| download: | index.html |
| Full analysis: | https://app.any.run/tasks/e77736a7-31a4-4a96-8bff-a0e508c2efc4 |
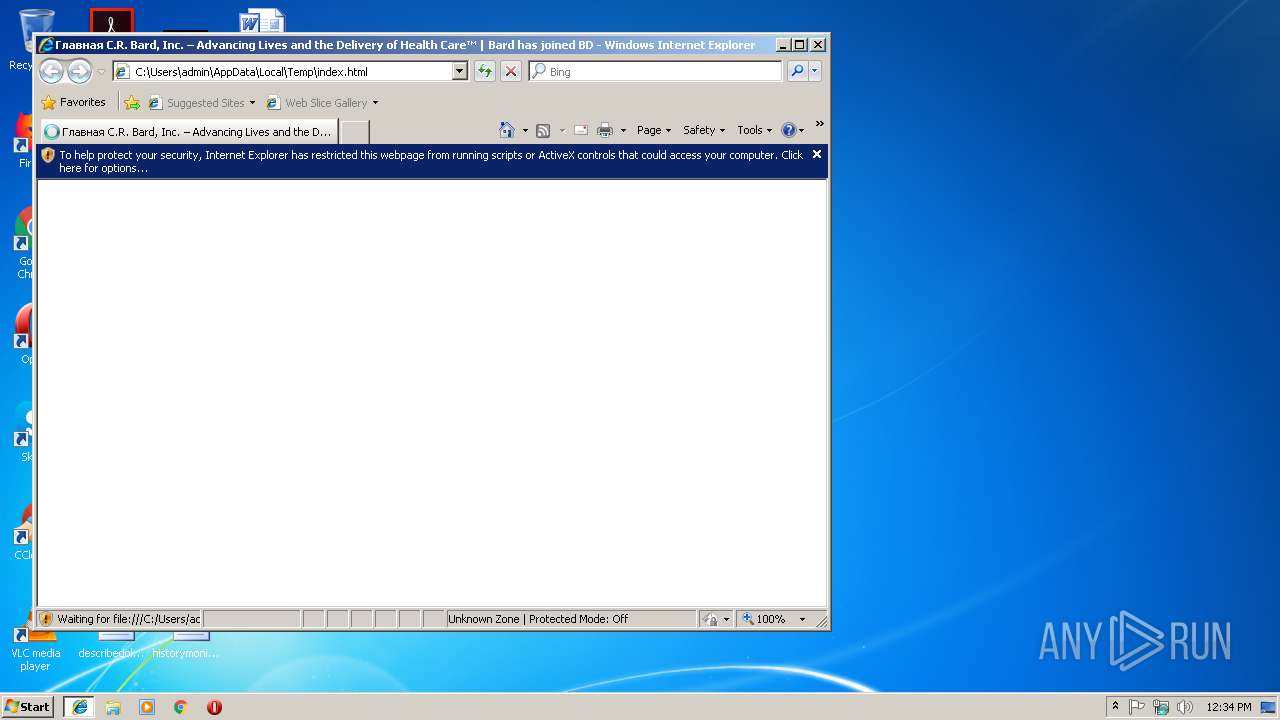
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2019, 12:34:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | A0AAA3D4BB26702E774FA278B2D289E1 |
| SHA1: | 5D2331B5FE1F26E5E2D138819948BF47F933AC58 |
| SHA256: | F7E58EC0D19E956B5EE8B38126A2C3941DBAFA31D5DF9FF051BB6FFB0D7B9949 |
| SSDEEP: | 1536:FRugijaBpBuSogdEvbxzQ5InTHdASYiYX:DugijaBpB5BOjL7YX |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 2996)
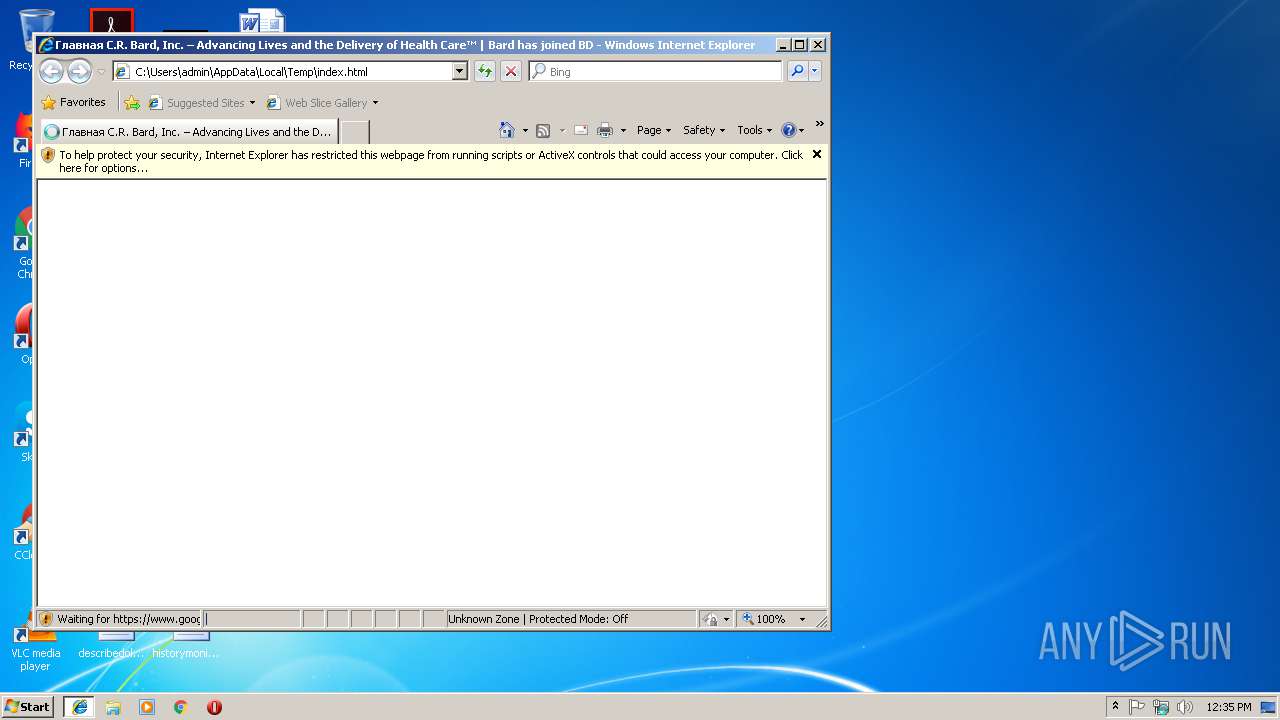
Application launched itself
- iexplore.exe (PID: 2996)
- chrome.exe (PID: 3724)
Reads internet explorer settings
- iexplore.exe (PID: 3440)
Reads settings of System Certificates
- iexplore.exe (PID: 3440)
Changes settings of System certificates
- iexplore.exe (PID: 3440)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3440)
Reads Internet Cache Settings
- iexplore.exe (PID: 3440)
Creates files in the user directory
- iexplore.exe (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
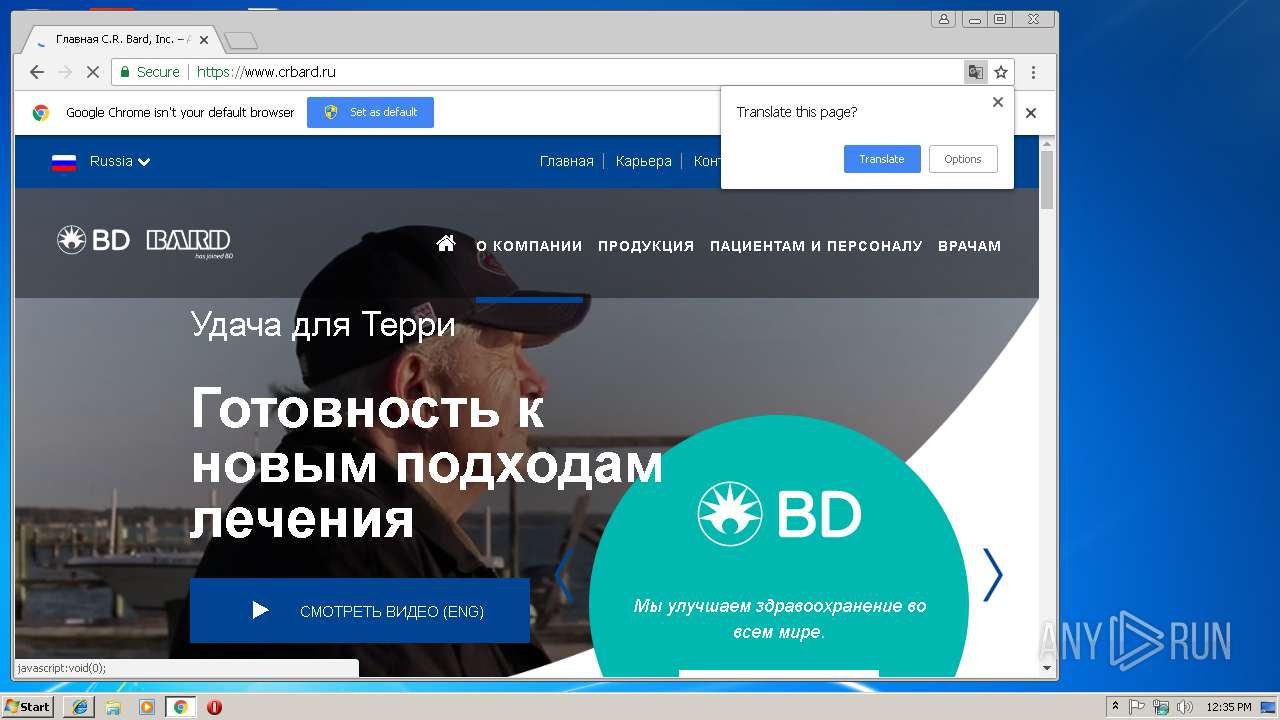
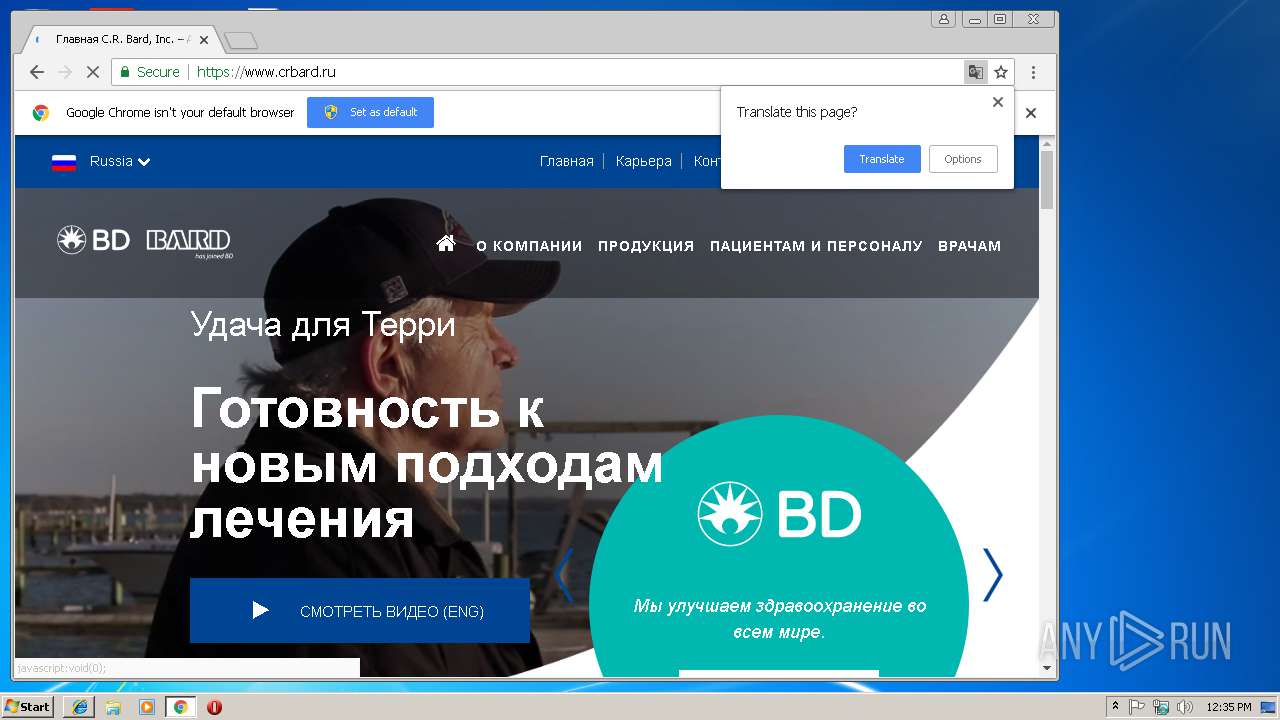
| Title: | Главная C.R. Bard, Inc. – Advancing Lives and the Delivery of Health Care™ | Bard has joined BD |
|---|---|
| Description: | Уже более века компания C. R. Bard, Inc. находится на переднем крае разработки и производства воодушевляющих новаторских медицинских технологий, предназначенных для специалистов в области заболеваний сосудов, урологии, онкологии и хирургии. |
| Keywords: | Медицинские устройства, Bard, новаторский, медицинская технология, урология, сосудистый, онкология, хирургический, инновация в области здравоохранения, медицинский, технология, лидер, здравоохранение |
| HTTPEquivXUACompatible: | IE=edge |
| viewport: | width=device-width, initial-scale=1 |
Total processes
46
Monitored processes
15
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6027066597280855664,8097066696359183829,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6F2FE387EB264E4C0A9613356EB50F0E --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6F2FE387EB264E4C0A9613356EB50F0E --renderer-client-id=7 --mojo-platform-channel-handle=4296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6027066597280855664,8097066696359183829,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=C3EBFFD6312A44493F65FCFF81041233 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C3EBFFD6312A44493F65FCFF81041233 --renderer-client-id=6 --mojo-platform-channel-handle=2928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6de300b0,0x6de300c0,0x6de300cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6027066597280855664,8097066696359183829,131072 --enable-features=PasswordImport --service-pipe-token=881D47761693DC7AEB65BE09EFBA77AF --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=881D47761693DC7AEB65BE09EFBA77AF --renderer-client-id=5 --mojo-platform-channel-handle=1916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2996 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6027066597280855664,8097066696359183829,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=D2A2EF780F138787384742A45577E8A8 --mojo-platform-channel-handle=3888 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3440 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2996 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6027066597280855664,8097066696359183829,131072 --enable-features=PasswordImport --service-pipe-token=193C383C9CEDBE888A854BBE9F416494 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=193C383C9CEDBE888A854BBE9F416494 --renderer-client-id=3 --mojo-platform-channel-handle=2084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6027066597280855664,8097066696359183829,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=EBC19844E3FE0622C2A5AC556D40B322 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=EBC19844E3FE0622C2A5AC556D40B322 --renderer-client-id=9 --mojo-platform-channel-handle=4180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,6027066597280855664,8097066696359183829,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=E7AA222D001E90FB0B8E77E4FBADD596 --mojo-platform-channel-handle=1028 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
934
Read events
808
Write events
120
Delete events
6
Modification events
| (PID) Process: | (2996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {70732817-2DF9-11E9-AA93-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307020001000B000C0022003A006600 | |||
Executable files
0
Suspicious files
91
Text files
131
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2996 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\D2YPIJ90\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab7C.tmp | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar7D.tmp | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab9D.tmp | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar9E.tmp | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab11C.tmp | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar11D.tmp | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\c0190c1152[1].js | text | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\css[1].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
186
DNS requests
76
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3440 | iexplore.exe | OPTIONS | 301 | 151.101.0.217:80 | http://player.vimeo.com/ | US | — | — | whitelisted |
3440 | iexplore.exe | OPTIONS | 301 | 151.101.0.217:80 | http://player.vimeo.com/ | US | — | — | whitelisted |
3440 | iexplore.exe | OPTIONS | 301 | 151.101.0.217:80 | http://player.vimeo.com/ | US | — | — | whitelisted |
3440 | iexplore.exe | OPTIONS | 301 | 151.101.0.217:80 | http://player.vimeo.com/ | US | — | — | whitelisted |
3440 | iexplore.exe | OPTIONS | 301 | 151.101.0.217:80 | http://player.vimeo.com/ | US | — | — | whitelisted |
3440 | iexplore.exe | OPTIONS | 301 | 151.101.0.217:80 | http://player.vimeo.com/ | US | — | — | whitelisted |
3440 | iexplore.exe | OPTIONS | 301 | 151.101.0.217:80 | http://player.vimeo.com/ | US | — | — | whitelisted |
3440 | iexplore.exe | OPTIONS | 301 | 151.101.0.217:80 | http://player.vimeo.com/ | US | — | — | whitelisted |
3440 | iexplore.exe | OPTIONS | 301 | 151.101.0.217:80 | http://player.vimeo.com/ | US | — | — | whitelisted |
3440 | iexplore.exe | OPTIONS | 301 | 151.101.0.217:80 | http://player.vimeo.com/ | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2996 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3440 | iexplore.exe | 205.185.208.52:443 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
3440 | iexplore.exe | 216.58.208.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3440 | iexplore.exe | 23.111.8.154:443 | oss.maxcdn.com | netDNA | US | unknown |
3440 | iexplore.exe | 161.47.83.236:443 | stage.crbard.com | Rackspace Ltd. | US | unknown |
4 | System | 151.101.192.217:445 | player.vimeo.com | Fastly | US | suspicious |
3440 | iexplore.exe | 104.19.195.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
3724 | chrome.exe | 172.217.22.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3440 | iexplore.exe | 50.57.238.107:443 | www.crbard.com | Rackspace Ltd. | US | unknown |
4 | System | 151.101.64.217:445 | player.vimeo.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
oss.maxcdn.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
code.jquery.com |
| whitelisted |
use.fontawesome.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
player.vimeo.com |
| whitelisted |
stage.crbard.com |
| unknown |
Threats
10 ETPRO signatures available at the full report