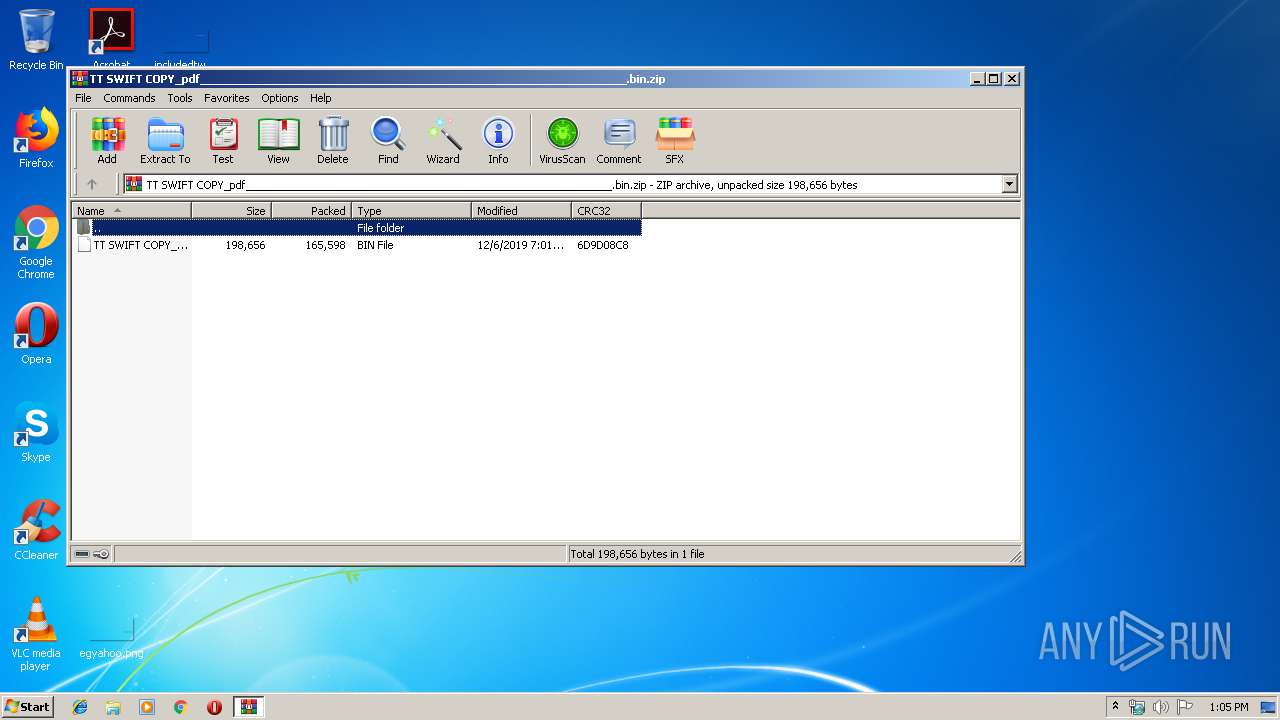
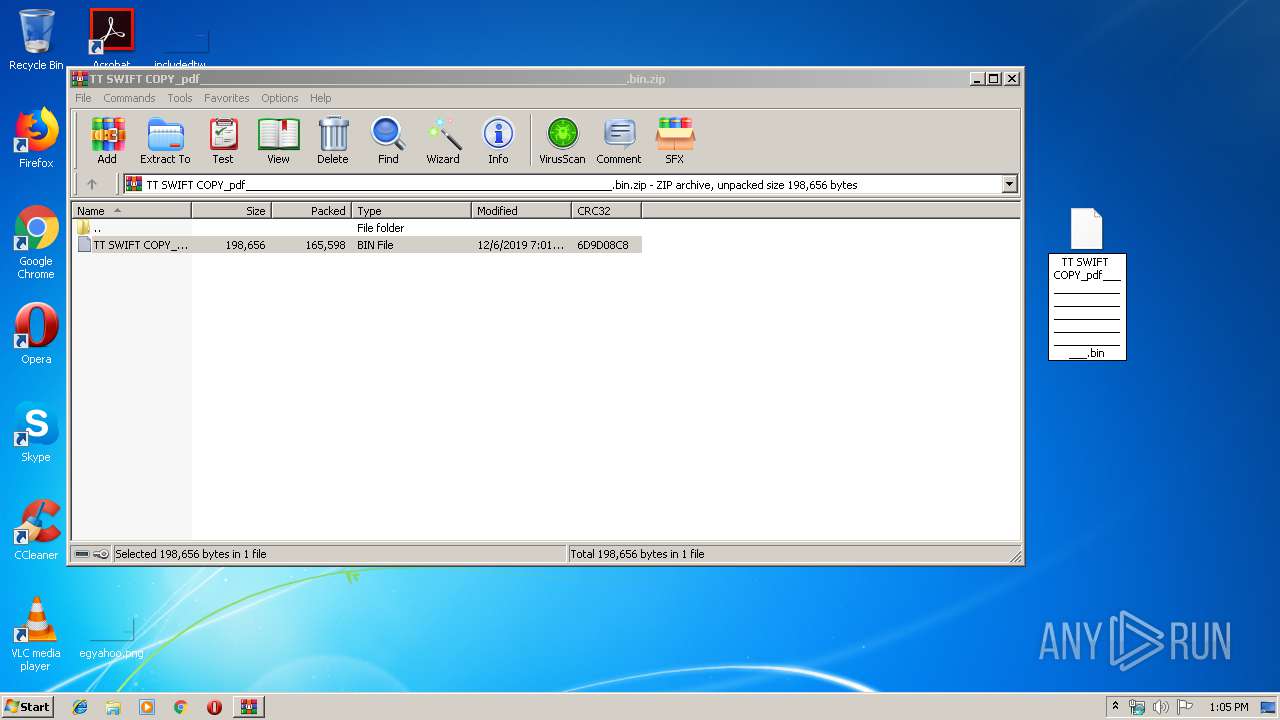
| File name: | TT SWIFT COPY_pdf_____________________________________________________________.bin.zip |
| Full analysis: | https://app.any.run/tasks/18b06975-2e5d-4cdf-95ea-00a68326dbbd |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 13:04:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 18B5BA2A76994BBE43814F4618E09C0A |
| SHA1: | 2A6D311574B5A5EFB4510A77F4225A819AC0D210 |
| SHA256: | F8590E6809A7E2CC642088349D4AEF8EBC5659DEC5F7C3673BF084E8E6EF130C |
| SSDEEP: | 3072:yt29II4rIECOD+vQaizSmkZGltUxbEIZbrt9qF1i24bh0rnTJrZLjPIbJ6m+8x:CZI4HavQVURbx9qOdhs50g8x |
MALICIOUS
Changes the autorun value in the registry
- TT SWIFT COPY_pdf_____________________________________________________________.exe (PID: 2928)
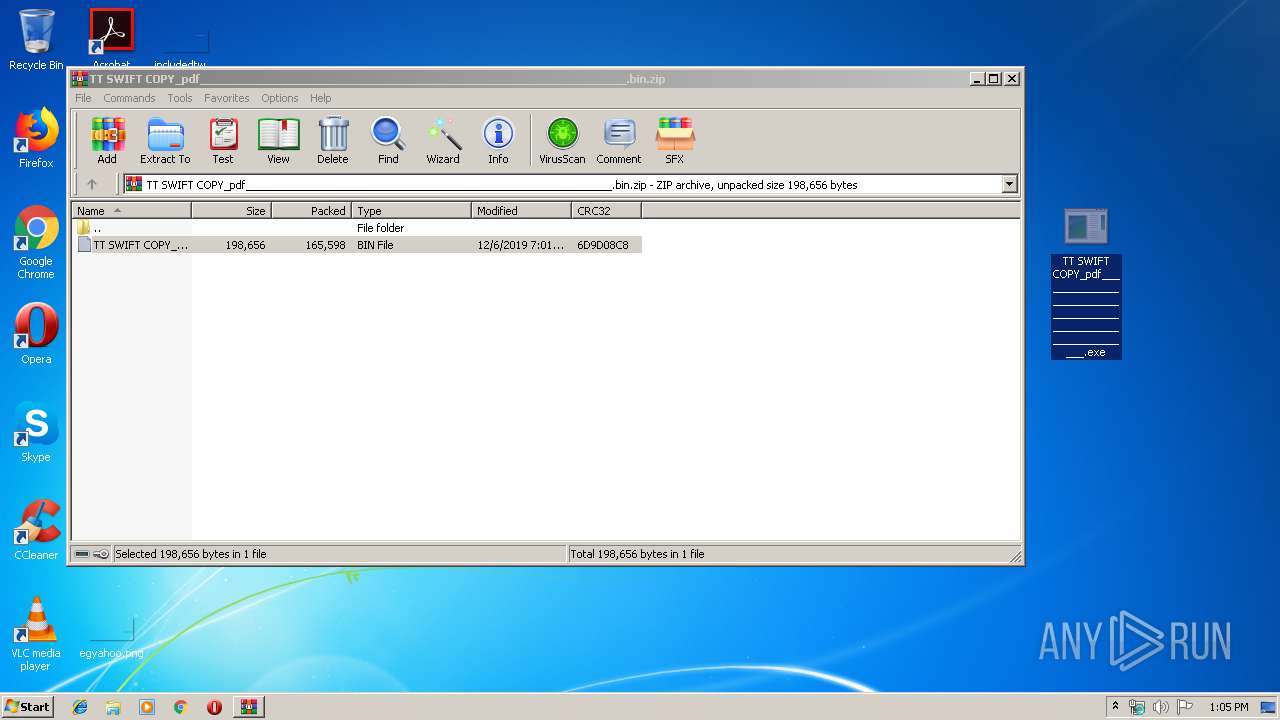
Application was dropped or rewritten from another process
- TT SWIFT COPY_pdf_____________________________________________________________.exe (PID: 2928)
Actions looks like stealing of personal data
- InstallUtil.exe (PID: 3452)
SUSPICIOUS
Creates files in the user directory
- TT SWIFT COPY_pdf_____________________________________________________________.exe (PID: 2928)
Loads DLL from Mozilla Firefox
- InstallUtil.exe (PID: 3452)
Checks for external IP
- InstallUtil.exe (PID: 3452)
Executable content was dropped or overwritten
- TT SWIFT COPY_pdf_____________________________________________________________.exe (PID: 2928)
Connects to SMTP port
- InstallUtil.exe (PID: 3452)
INFO
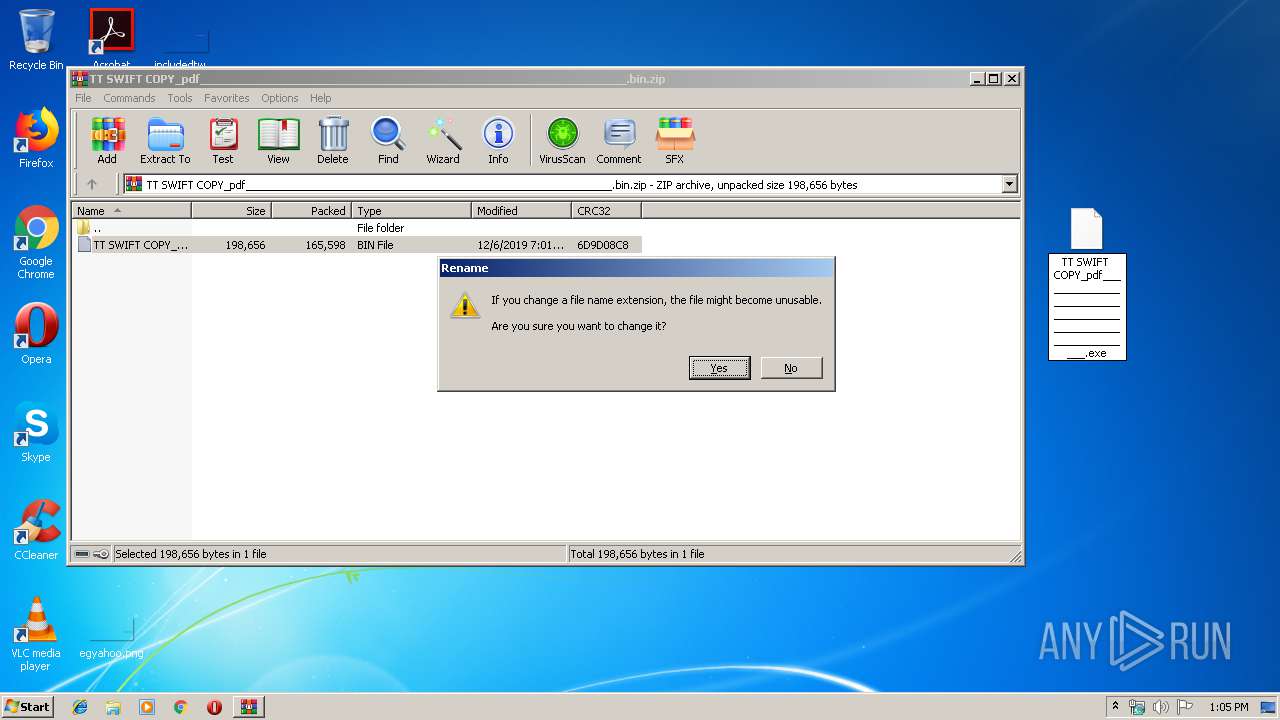
Manual execution by user
- TT SWIFT COPY_pdf_____________________________________________________________.exe (PID: 2928)
Reads settings of System Certificates
- InstallUtil.exe (PID: 3452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:06 08:01:01 |
| ZipCRC: | 0x6d9d08c8 |
| ZipCompressedSize: | 165598 |
| ZipUncompressedSize: | 198656 |
| ZipFileName: | TT SWIFT COPY_pdf_____________________________________________________________.bin |
Total processes
40
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
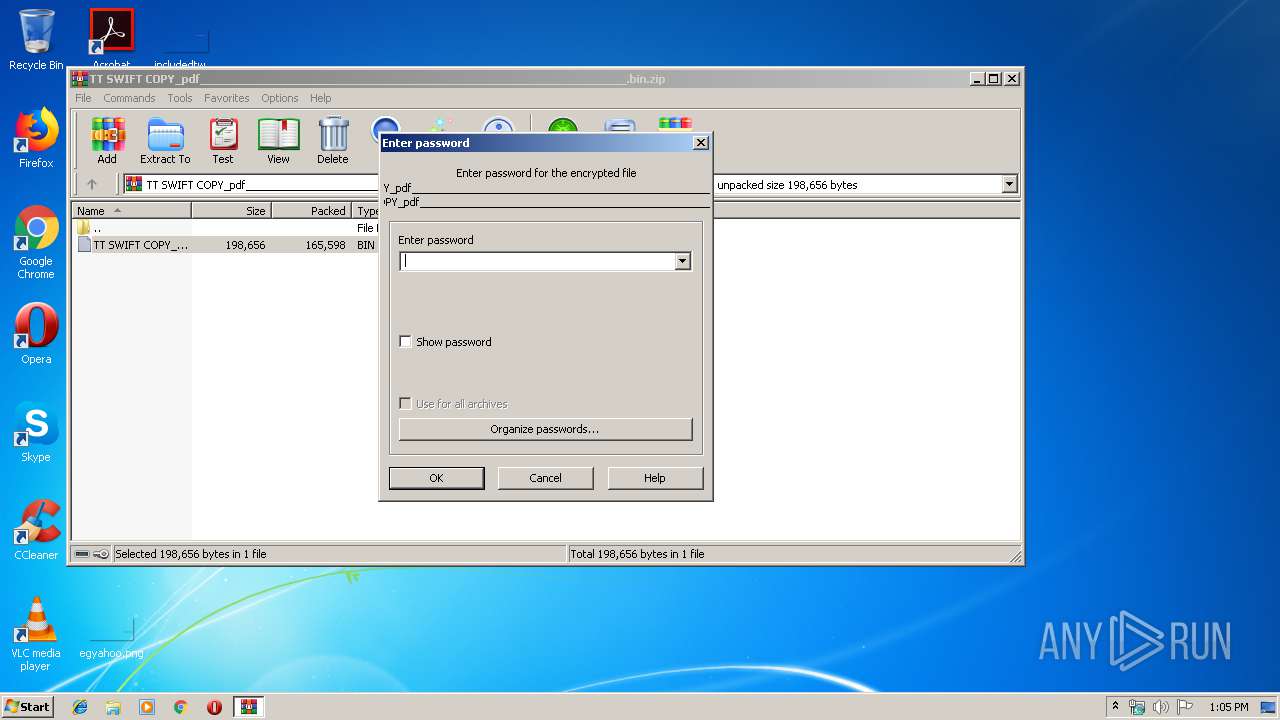
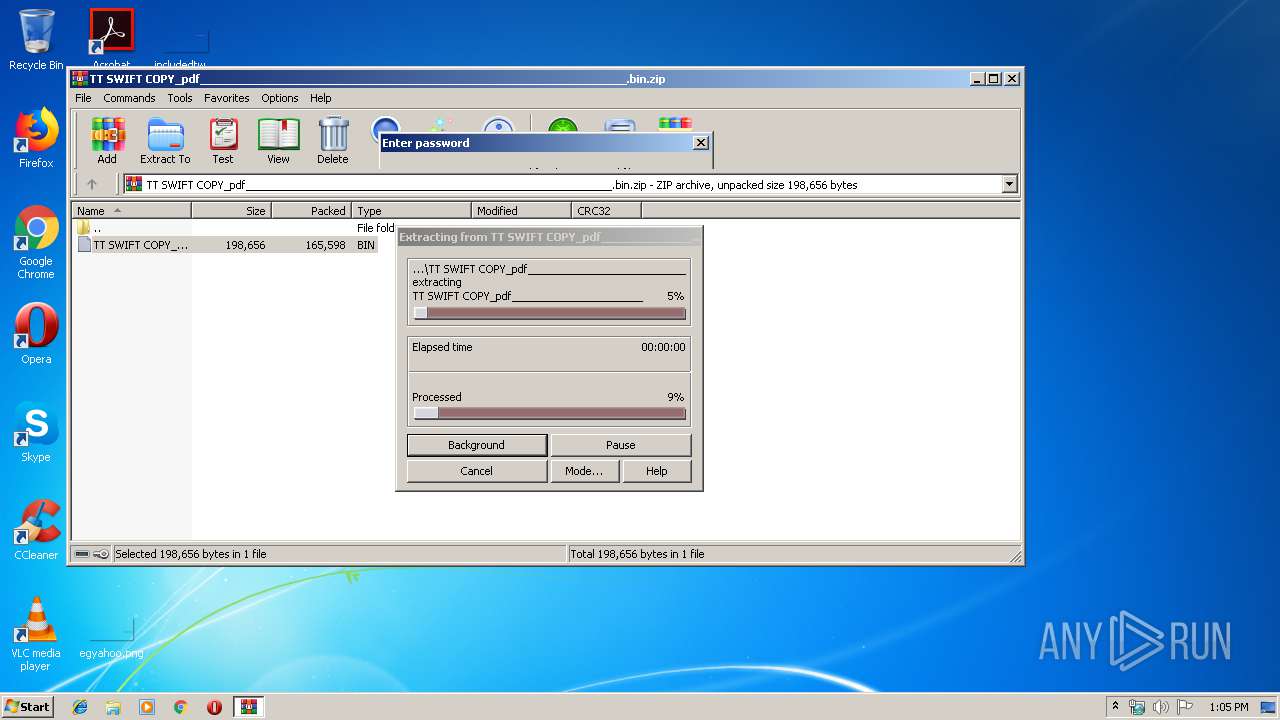
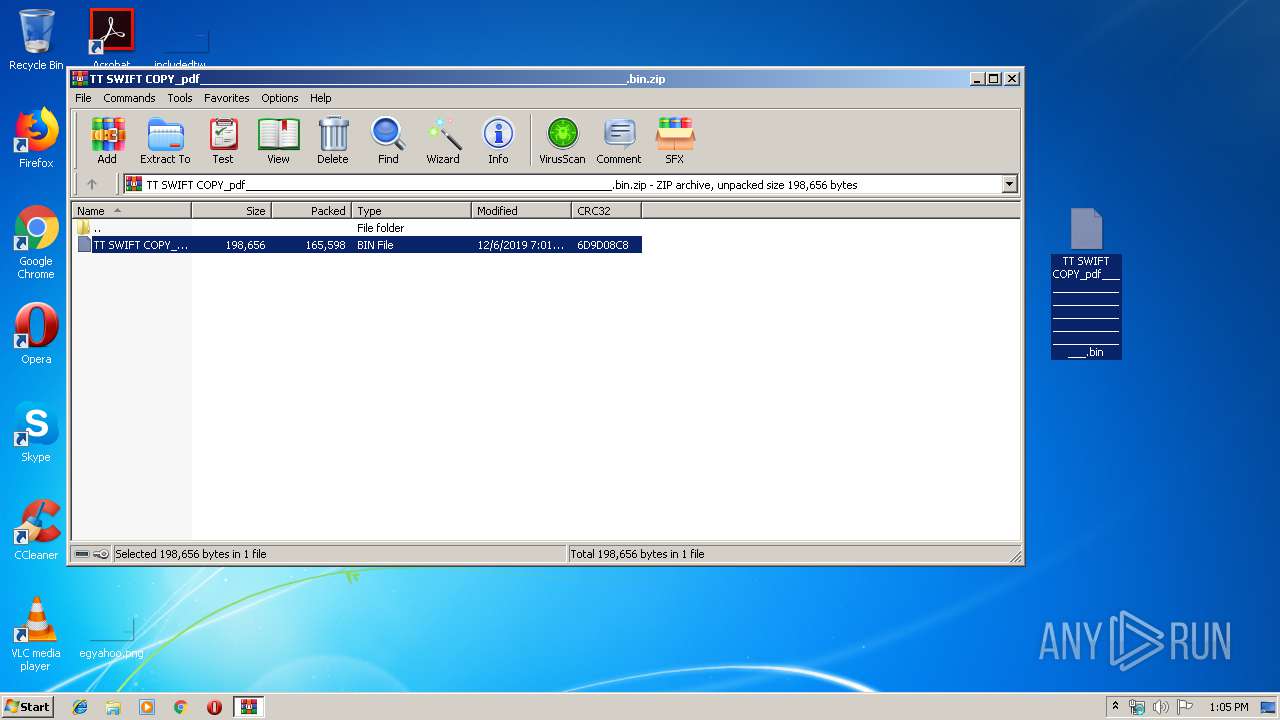
| 532 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\TT SWIFT COPY_pdf_____________________________________________________________.bin.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2928 | "C:\Users\admin\Desktop\TT SWIFT COPY_pdf_____________________________________________________________.exe" | C:\Users\admin\Desktop\TT SWIFT COPY_pdf_____________________________________________________________.exe | explorer.exe | ||||||||||||
User: admin Company: Atilla Best! Integrity Level: MEDIUM Description: Exit code: 1 Version: 1.1.1.1 Modules
| |||||||||||||||
| 3452 | "C:\Windows\\Microsoft.NET\\Framework\\v4.0.30319\\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | TT SWIFT COPY_pdf_____________________________________________________________.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
Total events
393
Read events
356
Write events
37
Delete events
0
Modification events
| (PID) Process: | (532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (532) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\TT SWIFT COPY_pdf_____________________________________________________________.bin.zip | |||
| (PID) Process: | (532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (2928) TT SWIFT COPY_pdf_____________________________________________________________.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | ZBeXB |
Value: C:\Users\admin\AppData\Roaming\ZBeXBQ\ZBeXBQKVQ.url | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb532.2704\TT SWIFT COPY_pdf_____________________________________________________________.bin | — | |
MD5:— | SHA256:— | |||
| 2928 | TT SWIFT COPY_pdf_____________________________________________________________.exe | C:\Users\admin\AppData\Roaming\ZBeXBQ\ZBeXB.exe | executable | |
MD5:— | SHA256:— | |||
| 2928 | TT SWIFT COPY_pdf_____________________________________________________________.exe | C:\Users\admin\AppData\Roaming\ZBeXBQ\ZBeXBQKVQ.url | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3452 | InstallUtil.exe | GET | 200 | 216.146.43.70:80 | http://checkip.dyndns.org/ | US | html | 104 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3452 | InstallUtil.exe | 199.193.7.228:587 | smtp.privateemail.com | Namecheap, Inc. | US | unknown |
3452 | InstallUtil.exe | 216.146.43.70:80 | checkip.dyndns.org | Dynamic Network Services, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkip.dyndns.org |
| shared |
smtp.privateemail.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.dyndns. Domain |
1080 | svchost.exe | Misc activity | AV INFO Query to checkip.dyndns. Domain |
3452 | InstallUtil.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup - checkip.dyndns.org |
3452 | InstallUtil.exe | Potentially Bad Traffic | ET POLICY DynDNS CheckIp External IP Address Server Response |
3452 | InstallUtil.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |