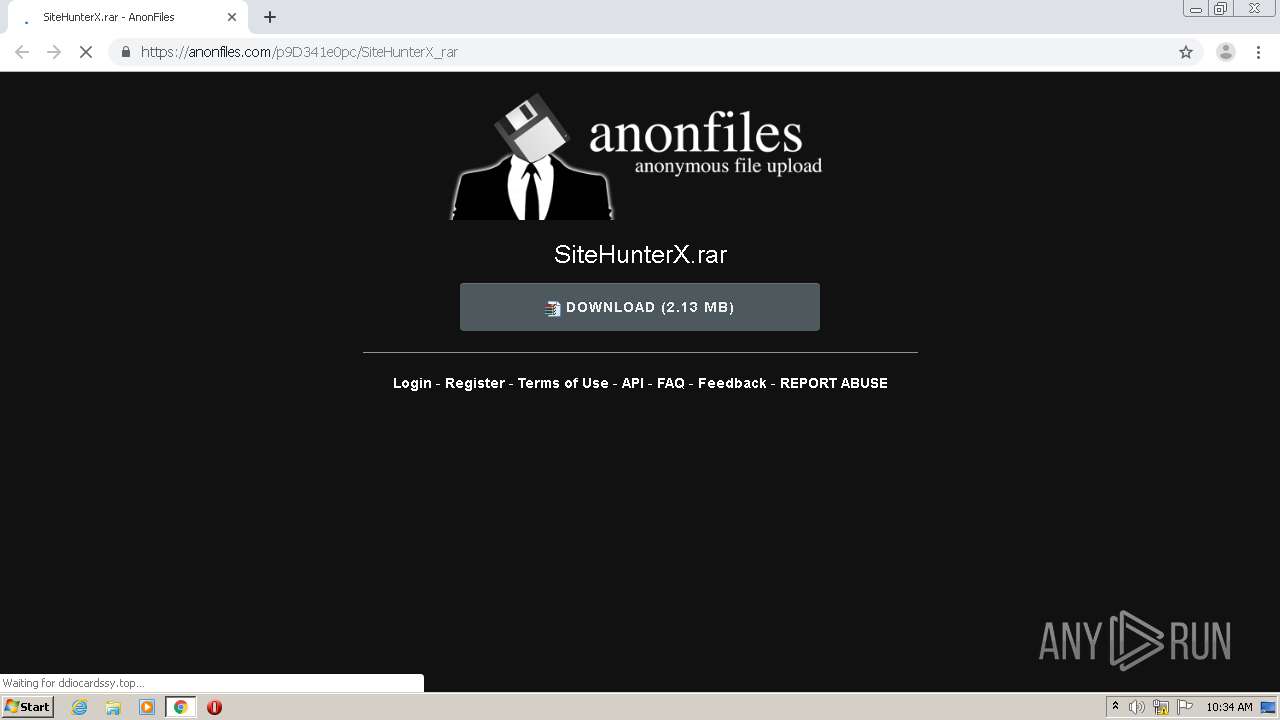
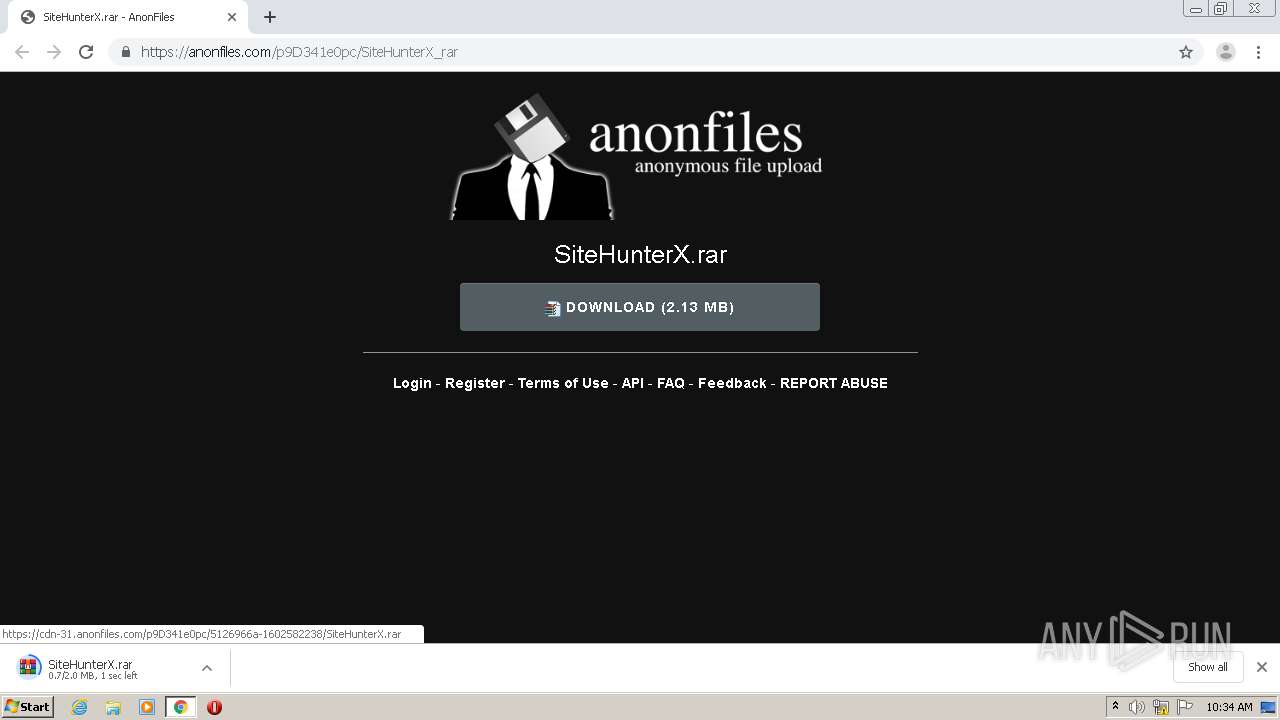
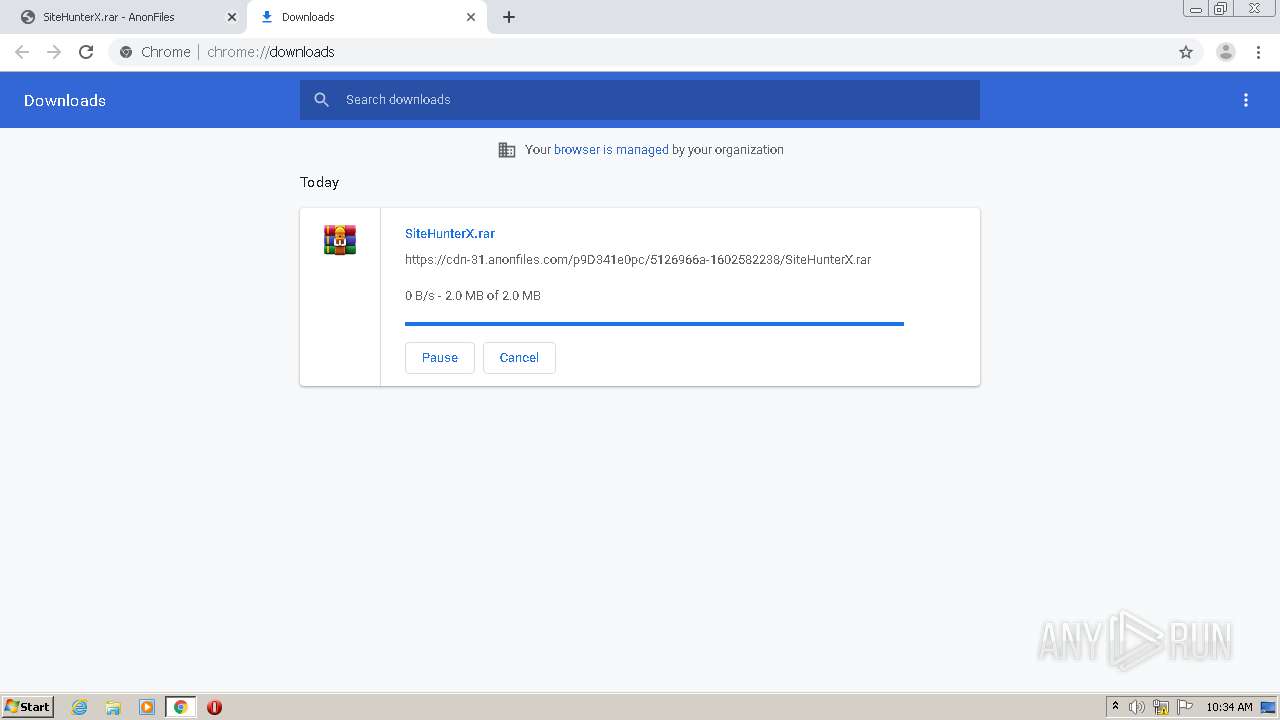
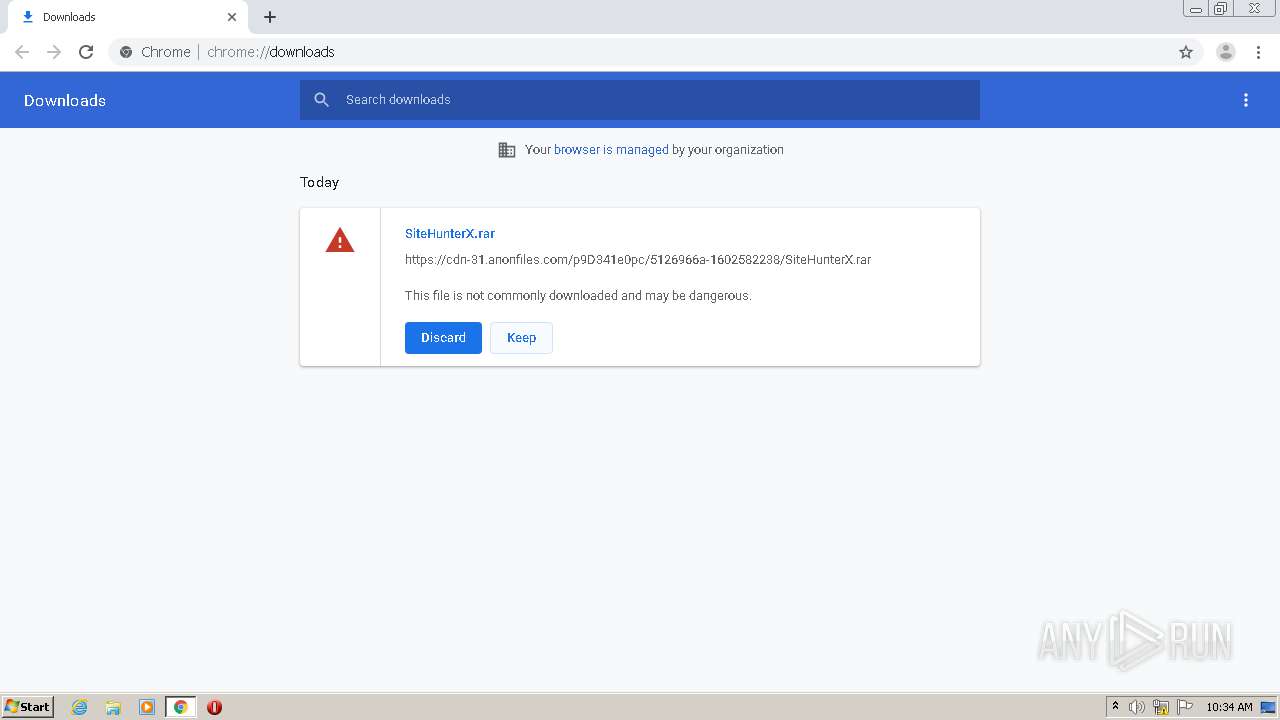
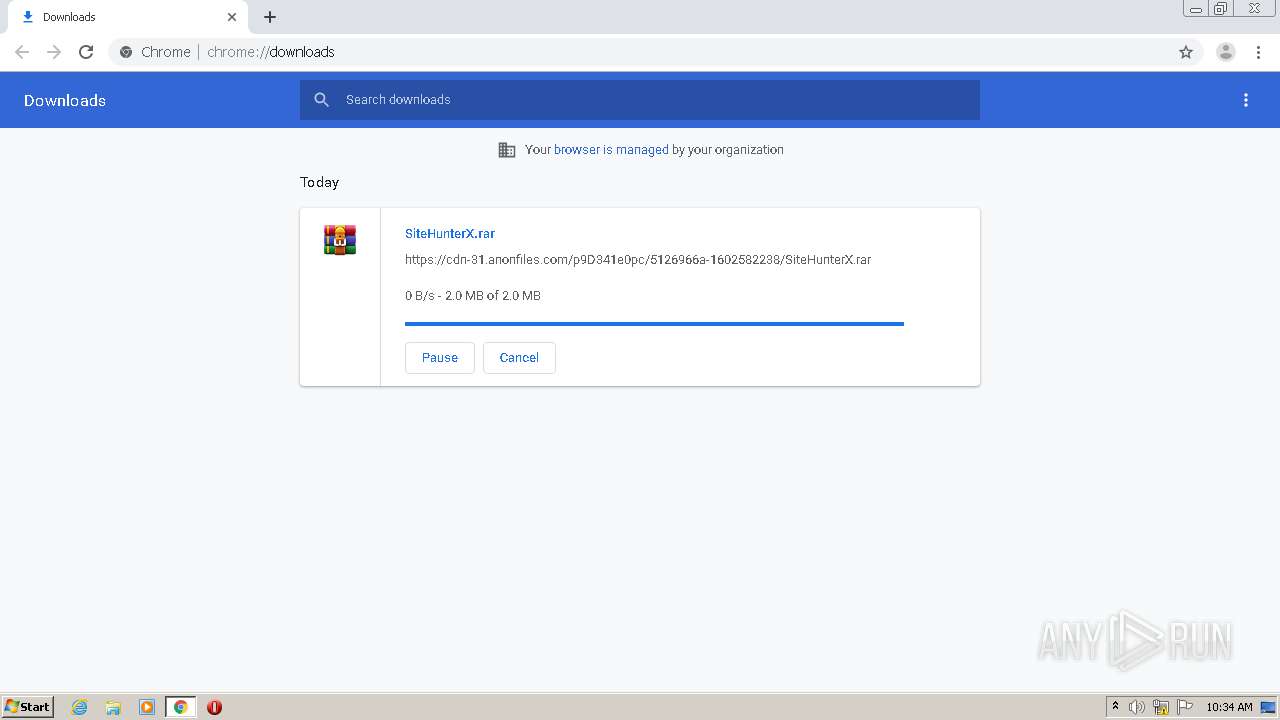
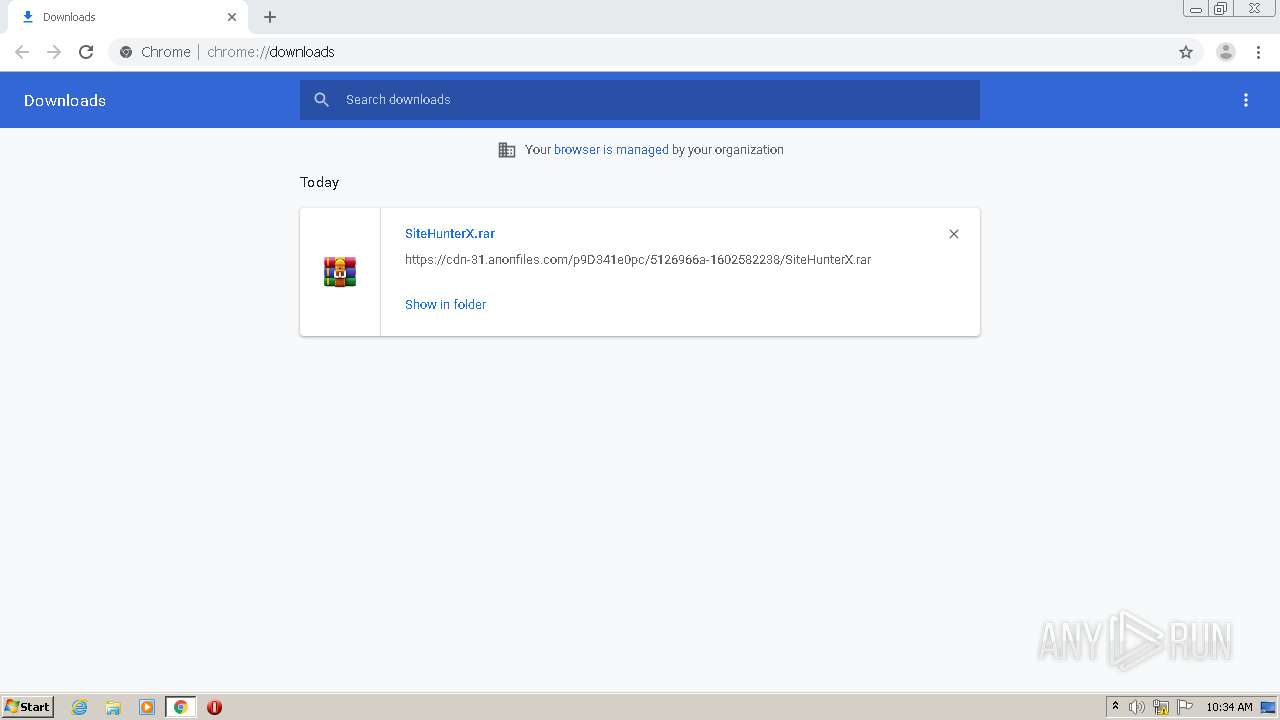
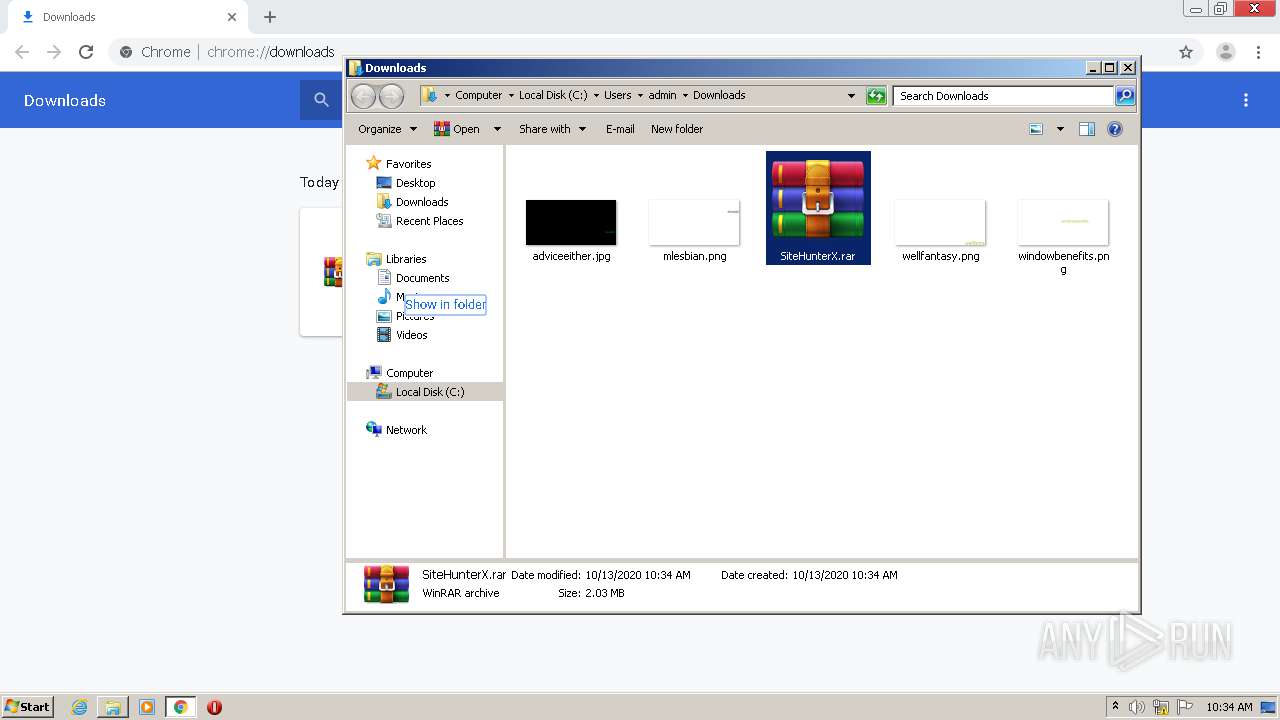
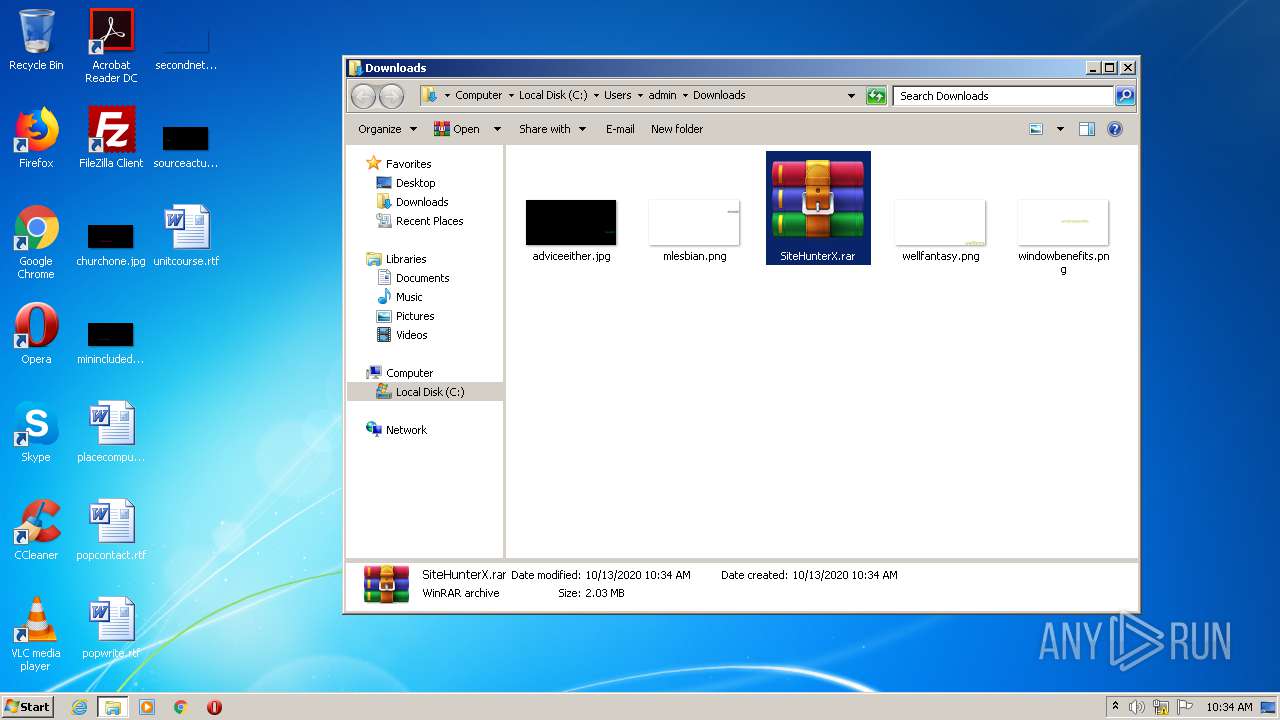
| URL: | https://anonfiles.com/p9D341e0pc/SiteHunterX_rar |
| Full analysis: | https://app.any.run/tasks/e13c95ba-7d3d-476b-9d1b-cf10a502db44 |
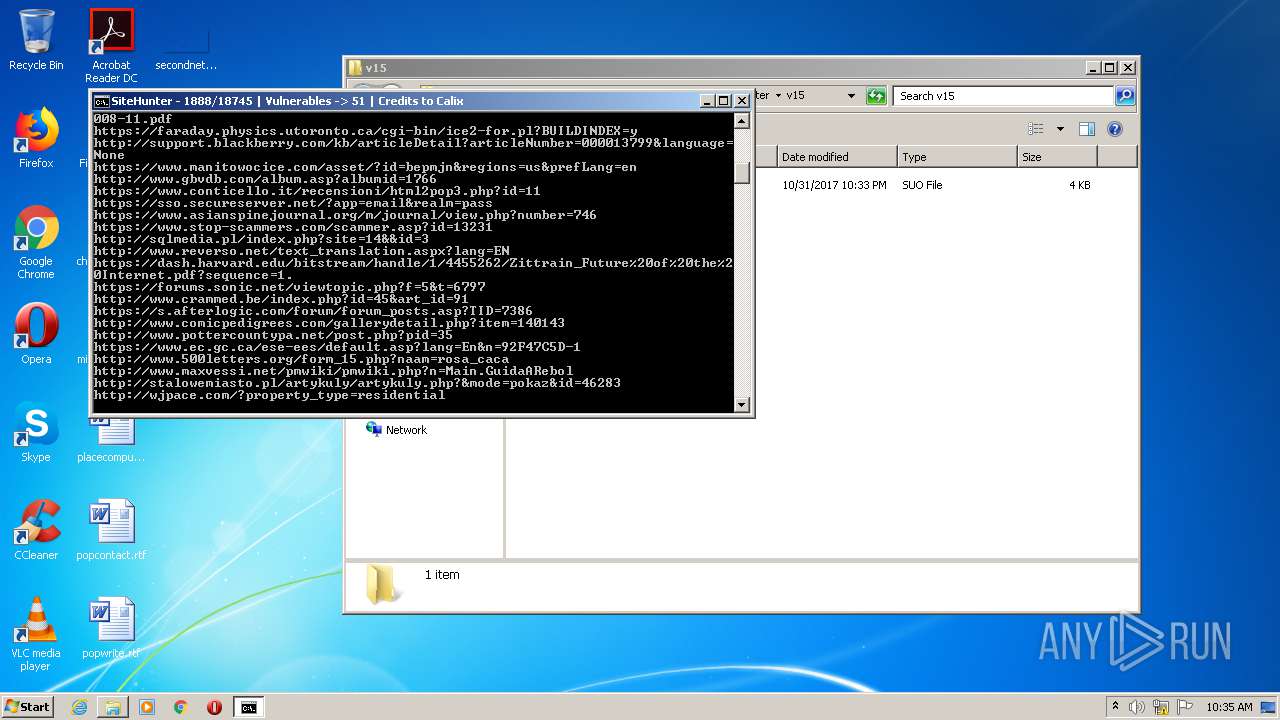
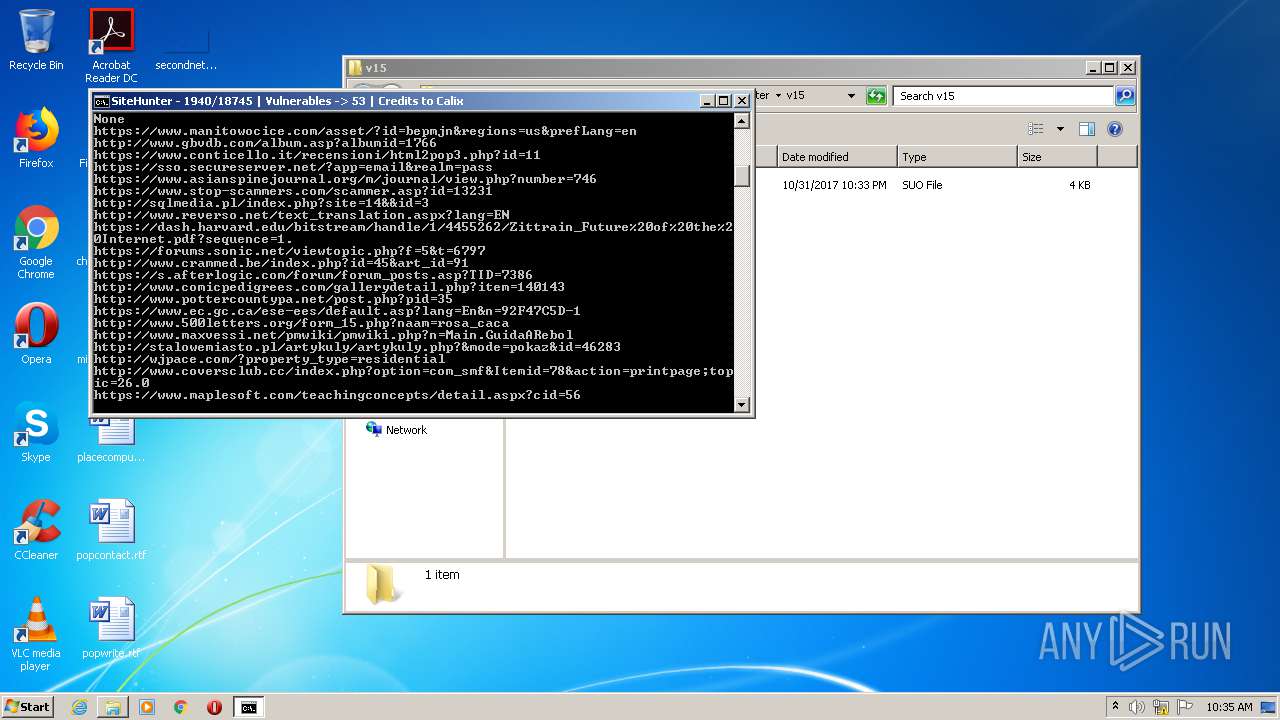
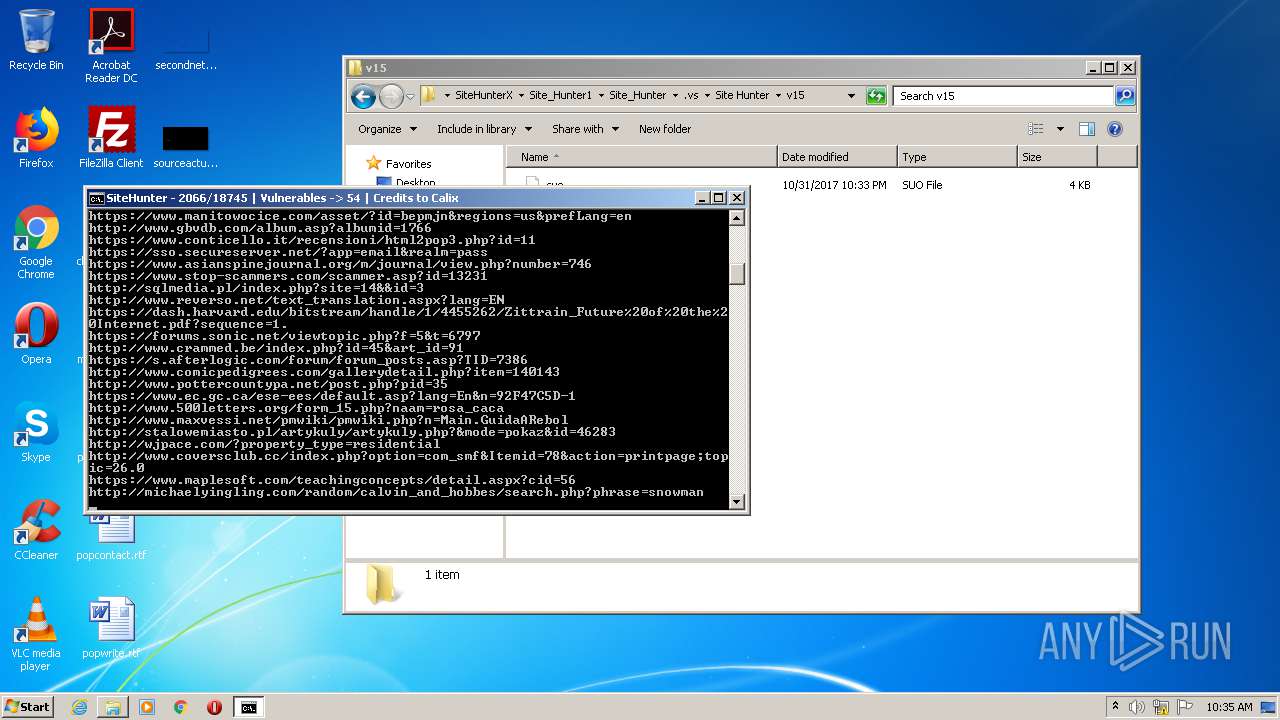
| Verdict: | Malicious activity |
| Analysis date: | October 13, 2020, 09:33:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BF21270C1389D25FB37406D6AB1C3478 |
| SHA1: | 9ECBA0C13D08FC9F7D6429E71D95688D4792056B |
| SHA256: | F814A27F7075EDCBD24EDC3C42CC6997D39574DB210824EE2952EAEF1213B622 |
| SSDEEP: | 3:N8M2Oc0ZVVdraemt6O:2M2z0rrraemt9 |
MALICIOUS
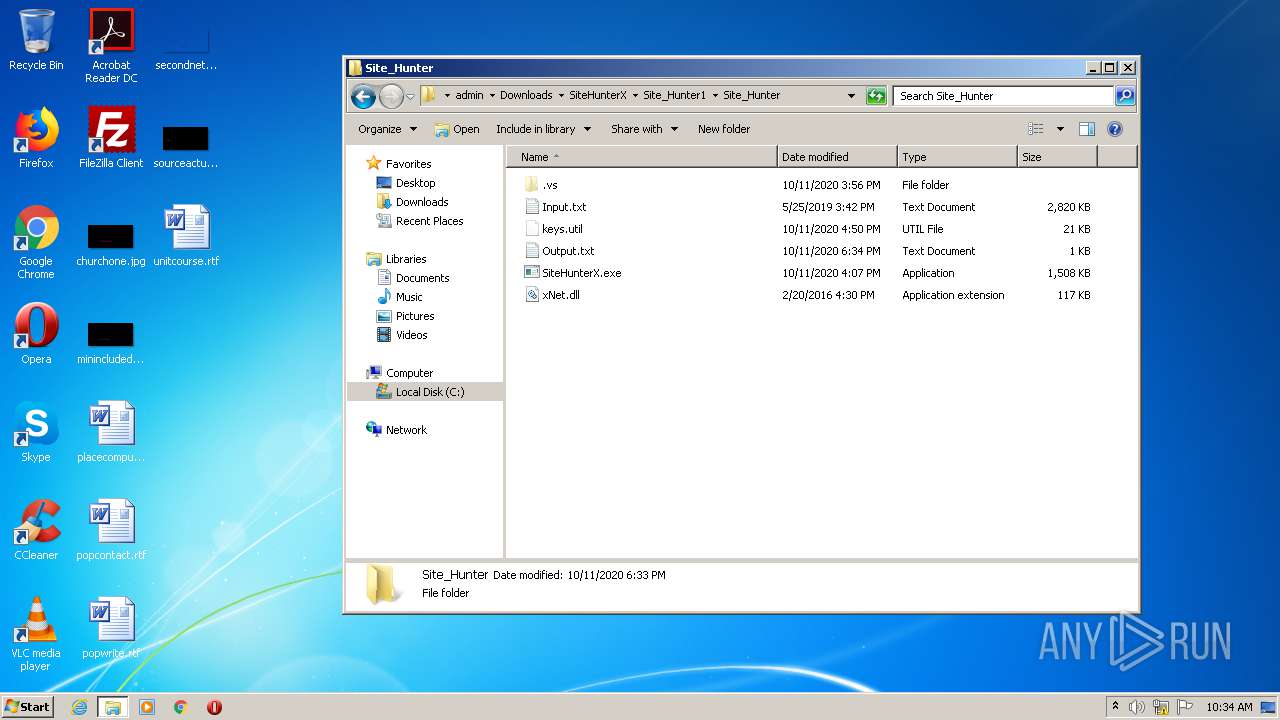
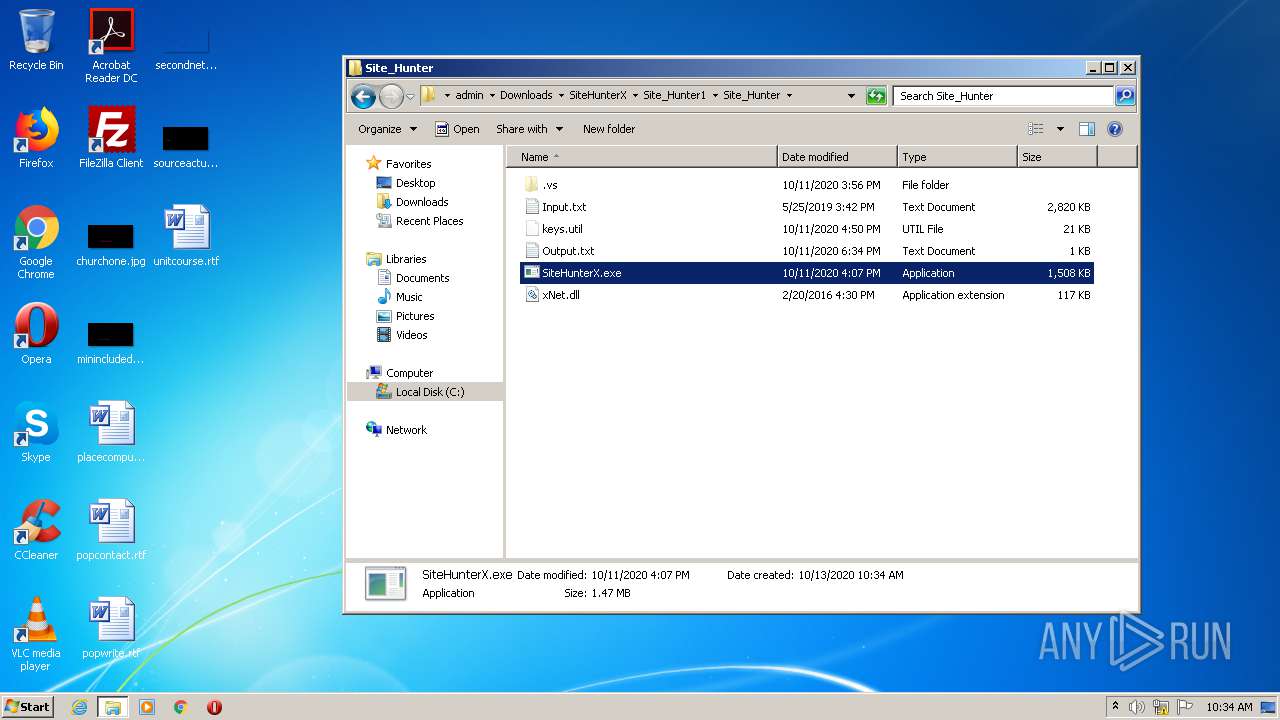
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 624)
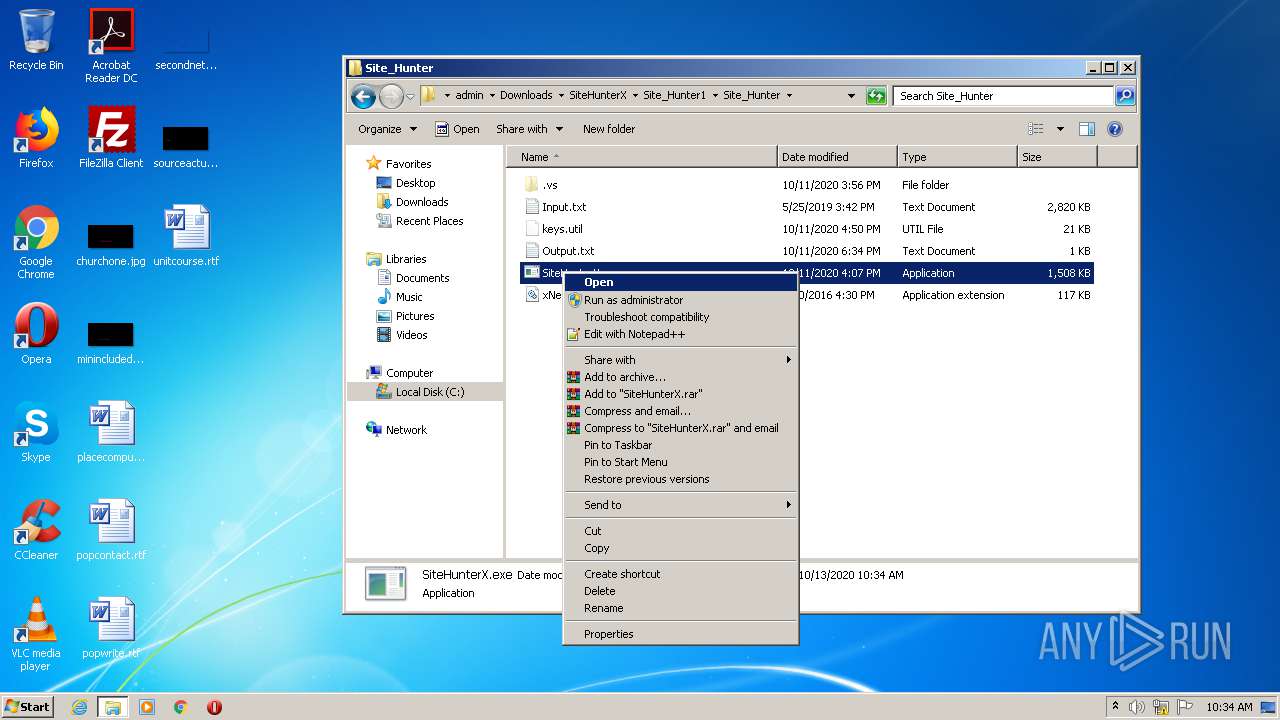
Application was dropped or rewritten from another process
- SiteHunterX.exe (PID: 3348)
- keys.util (PID: 2384)
Changes settings of System certificates
- keys.util (PID: 2384)
SUSPICIOUS
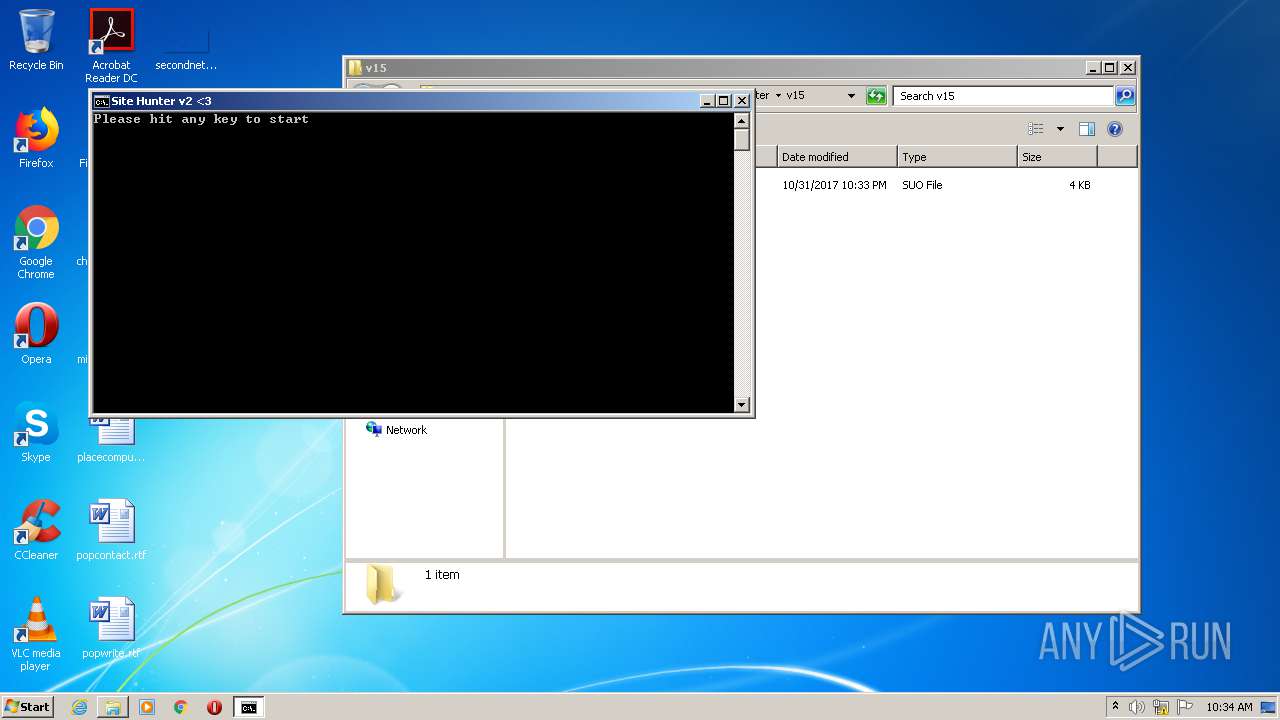
Starts CMD.EXE for commands execution
- SiteHunterX.exe (PID: 3348)
Starts application with an unusual extension
- cmd.exe (PID: 2584)
Adds / modifies Windows certificates
- keys.util (PID: 2384)
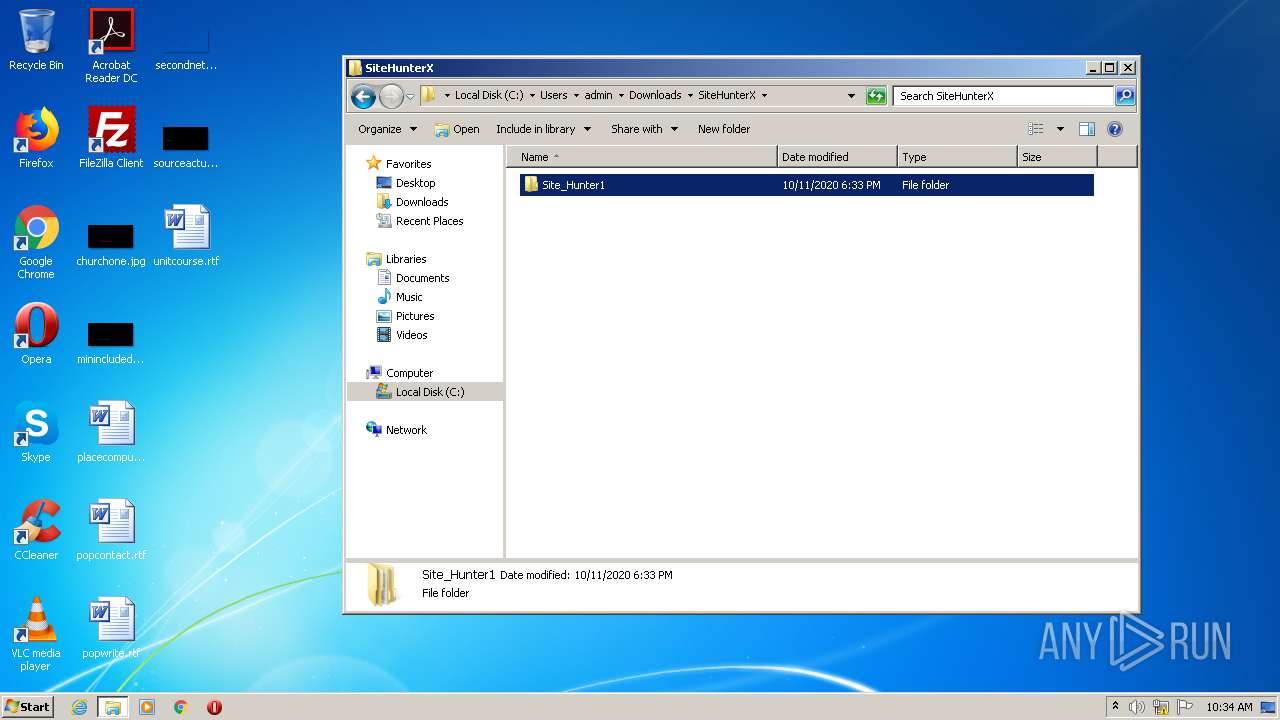
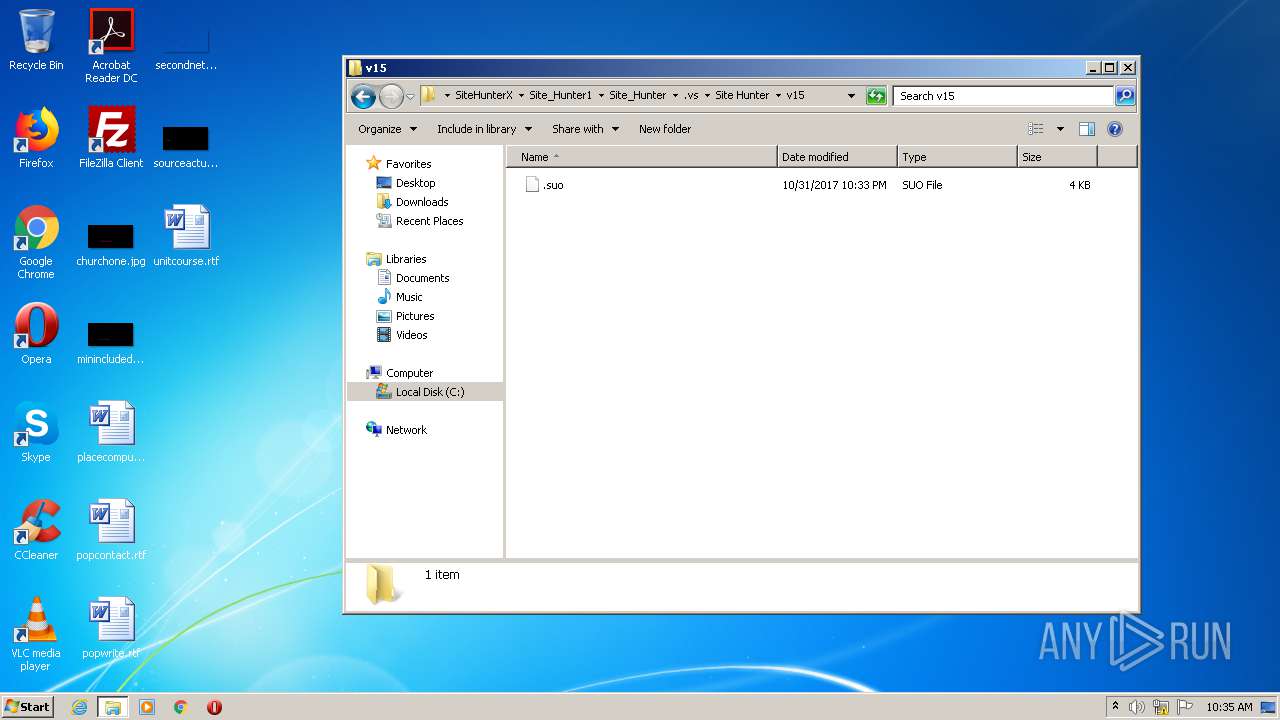
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2168)
INFO
Reads the hosts file
- chrome.exe (PID: 2508)
- chrome.exe (PID: 3320)
Application launched itself
- chrome.exe (PID: 2508)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2168)
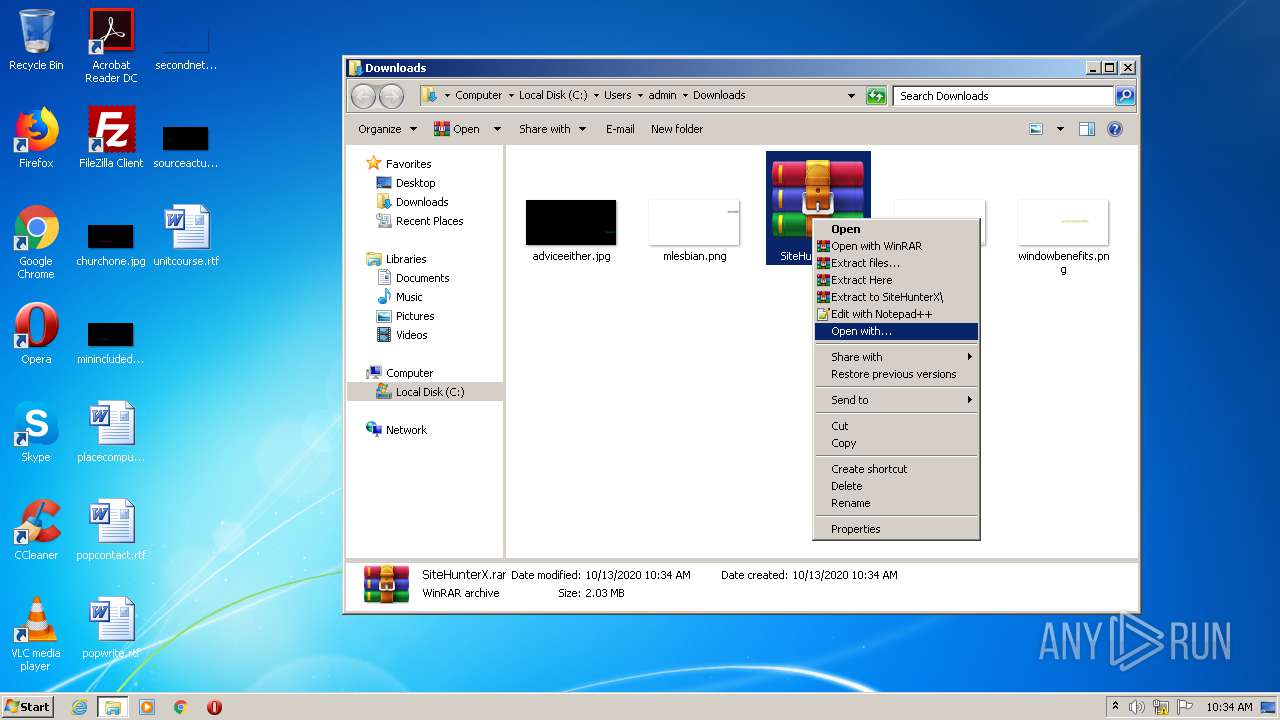
Manual execution by user
- SiteHunterX.exe (PID: 3348)
- WinRAR.exe (PID: 2168)
Reads settings of System Certificates
- keys.util (PID: 2384)
Reads Internet Cache Settings
- chrome.exe (PID: 2508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
22
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7610892324853253659,168913109070541663,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4376177707142625865 --mojo-platform-channel-handle=3940 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,7610892324853253659,168913109070541663,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=998778443413008663 --mojo-platform-channel-handle=3632 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7610892324853253659,168913109070541663,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1830521584121616788 --mojo-platform-channel-handle=2660 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7610892324853253659,168913109070541663,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1608019553033193456 --mojo-platform-channel-handle=2592 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,7610892324853253659,168913109070541663,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15349672734013499046 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3704 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7610892324853253659,168913109070541663,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16711968853051738123 --mojo-platform-channel-handle=3552 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7610892324853253659,168913109070541663,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=374198889086296814 --mojo-platform-channel-handle=2668 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2556 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\SiteHunterX.rar" C:\Users\admin\Downloads\SiteHunterX\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 434
Read events
1 277
Write events
153
Delete events
4
Modification events
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2508-13247055232438125 |
Value: 259 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
3
Suspicious files
83
Text files
150
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F857480-9CC.pma | — | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b03722d6-5fce-466b-924b-1d348e563aeb.tmp | — | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2d401b.TMP | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d401b.TMP | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF2d401b.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
838
TCP/UDP connections
2 327
DNS requests
2 177
Threats
129
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2384 | keys.util | GET | — | 212.27.63.35:80 | http://dl.free.fr/getfile.pl?file=/giB5cD8i' | FR | — | — | whitelisted |
2384 | keys.util | GET | 301 | 13.225.25.56:80 | http://www.harpercollinschildrens.com/Home/ImprintBooks.aspx?TCId=100&SIId=9438&ST=7' | US | — | — | shared |
2384 | keys.util | GET | — | 185.39.10.6:80 | http://livetv.sx/enx/megasearch/?msq=Basketball' | CH | — | — | whitelisted |
2384 | keys.util | GET | 301 | 104.31.73.15:80 | http://www.indianjpsychiatry.org/article.asp?issn=0019-5545;year=2019;volume=61;issue=9;spage=364;epage=378;aulast=' | US | — | — | suspicious |
2384 | keys.util | GET | 200 | 185.208.164.135:80 | http://bibliotekasulmierzyce.pl/?page_id=859' | PL | html | 763 b | suspicious |
2384 | keys.util | GET | 404 | 209.15.236.146:80 | http://www.worldcurl.com/events.php?task=Event&view=Main&eventid=5343' | CA | html | 208 b | unknown |
2384 | keys.util | GET | 200 | 217.198.114.128:80 | http://www.kromeriz.cz/index.php?id=firma&fce=detail&i=468' | CZ | html | 6.46 Kb | unknown |
2384 | keys.util | GET | 200 | 46.28.105.29:80 | http://www.svetwebu.cz/?p=16027' | CZ | html | 7.19 Kb | unknown |
2384 | keys.util | GET | 404 | 85.11.67.245:80 | http://nocek.pl/wiki/index.php?title=Inne_strony' | PL | html | 2.48 Kb | unknown |
2384 | keys.util | GET | 200 | 81.2.195.173:80 | http://www.katostwo-nyskie.pl/index.php?menu=sk&page=szkoly/biecz' | CZ | html | 4.98 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3320 | chrome.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
3320 | chrome.exe | 143.204.225.60:443 | djv99sxoqpv11.cloudfront.net | — | US | unknown |
3320 | chrome.exe | 52.206.71.220:443 | baconaces.pro | Amazon.com, Inc. | US | suspicious |
3320 | chrome.exe | 143.204.94.79:443 | cilcountee.top | — | US | unknown |
3320 | chrome.exe | 172.217.18.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
3320 | chrome.exe | 172.217.18.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3320 | chrome.exe | 216.58.212.142:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
2384 | keys.util | 104.111.239.155:443 | www.nvidia.com | Akamai International B.V. | NL | unknown |
3320 | chrome.exe | 54.237.125.12:443 | baconaces.pro | Amazon.com, Inc. | US | suspicious |
3320 | chrome.exe | 45.148.16.51:443 | cdn-31.anonfiles.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
baconaces.pro |
| shared |
cilcountee.top |
| malicious |
ddiocardssy.top |
| shared |
ssl.gstatic.com |
| whitelisted |
cdn-31.anonfiles.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2384 | keys.util | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 22 |
2384 | keys.util | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2384 | keys.util | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2384 | keys.util | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2384 | keys.util | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2384 | keys.util | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2384 | keys.util | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2384 | keys.util | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2384 | keys.util | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1 ETPRO signatures available at the full report