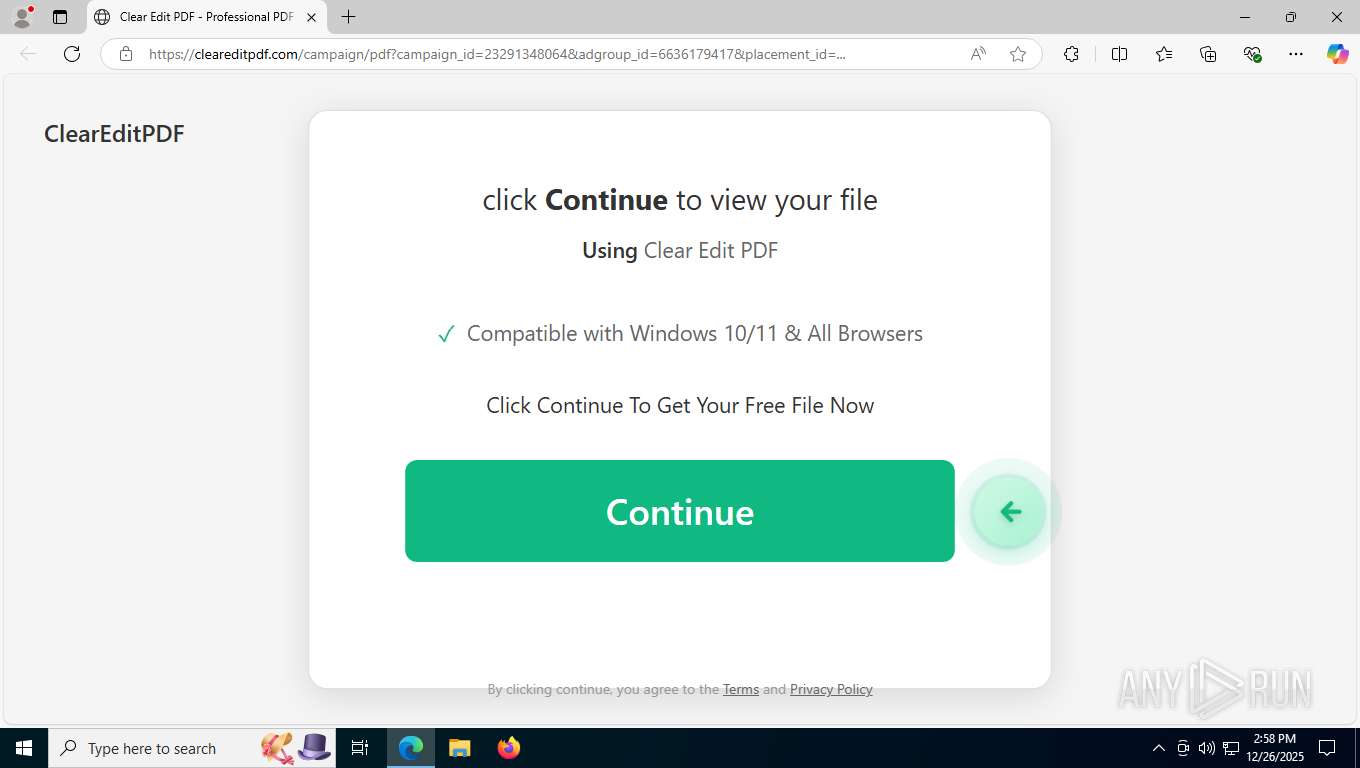
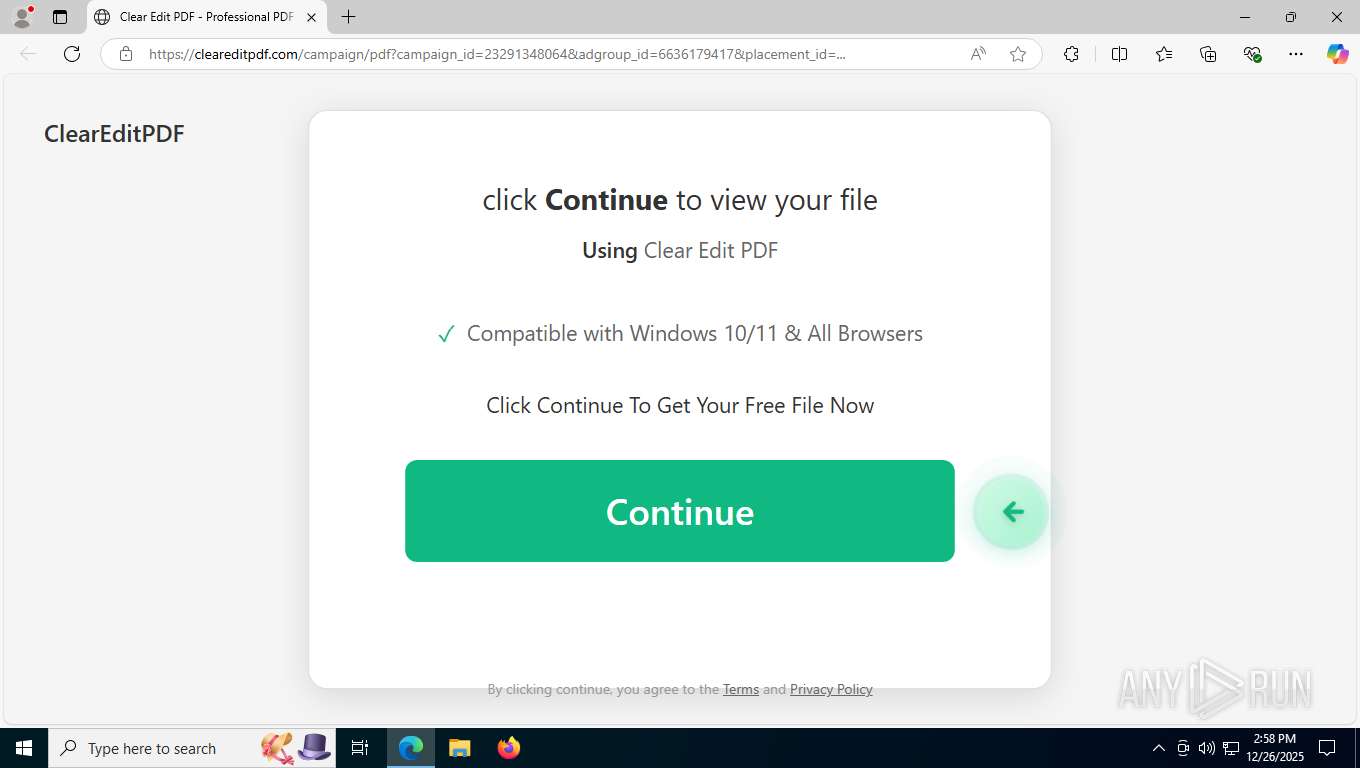
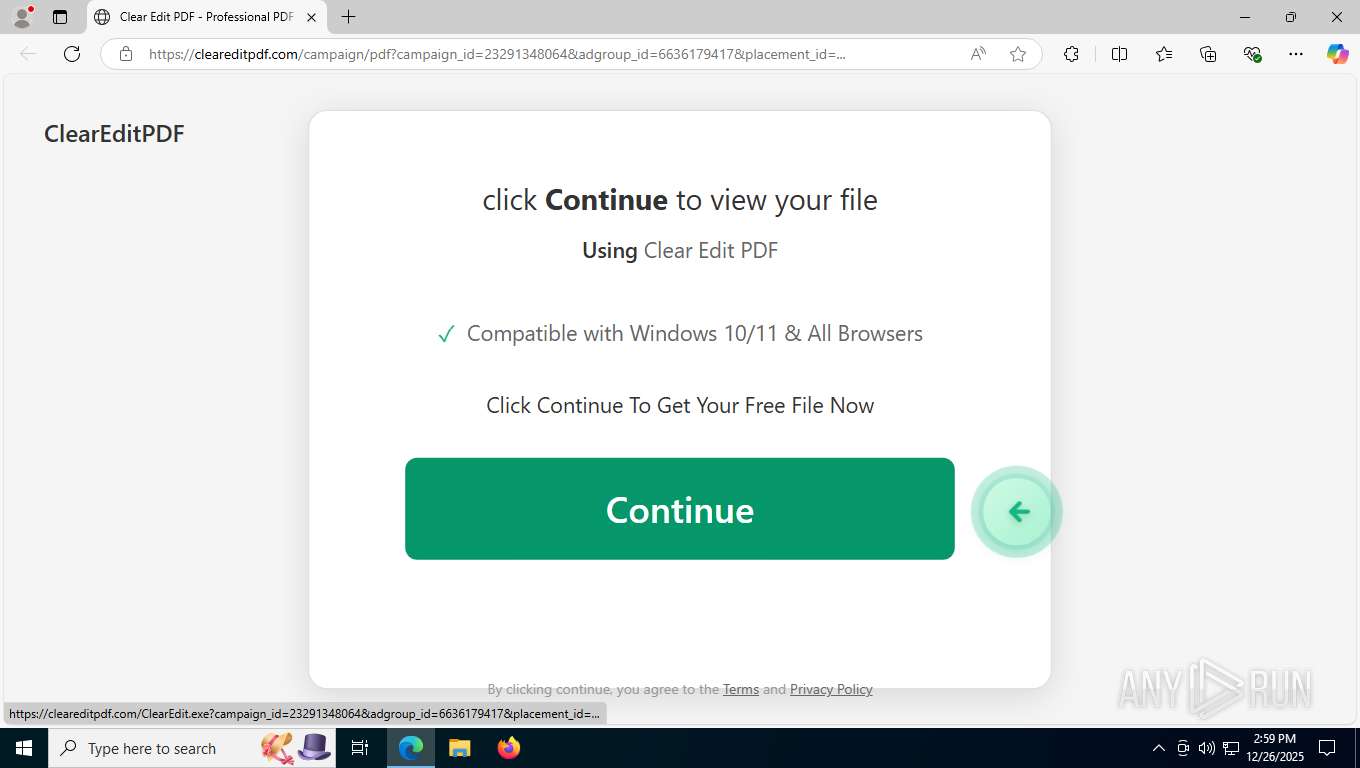
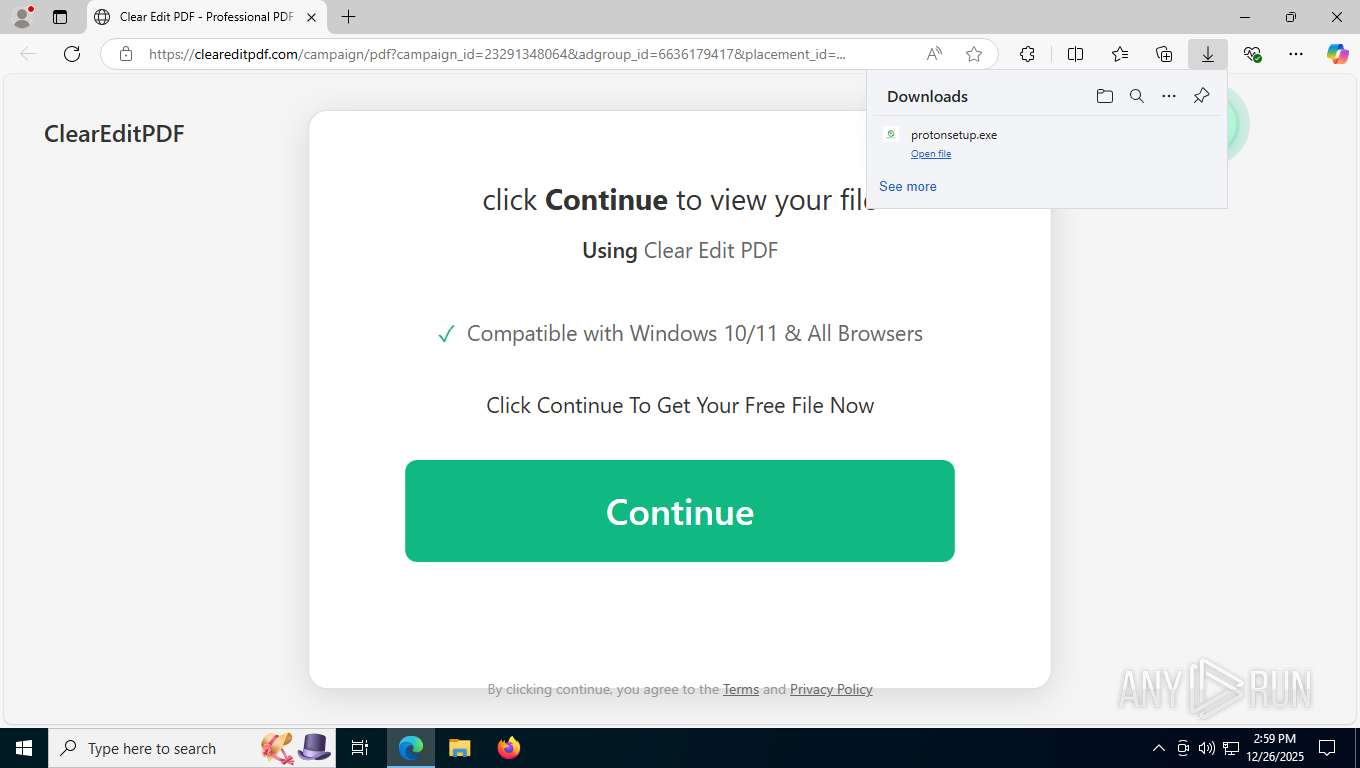
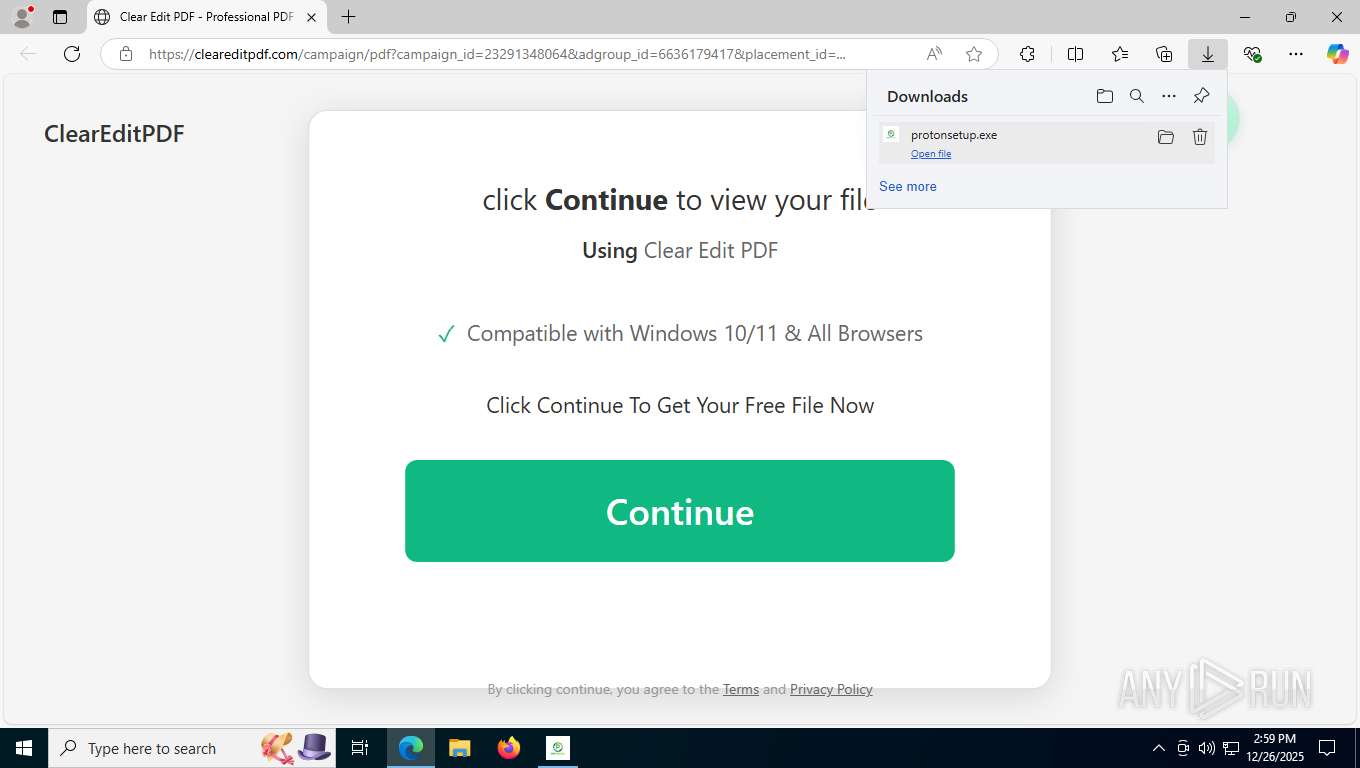
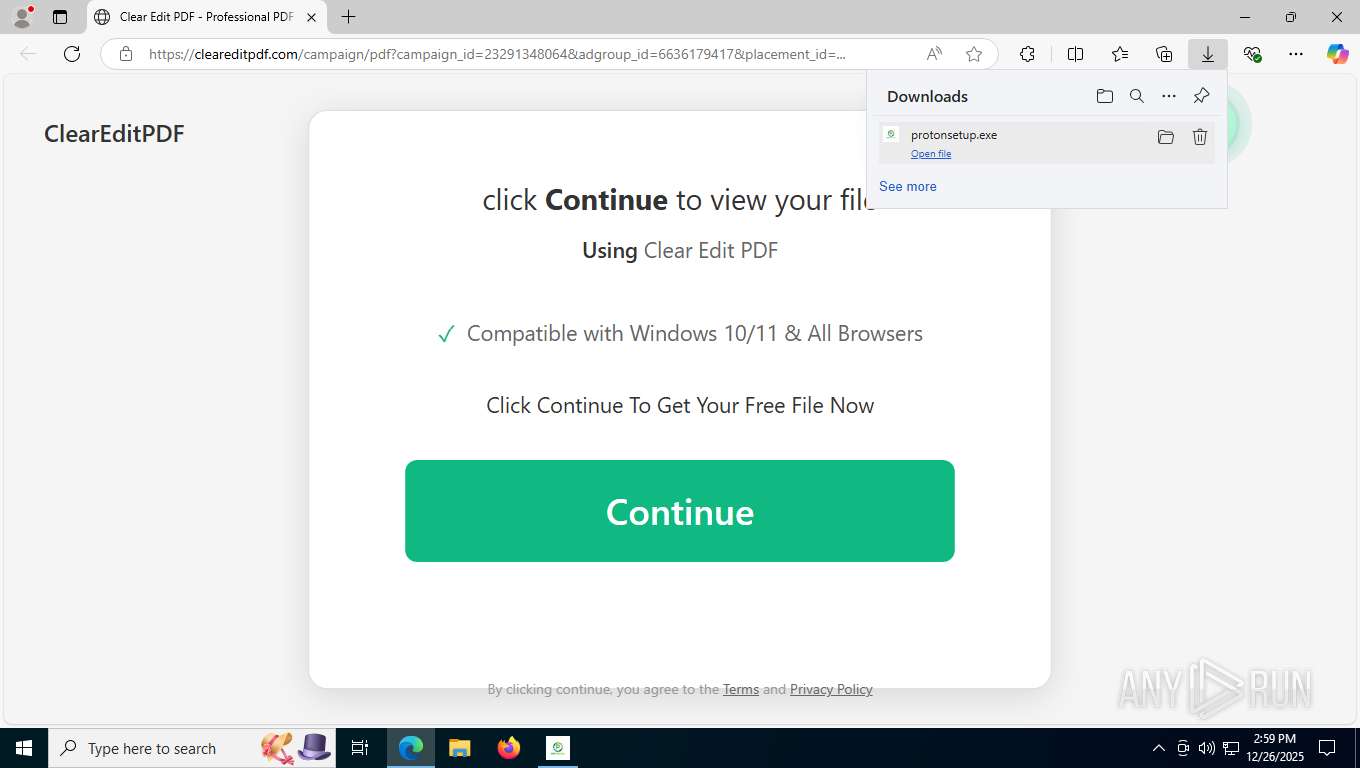
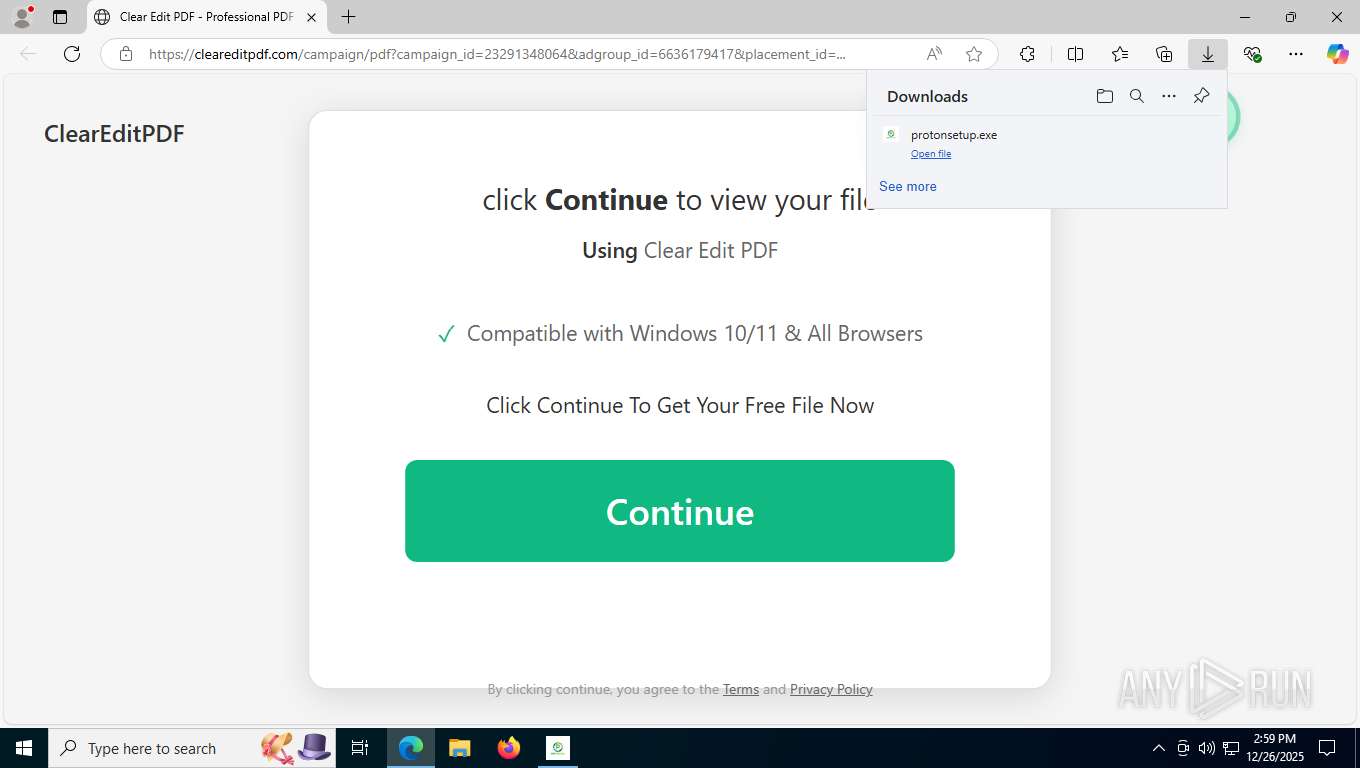
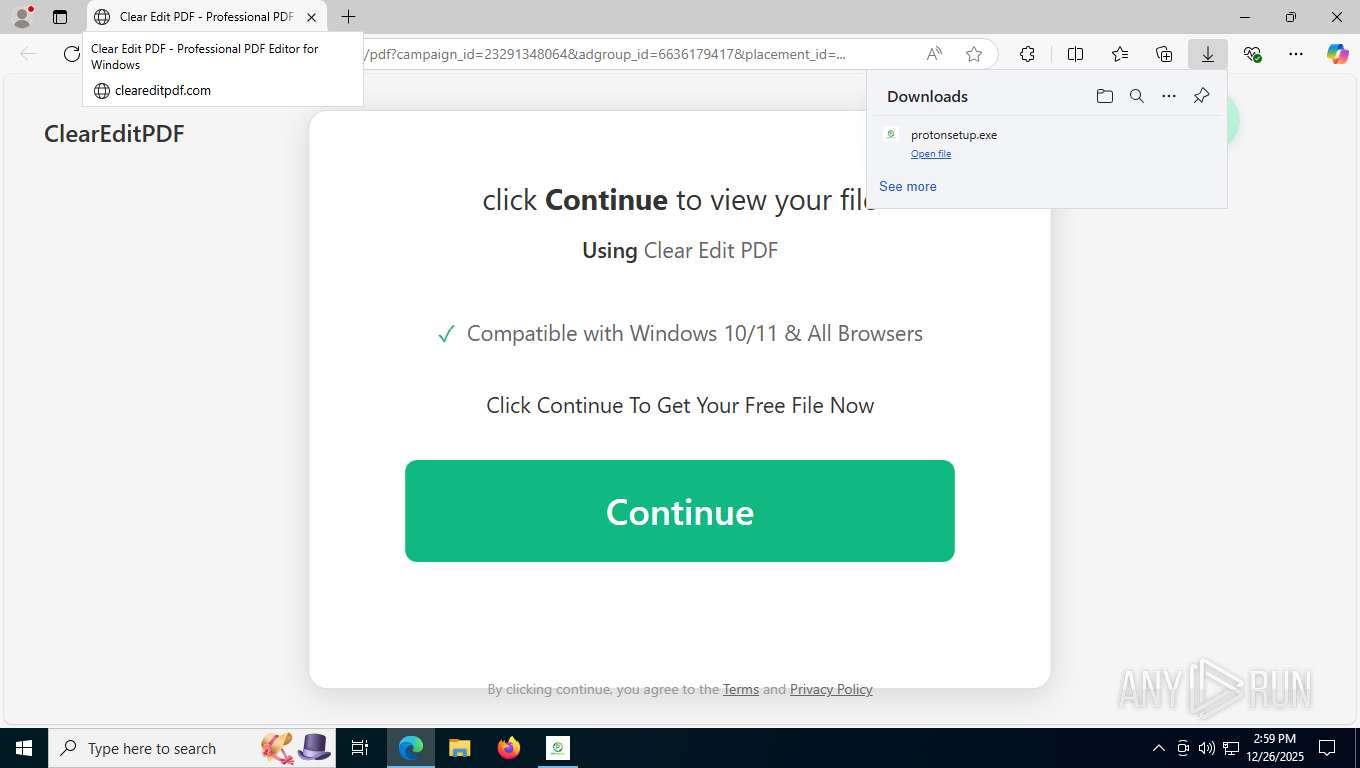
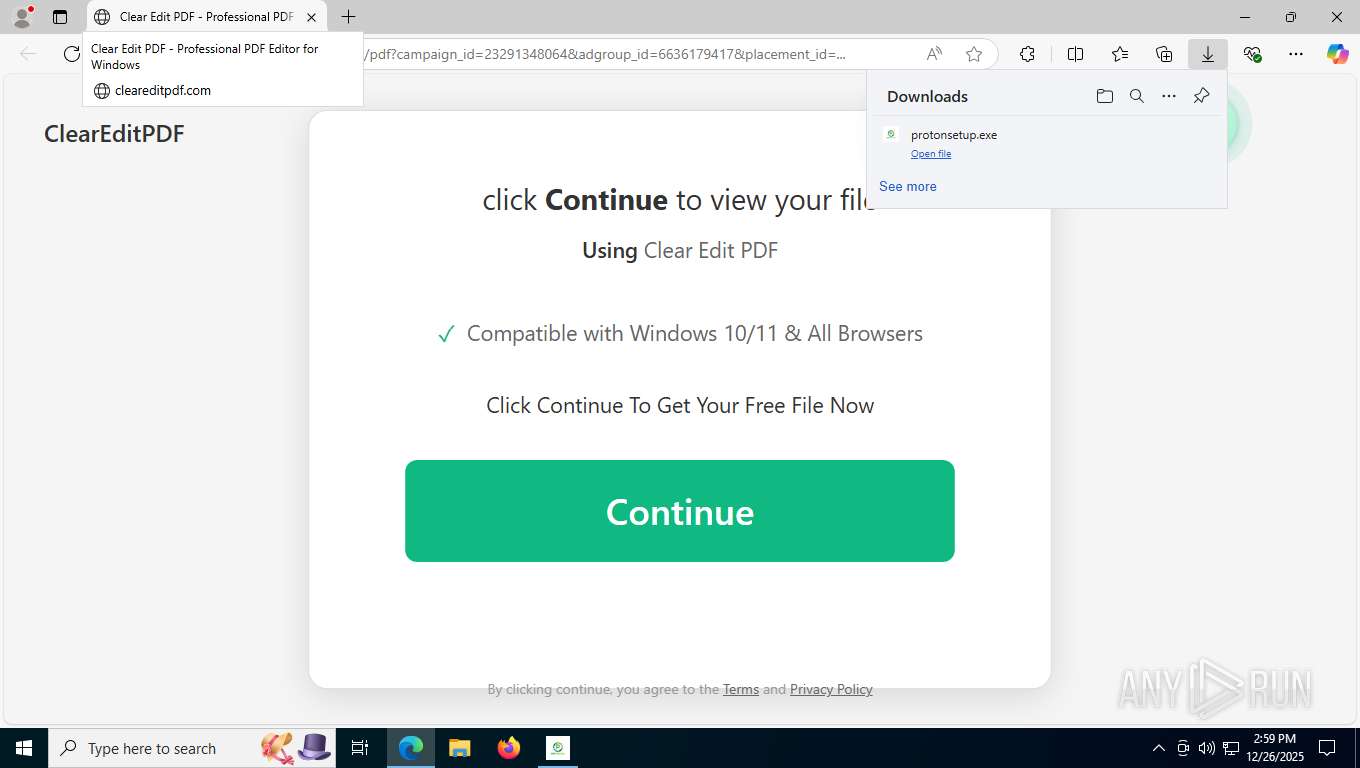
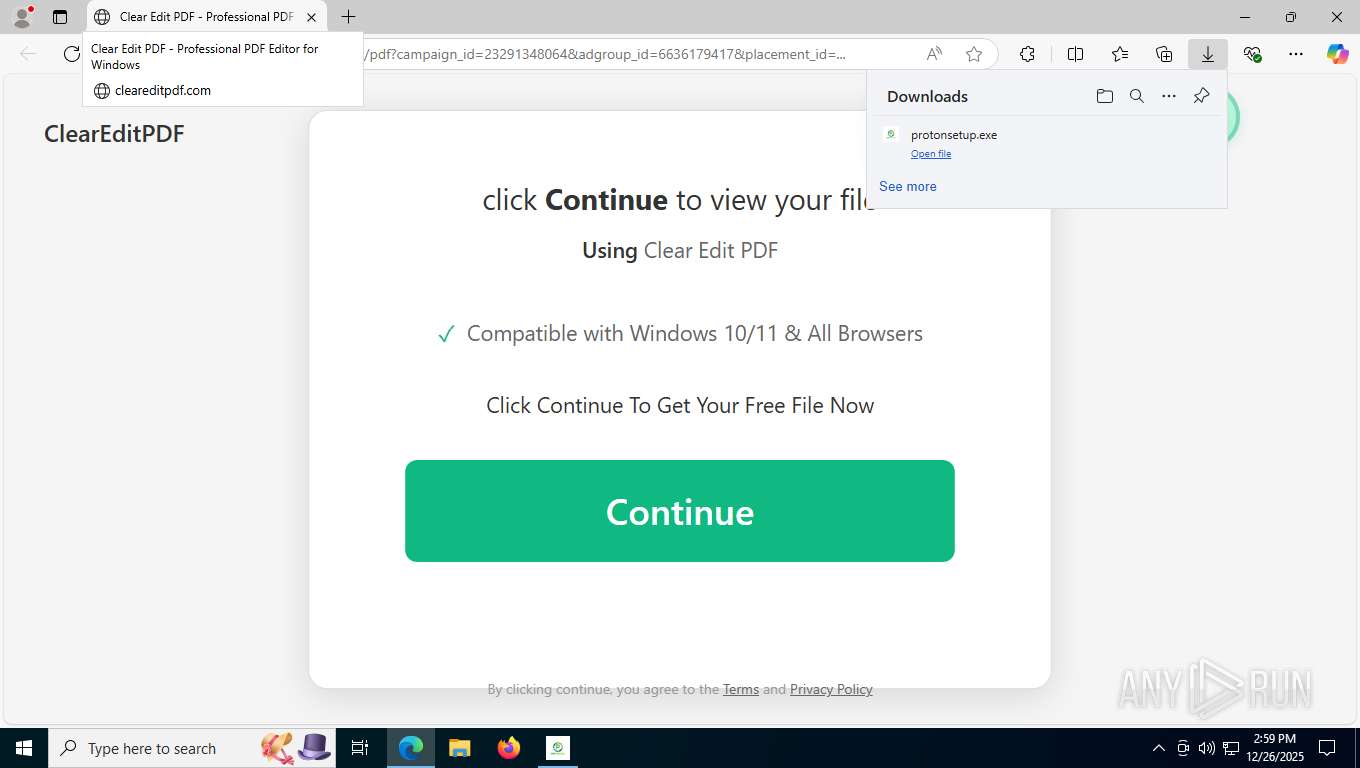
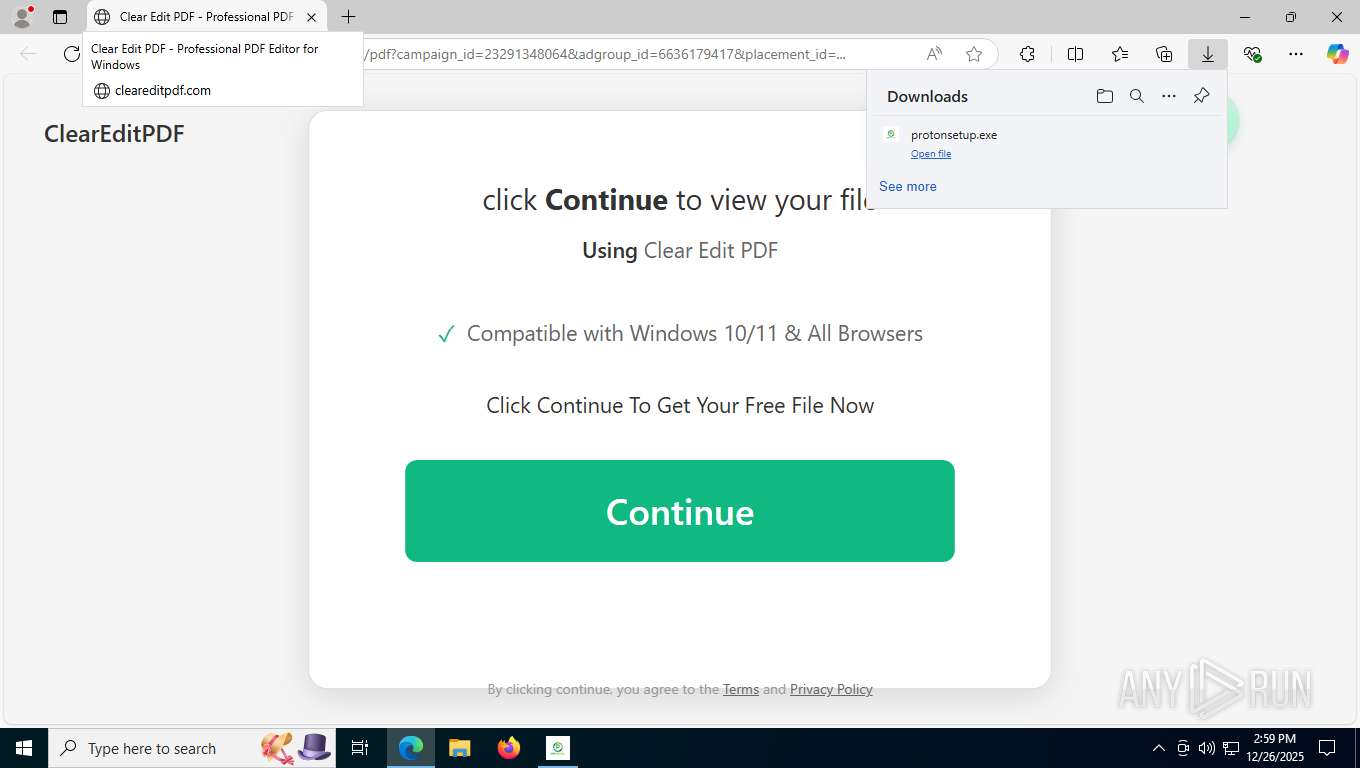
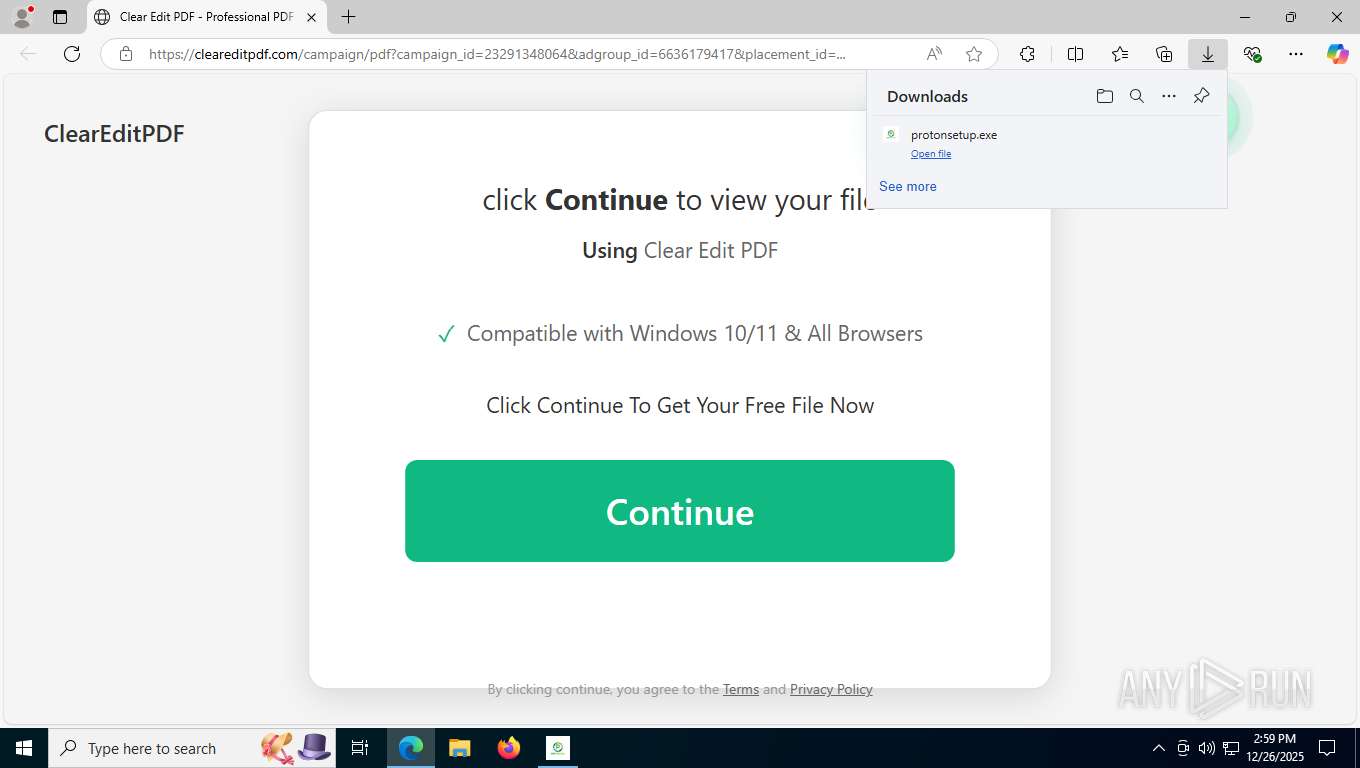
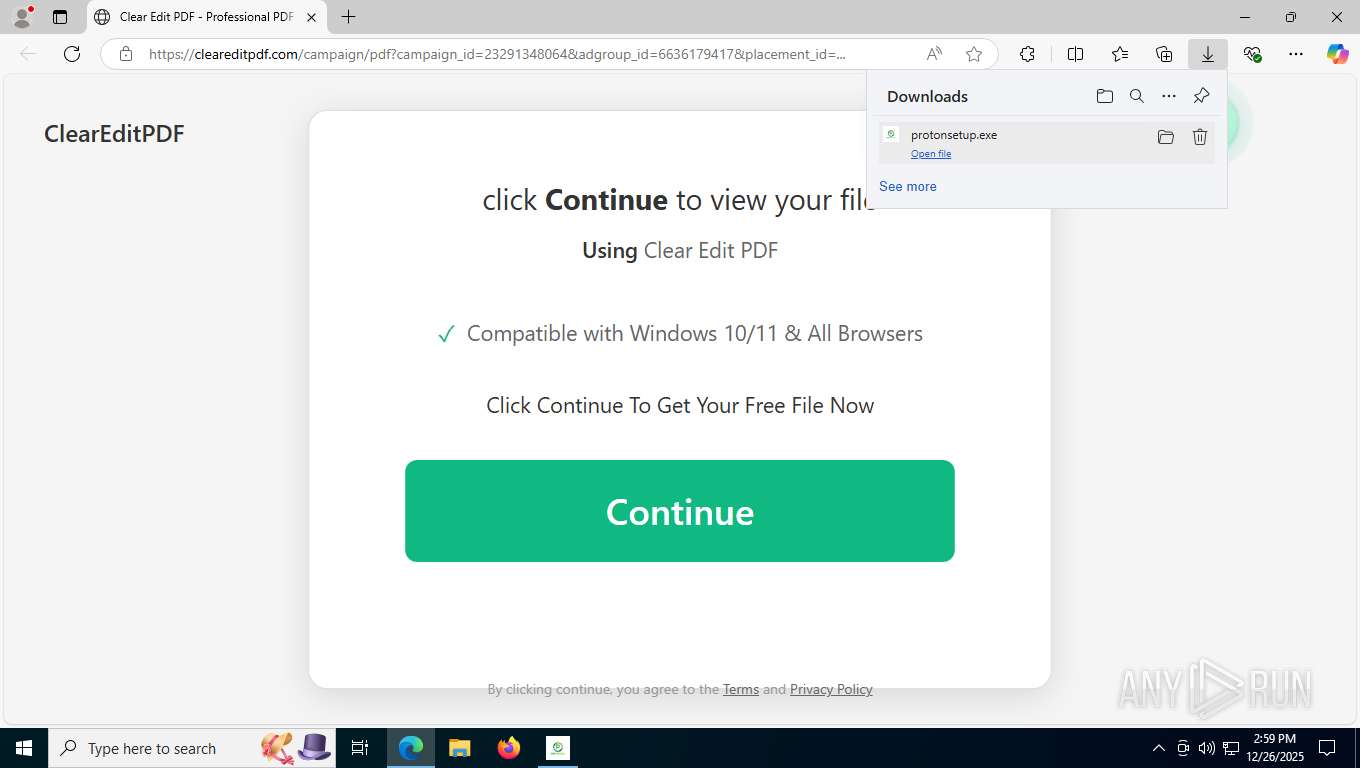
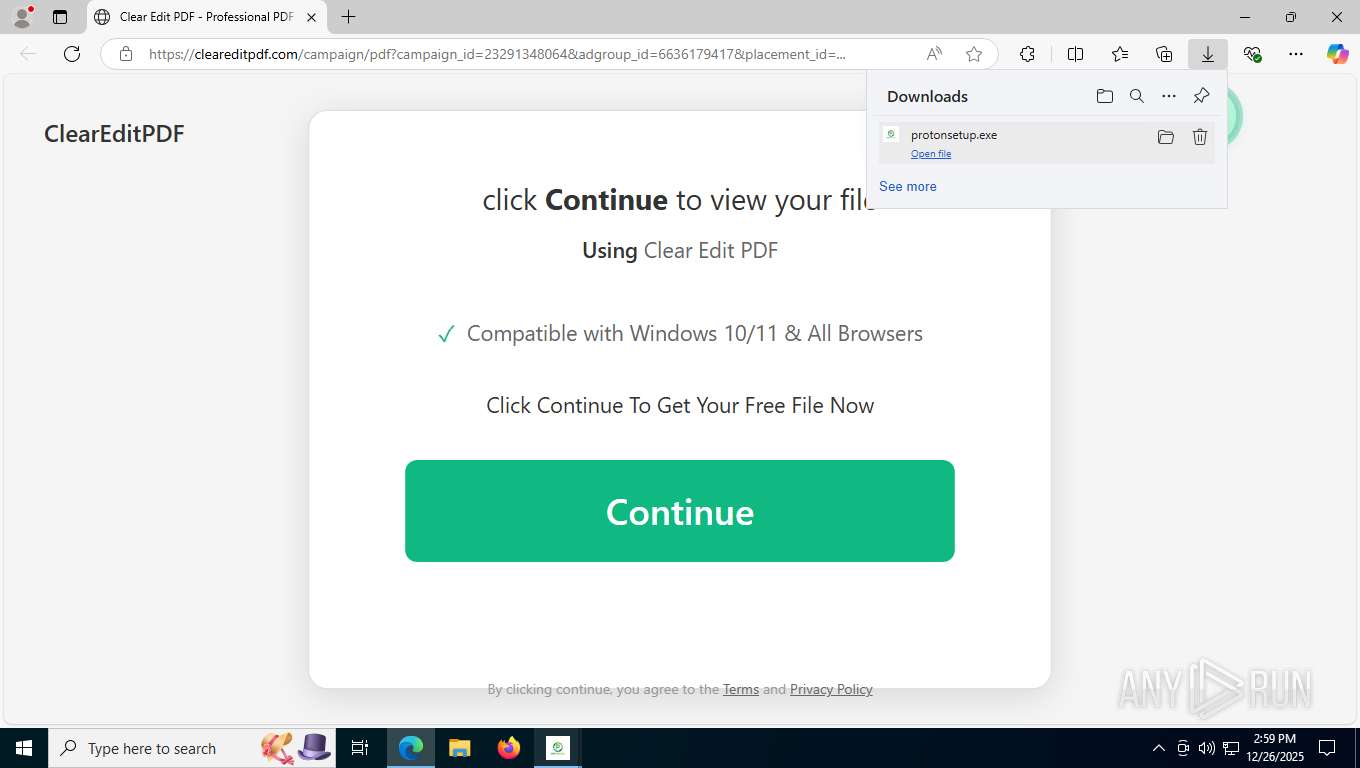
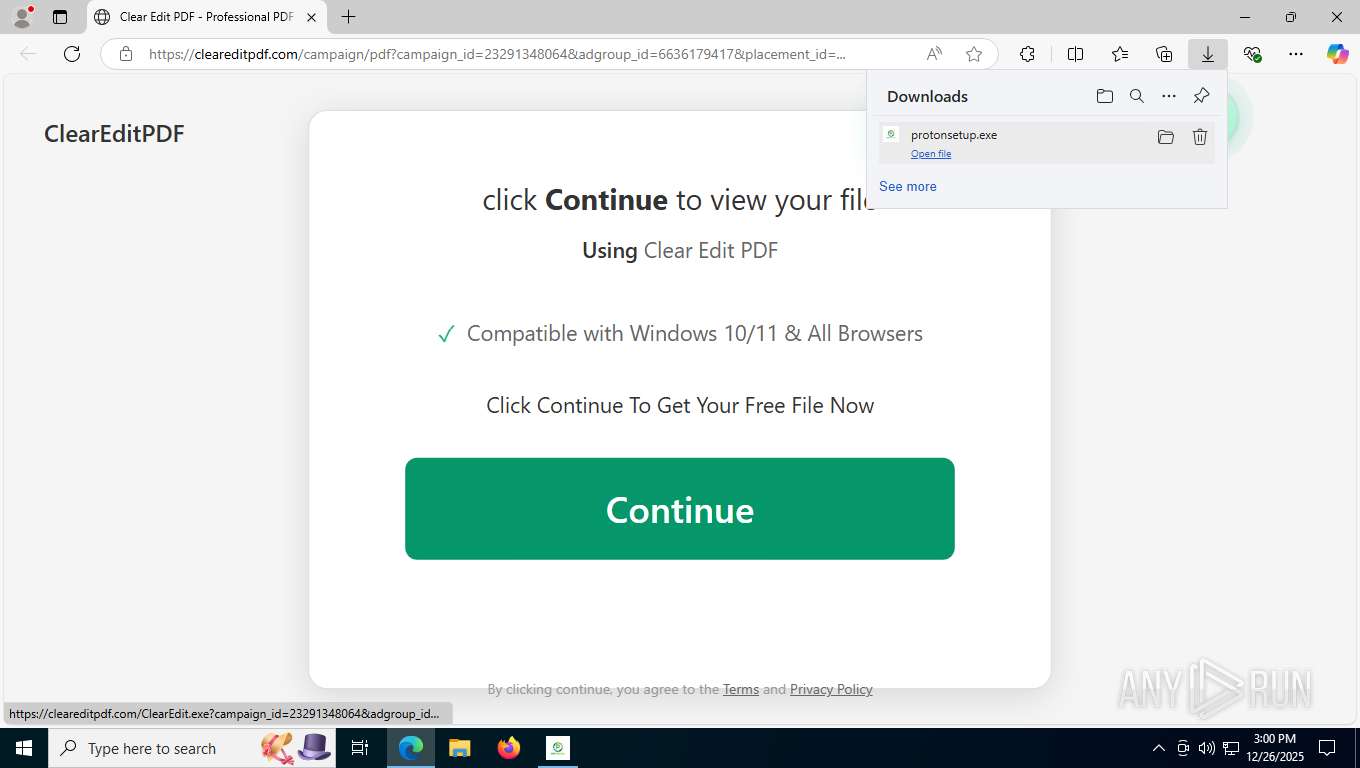
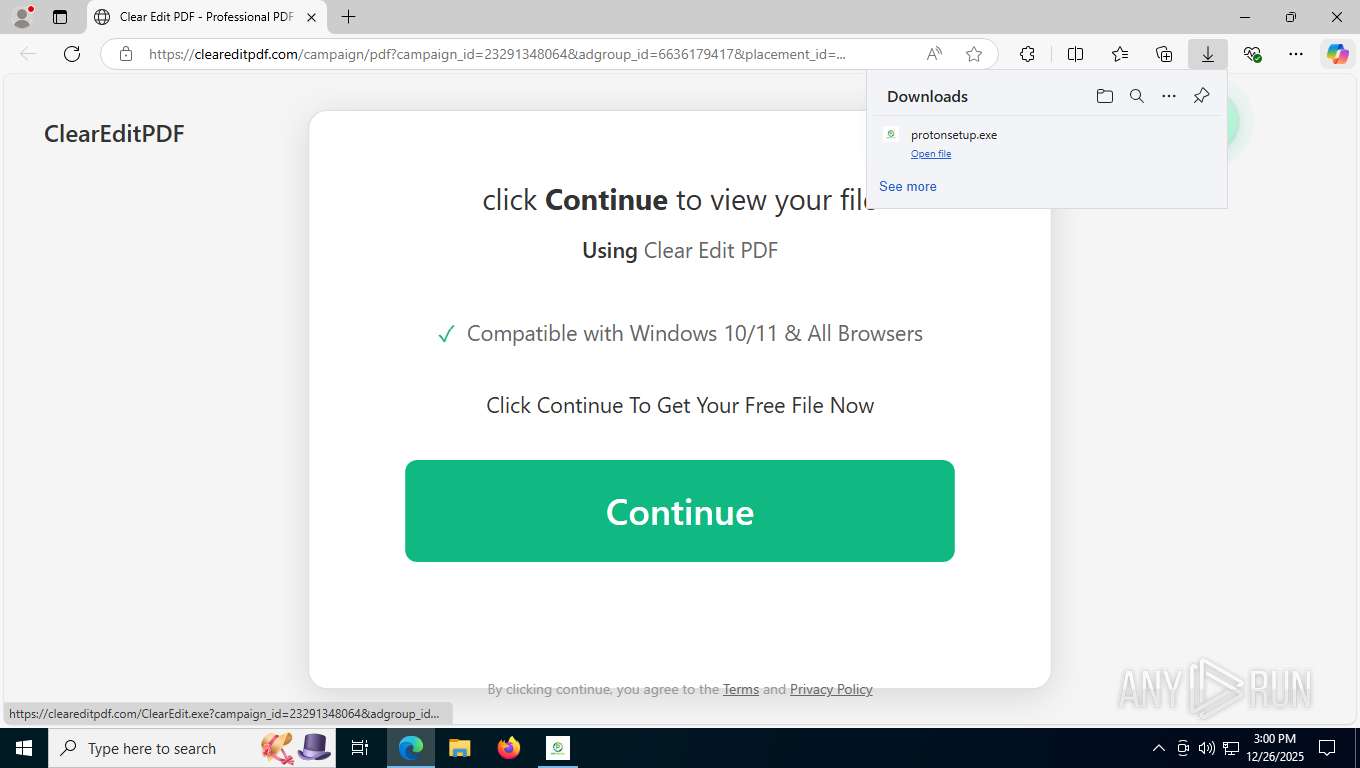
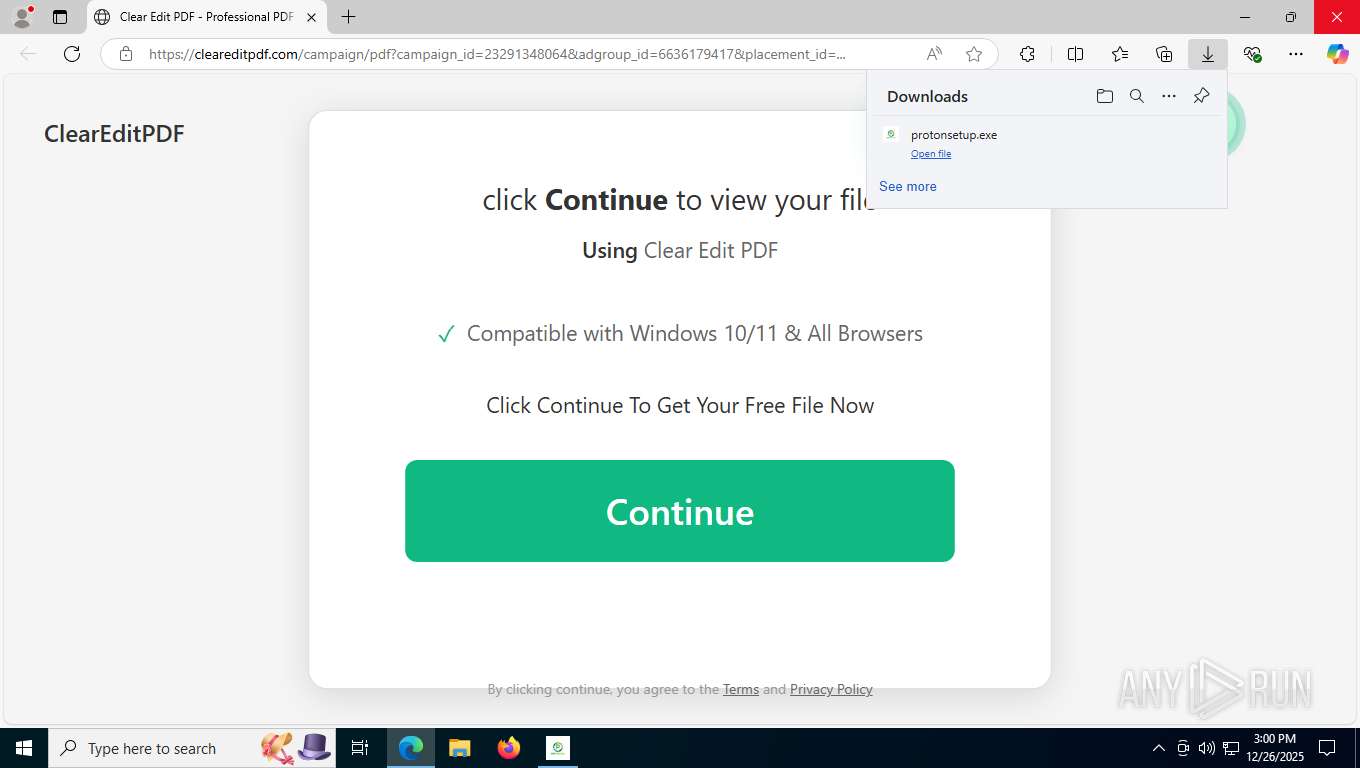
| URL: | https://cleareditpdf.com/campaign/pdf?campaign_id=23291348064&adgroup_id=6636179417&placement_id=... |
| Full analysis: | https://app.any.run/tasks/7e11b23d-cf63-4b17-9da9-09b57a94f5c8 |
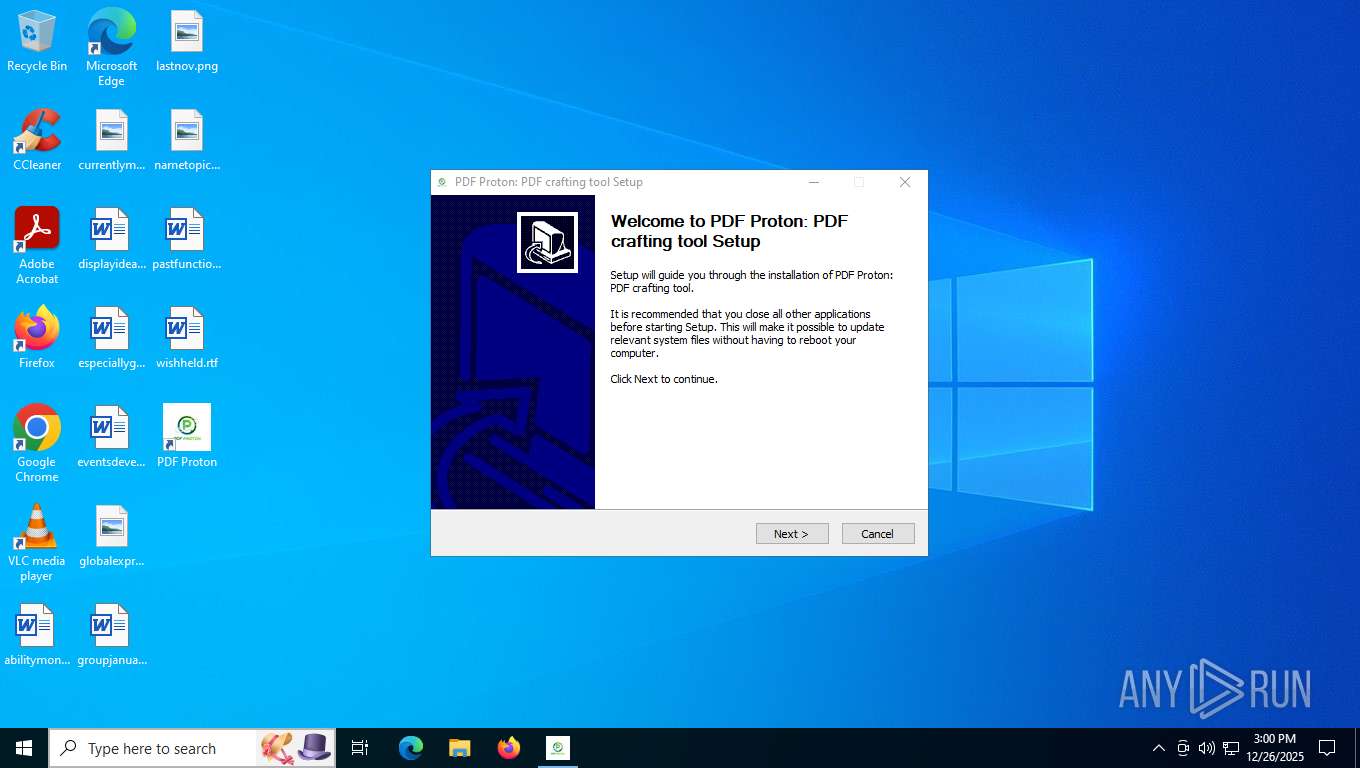
| Verdict: | Malicious activity |
| Analysis date: | December 26, 2025, 19:58:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B191FF1D710B51BEB9A40EB1795077D2 |
| SHA1: | 22D7DCC10D6AF21456C2824028A55BD77EF012F2 |
| SHA256: | F828EC2C47584E3942556AEC706DCCB0BF10695BFFDF96F19D188CF533D70E2C |
| SSDEEP: | 3:N8UBAY3TtMWtgRyBULV1/gUSDjvrMo:2U2QBtxBk1/gTvrMo |
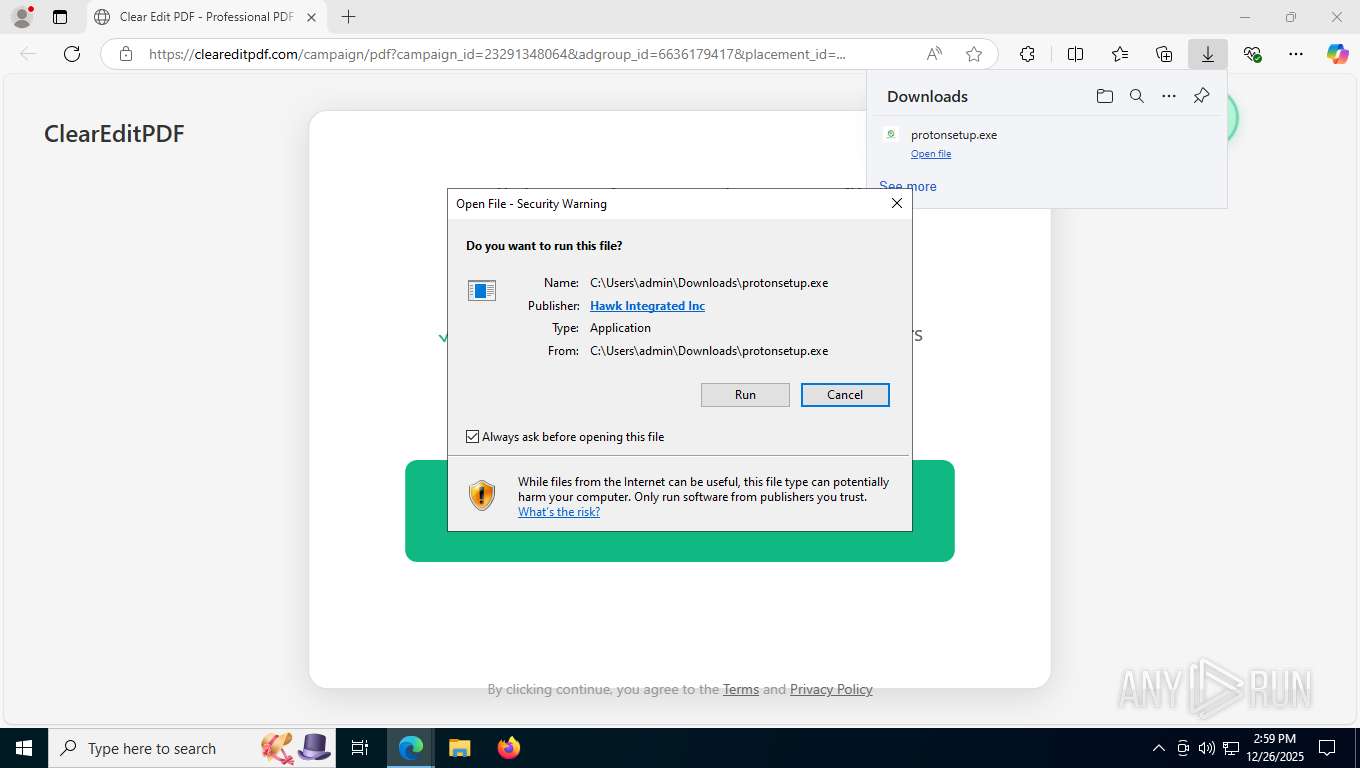
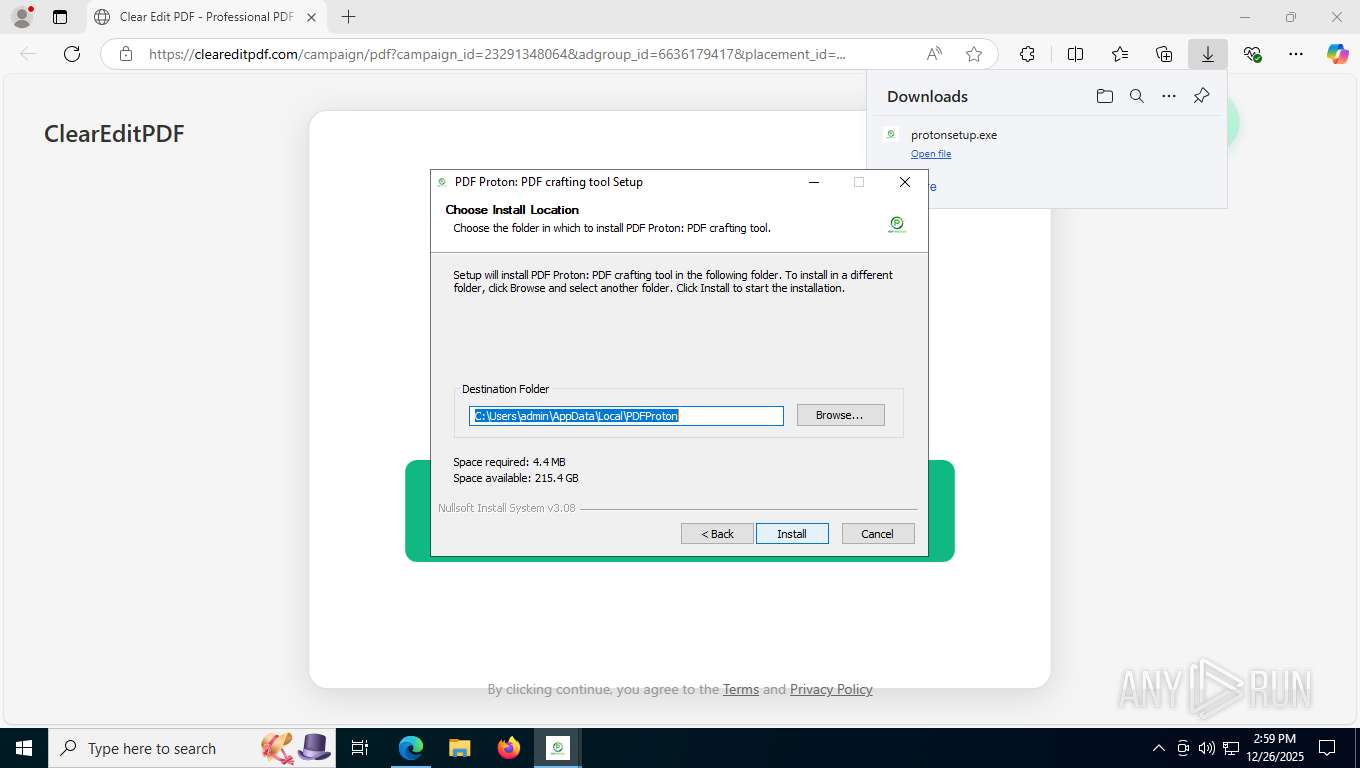
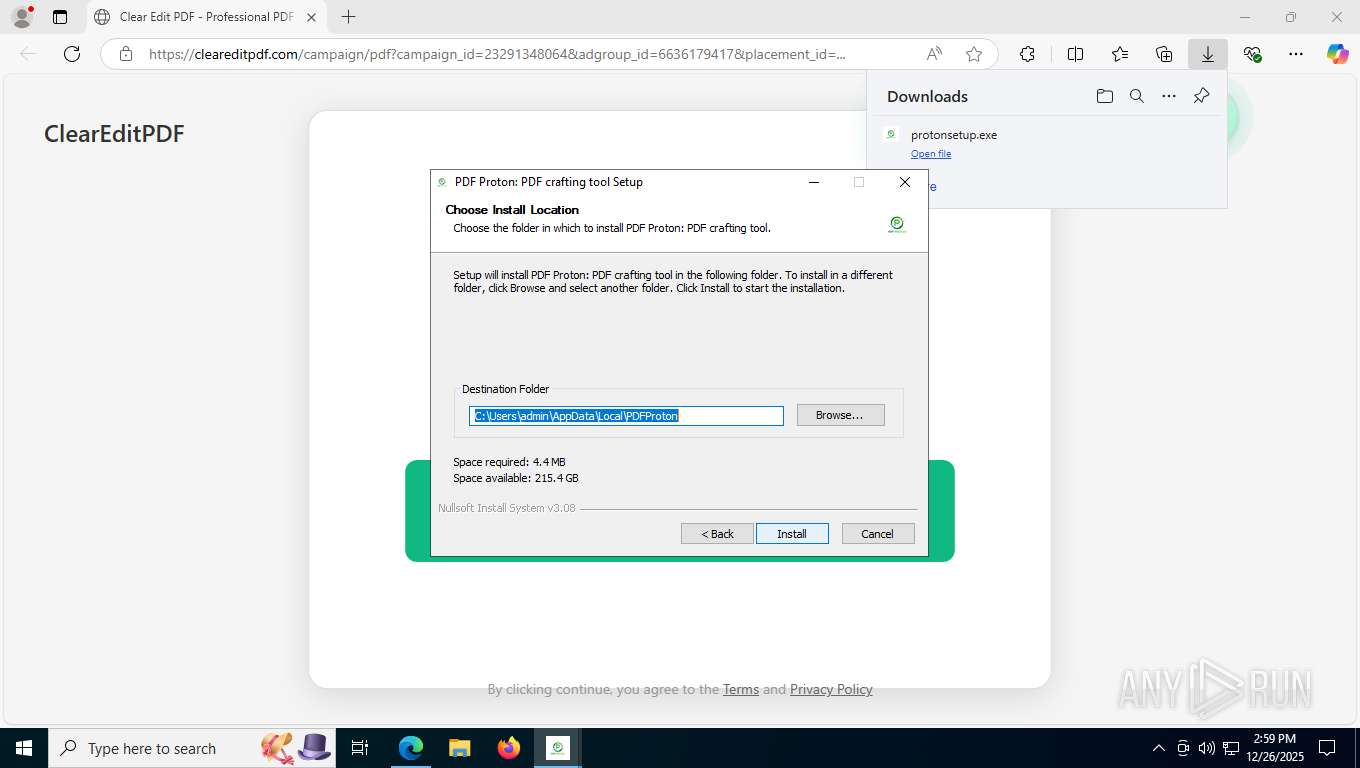
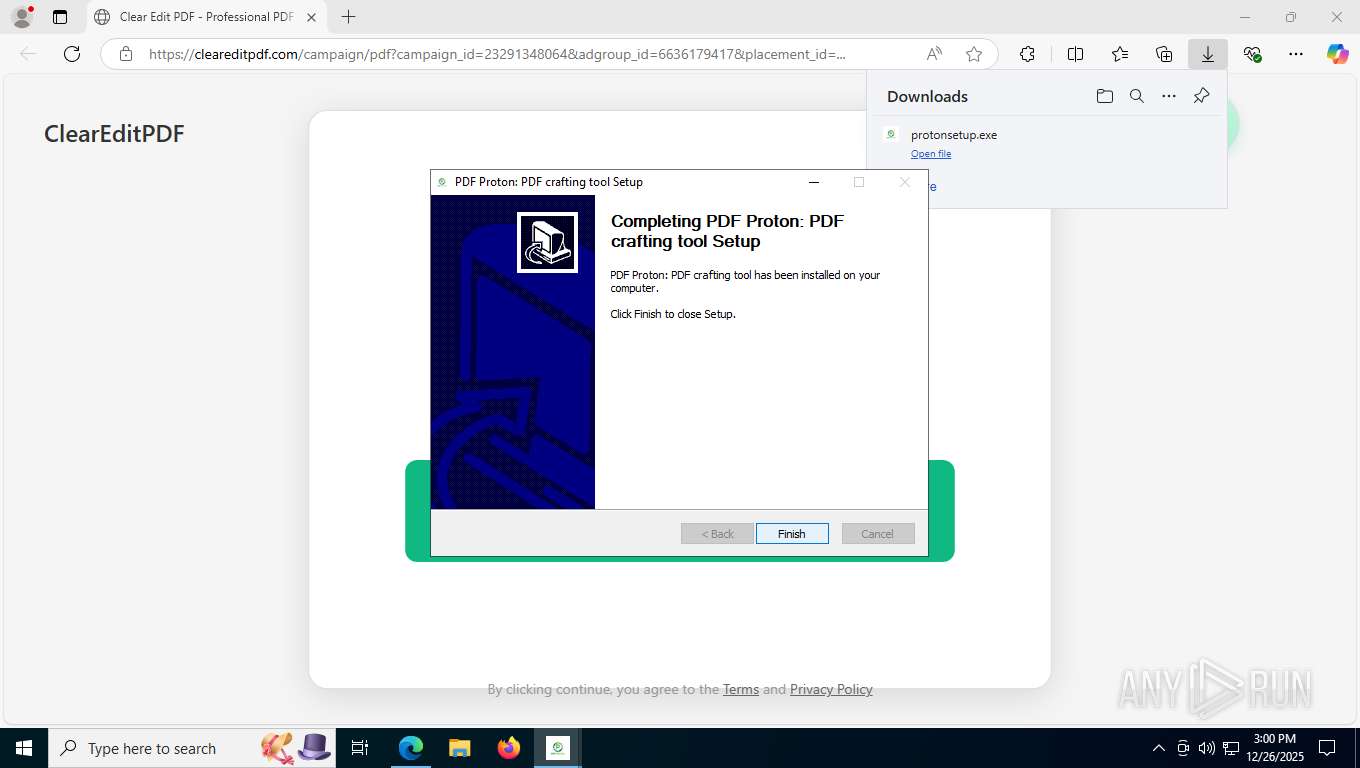
MALICIOUS
No malicious indicators.SUSPICIOUS
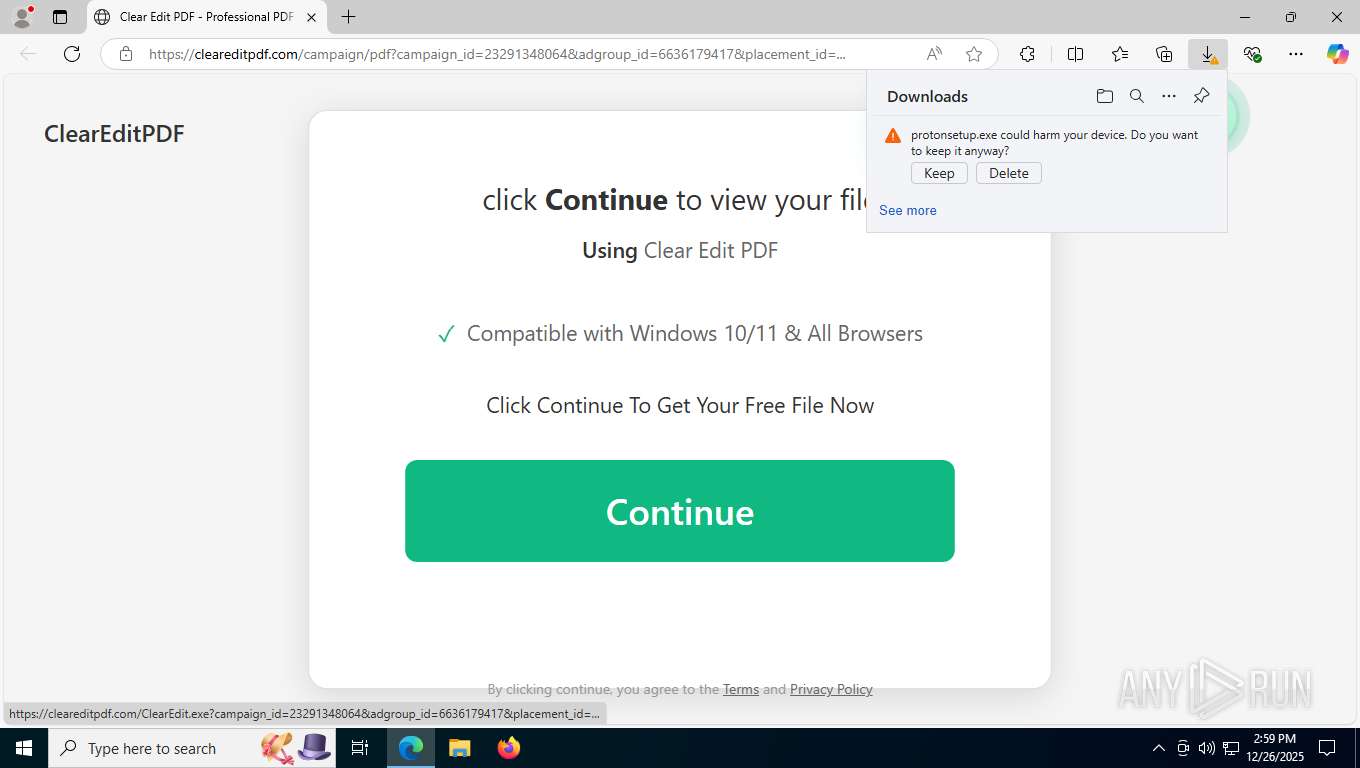
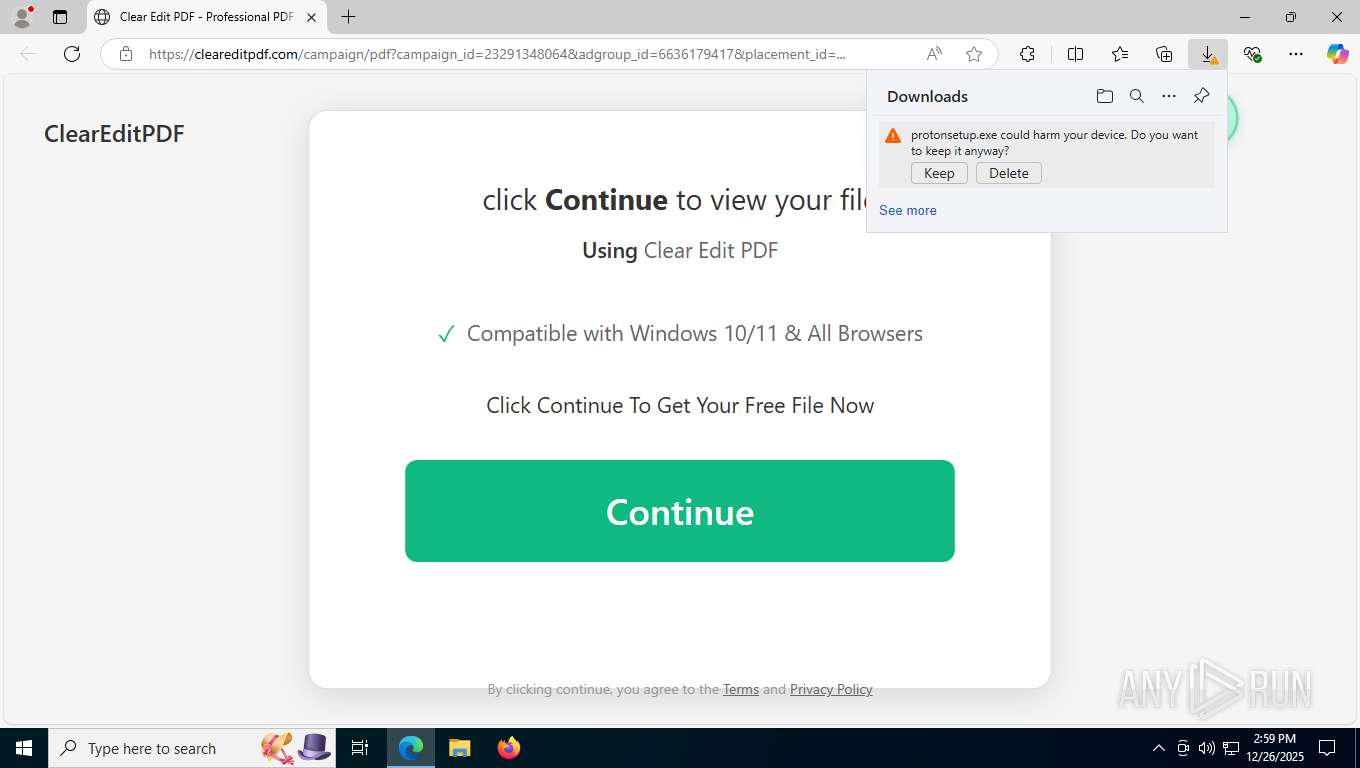
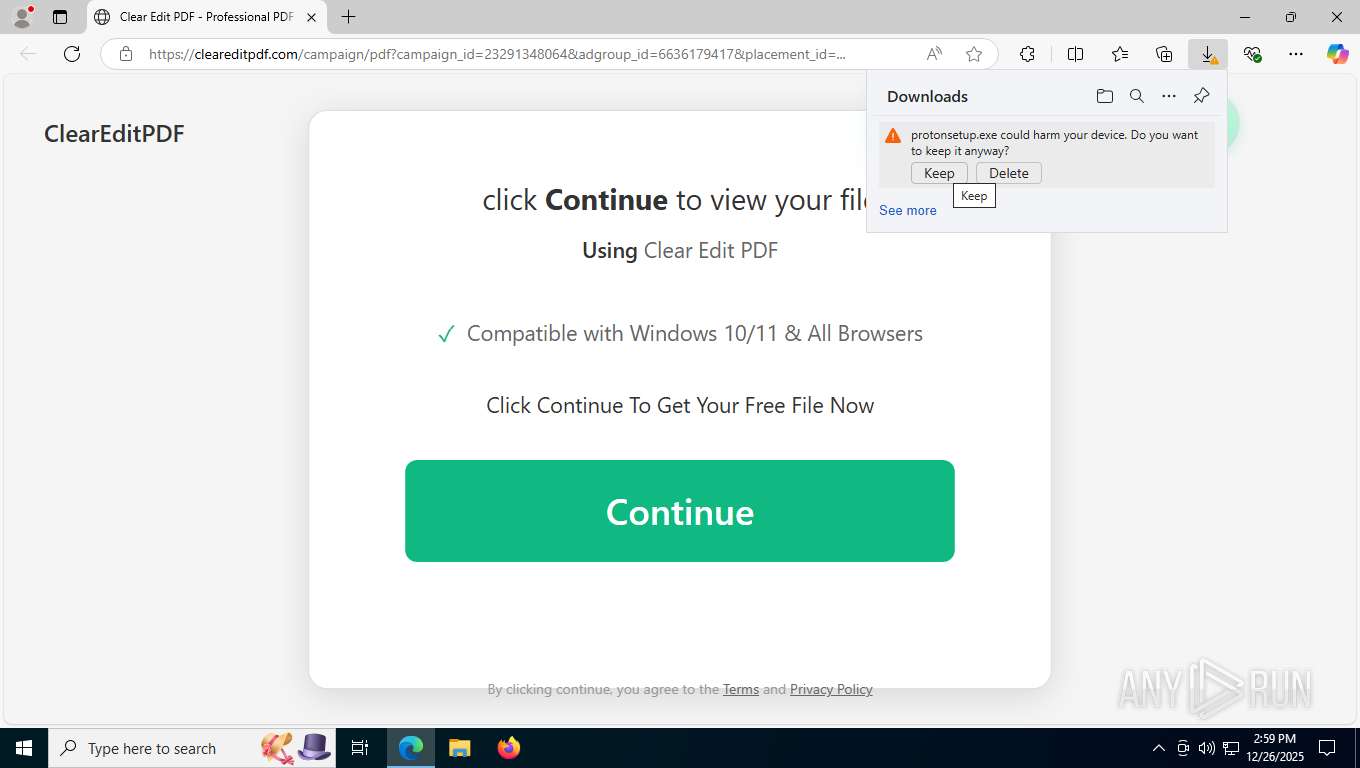
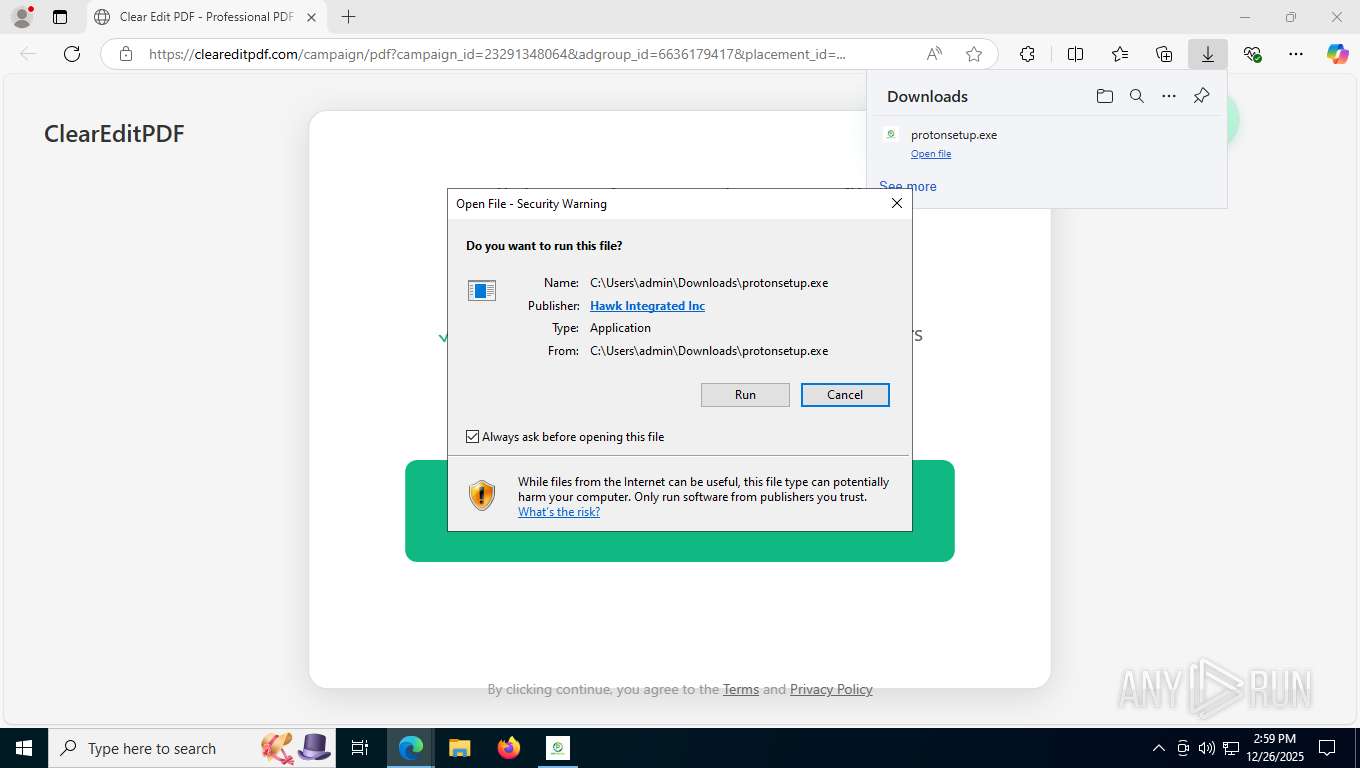
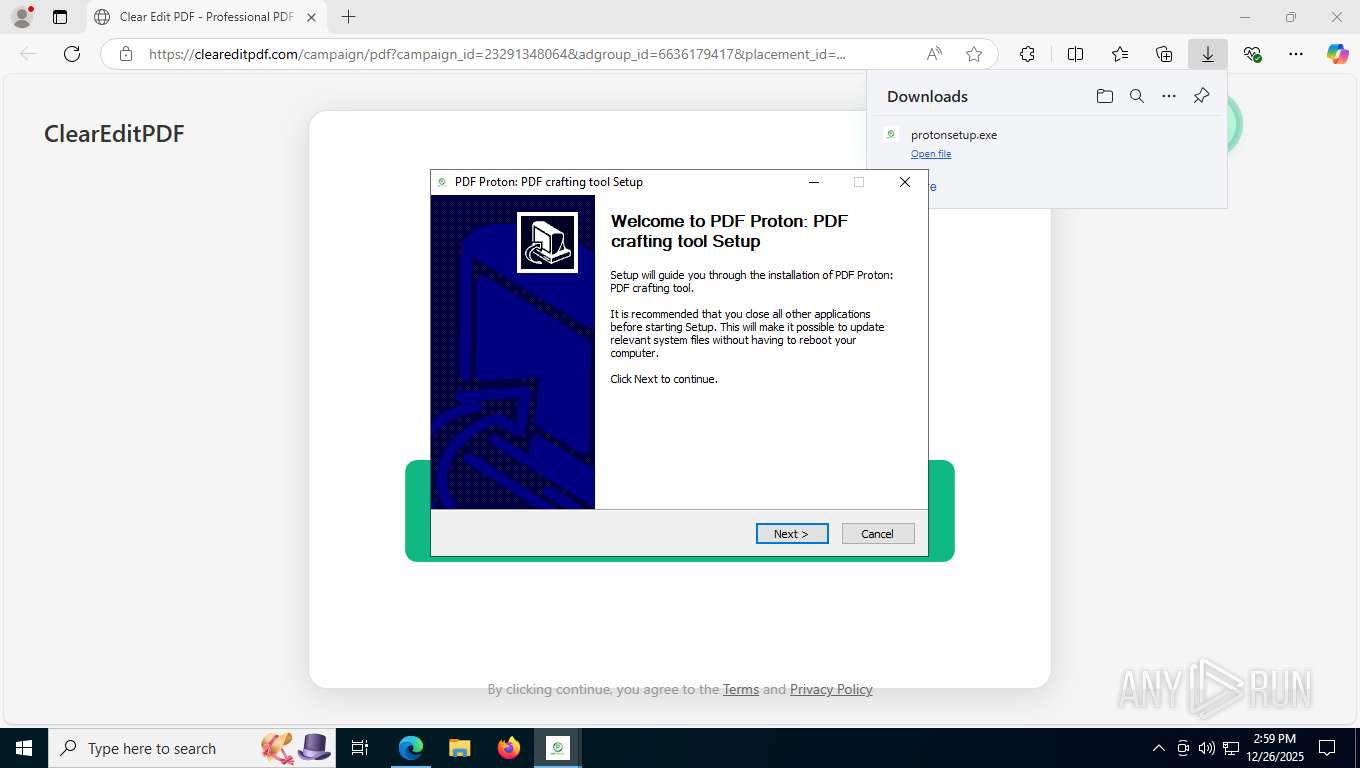
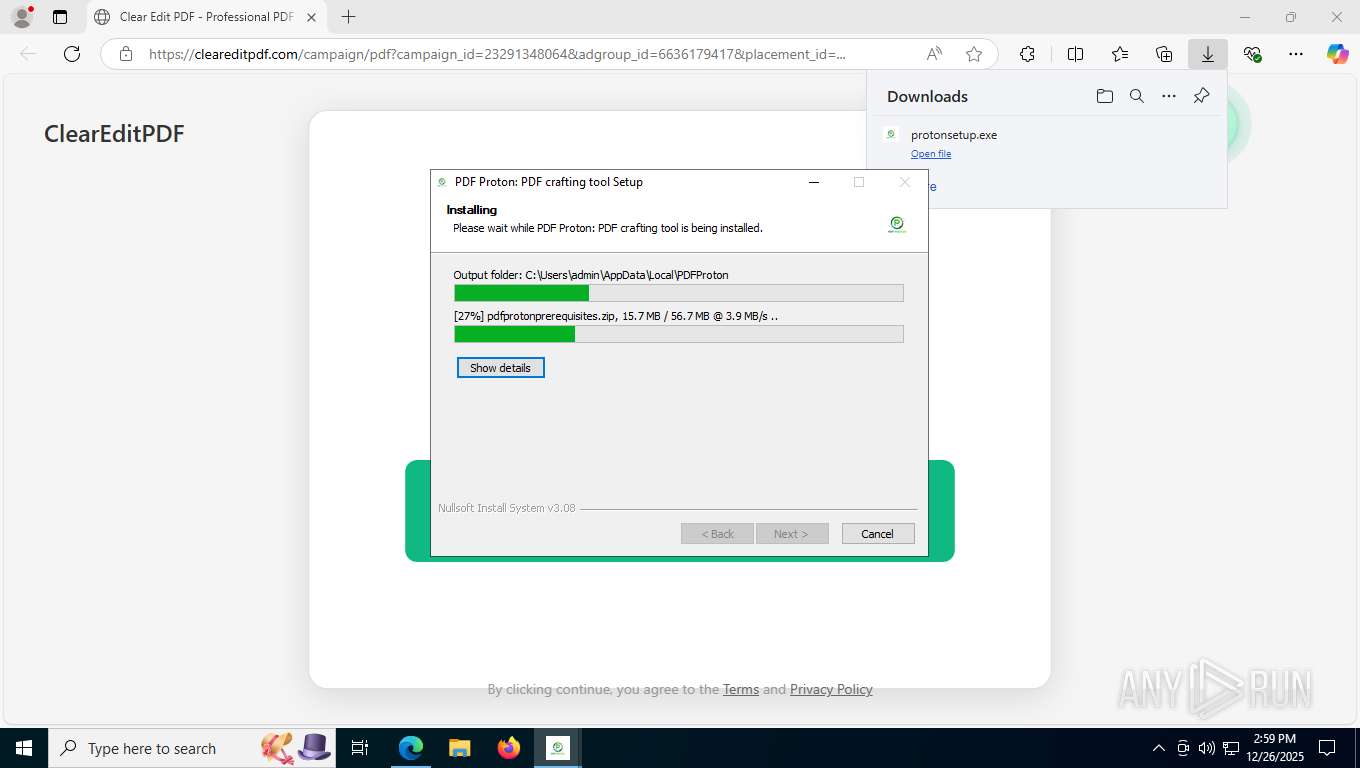
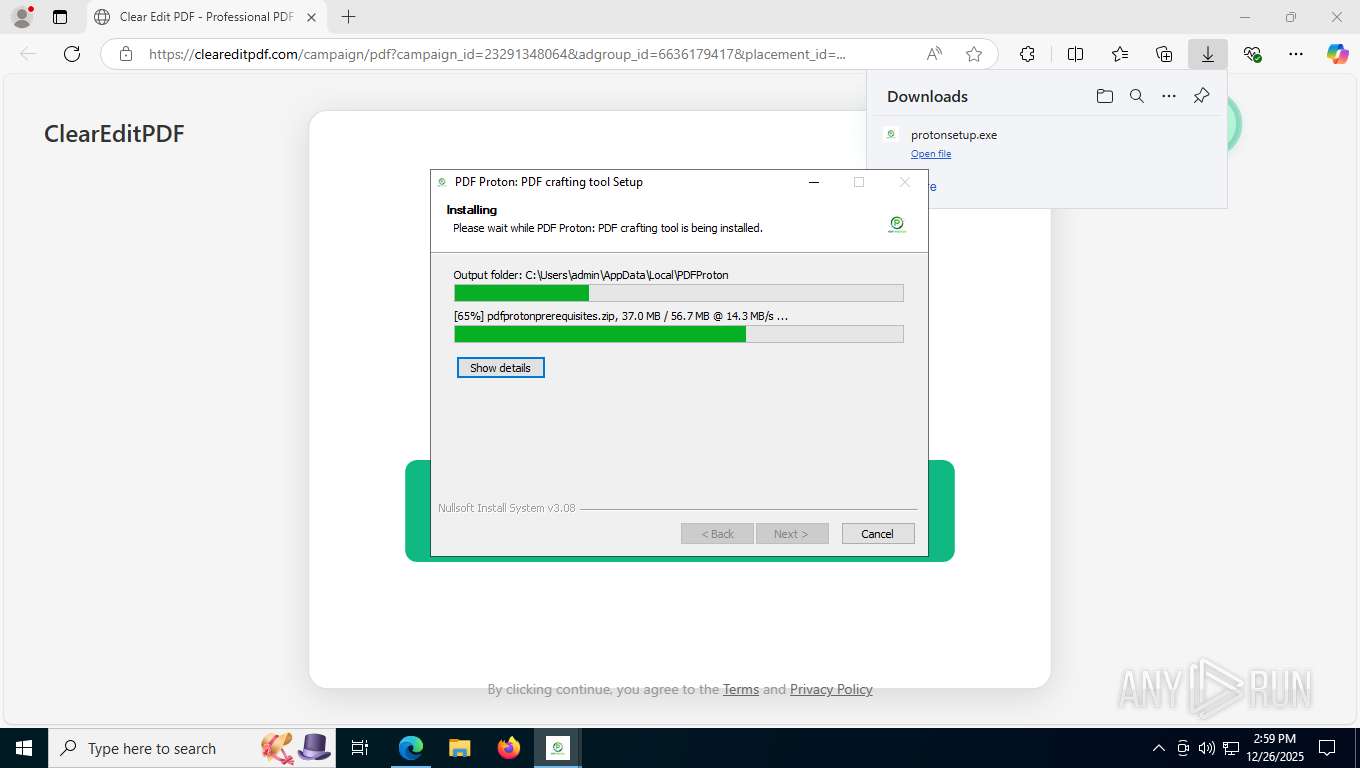
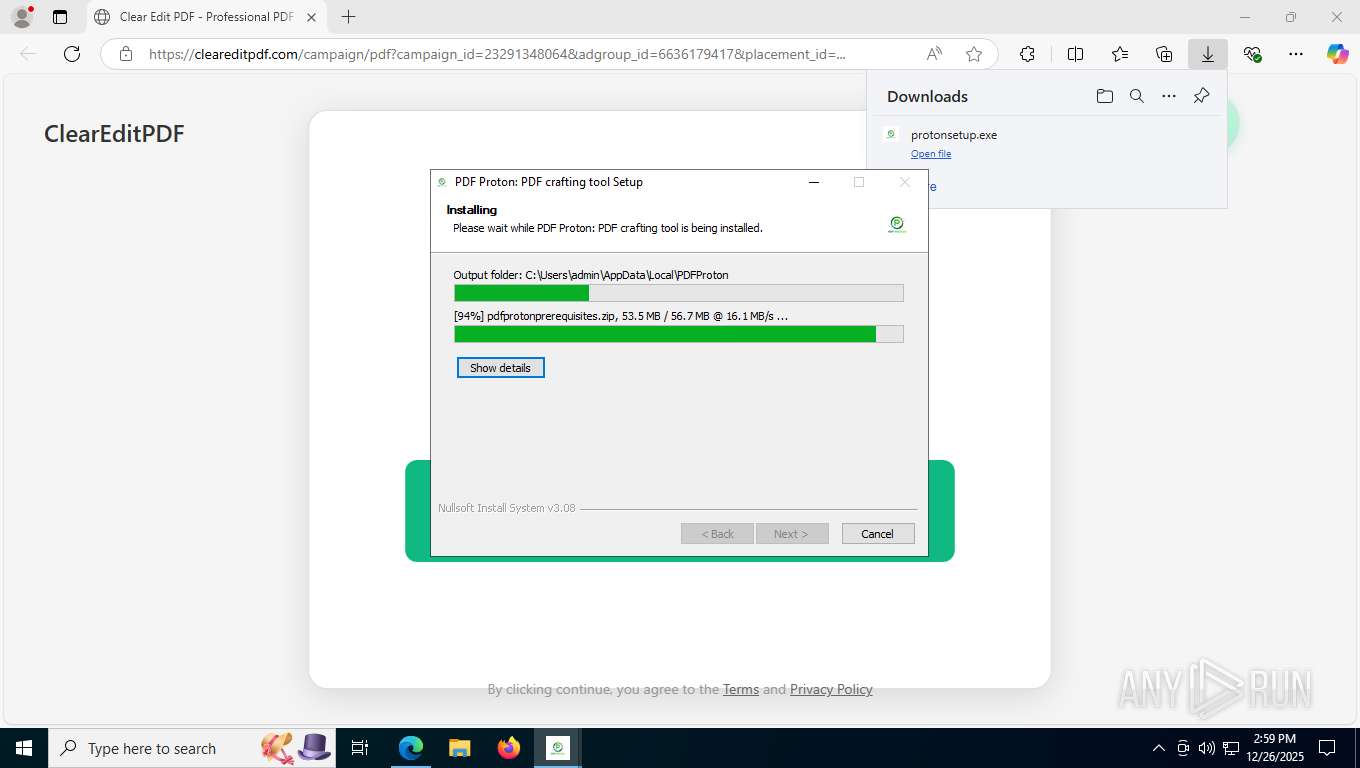
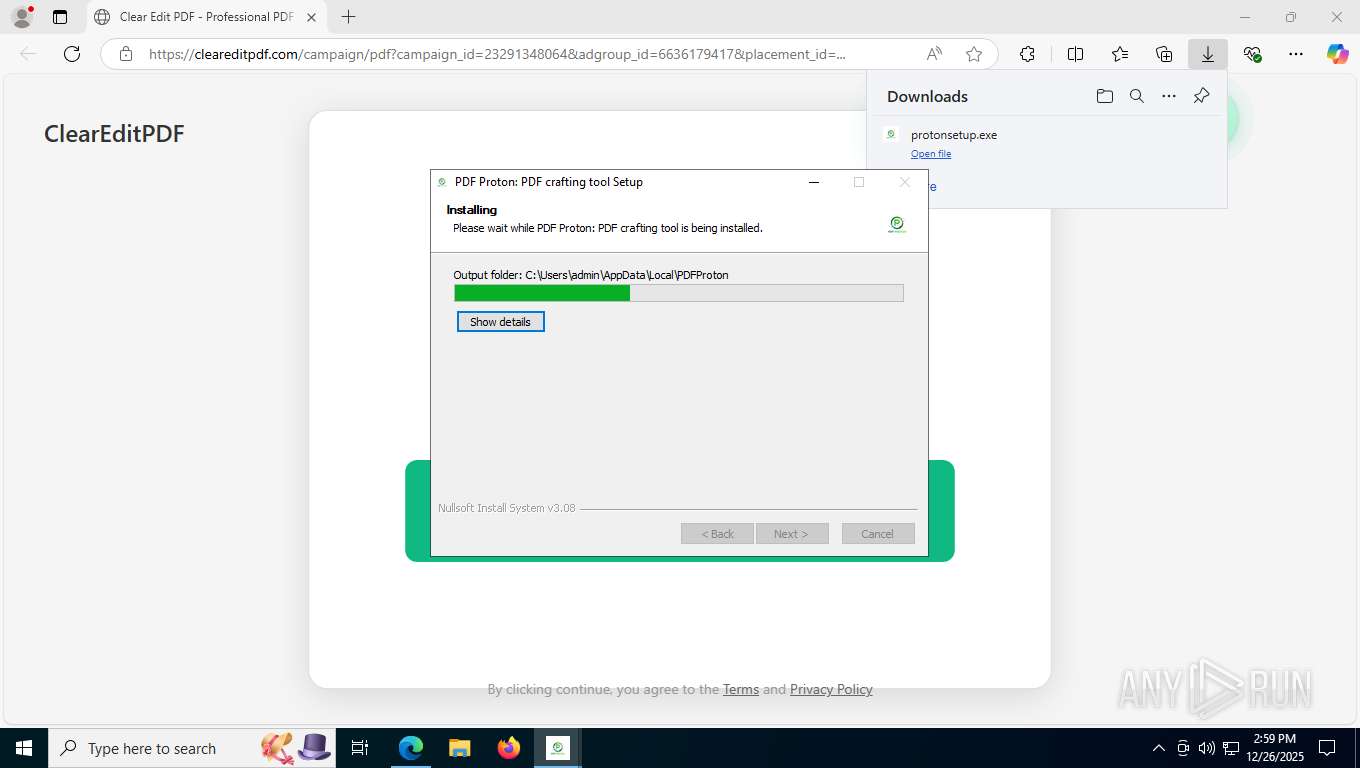
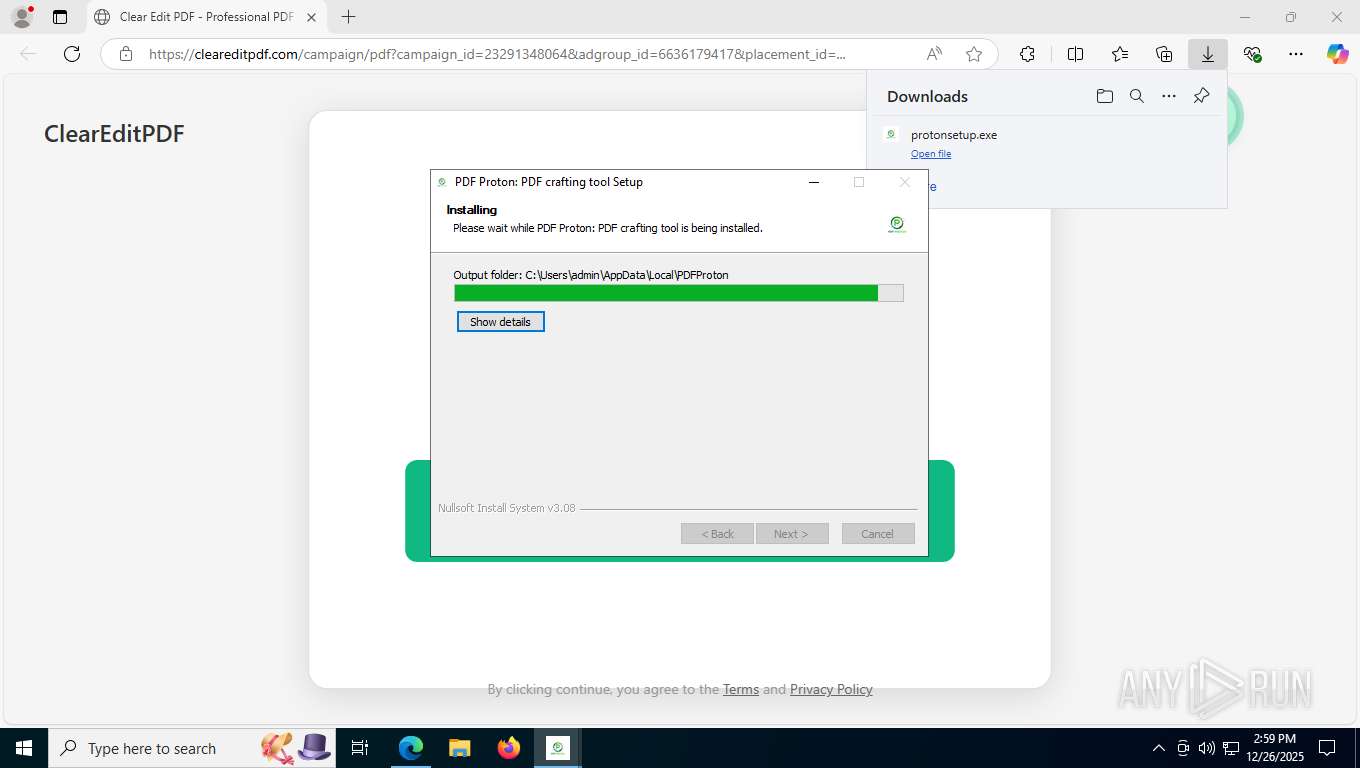
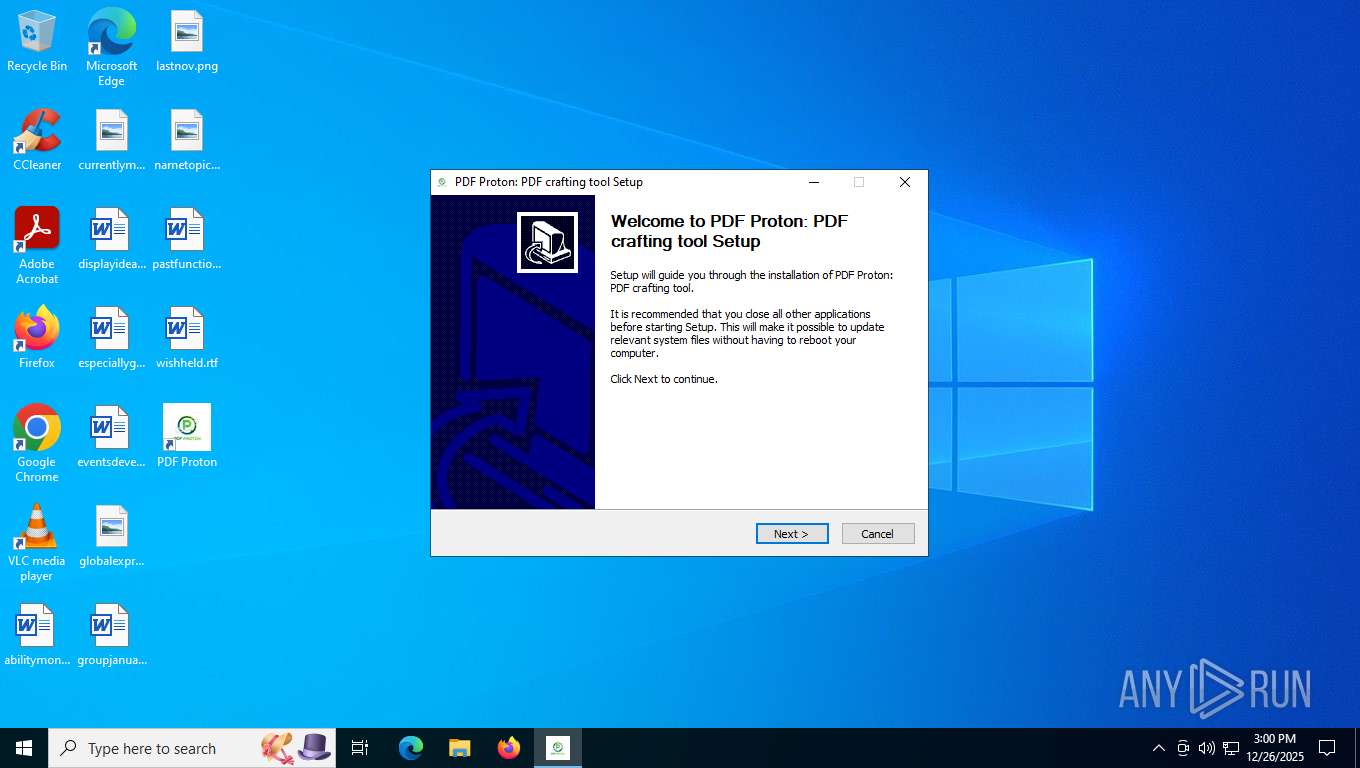
The process creates files with name similar to system file names
- protonsetup.exe (PID: 4912)
- protonsetup.exe (PID: 1156)
Malware-specific behavior (creating "System.dll" in Temp)
- protonsetup.exe (PID: 4912)
- protonsetup.exe (PID: 1156)
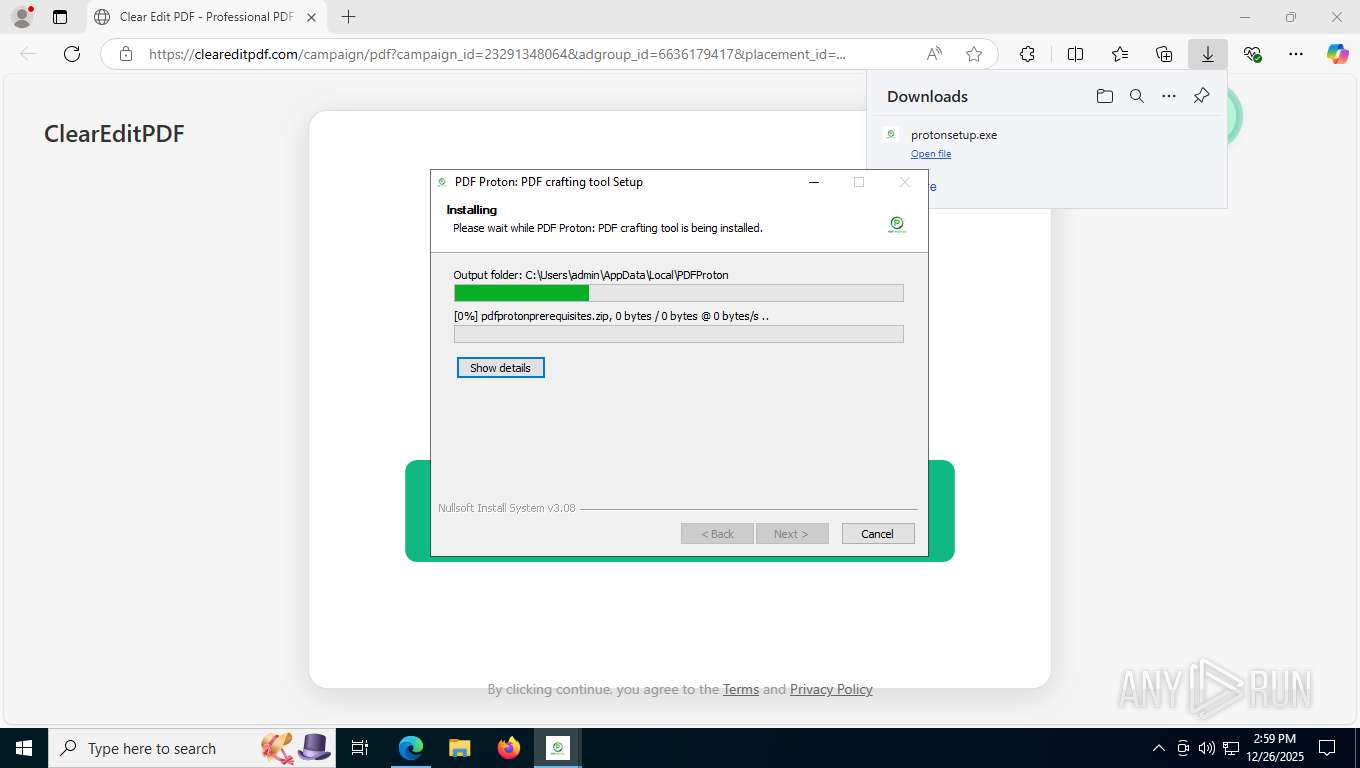
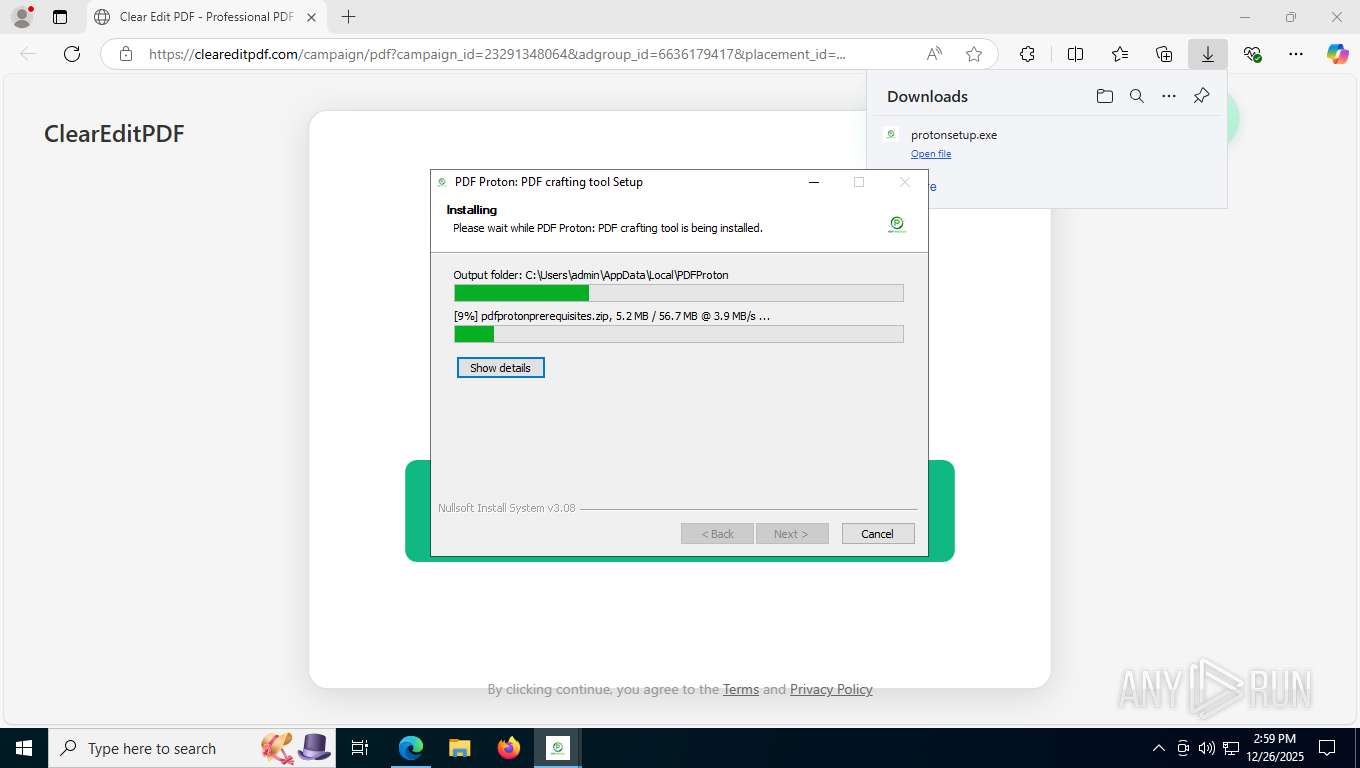
Drops 7-zip archiver for unpacking
- protonsetup.exe (PID: 4912)
- protonsetup.exe (PID: 1156)
Executable content was dropped or overwritten
- protonsetup.exe (PID: 4912)
- protonsetup.exe (PID: 1156)
There is functionality for taking screenshot (YARA)
- protonsetup.exe (PID: 4912)
- protonsetup.exe (PID: 1156)
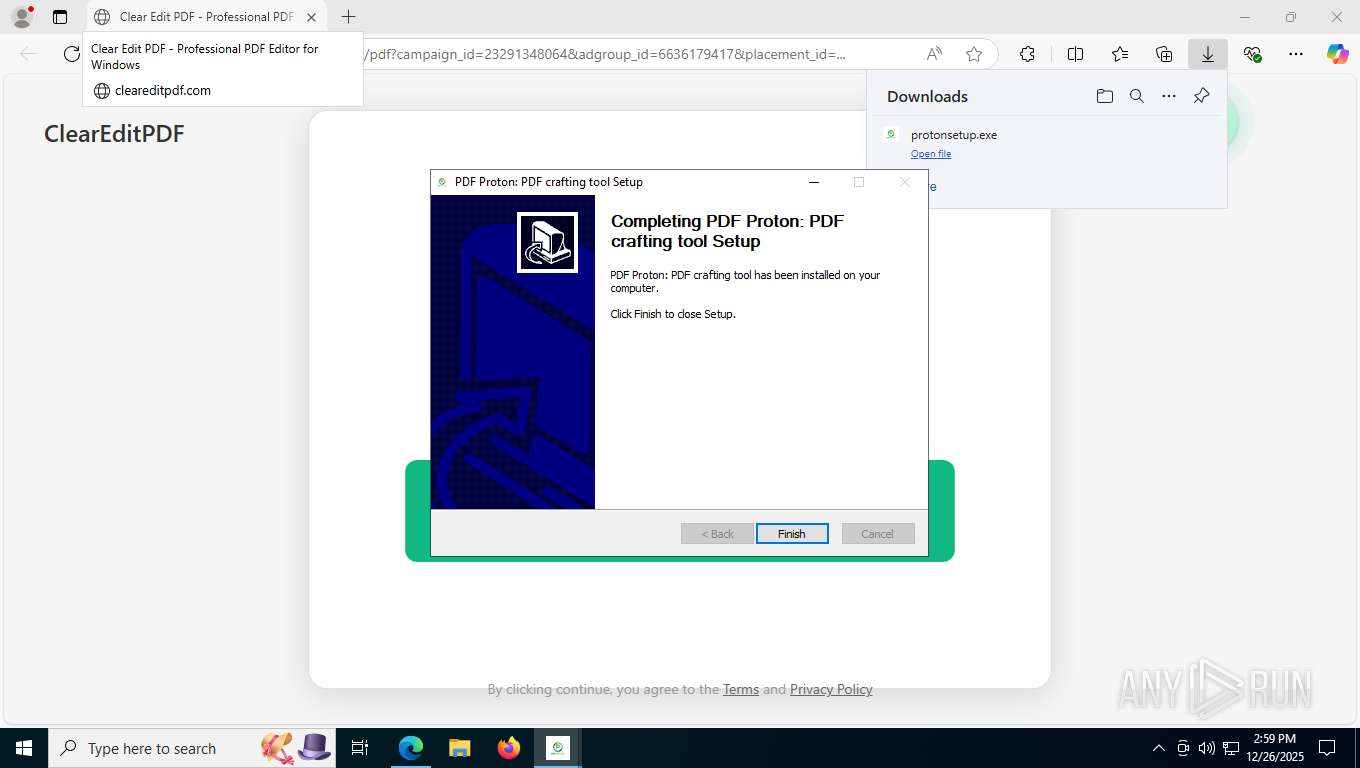
Process drops legitimate windows executable
- protonsetup.exe (PID: 1156)
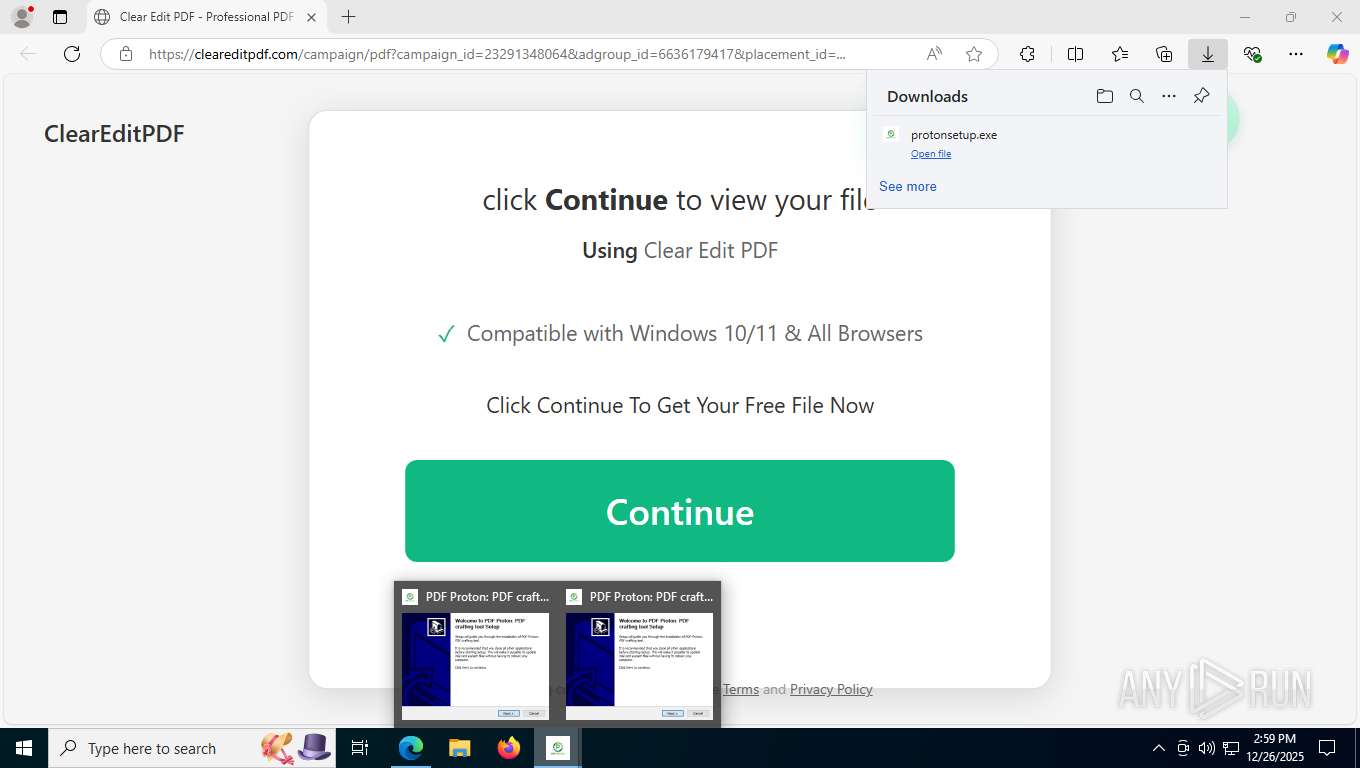
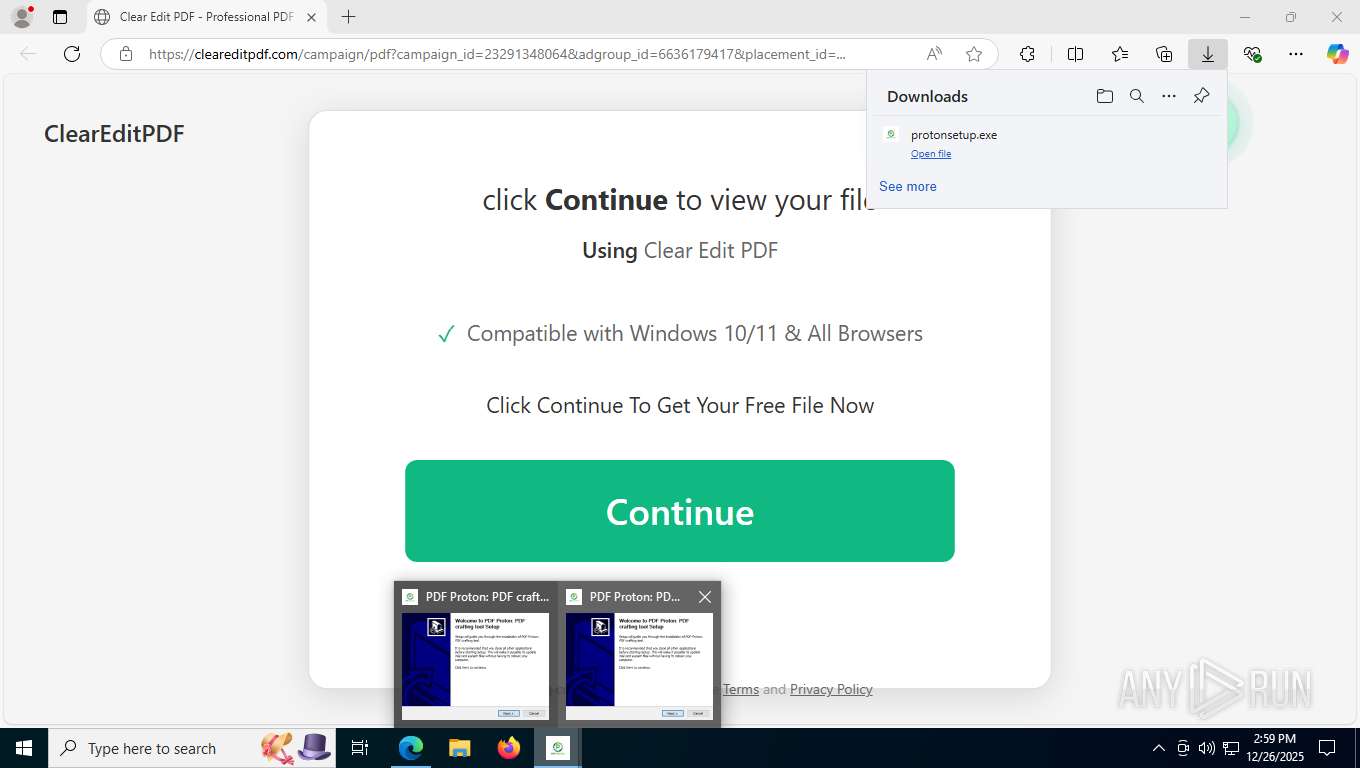
Application launched itself
- PDF Proton.exe (PID: 2196)
INFO
Checks supported languages
- identity_helper.exe (PID: 1388)
- protonsetup.exe (PID: 4912)
- protonsetup.exe (PID: 1156)
- TextInputHost.exe (PID: 424)
- PDF Proton.exe (PID: 2196)
- PDF Proton.exe (PID: 6792)
- PDF Proton.exe (PID: 6544)
- PDF Proton.exe (PID: 1600)
Executable content was dropped or overwritten
- msedge.exe (PID: 7580)
Reads the computer name
- identity_helper.exe (PID: 1388)
- protonsetup.exe (PID: 4912)
- protonsetup.exe (PID: 1156)
- TextInputHost.exe (PID: 424)
- PDF Proton.exe (PID: 2196)
- PDF Proton.exe (PID: 6792)
- PDF Proton.exe (PID: 6544)
The sample compiled with english language support
- msedge.exe (PID: 7580)
- protonsetup.exe (PID: 4912)
- protonsetup.exe (PID: 1156)
Application launched itself
- msedge.exe (PID: 7580)
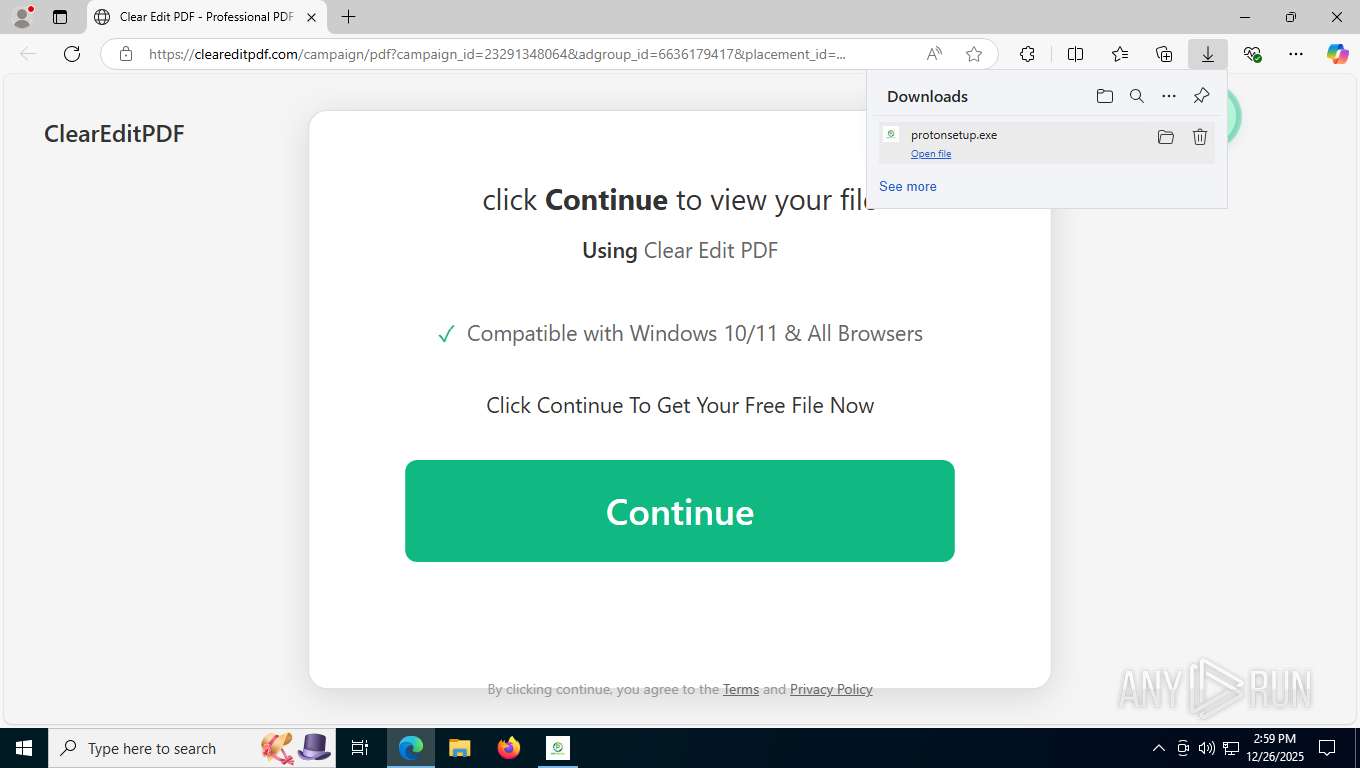
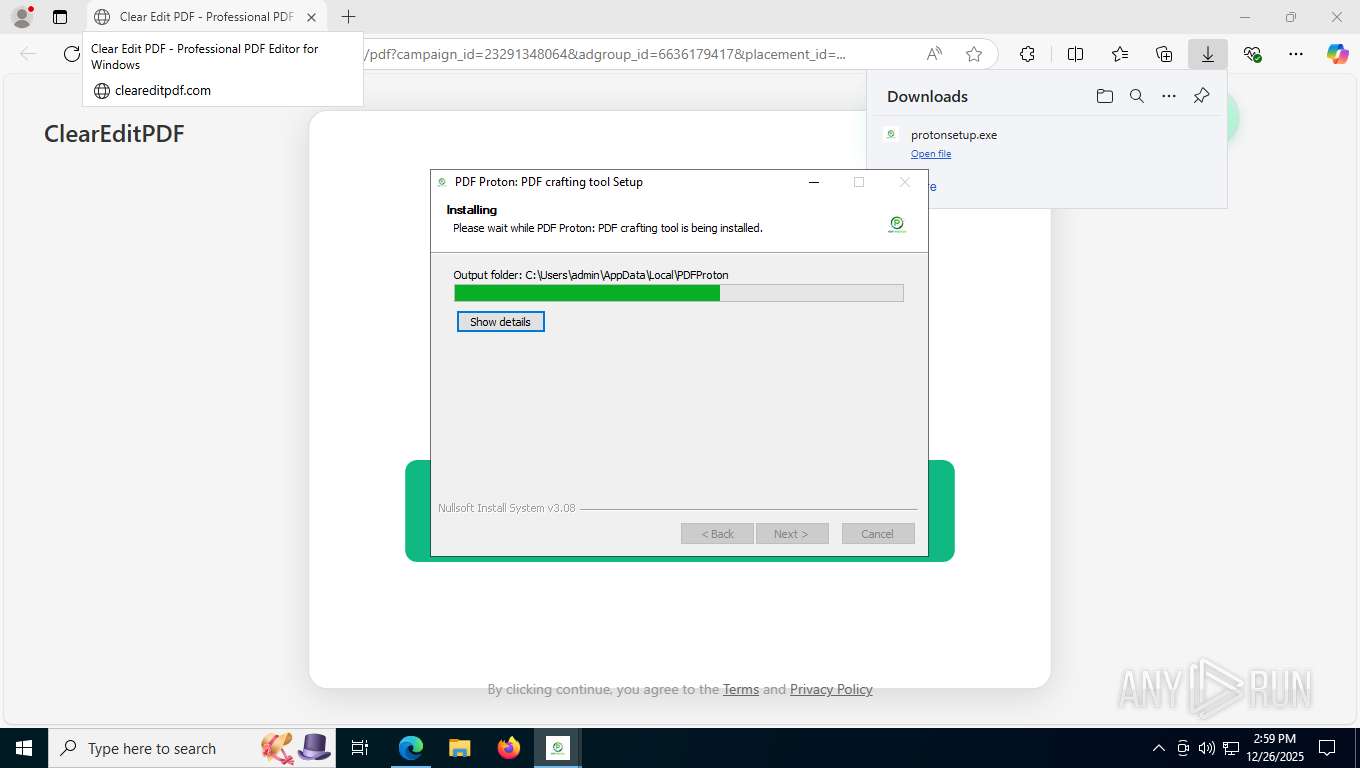
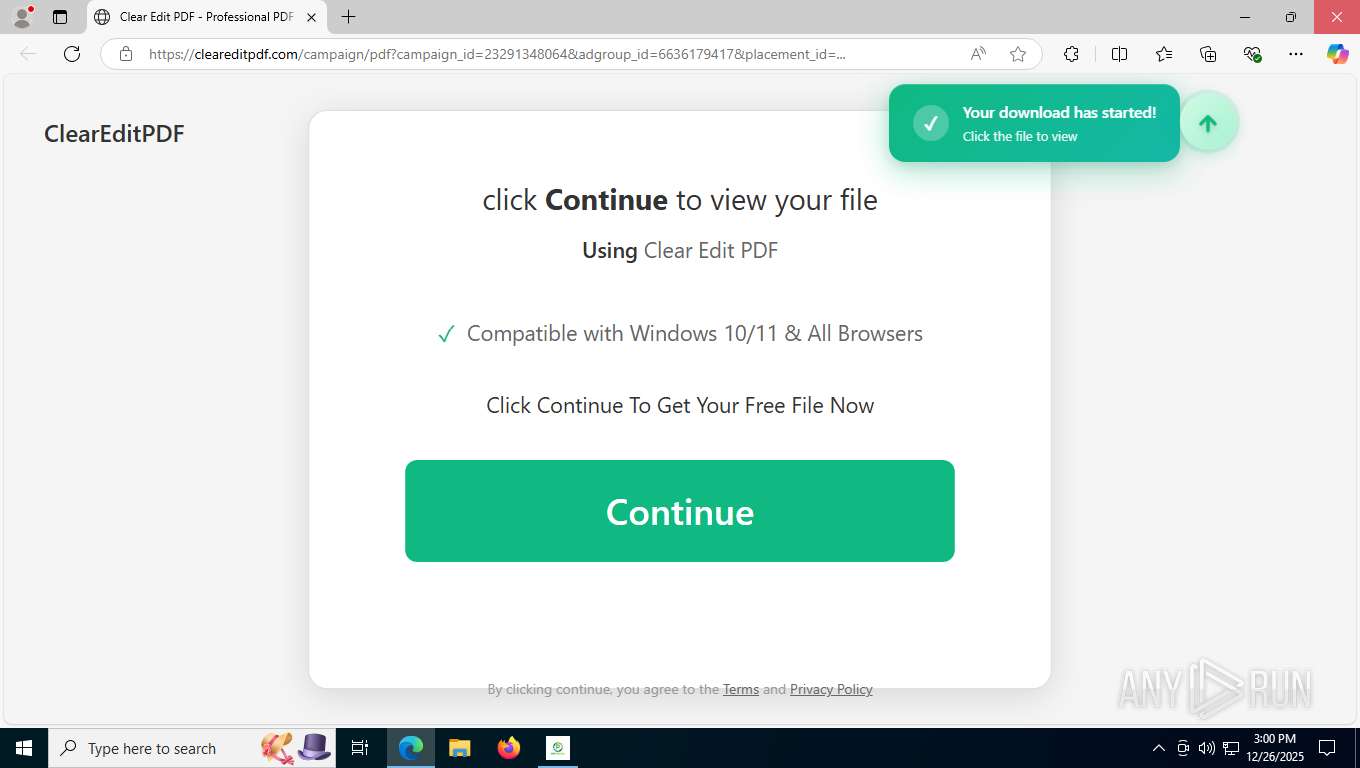
Launching a file from the Downloads directory
- msedge.exe (PID: 7580)
Reads Environment values
- identity_helper.exe (PID: 1388)
- PDF Proton.exe (PID: 2196)
- PDF Proton.exe (PID: 1600)
Create files in a temporary directory
- protonsetup.exe (PID: 4912)
- protonsetup.exe (PID: 1156)
- PDF Proton.exe (PID: 2196)
Reads the machine GUID from the registry
- protonsetup.exe (PID: 1156)
- PDF Proton.exe (PID: 2196)
Creates files or folders in the user directory
- protonsetup.exe (PID: 1156)
- PDF Proton.exe (PID: 2196)
- PDF Proton.exe (PID: 6544)
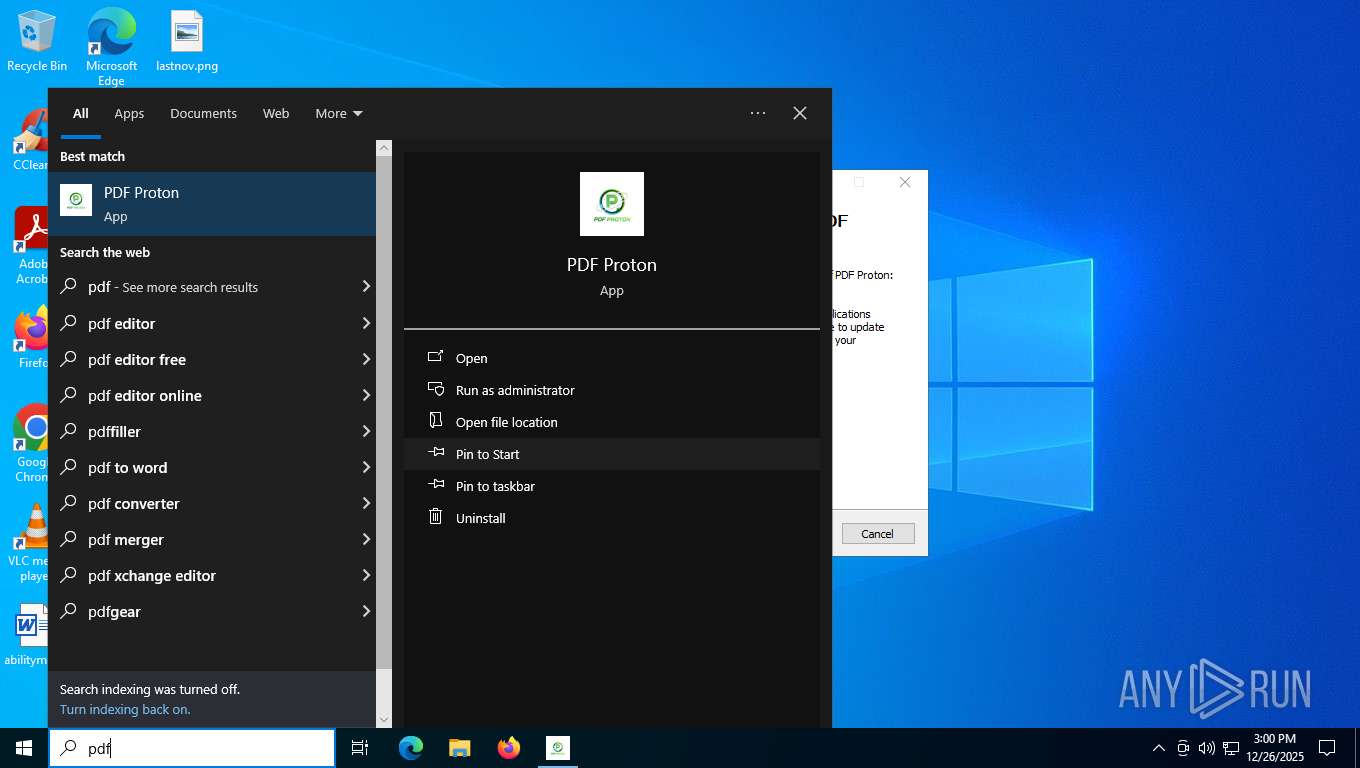
Manual execution by a user
- PDF Proton.exe (PID: 2196)
Checks proxy server information
- slui.exe (PID: 7404)
- PDF Proton.exe (PID: 2196)
Reads product name
- PDF Proton.exe (PID: 2196)
- PDF Proton.exe (PID: 1600)
Process checks computer location settings
- PDF Proton.exe (PID: 2196)
- PDF Proton.exe (PID: 1600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
186
Monitored processes
37
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 424 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 756 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5396,i,13730033266069311015,15414972490619055514,262144 --variations-seed-version --mojo-platform-channel-handle=7724 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 816 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6164,i,13730033266069311015,15414972490619055514,262144 --variations-seed-version --mojo-platform-channel-handle=1460 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1136 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6536,i,13730033266069311015,15414972490619055514,262144 --variations-seed-version --mojo-platform-channel-handle=5596 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
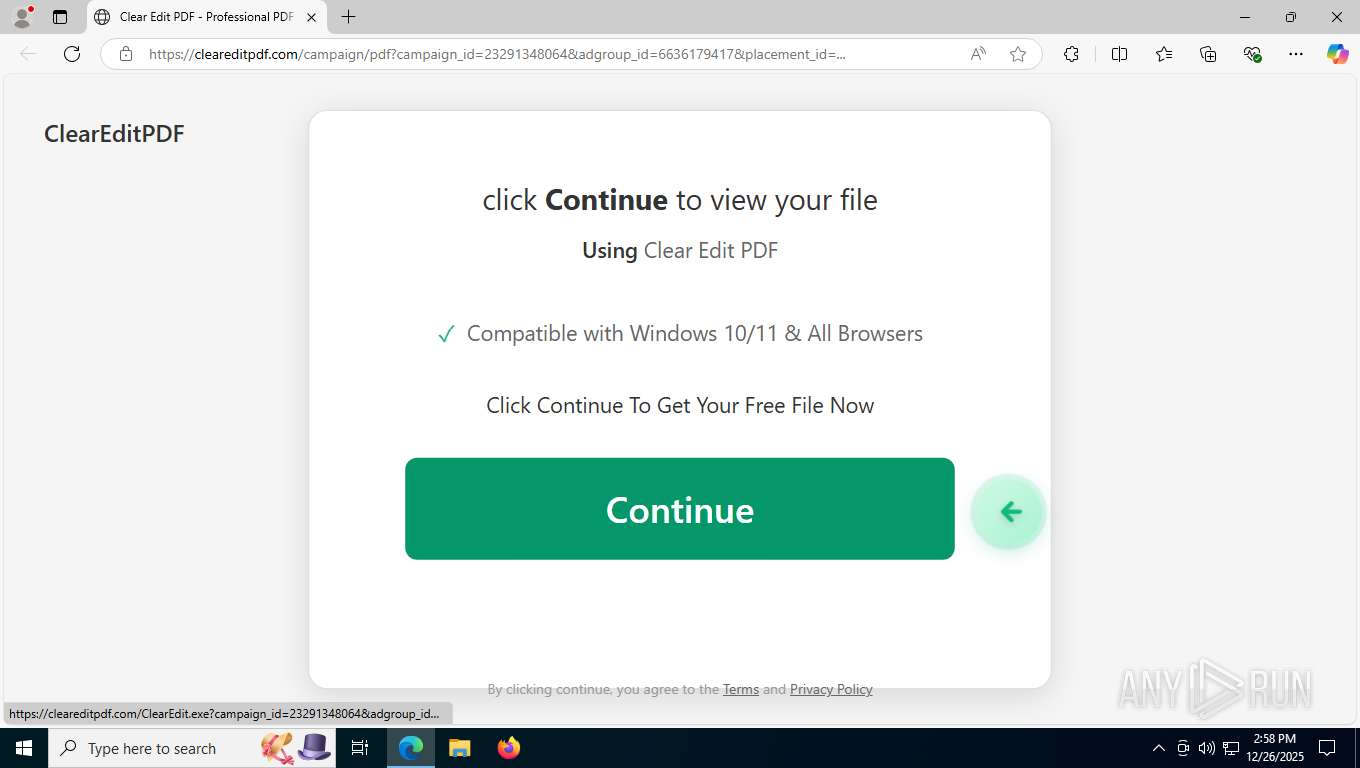
| 1156 | "C:\Users\admin\Downloads\protonsetup.exe" | C:\Users\admin\Downloads\protonsetup.exe | msedge.exe | ||||||||||||
User: admin Company: Hawk Integrated Inc Integrity Level: MEDIUM Description: PDF Proton Exit code: 0 Version: 2.0.0.1 Modules
| |||||||||||||||
| 1388 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6280,i,13730033266069311015,15414972490619055514,262144 --variations-seed-version --mojo-platform-channel-handle=6276 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1600 | "C:\Users\admin\AppData\Local\PDFProton\PDF Proton.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\pdf-proton-nativefier-72c1c6" --app-user-model-id=pdf-proton-nativefier-72c1c6 --app-path="C:\Users\admin\AppData\Local\PDFProton\resources\app" --no-sandbox --no-zygote --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2440 --field-trial-handle=1704,i,13367144001382261539,15864018184916392604,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Local\PDFProton\PDF Proton.exe | — | PDF Proton.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: MEDIUM Description: PDF Proton Version: 2.0.0.1 Modules
| |||||||||||||||
| 2196 | "C:\Users\admin\AppData\Local\PDFProton\PDF Proton.exe" | C:\Users\admin\AppData\Local\PDFProton\PDF Proton.exe | — | explorer.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: MEDIUM Description: PDF Proton Version: 2.0.0.1 Modules
| |||||||||||||||
| 2220 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5528,i,13730033266069311015,15414972490619055514,262144 --variations-seed-version --mojo-platform-channel-handle=7820 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3176 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7628,i,13730033266069311015,15414972490619055514,262144 --variations-seed-version --mojo-platform-channel-handle=7608 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
10 653
Read events
10 635
Write events
0
Delete events
18
Modification events
| (PID) Process: | (2196) PDF Proton.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en-US |
Value: | |||
| (PID) Process: | (2196) PDF Proton.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en |
Value: | |||
| (PID) Process: | (2196) PDF Proton.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | _Global_ |
Value: | |||
Executable files
18
Suspicious files
160
Text files
346
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfdfe7.TMP | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfdff7.TMP | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfdfe7.TMP | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFfe025.TMP | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFfe035.TMP | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfe006.TMP | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
140
TCP/UDP connections
91
DNS requests
77
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7916 | msedge.exe | GET | 204 | 18.66.102.14:443 | https://cleareditpdf.com/favicon.ico | unknown | — | — | unknown |
7916 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:9XTegAz5zgVFx3h-itmXKZZPA30I1czWJRRBMnE5PK8&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7916 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | unknown | text | 768 b | whitelisted |
7916 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 462 b | whitelisted |
7916 | msedge.exe | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | unknown | — | — | whitelisted |
7916 | msedge.exe | GET | 200 | 18.66.102.14:443 | https://cleareditpdf.com/static/css/main.63880ca1.css | unknown | — | 24.7 Kb | unknown |
7916 | msedge.exe | GET | 200 | 18.66.102.14:443 | https://cleareditpdf.com/campaign/pdf?campaign_id=23291348064&adgroup_id=6636179417&placement_id=... | unknown | html | 1.28 Kb | unknown |
7916 | msedge.exe | GET | 200 | 18.66.102.14:443 | https://cleareditpdf.com/static/js/main.90b8045f.js | unknown | text | 128 Kb | unknown |
7916 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | text | 25 b | whitelisted |
7916 | msedge.exe | GET | 200 | 2.16.204.149:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | unknown | text | 128 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
2452 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5788 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7916 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7916 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7916 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7916 | msedge.exe | 18.66.102.14:443 | cleareditpdf.com | AMAZON-02 | US | whitelisted |
7916 | msedge.exe | 104.18.22.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
cleareditpdf.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |