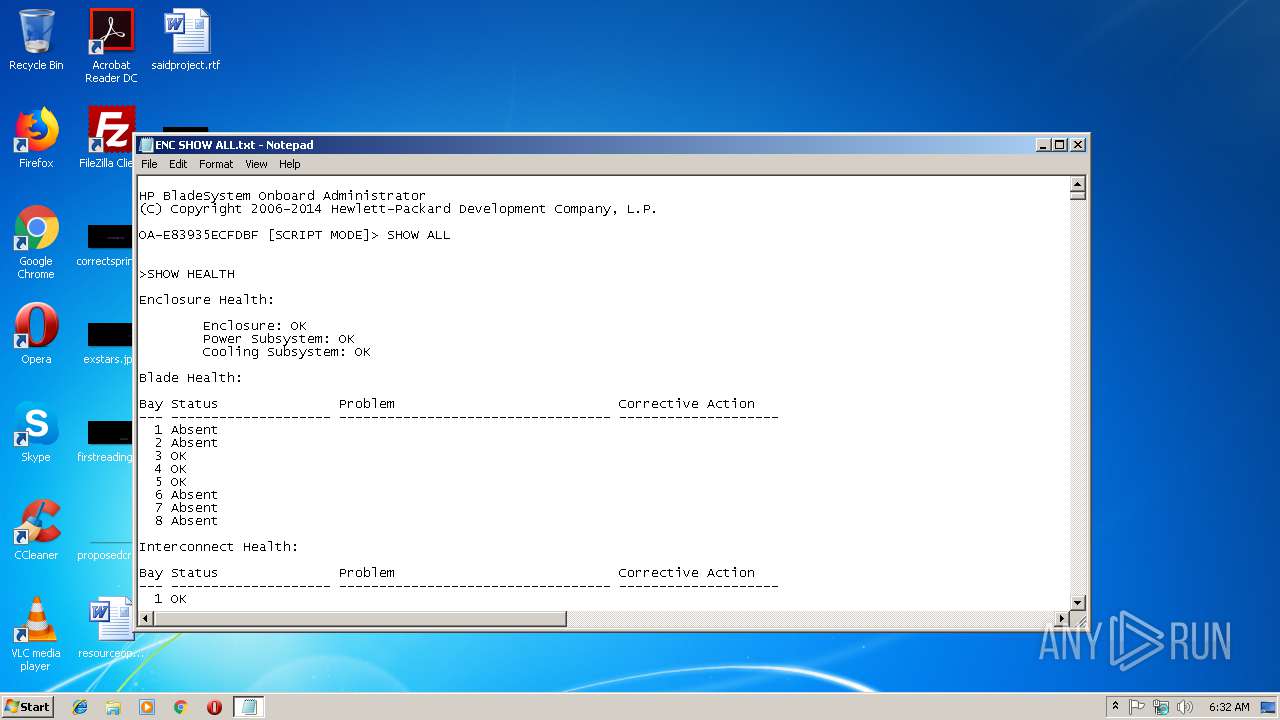
| File name: | ENC SHOW ALL.txt |
| Full analysis: | https://app.any.run/tasks/d72f89e9-d7d4-4114-9bb7-75170433d962 |
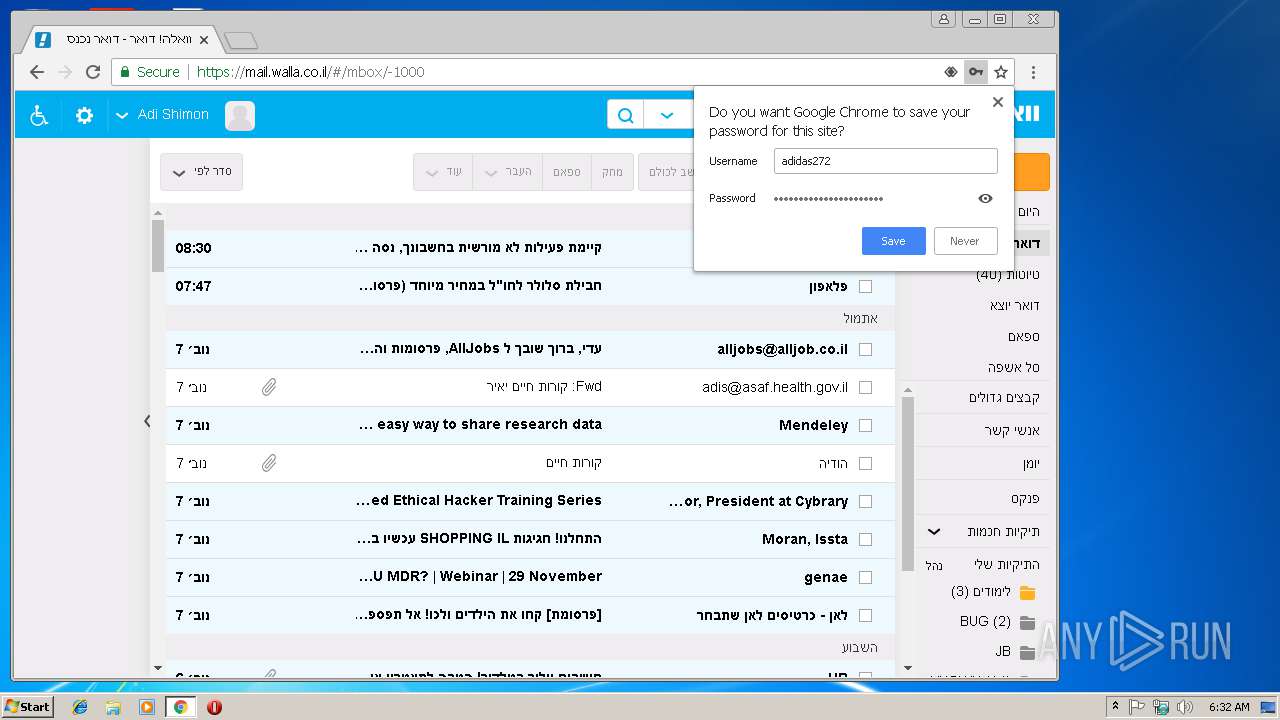
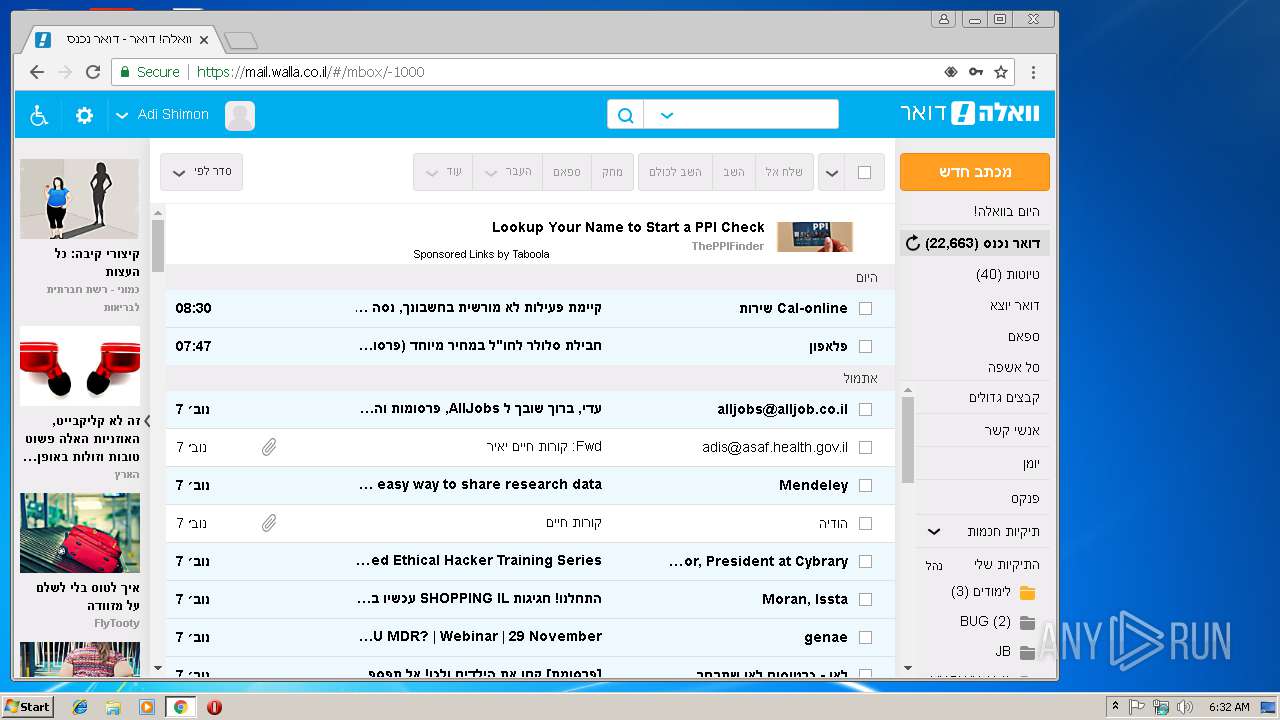
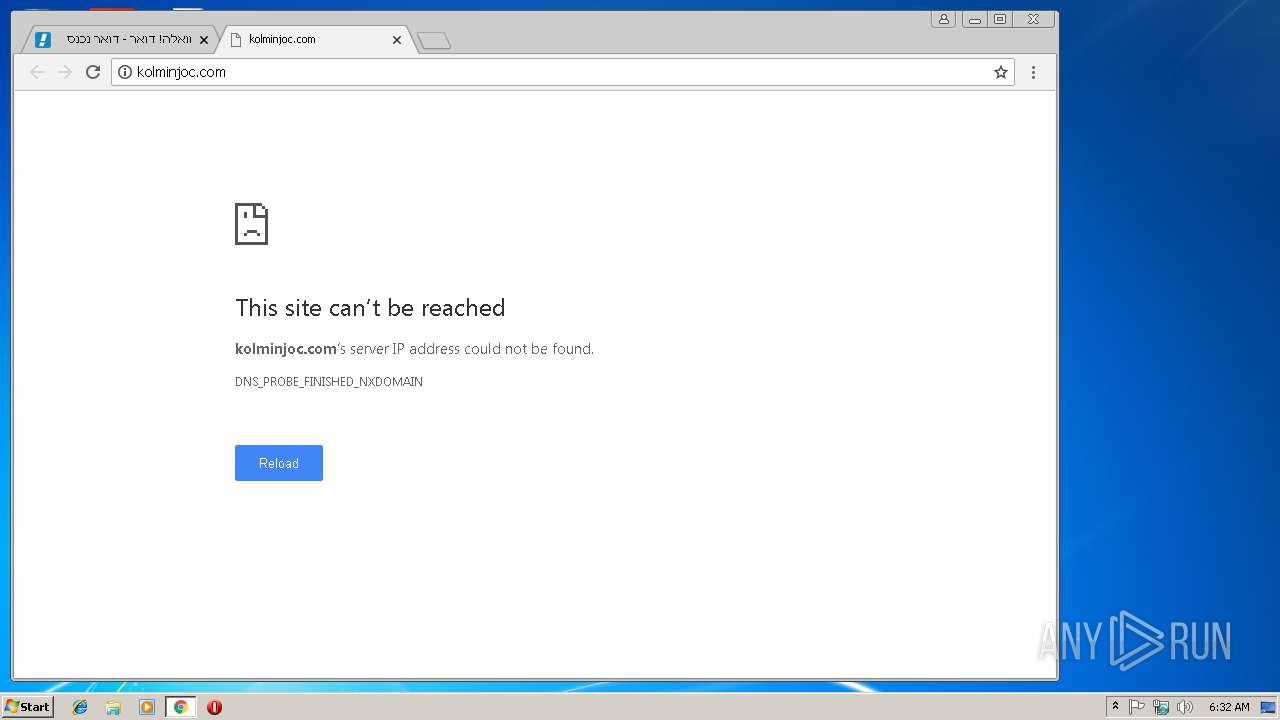
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2018, 06:31:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | AFCAE0D8B242394299C3BBCF51620BEF |
| SHA1: | E91FE00E8F03E8A23715E424678E93F6F0656DB4 |
| SHA256: | F818955BC27353E21D5E9AFA111847EA1B223D1C3426BD65AA3608ED68747495 |
| SSDEEP: | 6144:KBOIOXtC4Ho3FUThJaurswlh6iEFafXVs8AnOswHx8/qWETL0ZtXhUOZXjIK1M1U:jtsjIK1M161S14CnIymE6F0A |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
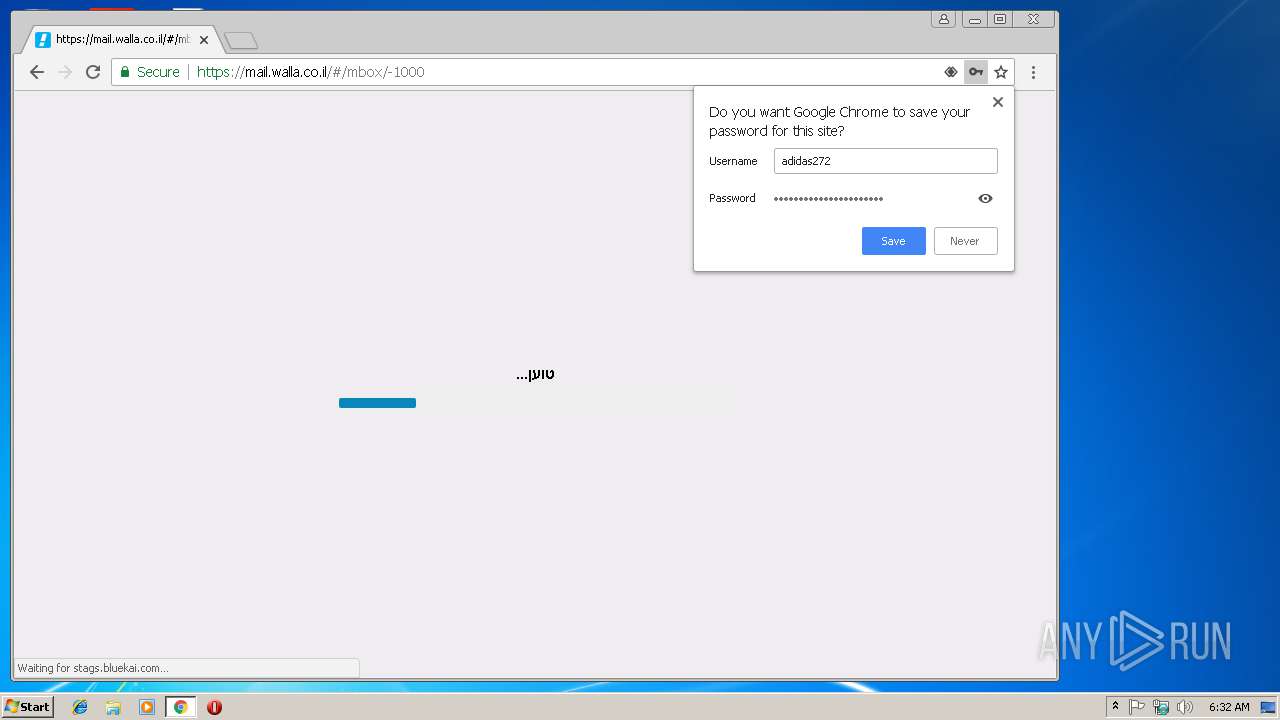
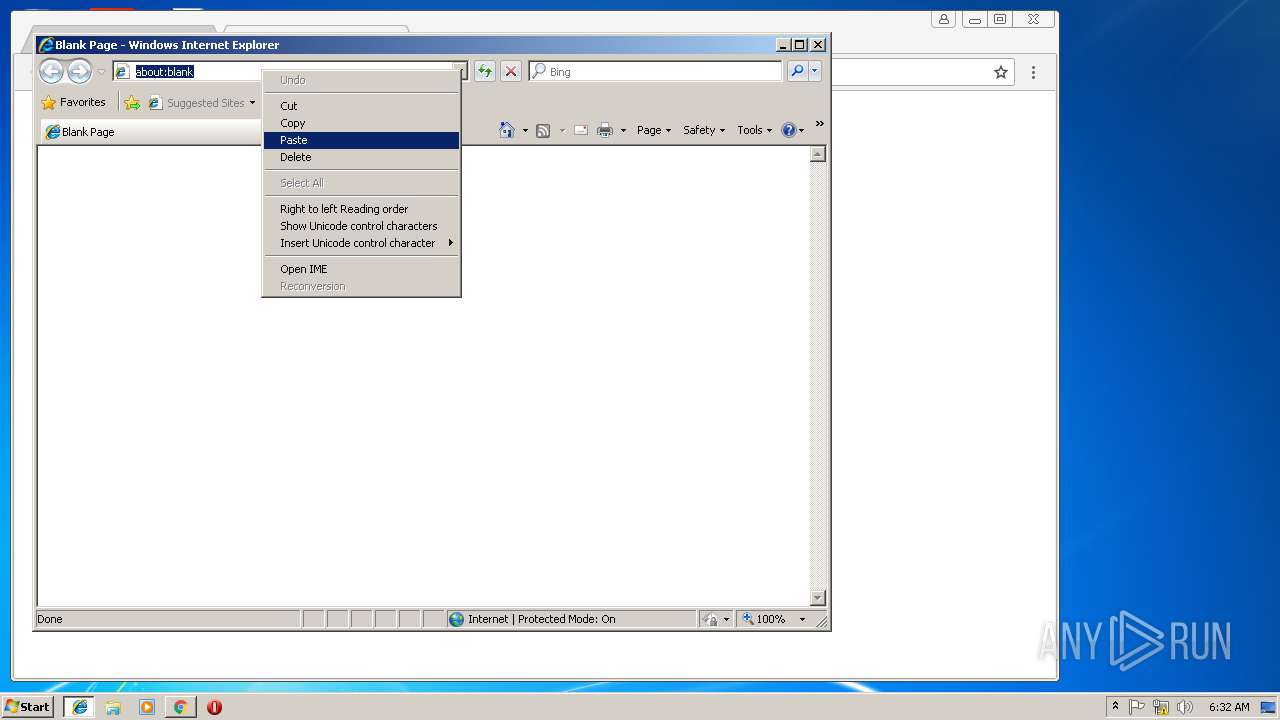
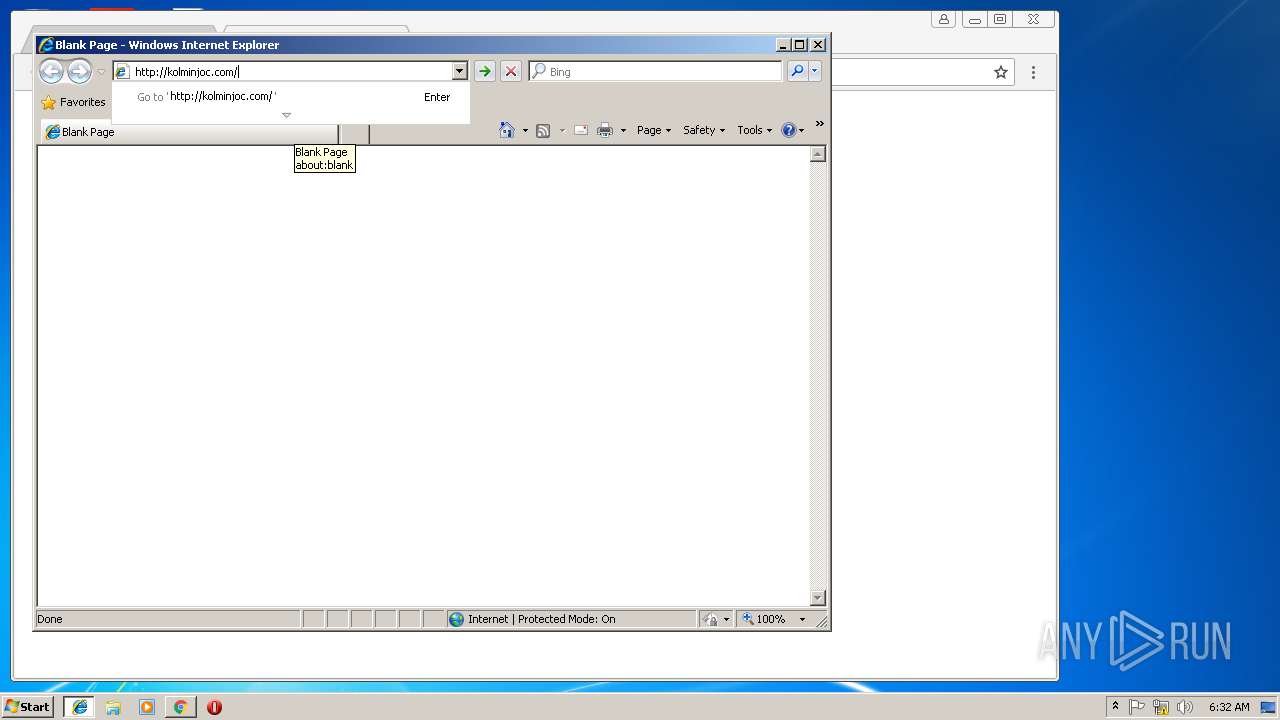
Changes internet zones settings
- iexplore.exe (PID: 1624)
Application launched itself
- chrome.exe (PID: 1448)
Reads Internet Cache Settings
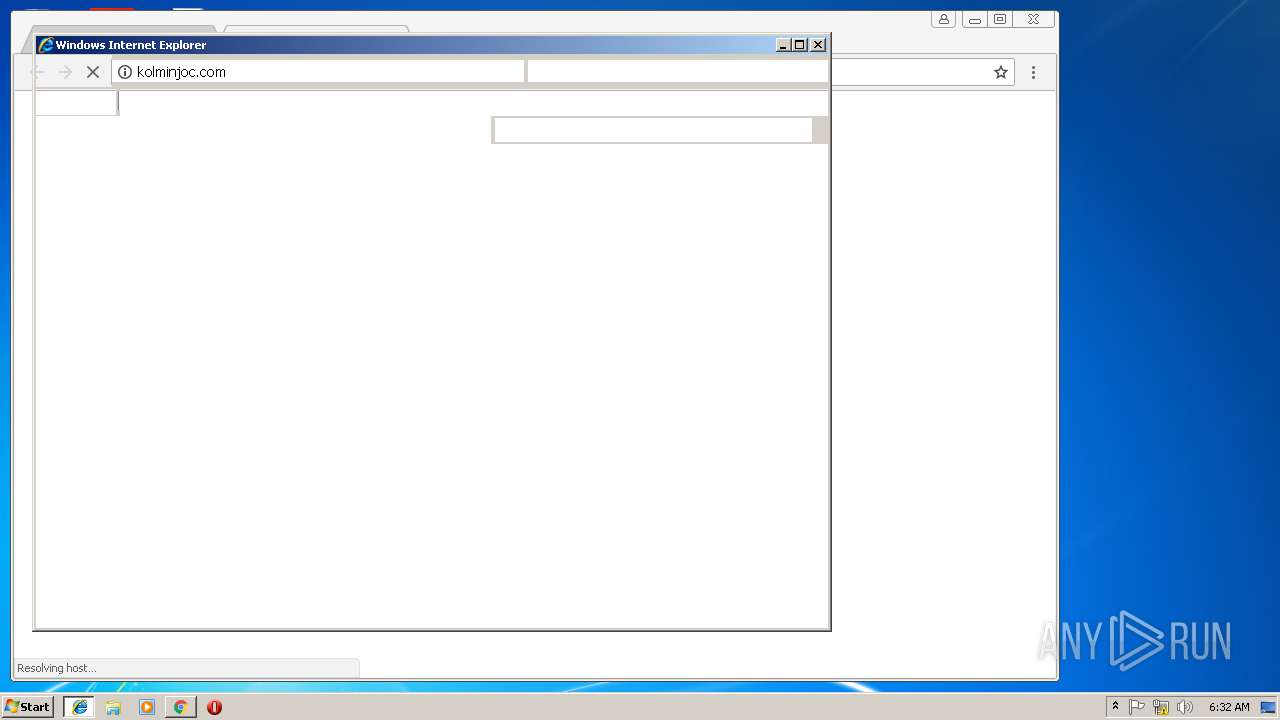
- iexplore.exe (PID: 3636)
Reads settings of System Certificates
- chrome.exe (PID: 1448)
Reads internet explorer settings
- iexplore.exe (PID: 3636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=932,17338208811397356374,11730050073046417664,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=06CB88625067A9F1A83845D4D248DA6F --mojo-platform-channel-handle=3944 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=932,17338208811397356374,11730050073046417664,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=4EA692E19D0D944C1B67854C3505F3C2 --mojo-platform-channel-handle=984 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,17338208811397356374,11730050073046417664,131072 --enable-features=PasswordImport --service-pipe-token=B1B083CFBD02761D6A0CEDAFD838175E --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B1B083CFBD02761D6A0CEDAFD838175E --renderer-client-id=5 --mojo-platform-channel-handle=1920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
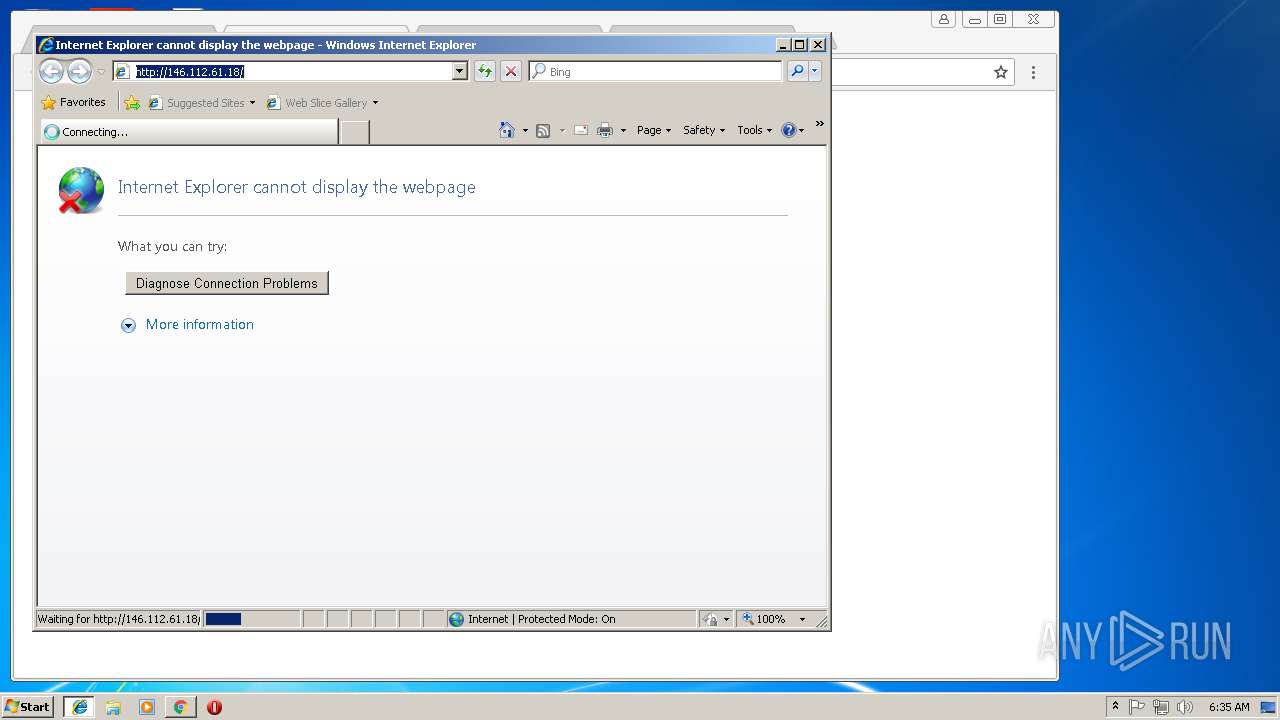
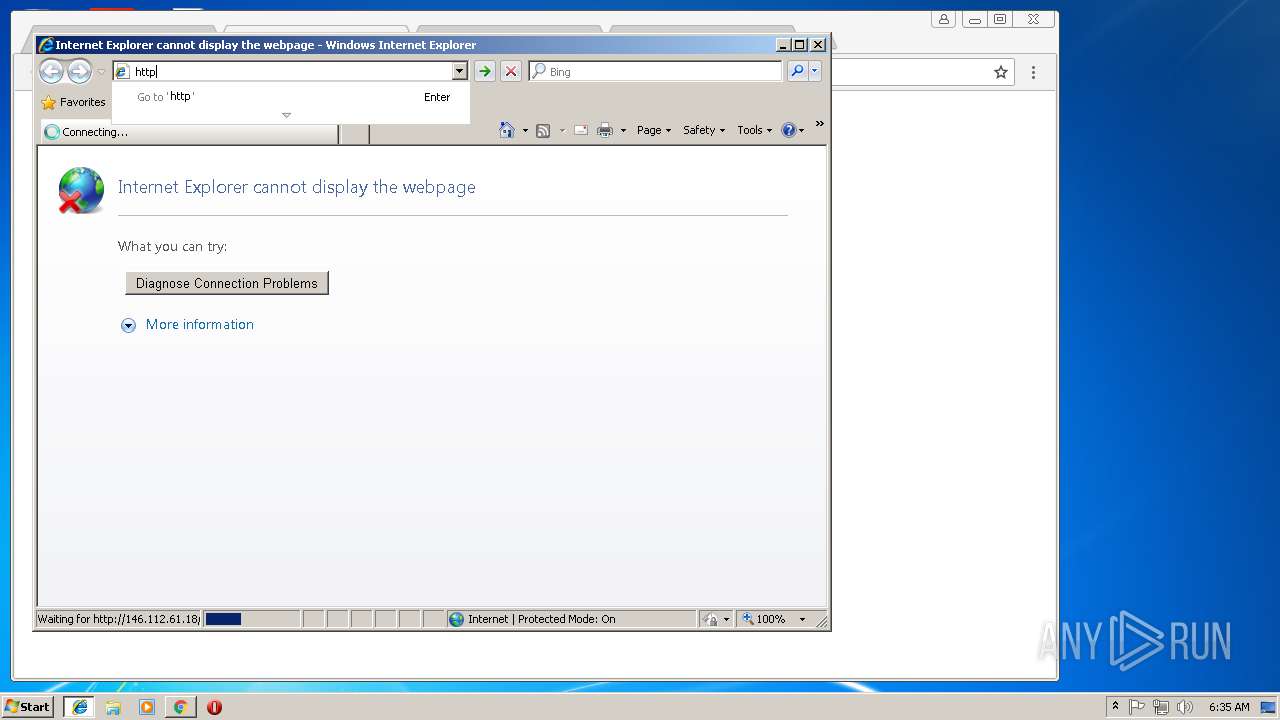
| 1624 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,17338208811397356374,11730050073046417664,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=19A136C6A4499009A69BB1131E056B4F --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=19A136C6A4499009A69BB1131E056B4F --renderer-client-id=18 --mojo-platform-channel-handle=1720 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,17338208811397356374,11730050073046417664,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=0CF1DCE91BD5B6CC50281AA28E9D45FE --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0CF1DCE91BD5B6CC50281AA28E9D45FE --renderer-client-id=15 --mojo-platform-channel-handle=3724 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,17338208811397356374,11730050073046417664,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=EFB3E8853158D628E26F777D58705893 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=EFB3E8853158D628E26F777D58705893 --renderer-client-id=16 --mojo-platform-channel-handle=4060 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,17338208811397356374,11730050073046417664,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=B2A0F50629779CDD9BAEADDFF14F9542 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B2A0F50629779CDD9BAEADDFF14F9542 --renderer-client-id=6 --mojo-platform-channel-handle=3564 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,17338208811397356374,11730050073046417664,131072 --enable-features=PasswordImport --service-pipe-token=998252402A53E7CCA8B6A223D8D867ED --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=998252402A53E7CCA8B6A223D8D867ED --renderer-client-id=3 --mojo-platform-channel-handle=2040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
976
Read events
837
Write events
135
Delete events
4
Modification events
| (PID) Process: | (3192) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 132 | |||
| (PID) Process: | (3192) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 132 | |||
| (PID) Process: | (3192) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (3192) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
| (PID) Process: | (1448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1448-13186132330878125 |
Value: 259 | |||
| (PID) Process: | (1448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
Executable files
0
Suspicious files
113
Text files
177
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\116ed8bd-6fa8-433a-805d-b4f83c6bb64f.tmp | — | |
MD5:— | SHA256:— | |||
| 1448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6a32b6c7-2c2b-4c90-8b44-39162af9584d.tmp | — | |
MD5:— | SHA256:— | |||
| 1448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF185b69.TMP | text | |
MD5:— | SHA256:— | |||
| 1448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 1448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF185b88.TMP | text | |
MD5:— | SHA256:— | |||
| 1448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
140
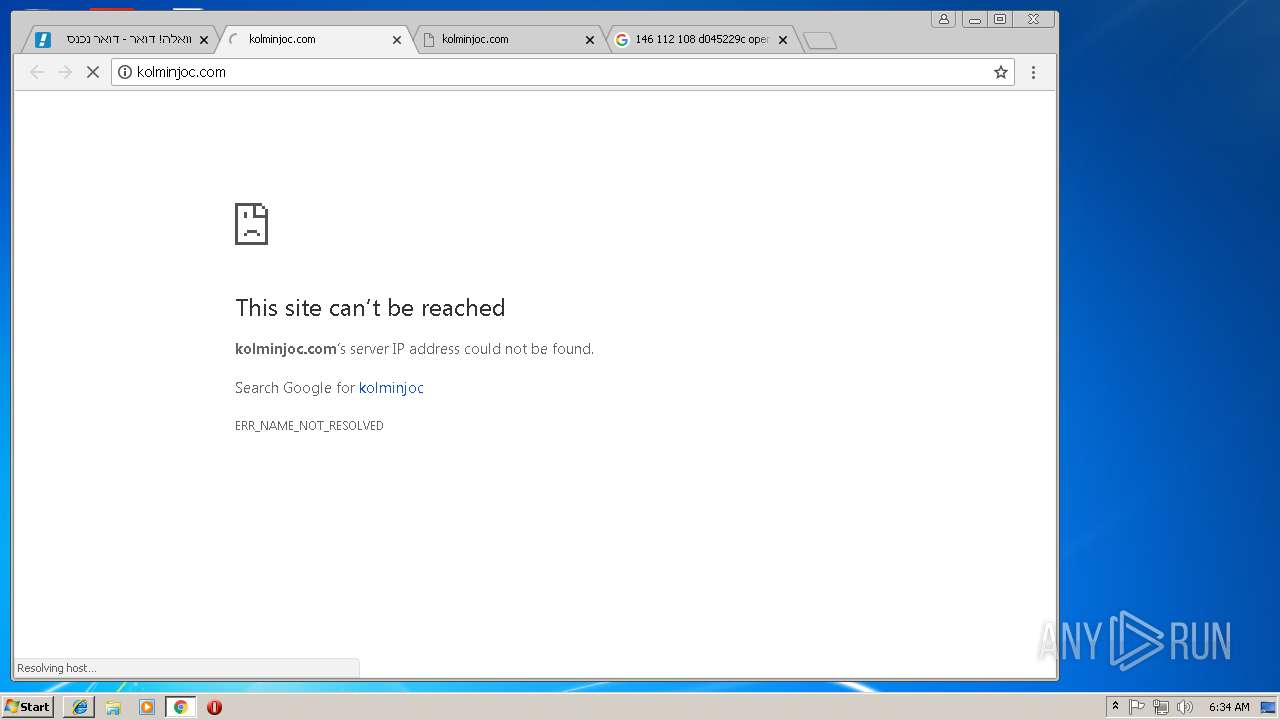
DNS requests
124
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
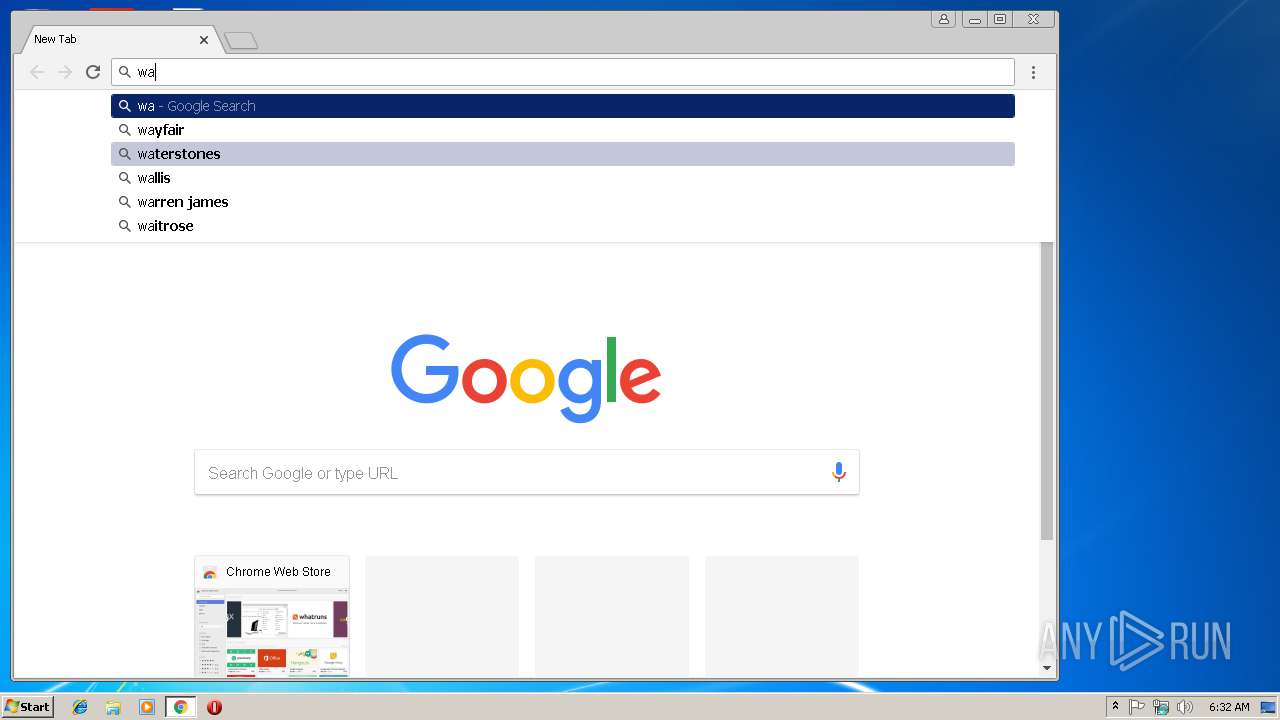
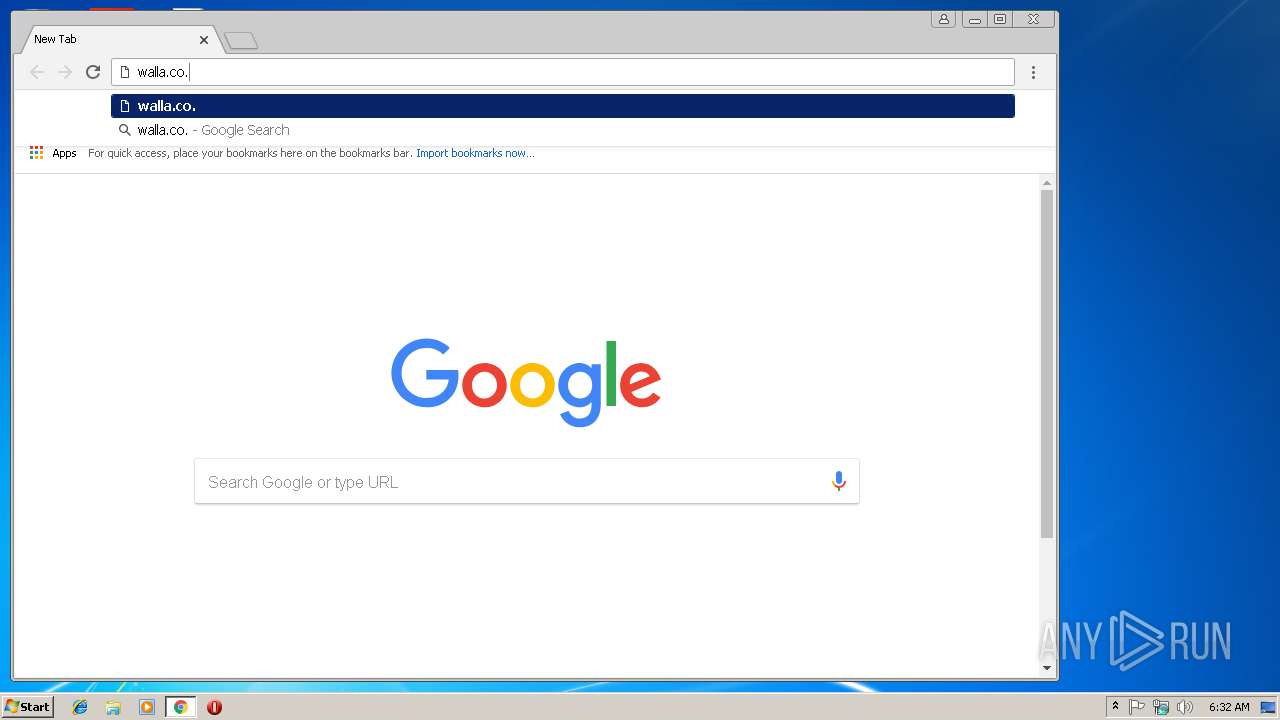
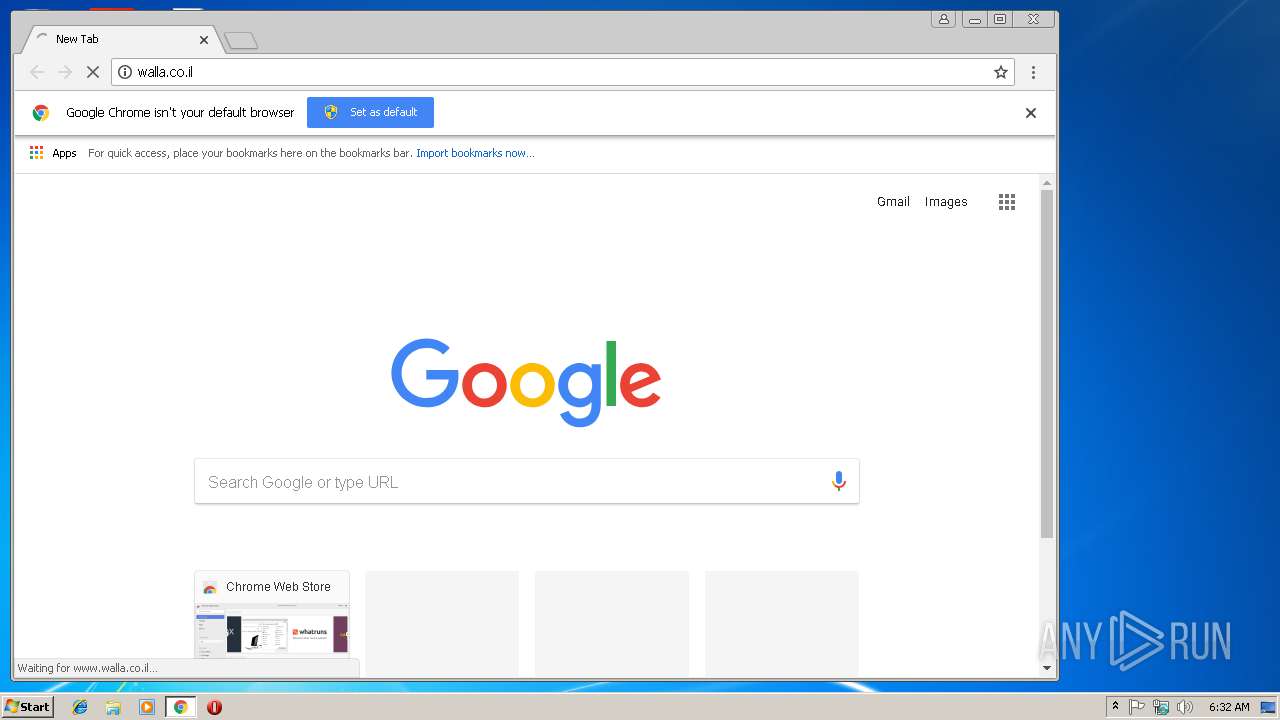
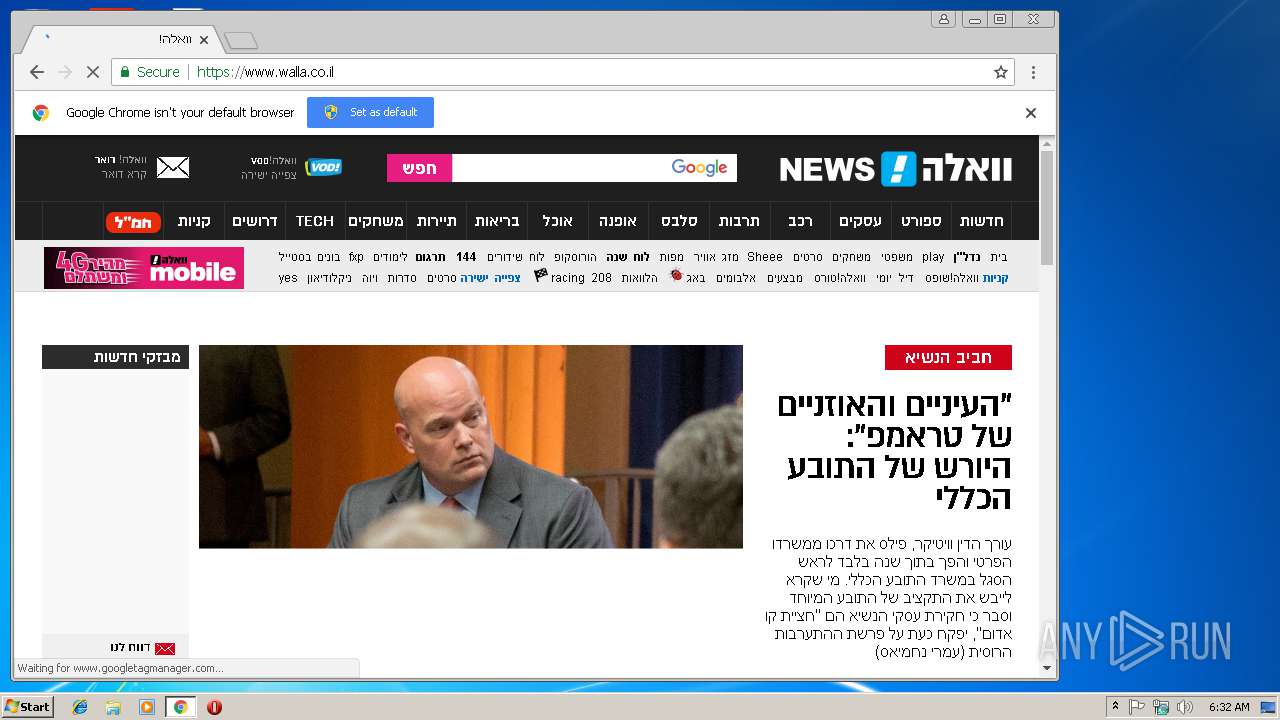
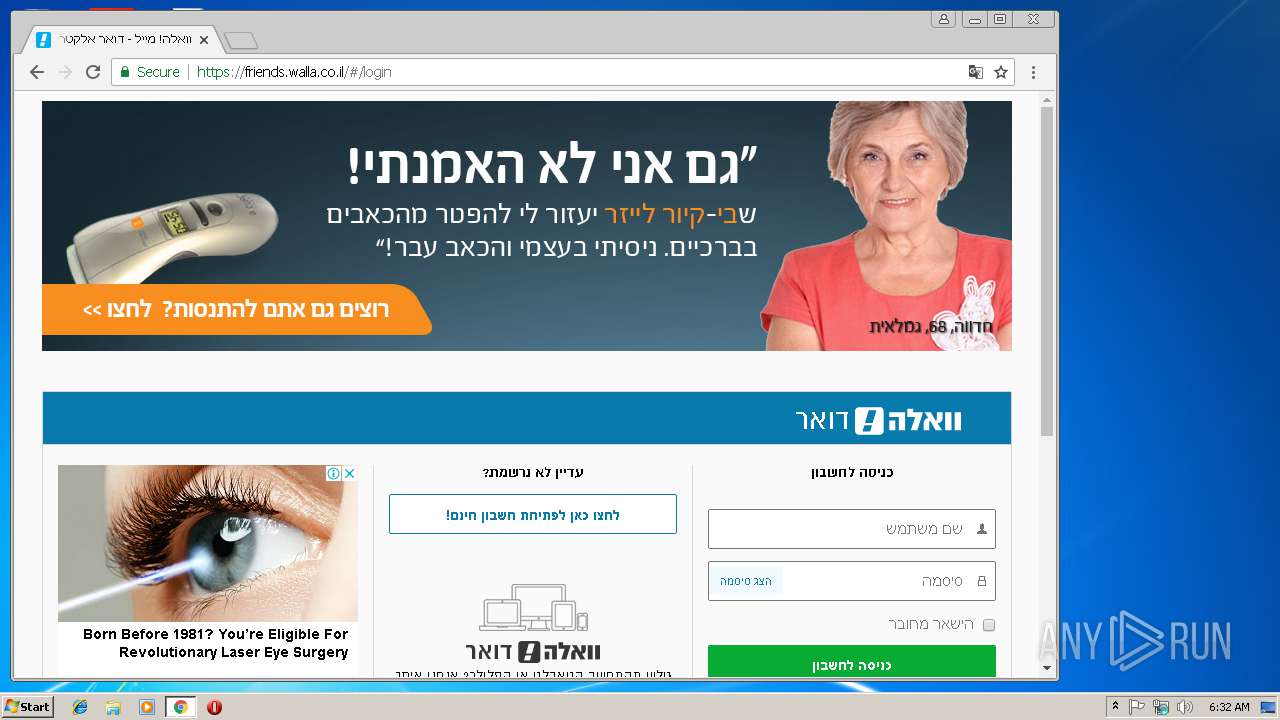
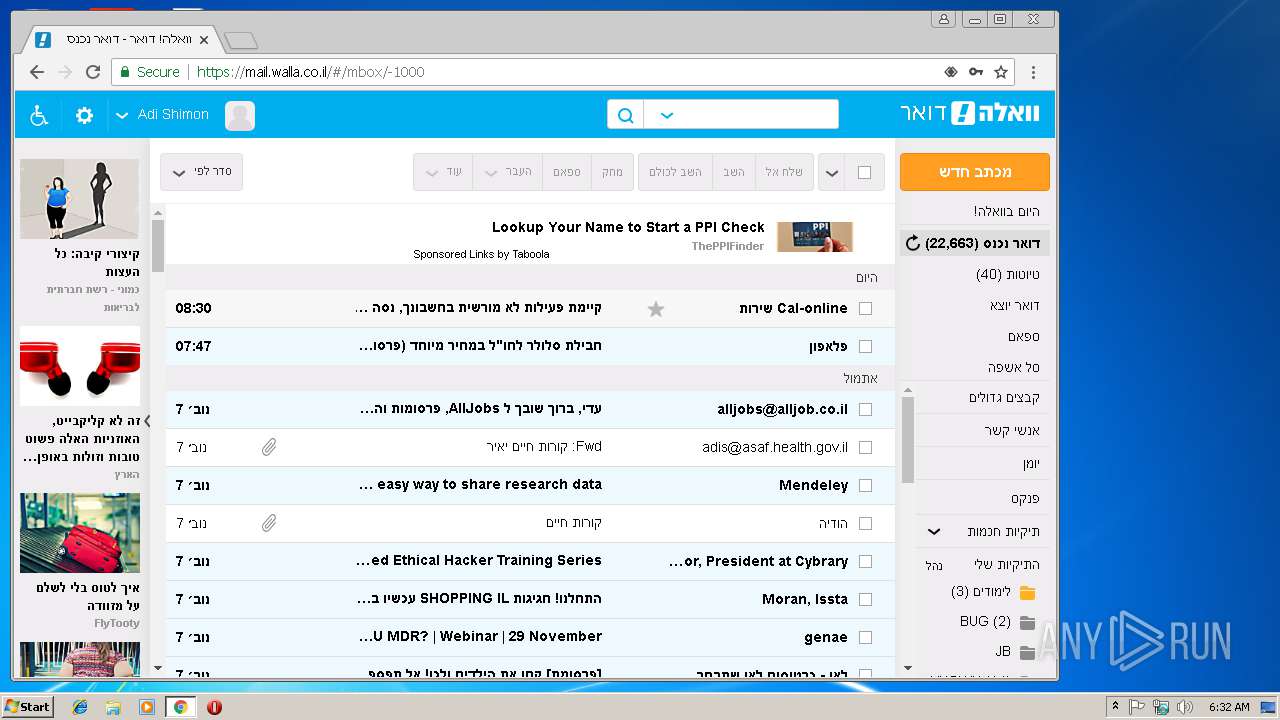
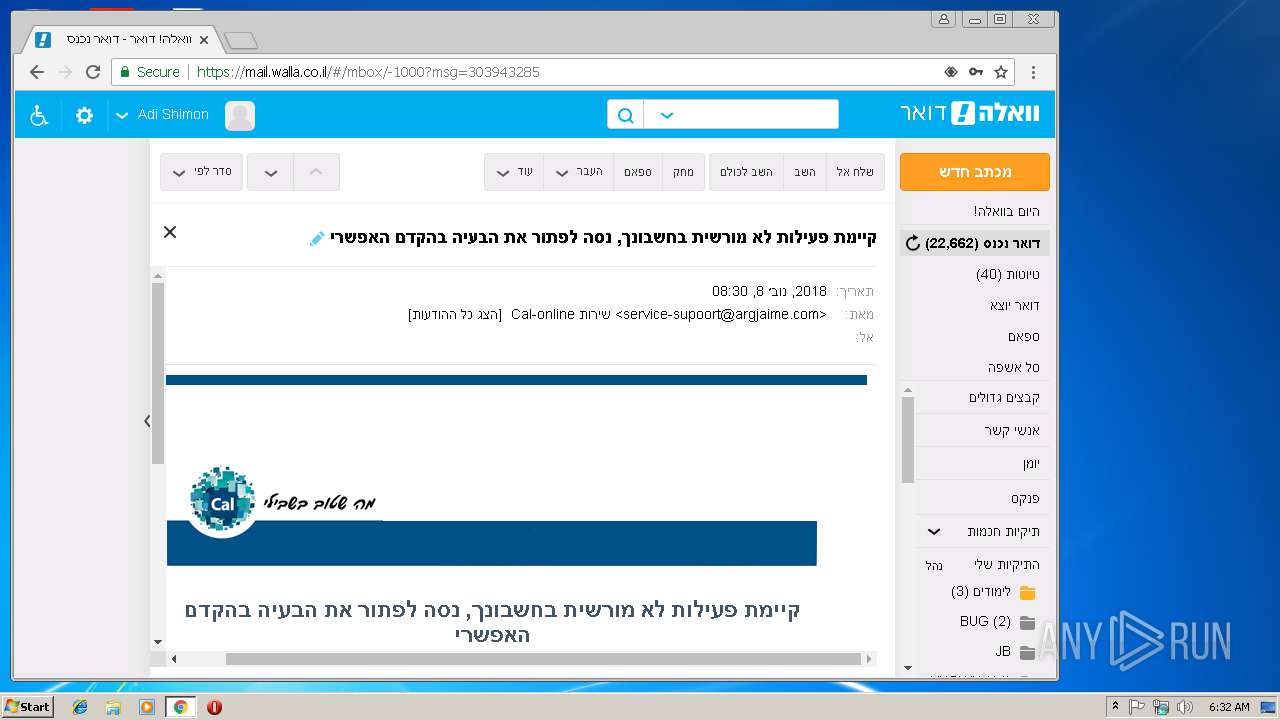
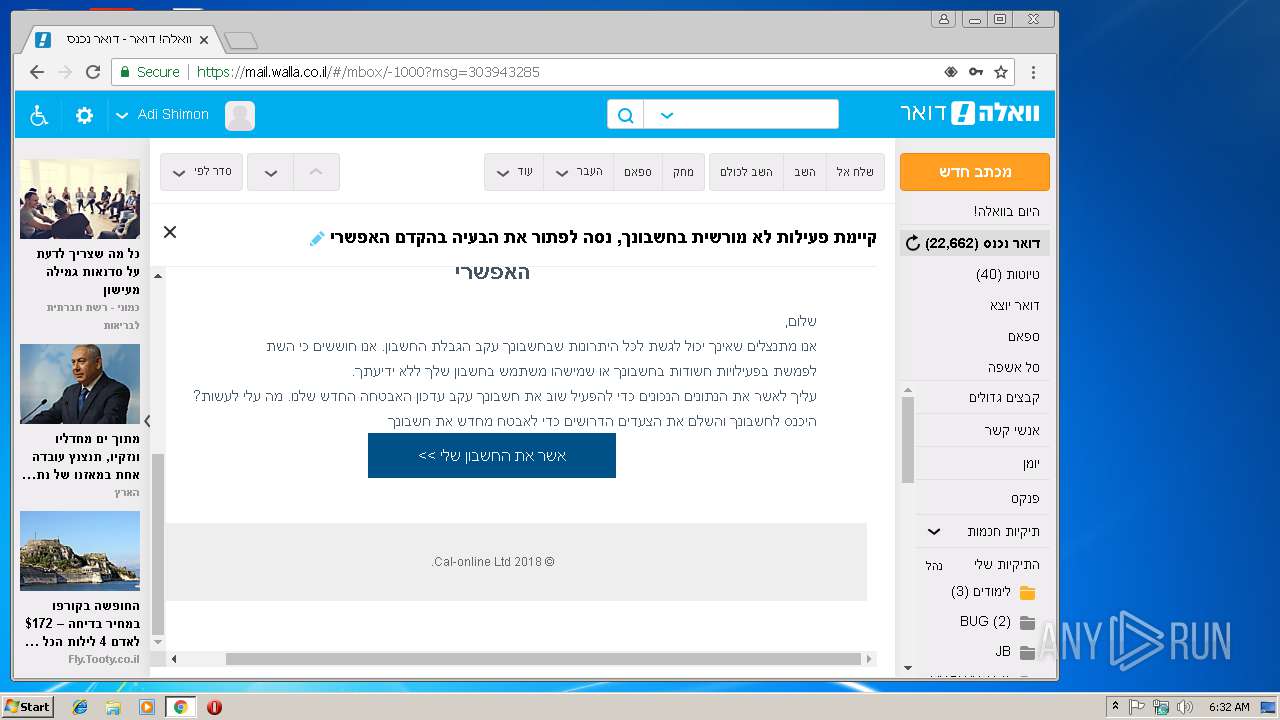
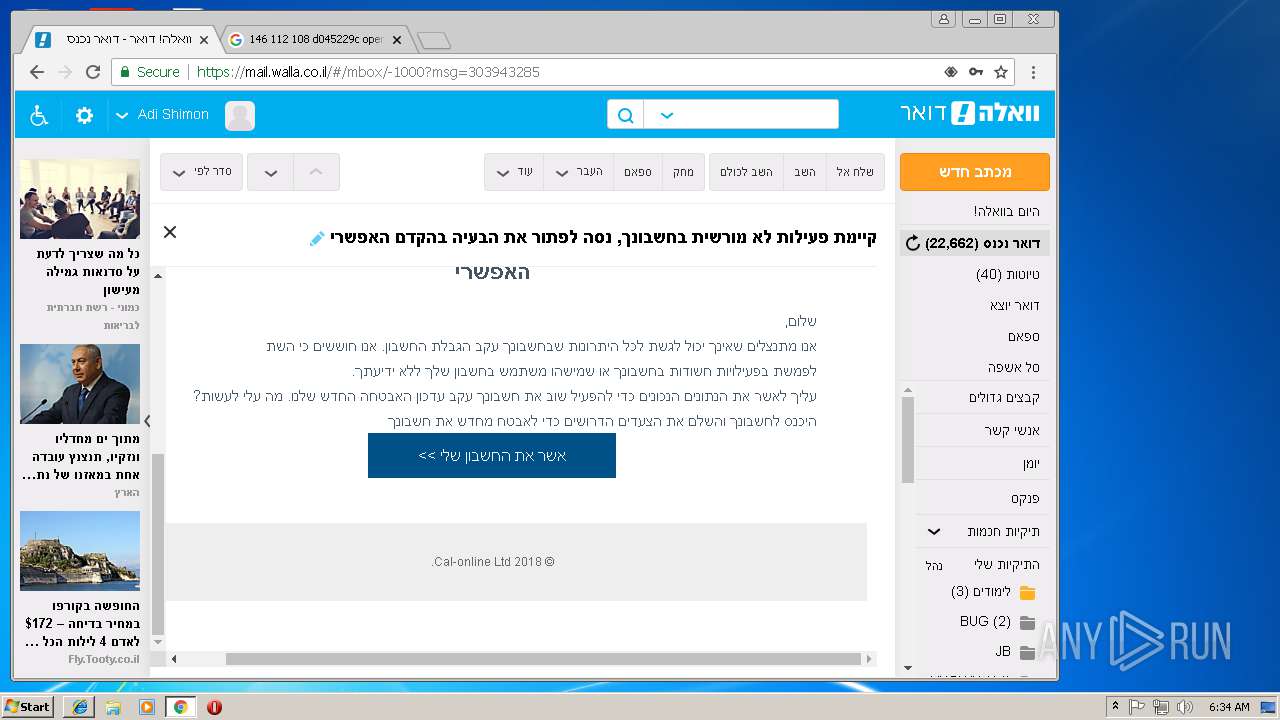
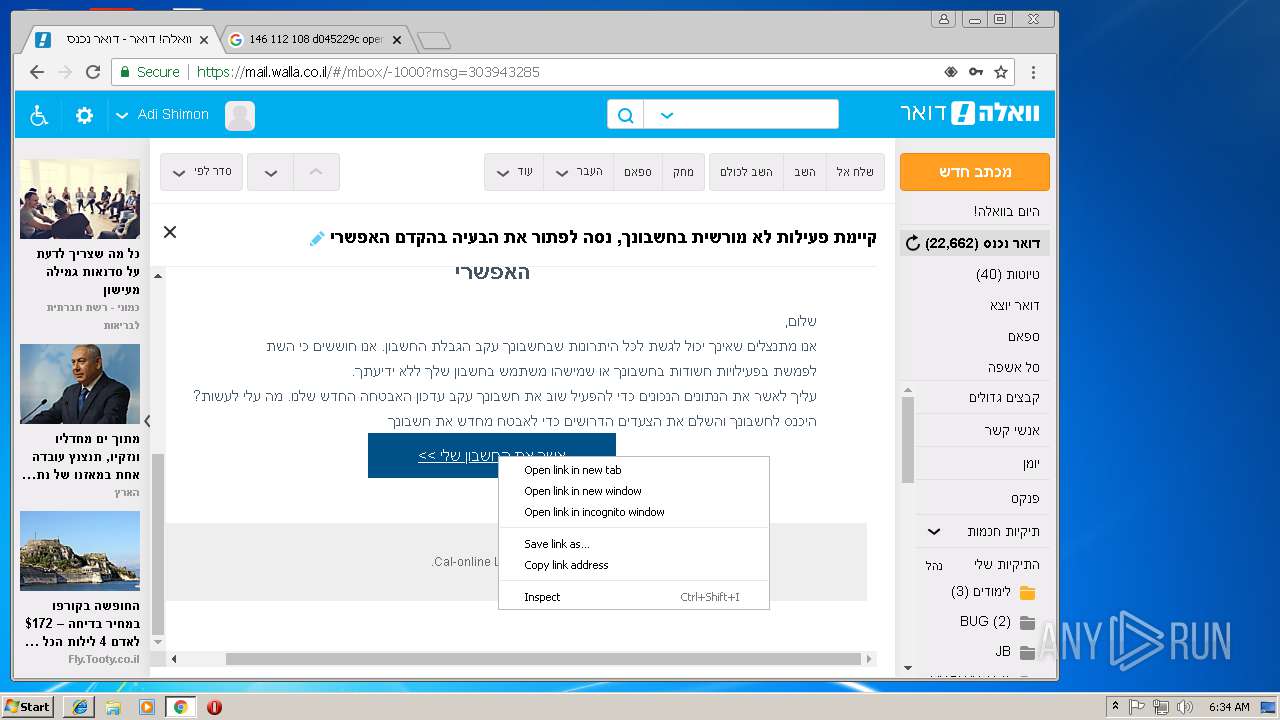
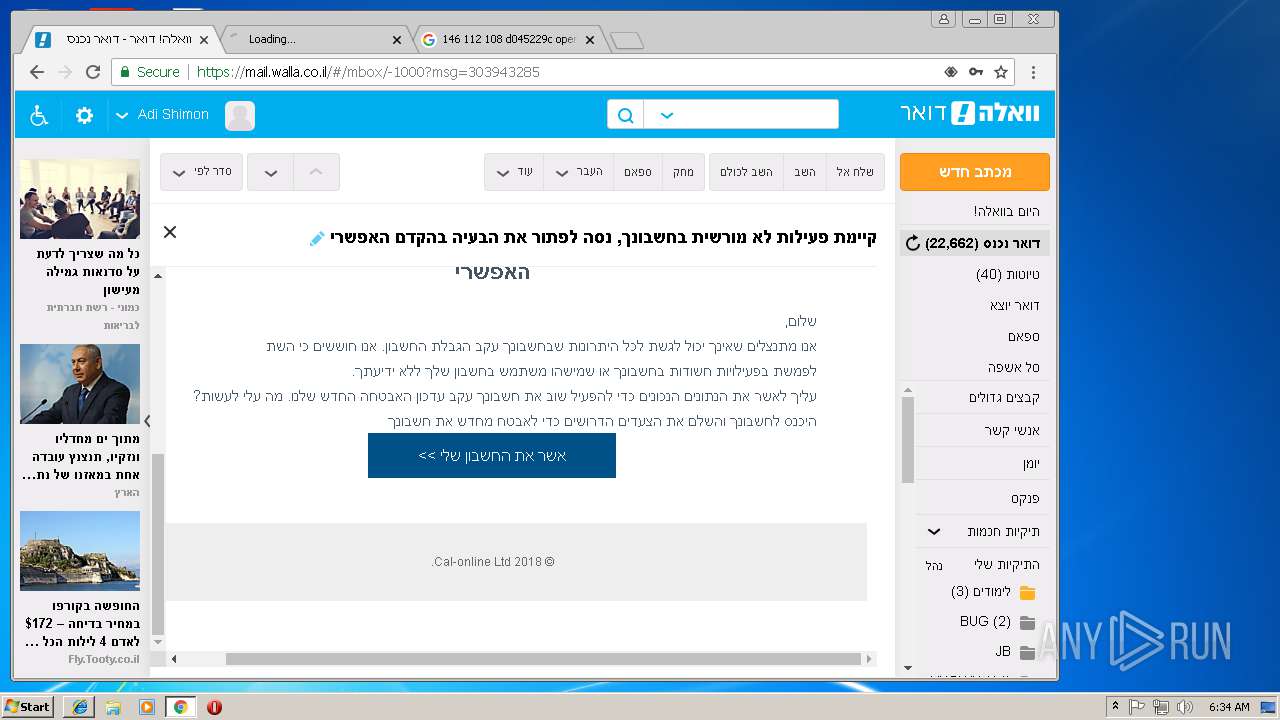
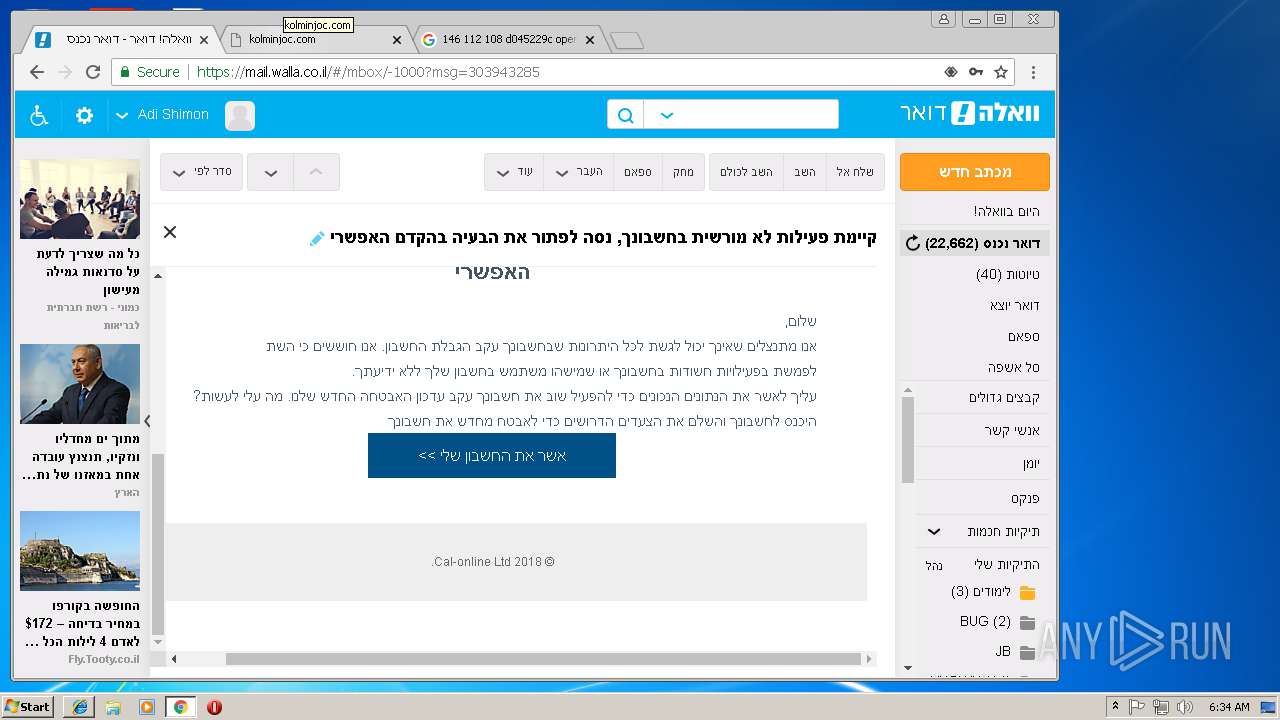
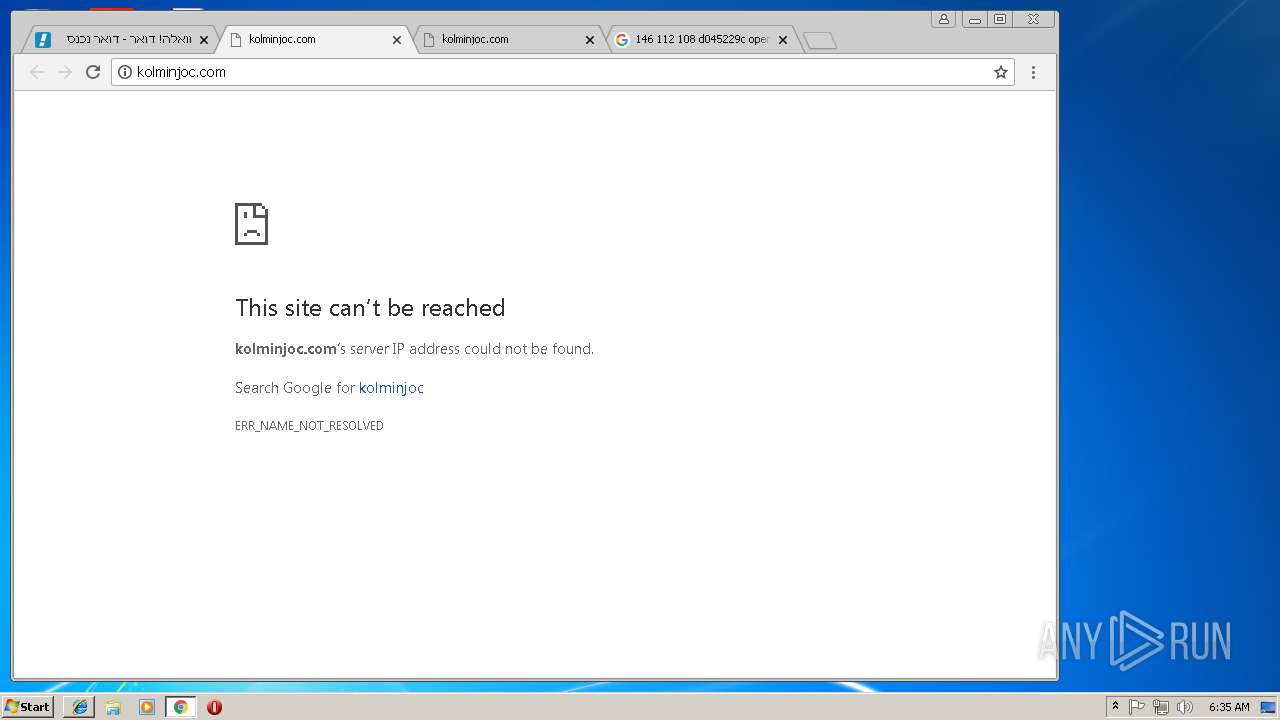
1448 | chrome.exe | GET | 301 | 2.18.234.79:80 | http://www.walla.co.il/ | unknown | — | — | whitelisted |
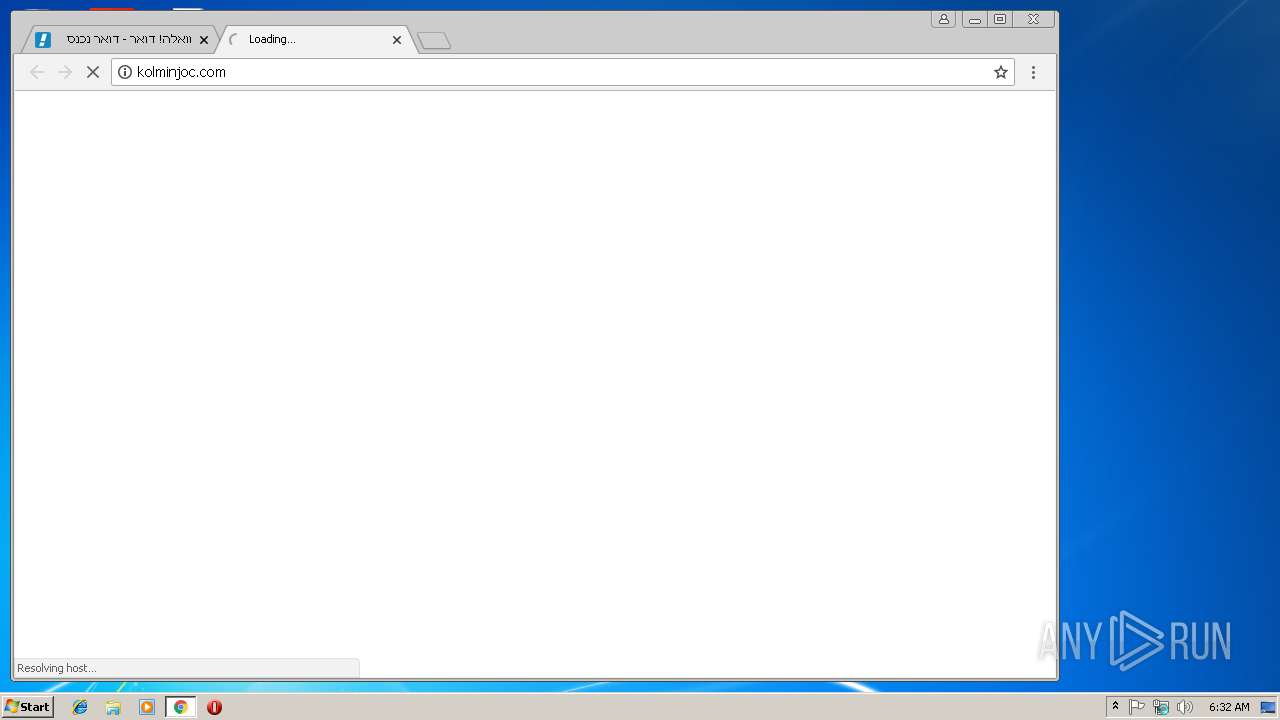
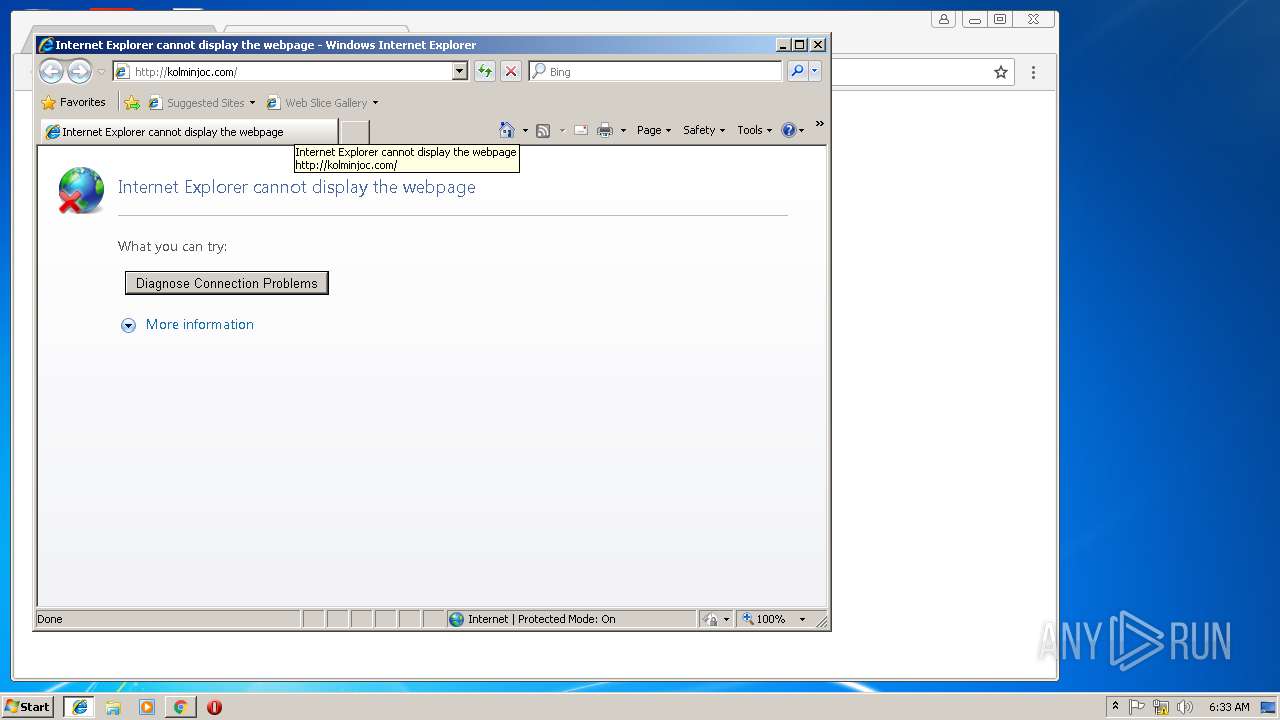
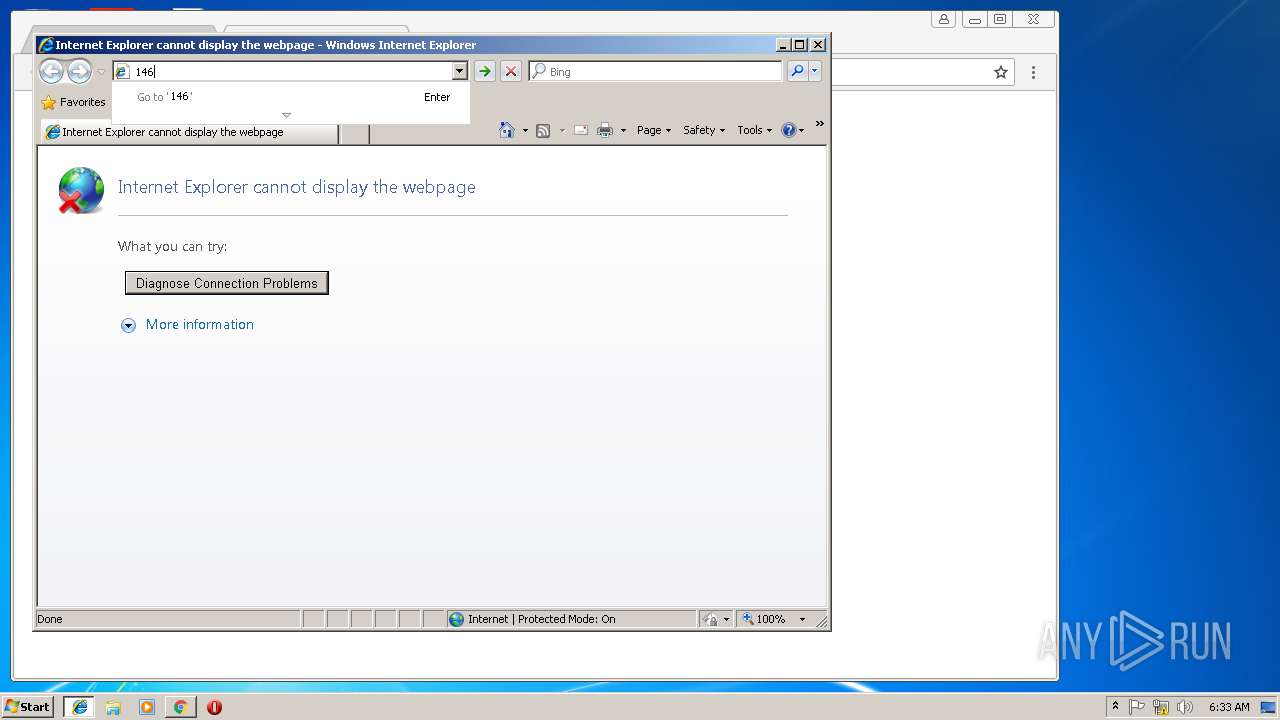
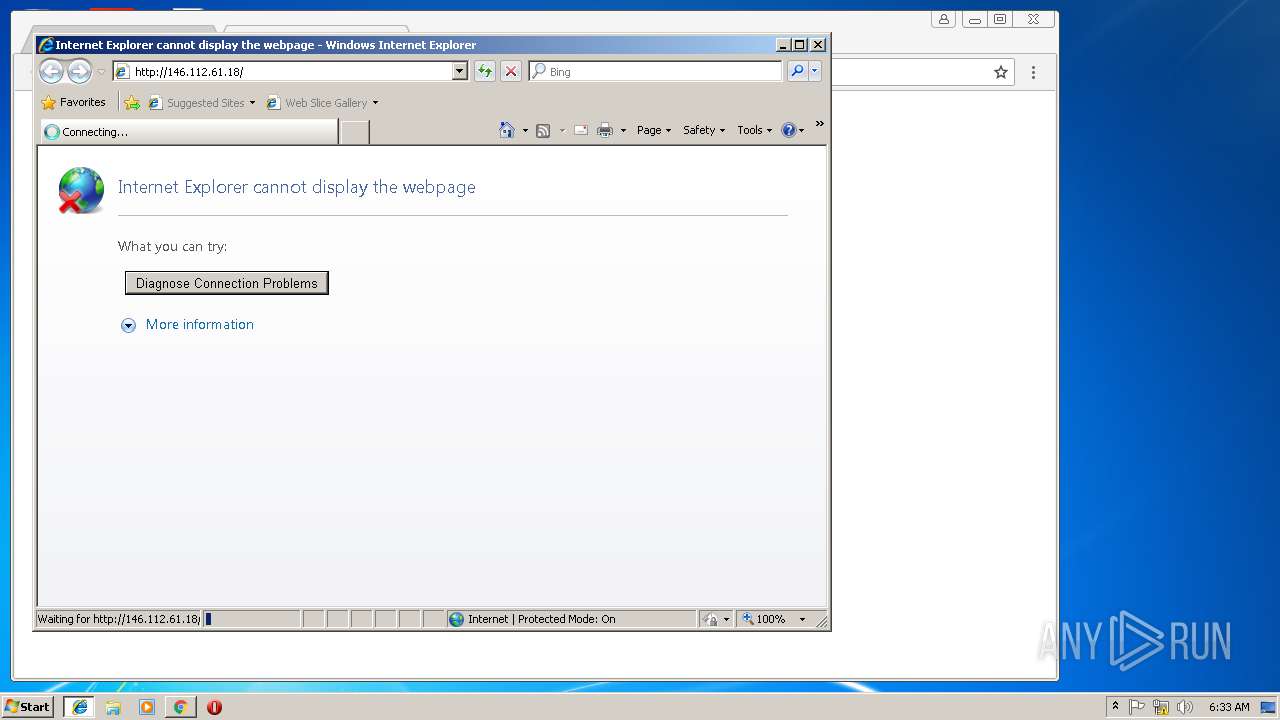
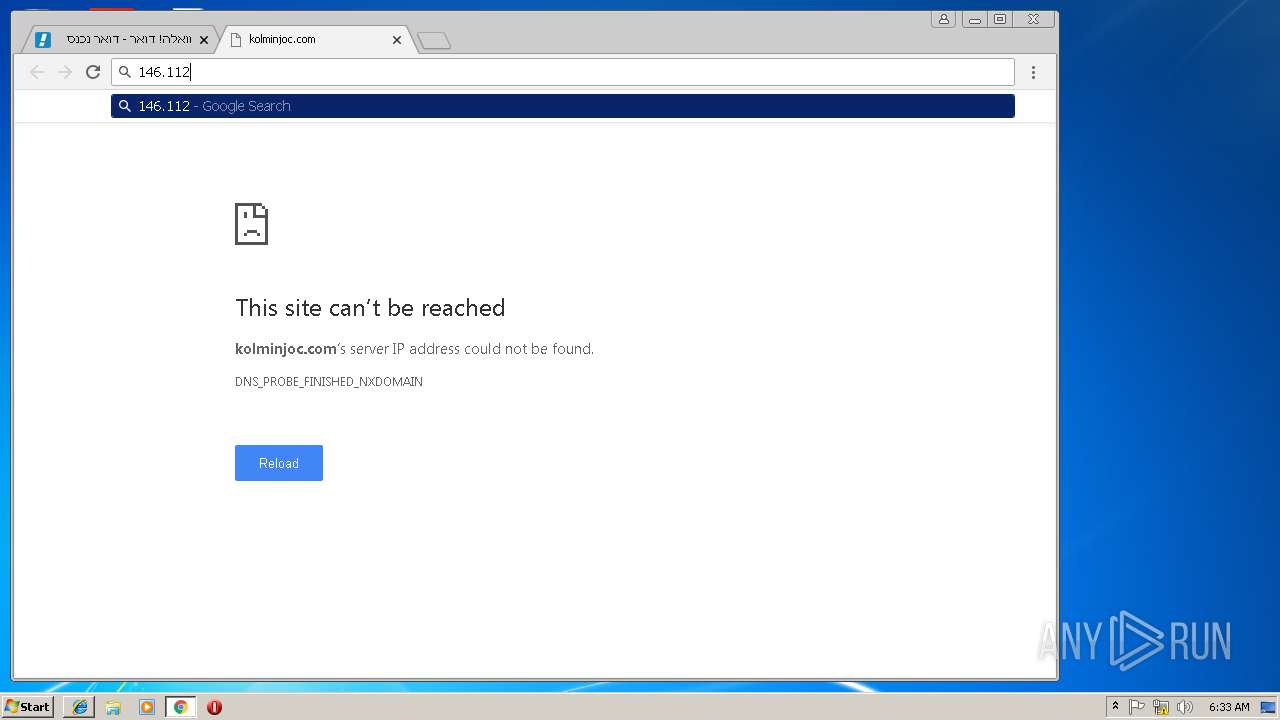
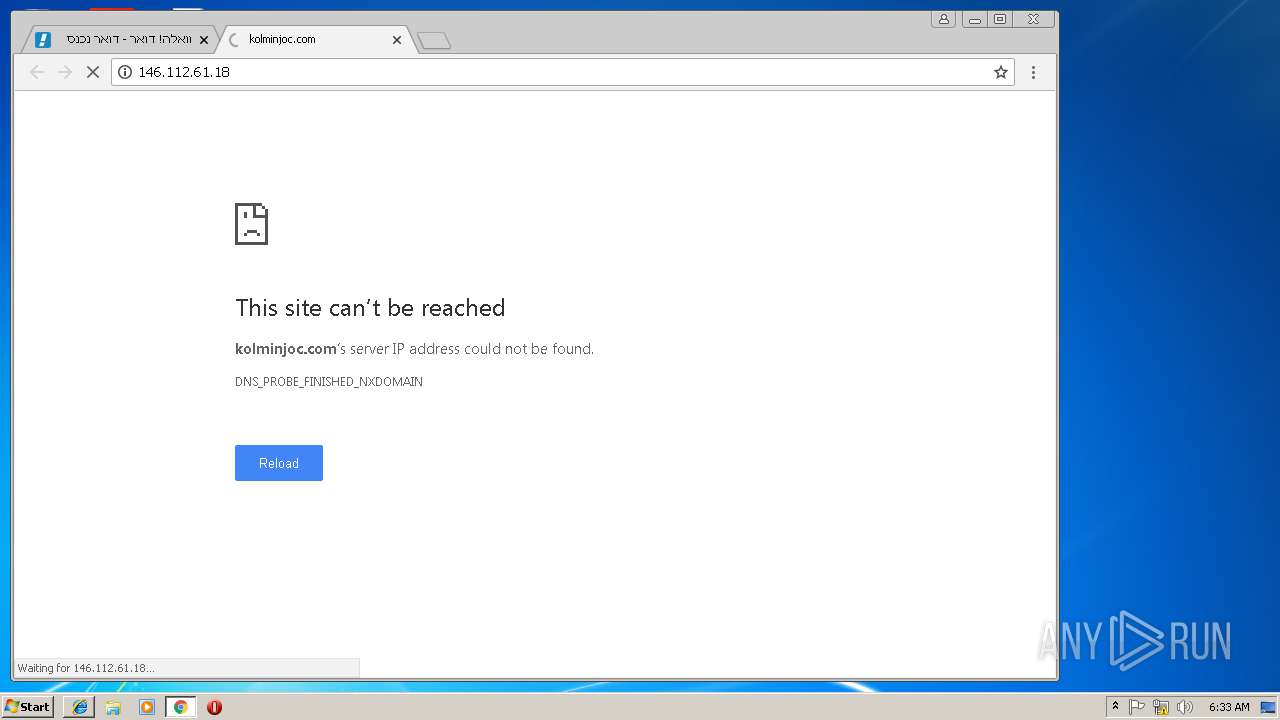
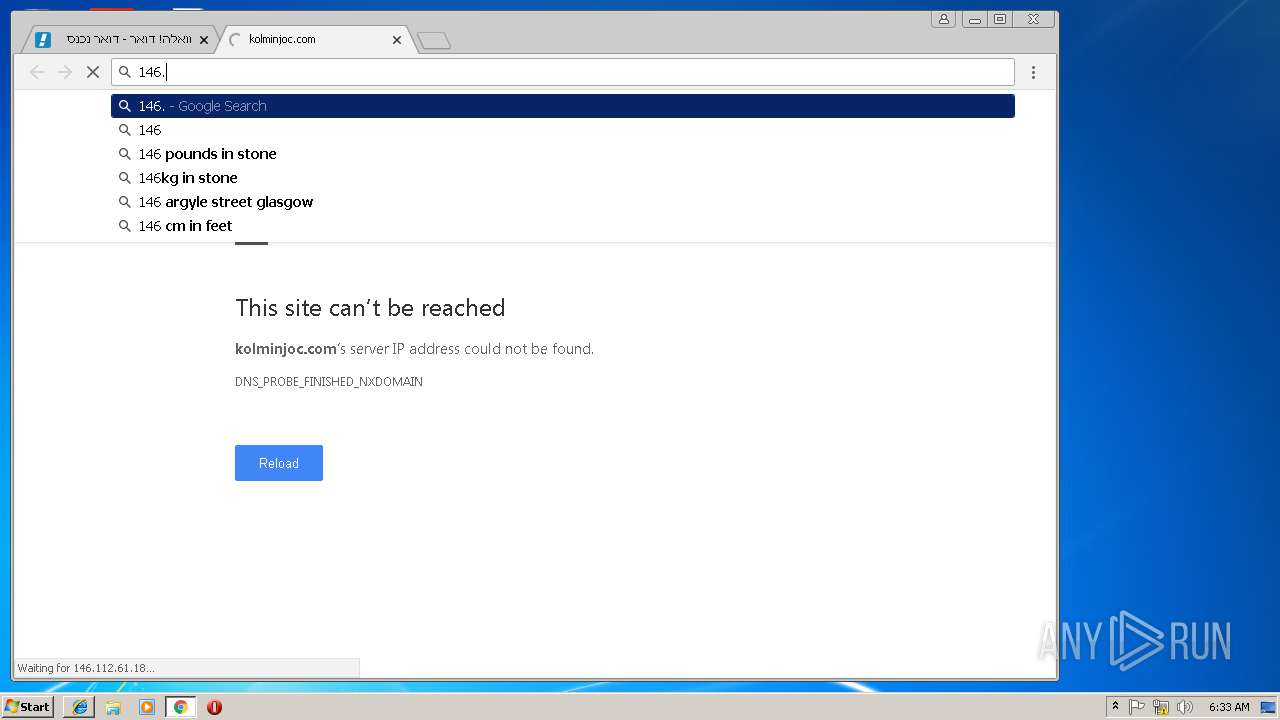
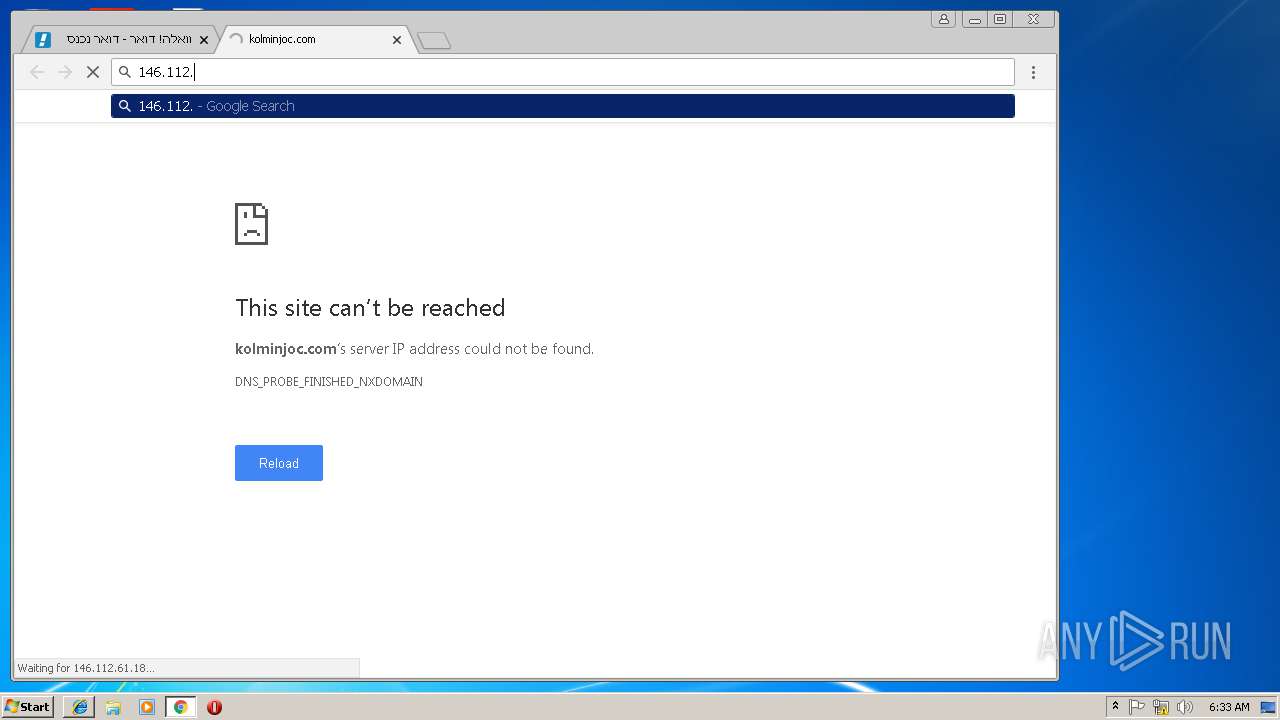
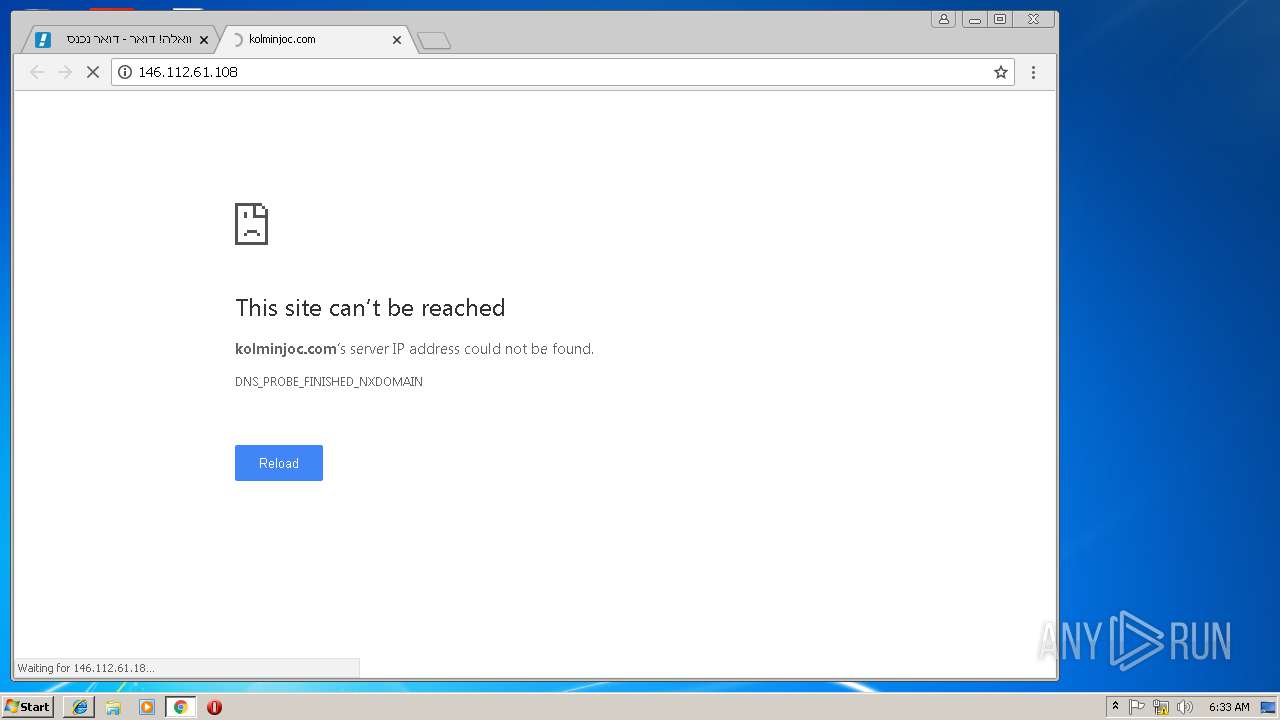
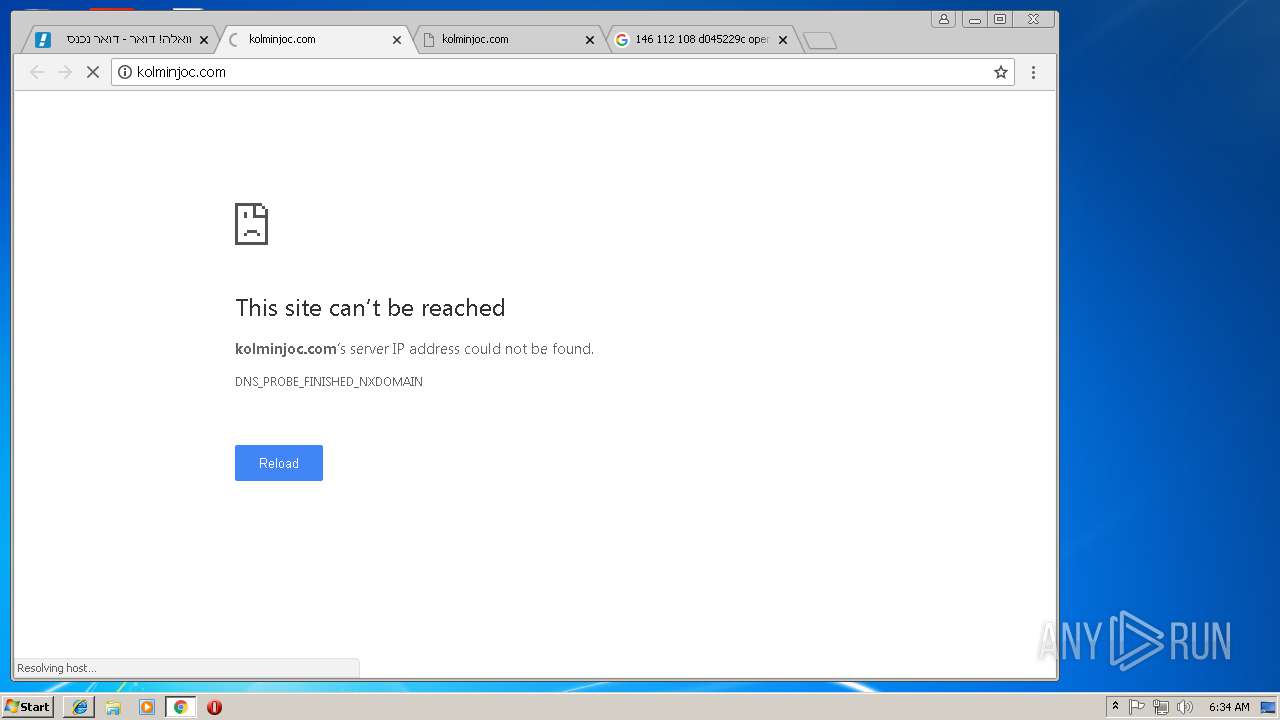
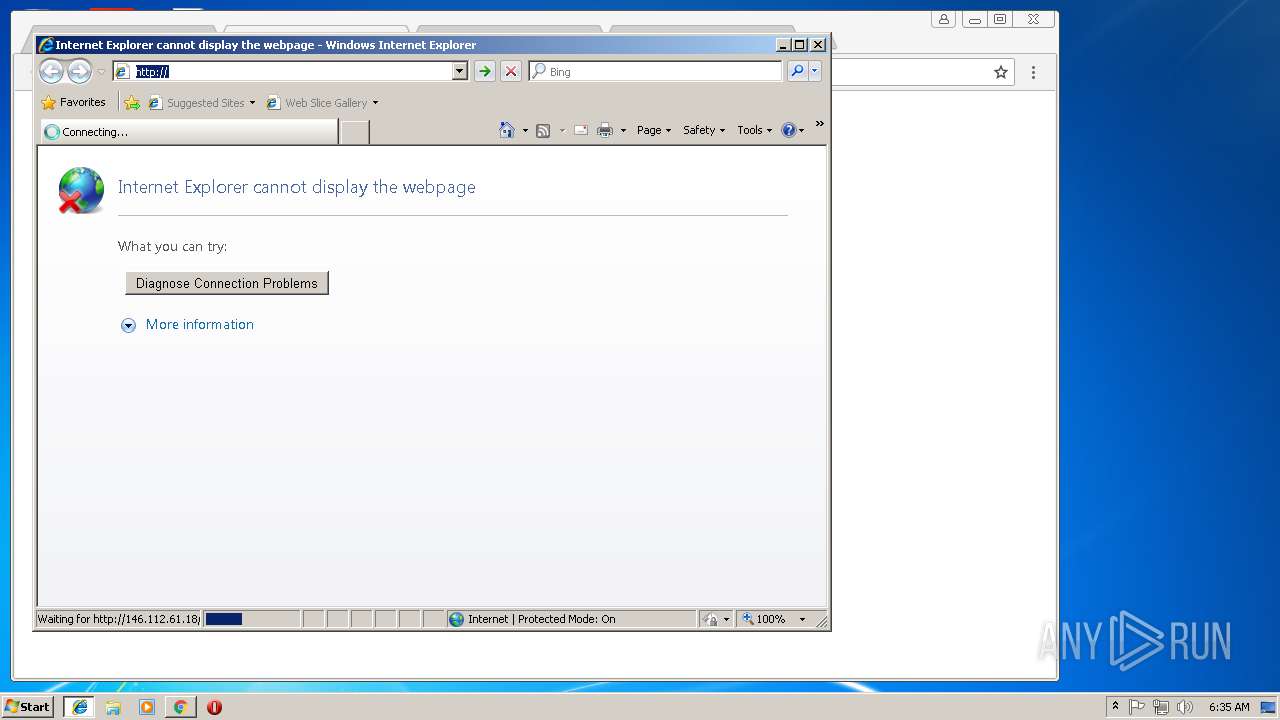
1448 | chrome.exe | GET | — | 146.112.61.18:80 | http://146.112.61.18/ | unknown | — | — | unknown |
3636 | iexplore.exe | GET | — | 146.112.61.18:80 | http://146.112.61.18/ | unknown | — | — | unknown |
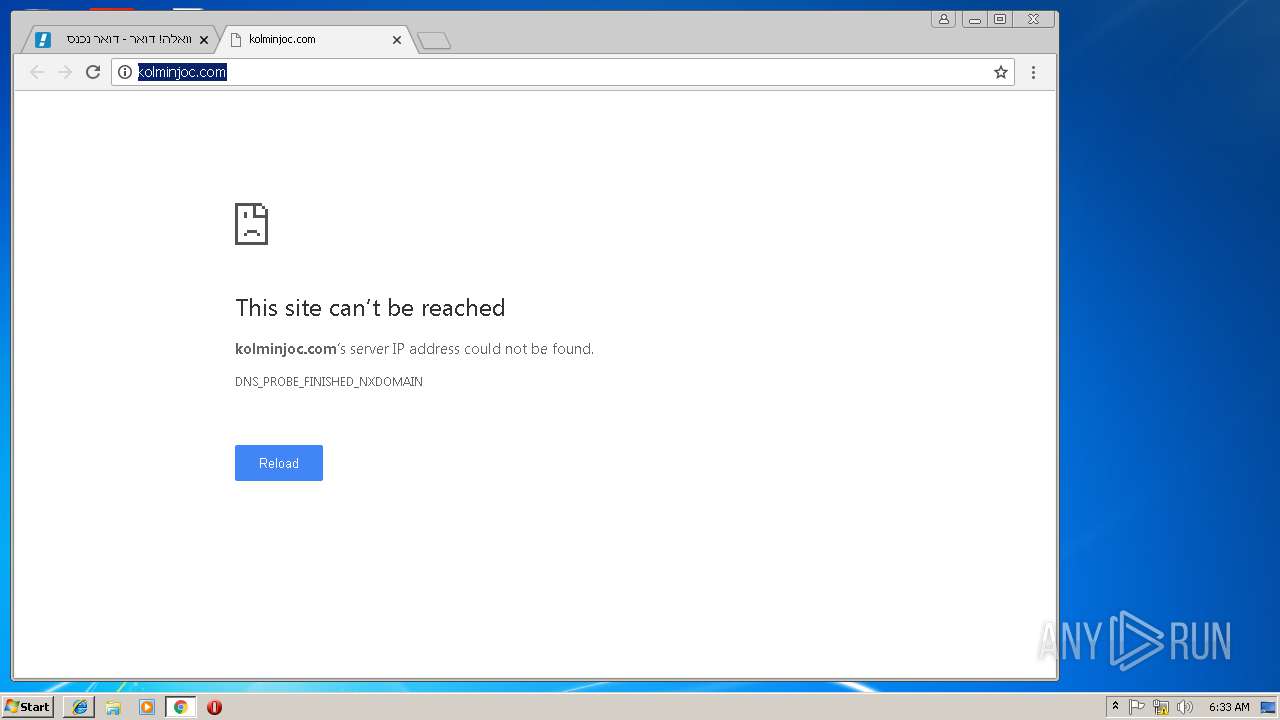
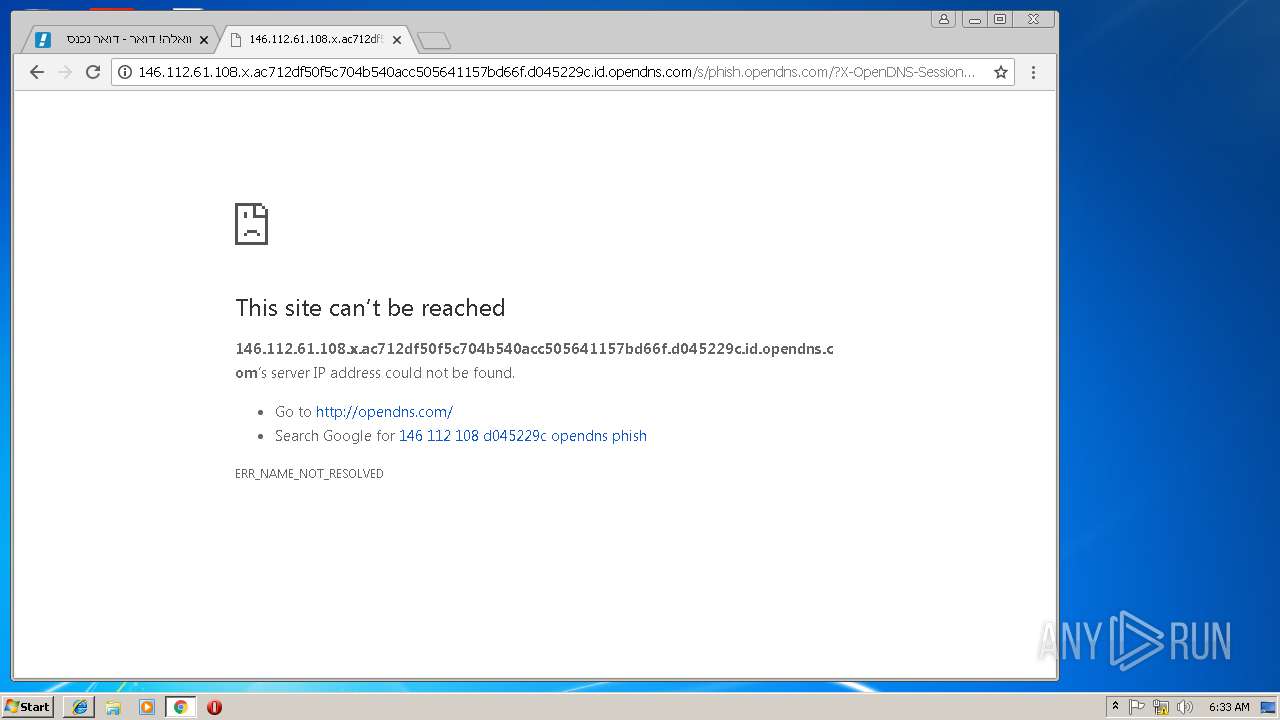
1448 | chrome.exe | GET | 403 | 146.112.61.108:80 | http://146.112.61.108/ | unknown | html | 514 b | suspicious |
1448 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 54.4 Kb | whitelisted |
1448 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 54.4 Kb | whitelisted |
1448 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 54.4 Kb | whitelisted |
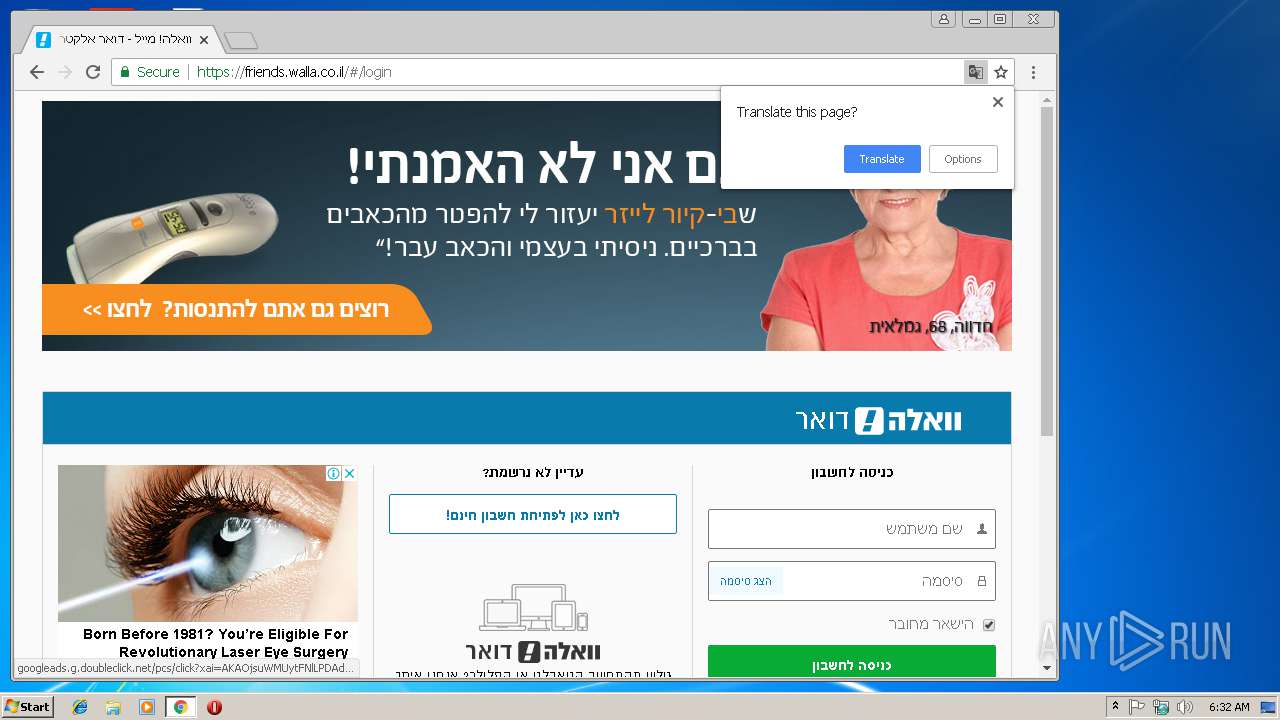
1448 | chrome.exe | GET | 301 | 2.18.234.79:80 | http://mail.walla.co.il/ | unknown | html | 183 b | shared |
1448 | chrome.exe | GET | 200 | 52.222.163.225:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
1448 | chrome.exe | GET | 301 | 54.77.201.172:80 | http://walla.co.il/ | IE | html | 191 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1448 | chrome.exe | 172.217.168.3:443 | www.google.de | Google Inc. | US | whitelisted |
1448 | chrome.exe | 172.217.168.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1448 | chrome.exe | 172.217.168.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1448 | chrome.exe | 172.217.168.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1448 | chrome.exe | 172.217.168.78:443 | apis.google.com | Google Inc. | US | whitelisted |
1448 | chrome.exe | 172.217.168.4:443 | www.google.com | Google Inc. | US | whitelisted |
1448 | chrome.exe | 172.217.168.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1448 | chrome.exe | 54.77.201.172:80 | walla.co.il | Amazon.com, Inc. | IE | unknown |
1448 | chrome.exe | 2.18.234.79:80 | www.walla.co.il | Akamai International B.V. | — | whitelisted |
1448 | chrome.exe | 2.18.234.79:443 | www.walla.co.il | Akamai International B.V. | — | whitelisted |
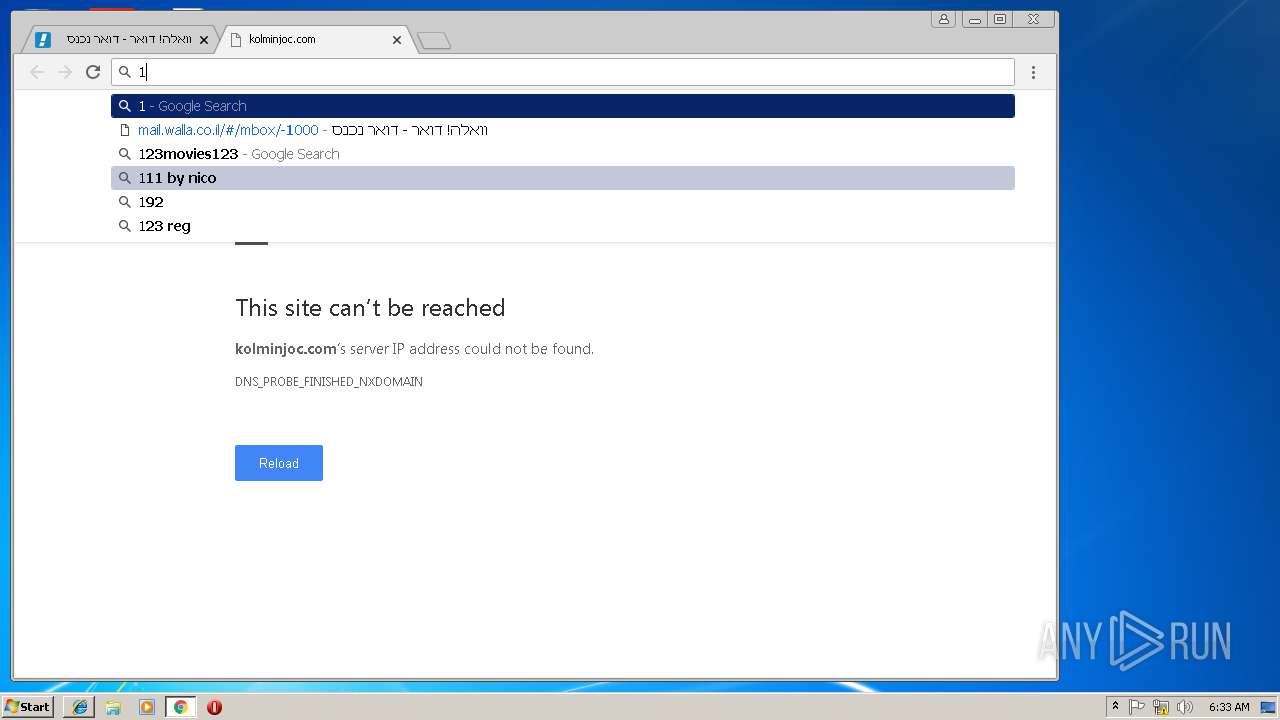
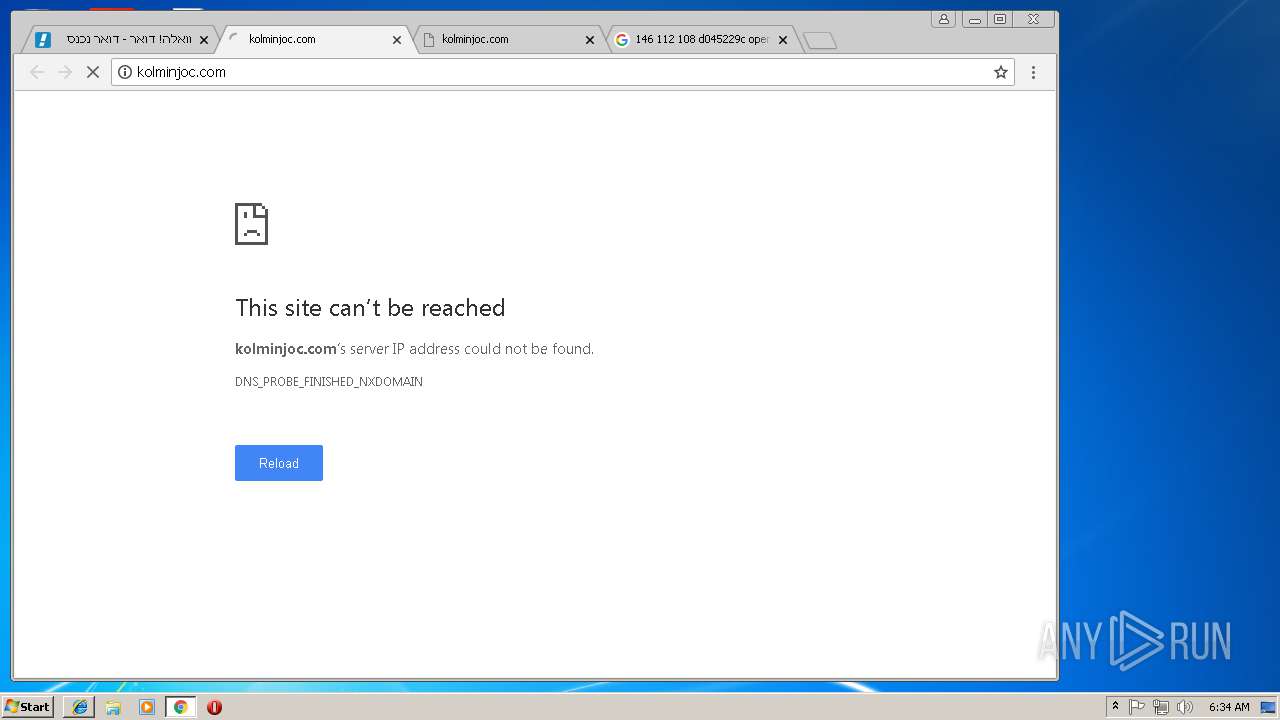
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
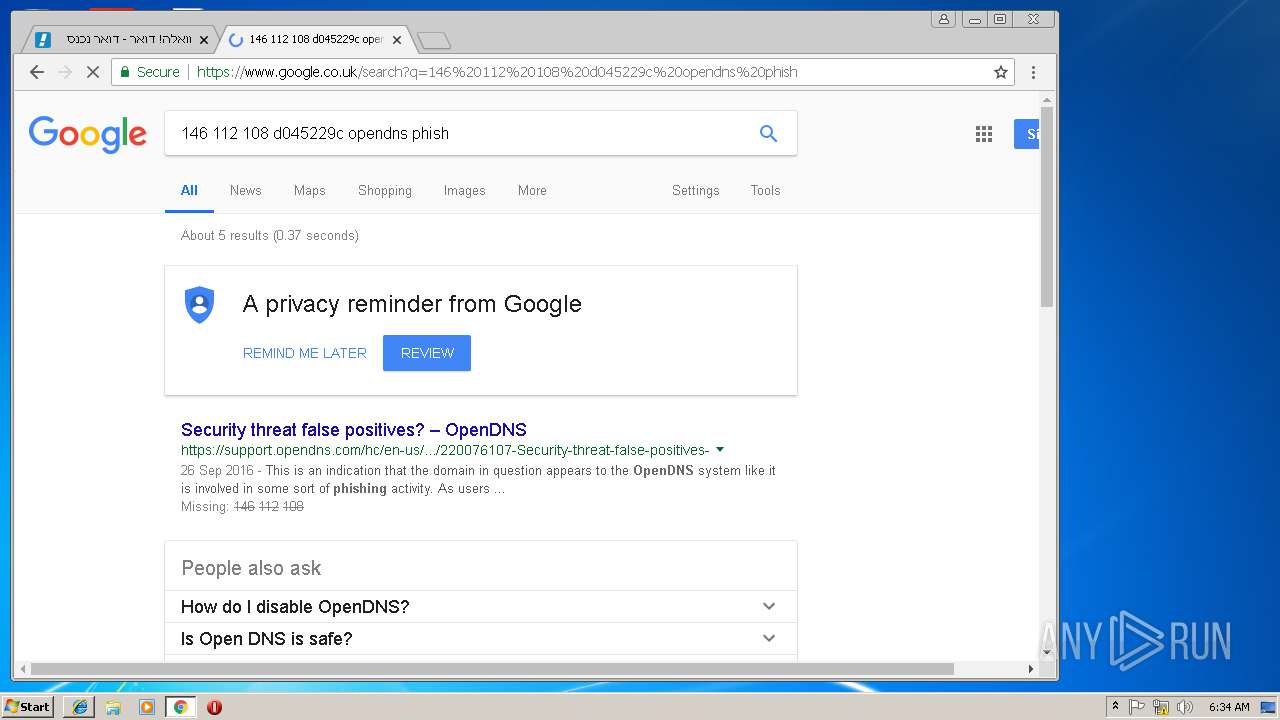
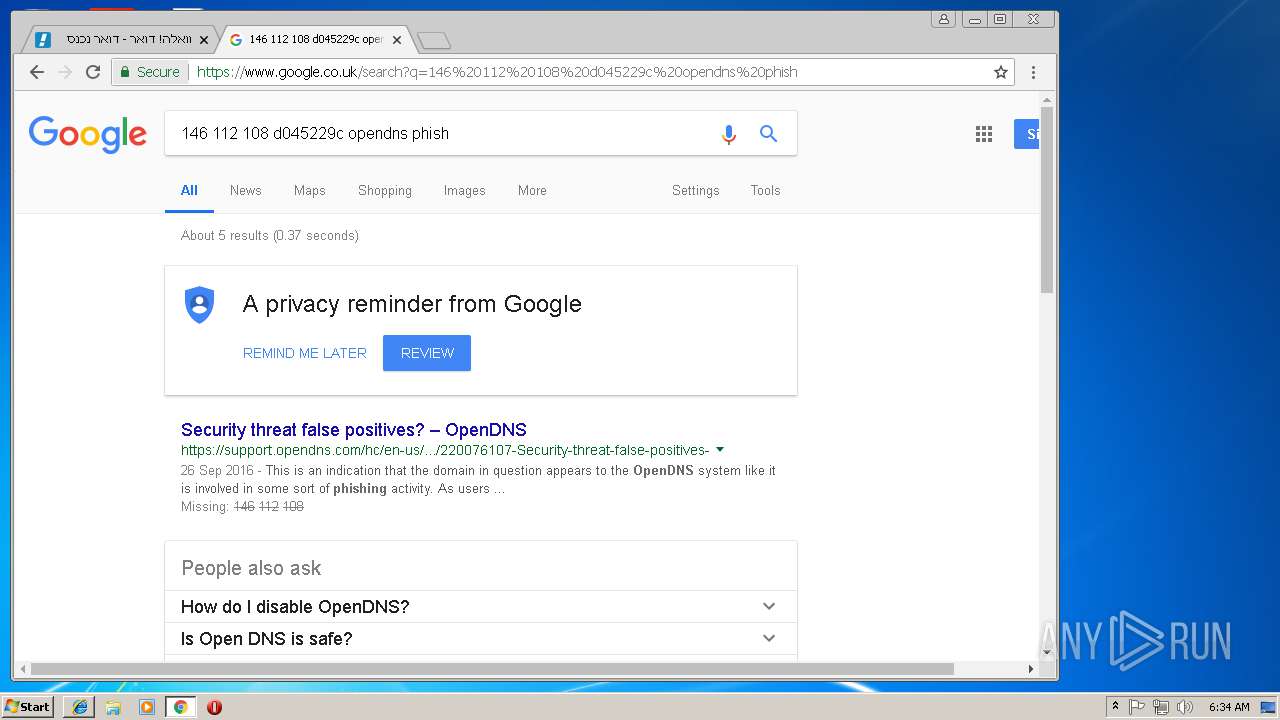
www.google.co.uk |
| whitelisted |
fonts.googleapis.com |
| whitelisted |