| File name: | putty.exe |
| Full analysis: | https://app.any.run/tasks/b8f1668e-fbe9-43f9-bff2-a87c48bda447 |
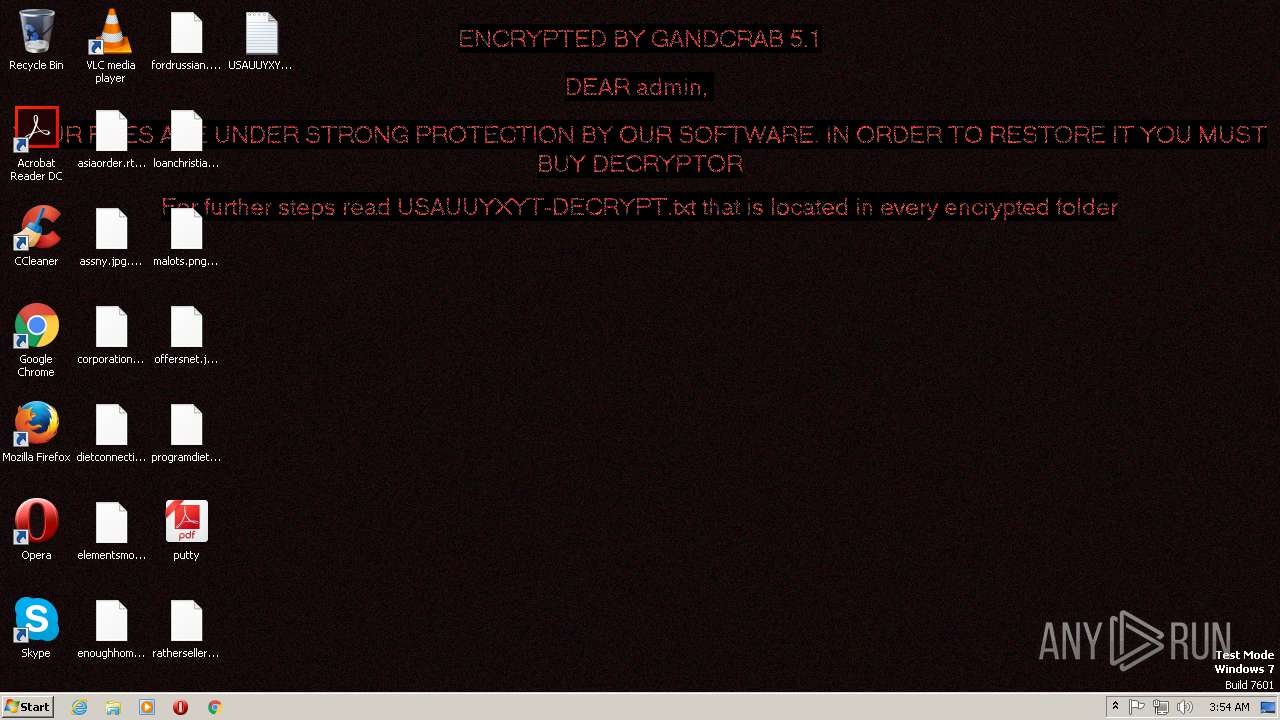
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
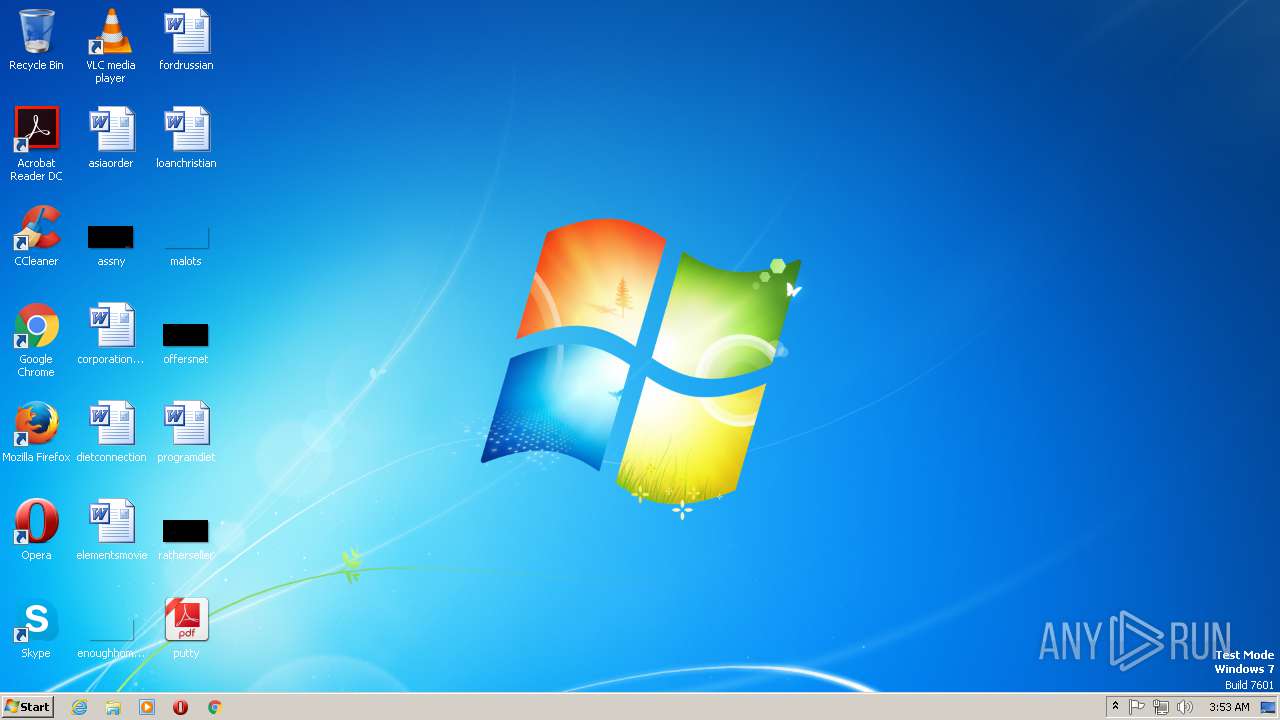
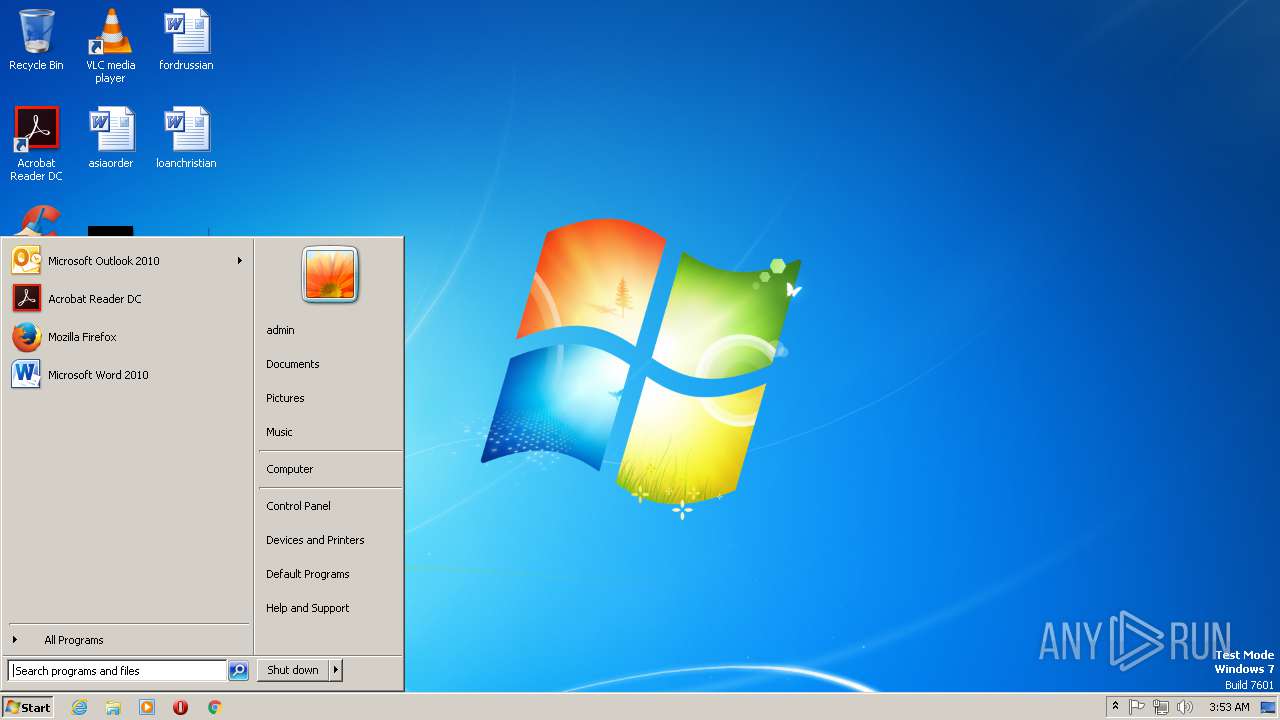
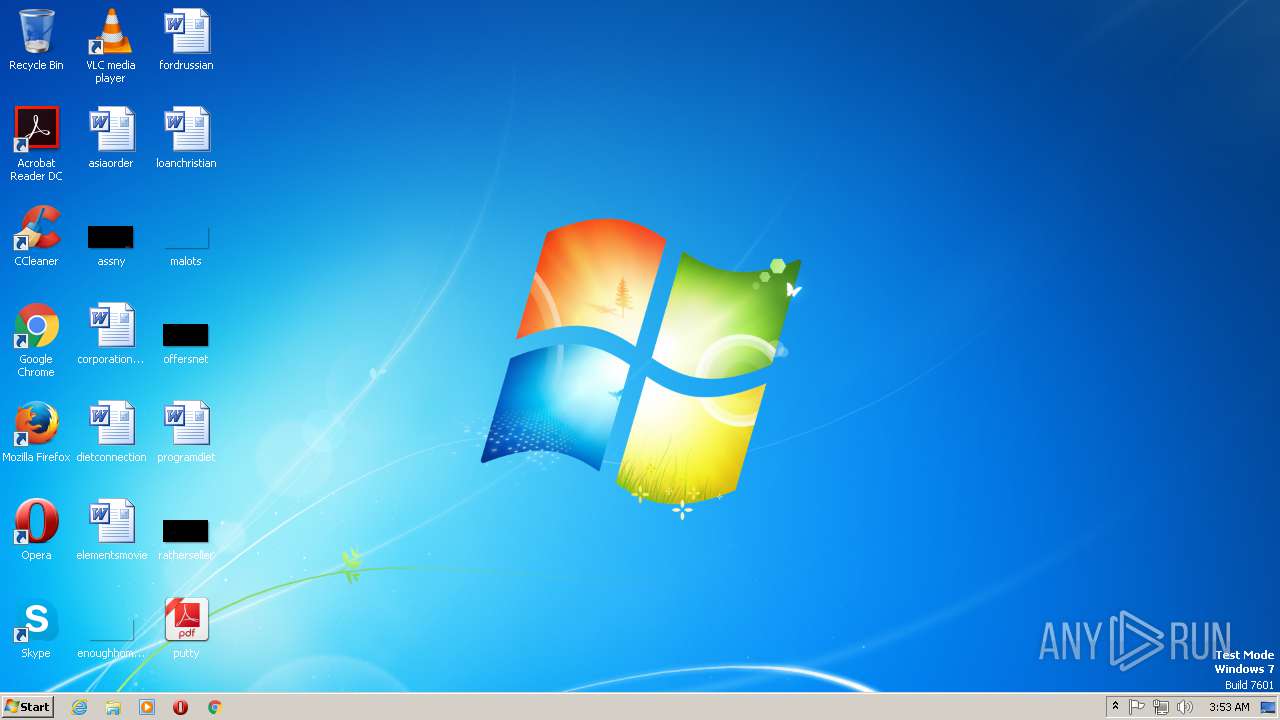
| Analysis date: | January 23, 2019, 03:52:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B6E45A0CDADC8A2A9561D0C207DA465B |
| SHA1: | 9AE5B4DF9A5880E07D61154A867D4E045A913C79 |
| SHA256: | F7EEDA93BCDE57D67B4A418077AE47F1F922FAB7188A994CB1795CE6D833EEB8 |
| SSDEEP: | 12288:e4Zb4OTyvLFGqIzSsuhzw21ZiWuWG8dg1yy0LlgTCmCNuc75:pZbdTU0Ssuhzw2Lnld0yy0LAeX |
MALICIOUS
GandCrab keys found
- putty.exe (PID: 2628)
Deletes shadow copies
- putty.exe (PID: 2628)
Renames files like Ransomware
- putty.exe (PID: 2628)
Writes file to Word startup folder
- putty.exe (PID: 2628)
Dropped file may contain instructions of ransomware
- putty.exe (PID: 2628)
SUSPICIOUS
Creates files like Ransomware instruction
- putty.exe (PID: 2628)
Creates files in the user directory
- putty.exe (PID: 2628)
INFO
Reads settings of System Certificates
- putty.exe (PID: 2628)
Dropped object may contain TOR URL's
- putty.exe (PID: 2628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:22 20:54:28+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 401408 |
| InitializedDataSize: | 254464 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x50a57 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.1.22.6 |
| ProductVersionNumber: | 3.1.22.6 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| LegalCopyright: | Nullsoft, Inc. (C) 2007-2015 |
| PrivateBuild: | 3.1.22.6 |
| Comments: | Audience Need Zimmerman |
| CompanyName: | Nullsoft, Inc. |
| FileDescription: | Audience Need Zimmerman |
| OriginalFileName: | Dbmsrpc3 Follow.exe |
| ProductName: | Dbmsrpc3 Follow |
| LegalTrademarks: | Nullsoft, Inc. (C) 2007-2015 |
| FileVersion: | 3.1.22.6 |
| ProductVersion: | 3.1.22.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Jan-2019 19:54:28 |
| Detected languages: |
|
| Debug artifacts: |
|
| LegalCopyright: | Nullsoft, Inc. (C) 2007-2015 |
| PrivateBuild: | 3.1.22.6 |
| Comments: | Audience Need Zimmerman |
| CompanyName: | Nullsoft, Inc. |
| FileDescription: | Audience Need Zimmerman |
| OriginalFilename: | Dbmsrpc3 Follow.exe |
| ProductName: | Dbmsrpc3 Follow |
| LegalTrademarks: | Nullsoft, Inc. (C) 2007-2015 |
| FileVersion: | 3.1.22.6 |
| ProductVersion: | 3.1.22.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 22-Jan-2019 19:54:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00061F8C | 0x00062000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45005 |
.rdata | 0x00063000 | 0x000161A2 | 0x00016200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.31603 |
.data | 0x0007A000 | 0x000038C4 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.46021 |
.rsrc | 0x0007E000 | 0x0002693C | 0x00026A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.52759 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.03105 | 747 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.76049 | 10344 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.63445 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.7825 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.85642 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 6.01024 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.73717 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.97573 | 104 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
494 | 2.67459 | 464 | Latin 1 / Western European | English - United States | RT_BITMAP |
495 | 4.1166 | 236 | Latin 1 / Western European | English - United States | RT_BITMAP |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSACM32.dll |
OLEAUT32.dll |
OPENGL32.dll |
SHELL32.dll |
SHLWAPI.dll |
Total processes
37
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2064 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\SysWOW64\wbem\wmic.exe | — | putty.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2628 | "C:\Users\admin\Desktop\putty.exe" | C:\Users\admin\Desktop\putty.exe | explorer.exe | ||||||||||||
User: admin Company: Nullsoft, Inc. Integrity Level: MEDIUM Description: Audience Need Zimmerman Exit code: 0 Version: 3.1.22.6 Modules
| |||||||||||||||
Total events
91
Read events
70
Write events
21
Delete events
0
Modification events
| (PID) Process: | (2628) putty.exe | Key: | HKEY_CURRENT_USER\Software\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E007500730061007500750079007800790074000000 | |||
| (PID) Process: | (2628) putty.exe | Key: | HKEY_CURRENT_USER\Software\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A4000052534131000800000100010051897485A0C95EA03806179ADF5FB26045F491A07D24652C1BDE20553E4E58BE04CBEBF5AFBB851E573B1D76AB0CE7096EE26E725ADEEA5F8D9F2E5D48918CE443BBC07DC34A46EAD80EDD181AA1A355882F1CDA6A2E460A00BA79F35C2DE5B361277A7D5F99E9062C77E750B3AE1FB8213E281C11A0311AA1DFADFA7F86F667814E91E364437D500DFC59586BAC2099F035BBD9CB8EB3157090FB02160C137093A9C42B2A4735391FAD1AA9899D4CADF30B77CEBE3ACFB6AE44FDD50B2604E4BA867E3F76D3F727A189690B9BB30E88FD384440236B99B7014C98C232699F32733C7F463B69F28B1498A96E8CB36C8849B6B9B646332BD7C6426277B209AD9C | |||
| (PID) Process: | (2628) putty.exe | Key: | HKEY_CURRENT_USER\Software\keys_data\data |
| Operation: | write | Name: | private |
Value: 94040000E652D684D2EA4949ABD3F2136901A9EE98DC50585CBBE843B1E8D98AE2523A7A007E2ECBD0FBBD891C74540747007AFFFC459A36F26711E9D060248E54BC57FFD4E6BE8A23405E27C04C44EAD4732ADA1A41D6E14E408B740780EA971779C14091C10CDE5EA28ED2E4C84FE430DB0D6F8F7B955BE9834CF2E5A6ADF44A1D762DE8621294A6B59E3685C112F12E416BFCD2BC1FBD66BDFED7121AC470D72614F555B2513AAB12FBC931B1F940E3102A08434F6FEDFA2740E521FB3EB05AA19CF887D4B73F6BDC04ACAA11BDF6618768B5C8086EAF92B2B714A54A3A196C2DC5183E7D8883965F5C53F815F64D013C1D1290F99BF87601CA3F673B94EAE3CF794E330FF1F348000E86F334A90BFE381314762D97043A76F78BCB034EEBBD9528E462BCD425C8F3213FD019DEAE08918F95417022A305D8FA6D8B99577FFD0C87B1C6FDE605B277FA15C55BF9CACFF0AFFD7925879EC13A7D58DD6C5DF178AC1F26766D80950B195CD00E0777011723C80233B717A98697670DBA7051841CD2CFF738770C0F53FD03CA685FFD3B62213E69B2E3CB385AE38AF7AC7F3E5461A31EBD426726AD6E8F549E811783E8905E6991D73DCB8BB904DA6EEF266F09B7E62BB627D21105BA5A1FE0F2EC09DE04FF585A0BD148F79587A9E61121409424FF14E14A8550FD4E4732FFCB5BA9E3CC32C1255634069F721CC53AC02104D205637C5EC96F71C8AD16BF1AD2DBF7014E56E5515C71DA1A6953E882B5036C14A1FF8999F4F1884261DC534FE48C89FC2F08B2ABD21FA1822149A811AFA4518BD93FB8284C014283F821FC3AC5B9704D5E76EB1369CCD2F1D8CE6A4525614EBD15360C1DC427D4EC935C393FF897E53689DF3A374AD1C6118584EAEC6E98F6C8740FA3D1500A21ED1718CA5AB9647E344FE4D6DAEBA727DAD4F178FC8742B337849A7677562FD2699875DD61F08B8A5E2B0FD7DDAE0D47832FC7ACB628C25174DD7C251ACDDACE7C91FECC992C5F56100FA9257E3A901CABFEA8409EAC756188FF32AF9B3583260F16437654505B51FECD2139C0D39B47BCAB652AA3CA733F5F49F1CBF255E032A54A3584787B499D047C80D0A822404C4BF51DD313FA51910F69C61E99C47DADD97CFA3C564836E30FC57FB7BE97BD5972A6A4C6D34AF5A1B7EF1AB8DC597F13B9B406C68A292C66E8F7A420A4E4E6E9DFF31ABB0F1A3EEF857CA70A8FDCE0882D9C5F70A80173A52E9BA618A05D8D14F6A0495E0612A41C52340D9D032A041162717407E97E6933FE16C0A56D739EFD83FB3E0C6229D16E27A2E4DD16B8B36C2AE712F1B8975A601456301003619385FCE5DAEFB60372AF1B866A24C322DBAD2FE2DEB9046EBDFDCEBE7A34D19608B65DDF89C8165CE5A6A210F3DCA0154B8DC25010E998901A78A88FAB757CD5316B92B011C01716E89F76668270D2DBE2912AA941597DED5264EC149829620D2AC72B441F6D5A1970966C8515D3F214807CA585A2A81D6B728066DEAC9BB9D1B4E8C5D15782B13D438A4C11817C2F8D1CCC9FF793C3C9ABA390185C739577F23A7F50C7A825D3BD7A9EDF91100B60920A824779889CE5CC3BC906D1BA45B99DC69C57F92967607E43B8F36968193B74BB49F65DBD30DA3D296F4315E2FBDEC92A4E3B8F51CD532FB1669467AB76688B70872908122D0C4D7E7EF41173D8FC34AEC463A0AA5E964774DA44E86BAC0856B0FEB83C1A37B7E6E4DD2CF039A8F0833F0B2998D21E8397009DBDD5F12CB9558DA67EF81136E79C5C1DCE68CCF99B6F5340D522292B5969F54C361F3F413EB1321B30041552B77C23106D5FBFEBE535A5E26B630A7A0ABF73CD6E31E458DA33FA4CE3A155CE402451E713226F50D8888811E5A1B5254C9BF776ABEF98BE42A1ABE98122E94D8913A48A19C7EE21BB394D77CDCCD13DBED3DE3C7D6EE09327E5A02F96B619AAF97ED731F9F2582DA60B46CDCDC77B9B1F0AE66FEBFA1A43C9E575A3707D57F646D20FD2BA17FC525FACFBF9344B385E4F9A85D4356D8CE2EFE5350BDD49DEA3B1EB0E6A5EFADE8A1E00161E26B38BFC2079443A8F725CA3ABDFBCF64D372149E2FCDCD18EF152A6523B121AA92C08B7F27D4154D0F9E760ECE6B7DD731E2FABA4530E81453D77F9B080608D40A97F30592337A668FAC115F08346C7B711F36C2CADD199B4E4B46505C4F9A7BDB1DF5F14F2747A11FF0AB8520D5704059BF95E12E109E1CACF79C67696CE4F6D85BD87D064744555D4975617992683DA2804320F0797325F816DBF9EF6B3796E6C5B213072C638F302D044C53E8CDAE079B1498E04A9BB142E8CF228FD4846629E5172FB8C5F4A202DD6974AFBC9A5BF3340EB8D6BEC7A6D696F90242F5896CD | |||
| (PID) Process: | (2628) putty.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2628) putty.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2628) putty.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2628) putty.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2628) putty.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2628) putty.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006A000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2628) putty.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
0
Suspicious files
2 185
Text files
208
Unknown types
73
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2628 | putty.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 2628 | putty.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 2628 | putty.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobSettings | — | |
MD5:— | SHA256:— | |||
| 2628 | putty.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\addressbook.acrodata | — | |
MD5:— | SHA256:— | |||
| 2628 | putty.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\0FDED5CEB68C302B1CDB2BDDD9D0000E76539CB0.crl | — | |
MD5:— | SHA256:— | |||
| 2628 | putty.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\CE338828149963DCEA4CD26BB86F0363B4CA0BA5.crl | — | |
MD5:— | SHA256:— | |||
| 2628 | putty.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\USAUUYXYT-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 2628 | putty.exe | C:\Users\admin\AppData\Roaming\USAUUYXYT-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 2628 | putty.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Forms\USAUUYXYT-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 2628 | putty.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\USAUUYXYT-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2628 | putty.exe | GET | 301 | 138.201.162.99:80 | http://www.kakaocorp.link/ | DE | html | 162 b | malicious |
2628 | putty.exe | POST | 404 | 138.201.162.99:443 | https://www.kakaocorp.link/uploads/tmp/kafudemo.png | DE | html | 601 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2628 | putty.exe | 138.201.162.99:80 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
2628 | putty.exe | 138.201.162.99:443 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakaocorp.link |
| malicious |