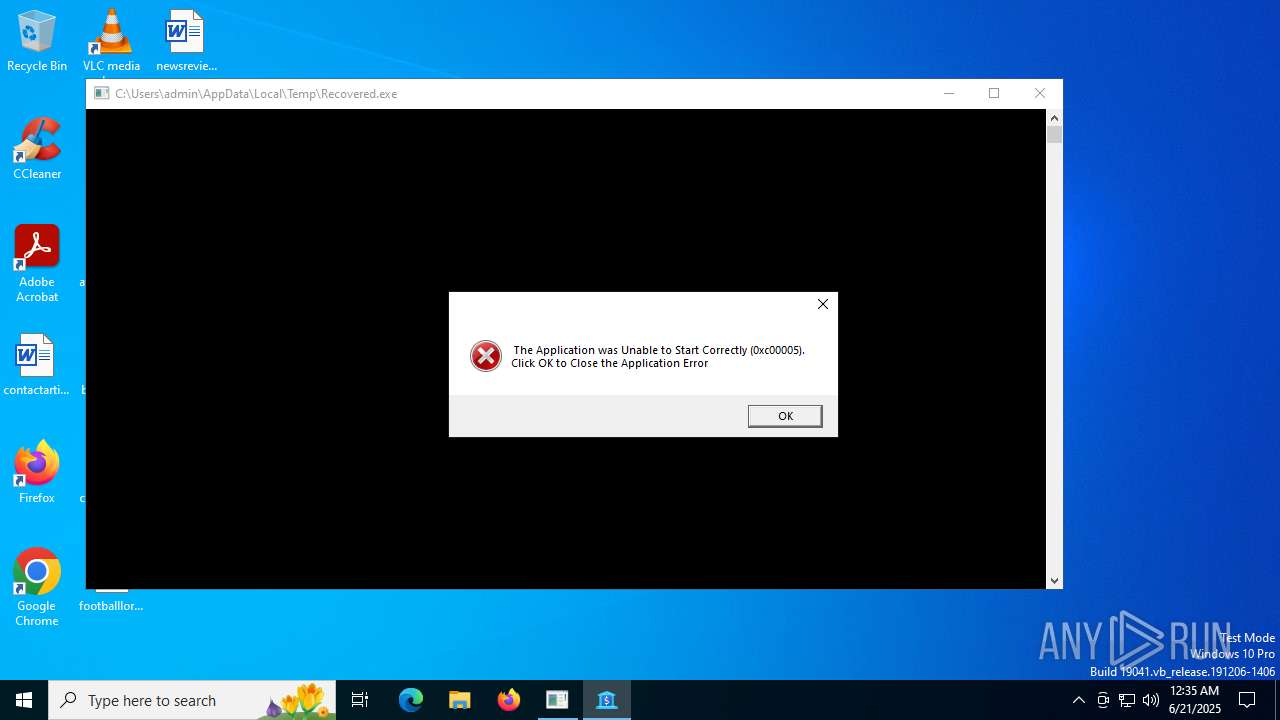
| File name: | Recovered.exe |
| Full analysis: | https://app.any.run/tasks/4f047629-f970-4fc4-b2b1-c42c9d3114bf |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 00:34:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 12C725E3EC3829E06CB3085005A14325 |
| SHA1: | F7B001D143994067EC37D2C5DC6BC3E26A40E36C |
| SHA256: | F85FD54AF77B8F1222BC4AD4EA65D883A5CE1236C72913521E25144DBBA67E09 |
| SSDEEP: | 12288:OvgCPZAPMk9ifKzWsH8aR/s8or4uP5t0ire1H:8gCPZeM0iiWsH8aZs8or4uPle1H |
MALICIOUS
Changes Windows Defender settings
- Recovered.exe (PID: 1560)
Adds path to the Windows Defender exclusion list
- Recovered.exe (PID: 1560)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- Recovered.exe (PID: 1560)
Script adds exclusion path to Windows Defender
- Recovered.exe (PID: 1560)
Removes files via Powershell
- powershell.exe (PID: 2220)
- powershell.exe (PID: 3832)
Reads the date of Windows installation
- Recovered.exe (PID: 1560)
Connects to unusual port
- Recovered.exe (PID: 1560)
- A1.exe (PID: 5720)
Executable content was dropped or overwritten
- Recovered.exe (PID: 1560)
Reads security settings of Internet Explorer
- Recovered.exe (PID: 1560)
INFO
Process checks computer location settings
- Recovered.exe (PID: 1560)
Reads the computer name
- Recovered.exe (PID: 1560)
- A1.exe (PID: 5720)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1296)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1296)
Reads the machine GUID from the registry
- Recovered.exe (PID: 1560)
- A1.exe (PID: 5720)
Create files in a temporary directory
- Recovered.exe (PID: 1560)
Confuser has been detected (YARA)
- Recovered.exe (PID: 1560)
Checks supported languages
- Recovered.exe (PID: 1560)
- A1.exe (PID: 5720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:08:29 10:23:30+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 288256 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4859e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | yaLUvH.tmp |
| LegalCopyright: | |
| OriginalFileName: | yaLUvH.tmp |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
144
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" add-mppreference -exclusionpath @('C:\') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Recovered.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1560 | "C:\Users\admin\AppData\Local\Temp\Recovered.exe" | C:\Users\admin\AppData\Local\Temp\Recovered.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 2220 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $a = [System.Diagnostics.Process]::GetProcessById(5720);$b = $a.MainModule.FileName;$a.WaitForExit();Remove-Item -Force -Path $b; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Recovered.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2404 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Recovered.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3832 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $a = [System.Diagnostics.Process]::GetProcessById(1560);$b = $a.MainModule.FileName;$a.WaitForExit();Remove-Item -Force -Path $b; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Recovered.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4968 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5720 | "C:\Users\admin\AppData\Local\Temp\A1.exe" | C:\Users\admin\AppData\Local\Temp\A1.exe | Recovered.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Nirtro CPU Version: 15.9.1.22 Modules
| |||||||||||||||
| 6700 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 161
Read events
18 152
Write events
9
Delete events
0
Modification events
| (PID) Process: | (1560) Recovered.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1560) Recovered.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1560) Recovered.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1560) Recovered.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1560) Recovered.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
Executable files
1
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1296 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qolvoapn.1mn.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1560 | Recovered.exe | C:\Users\admin\AppData\Local\Temp\A1.exe | executable | |
MD5:28CAECE68C96BEC864C5B61D09A8AD06 | SHA256:197B50F15375335928E08C5CC5B6F50CD93864655237B8DB85556D4057F3B988 | |||
| 2220 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qi1dqr5f.2ny.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1296 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bzqtz0b3.g5v.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1296 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:966890C0BE6EA9B41BA97F9218B6AA30 | SHA256:CACD5FF7A231D145562EA9382447D0E6F1212C3FDD4EAF661BBC09F0FA668FAB | |||
| 3832 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xztjt5sw.sng.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3832 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_iedrxo1x.rdd.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2220 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3ocxmzku.f0v.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
67
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
420 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.25.50.8:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
420 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2292 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2668 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1560 | Recovered.exe | 192.248.145.110:2206 | — | AS-CHOOPA | GB | unknown |
5720 | A1.exe | 80.85.152.191:27465 | — | Chelyabinsk-Signal LLC | RU | malicious |
2292 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2292 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |