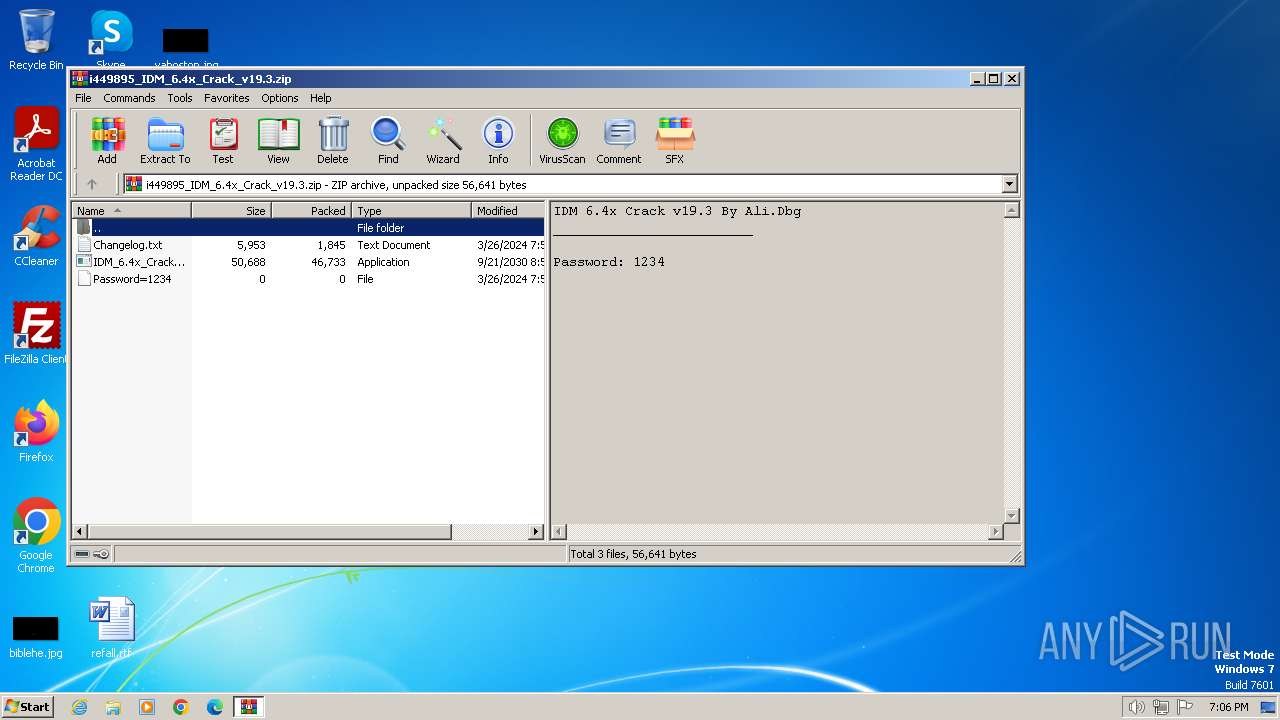
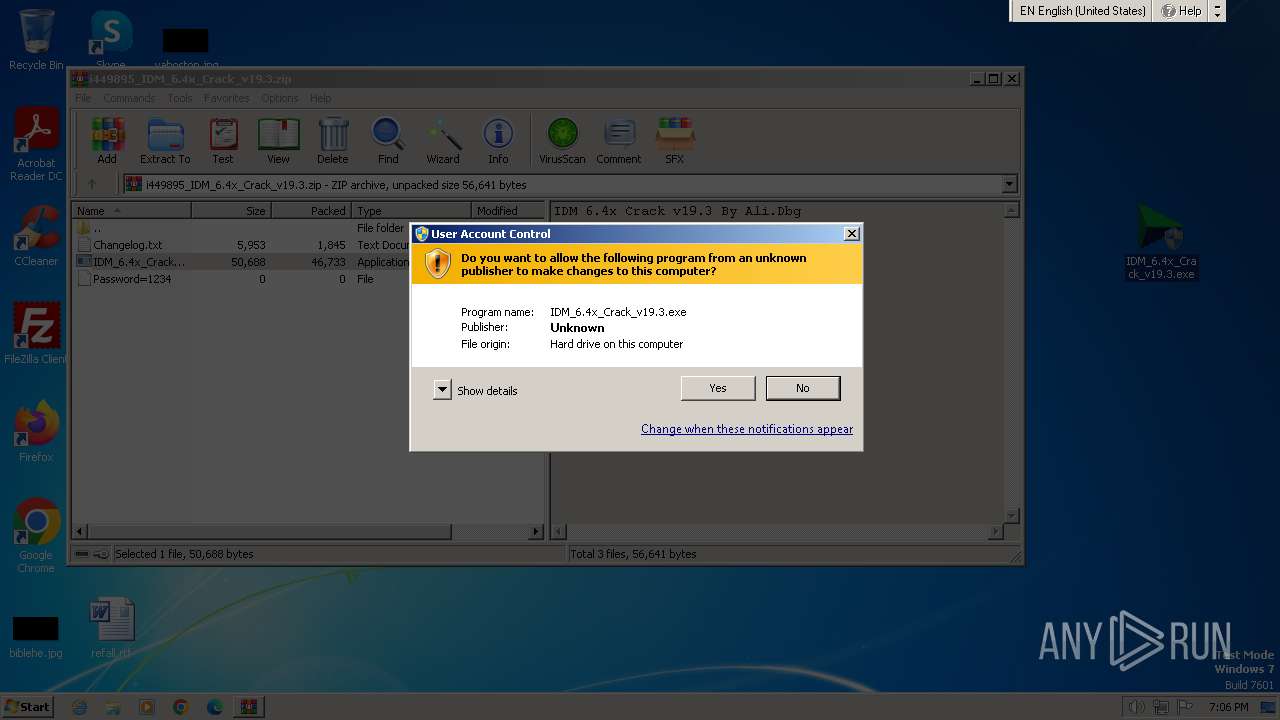
| File name: | i449895_IDM_6.4x_Crack_v19.3.zip |
| Full analysis: | https://app.any.run/tasks/49dd50f1-27b4-4b9f-9147-4bb2cacd69b6 |
| Verdict: | Malicious activity |
| Analysis date: | April 05, 2024, 18:06:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=AES Encrypted |
| MD5: | F1ABD8A20C3FC9EB6E6F6B67749E7565 |
| SHA1: | 241C9201FF4B6FE2AAC94D1BD91D992A0A02AA74 |
| SHA256: | F7F3DC7CBFA194EC8B4C97D62F0ADA43B1DFAD775A6A541B452413991417131D |
| SSDEEP: | 1536:QcLl3I/ilvRyD+zwYWGCNX3YspwjhIRivDDzj:HLLvqMCx3DwjhI+7j |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 2320)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 2320)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 2320)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 2320)
Unusual connection from system programs
- wscript.exe (PID: 2320)
Deletes a file (SCRIPT)
- wscript.exe (PID: 2320)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2320)
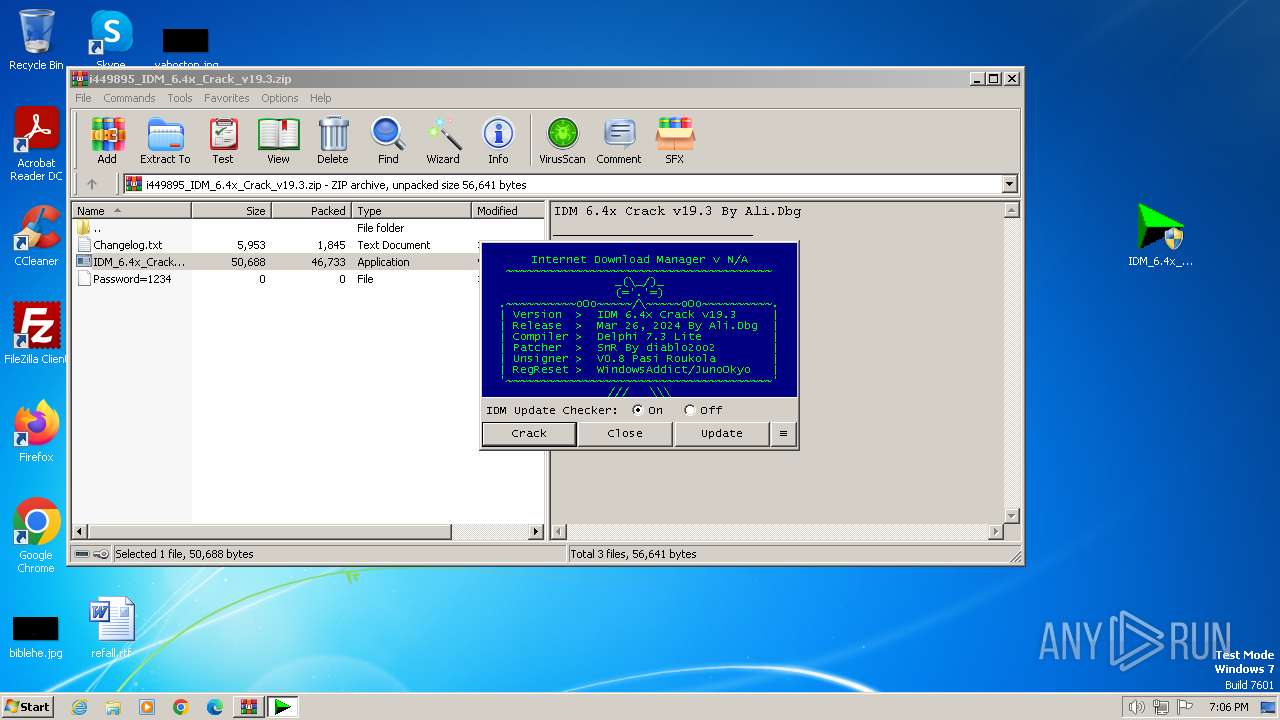
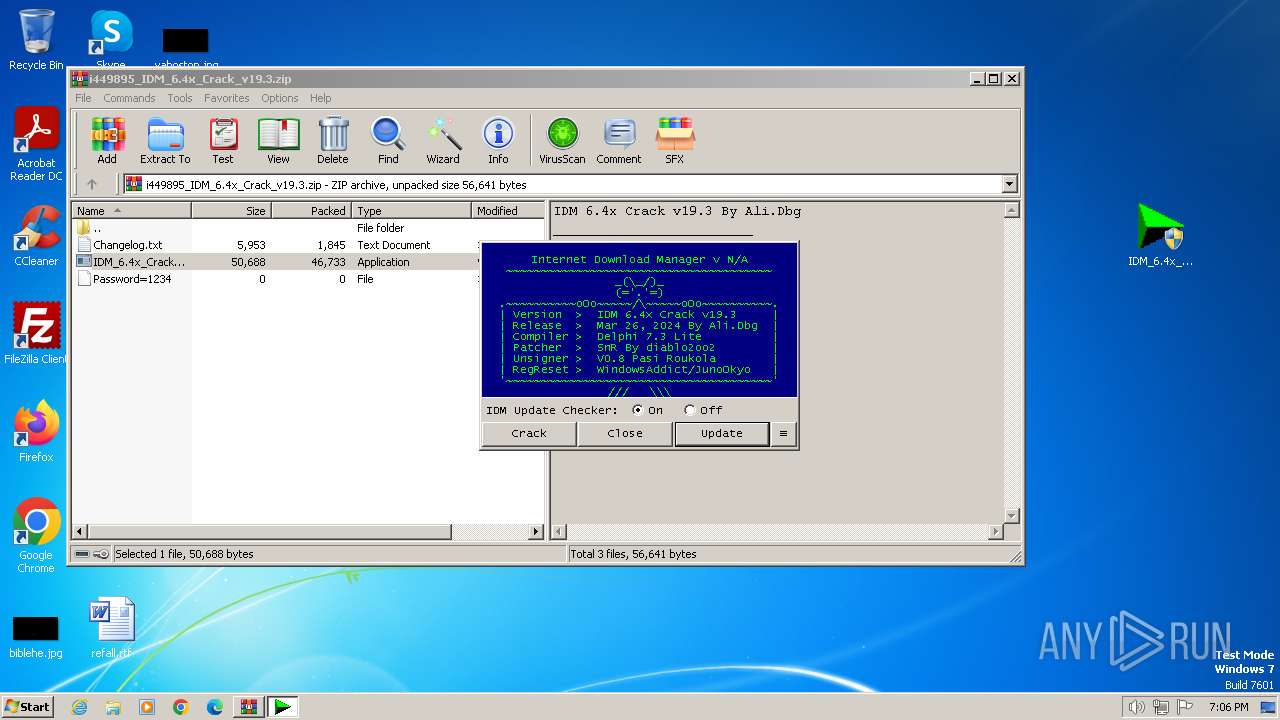
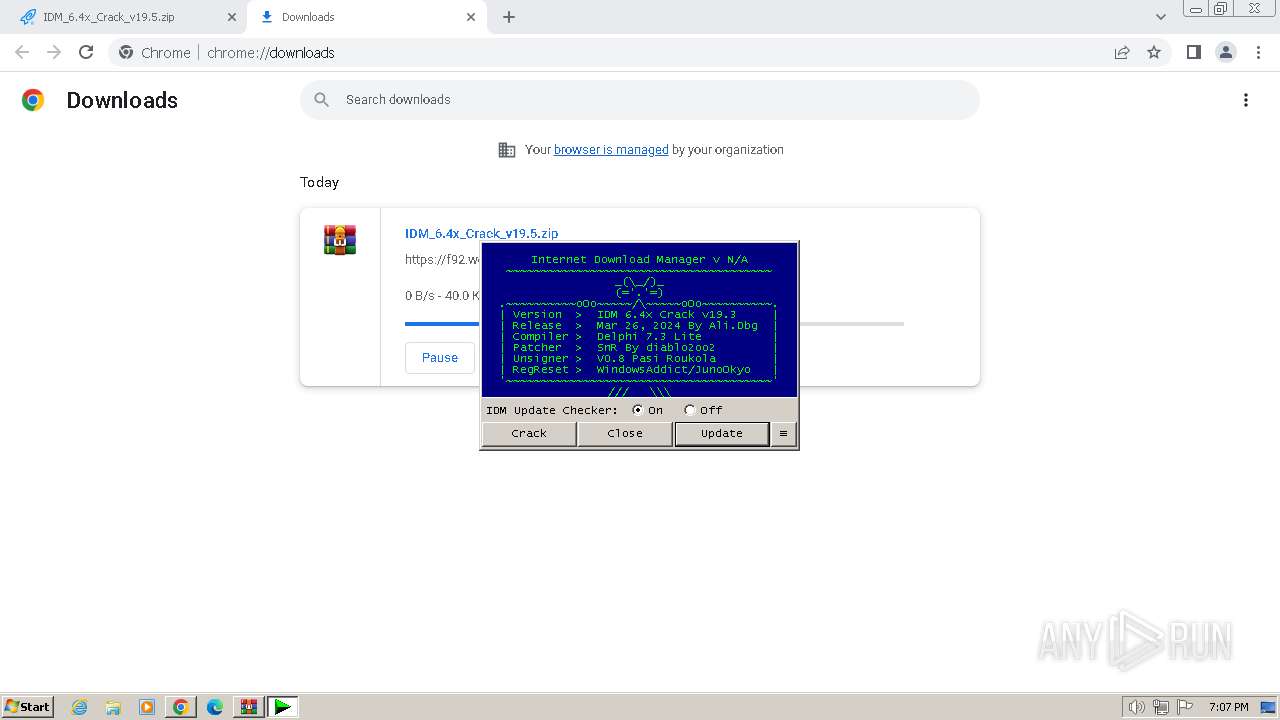
The process executes VB scripts
- IDM_6.4x_Crack_v19.3.exe (PID: 3072)
Reads the Internet Settings
- wscript.exe (PID: 2320)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 2320)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2320)
INFO
Reads the computer name
- IDM_6.4x_Crack_v19.3.exe (PID: 3072)
Checks supported languages
- IDM_6.4x_Crack_v19.3.exe (PID: 3072)
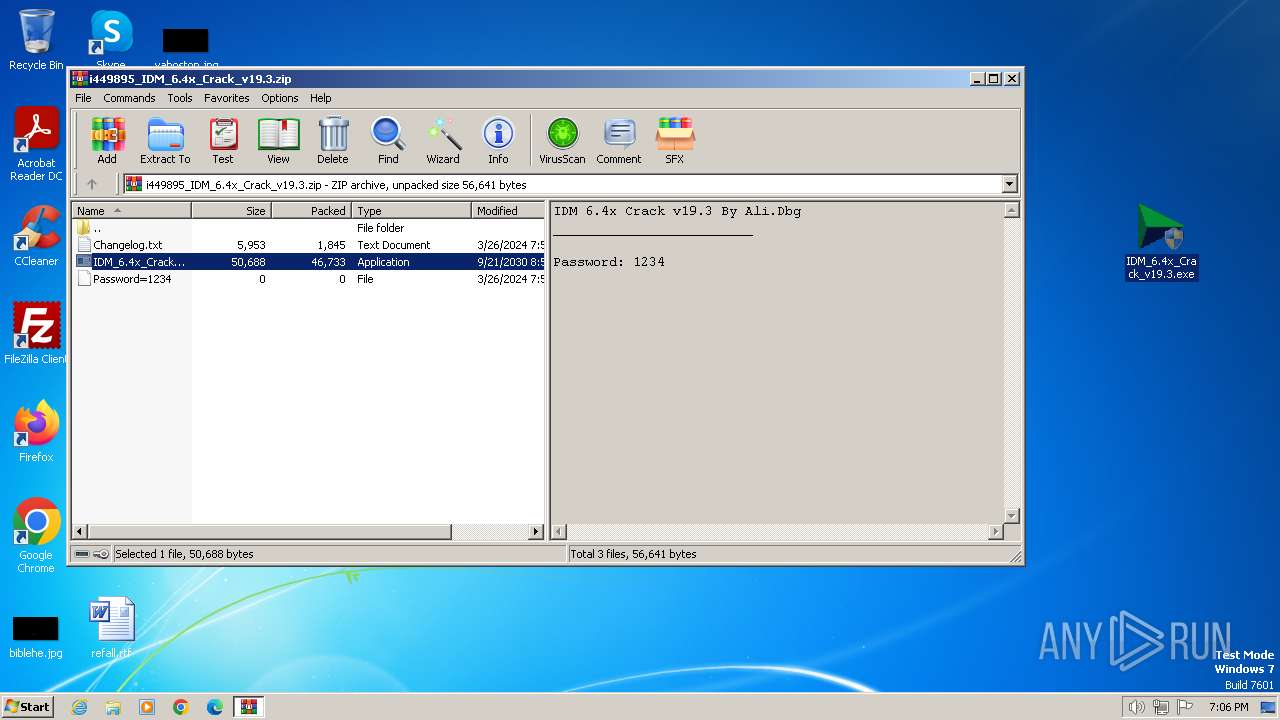
Manual execution by a user
- IDM_6.4x_Crack_v19.3.exe (PID: 956)
- IDM_6.4x_Crack_v19.3.exe (PID: 3072)
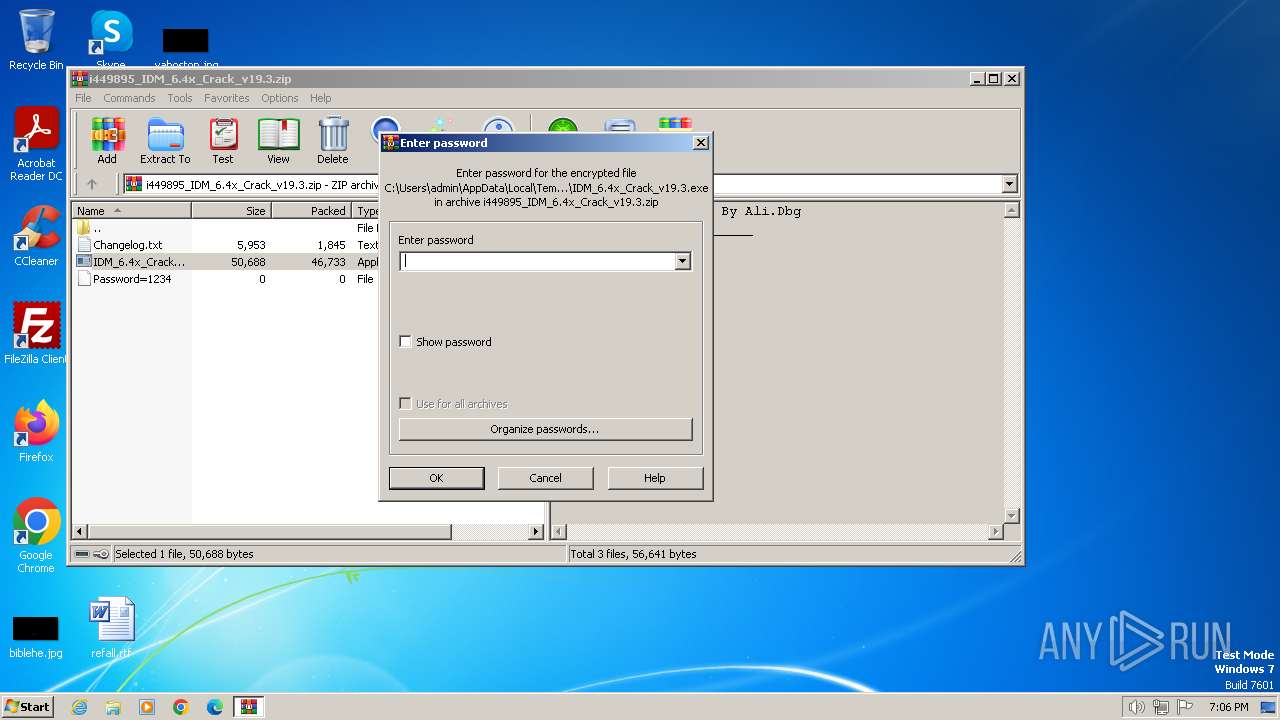
Drops the executable file immediately after the start
- WinRAR.exe (PID: 4008)
Create files in a temporary directory
- IDM_6.4x_Crack_v19.3.exe (PID: 3072)
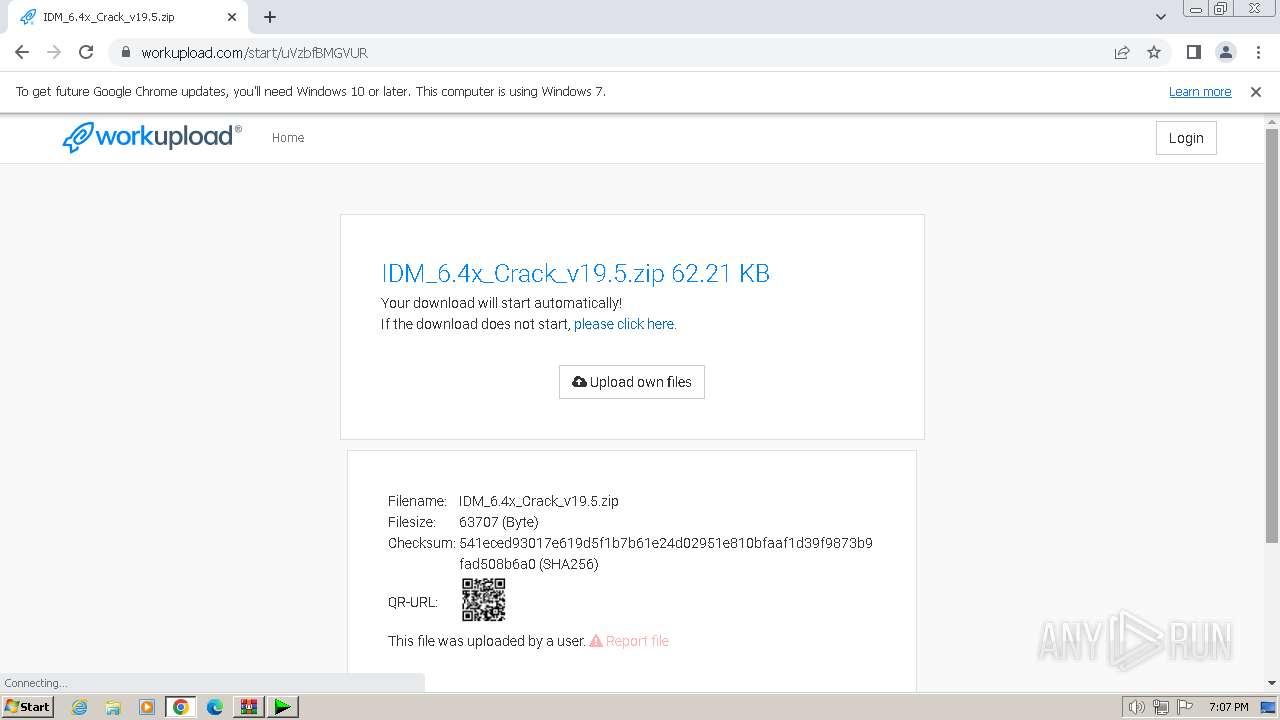
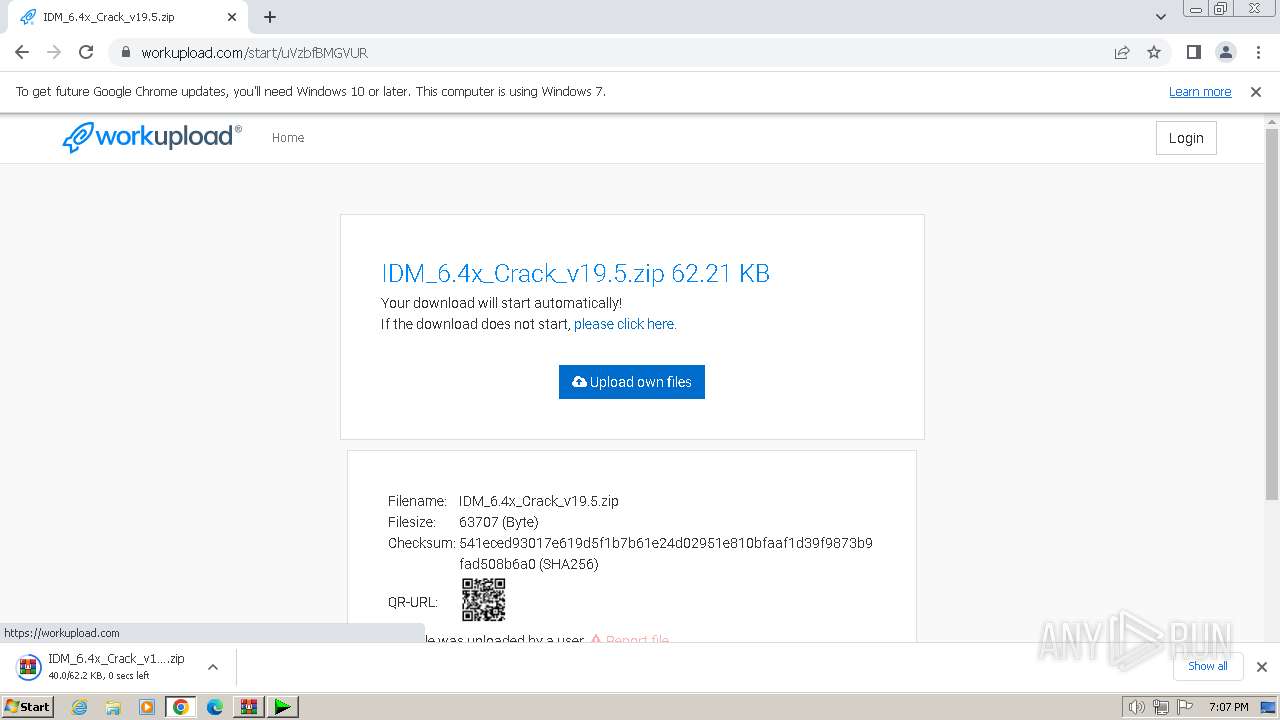
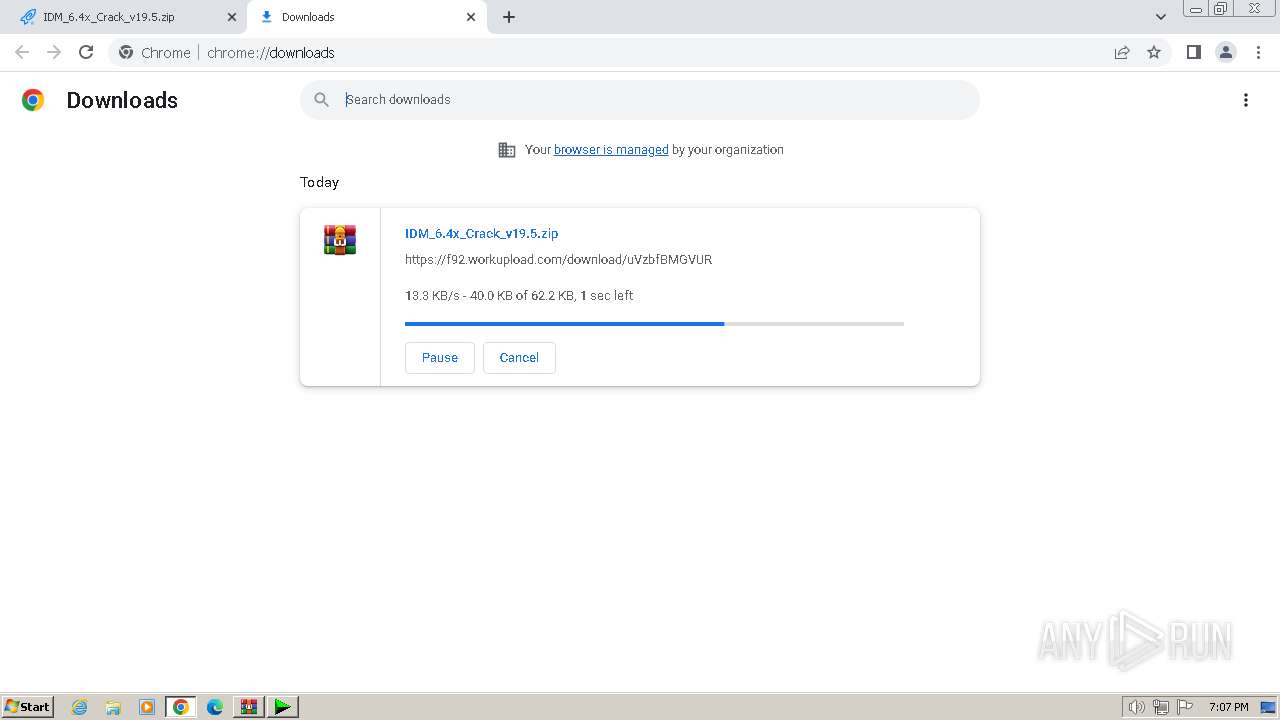
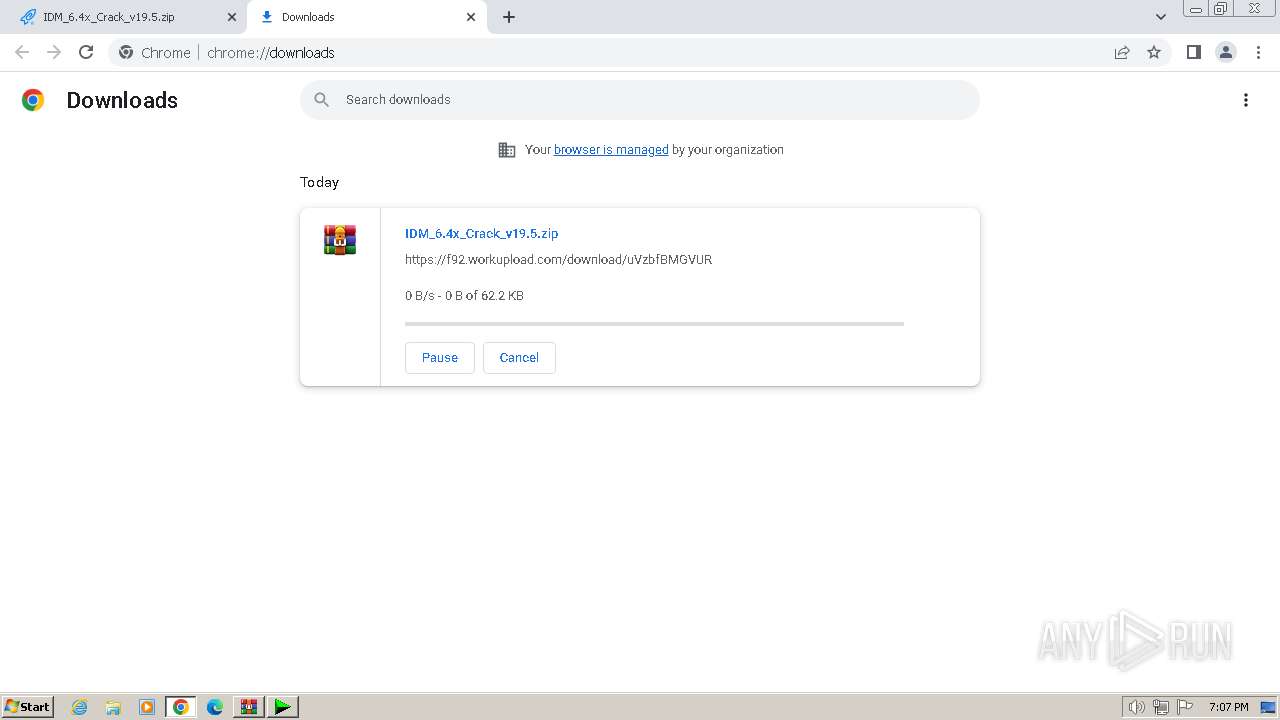
The process uses the downloaded file
- chrome.exe (PID: 668)
- chrome.exe (PID: 3600)
Creates files in the program directory
- chrome.exe (PID: 2336)
Application launched itself
- chrome.exe (PID: 2336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
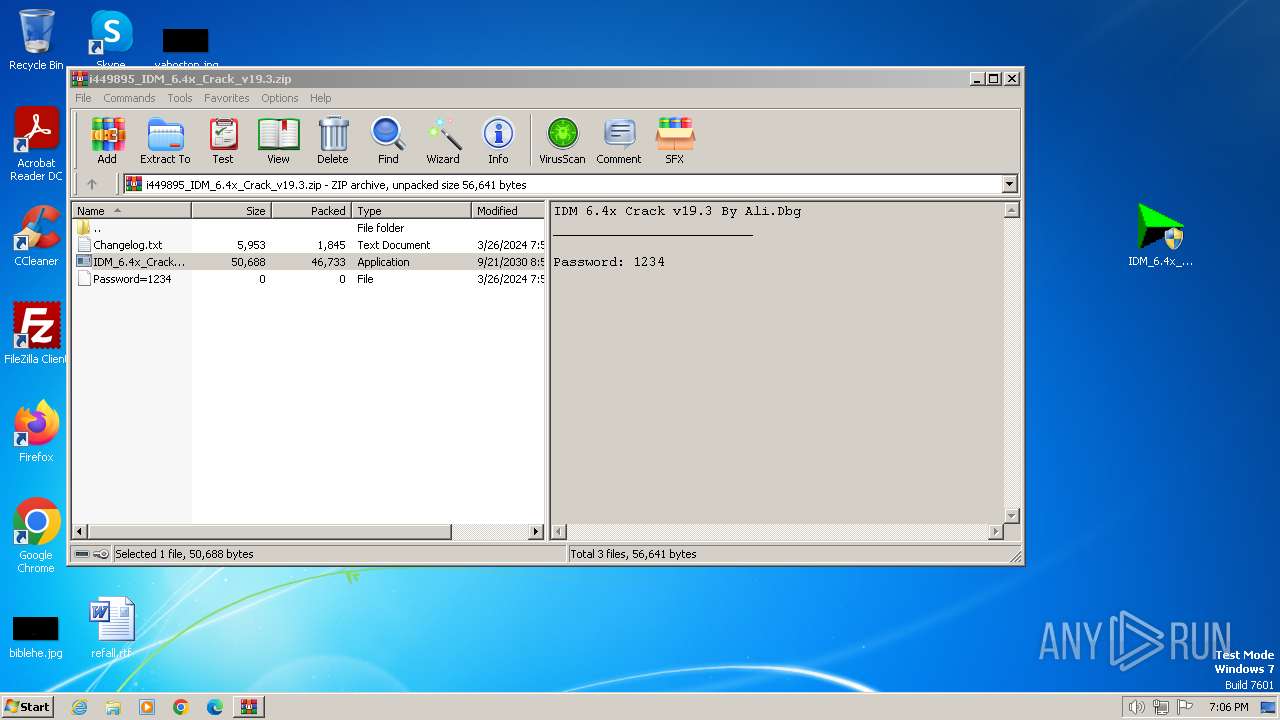
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2030:09:21 07:55:36 |
| ZipCRC: | 0xace74051 |
| ZipCompressedSize: | 46733 |
| ZipUncompressedSize: | 50688 |
| ZipFileName: | IDM_6.4x_Crack_v19.3.exe |
Total processes
60
Monitored processes
18
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1332 --field-trial-handle=1148,i,13433668587424119225,2665266034870954909,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3996 --field-trial-handle=1148,i,13433668587424119225,2665266034870954909,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 956 | "C:\Users\admin\Desktop\IDM_6.4x_Crack_v19.3.exe" | C:\Users\admin\Desktop\IDM_6.4x_Crack_v19.3.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=3720 --field-trial-handle=1148,i,13433668587424119225,2665266034870954909,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1068 --field-trial-handle=1148,i,13433668587424119225,2665266034870954909,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6a588b38,0x6a588b48,0x6a588b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2320 | wscript.exe "C:\Users\admin\AppData\Local\Temp\\UPDT.vbs" /browser:"C:\Program Files\Google\Chrome\Application\chrome.exe" /crkver:"19.3" | C:\Windows\System32\wscript.exe | IDM_6.4x_Crack_v19.3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
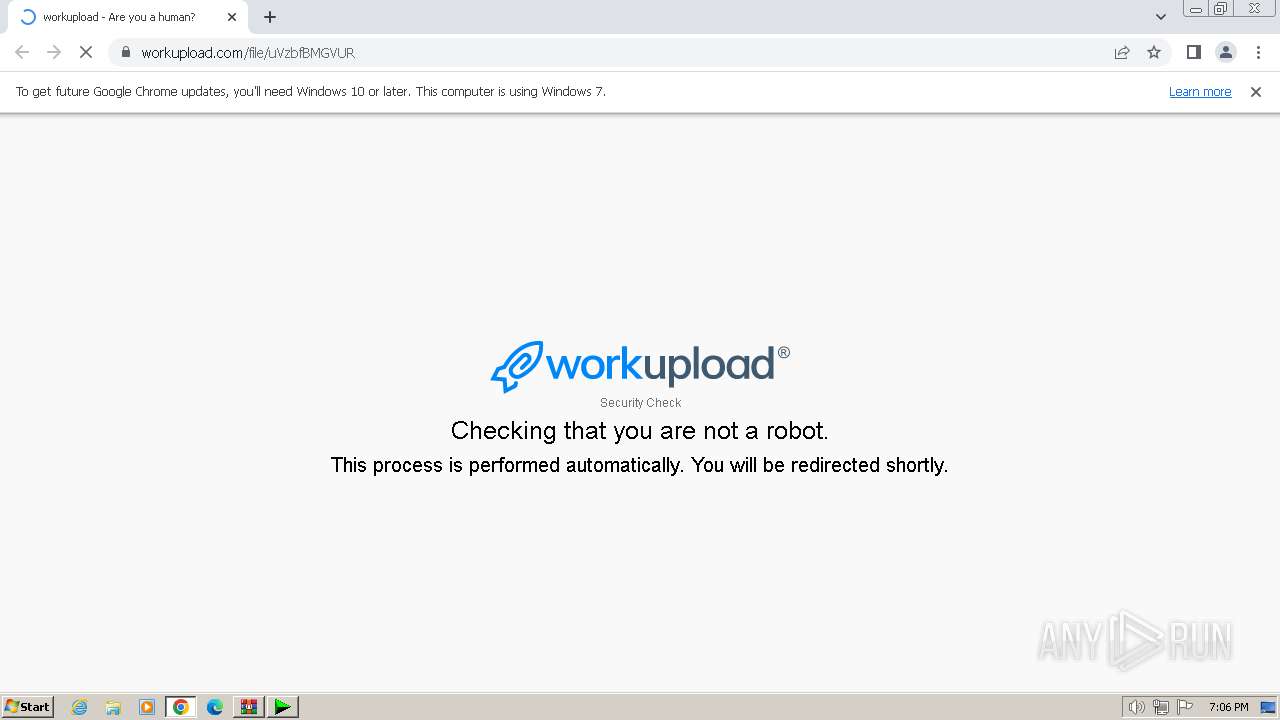
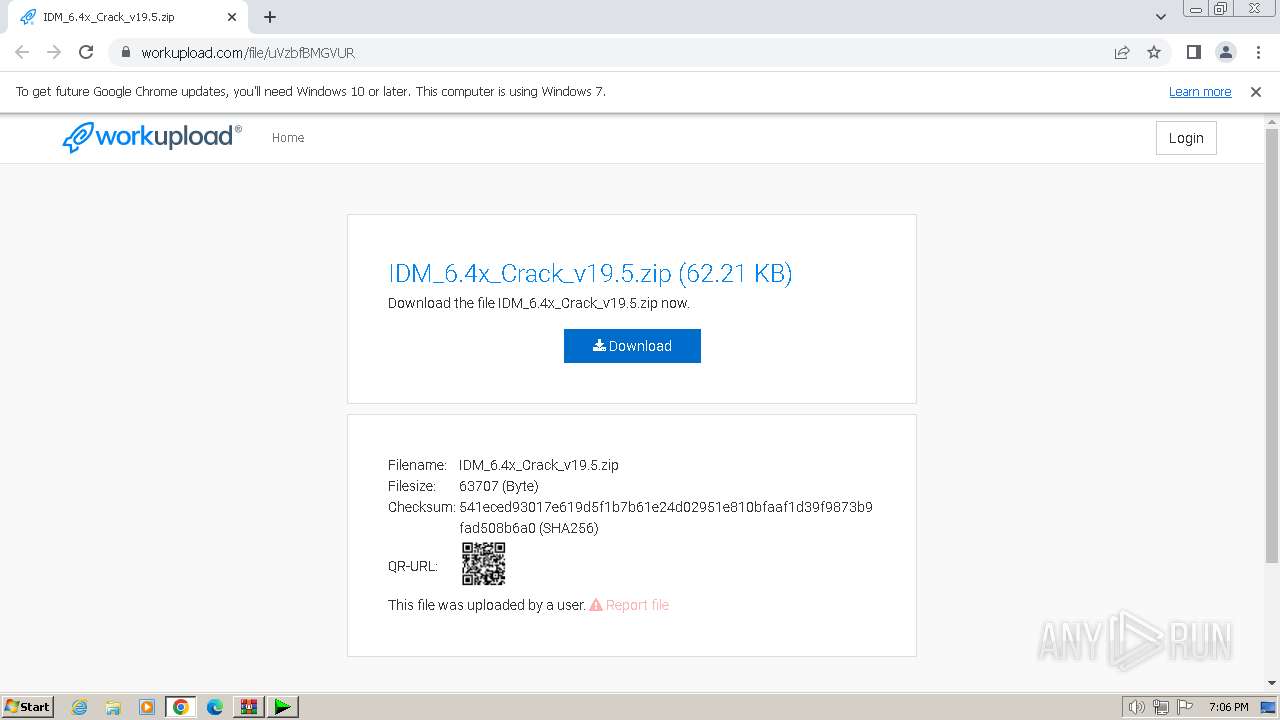
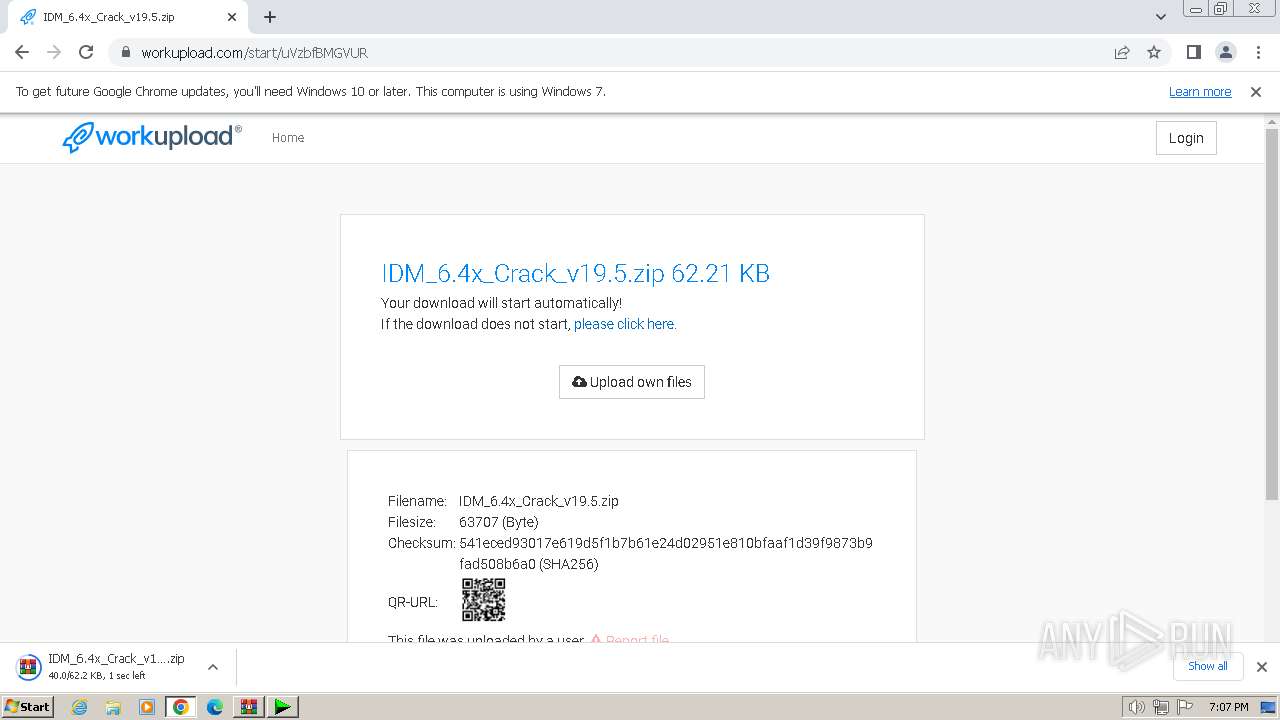
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://workupload.com/file/uVzbfBMGVUR | C:\Program Files\Google\Chrome\Application\chrome.exe | wscript.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2096 --field-trial-handle=1148,i,13433668587424119225,2665266034870954909,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2104 --field-trial-handle=1148,i,13433668587424119225,2665266034870954909,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
13 873
Read events
13 736
Write events
124
Delete events
13
Modification events
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\i449895_IDM_6.4x_Crack_v19.3.zip | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
1
Suspicious files
17
Text files
22
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb4008.38380\IDM_6.4x_Crack_v19.3.exe | executable | |
MD5:— | SHA256:— | |||
| 3072 | IDM_6.4x_Crack_v19.3.exe | C:\Users\admin\AppData\Local\Temp\UPDT.vbs | text | |
MD5:— | SHA256:— | |||
| 2336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:— | SHA256:— | |||
| 2336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:— | SHA256:— | |||
| 2336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF187fca.TMP | text | |
MD5:— | SHA256:— | |||
| 2336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF187fca.TMP | text | |
MD5:— | SHA256:— | |||
| 2336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF187fba.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
30
DNS requests
28
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
2320 | wscript.exe | 188.114.96.3:443 | idm.0dy.ir | CLOUDFLARENET | NL | unknown |
2336 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
480 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
480 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | unknown |
480 | chrome.exe | 5.9.116.176:443 | workupload.com | Hetzner Online GmbH | DE | unknown |
480 | chrome.exe | 142.250.184.194:443 | googleads.g.doubleclick.net | GOOGLE | US | unknown |
480 | chrome.exe | 142.250.185.162:443 | pagead2.googlesyndication.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
idm.0dy.ir |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
workupload.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
t.workupload.com |
| unknown |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |