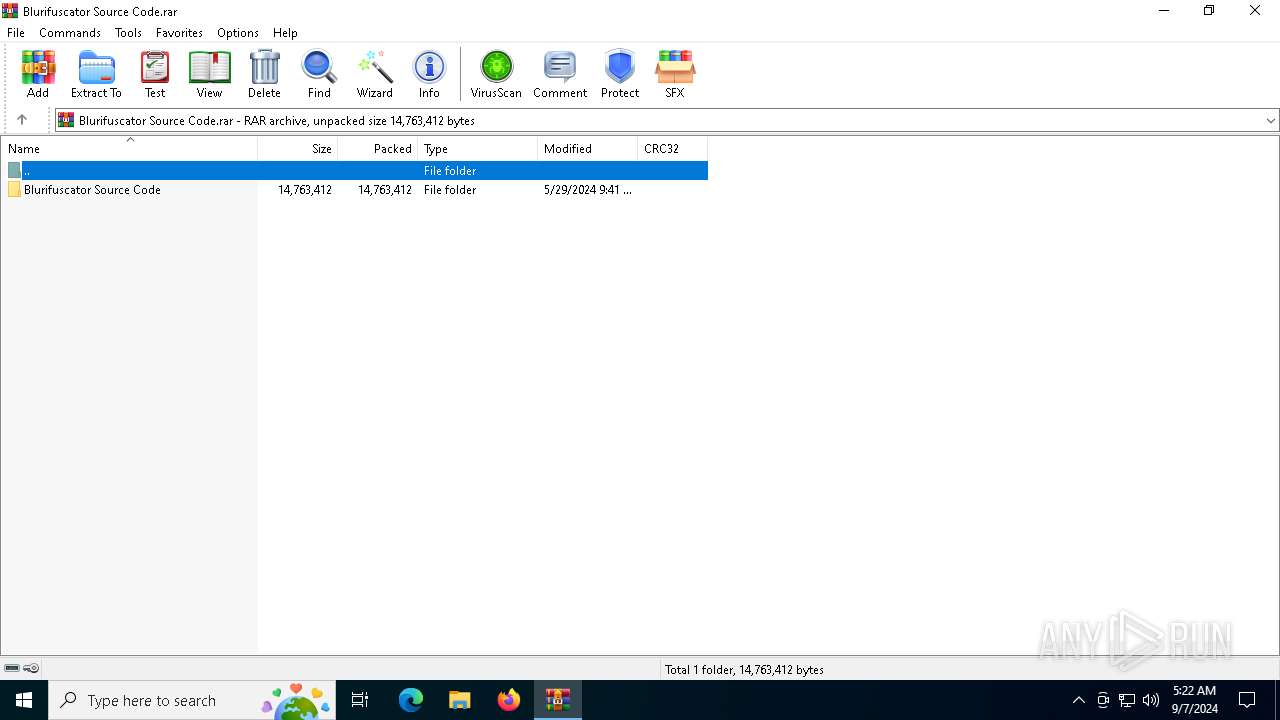
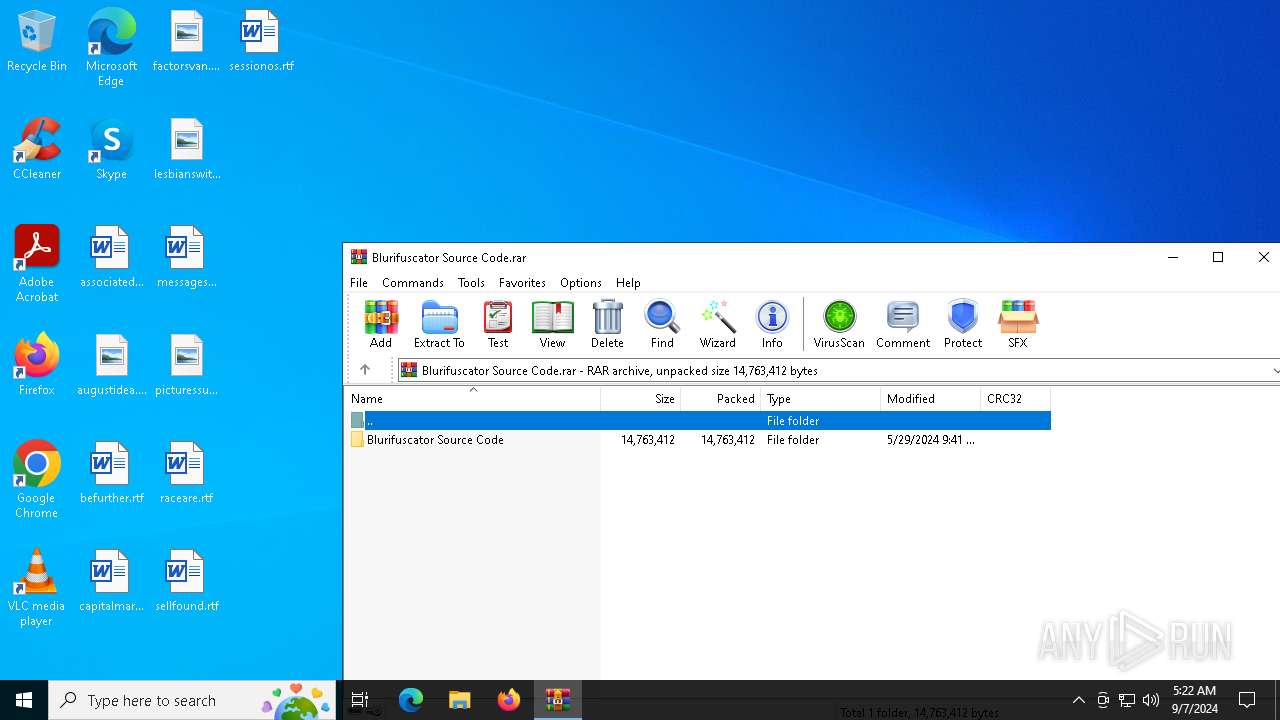
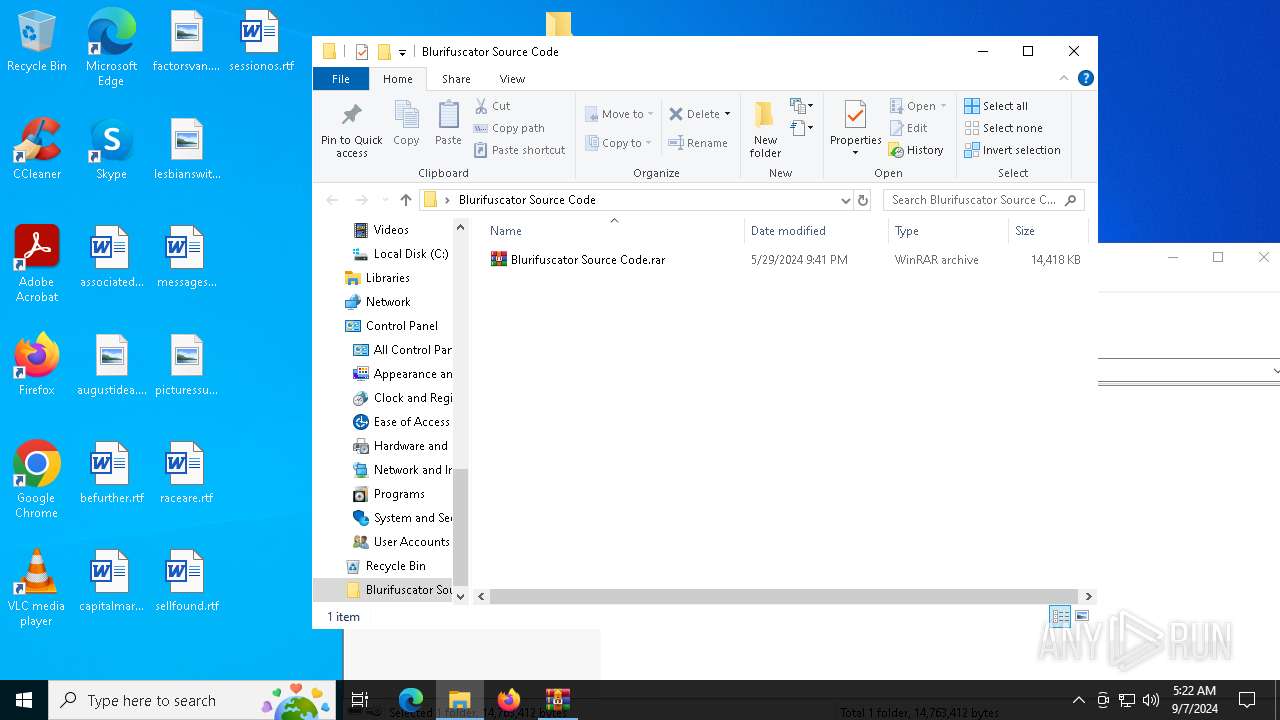
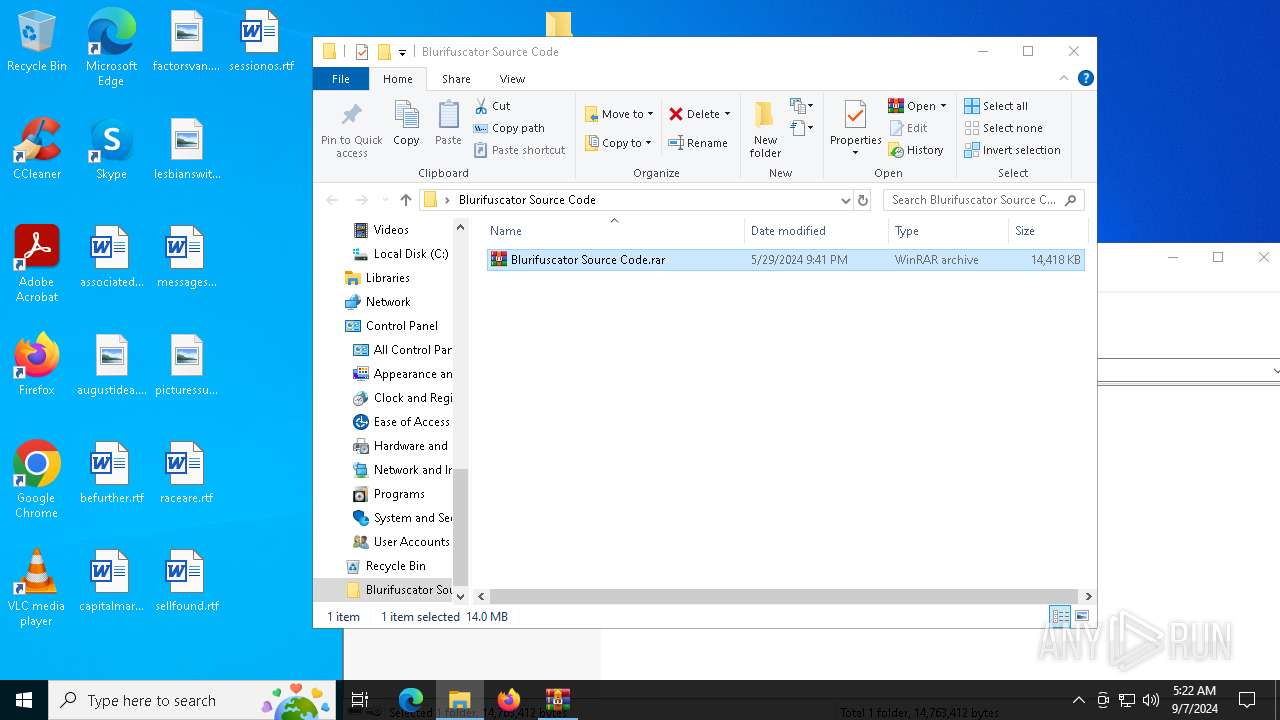
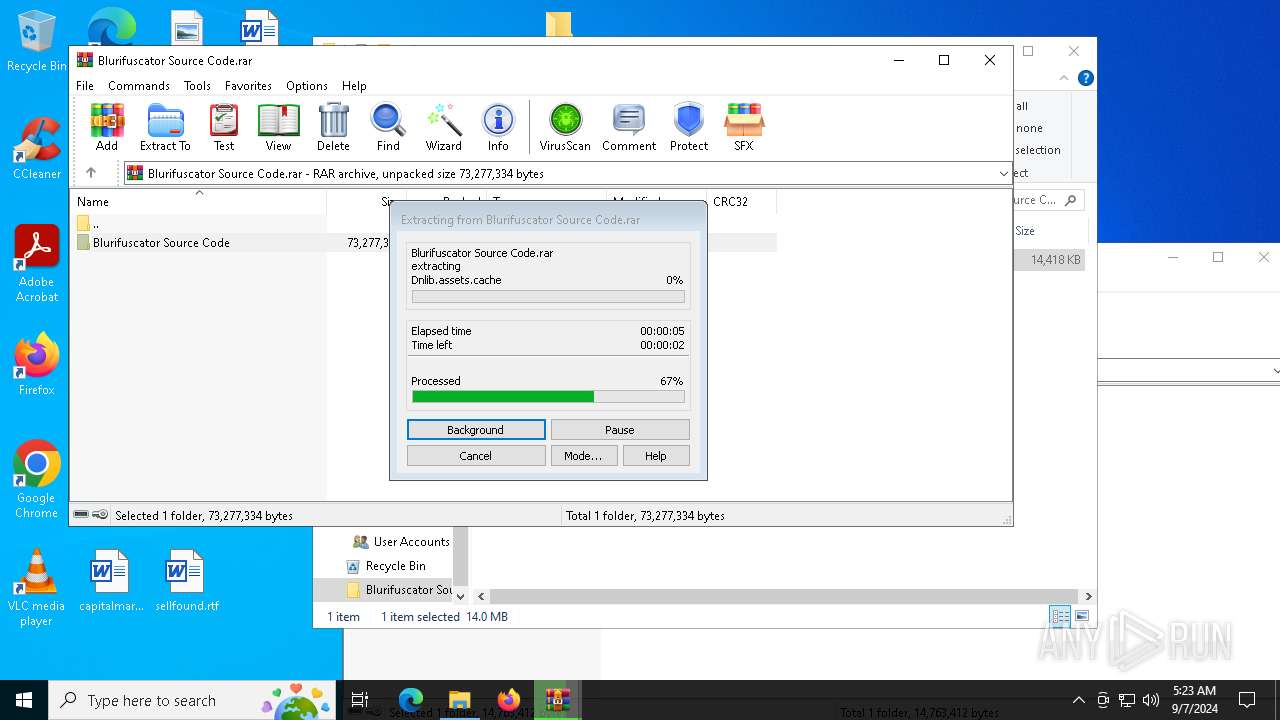
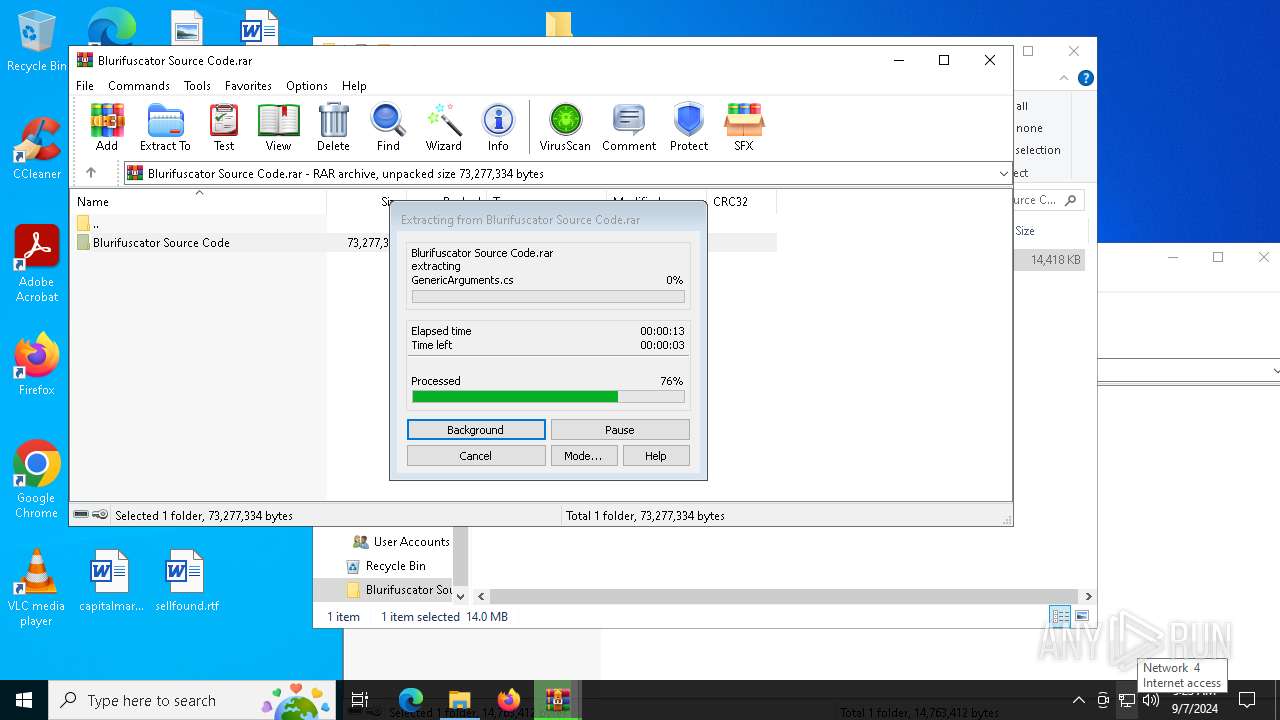
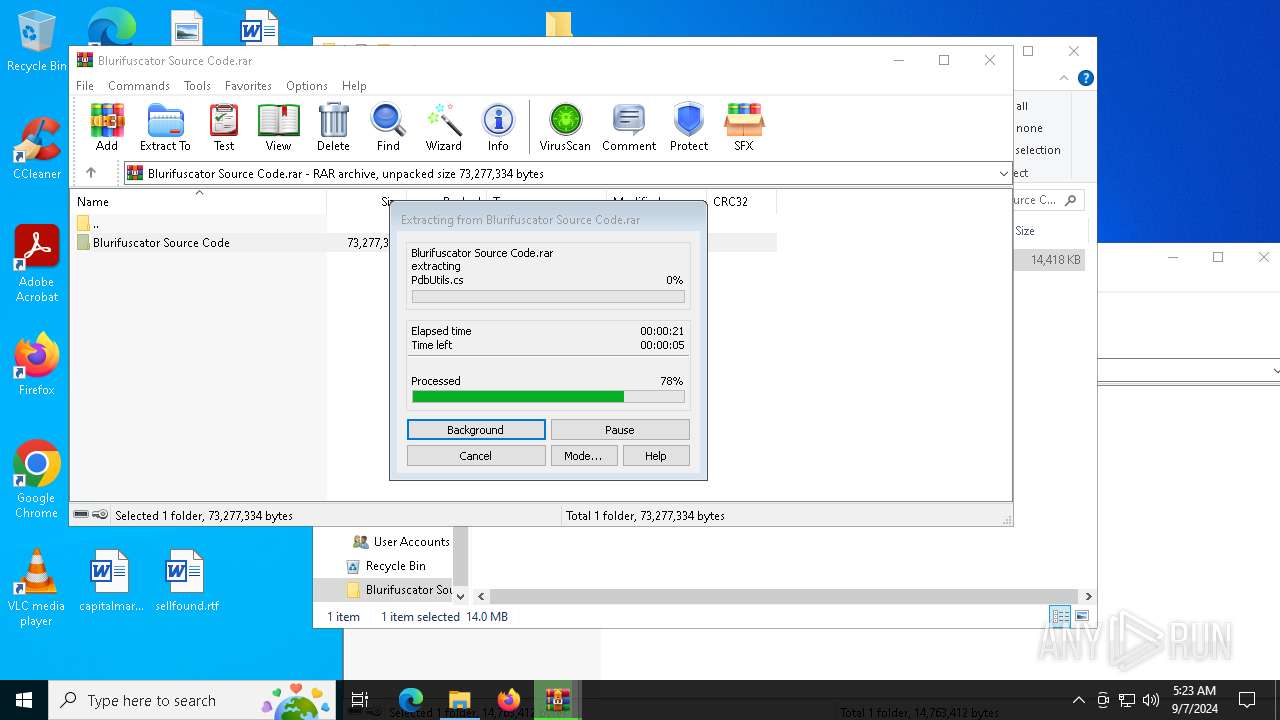
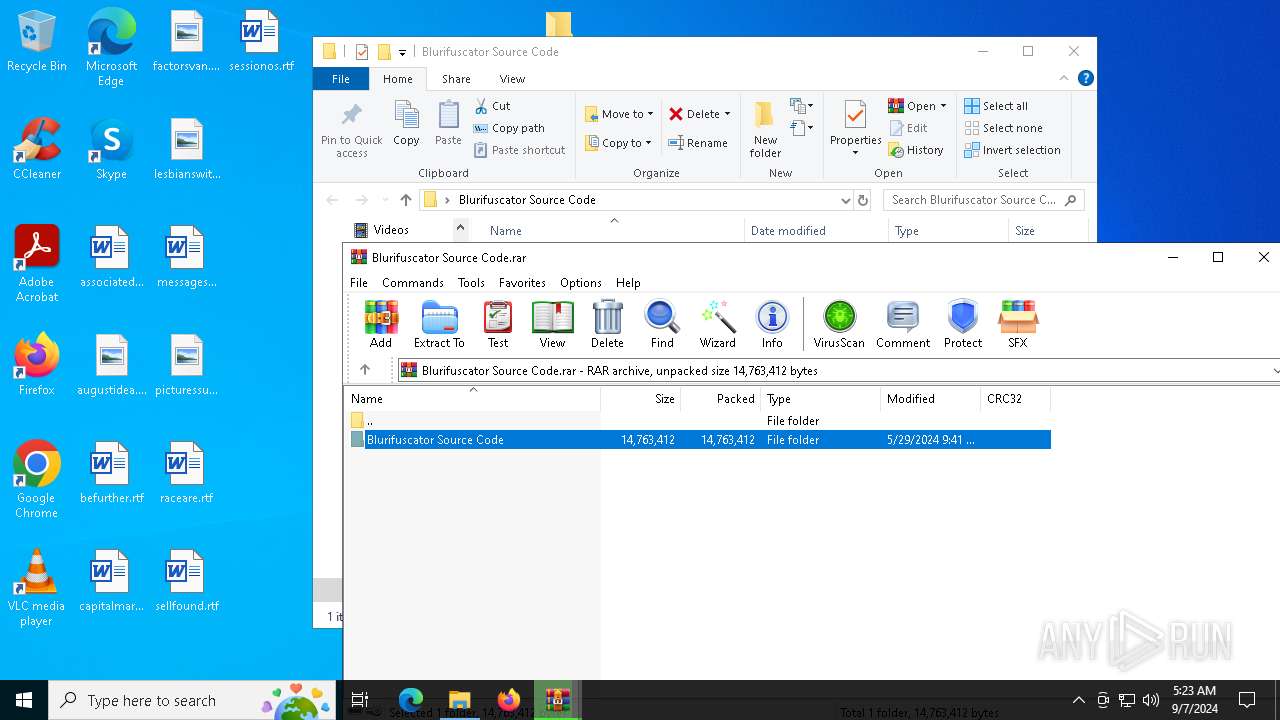
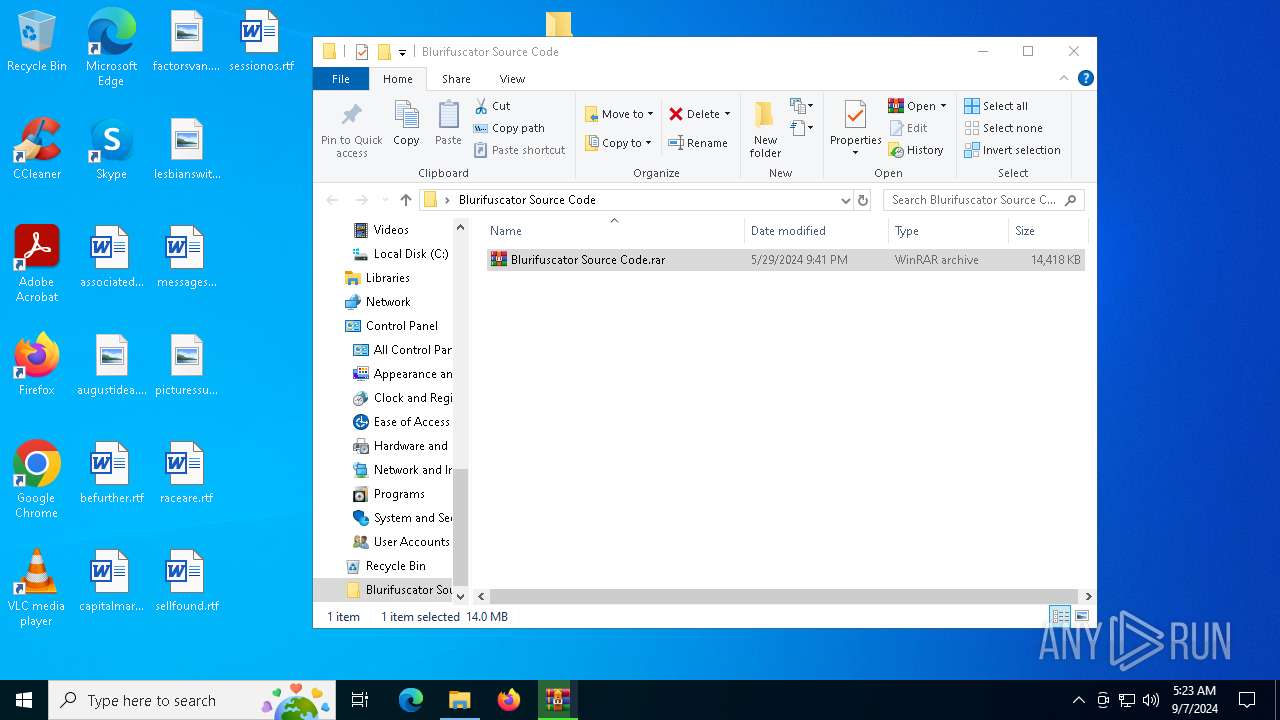
| File name: | Blurifuscator Source Code.rar |
| Full analysis: | https://app.any.run/tasks/eb7cfe27-c46f-4728-a8e4-afadece32208 |
| Verdict: | Malicious activity |
| Analysis date: | September 07, 2024, 05:22:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 6A1F7923DF2F85BCDBC72DCEF44C02BA |
| SHA1: | 20FF4F7970909E2122592A89D899F9CA895EB8E2 |
| SHA256: | F8042804E027C786C0D0264E210FE6D2D26CC3603E6BA5EE3F8BD162736A5CFE |
| SSDEEP: | 98304:izVv/tOg3OKxrax7CogTfi4iLH6wsfVTrN1DoKARfqKsrUcOhrl30jt9puD4WAyb:BgSjB3fUByt3XgQhNfv6hNs+pqR |
MALICIOUS
No malicious indicators.SUSPICIOUS
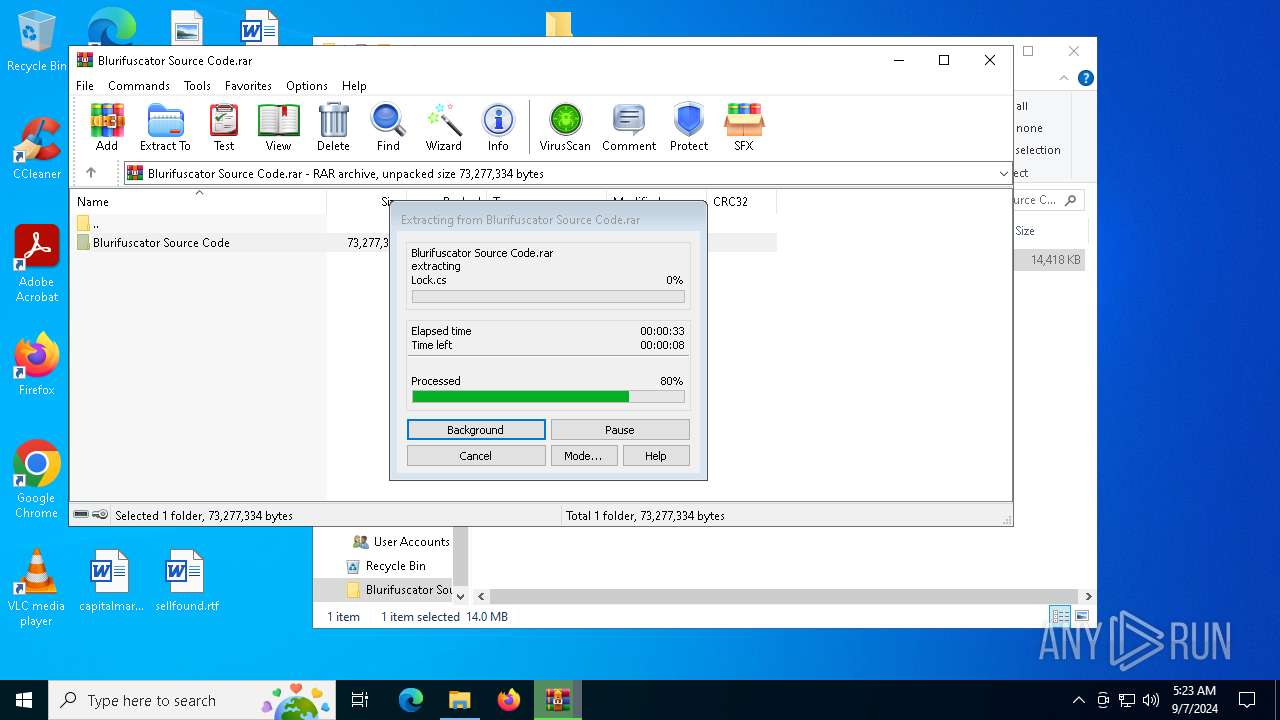
Process drops legitimate windows executable
- WinRAR.exe (PID: 6012)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 6012)
INFO
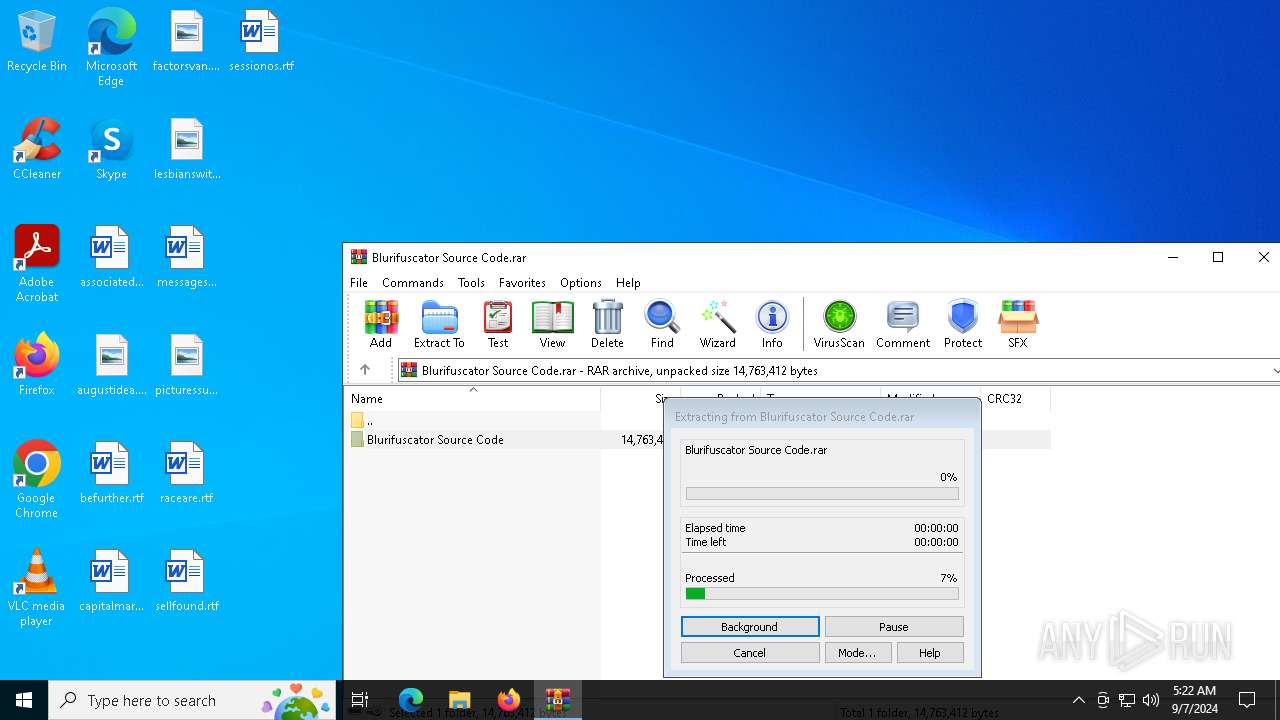
Manual execution by a user
- WinRAR.exe (PID: 6012)
The process uses the downloaded file
- WinRAR.exe (PID: 5140)
- WinRAR.exe (PID: 6012)
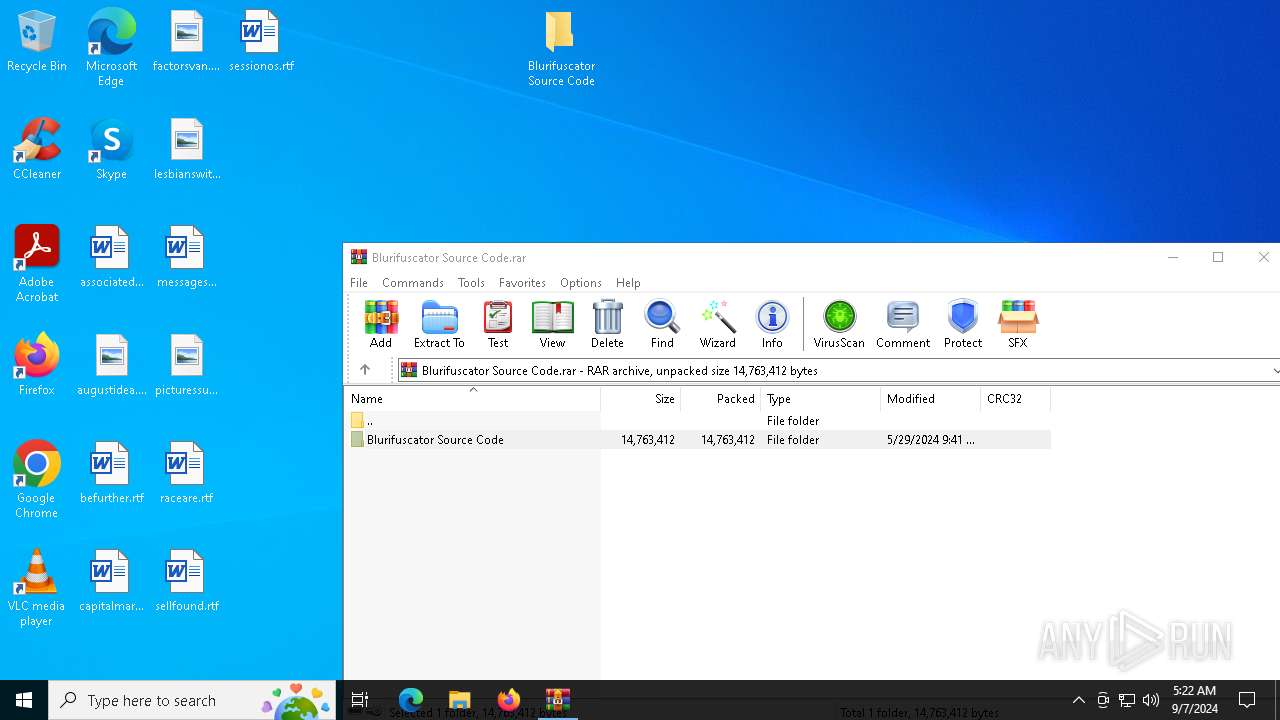
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
132
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2584 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3980 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4820 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
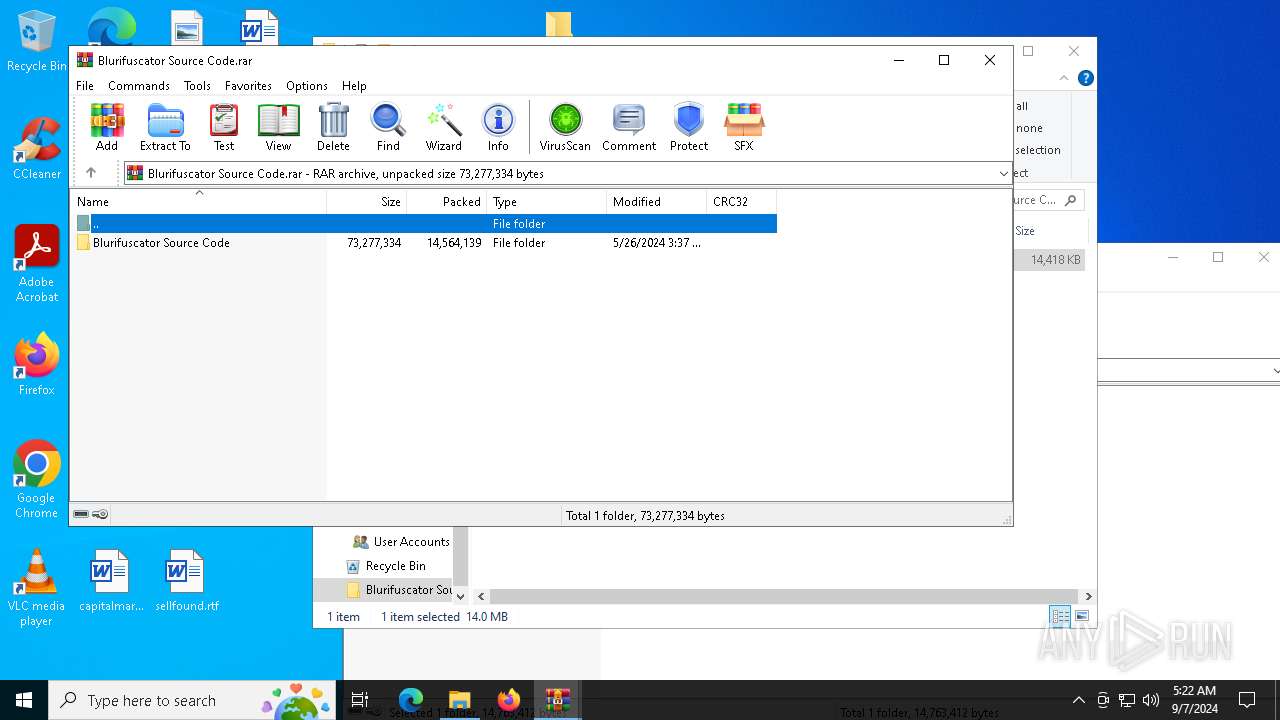
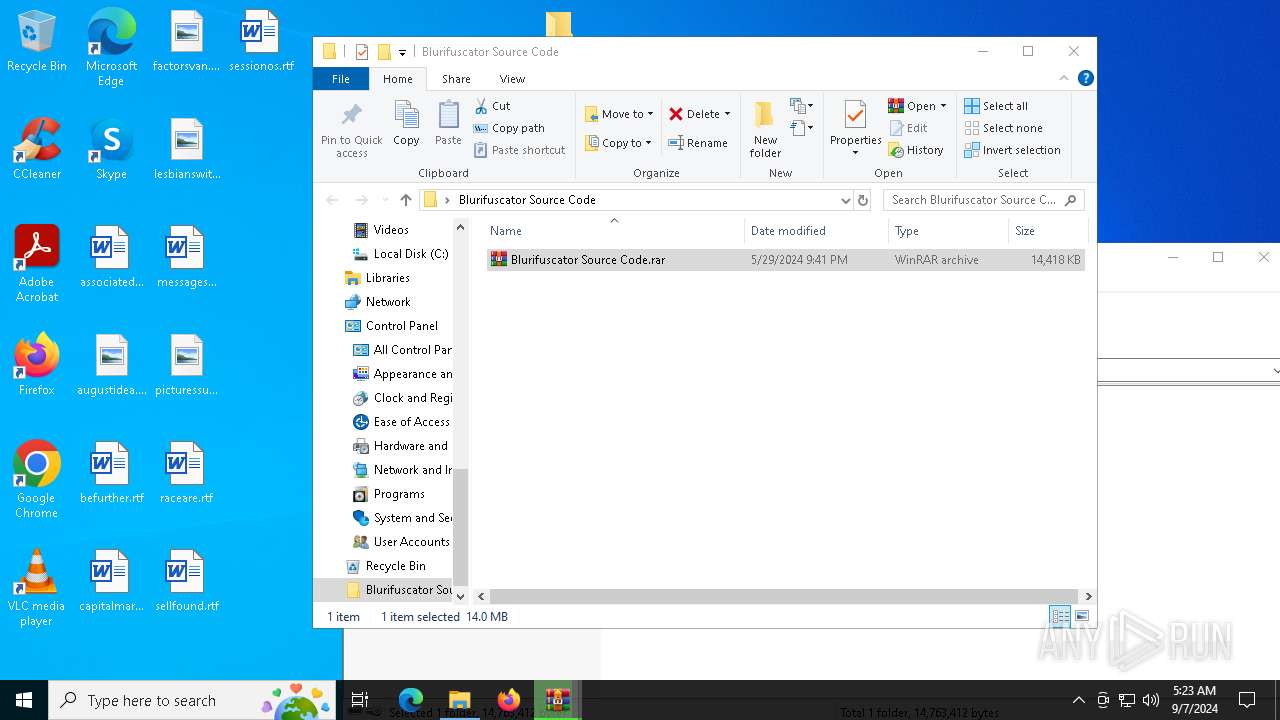
| 5140 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Blurifuscator Source Code.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
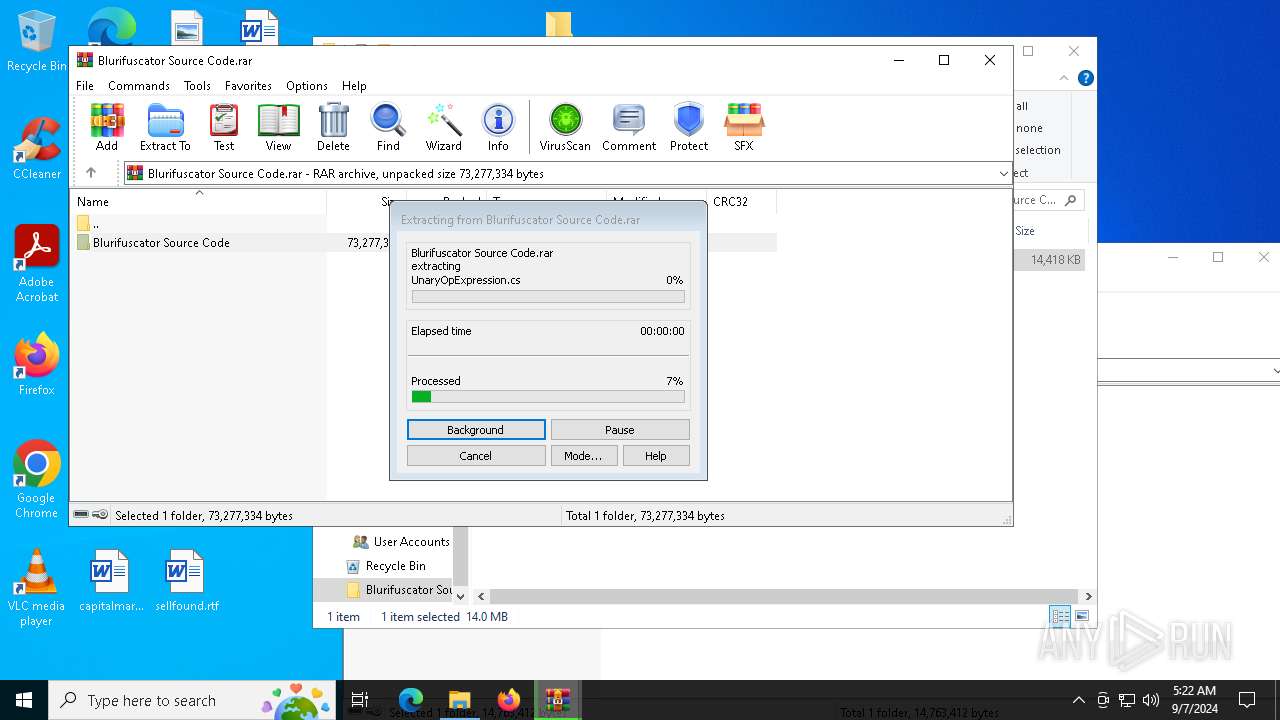
| 6012 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Blurifuscator Source Code\Blurifuscator Source Code.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
3 086
Read events
3 063
Write events
23
Delete events
0
Modification events
| (PID) Process: | (5140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (5140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Blurifuscator Source Code.rar | |||
| (PID) Process: | (5140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\AppData\Local\Temp\Blurifuscator Source Code.rar | |||
| (PID) Process: | (6012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Blurifuscator Source Code\Blurifuscator Source Code.rar | |||
| (PID) Process: | (6012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
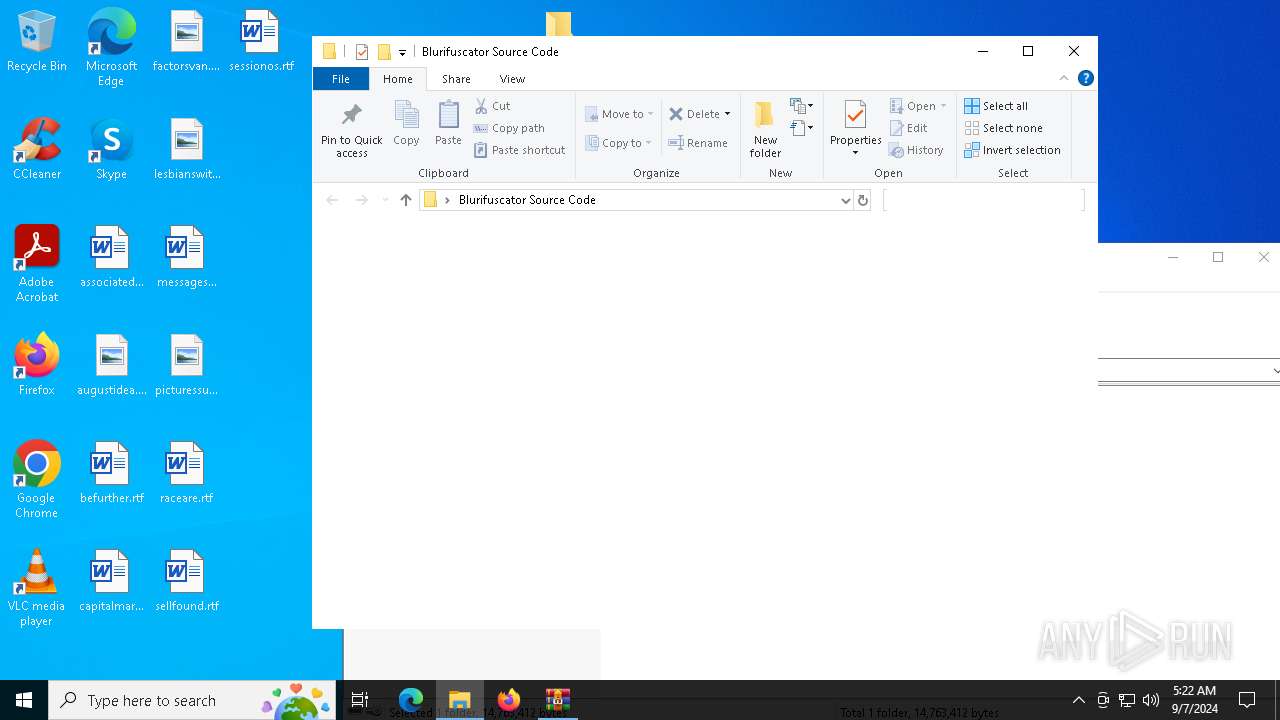
Executable files
108
Suspicious files
128
Text files
751
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5140 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5140.37805\Blurifuscator Source Code\Blurifuscator Source Code.rar | — | |
MD5:— | SHA256:— | |||
| 6012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6012.38838\Blurifuscator Source Code\.vs\ProjectEvaluation\blurifuscator.projects.v7.bin | — | |
MD5:— | SHA256:— | |||
| 6012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6012.38838\Blurifuscator Source Code\.vs\Blurifuscator\FileContentIndex\704e3d5c-a0f3-4314-b2a8-ec78407c9092.vsidx | binary | |
MD5:7BCEA34848A6AE5BE04B1F9301333A23 | SHA256:F3B2EDF181864B430A2FE487D920C4A3BF4963BC6D02036ECE17E9697F2B66E6 | |||
| 6012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6012.38838\Blurifuscator Source Code\.vs\Blurifuscator\v17\fileList.bin | binary | |
MD5:D47F9CF77C432CF1CEA648076D44F9F7 | SHA256:56CC1EBF5C95F5CA92B2CB5CA25CC7E104F1FEFE70F518577B862287609EC1E6 | |||
| 6012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6012.38838\Blurifuscator Source Code\.vs\Blurifuscator\v17\.suo | binary | |
MD5:DFE1FEE044E4CFEFF1FC64EFDD3EA429 | SHA256:F32E7DFA7DA10528BE26D7CC933ADD21CED9E65F7B245D6864BE2298363CE4DF | |||
| 6012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6012.38838\Blurifuscator Source Code\Blurifuscator.CLI\Blurifuscator.CLI.csproj | text | |
MD5:AD6E15779EED599836DF81399A330040 | SHA256:3025D26C391541AC701497EA0BD5CE77DA7059DFC707C40B2EA8B3C5F74D0F4B | |||
| 6012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6012.38838\Blurifuscator Source Code\.vs\Blurifuscator\v17\DocumentLayout.json | binary | |
MD5:0B7C6A7458468FB1D23FDCF1F120F6C0 | SHA256:B9A070B79C4A089780130B6DD26137732CF2CA7E94867D9147CB4A22F3B15E8B | |||
| 6012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6012.38838\Blurifuscator Source Code\Blurifuscator.CLI\obj\Blurifuscator.CLI.csproj.nuget.dgspec.json | binary | |
MD5:C6378163F912511A445520D4AC812FBE | SHA256:ED936F7290D0DA6AB2DCD3175AE986146CC178D98BC35E84232E611D4B793574 | |||
| 6012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6012.38838\Blurifuscator Source Code\.vs\Blurifuscator\FileContentIndex\6aa5ab58-8f28-494c-abe0-5d2dc6b1f637.vsidx | binary | |
MD5:CE5CF4A7B7425E67C8F383C4C79A9E34 | SHA256:0C3952A3FCCB4CD58F2928E344B2C5F6877F9FF091D4741E825F8697FC9514B1 | |||
| 6012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6012.38838\Blurifuscator Source Code\Blurifuscator.CLI\obj\Blurifuscator.CLI.csproj.nuget.g.props | xml | |
MD5:38FB35EB188880C34BE029FC9795428B | SHA256:8E985DE506F5366A0A0DA9FBBB307508BAB2E7AE9263E5A9FA8CE1DA7FAB3C80 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
25
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6160 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5656 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4164 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5656 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6160 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6288 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6160 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6160 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.11.168.232:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
4164 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |