| File name: | TikTok Report Bot.exe |
| Full analysis: | https://app.any.run/tasks/6cb619ba-e871-4a0c-bb43-2ded23f63494 |
| Verdict: | Suspicious activity |
| Analysis date: | June 04, 2020, 07:58:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 8E6569ED8DA956E76DC37C48A3810411 |
| SHA1: | E486C17192E13419C356C7A4AF399118AD27C372 |
| SHA256: | F7EE0D4F9163573A3C0E97A9E720CFDE2681C490DAFA5DD932DC9C83306C86F8 |
| SSDEEP: | 196608:tkUpmKhT3VVptumuTDpfwmJ8EHlfTCW6EWsQeUpg176ekxyaq56HlpiMMTxNsAl9:tp1vpt8ZwCteW6EWsVMg1O5fWS8MiGA |
MALICIOUS
Loads dropped or rewritten executable
- TikTok Report Bot.exe (PID: 2112)
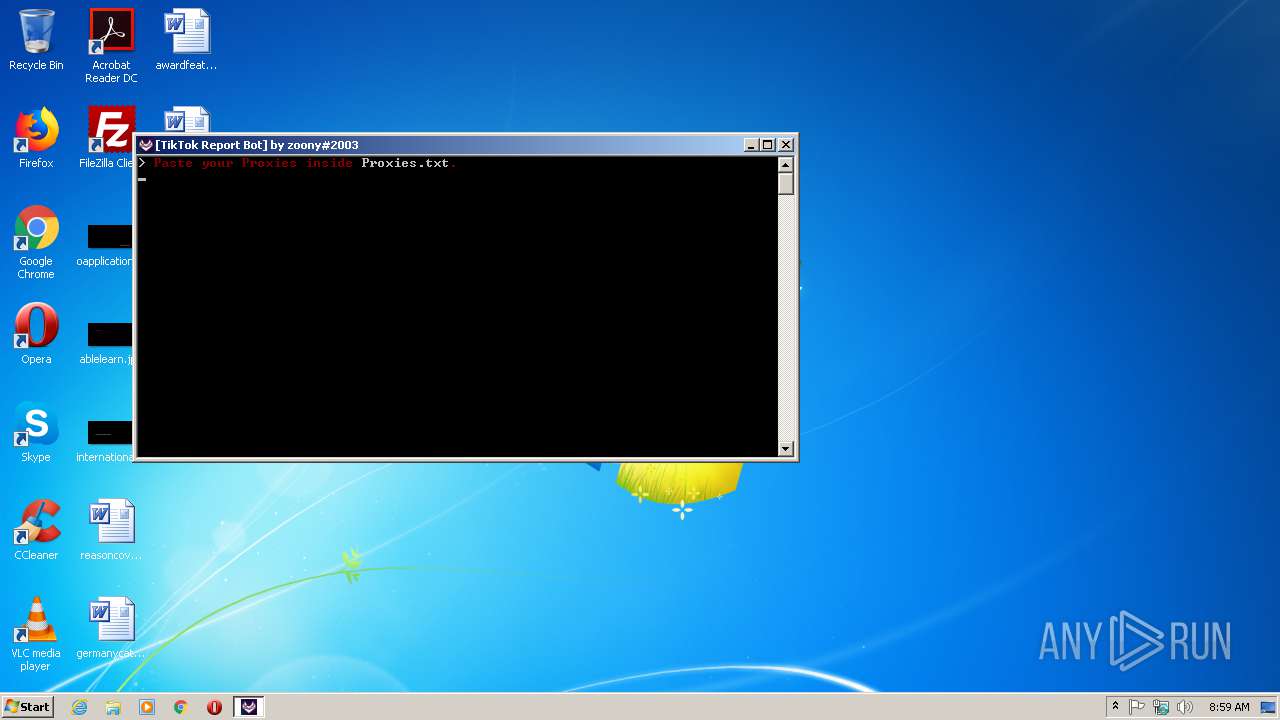
SUSPICIOUS
Application launched itself
- TikTok Report Bot.exe (PID: 2572)
Uses WMIC.EXE to obtain a system information
- TikTok Report Bot.exe (PID: 2112)
Loads Python modules
- TikTok Report Bot.exe (PID: 2112)
Executable content was dropped or overwritten
- TikTok Report Bot.exe (PID: 2572)
INFO
Dropped object may contain Bitcoin addresses
- TikTok Report Bot.exe (PID: 2572)
Reads settings of System Certificates
- TikTok Report Bot.exe (PID: 2112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:09 16:22:19+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 128000 |
| InitializedDataSize: | 123904 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x790a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 09-Jul-2019 14:22:19 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 09-Jul-2019 14:22:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F3B4 | 0x0001F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66635 |
.rdata | 0x00021000 | 0x0000B0EC | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10031 |
.data | 0x0002D000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.94098 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.86637 |
.rsrc | 0x0003D000 | 0x00010D48 | 0x00010E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.54544 |
.reloc | 0x0004E000 | 0x000017D0 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64245 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 2.64638 | 76 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
1 | 5.29574 | 1037 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 6.04955 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.88597 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.63549 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 7.98065 | 44284 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2112 | "C:\Users\admin\AppData\Local\Temp\TikTok Report Bot.exe" | C:\Users\admin\AppData\Local\Temp\TikTok Report Bot.exe | TikTok Report Bot.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2572 | "C:\Users\admin\AppData\Local\Temp\TikTok Report Bot.exe" | C:\Users\admin\AppData\Local\Temp\TikTok Report Bot.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3904 | wmic csproduct get uuid | C:\Windows\System32\Wbem\wmic.exe | — | TikTok Report Bot.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
40
Read events
40
Write events
0
Delete events
0
Modification events
Executable files
66
Suspicious files
2
Text files
17
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | TikTok Report Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI25722\Crypto\Cipher\_raw_aes.cp37-win32.pyd | executable | |
MD5:251902776999479B14CA70BC55271036 | SHA256:37B206E3F689132D449117C4C2778FDDFFF0F9CBE9240AC4A38D779E6641BDFE | |||
| 2572 | TikTok Report Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI25722\Crypto\Cipher\_ARC4.cp37-win32.pyd | executable | |
MD5:9B7D95BE42EFDC9B6BB0A95A1357FB4A | SHA256:6B9DF924CA40F90A9312D9C94F4F6D78295EB91671A8C1D0F2D3C79EDE6CC640 | |||
| 2572 | TikTok Report Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI25722\Crypto\Cipher\_Salsa20.cp37-win32.pyd | executable | |
MD5:8D1CD3515AF7C10AF5E56C08641A0945 | SHA256:26B5AA91AC51F701E5C58680674CBA5BEF75D012D5AE3FDAE54E74EC762F2767 | |||
| 2572 | TikTok Report Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI25722\Crypto\Cipher\_raw_aesni.cp37-win32.pyd | executable | |
MD5:6E2246CF80FB80BBBF4EF4EC427F1551 | SHA256:1CE466D147637C7DDD906854506D01A07FCFF807146A73E4F7B54AC7DD74977E | |||
| 2572 | TikTok Report Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI25722\Crypto\Cipher\_raw_ctr.cp37-win32.pyd | executable | |
MD5:1ED1FA9D2CA368AFF1AE133E6DB469C2 | SHA256:D8A5300EB9E1CC717036C9B47EDEED3B41405BCC2FCAE0E4CDBD1A676934D137 | |||
| 2572 | TikTok Report Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI25722\Crypto\Cipher\_raw_blowfish.cp37-win32.pyd | executable | |
MD5:BDF2E776C9344B811D3B211CA0AAE84B | SHA256:2465B1FD959A8DF6B9C46ADBD01DD089951E54334759B3FC49C3BFDCFECD53BE | |||
| 2572 | TikTok Report Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI25722\Crypto\Cipher\_raw_cast.cp37-win32.pyd | executable | |
MD5:8FF66E96E39F44056B1C0E49F5D6F15C | SHA256:4BEDBE1230EB95949D9B5F20A50E51CBD4910C0589BC679B9D3D97F3720C8A2E | |||
| 2572 | TikTok Report Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI25722\Crypto\Cipher\_chacha20.cp37-win32.pyd | executable | |
MD5:06A6A12719FA7E4B610BFC4CF0F075DA | SHA256:A8ACB90DCEACEC09F6B22394229BC0144A286BC5DDC1E609E0FE8CE6A242F1D1 | |||
| 2572 | TikTok Report Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI25722\Crypto\Cipher\_raw_des3.cp37-win32.pyd | executable | |
MD5:708B780DFB8ED59111B988A42330D0E7 | SHA256:265DFFF8267CBE91C83AD3AC42D5728E273D5B52DB2B53C0691D4CD53E94D175 | |||
| 2572 | TikTok Report Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI25722\Crypto\Cipher\_raw_cfb.cp37-win32.pyd | executable | |
MD5:E92E8E711ECB30CFF67014C39176E180 | SHA256:E9C7E46571D11977D7A5D57B9D8420B8413DCFC0F4897C3AFAE21EC457976181 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
6
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2112 | TikTok Report Bot.exe | 104.23.99.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
2112 | TikTok Report Bot.exe | 3.127.93.191:27017 | zoony-shard-00-00-kn0um.mongodb.net | — | US | unknown |
2112 | TikTok Report Bot.exe | 3.123.151.6:27017 | zoony-shard-00-02-kn0um.mongodb.net | — | US | unknown |
2112 | TikTok Report Bot.exe | 3.125.110.76:27017 | zoony-shard-00-01-kn0um.mongodb.net | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
_mongodb._tcp.zoony-kn0um.mongodb.net |
| unknown |
zoony-kn0um.mongodb.net |
| unknown |
zoony-shard-00-02-kn0um.mongodb.net |
| unknown |
zoony-shard-00-01-kn0um.mongodb.net |
| unknown |
zoony-shard-00-00-kn0um.mongodb.net |
| unknown |