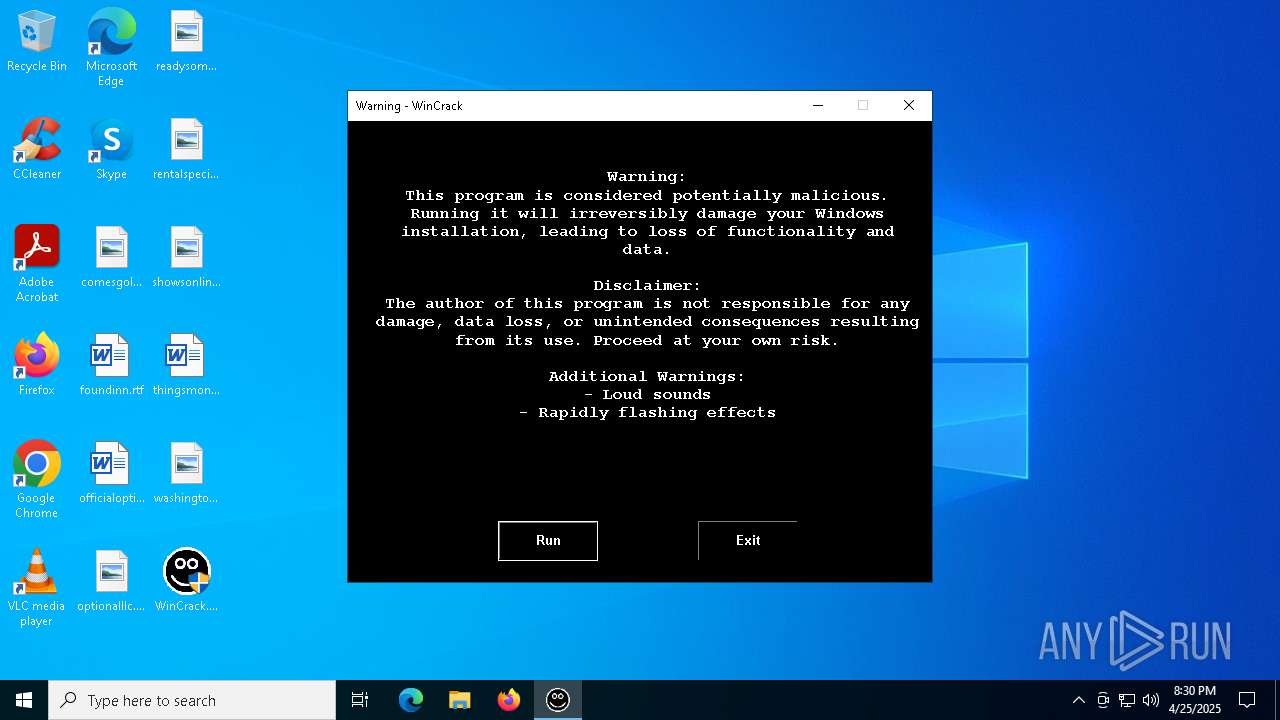
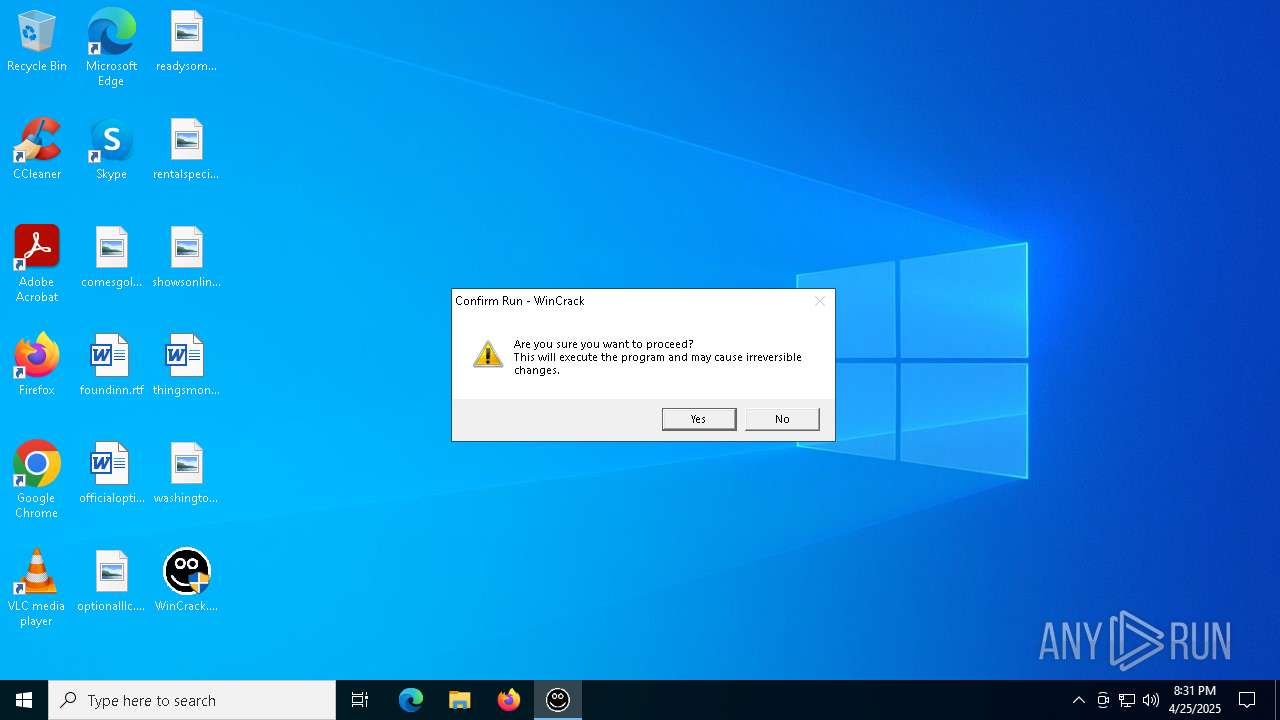
| File name: | WinCrack.exe |
| Full analysis: | https://app.any.run/tasks/aedad0b2-a939-4bd5-ae9b-10ba10880753 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2025, 20:30:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | 71BA1B4BA5D9B525BFD0565E12846B5F |
| SHA1: | 0F5300AAF57F473BD1ED3283DFB6E12A3A007F9E |
| SHA256: | F898D4C0B2666E6B01AD5EB8123E582C5276B0EF72491C466D7C118216DE66A6 |
| SSDEEP: | 98304:QFP/dmCxbC5HU5yx+VC5bix0FHOFqBoIB7Bpej90N1S0xLJEladseTtcbFcsWyHS:Yj7AU |
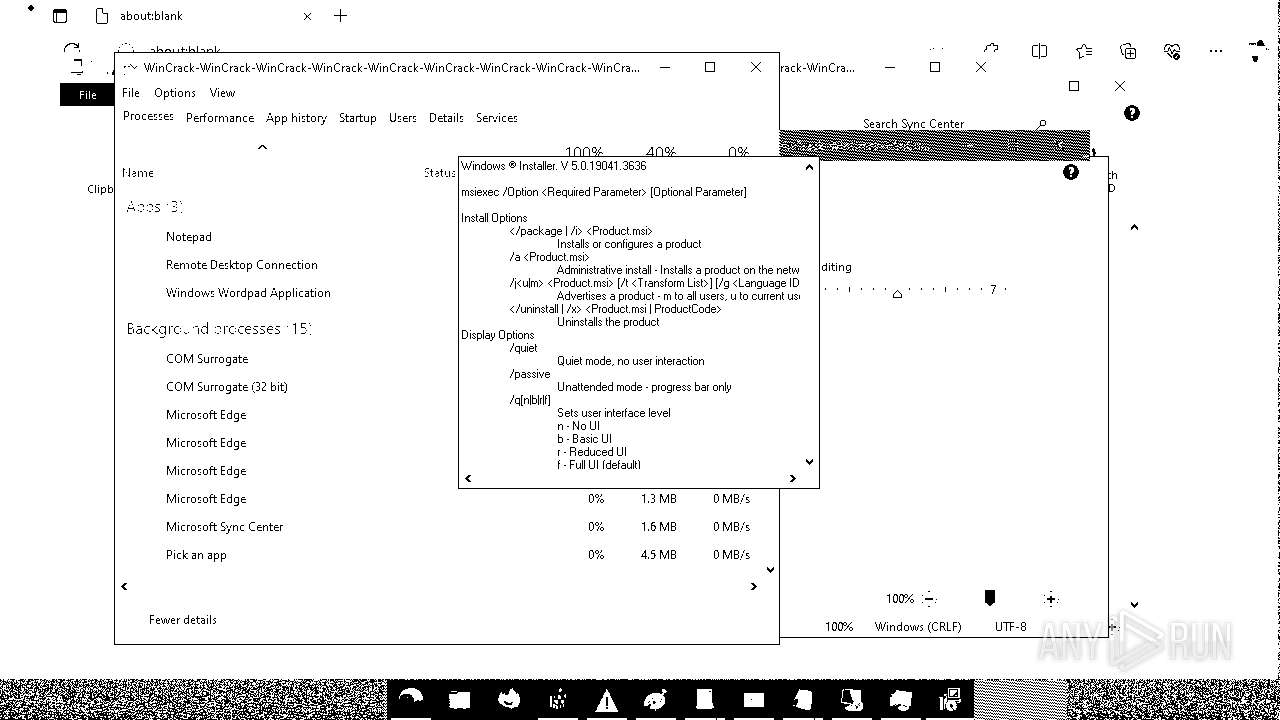
MALICIOUS
Changes the login/logoff helper path in the registry
- WinCrack.exe (PID: 7700)
Disables Windows Defender
- WinCrack.exe (PID: 7700)
Starts REAGENTC.EXE to disable the Windows Recovery Environment
- ReAgentc.exe (PID: 7896)
UAC/LUA settings modification
- WinCrack.exe (PID: 7700)
Deletes shadow copies
- cmd.exe (PID: 8032)
SUSPICIOUS
Executable content was dropped or overwritten
- WinCrack.exe (PID: 7700)
Starts CMD.EXE for commands execution
- WinCrack.exe (PID: 7700)
- msmgr.exe (PID: 4508)
There is functionality for taking screenshot (YARA)
- WinCrack.exe (PID: 7700)
Uses WMIC.EXE to obtain user accounts information
- cmd.exe (PID: 7248)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 5408)
- msmgr.exe (PID: 4508)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 5988)
- cmd.exe (PID: 5980)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 3620)
The system shut down or reboot
- cmd.exe (PID: 7248)
Reads the date of Windows installation
- msmgr.exe (PID: 4508)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 5980)
The process checks if it is being run in the virtual environment
- icacls.exe (PID: 5916)
Start notepad (likely ransomware note)
- msmgr.exe (PID: 4508)
Changes the desktop background image
- WinCrack.exe (PID: 7700)
Executes as Windows Service
- VSSVC.exe (PID: 8116)
INFO
Reads the computer name
- WinCrack.exe (PID: 7700)
- ShellExperienceHost.exe (PID: 5408)
- PLUGScheduler.exe (PID: 3620)
Changes file name
- cmd.exe (PID: 7248)
Reads the machine GUID from the registry
- WinCrack.exe (PID: 7700)
- msmgr.exe (PID: 4508)
Checks supported languages
- ShellExperienceHost.exe (PID: 5408)
- WinCrack.exe (PID: 7700)
- msmgr.exe (PID: 4508)
Process checks whether UAC notifications are on
- WinCrack.exe (PID: 7700)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7240)
Process checks computer location settings
- msmgr.exe (PID: 4508)
Creates files in the program directory
- PLUGScheduler.exe (PID: 3620)
Application launched itself
- msedge.exe (PID: 5764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2058:09:21 05:30:56+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 48 |
| CodeSize: | 4818944 |
| InitializedDataSize: | 99840 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | WinCrack.exe |
| LegalCopyright: | |
| OriginalFileName: | WinCrack.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
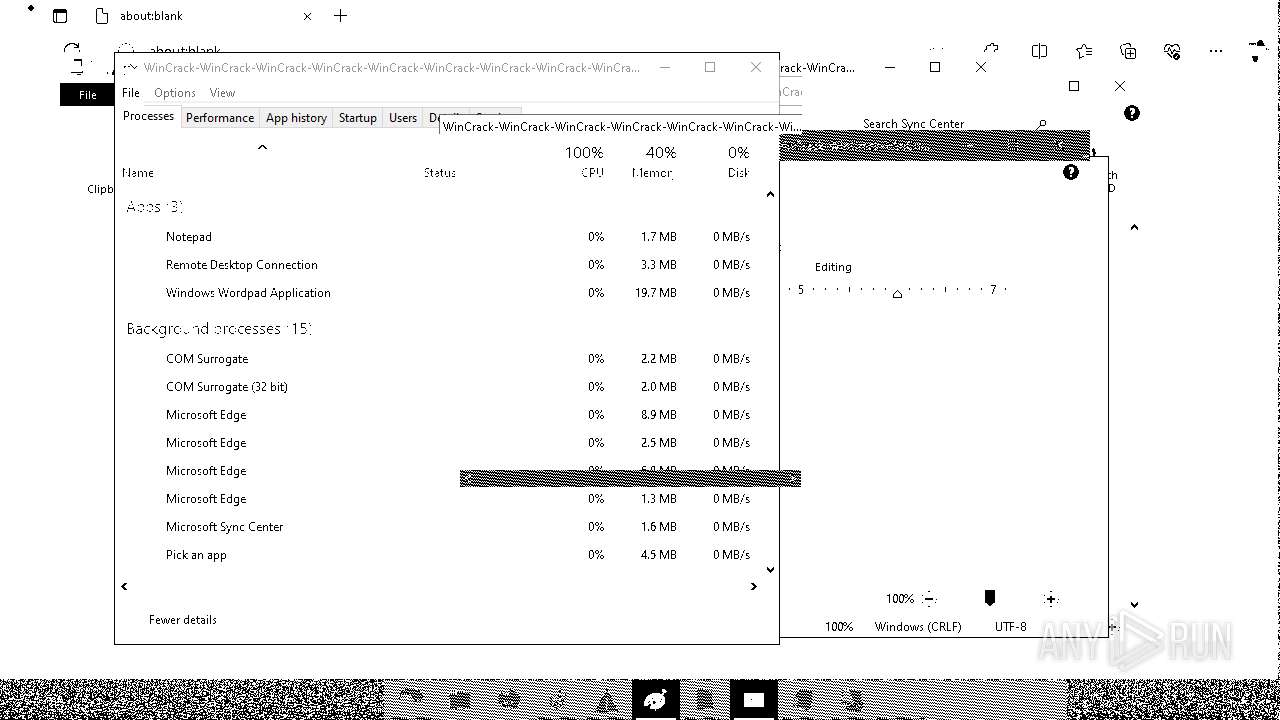
Total processes
323
Monitored processes
76
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6004 --field-trial-handle=1992,i,9283604046132442250,14855267912029185802,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: WinCrack Company: Microsoft Corporation Integrity Level: HIGH Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 628 | "C:\Windows\System32\notepad.exe" | C:\Windows\System32\notepad.exe | — | msmgr.exe | |||||||||||
User: WinCrack Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 860 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | — | msmgr.exe | |||||||||||
User: WinCrack Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2652 | "C:\Windows\System32\mstsc.exe" | C:\Windows\System32\mstsc.exe | — | msmgr.exe | |||||||||||
User: WinCrack Company: Microsoft Corporation Integrity Level: HIGH Description: Remote Desktop Connection Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3620 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3620 | "C:\WINDOWS\system32\mmc.exe" "C:\Windows\System32\gpedit.msc" | C:\Windows\System32\mmc.exe | — | msmgr.exe | |||||||||||
User: WinCrack Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3656 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | msmgr.exe | |||||||||||
User: WinCrack Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3996 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x264,0x268,0x26c,0x240,0x274,0x7ffd62bf5fd8,0x7ffd62bf5fe4,0x7ffd62bf5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: WinCrack Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4508 | C:\WINDOWS\system32\msmgr.exe | C:\Windows\System32\msmgr.exe | — | winlogon.exe | |||||||||||
User: WinCrack Integrity Level: HIGH Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 4688 | shutdown /f /r /t 0 | C:\Windows\System32\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 350
Read events
20 187
Write events
102
Delete events
61
Modification events
| (PID) Process: | (7700) WinCrack.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (7700) WinCrack.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableBehaviorMonitoring |
Value: 1 | |||
| (PID) Process: | (7700) WinCrack.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableOnAccessProtection |
Value: 1 | |||
| (PID) Process: | (7700) WinCrack.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableScanOnRealtimeEnable |
Value: 1 | |||
| (PID) Process: | (7700) WinCrack.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Userinit |
Value: C:\WINDOWS\system32\winlogon.exe, C:\WINDOWS\system32\msmgr.exe, explorer.exe | |||
| (PID) Process: | (7896) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7896) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (7896) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7896) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Microsoft\Boot\bootmgfw.efi | |||
| (PID) Process: | (7896) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
7
Suspicious files
231
Text files
41
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7700 | WinCrack.exe | C:\Windows\System32\bg.bmp | — | |
MD5:— | SHA256:— | |||
| 7896 | ReAgentc.exe | C:\Windows\System32\Recovery\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 7700 | WinCrack.exe | C:\Windows\System32\msmgr.exe | executable | |
MD5:71BA1B4BA5D9B525BFD0565E12846B5F | SHA256:F898D4C0B2666E6B01AD5EB8123E582C5276B0EF72491C466D7C118216DE66A6 | |||
| 3620 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.041.etl | etl | |
MD5:09359EE89B0634478ADFF73CDA7BFB12 | SHA256:4D800AC7C55960B107C9D3E40F63130407835E69DF4F5C558C500FC0BD20D8ED | |||
| 7896 | ReAgentc.exe | C:\Windows\Panther\UnattendGC\diagwrn.xml | text | |
MD5:E7D61F31E13255B53337512E2D6EDF08 | SHA256:F5FD217C66A78E469FC33EE079506702CA14280B58FEFABFDEEE310F25E314FE | |||
| 7896 | ReAgentc.exe | C:\Windows\Panther\UnattendGC\diagerr.xml | text | |
MD5:3A8D2D92D67445734789F82D6E6D90A6 | SHA256:E80AA5A43C517844228A67E8A49E30EE8CF68979E54BA0A3FE660C80978808C6 | |||
| 3620 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.047.etl | binary | |
MD5:FED961067F664B5381B65A534B7AB728 | SHA256:652F31A8284AE812D1D9D24192BC800976BF74C240591C6AC443A28C4709FB7C | |||
| 3620 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.036.etl | binary | |
MD5:A477FE56C25FCDB850EA1AAB8D01B5C2 | SHA256:5C85DC2B41C2D076D6B2653C0BA5F5681ADABFEBDA8883C704E625EB9338F505 | |||
| 3620 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.048.etl | etl | |
MD5:A23907B6FDD47DCABFDFD7CF2FCD7671 | SHA256:0C9C33FE9E984A2E5A70EBA51F36B9929A86199E424AF2F8080E1267B87DC970 | |||
| 3620 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.050.etl | etl | |
MD5:C8834D365FAE073DEDE1F1620454CE71 | SHA256:C6DD793EEE1D5551CA507A3C5BFFECA82DD3E29C63C2C6DD218A7D4BFB37046B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
48
DNS requests
39
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4380 | RUXIMICS.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 401 | 13.107.6.158:443 | https://business.bing.com/api/v1/user/token/microsoftgraph?&clienttype=edge-omnibox | unknown | — | — | unknown |
— | — | OPTIONS | 200 | 2.16.168.201:443 | https://bzib.nelreports.net/api/report?cat=bingbusiness | unknown | — | — | unknown |
4380 | RUXIMICS.exe | GET | 200 | 92.123.22.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.227.215:443 | https://www.bing.com/rb/16/jnc,nj/-M-8YWX0KlEtdAHVrkTvKQHOghs.js?bu=DicwgAGNAZQBlwGKAYMBhwHCAcUBMLoByAE&or=w | unknown | binary | 22.0 Kb | whitelisted |
— | — | GET | 401 | 13.107.6.158:443 | https://business.bing.com/work/api/v2/tenant/my/settingswithflights?&clienttype=edge-omnibox | unknown | binary | 582 b | whitelisted |
— | — | GET | 200 | 2.23.227.215:443 | https://www.bing.com/rb/19/cir3,ortl,cc,nc/FgBbpIj0thGWZOh_xFnM9i4O7ek.css?bu=C6QK2APsBPYK3gnICcAHYWFhYQ&or=w | unknown | text | 19.8 Kb | whitelisted |
— | — | GET | 200 | 2.23.227.208:443 | https://www.bing.com/rb/19/cir3,ortl,cc,nc/EdGMywLcB7jTlSP4Cnh3fVWBpmk.css?bu=B-oCRtgC0gFhYfMC&or=w | unknown | text | 6.30 Kb | whitelisted |
— | — | GET | 200 | 2.23.227.215:443 | https://www.bing.com/rb/3D/ortl,cc,nc/AptopUBu7_oVDubJxwvaIprW-lI.css?bu=A4gCjAKPAg&or=w | unknown | text | 15.5 Kb | whitelisted |
— | — | GET | 200 | 2.23.227.215:443 | https://www.bing.com/rb/18/jnc,nj/6hU_LneafI_NFLeDvM367ebFaKQ.js?bu=DyIrb3t-gQF4cnWyAbUBK6UBK7gB&or=w | unknown | binary | 21.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4380 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4380 | RUXIMICS.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
4380 | RUXIMICS.exe | 92.123.22.101:80 | www.microsoft.com | AKAMAI-AS | AT | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
5764 | msedge.exe | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
www.bing.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |