| URL: | https://ctrk.klclick3.com/l/01KFZ21ZE4DD098RP62GWF94JH_0 |
| Full analysis: | https://app.any.run/tasks/14cd3dd5-0188-4982-a884-93adbc344626 |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2026, 14:31:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3D6C9FFED813FDD153212891941BCB4D |
| SHA1: | 1B825DA07B8E1DCB88980C9C5C44B5BF004DD636 |
| SHA256: | F7ECF0A66DED06F8EFCBACB7BDE9C27C46A7E7AAD8A7282FD226706C3BF09AF6 |
| SSDEEP: | 3:N8Mel0HV+sfTWYvo:2MelKVFfNo |
MALICIOUS
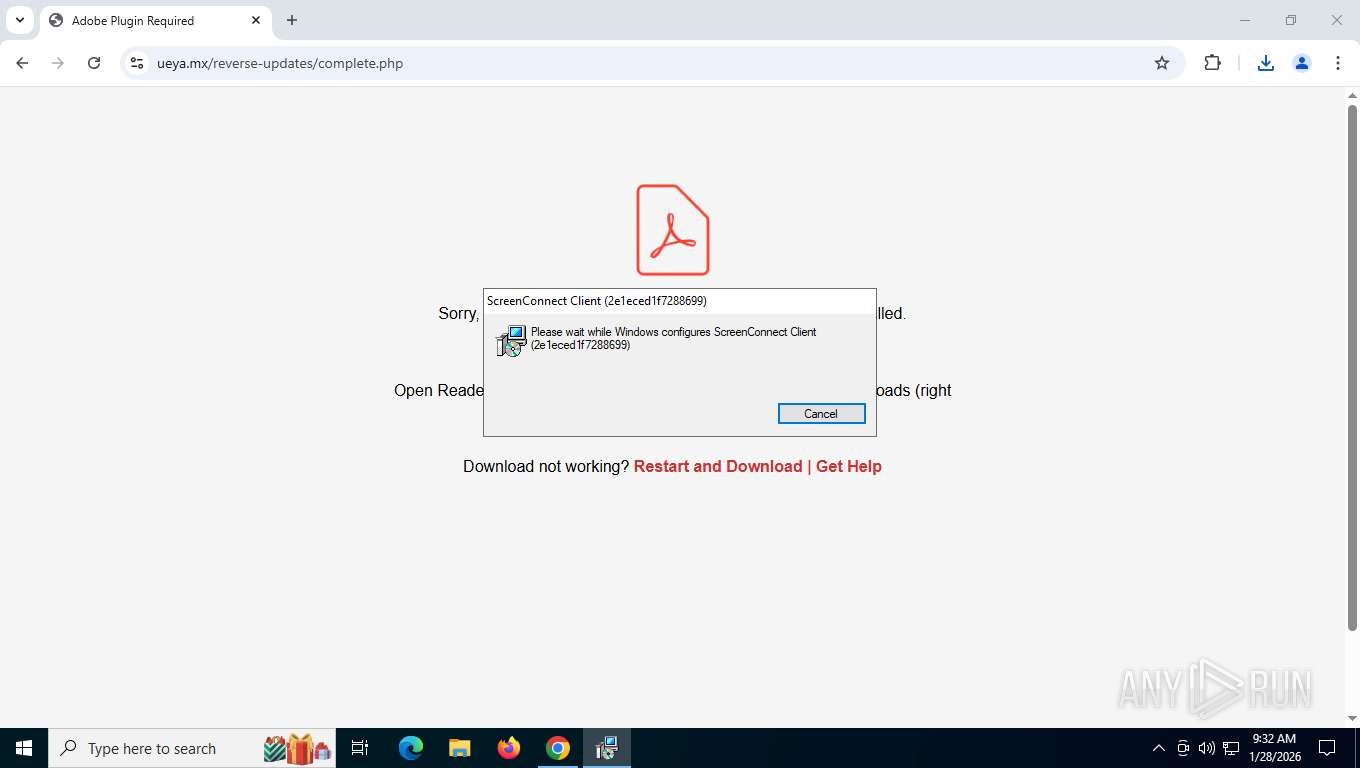
SCREENCONNECT has been detected
- rundll32.exe (PID: 7720)
- msiexec.exe (PID: 2348)
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 7268)
SUSPICIOUS
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 7268)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 7268)
Executes as Windows Service
- VSSVC.exe (PID: 6668)
- ScreenConnect.ClientService.exe (PID: 7268)
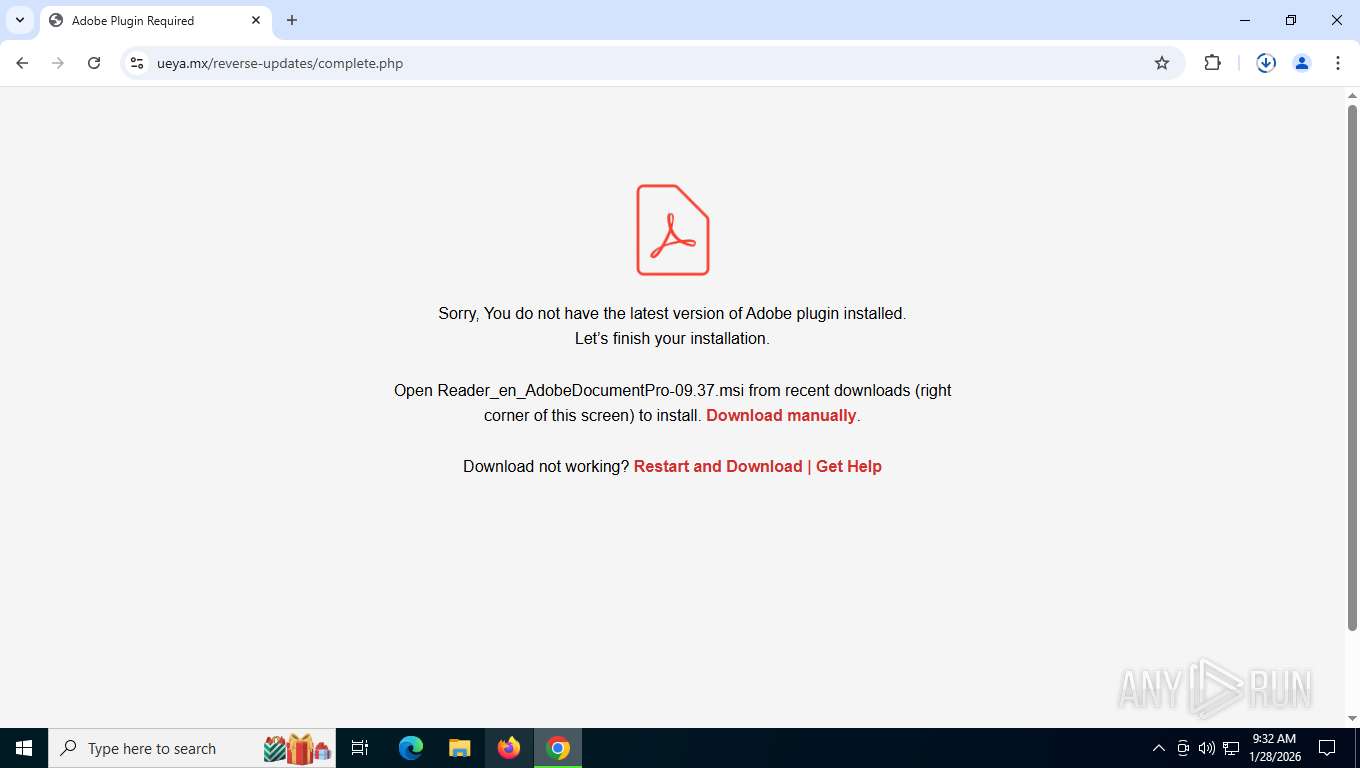
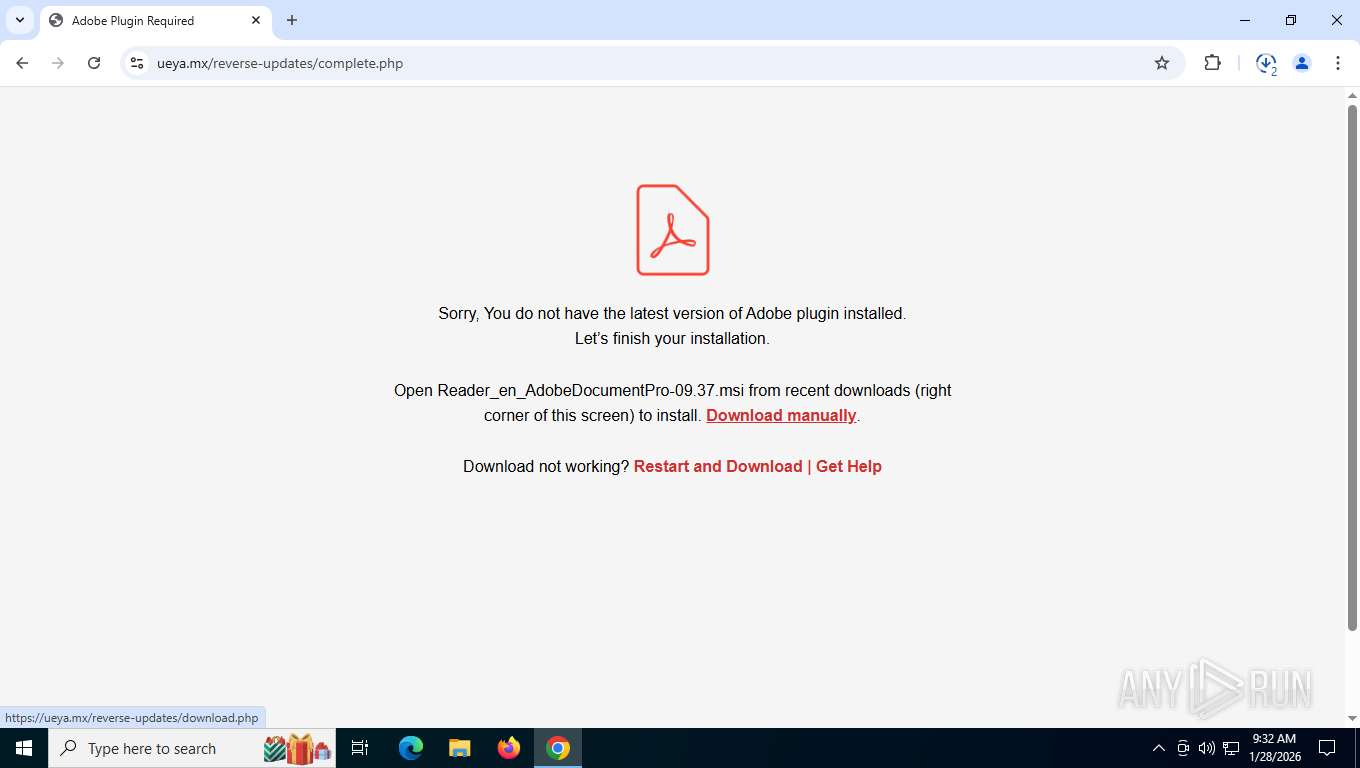
Executable content was dropped or overwritten
- rundll32.exe (PID: 7720)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 7268)
- ScreenConnect.ClientService.exe (PID: 7268)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 7268)
INFO
Reads security settings of Internet Explorer
- msiexec.exe (PID: 4036)
- ScreenConnect.ClientService.exe (PID: 7268)
- ScreenConnect.WindowsClient.exe (PID: 1704)
- ScreenConnect.WindowsClient.exe (PID: 4072)
Application launched itself
- chrome.exe (PID: 4256)
Checks supported languages
- msiexec.exe (PID: 1492)
- msiexec.exe (PID: 2348)
- ScreenConnect.ClientService.exe (PID: 7268)
- msiexec.exe (PID: 864)
- msiexec.exe (PID: 5472)
- ScreenConnect.WindowsClient.exe (PID: 4072)
- ScreenConnect.WindowsClient.exe (PID: 1704)
Reads the computer name
- msiexec.exe (PID: 2348)
- msiexec.exe (PID: 1492)
- ScreenConnect.ClientService.exe (PID: 7268)
- msiexec.exe (PID: 864)
- msiexec.exe (PID: 5472)
- ScreenConnect.WindowsClient.exe (PID: 1704)
- ScreenConnect.WindowsClient.exe (PID: 4072)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4036)
- msiexec.exe (PID: 2348)
Create files in a temporary directory
- rundll32.exe (PID: 7720)
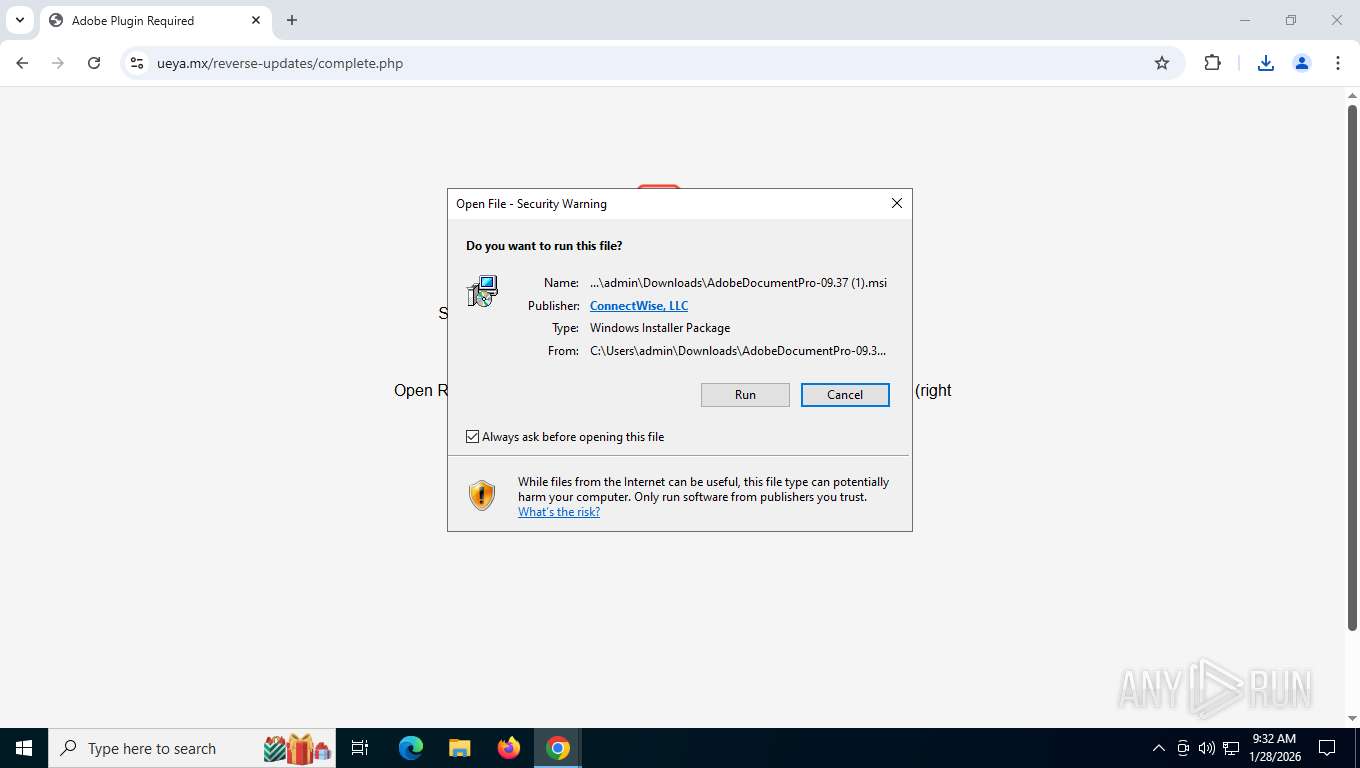
CONNECTWISE has been detected
- msiexec.exe (PID: 4036)
- ScreenConnect.WindowsClient.exe (PID: 1704)
- ScreenConnect.ClientService.exe (PID: 7268)
- ScreenConnect.WindowsClient.exe (PID: 4072)
Reads the machine GUID from the registry
- ScreenConnect.ClientService.exe (PID: 7268)
- ScreenConnect.WindowsClient.exe (PID: 1704)
- ScreenConnect.WindowsClient.exe (PID: 4072)
SCREENCONNECT has been detected
- ScreenConnect.ClientService.exe (PID: 7268)
Manages system restore points
- SrTasks.exe (PID: 4552)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 4072)
Checks proxy server information
- slui.exe (PID: 9188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
202
Monitored processes
44
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | C:\Windows\syswow64\MsiExec.exe -Embedding 4670432FE28211EE02C9B45C1E767A42 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5632,i,12599819912203112879,1215130814150963805,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5848 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=3252,i,12599819912203112879,1215130814150963805,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=3424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1492 | C:\Windows\syswow64\MsiExec.exe -Embedding 1E0505FA626A828AADD2F01CA7867BD5 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1704 | "C:\Program Files (x86)\ScreenConnect Client (2e1eced1f7288699)\ScreenConnect.WindowsClient.exe" "RunRole" "66a6f24c-9534-42ad-8c64-58a8b4fa097d" "User" | C:\Program Files (x86)\ScreenConnect Client (2e1eced1f7288699)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Version: 25.9.5.9473 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5668,i,12599819912203112879,1215130814150963805,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4972,i,12599819912203112879,1215130814150963805,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5644 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2348 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=6132,i,12599819912203112879,1215130814150963805,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6152 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6128,i,12599819912203112879,1215130814150963805,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5700 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
5 757
Read events
5 606
Write events
142
Delete events
9
Modification events
| (PID) Process: | (2348) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000EB3647EE6290DC012C09000034080000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2348) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000EB3647EE6290DC012C09000034080000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2348) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000CE1F91EE6290DC012C09000034080000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2348) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000CE1F91EE6290DC012C09000034080000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2348) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000CE1F91EE6290DC012C09000034080000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2348) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000648293EE6290DC012C09000034080000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2348) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 15 | |||
| (PID) Process: | (2348) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000BF59ABEE6290DC012C0900001C1B0000E803000001000000000000000000000062AC742E768F0441B4922058A892DA3200000000000000000000000000000000 | |||
| (PID) Process: | (6668) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000009E3B4EE6290DC010C1A0000641E0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6668) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000009E3B4EE6290DC010C1A0000500A0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
20
Suspicious files
90
Text files
77
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF1b416a.TMP | — | |
MD5:— | SHA256:— | |||
| 4256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF1b417a.TMP | — | |
MD5:— | SHA256:— | |||
| 4256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF1b417a.TMP | — | |
MD5:— | SHA256:— | |||
| 4256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1b415b.TMP | — | |
MD5:— | SHA256:— | |||
| 4256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1b417a.TMP | — | |
MD5:— | SHA256:— | |||
| 4256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1b417a.TMP | — | |
MD5:— | SHA256:— | |||
| 4256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
77
TCP/UDP connections
67
DNS requests
58
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5804 | chrome.exe | GET | 200 | 172.217.16.206:80 | http://clients2.google.com/time/1/current?cup2key=8:Q9Cn5flF-5GQtGFpvnnic_Nt5iazcXkGJ3dQDChetA0&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
5804 | chrome.exe | GET | 200 | 216.58.206.74:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | unknown | binary | 41 b | whitelisted |
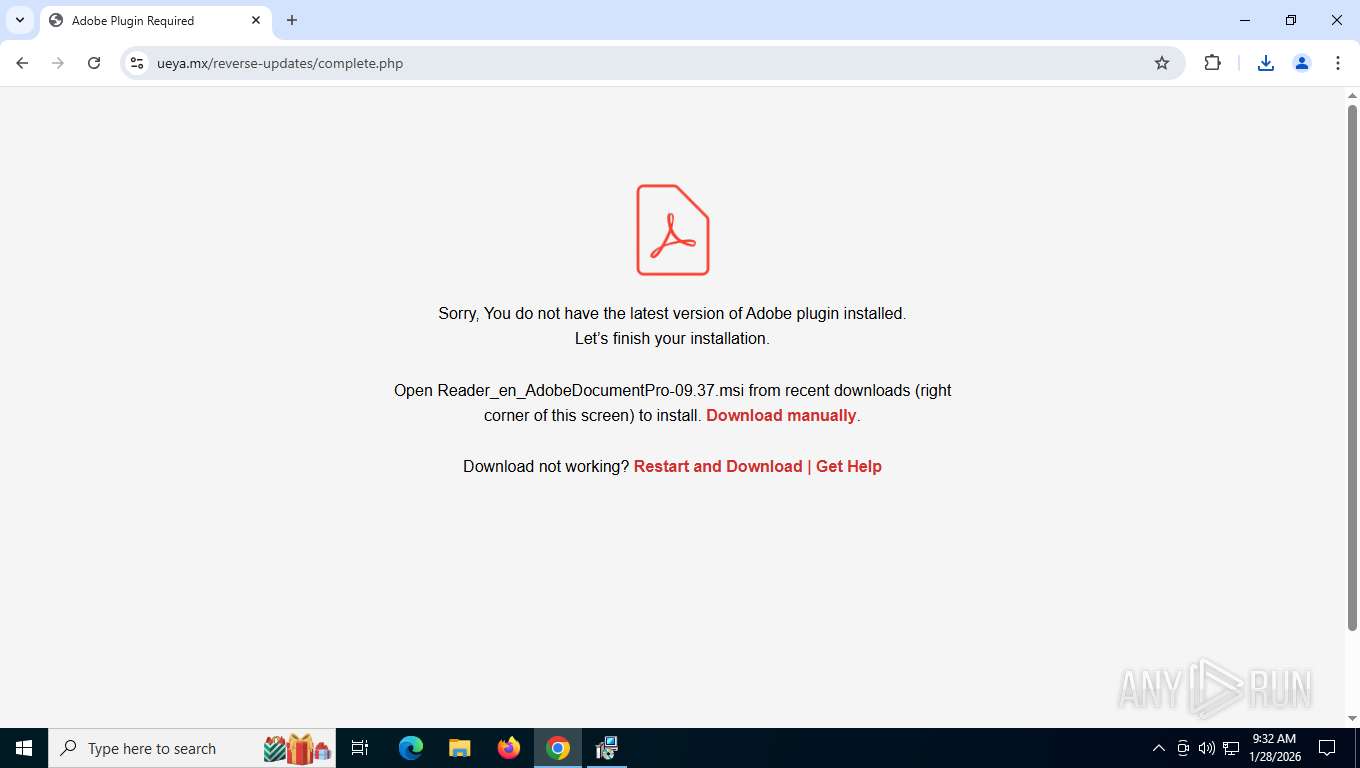
5804 | chrome.exe | GET | 302 | 104.17.93.1:443 | https://ctrk.klclick3.com/l/01KFZ21ZE4DD098RP62GWF94JH_0 | unknown | html | 131 b | unknown |
5804 | chrome.exe | GET | 200 | 172.217.208.94:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=win&channel=stable&milestone=133 | unknown | compressed | 81.1 Kb | whitelisted |
5804 | chrome.exe | POST | 200 | 142.251.127.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | unknown | text | 17 b | whitelisted |
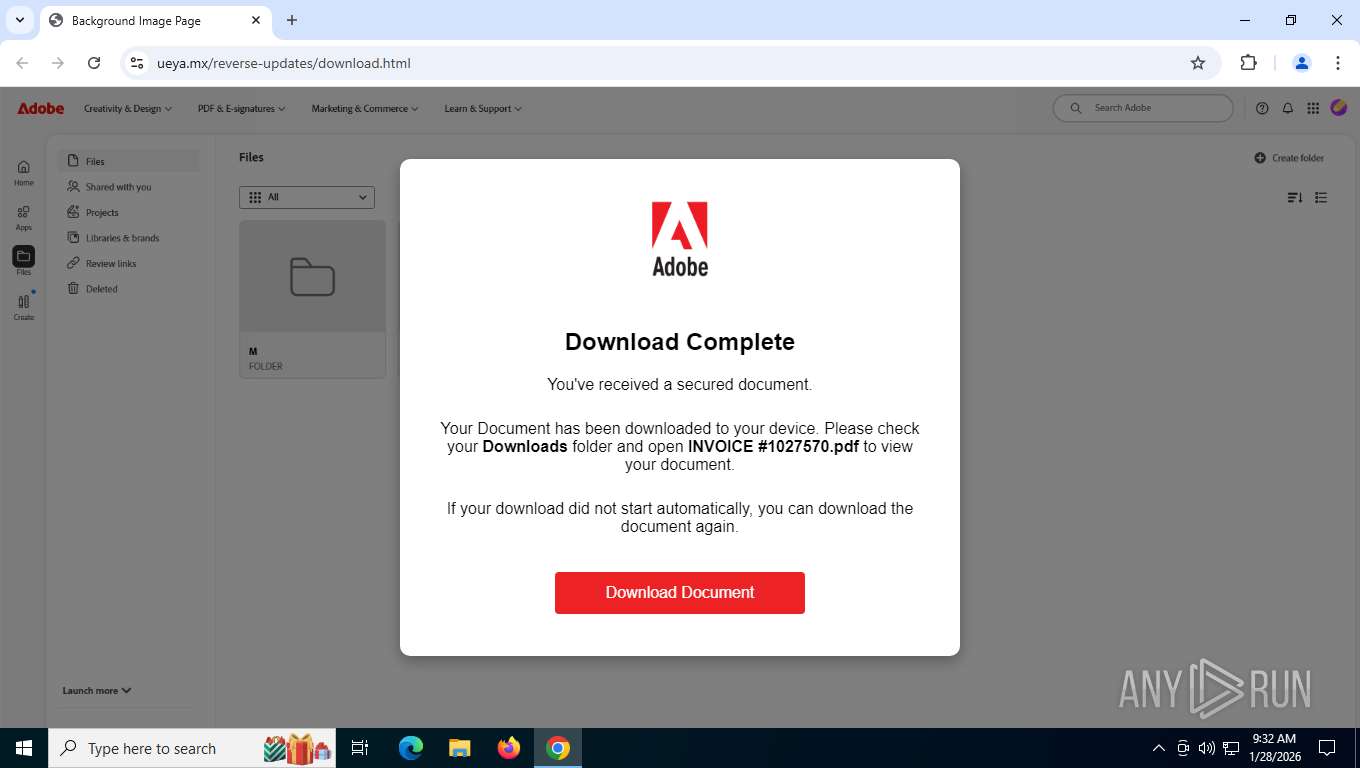
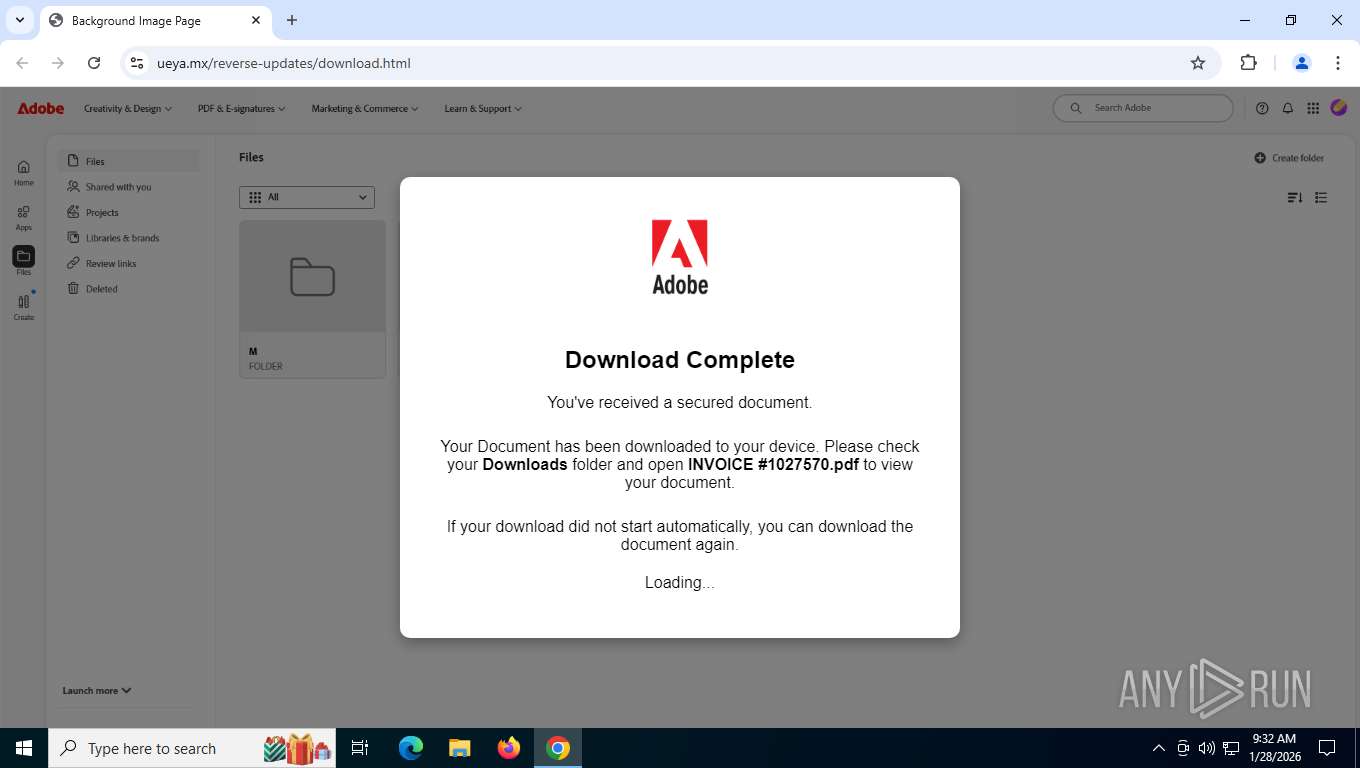
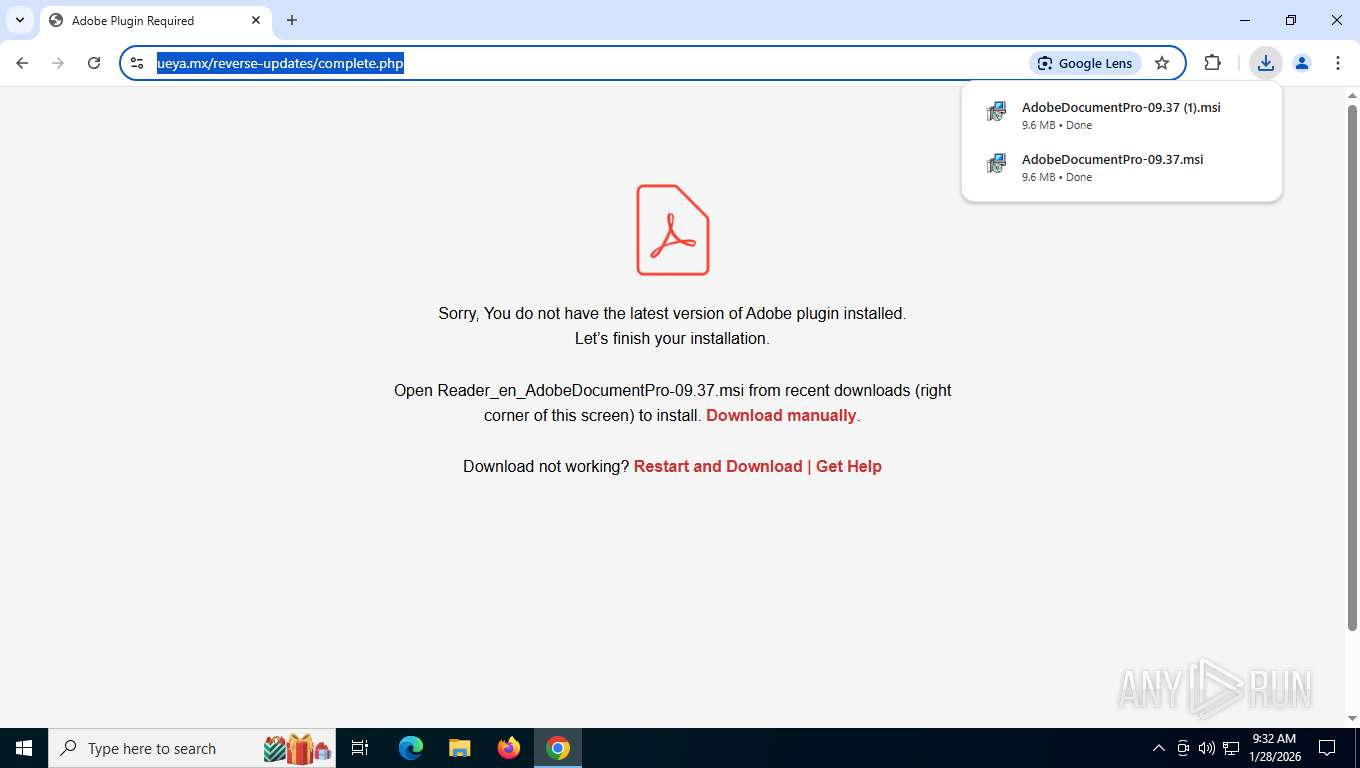
5804 | chrome.exe | GET | 200 | 108.179.194.83:443 | https://ueya.mx/reverse-updates/?_kx=_Q5h34PpRB501oQcjv4QoG3oJ6tCWx3rsEx5jh0olzqYKj7XzydbKOD1XRaEjY9G.TUeSXV | unknown | html | 2.72 Kb | unknown |
5804 | chrome.exe | GET | 200 | 142.251.208.163:443 | https://fonts.gstatic.com/s/poppins/v24/pxiByp8kv8JHgFVrLGT9Z1xlFQ.woff2 | unknown | binary | 7.57 Kb | whitelisted |
5804 | chrome.exe | GET | 200 | 108.179.194.83:443 | https://ueya.mx/reverse-updates/adobe-logo.png | unknown | image | 69.0 Kb | unknown |
5804 | chrome.exe | GET | 404 | 108.179.194.83:443 | https://ueya.mx/favicon.ico | unknown | html | 11.5 Kb | unknown |
5804 | chrome.exe | GET | 200 | 74.125.29.95:443 | https://fonts.googleapis.com/css2?family=Poppins:wght@200;300;400;500&display=swap | unknown | text | 4.68 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4336 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2496 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.204.160:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
5804 | chrome.exe | 172.217.16.206:80 | clients2.google.com | GOOGLE | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5804 | chrome.exe | 172.217.208.94:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
5804 | chrome.exe | 216.58.206.74:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
5804 | chrome.exe | 142.251.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
ctrk.klclick3.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
ueya.mx |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5804 | chrome.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
5804 | chrome.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
5804 | chrome.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
— | — | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2292 | svchost.exe | Misc activity | ET REMOTE_ACCESS Observed DNS Query to Known ScreenConnect/ConnectWise Remote Desktop Service Domain |
7268 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |