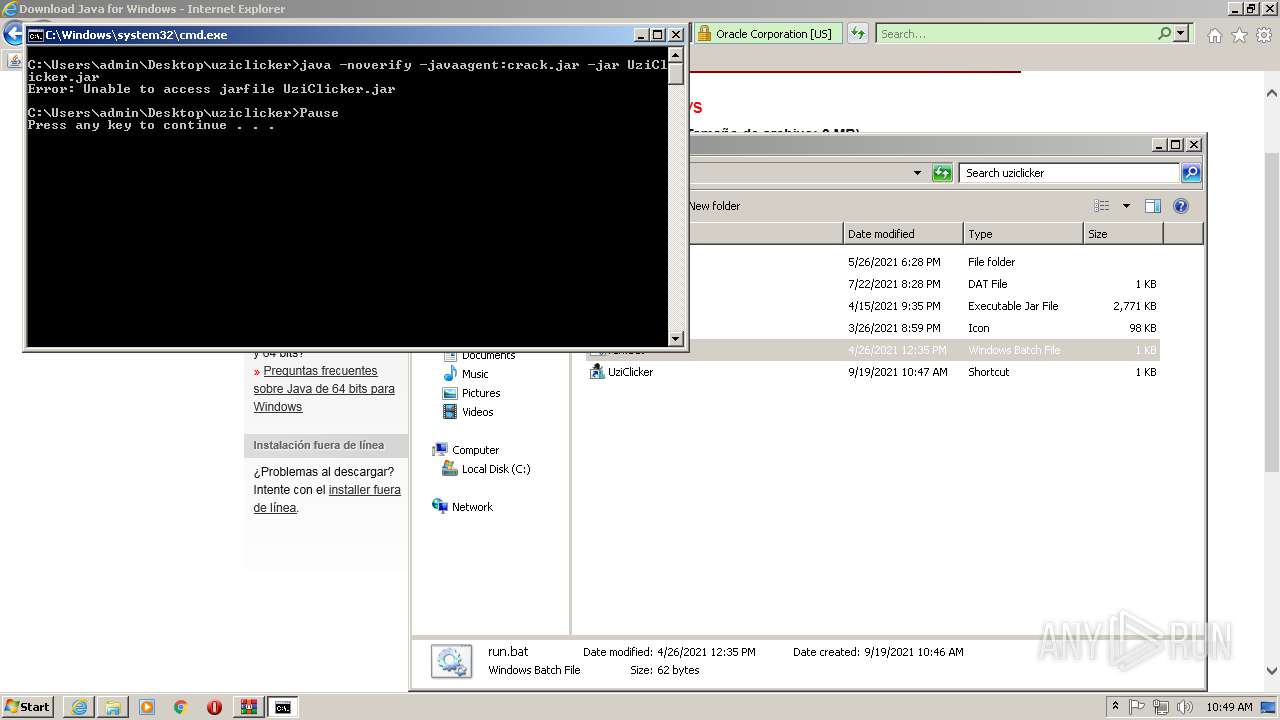
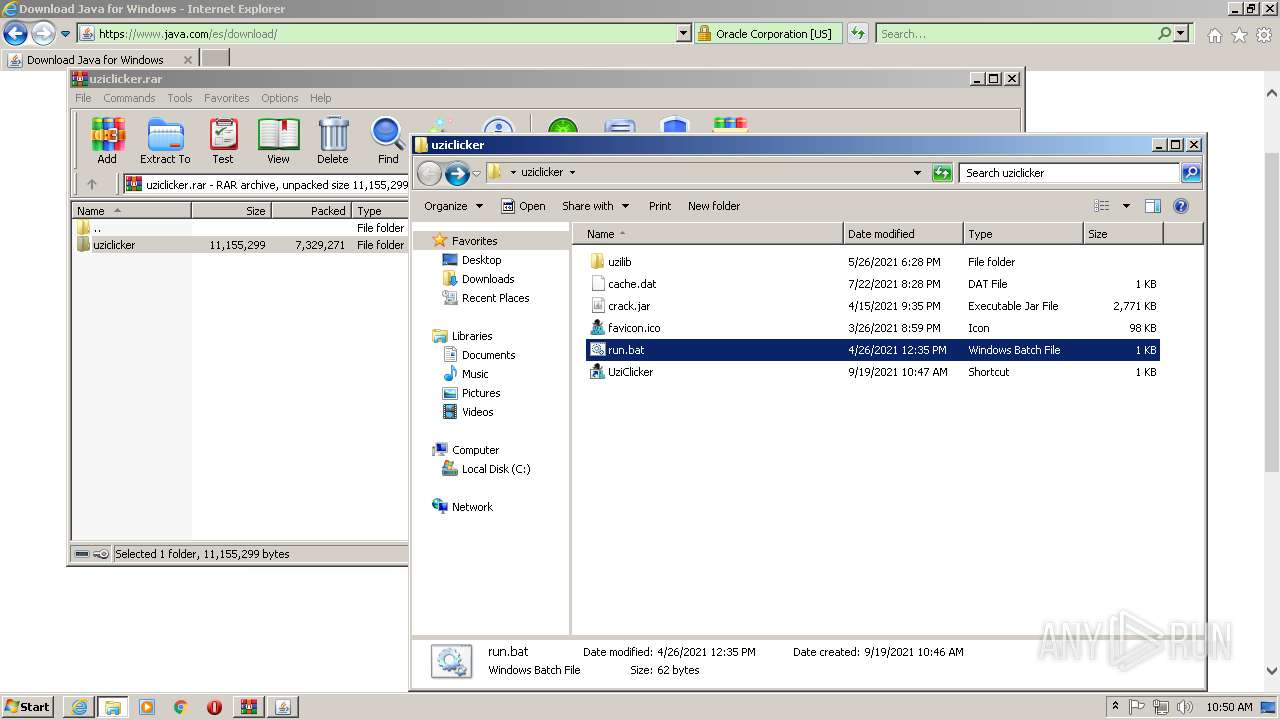
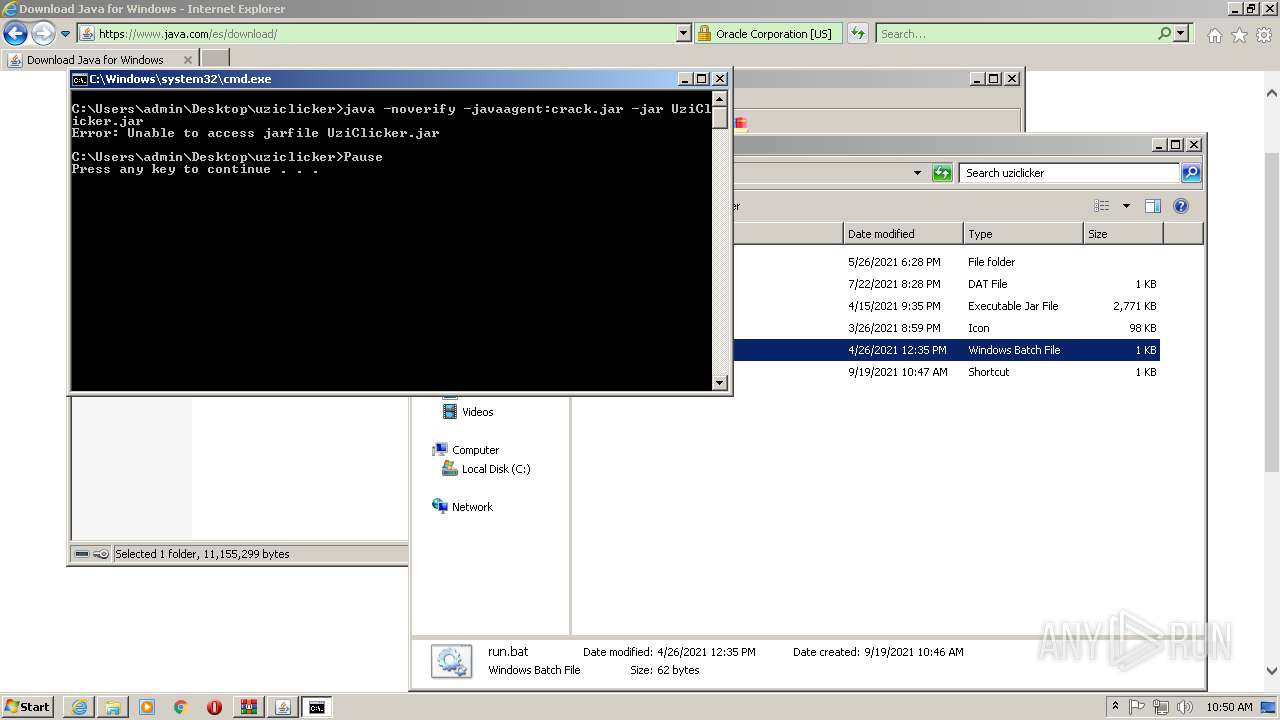
| 276 | java -noverify -javaagent:crack.jar -jar UziClicker.jar | C:\Program Files\Common Files\Oracle\Java\javapath\java.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 296 | "C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_301\LZMA_EXE" d "C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_301\jre1.8.0_301full.msi" "C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_301\msi.tmp" | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_301\LZMA_EXE | — | JavaSetup8u301.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 372 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | java -noverify -javaagent:crack.jar -jar UziClicker.jar | C:\Program Files\Common Files\Oracle\Java\javapath\java.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 796 | "C:\Program Files\Java\jre1.8.0_301\bin\javaw.exe" -Xshare:dump -Djdk.disableLastUsageTracking | C:\Program Files\Java\jre1.8.0_301\bin\javaw.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.3010.9 Modules
| |||||||||||||||
| 868 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 888 | "C:\Program Files\Java\jre1.8.0_301\bin\ssvagent.exe" -doHKCUSSVSetup | C:\Program Files\Java\jre1.8.0_301\bin\ssvagent.exe | — | installer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 1 Version: 11.301.2.09 Modules
| |||||||||||||||
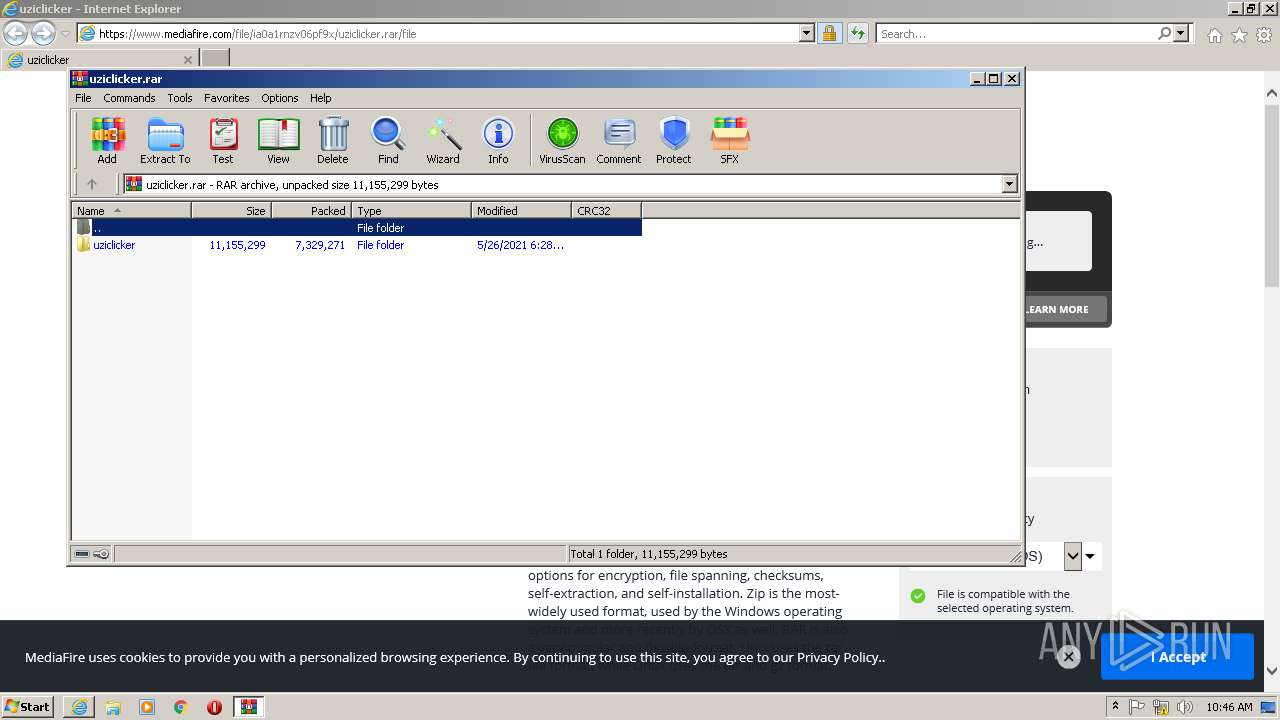
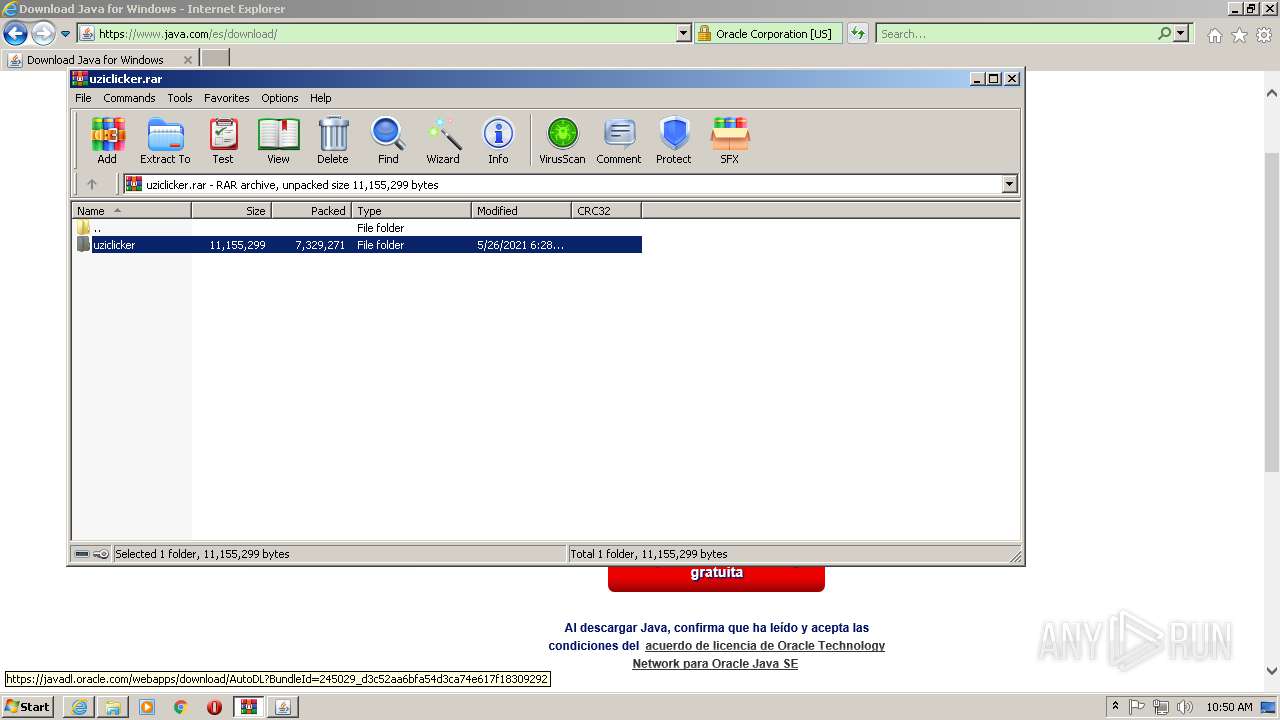
| 1008 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\uziclicker.rar" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1476 | java -noverify -javaagent:crack.jar -jar UziClicker.jar | C:\Program Files\Common Files\Oracle\Java\javapath\java.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 1540 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
97 550
Read events
48 255
Write events
30 265
Delete events
19 030
Modification events
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 933715312 | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30911803 | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30911803 | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
185
Suspicious files
66
Text files
470
Unknown types
62
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\P9GSH5F9.txt | text | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\M3FP3Q81.txt | text | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\HGV5O0T5.txt | text | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\file[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
146
DNS requests
65
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2576 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?677f40872a813f2b | US | — | — | whitelisted |
2576 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8894ba70aa3e7ae5 | US | — | — | whitelisted |
1556 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1556 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEF6zheUj6D92CgAAAAD87%2BI%3D | US | der | 471 b | whitelisted |
1556 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDc6ok2a4jVfAoAAAAA%2FPgi | US | der | 472 b | whitelisted |
1556 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFHaWjEYFdW1AwAAAADMrDQ%3D | US | der | 471 b | whitelisted |
1556 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1556 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEBpGpe6uocJhCgAAAAD87%2BQ%3D | US | der | 471 b | whitelisted |
1556 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDZ%2Fa9m7efDAwoAAAAA%2FO%2Fg | US | der | 472 b | whitelisted |
1556 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECECUTgfQsc%2BcBwNBMQNWQl0M%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1556 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
1556 | iexplore.exe | 142.250.185.174:443 | translate.google.com | Google Inc. | US | whitelisted |
1556 | iexplore.exe | 104.16.202.237:443 | www.mediafire.com | Cloudflare Inc | US | unknown |
1556 | iexplore.exe | 104.16.203.237:443 | www.mediafire.com | Cloudflare Inc | US | unknown |
1556 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1556 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1556 | iexplore.exe | 142.250.180.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
1556 | iexplore.exe | 142.250.185.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1556 | iexplore.exe | 142.250.185.74:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
1556 | iexplore.exe | 142.250.184.193:443 | lh3.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
translate.google.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
c.aaxads.com |
| whitelisted |
cdn.otnolatrnup.com |
| whitelisted |