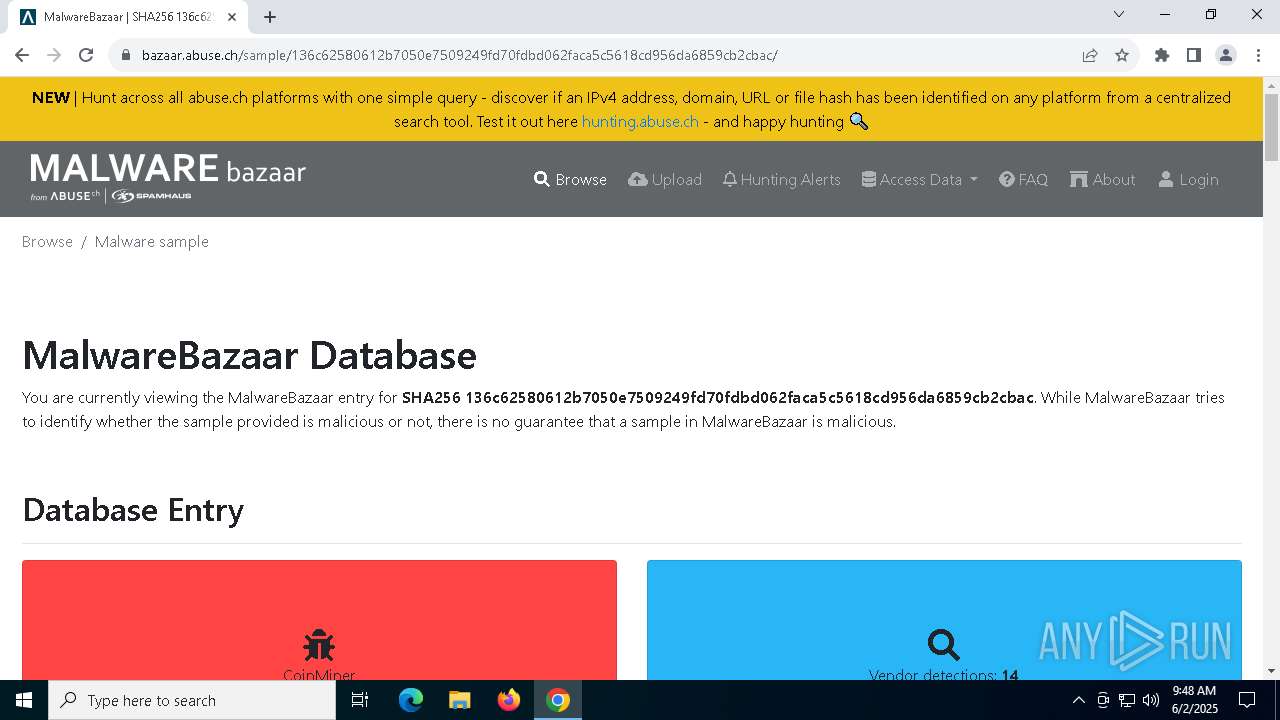
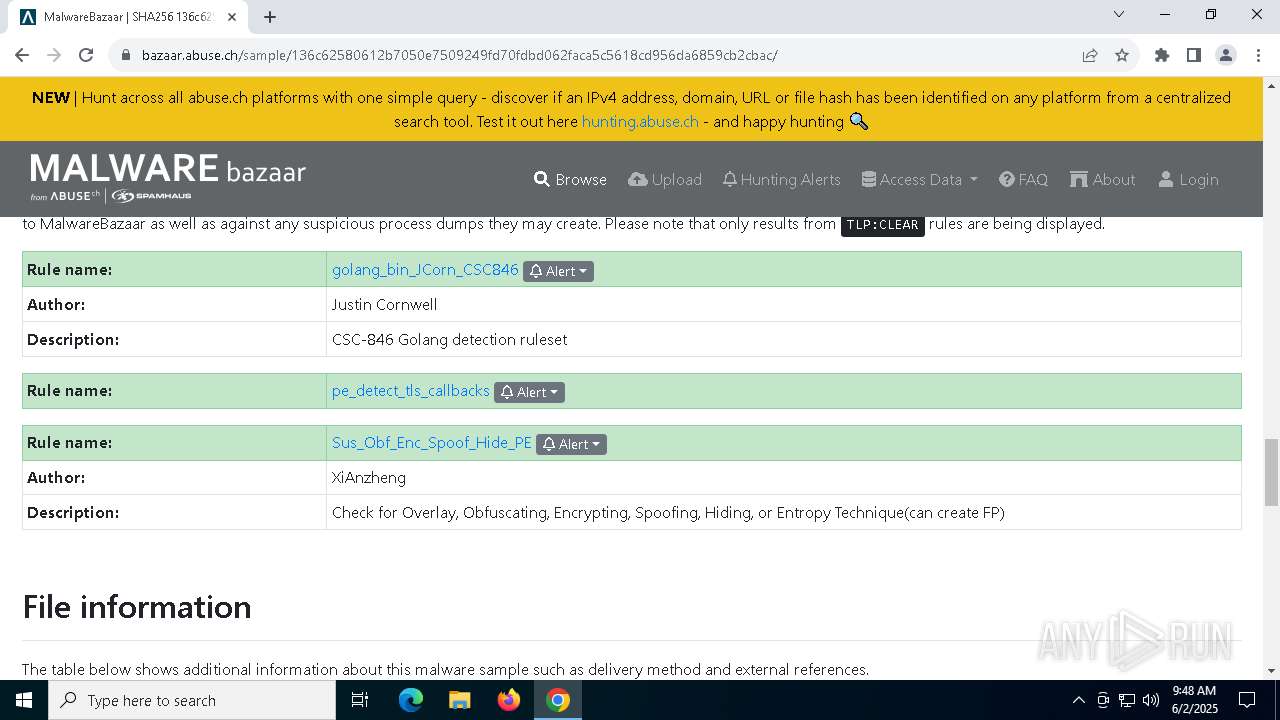
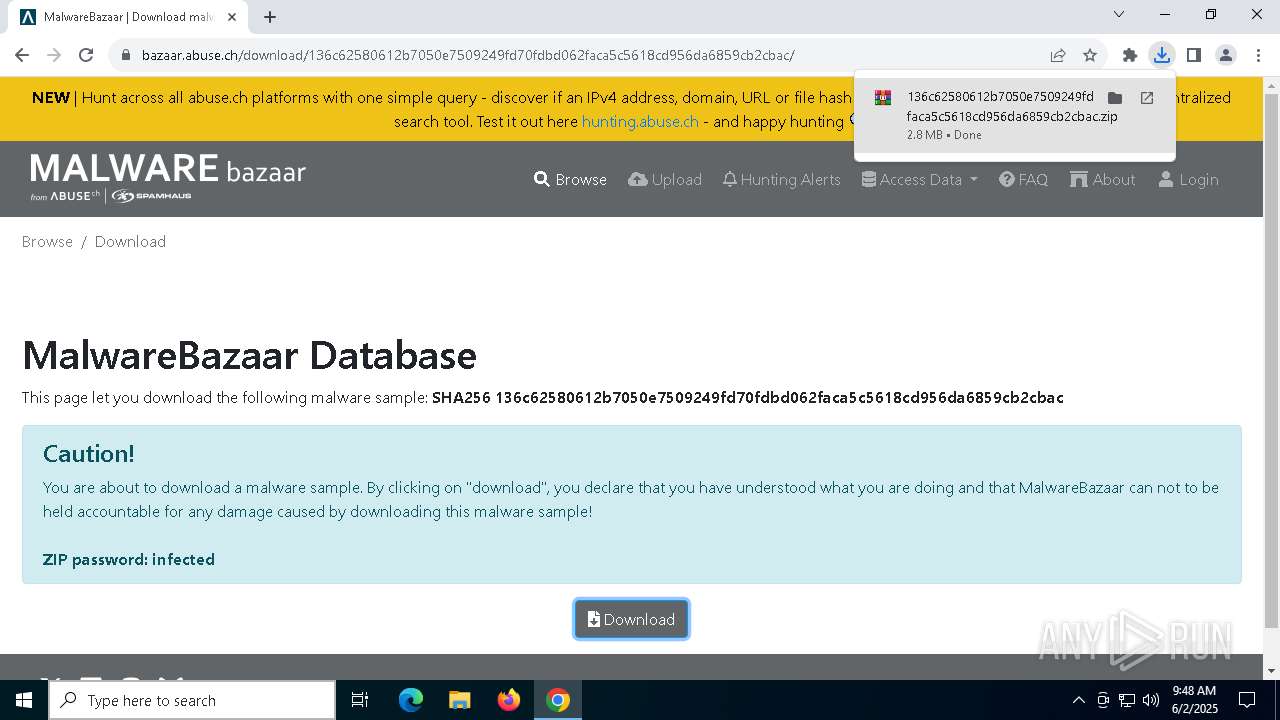
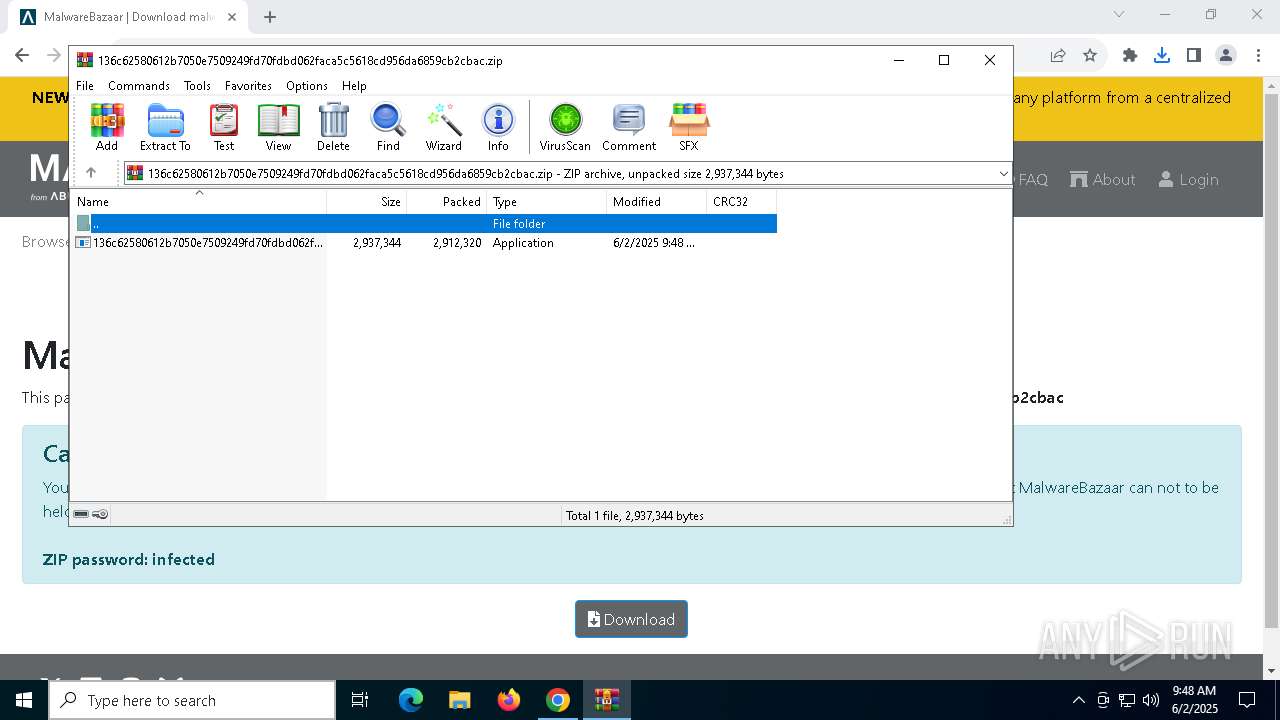
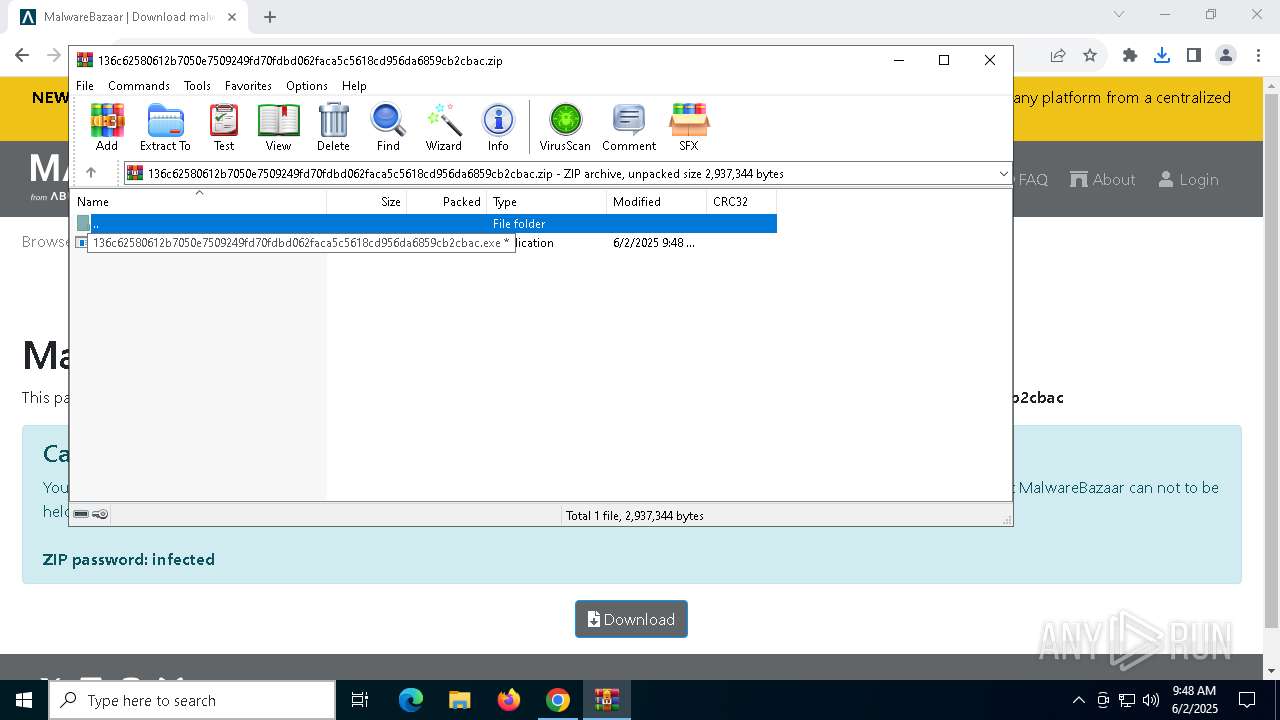
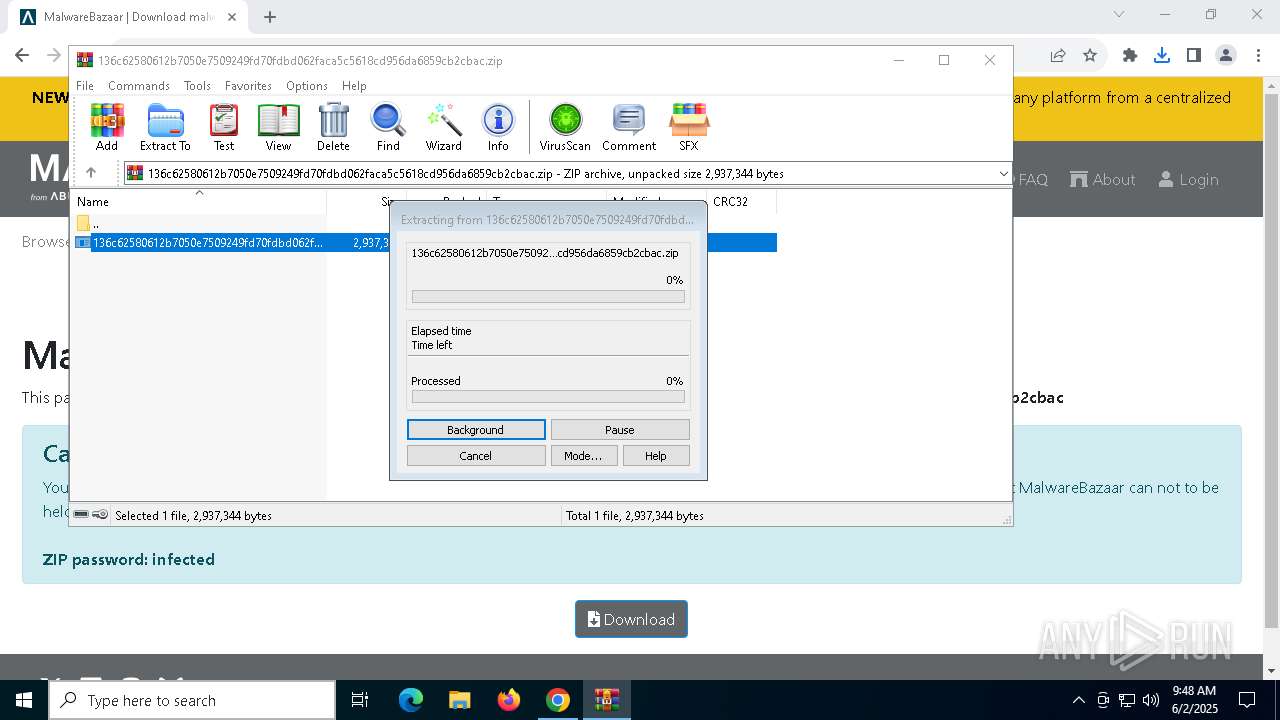
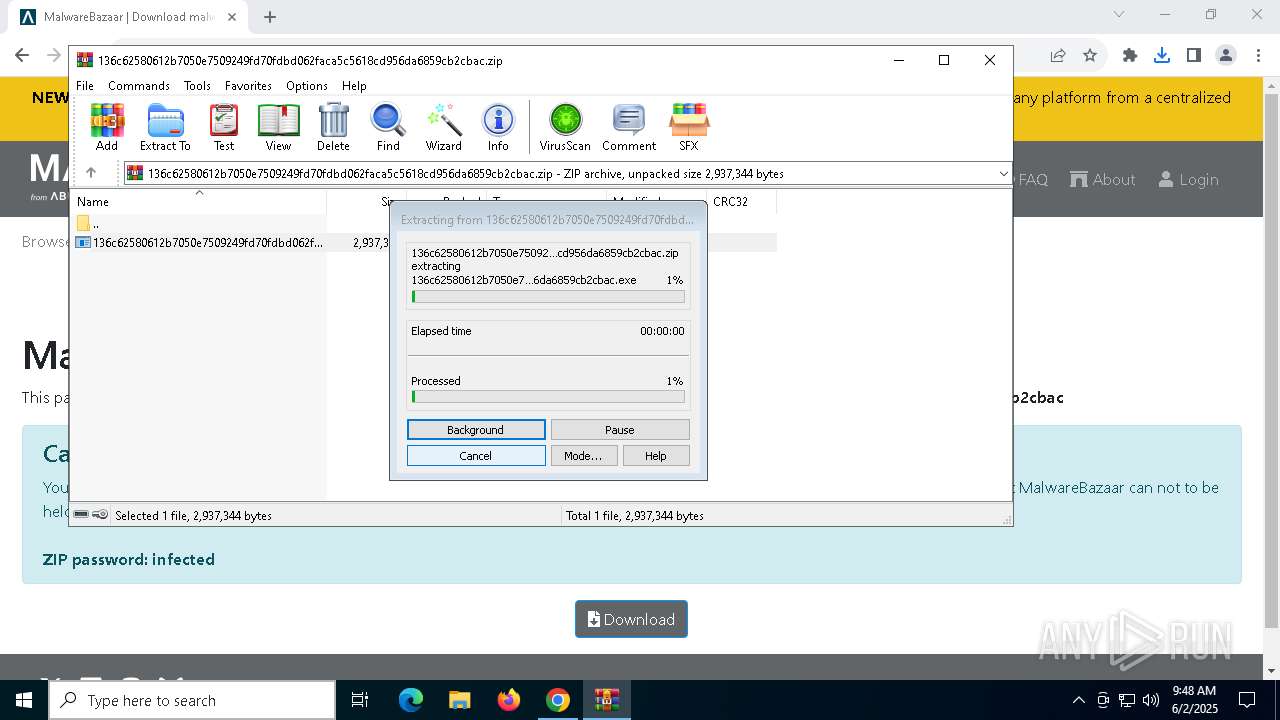
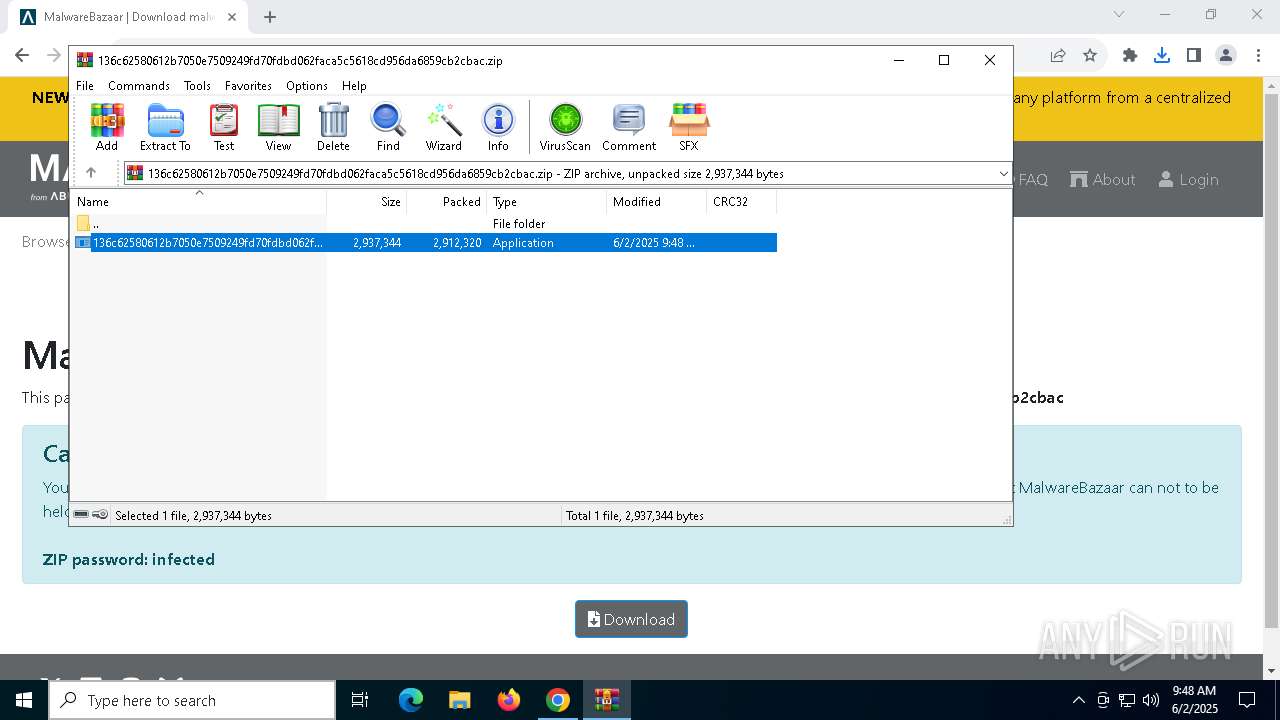
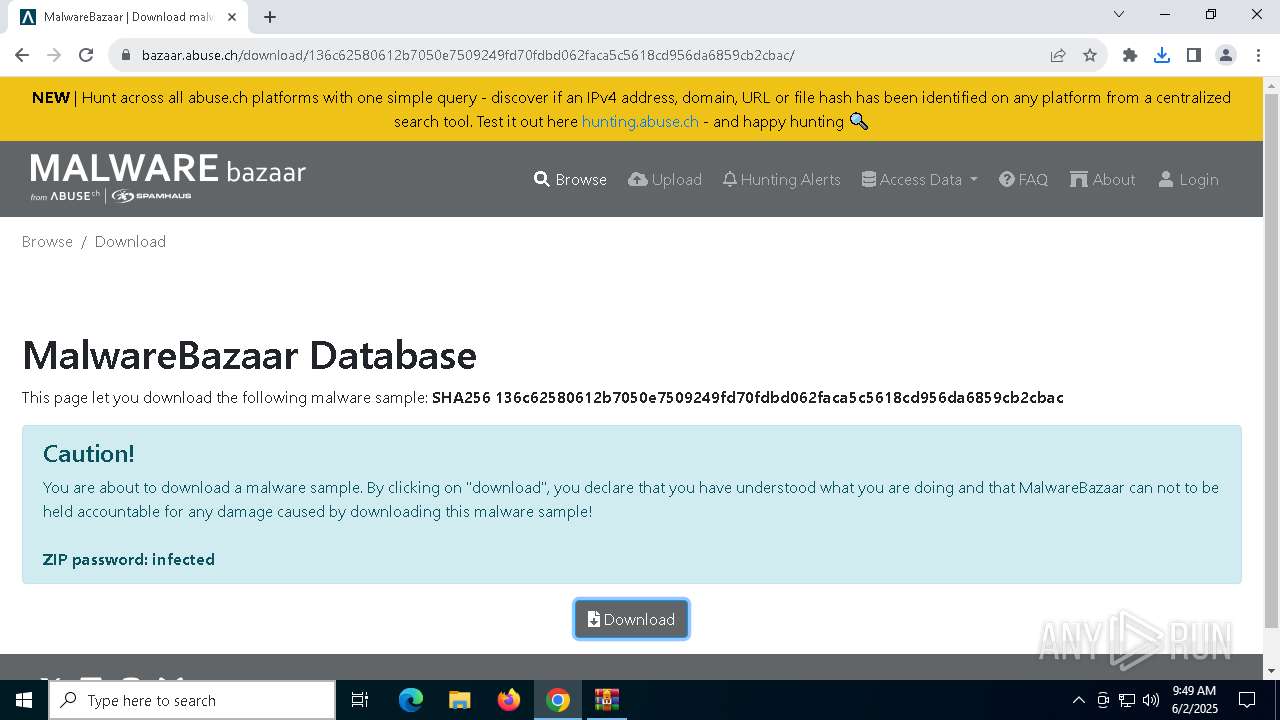
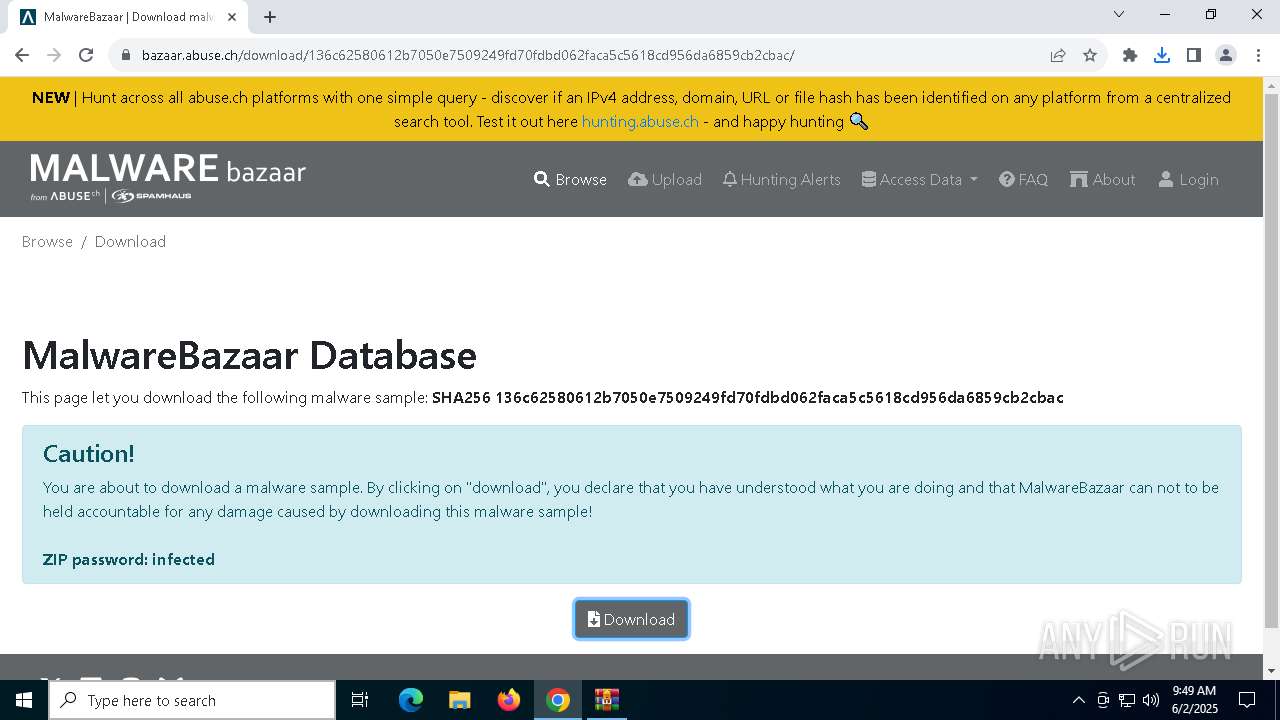
| URL: | https://bazaar.abuse.ch/sample/136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac/ |
| Full analysis: | https://app.any.run/tasks/6f3edd60-8912-4811-8112-1114fe7fff8a |
| Verdict: | Malicious activity |
| Analysis date: | June 02, 2025, 09:47:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6F25FCCDC3DF67686D34750F0BD4B241 |
| SHA1: | DC8E9C2C75AE720409F97F5CE7FE7C31FBA31198 |
| SHA256: | F8302A16EE0B355CFD1321155633A341A3C195B8603E28347FE943341FAA7762 |
| SSDEEP: | 3:N8N0uDWWdTPxc7dzUdblHS:23zTpgzUdbly |
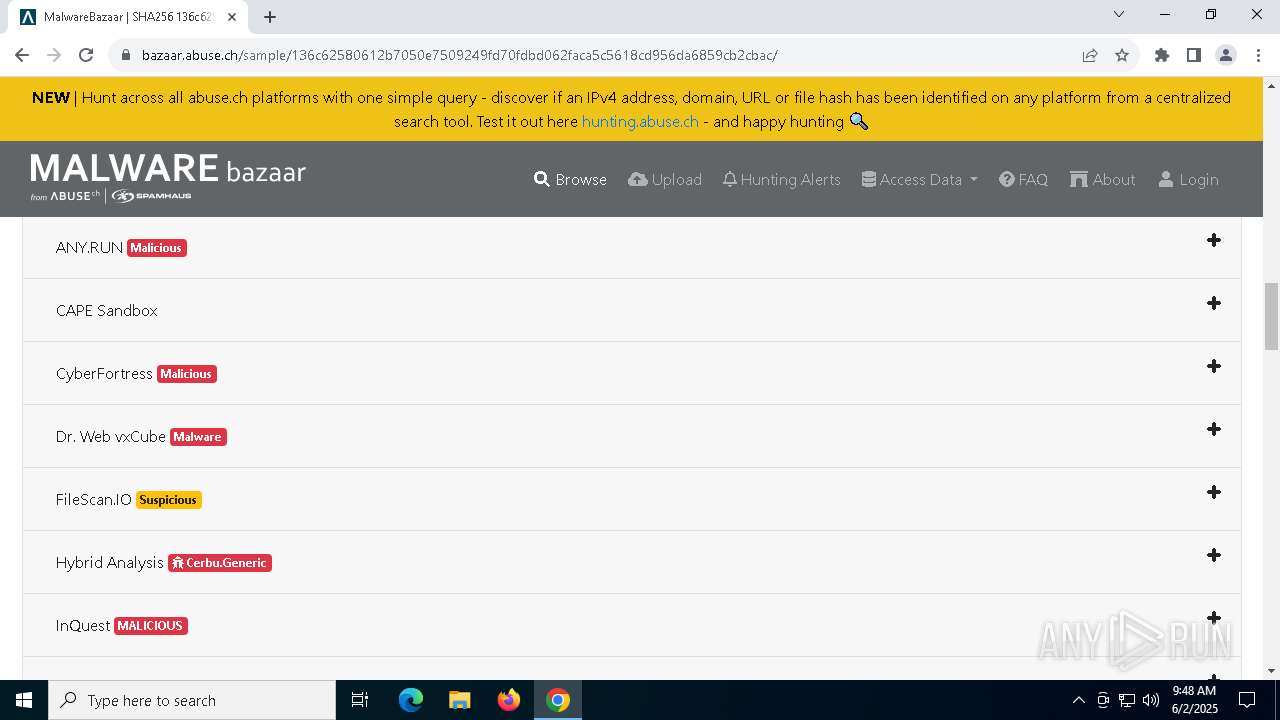
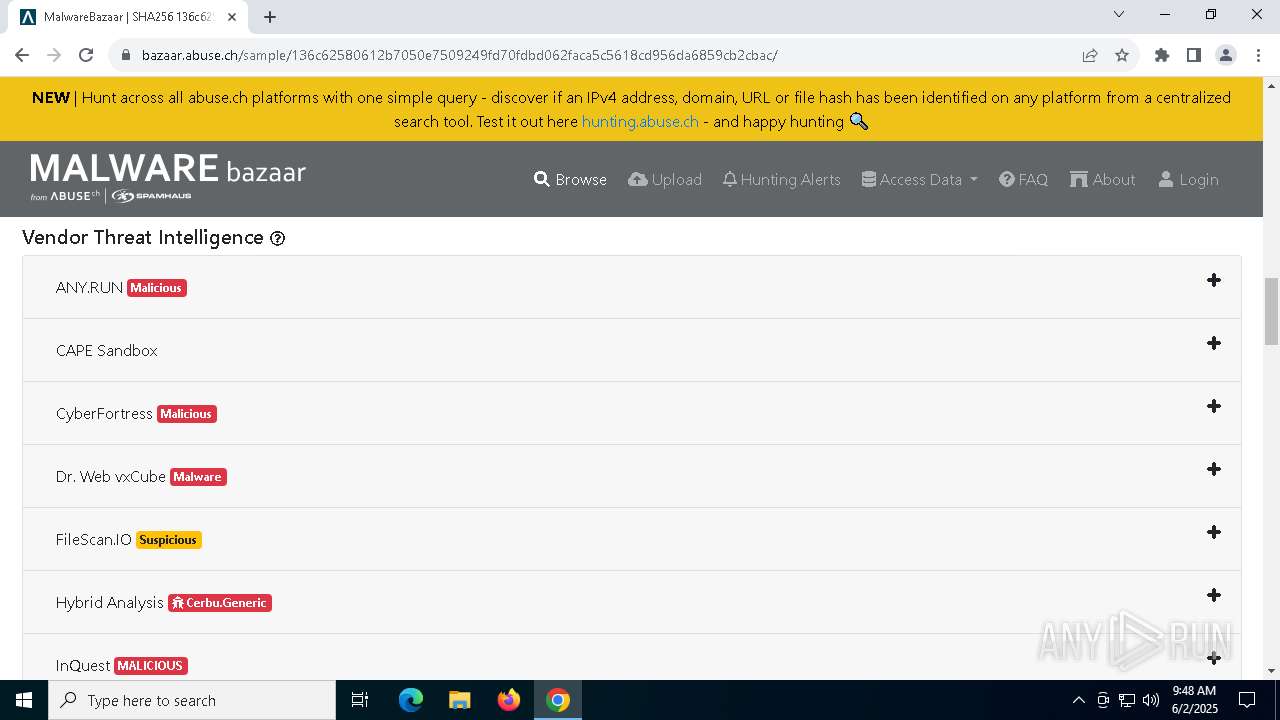
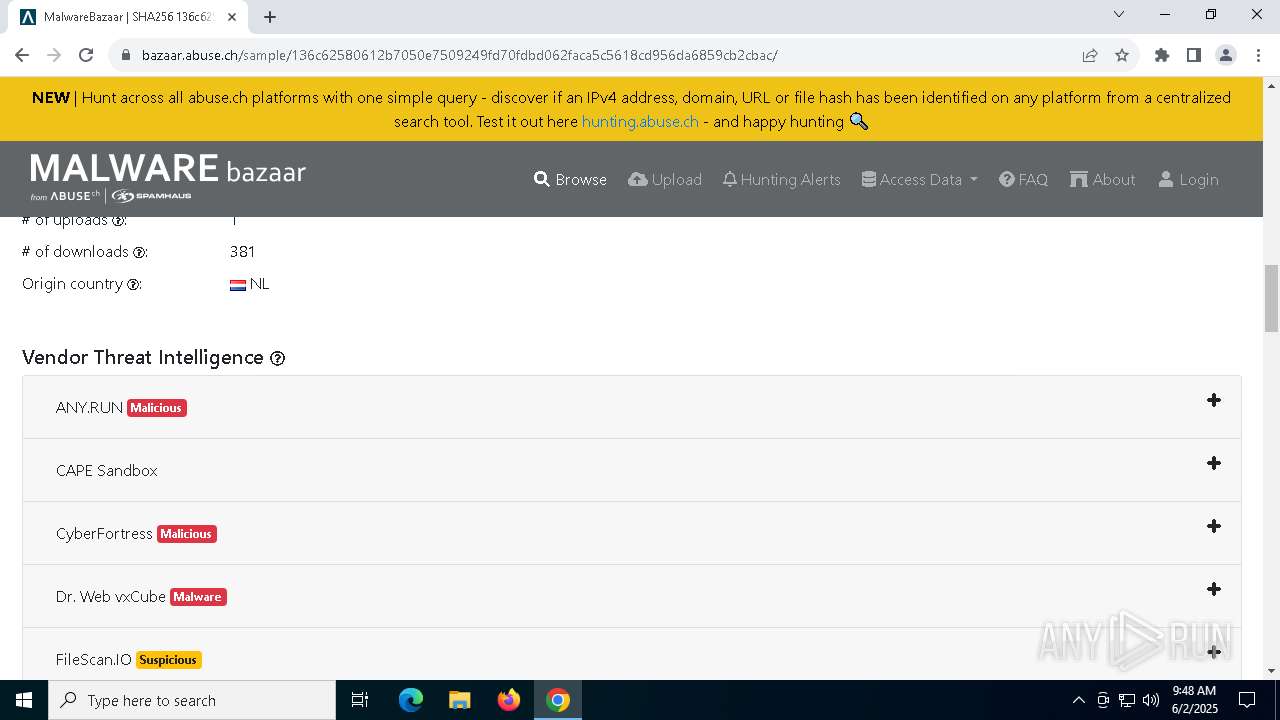
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 7276)
Changes Windows Defender settings
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
- WmiPrvSE.exe (PID: 3140)
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 4224)
- cmd.exe (PID: 1704)
Adds extension to the Windows Defender exclusion list
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
- WmiPrvSE.exe (PID: 3140)
Adds path to the Windows Defender exclusion list
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
- WmiPrvSE.exe (PID: 3140)
Changes the Windows auto-update feature
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
Deletes shadow copies
- cmd.exe (PID: 7824)
- cmd.exe (PID: 8068)
Uses Task Scheduler to run other applications
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
Starts CMD.EXE for self-deleting
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
Vulnerable driver has been detected
- WmiPrvSE.exe (PID: 3140)
SUSPICIOUS
Process drops legitimate windows executable
- chrome.exe (PID: 3364)
- WinRAR.exe (PID: 7936)
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7936)
Starts a Microsoft application from unusual location
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 2284)
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
Starts CMD.EXE for commands execution
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 2284)
- powershell.exe (PID: 7276)
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
- WmiPrvSE.exe (PID: 3140)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 6632)
- net.exe (PID: 5260)
- cmd.exe (PID: 404)
- net.exe (PID: 3272)
- cmd.exe (PID: 5640)
- net.exe (PID: 7844)
Starts process via Powershell
- powershell.exe (PID: 7276)
Starts POWERSHELL.EXE for commands execution
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 2284)
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
- WmiPrvSE.exe (PID: 3140)
Stops a currently running service
- sc.exe (PID: 5132)
- sc.exe (PID: 5736)
- sc.exe (PID: 4336)
- sc.exe (PID: 7700)
- sc.exe (PID: 7292)
- sc.exe (PID: 7220)
- sc.exe (PID: 1300)
- sc.exe (PID: 5236)
- sc.exe (PID: 7744)
- sc.exe (PID: 5304)
Windows service management via SC.EXE
- sc.exe (PID: 7680)
- sc.exe (PID: 7084)
- sc.exe (PID: 8084)
- sc.exe (PID: 7836)
- sc.exe (PID: 7904)
- sc.exe (PID: 232)
- sc.exe (PID: 7396)
- sc.exe (PID: 1120)
- sc.exe (PID: 5392)
- sc.exe (PID: 7272)
The executable file from the user directory is run by the CMD process
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
Starts SC.EXE for service management
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
- WmiPrvSE.exe (PID: 3140)
Script adds exclusion path to Windows Defender
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
- WmiPrvSE.exe (PID: 3140)
Script adds exclusion extension to Windows Defender
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
- WmiPrvSE.exe (PID: 3140)
Process uninstalls Windows update
- wusa.exe (PID: 7292)
- wusa.exe (PID: 7944)
The process deletes folder without confirmation
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
- WmiPrvSE.exe (PID: 3140)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 2984)
- cmd.exe (PID: 772)
- cmd.exe (PID: 7876)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 1312)
- cmd.exe (PID: 7700)
- cmd.exe (PID: 3036)
- cmd.exe (PID: 7728)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 8092)
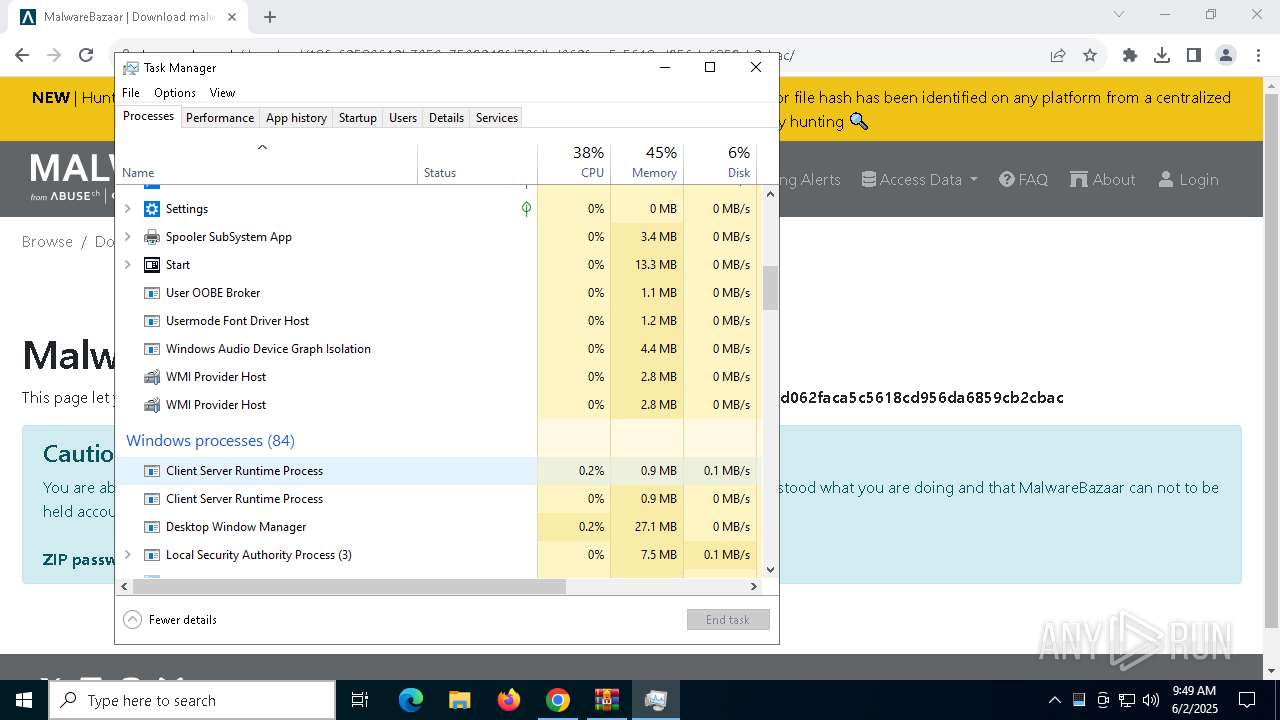
Executes as Windows Service
- VSSVC.exe (PID: 6324)
Executable content was dropped or overwritten
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
- WmiPrvSE.exe (PID: 3140)
Hides command output
- cmd.exe (PID: 2136)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2136)
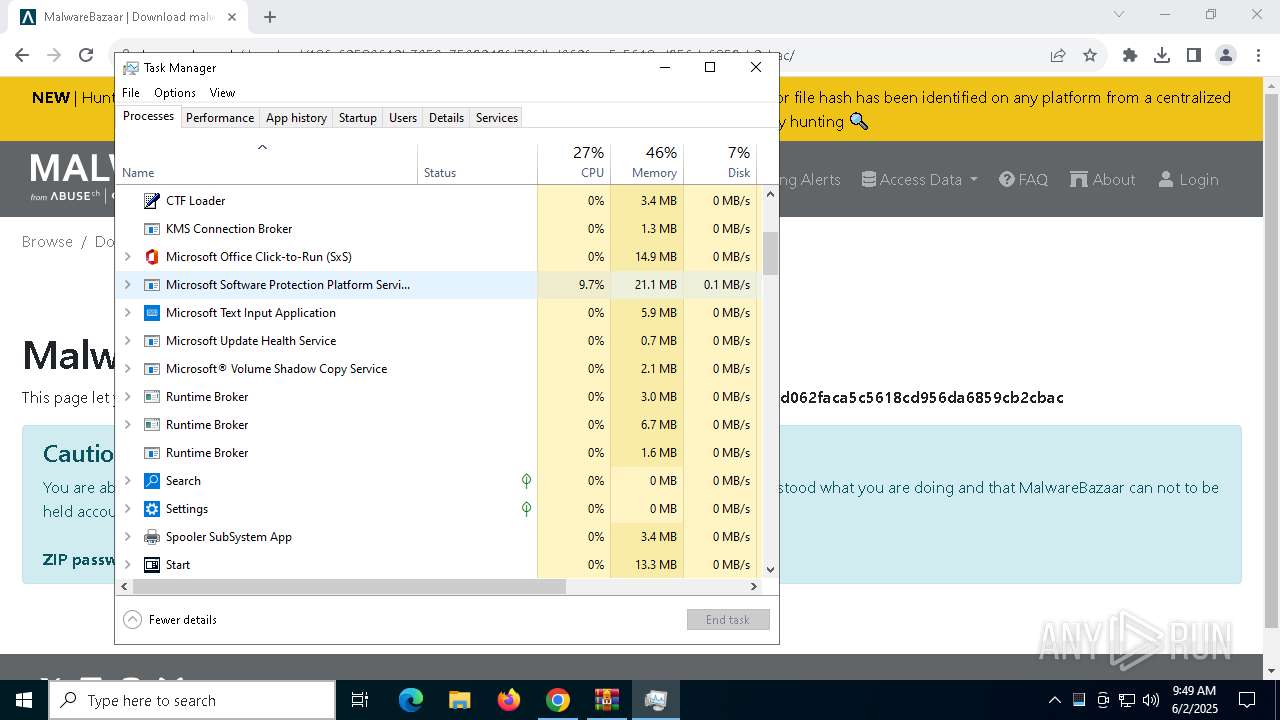
The process executes via Task Scheduler
- WmiPrvSE.exe (PID: 3140)
Drops a system driver (possible attempt to evade defenses)
- WmiPrvSE.exe (PID: 3140)
INFO
Reads the software policy settings
- slui.exe (PID: 7224)
The sample compiled with english language support
- WinRAR.exe (PID: 7936)
- chrome.exe (PID: 3364)
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
- chrome.exe (PID: 4884)
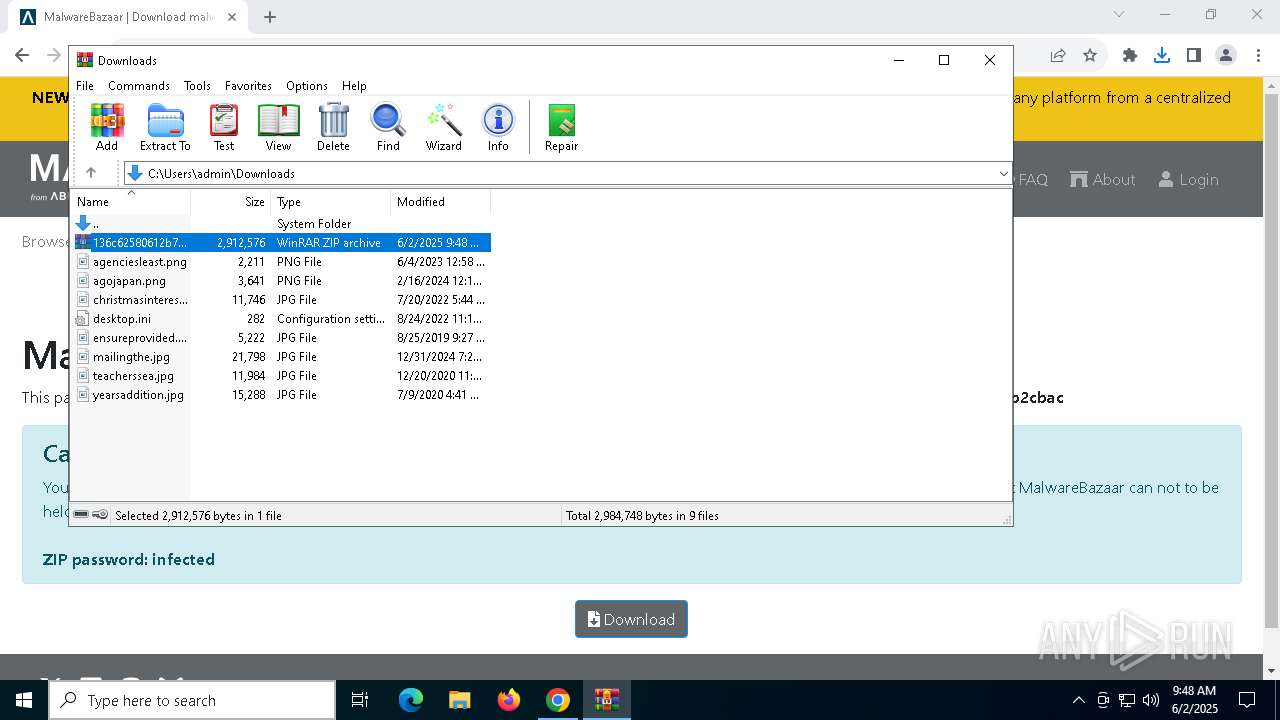
Launch of the file from Downloads directory
- chrome.exe (PID: 3364)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7936)
- chrome.exe (PID: 4884)
Reads Microsoft Office registry keys
- chrome.exe (PID: 3364)
Application launched itself
- chrome.exe (PID: 3364)
Checks supported languages
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 2284)
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
Reads the computer name
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 2284)
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7716)
- powershell.exe (PID: 2780)
- powershell.exe (PID: 7196)
- powershell.exe (PID: 6652)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7716)
- powershell.exe (PID: 7196)
- powershell.exe (PID: 2780)
- powershell.exe (PID: 6652)
Creates files in the program directory
- 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe (PID: 3168)
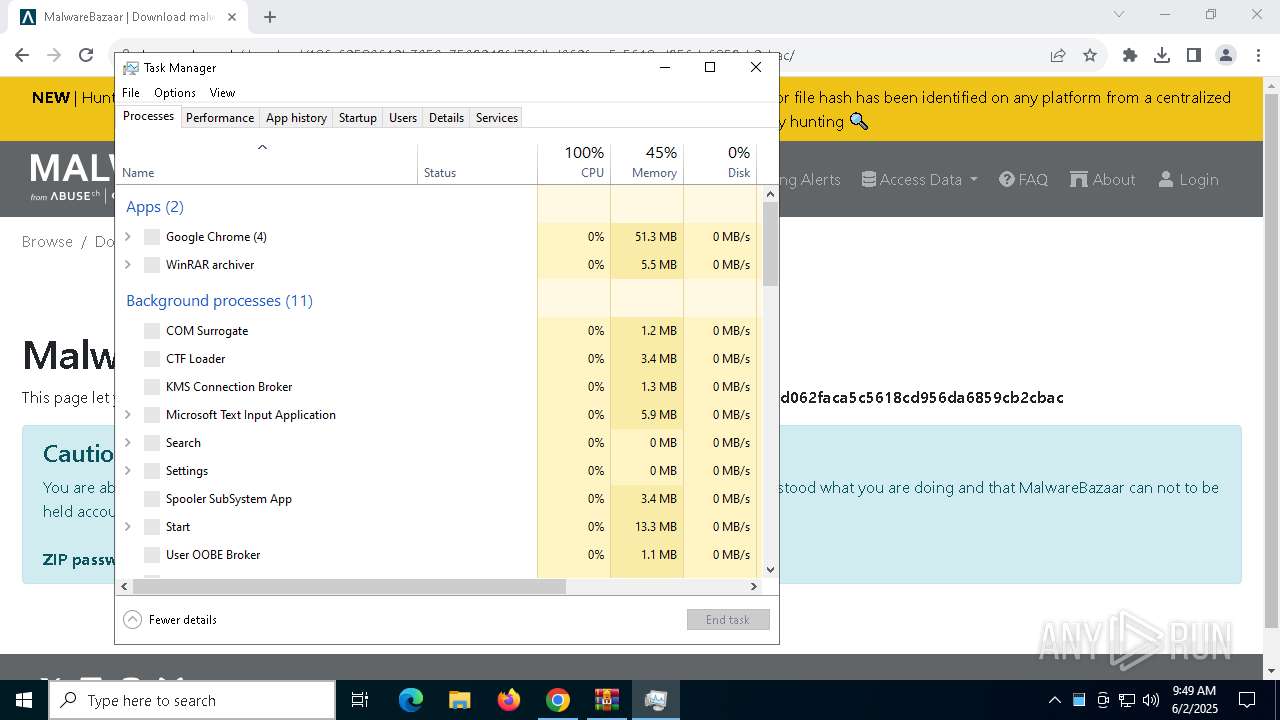
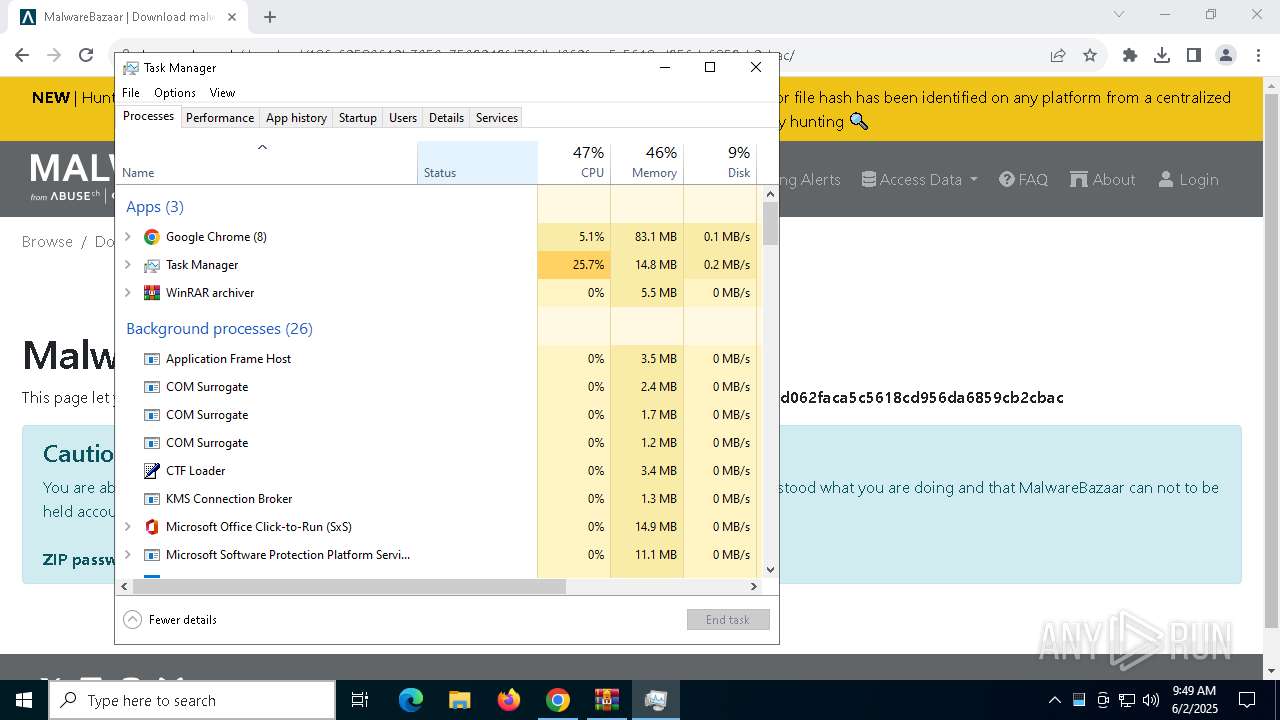
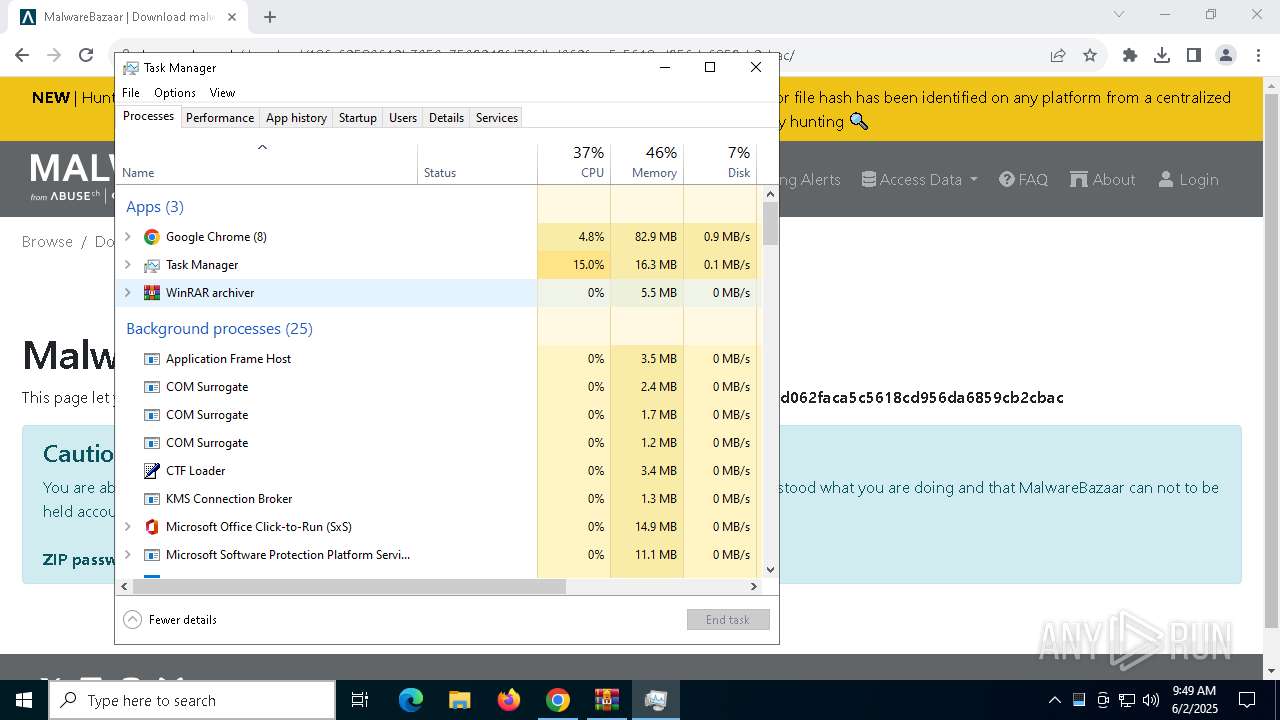
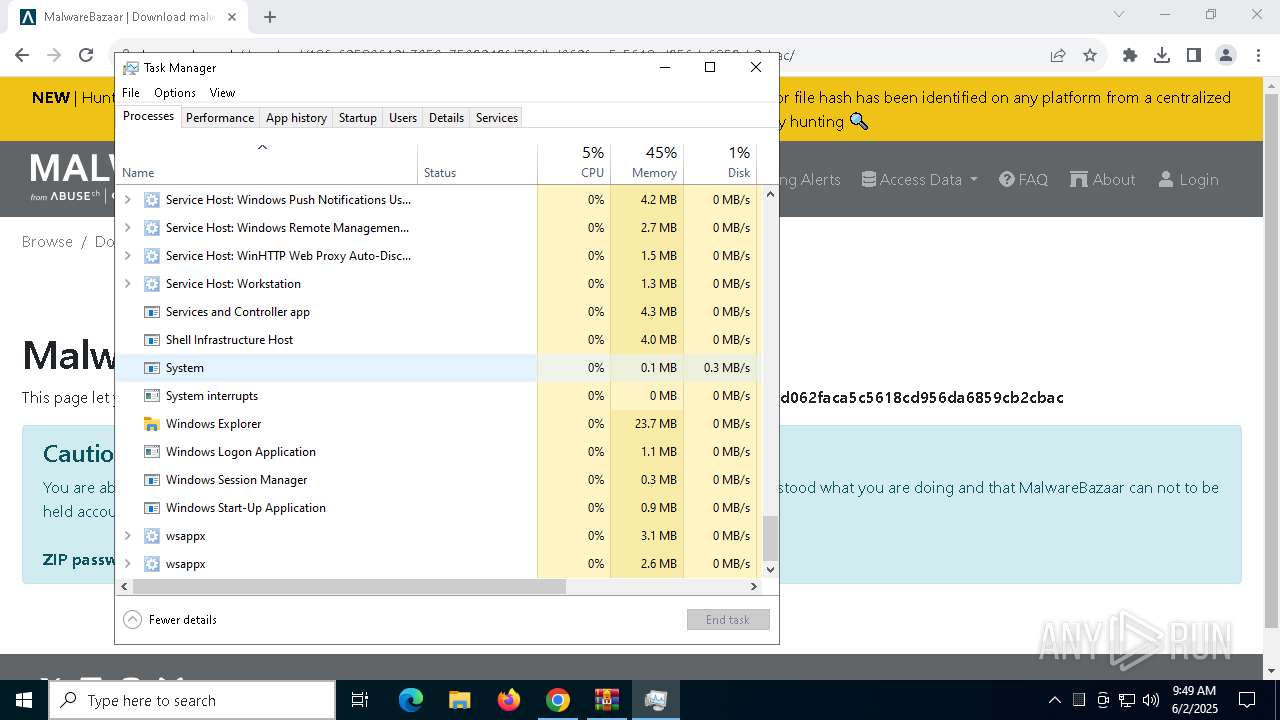
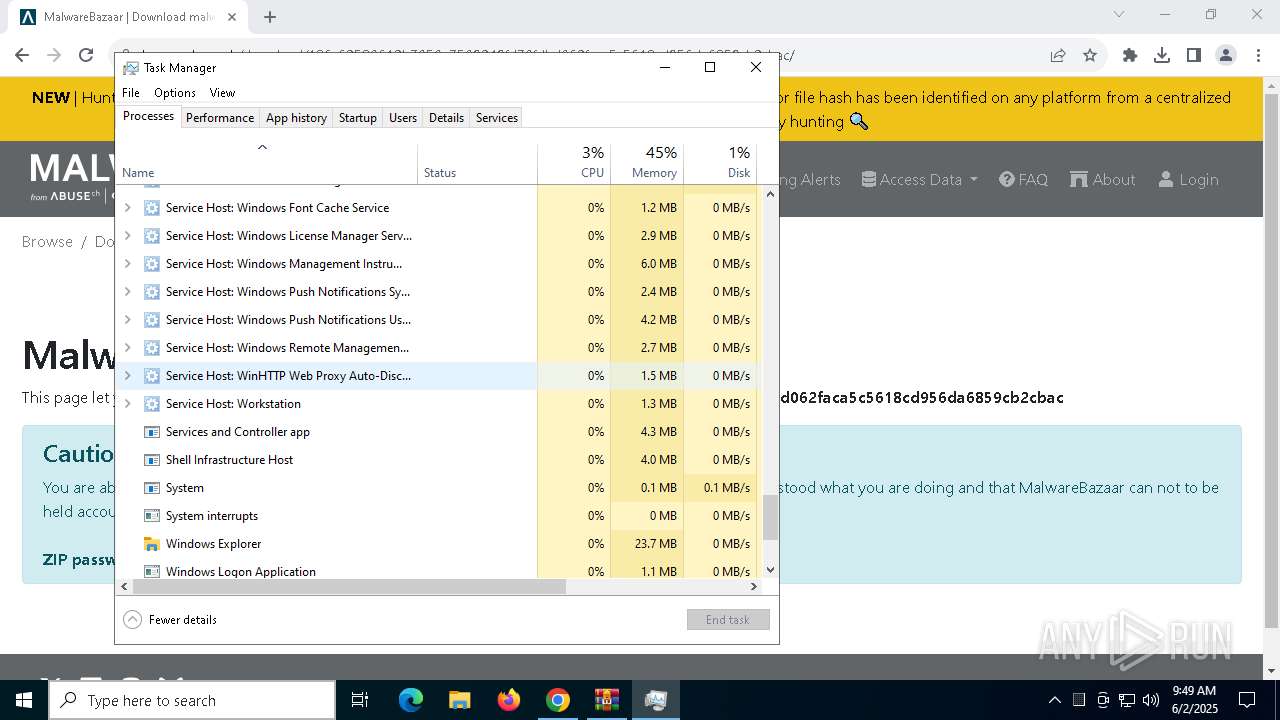
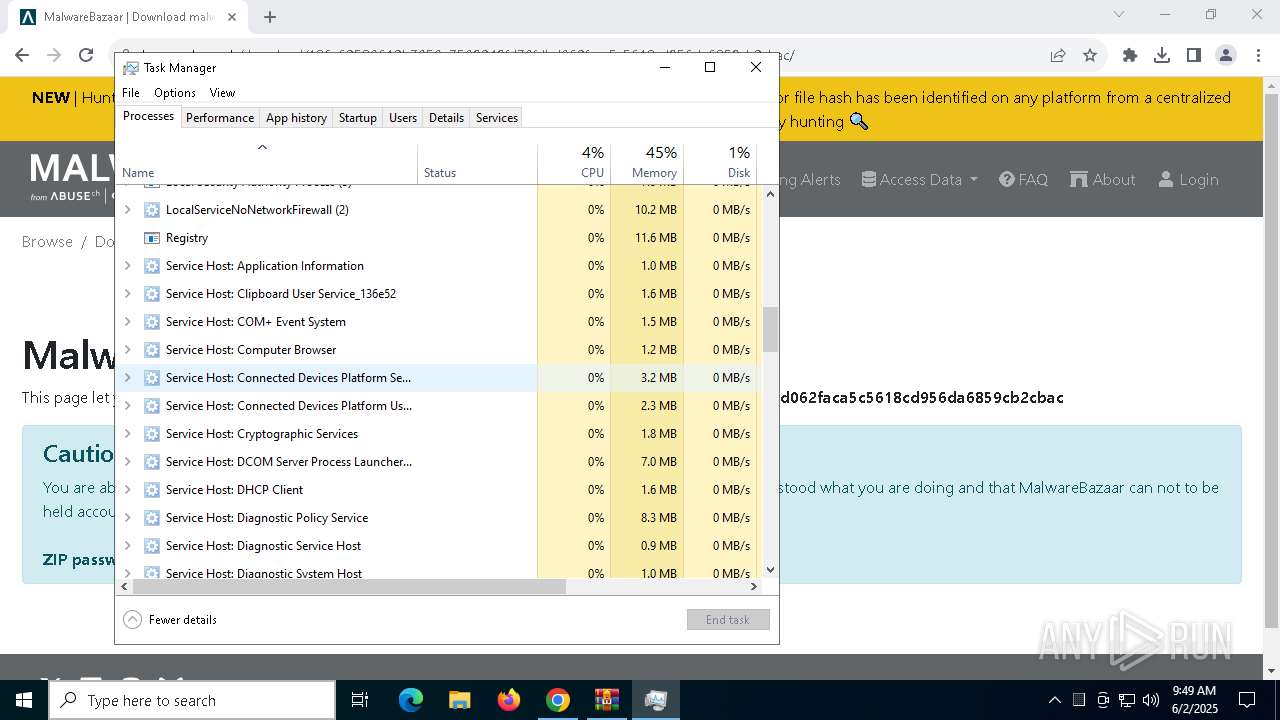
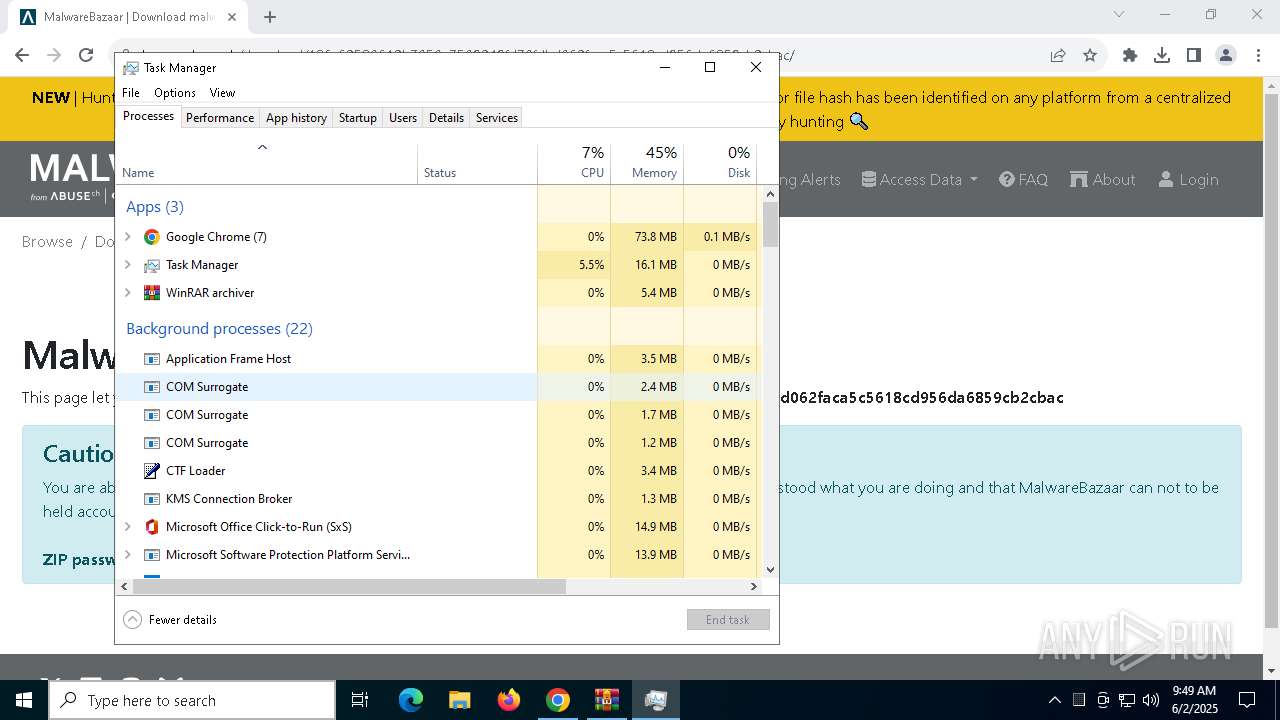
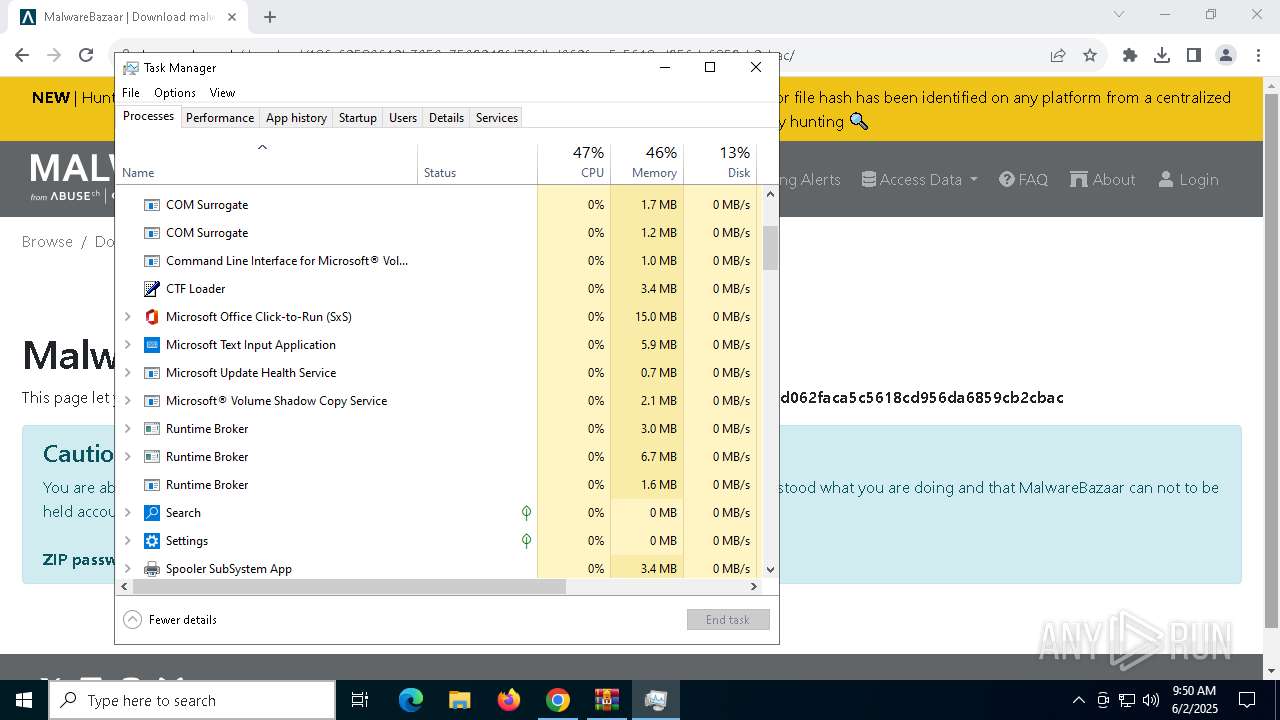
Manual execution by a user
- Taskmgr.exe (PID: 7692)
- Taskmgr.exe (PID: 5512)
The sample compiled with japanese language support
- WmiPrvSE.exe (PID: 3140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
290
Monitored processes
158
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | sc.exe config wuauserv start= disabled | C:\Windows\System32\sc.exe | — | WmiPrvSE.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 404 | cmd.exe /C net session | C:\Windows\System32\cmd.exe | — | 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 704 | cmd.exe /C rmdir /S /Q "%SystemDrive%\\inetpub" | C:\Windows\System32\cmd.exe | — | 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 772 | cmd.exe /c powercfg /x -standby-timeout-dc 0 | C:\Windows\System32\cmd.exe | — | 136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | powercfg /setactive 8c5e7fda-e8bf-4a96-9a85-a6e23a8c635c | C:\Windows\System32\powercfg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1120 | sc.exe config bits start= disabled | C:\Windows\System32\sc.exe | — | WmiPrvSE.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5676 --field-trial-handle=1900,i,3433615550500783206,9562095149763147551,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
61 136
Read events
61 067
Write events
61
Delete events
8
Modification events
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7456) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000008353967EA3D3DB01 | |||
| (PID) Process: | (7936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\136c62580612b7050e7509249fd70fdbd062faca5c5618cd956da6859cb2cbac.zip | |||
Executable files
15
Suspicious files
417
Text files
42
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF11fc7e.TMP | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF11fc8d.TMP | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF11fcac.TMP | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF11fc9d.TMP | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF11fcbc.TMP | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
57
DNS requests
59
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1088 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1088 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2908 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/hcdobhqe6gujxetn3rwydp3v3a_20250522.762470205.14/obedbbhbpmojnkanicioggnmelmoomoc_20250522.762470205.14_all_ENUS500000_ajivmzppurzzshnykrvshhwuxa.crx3 | unknown | — | — | whitelisted |
2908 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/hcdobhqe6gujxetn3rwydp3v3a_20250522.762470205.14/obedbbhbpmojnkanicioggnmelmoomoc_20250522.762470205.14_all_ENUS500000_ajivmzppurzzshnykrvshhwuxa.crx3 | unknown | — | — | whitelisted |
2908 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/hcdobhqe6gujxetn3rwydp3v3a_20250522.762470205.14/obedbbhbpmojnkanicioggnmelmoomoc_20250522.762470205.14_all_ENUS500000_ajivmzppurzzshnykrvshhwuxa.crx3 | unknown | — | — | whitelisted |
2908 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/hcdobhqe6gujxetn3rwydp3v3a_20250522.762470205.14/obedbbhbpmojnkanicioggnmelmoomoc_20250522.762470205.14_all_ENUS500000_ajivmzppurzzshnykrvshhwuxa.crx3 | unknown | — | — | whitelisted |
2908 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/hcdobhqe6gujxetn3rwydp3v3a_20250522.762470205.14/obedbbhbpmojnkanicioggnmelmoomoc_20250522.762470205.14_all_ENUS500000_ajivmzppurzzshnykrvshhwuxa.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6488 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3364 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6072 | chrome.exe | 151.101.194.49:443 | bazaar.abuse.ch | FASTLY | US | whitelisted |
6072 | chrome.exe | 74.125.206.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
bazaar.abuse.ch |
| whitelisted |
accounts.google.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
js.hcaptcha.com |
| whitelisted |
newassets.hcaptcha.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6072 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6072 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6072 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
6072 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
6072 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6072 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |