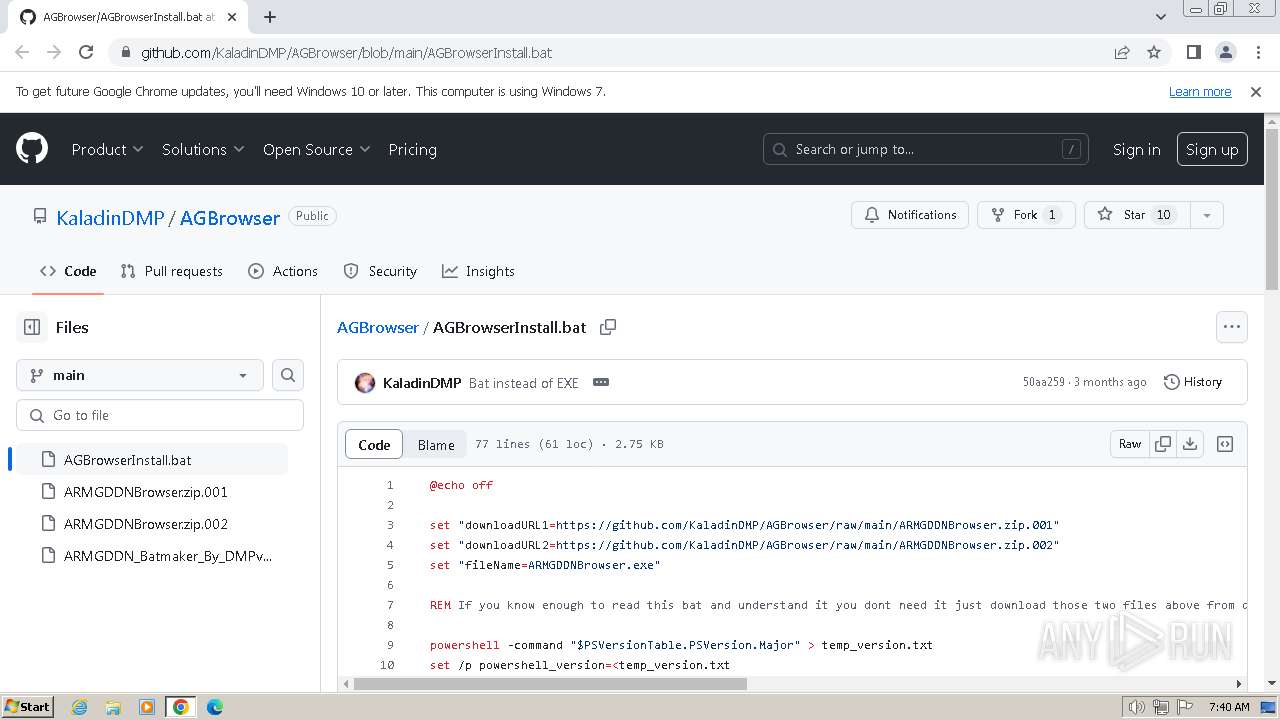
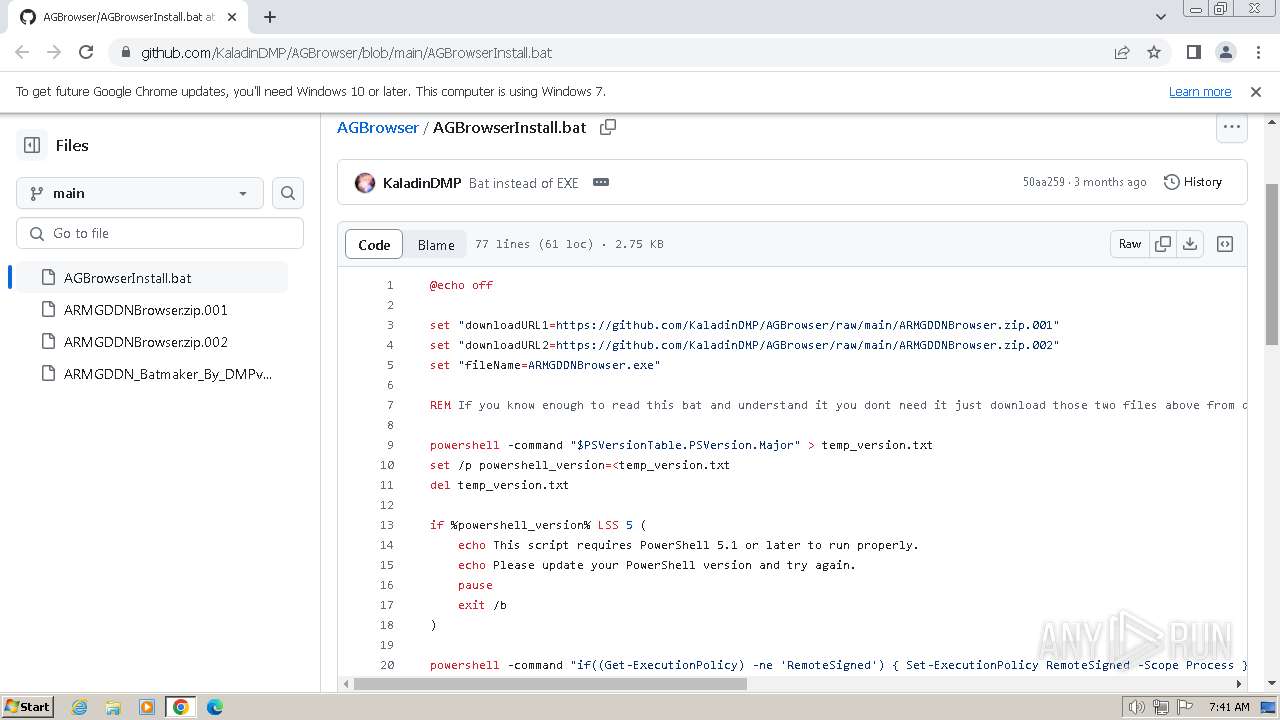
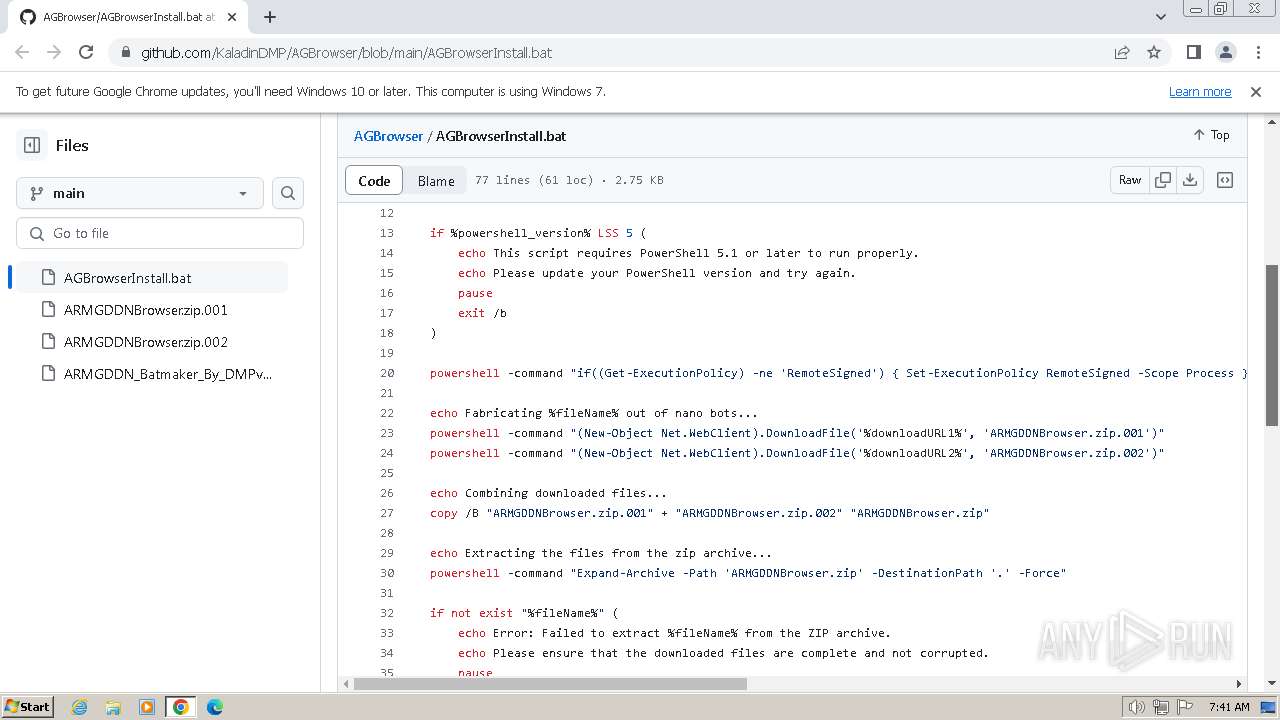
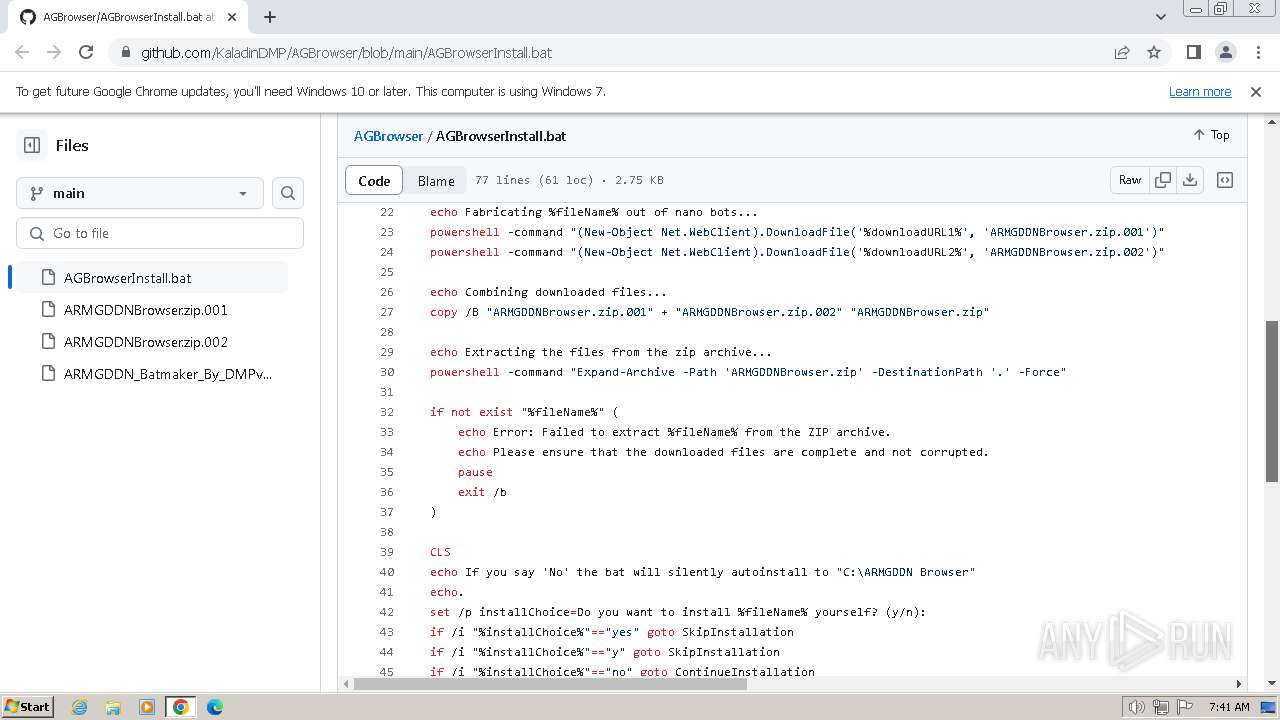
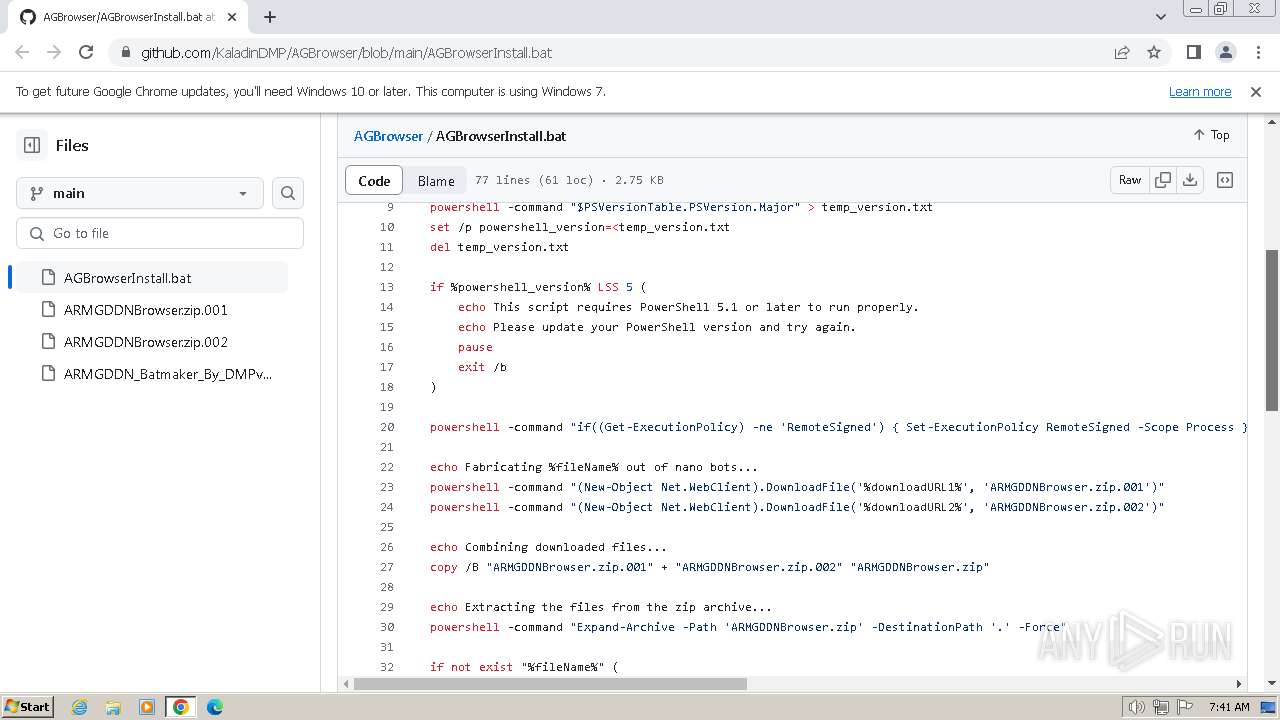
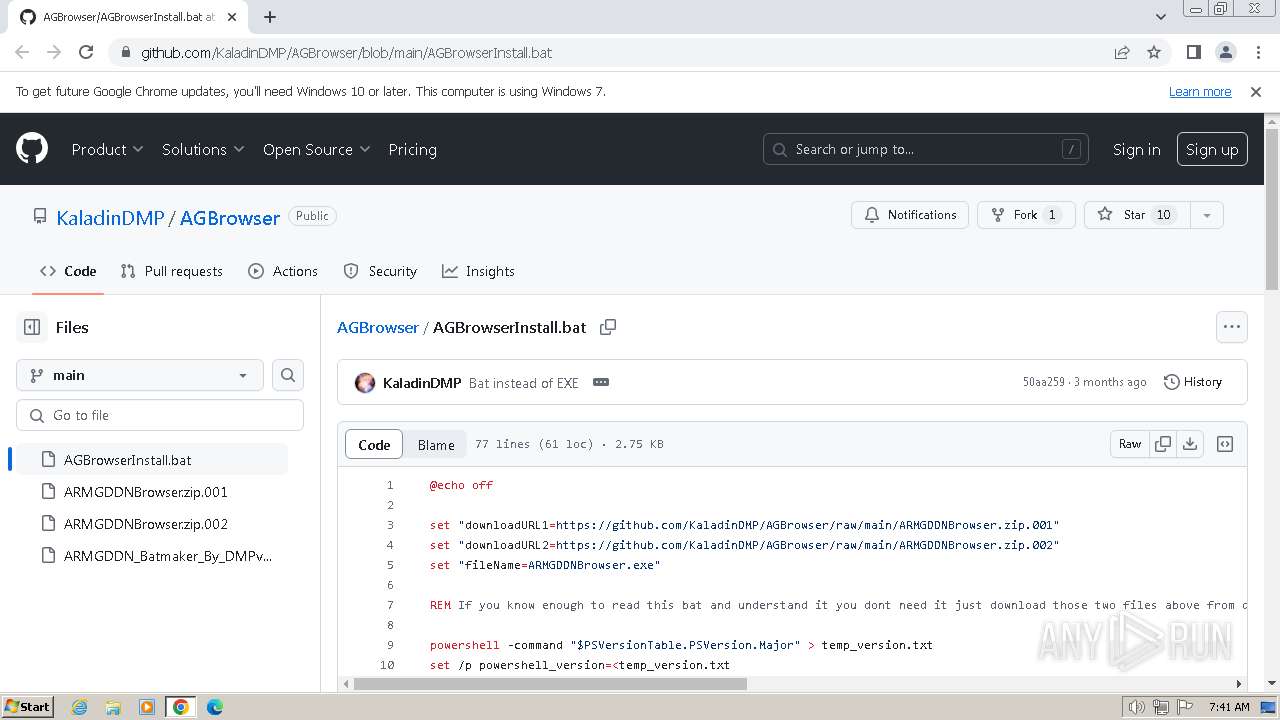
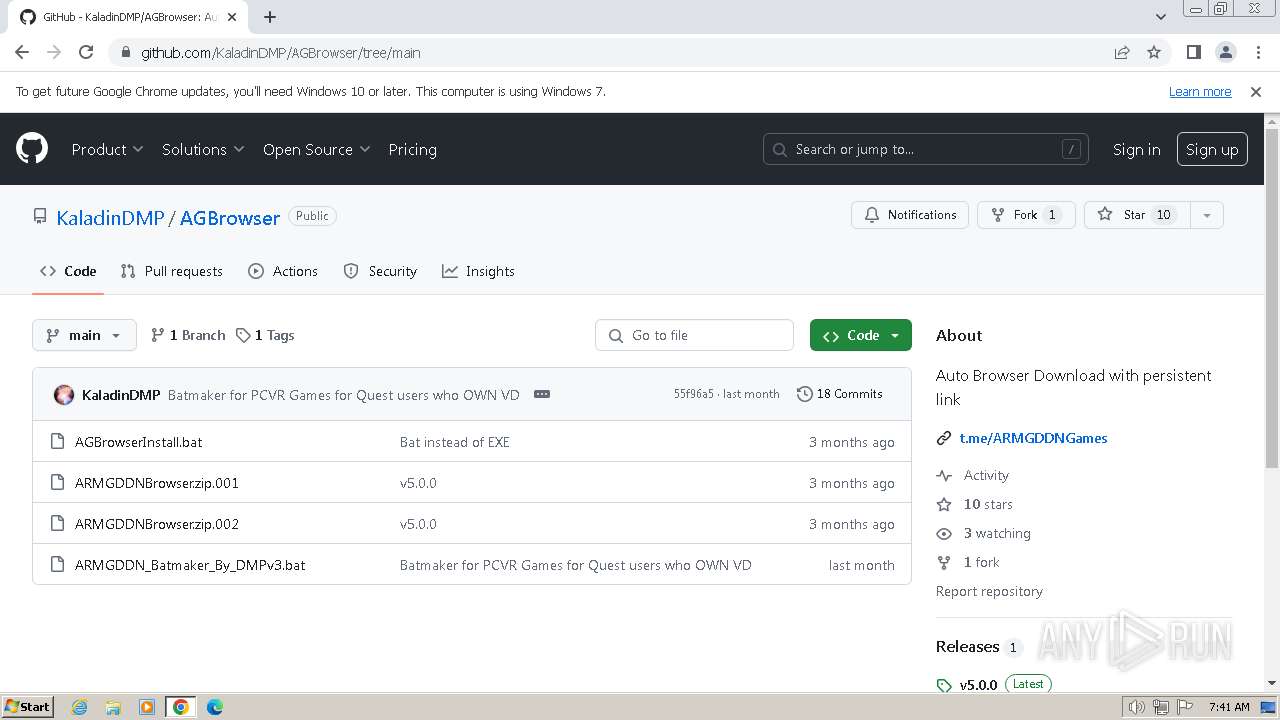
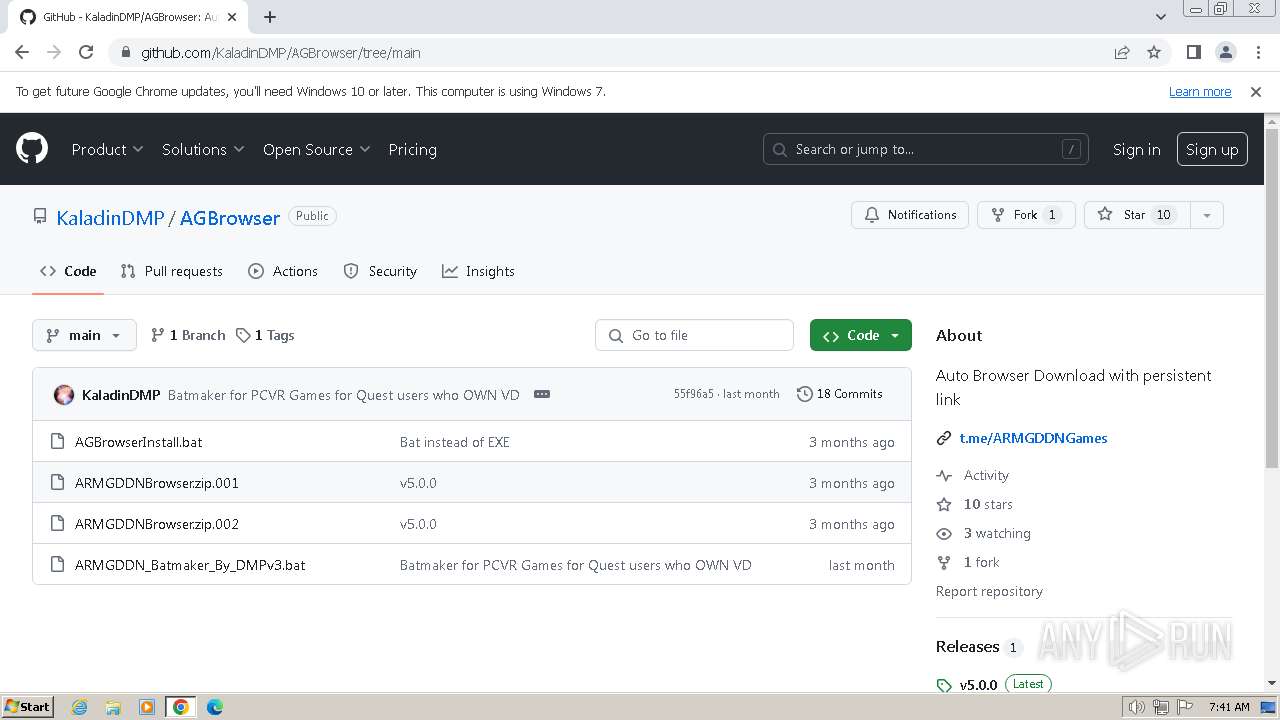
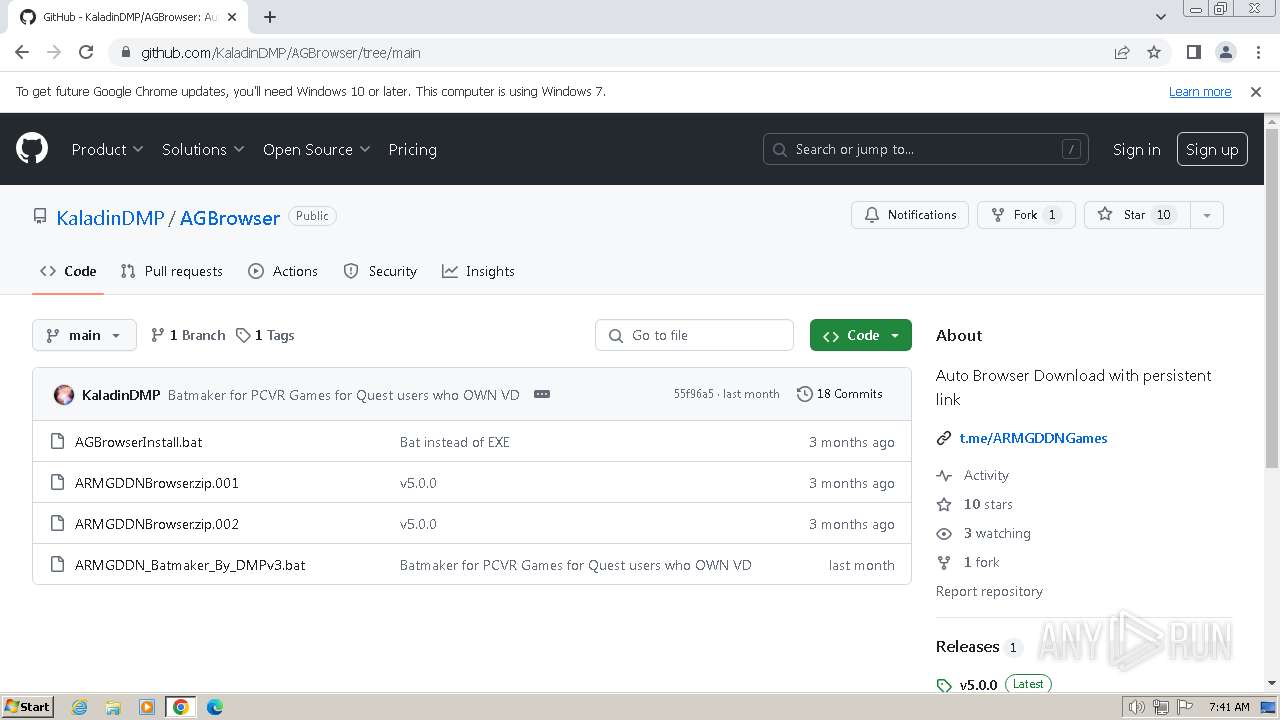
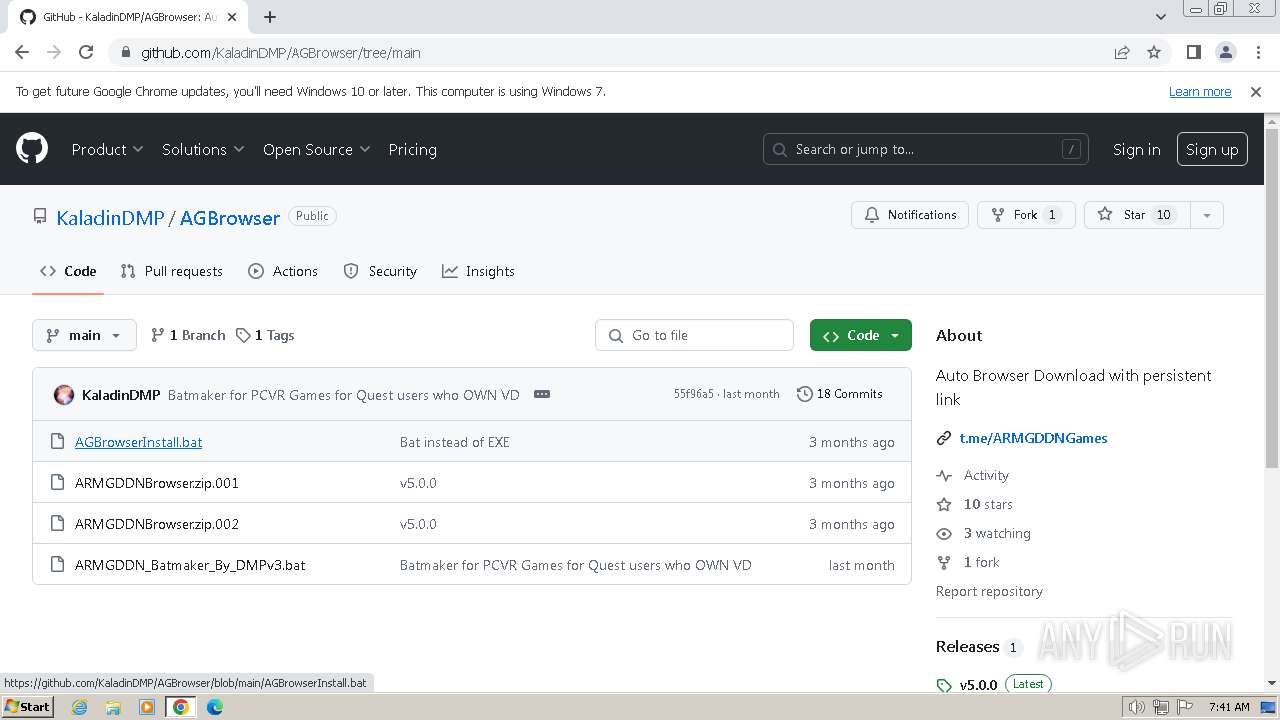
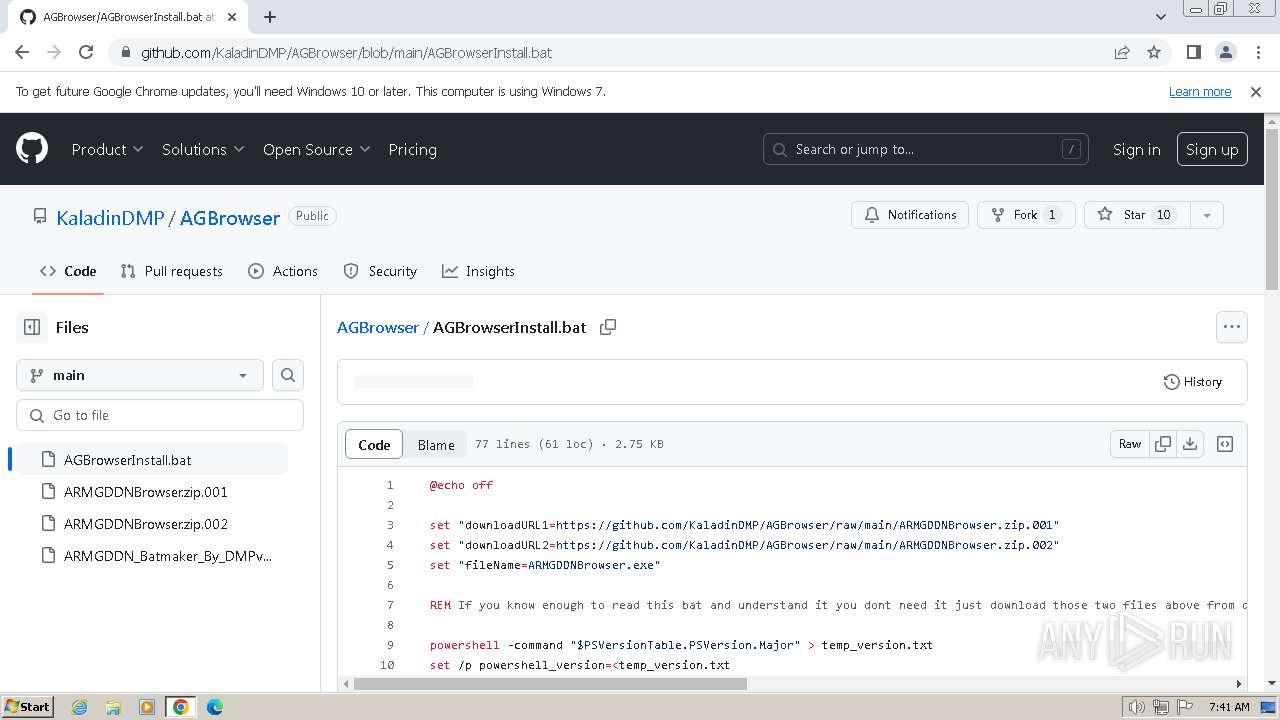
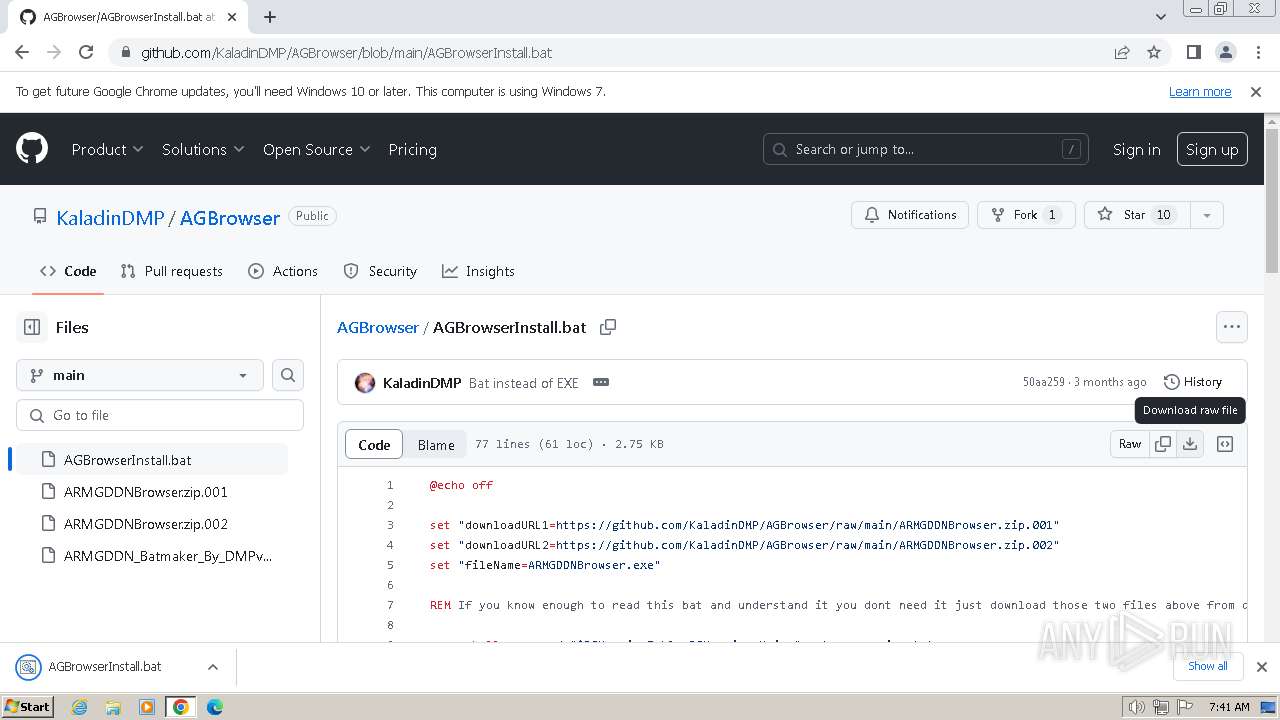
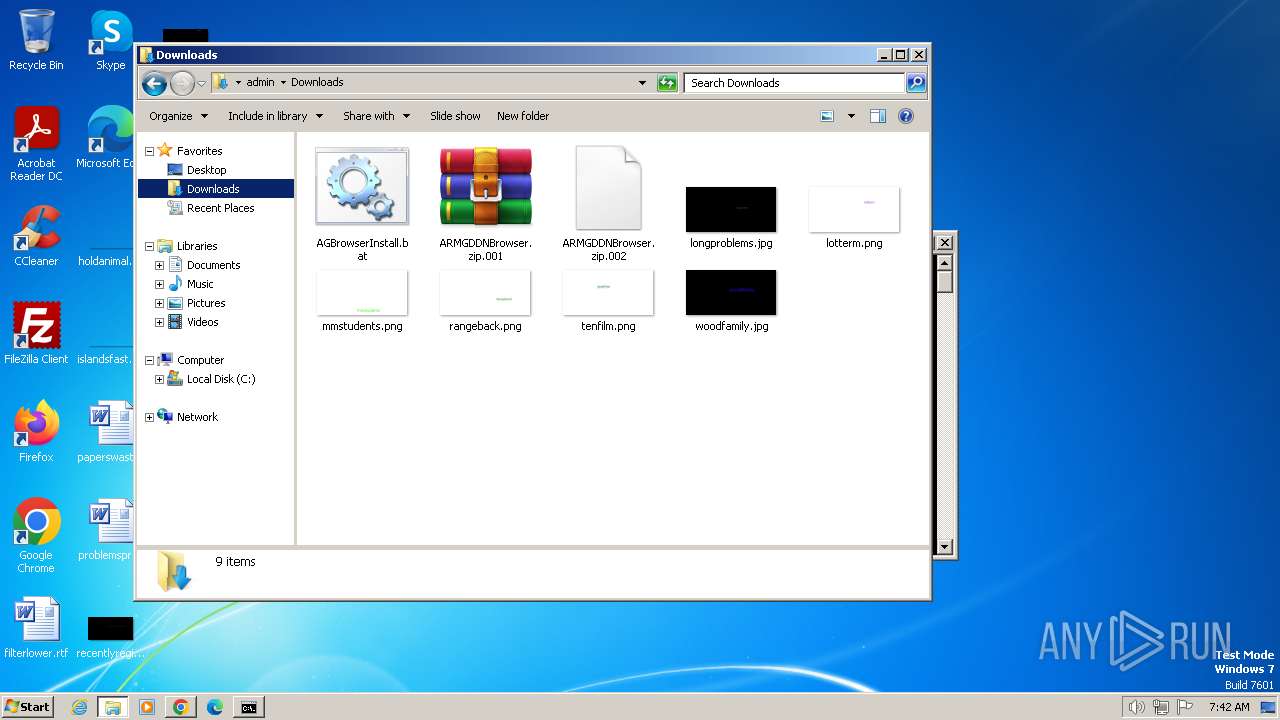
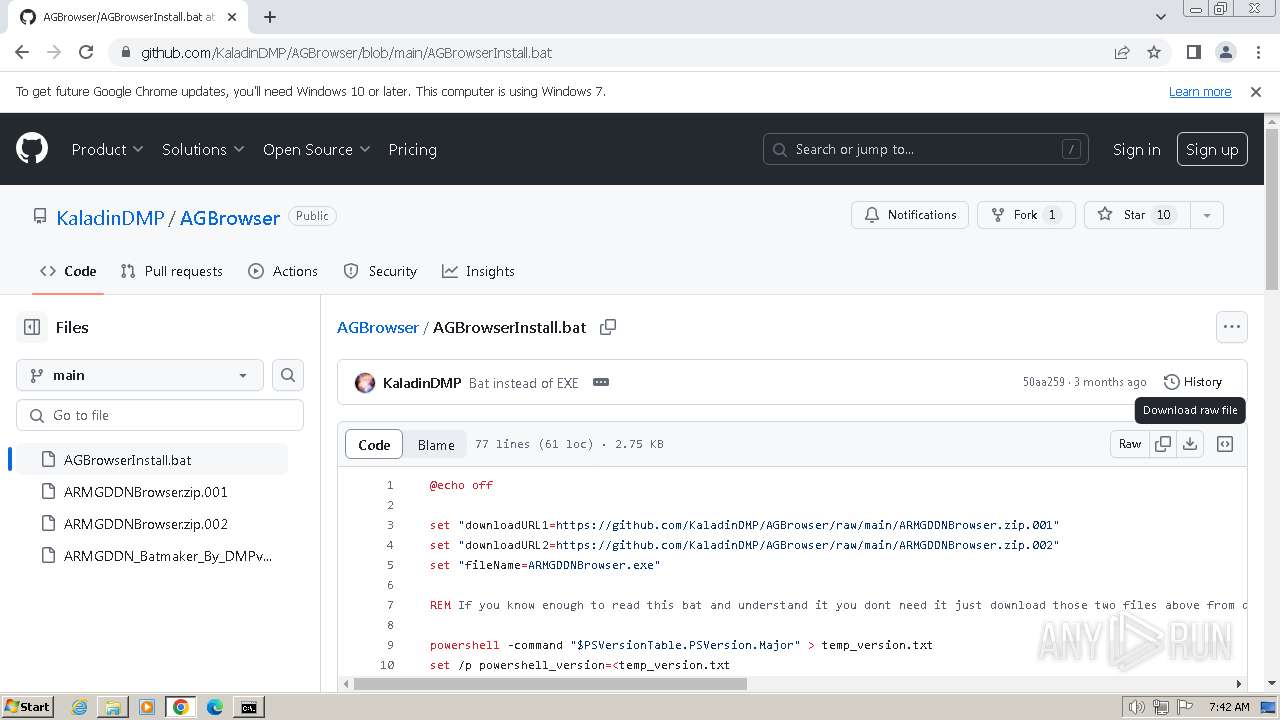
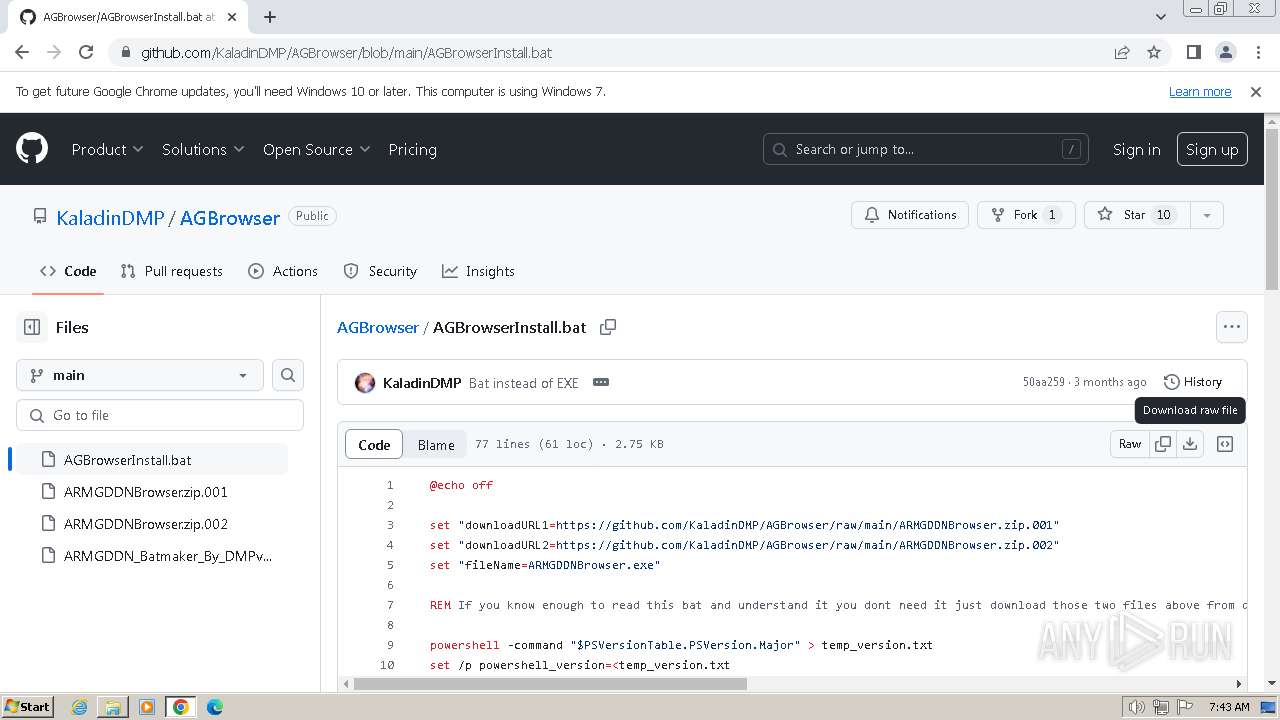
| URL: | https://github.com/KaladinDMP/AGBrowser/blob/main/AGBrowserInstall.bat |
| Full analysis: | https://app.any.run/tasks/2effd967-12cd-4a14-a56b-73928f0d7a37 |
| Verdict: | Malicious activity |
| Analysis date: | April 17, 2024, 06:40:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D3EDBF21C3FDEE5755AB6D60061781F2 |
| SHA1: | 4BF29960A8B5F94185BFDD43A3B2C7E9AF93D217 |
| SHA256: | F80D9B2BDAAB1326564E50295F355D725E26F5A92886CD4DE1276443D44E88BE |
| SSDEEP: | 3:N8tEdtoMt5IKzER5aWErY:2uXo+IKzs5aWEs |
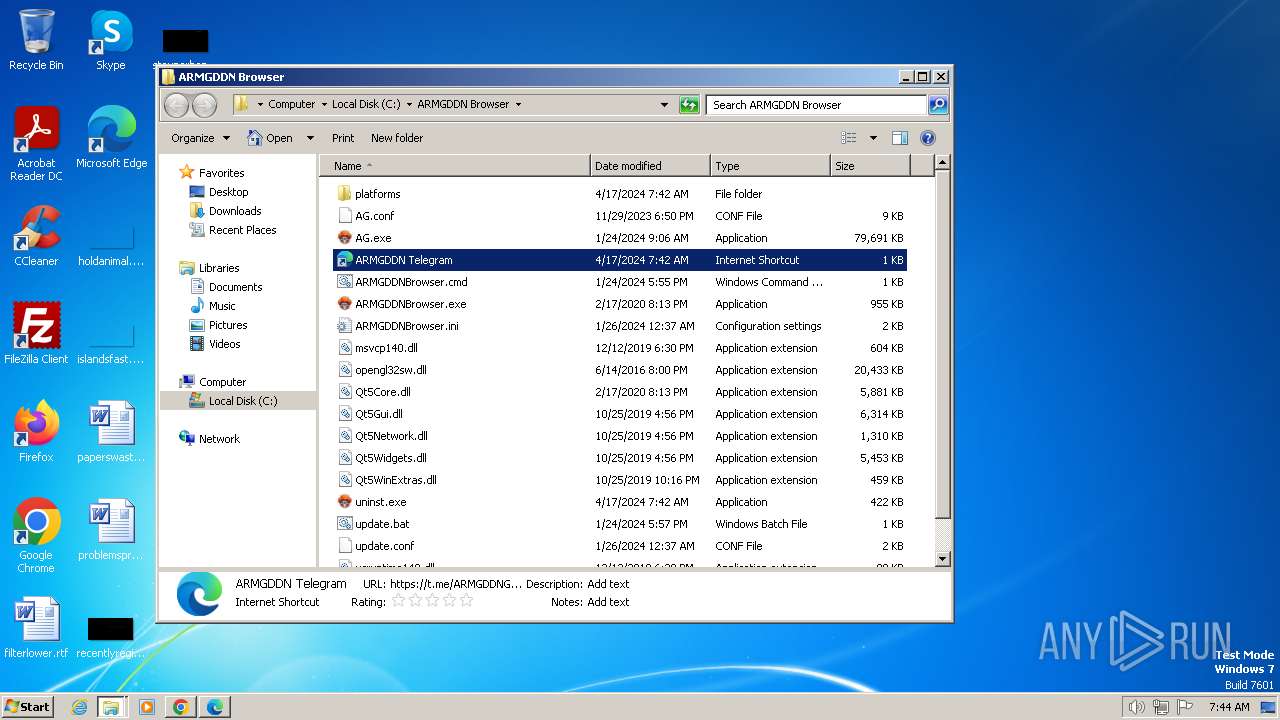
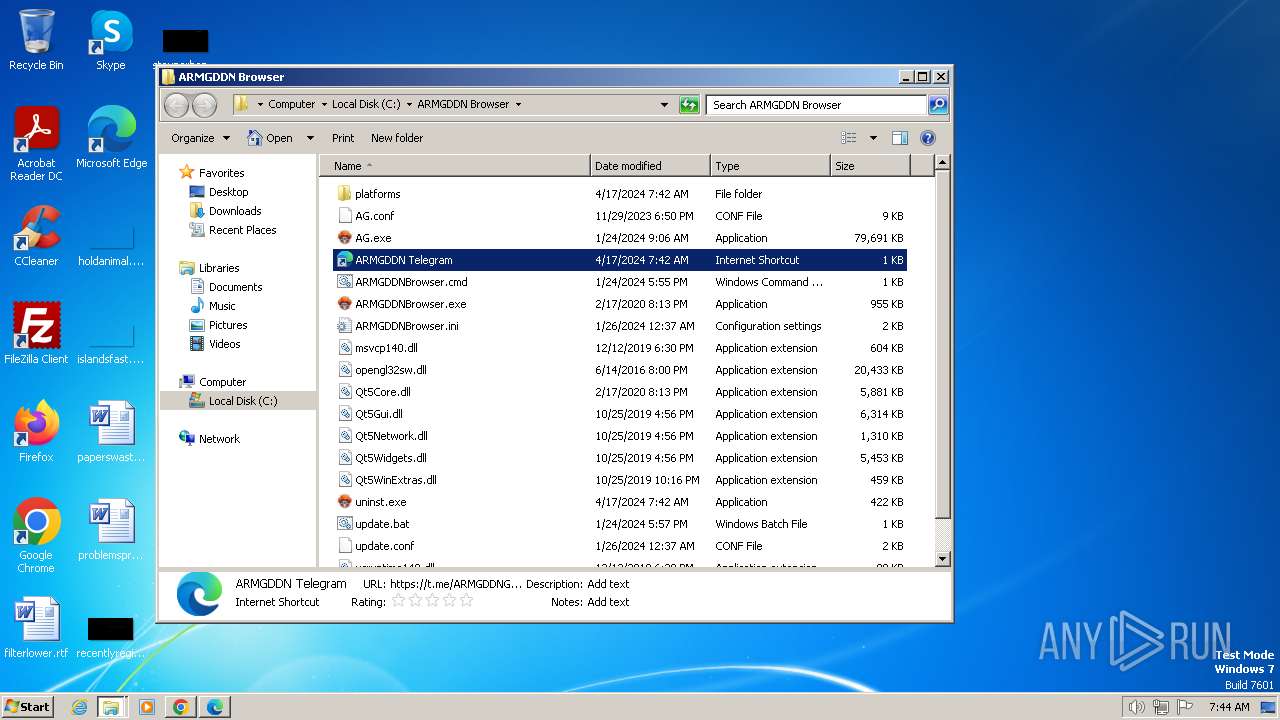
MALICIOUS
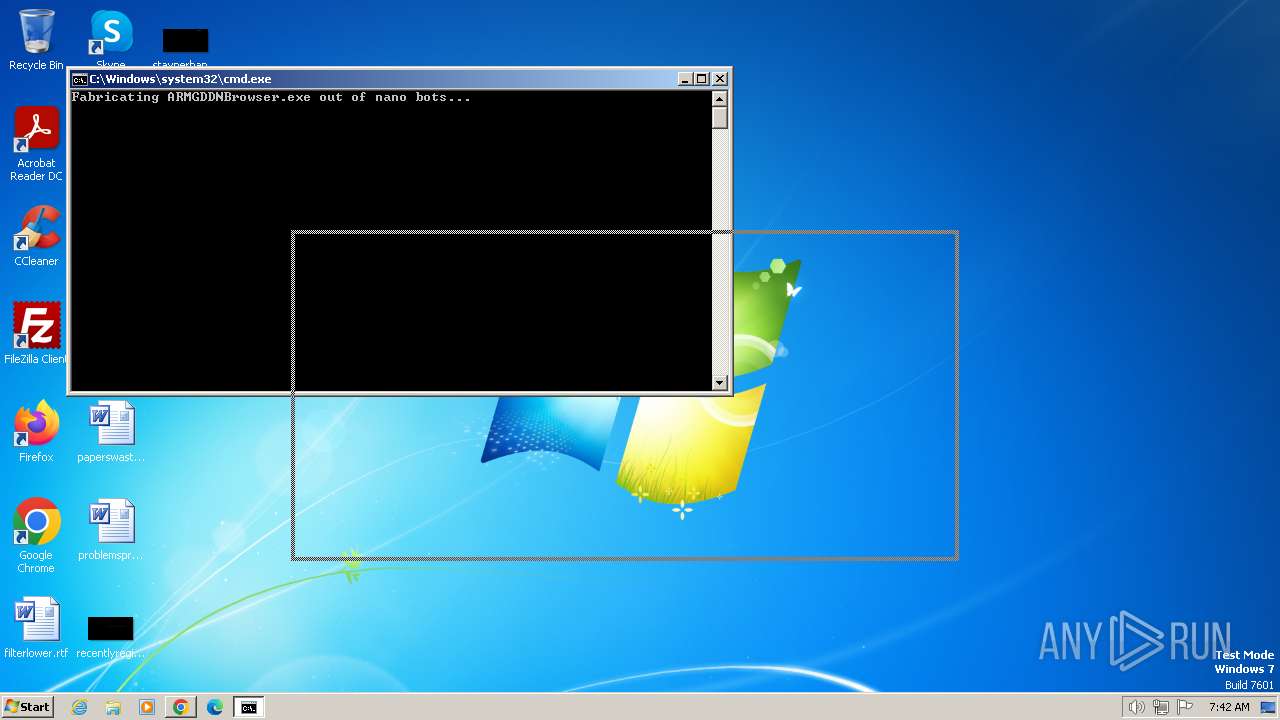
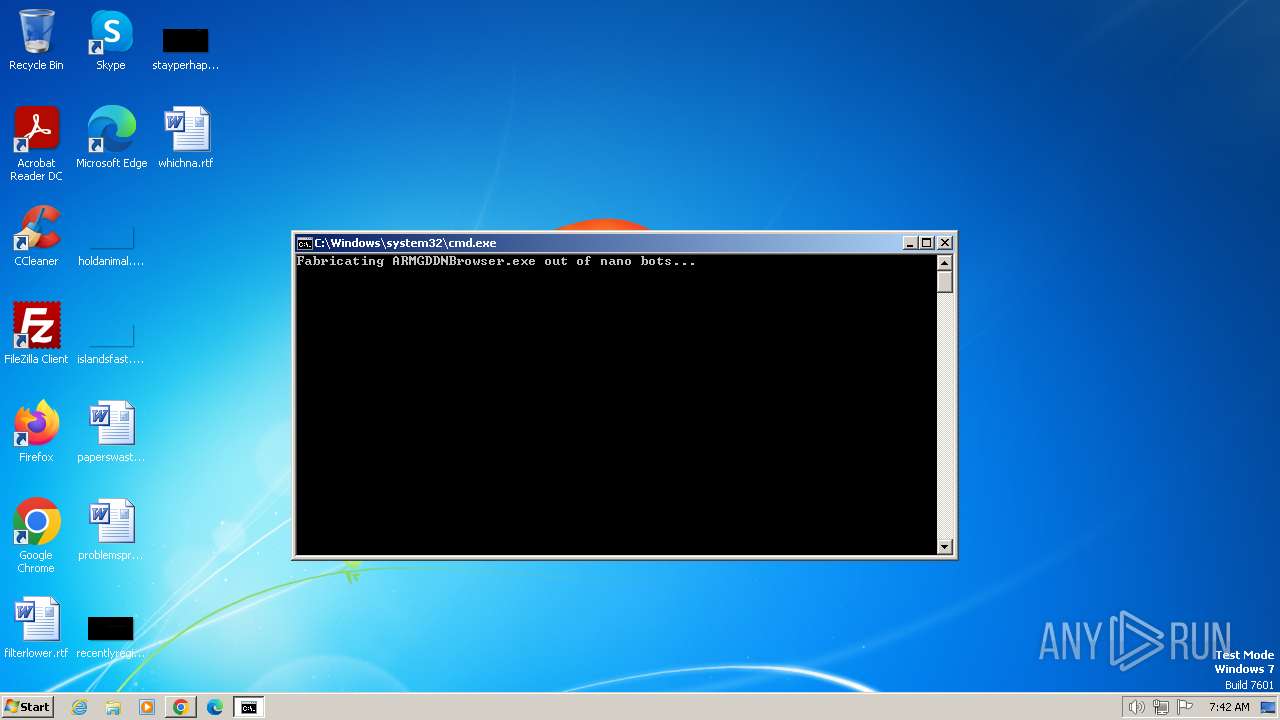
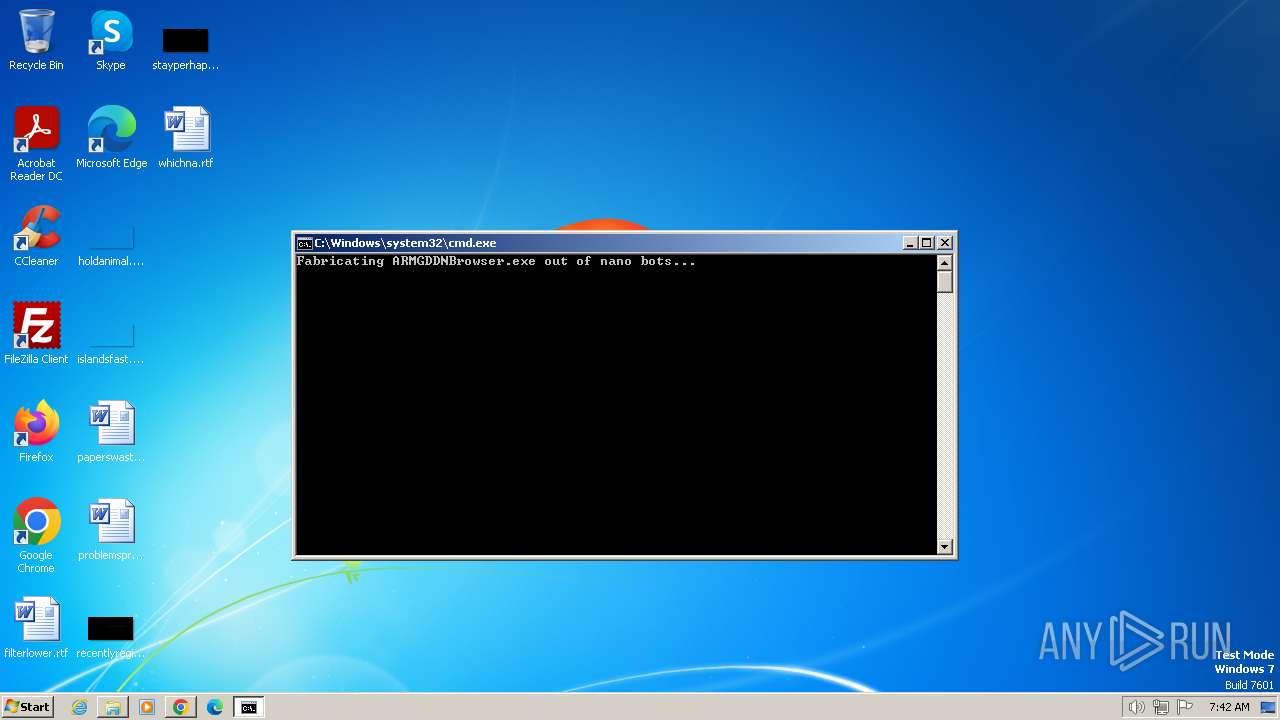
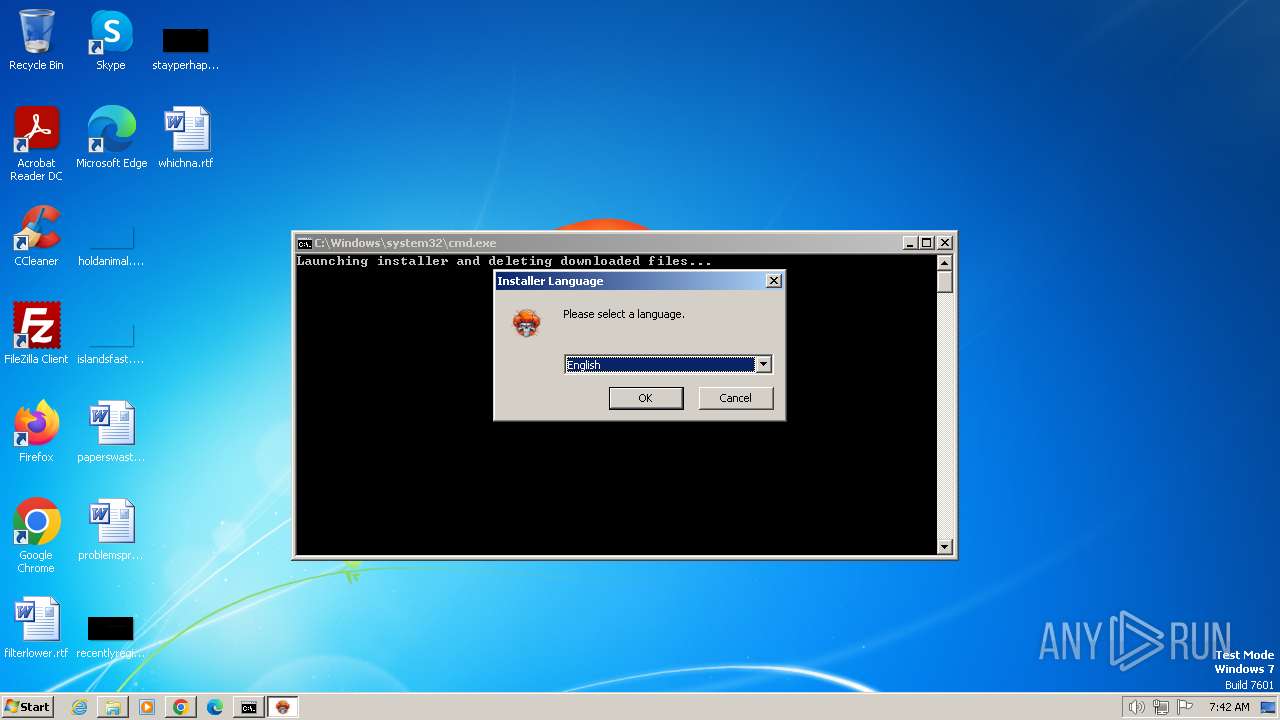
Starts CMD.EXE for commands execution
- chrome.exe (PID: 920)
Changes powershell execution policy (RemoteSigned)
- cmd.exe (PID: 3368)
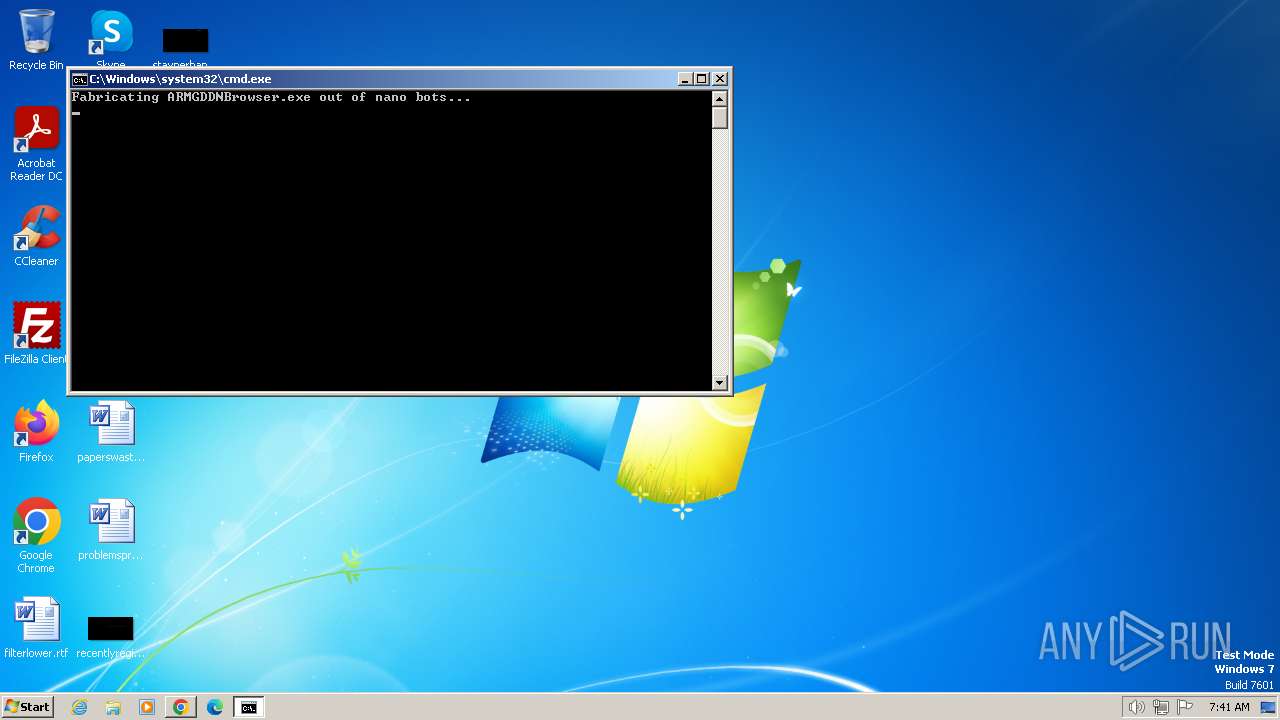
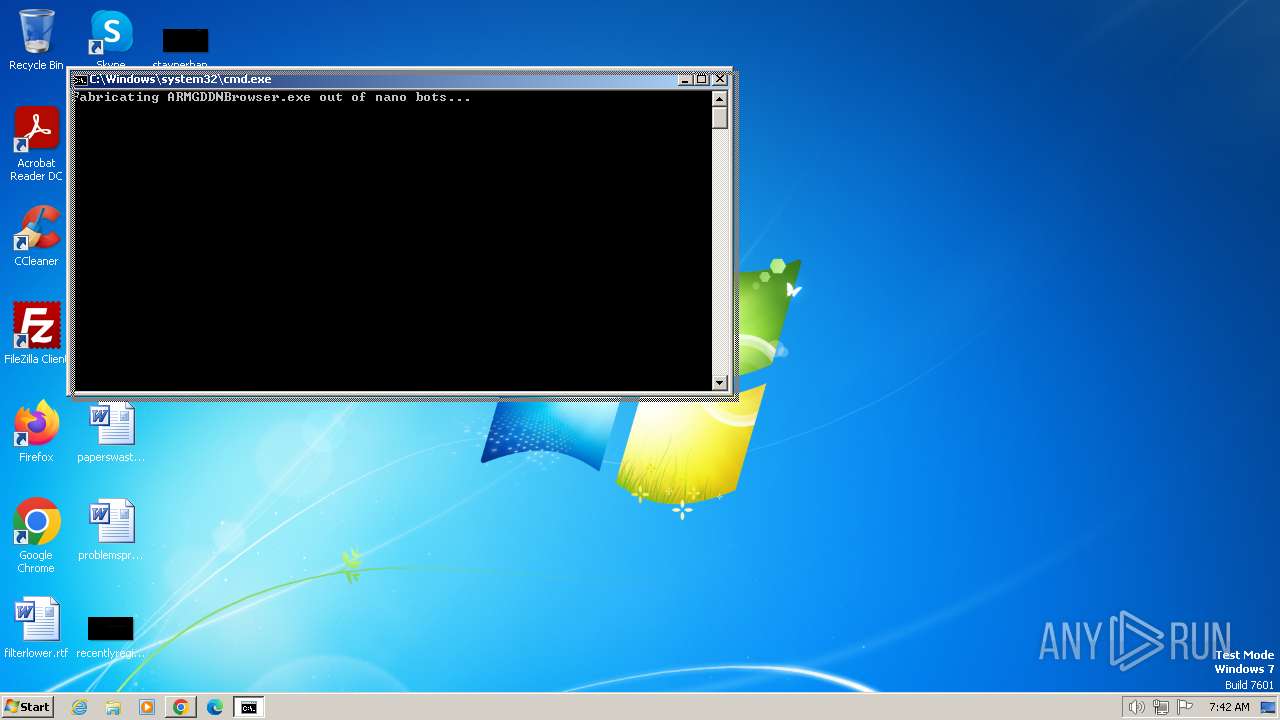
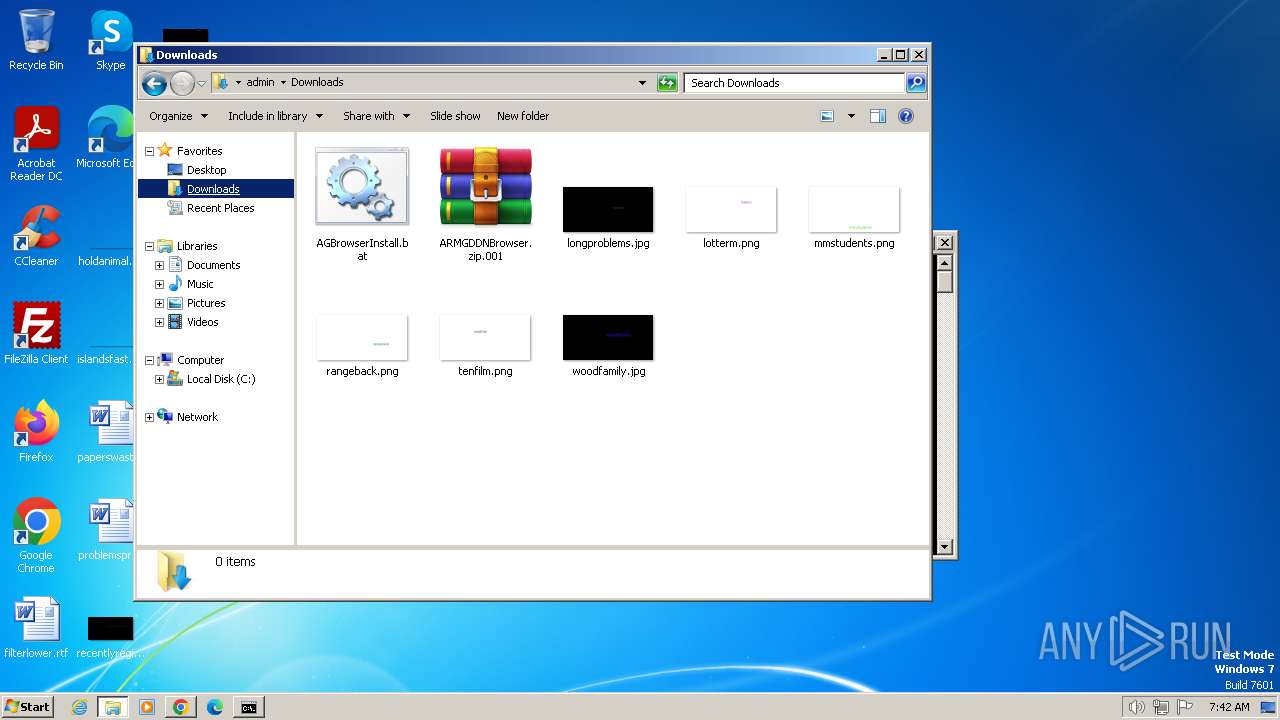
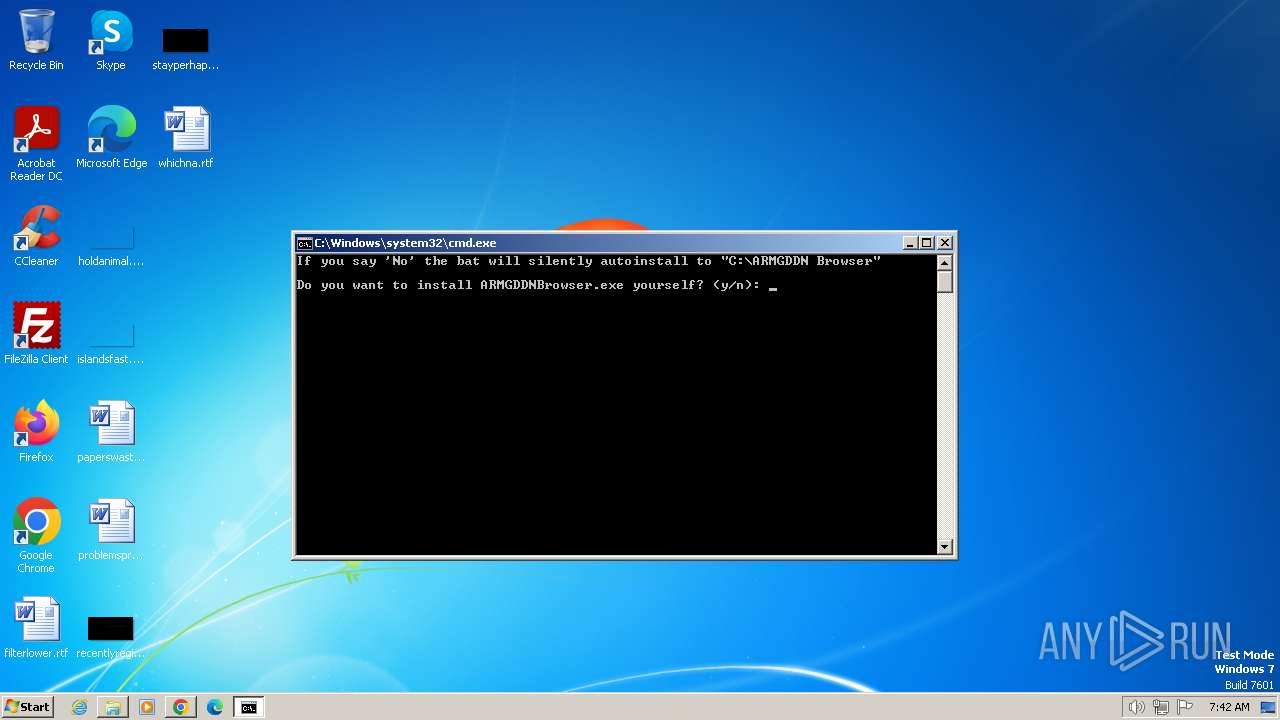
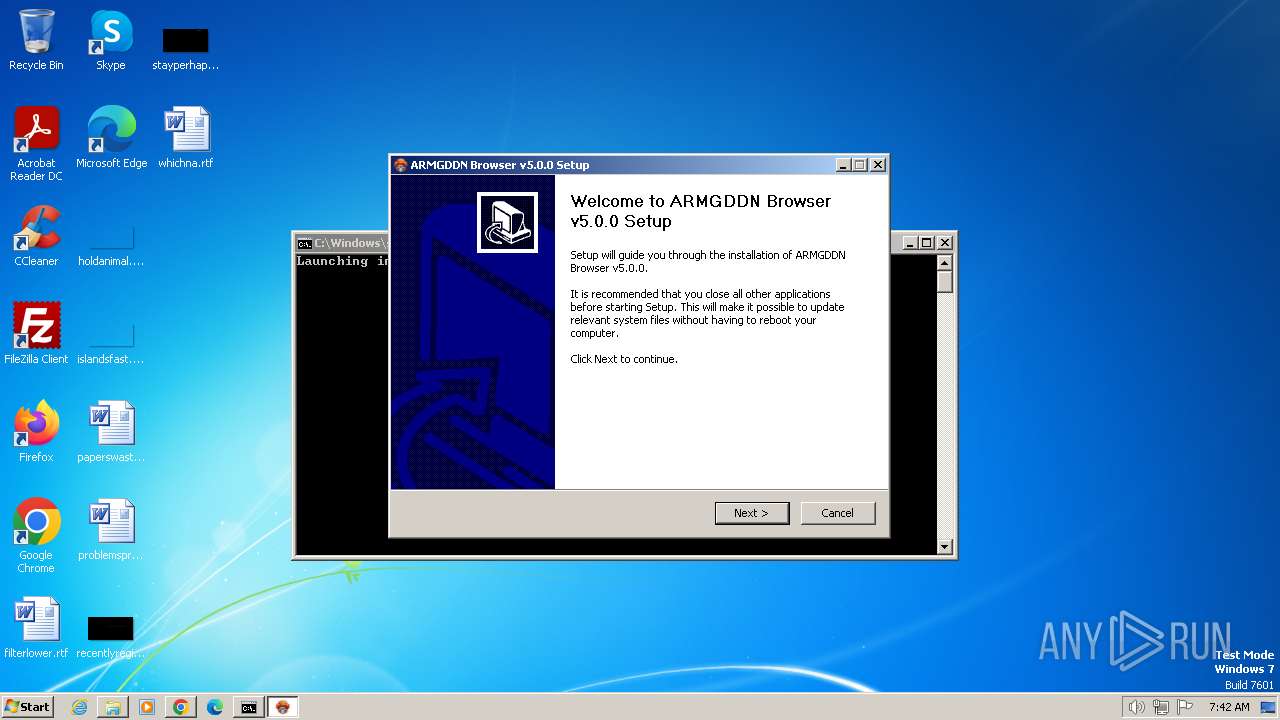
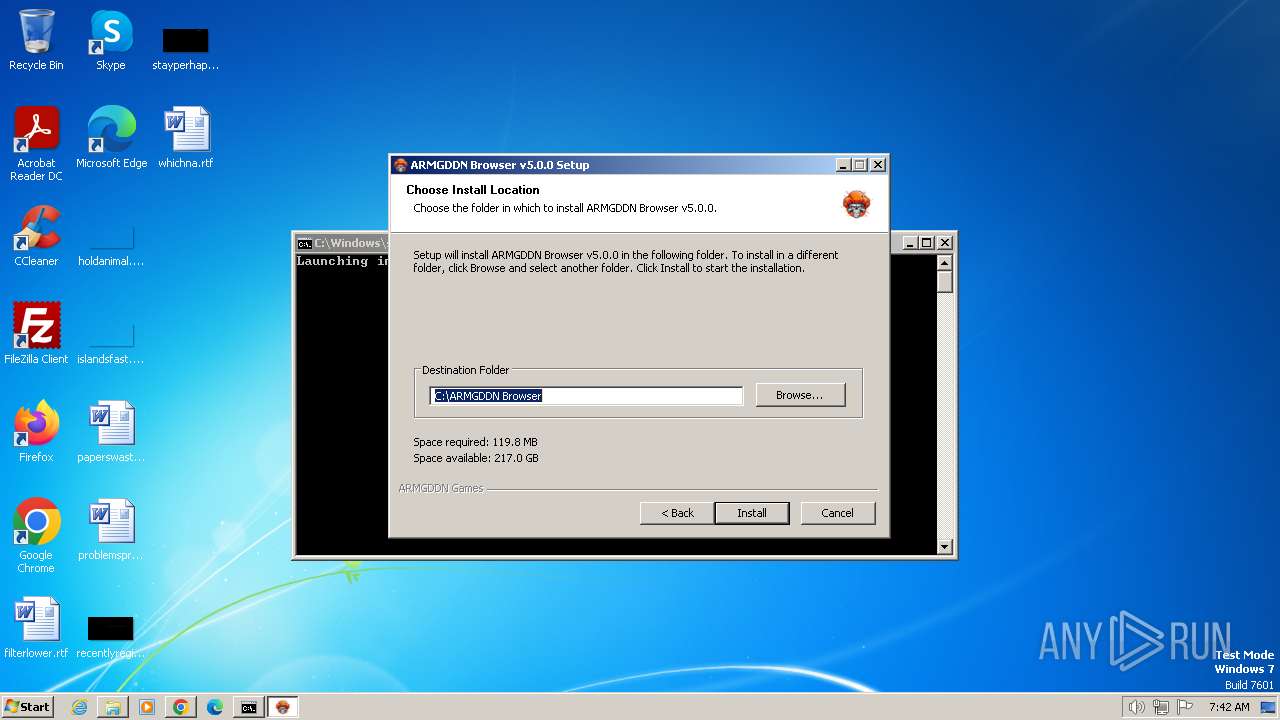
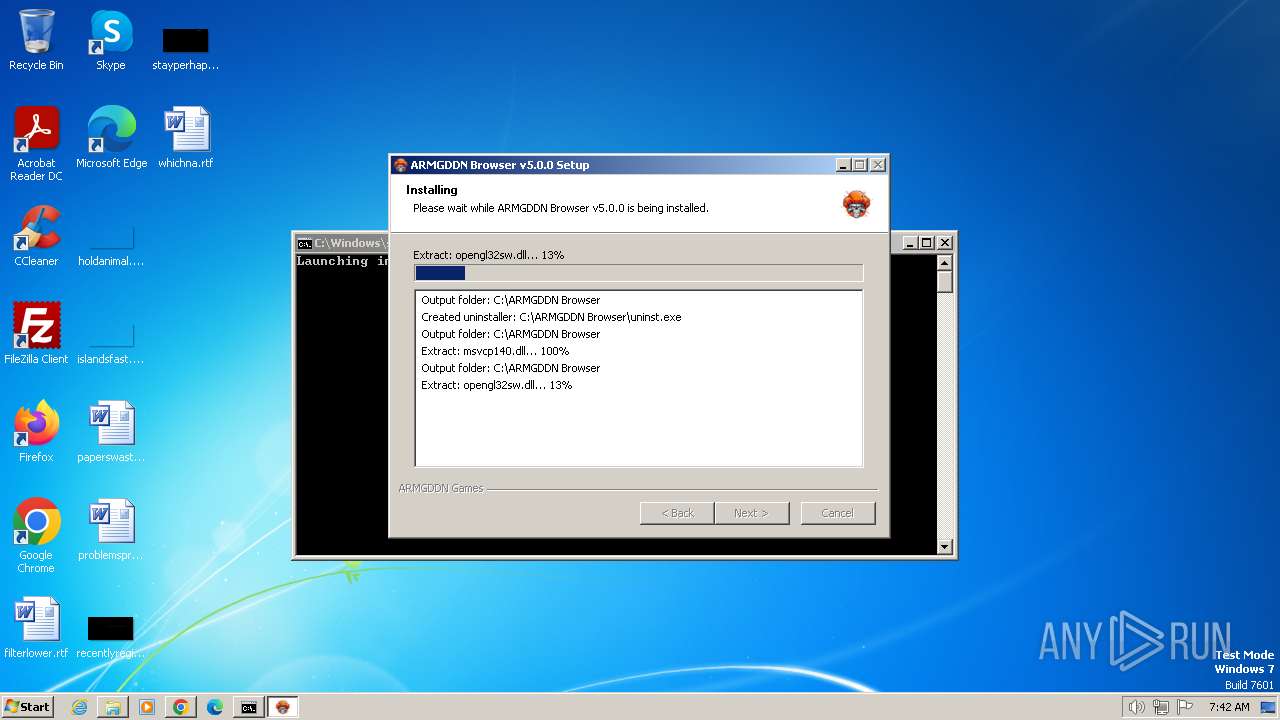
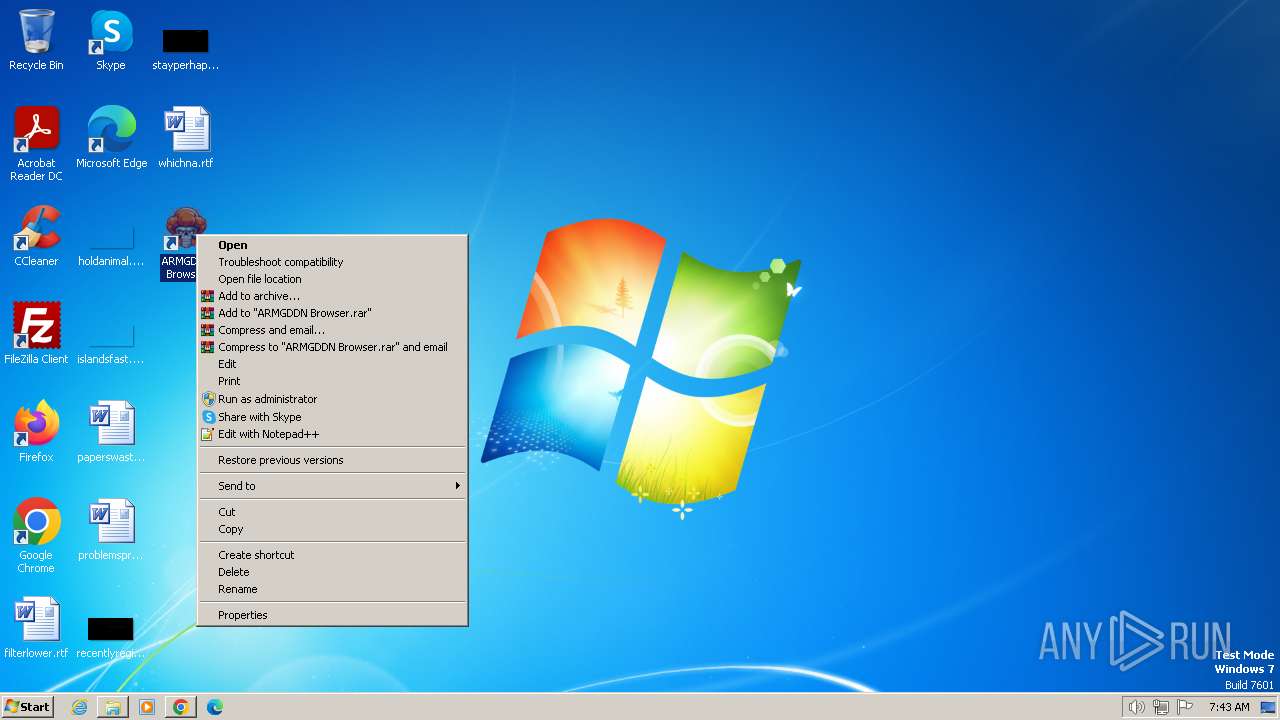
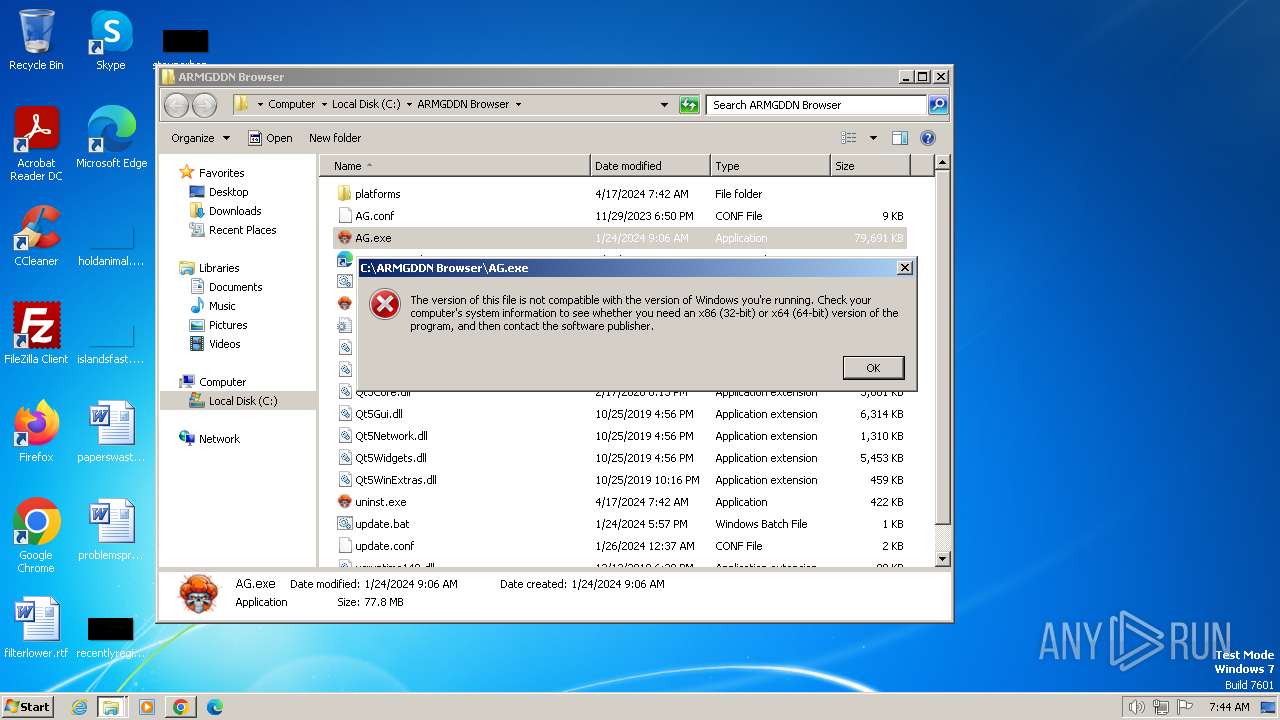
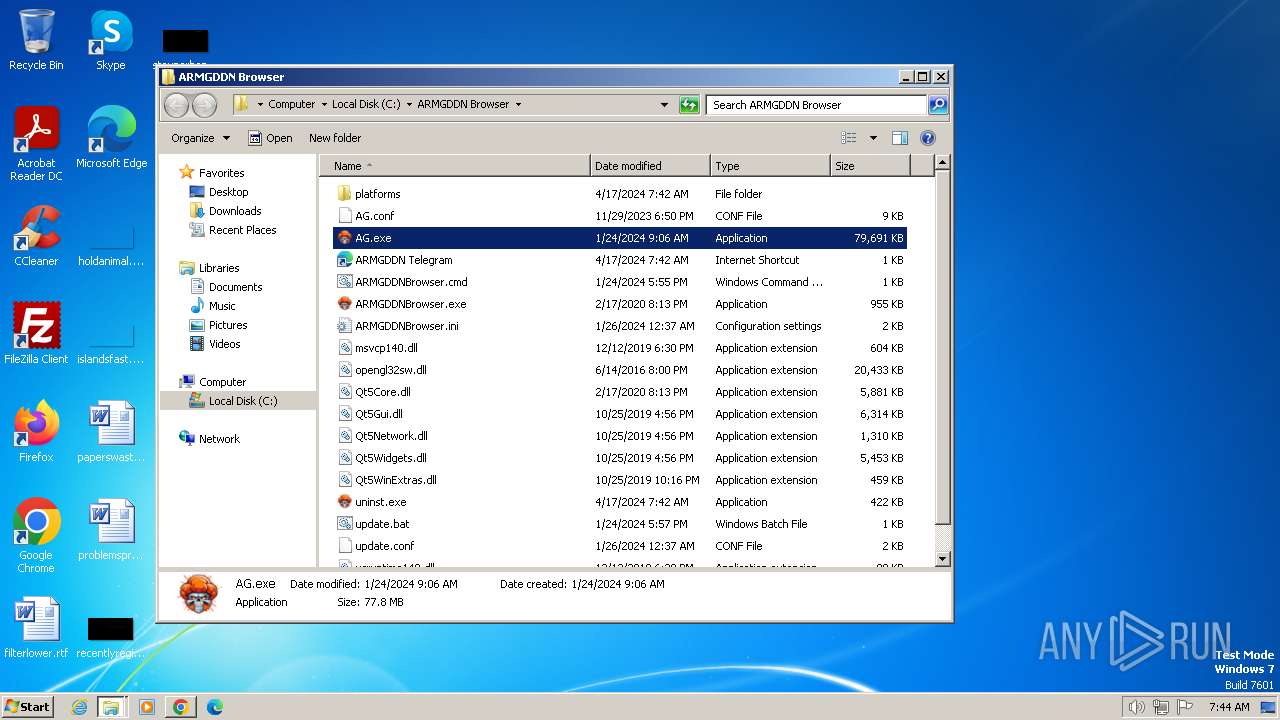
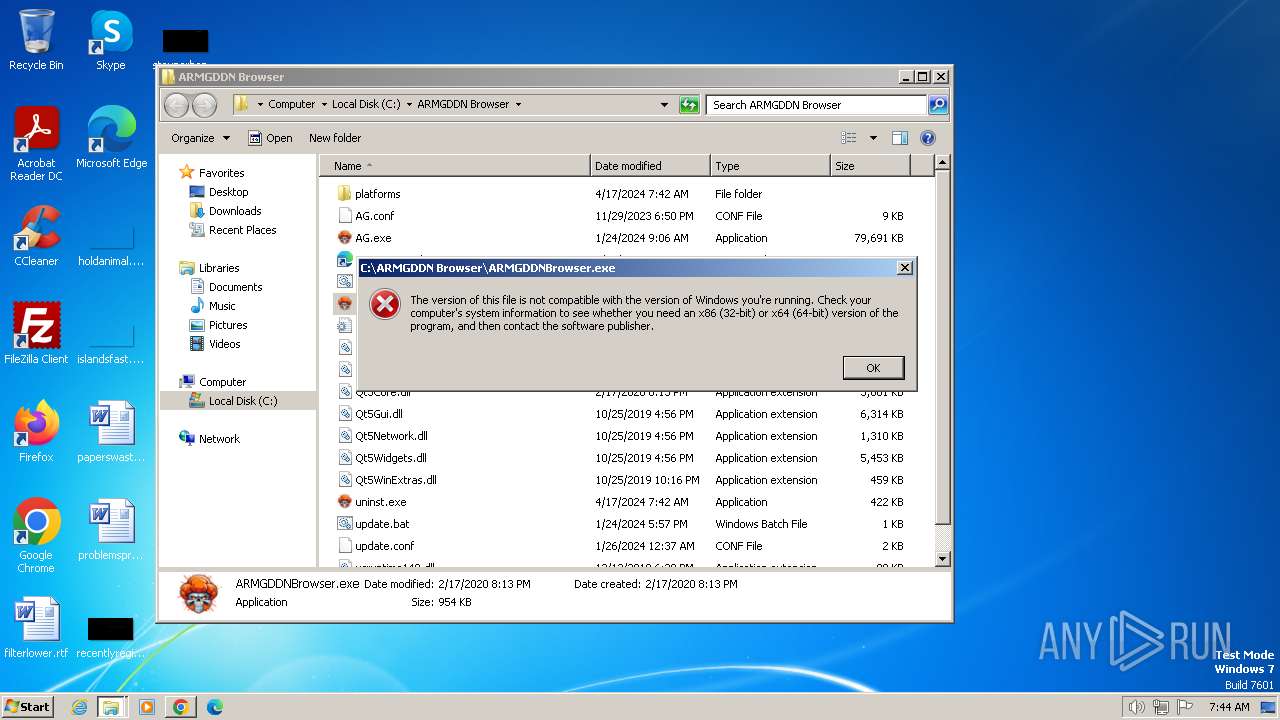
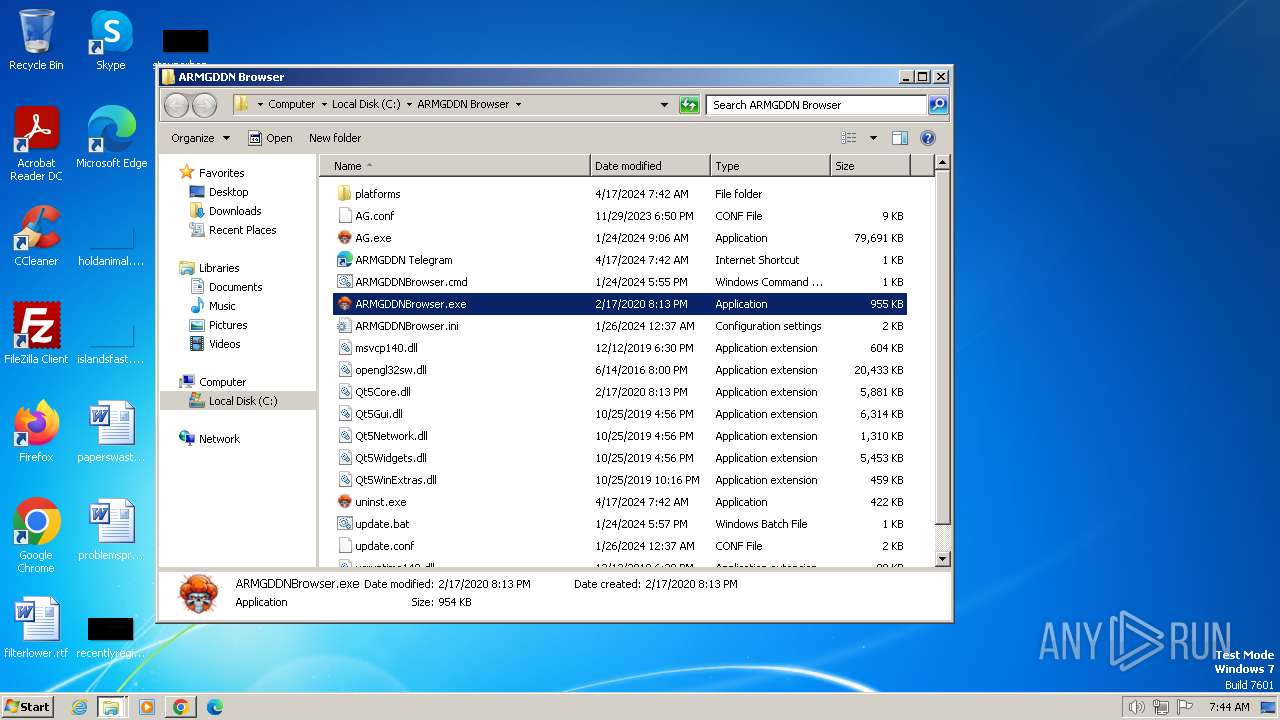
Drops the executable file immediately after the start
- ARMGDDNBrowser.exe (PID: 572)
SUSPICIOUS
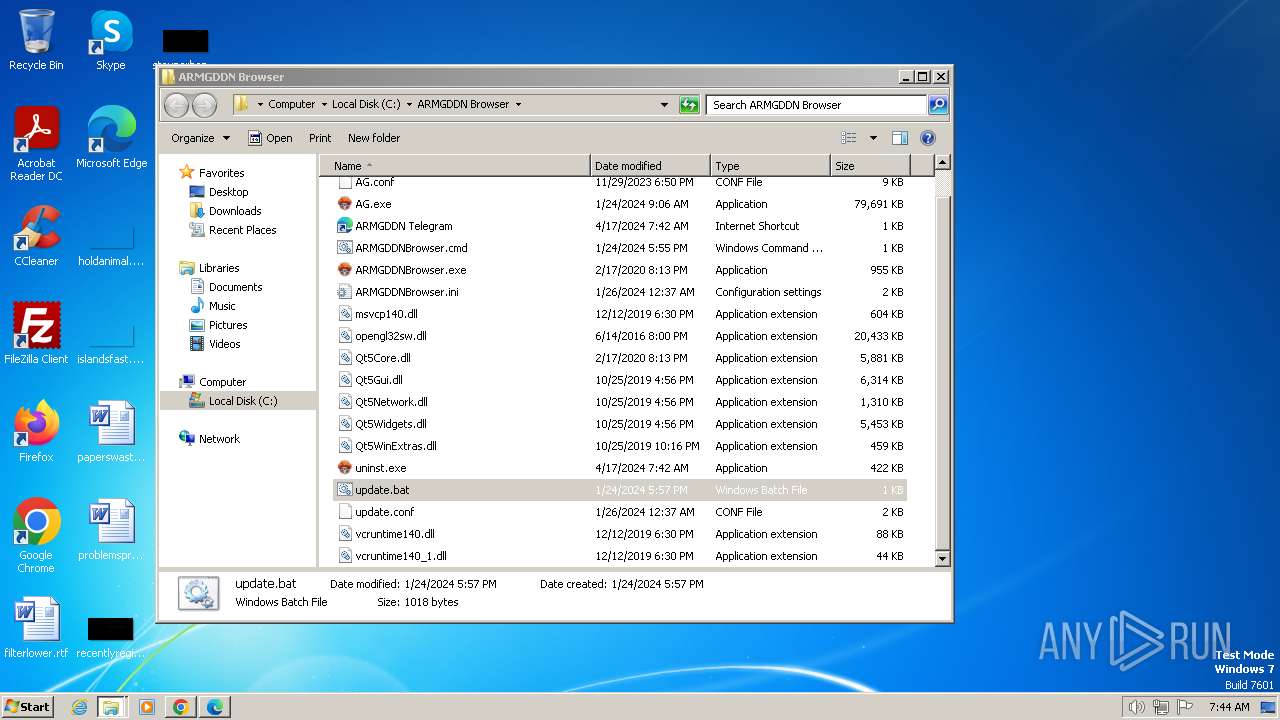
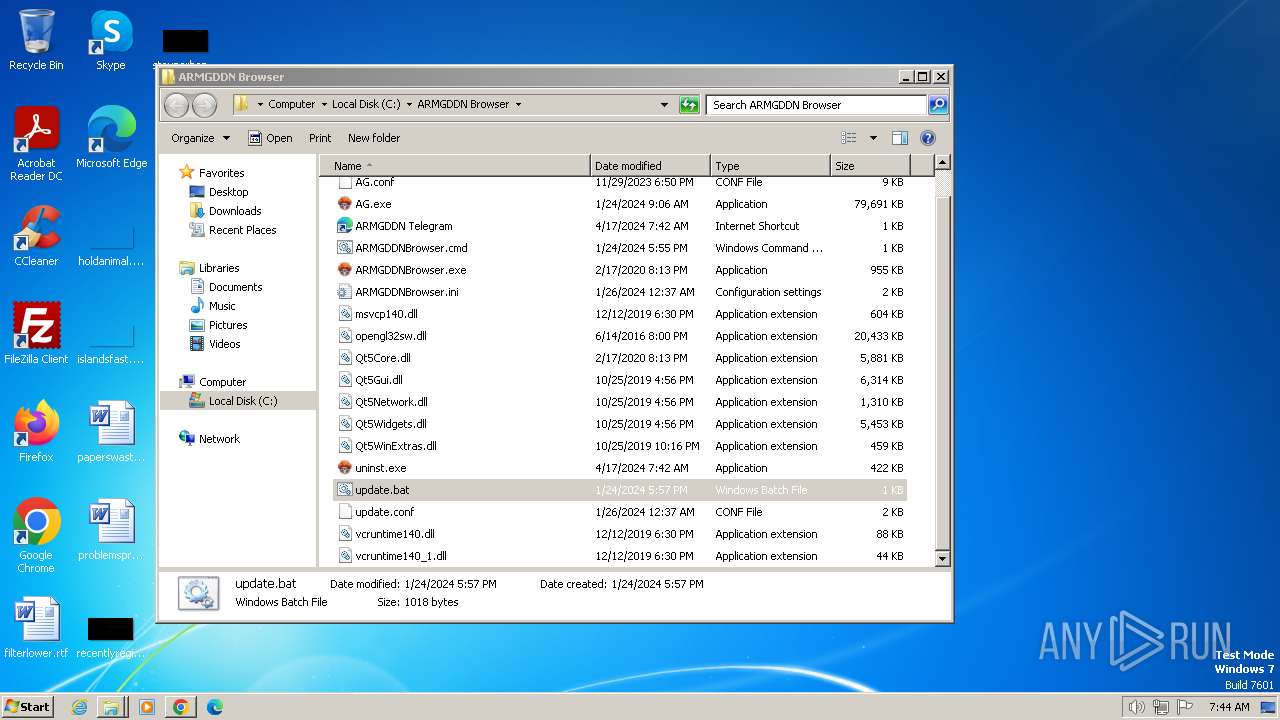
Executing commands from a ".bat" file
- chrome.exe (PID: 920)
- cmd.exe (PID: 2988)
- cmd.exe (PID: 2812)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 3500)
- cmd.exe (PID: 2912)
- cmd.exe (PID: 2364)
- cmd.exe (PID: 3992)
- cmd.exe (PID: 2928)
- cmd.exe (PID: 116)
Reads the Internet Settings
- powershell.exe (PID: 2292)
- powershell.exe (PID: 4060)
- powershell.exe (PID: 2244)
- ARMGDDNBrowser.exe (PID: 572)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 2292)
The Powershell connects to the Internet
- powershell.exe (PID: 4060)
- powershell.exe (PID: 2244)
Probably download files using WebClient
- cmd.exe (PID: 3368)
Unusual connection from system programs
- powershell.exe (PID: 4060)
- powershell.exe (PID: 2244)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3368)
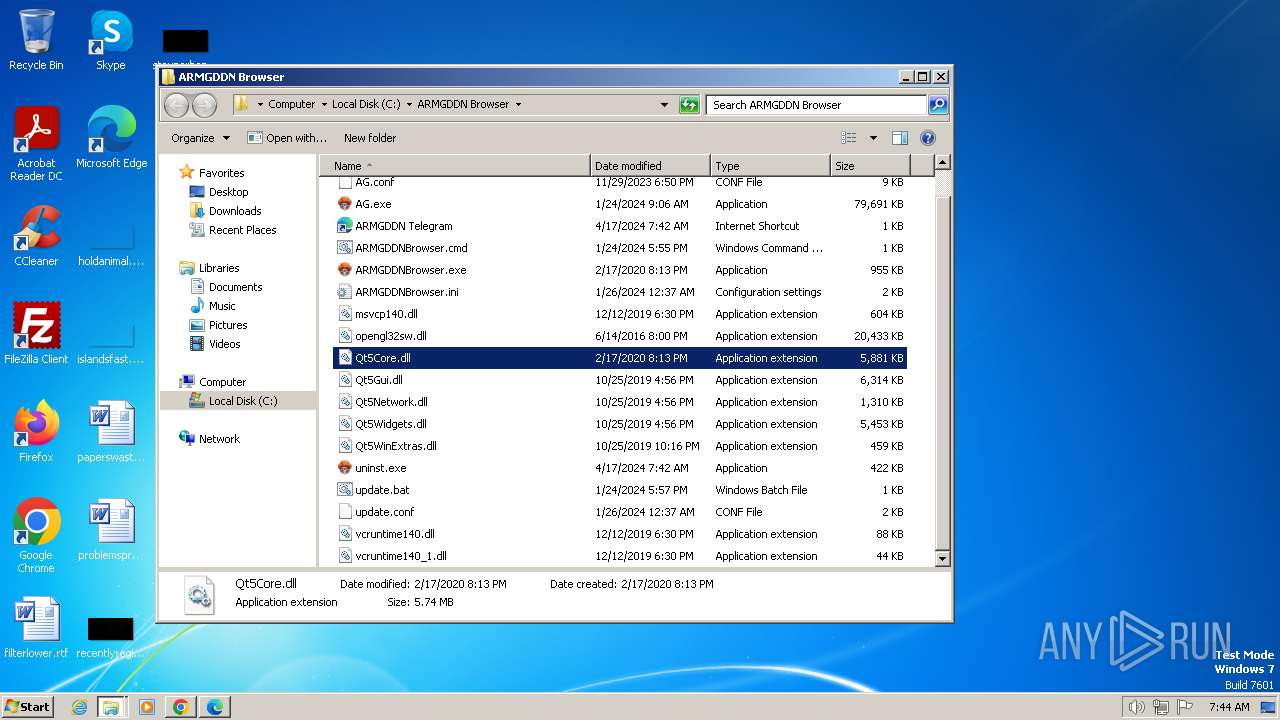
The process drops C-runtime libraries
- ARMGDDNBrowser.exe (PID: 572)
The executable file from the user directory is run by the CMD process
- ARMGDDNBrowser.exe (PID: 572)
The process creates files with name similar to system file names
- ARMGDDNBrowser.exe (PID: 572)
Executable content was dropped or overwritten
- ARMGDDNBrowser.exe (PID: 572)
Process drops legitimate windows executable
- ARMGDDNBrowser.exe (PID: 572)
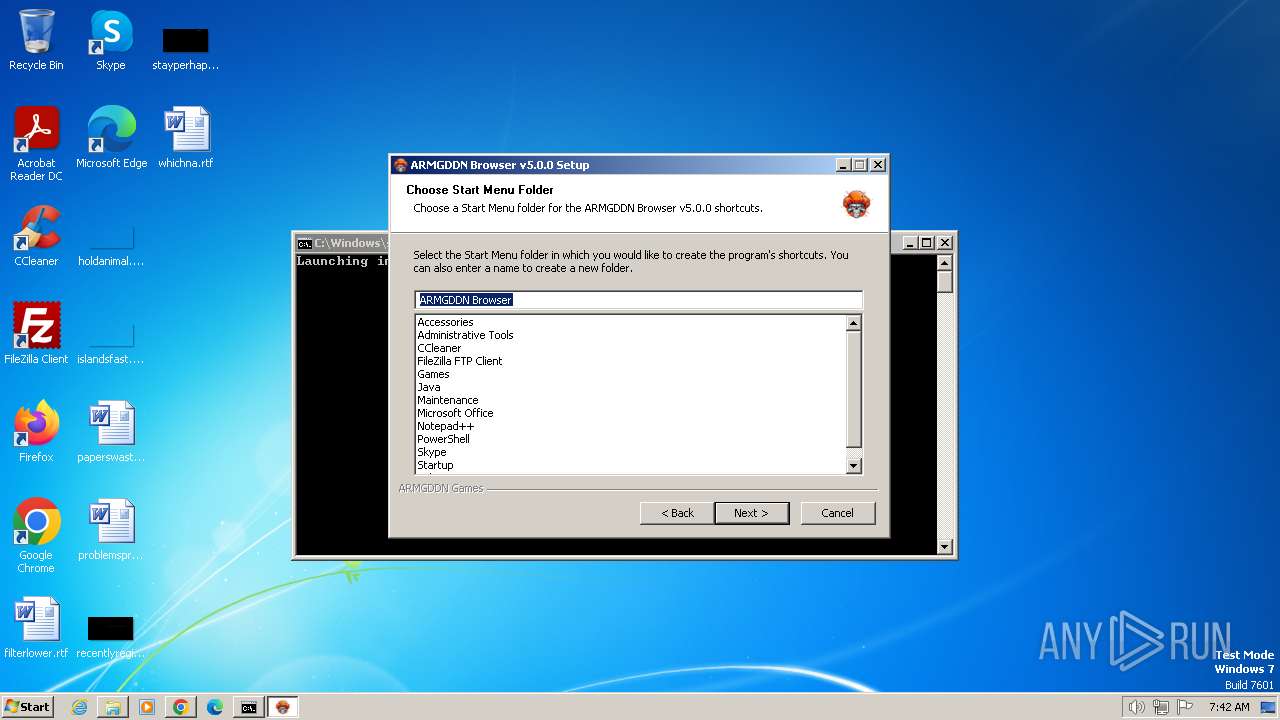
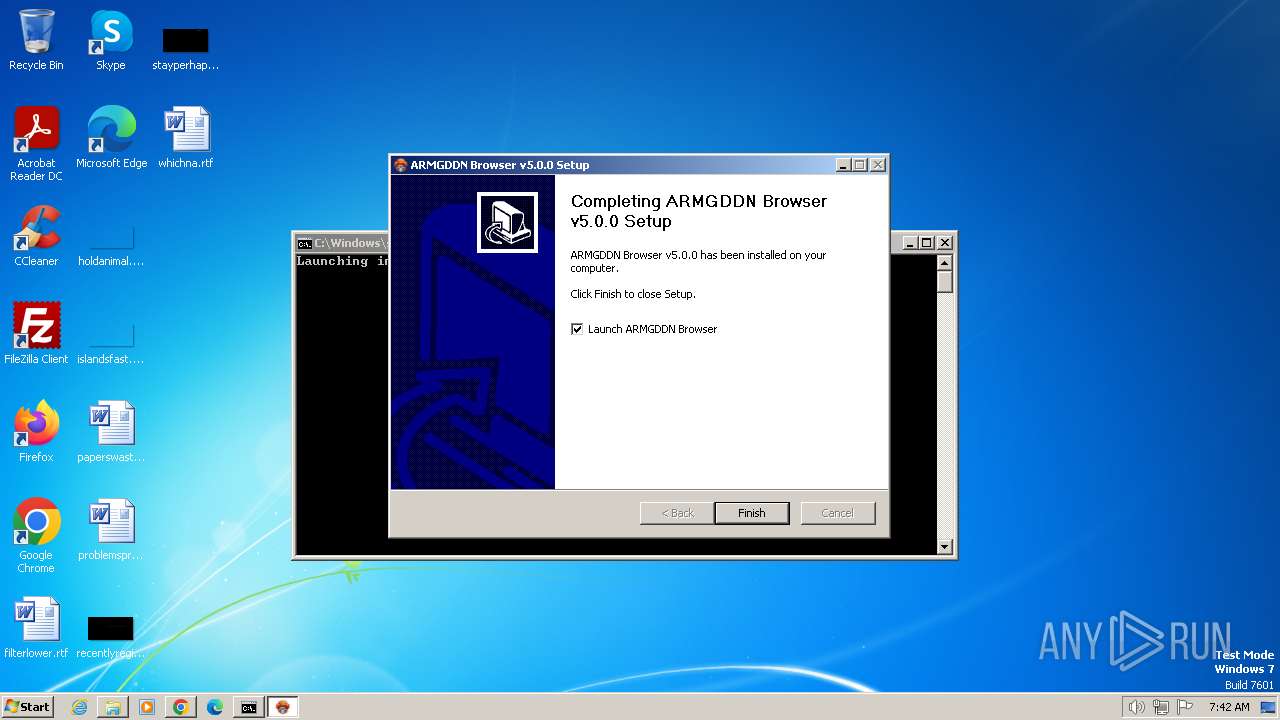
Creates a software uninstall entry
- ARMGDDNBrowser.exe (PID: 572)
Malware-specific behavior (creating "System.dll" in Temp)
- ARMGDDNBrowser.exe (PID: 572)
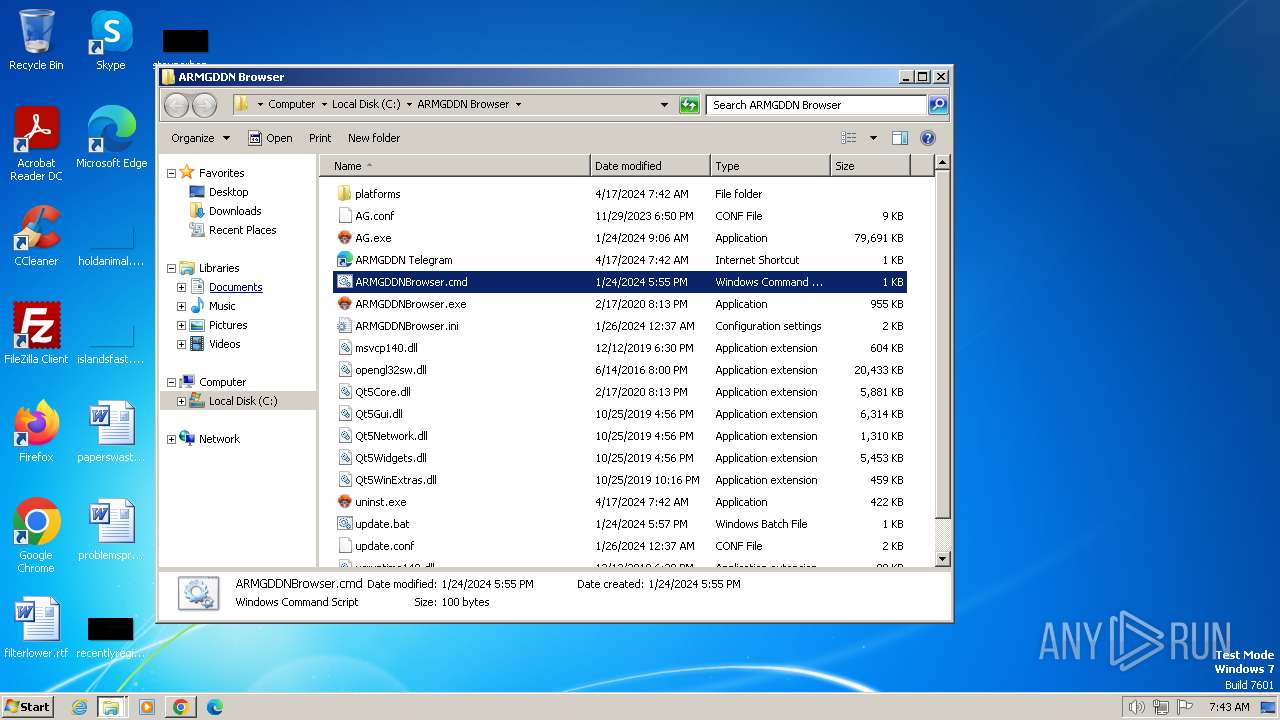
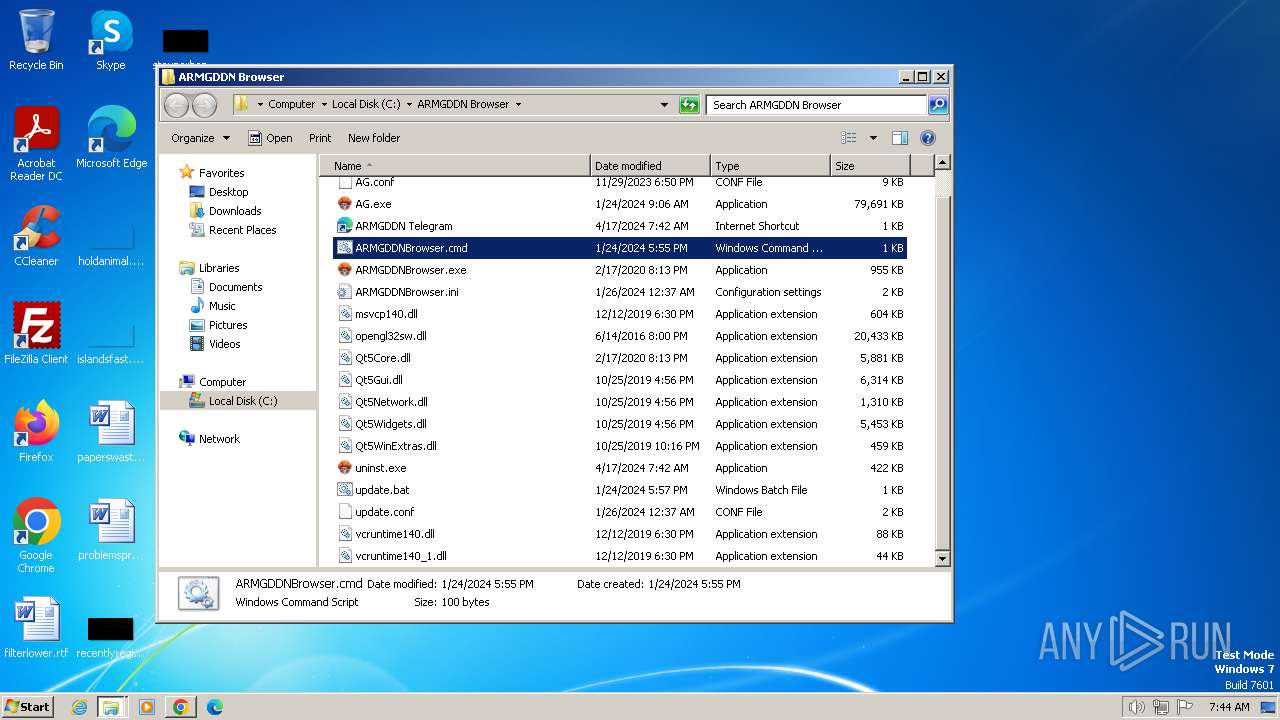
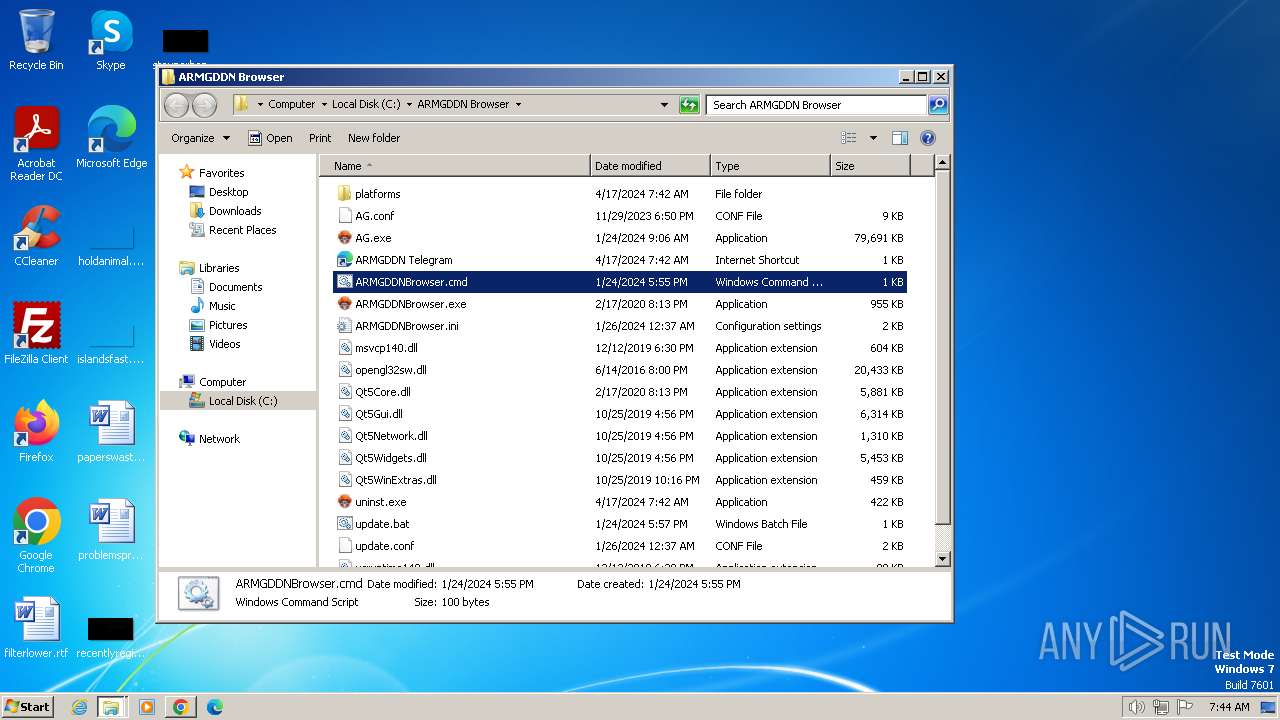
Executing commands from ".cmd" file
- ARMGDDNBrowser.exe (PID: 572)
Starts CMD.EXE for commands execution
- ARMGDDNBrowser.exe (PID: 572)
- cmd.exe (PID: 2988)
- cmd.exe (PID: 2812)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 2912)
- cmd.exe (PID: 2364)
- cmd.exe (PID: 3992)
- cmd.exe (PID: 2928)
- cmd.exe (PID: 3500)
- cmd.exe (PID: 116)
Reads security settings of Internet Explorer
- ARMGDDNBrowser.exe (PID: 572)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 3980)
Application launched itself
- cmd.exe (PID: 2988)
- cmd.exe (PID: 2812)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 3500)
- cmd.exe (PID: 2912)
- cmd.exe (PID: 2364)
- cmd.exe (PID: 3992)
- cmd.exe (PID: 2928)
- cmd.exe (PID: 116)
INFO
The process uses the downloaded file
- chrome.exe (PID: 920)
- chrome.exe (PID: 3704)
Application launched itself
- chrome.exe (PID: 920)
- msedge.exe (PID: 1340)
Gets the execution policy for the powershell session
- cmd.exe (PID: 3368)
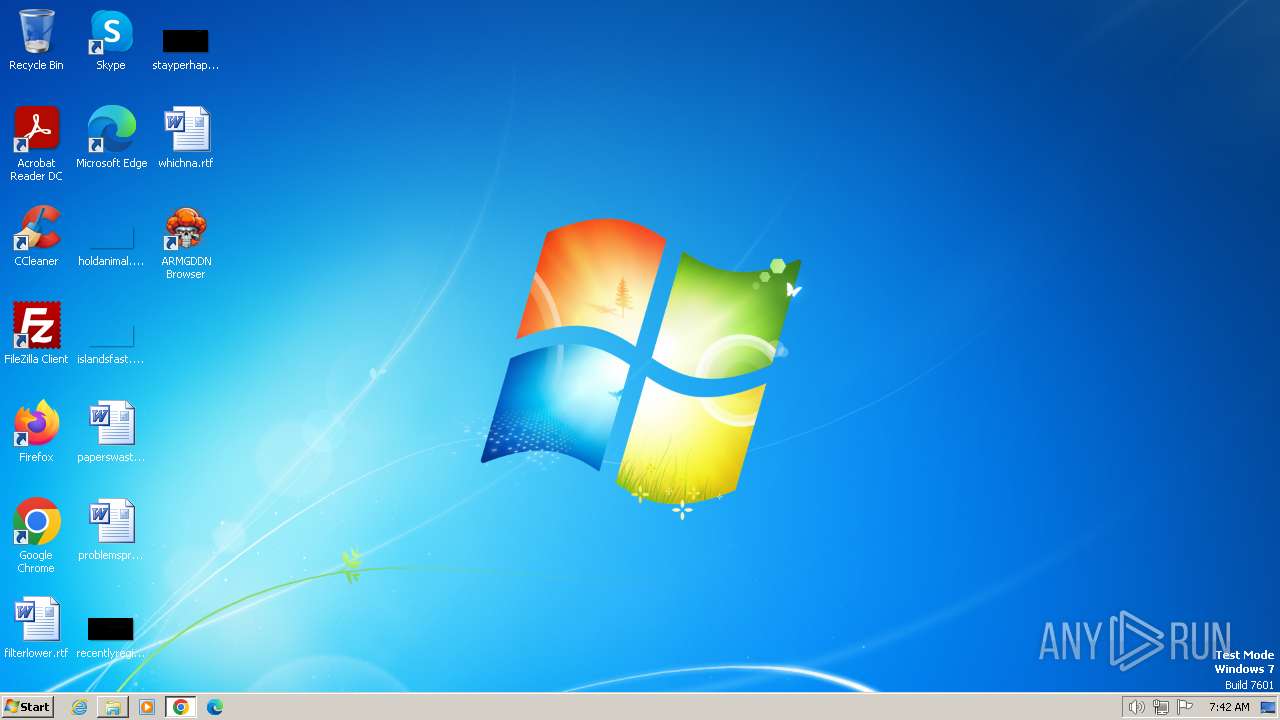
Manual execution by a user
- explorer.exe (PID: 2332)
- cmd.exe (PID: 2988)
- cmd.exe (PID: 2812)
- cmd.exe (PID: 3500)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 3992)
- msedge.exe (PID: 1340)
- cmd.exe (PID: 2928)
- cmd.exe (PID: 116)
- cmd.exe (PID: 2364)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 3980)
- powershell.exe (PID: 3980)
Reads the computer name
- ARMGDDNBrowser.exe (PID: 572)
Create files in a temporary directory
- ARMGDDNBrowser.exe (PID: 572)
Creates files or folders in the user directory
- ARMGDDNBrowser.exe (PID: 572)
Checks supported languages
- ARMGDDNBrowser.exe (PID: 572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
122
Monitored processes
57
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\system32\cmd.exe /c ""C:\ARMGDDN Browser\ARMGDDNBrowser.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 124 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3708 --field-trial-handle=1324,i,6291174844370433804,7136915769964497289,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 268 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3728 --field-trial-handle=1324,i,6291174844370433804,7136915769964497289,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3212 --field-trial-handle=1164,i,8049899880201437585,13841543173673974489,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 572 | ".\ARMGDDNBrowser.exe" | C:\Users\admin\Downloads\ARMGDDNBrowser.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://github.com/KaladinDMP/AGBrowser/blob/main/AGBrowserInstall.bat" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=2412 --field-trial-handle=1324,i,6291174844370433804,7136915769964497289,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bb78b38,0x6bb78b48,0x6bb78b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
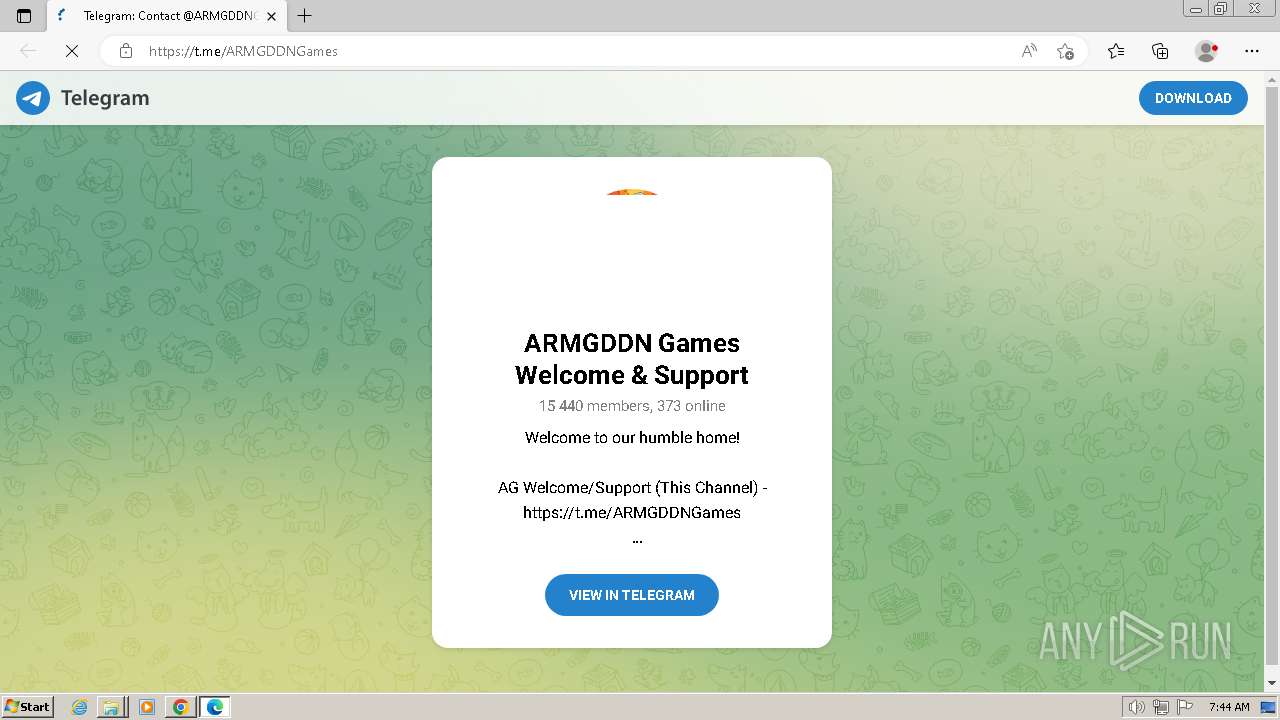
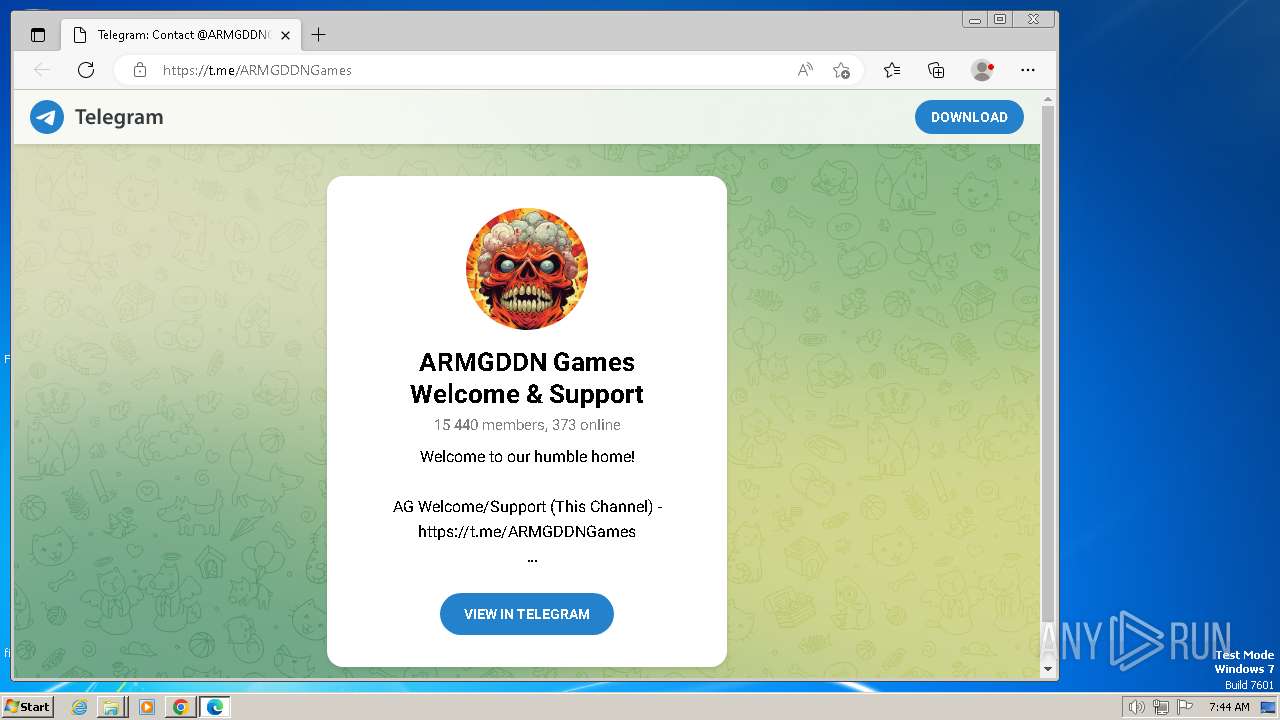
| 1340 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --single-argument https://t.me/ARMGDDNGames | C:\Program Files\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1388 | cmd /c "update.bat & start "" /WAIT /MAX "ARMGDDNBrowser.exe"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
30 546
Read events
30 342
Write events
191
Delete events
13
Modification events
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
17
Suspicious files
63
Text files
111
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF18e2d9.TMP | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF18e29b.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF18e47f.TMP | text | |
MD5:B36B68CE4A71A5BFAF89A4D1CC07893F | SHA256:6422CC04455EF100D67FD9F299AACFEF3BA4F77D0FA1D2440D89E7D1CF65EBBC | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\19933547-4d4a-42ff-8b83-07c6d71673fa.tmp | — | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF18e932.TMP | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF18e47f.TMP | text | |
MD5:F5B58F0B08202C8D6DE12514994A84BF | SHA256:F5BA8809B6A3920A11CF31E7F6A1DEC46EF4F4339D6158967CCB1405409D1241 | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF18fa0b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
54
DNS requests
59
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1956 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | unknown |
920 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1956 | chrome.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
1956 | chrome.exe | 185.199.110.154:443 | github.githubassets.com | FASTLY | US | unknown |
1956 | chrome.exe | 172.217.16.202:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
1956 | chrome.exe | 185.199.110.133:443 | avatars.githubusercontent.com | FASTLY | US | unknown |
1956 | chrome.exe | 142.250.185.74:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
accounts.google.com |
| shared |
github.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
collector.github.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3660 | msedge.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
3660 | msedge.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |