| File name: | Mojo.setup.exe |
| Full analysis: | https://app.any.run/tasks/9b92c6cc-6df5-4413-892c-dad495aa8ed3 |
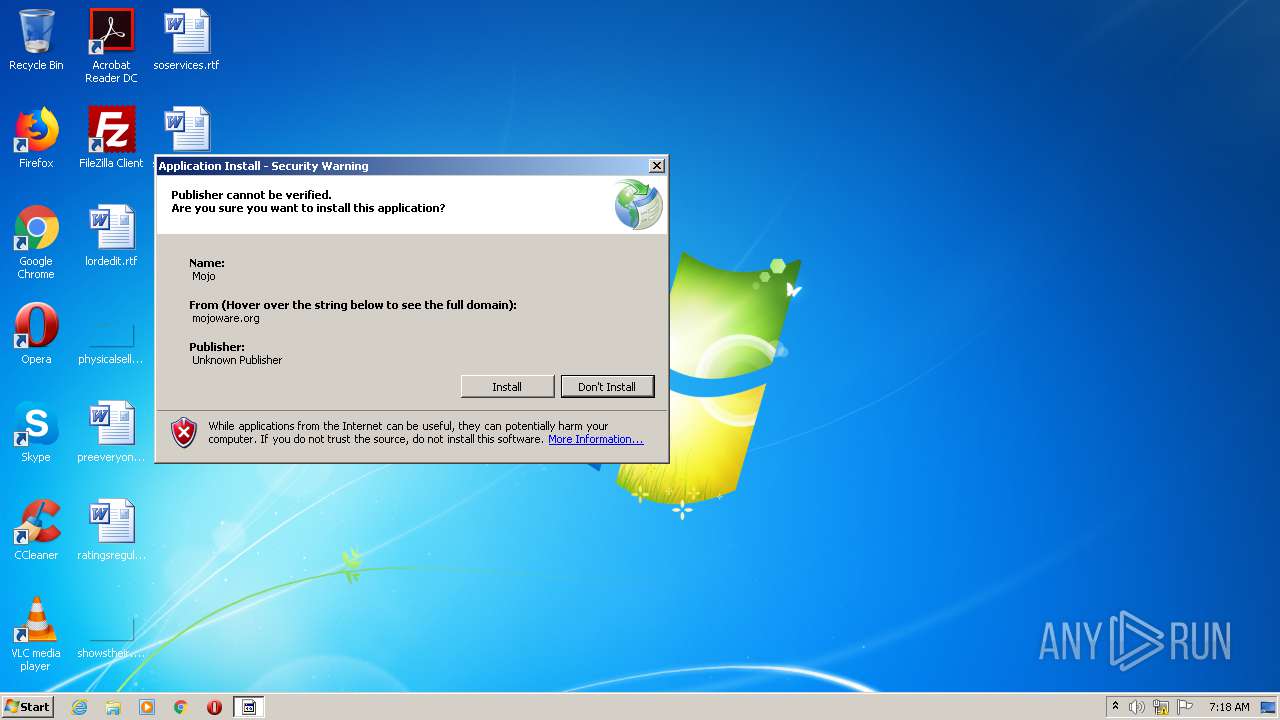
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 06:18:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 93D8FDCCC7CFF0BA01AF1982EF6D1825 |
| SHA1: | 73554F41D024298672C2776DE1B44153B74A41D6 |
| SHA256: | F7DD21583727DAB31175FD5F9822B21766C09108AE76A2CC9F0CCFA16D3A9FDC |
| SSDEEP: | 6144:MqI9MzRJtM/mQU+27Udfz88bXoLBIiW6RwTePiAHSluQUojDuUl0pY:M7CEd7UVIiW6RwTeKAHTeDuUl7 |
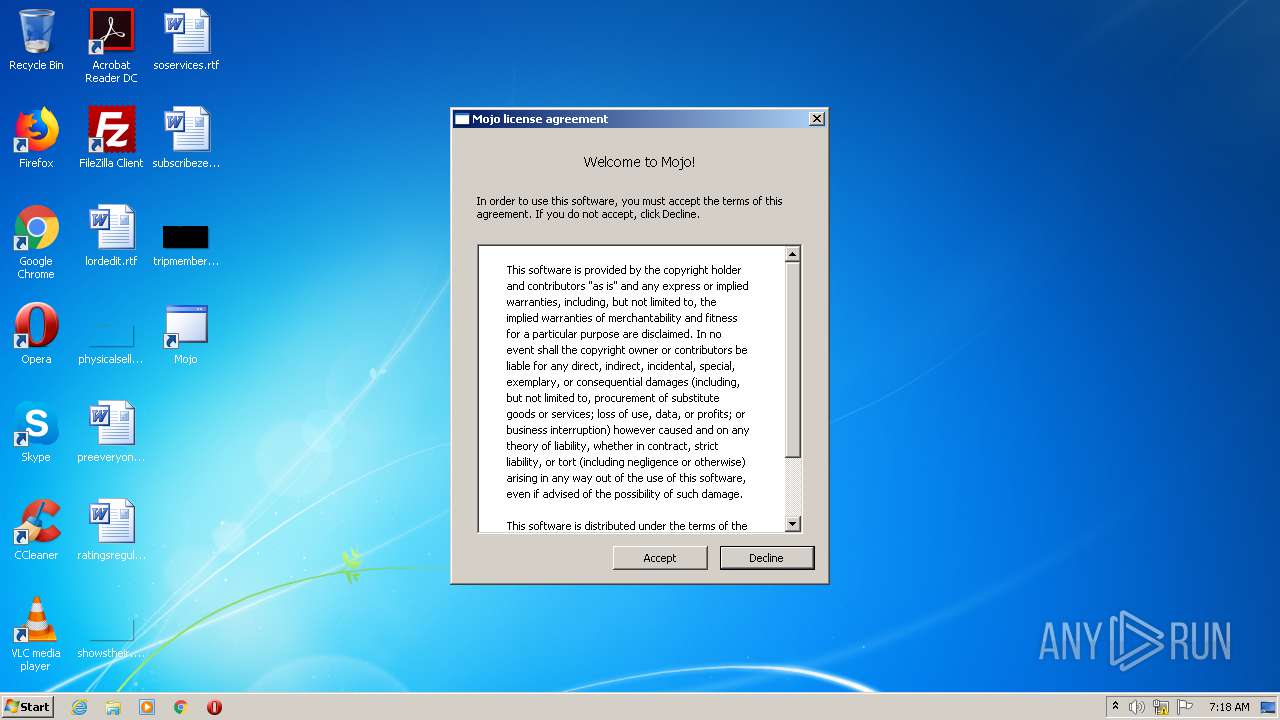
MALICIOUS
Application was dropped or rewritten from another process
- mojo.exe (PID: 2236)
- mojo.exe (PID: 2212)
- MojoInstaller.exe (PID: 3000)
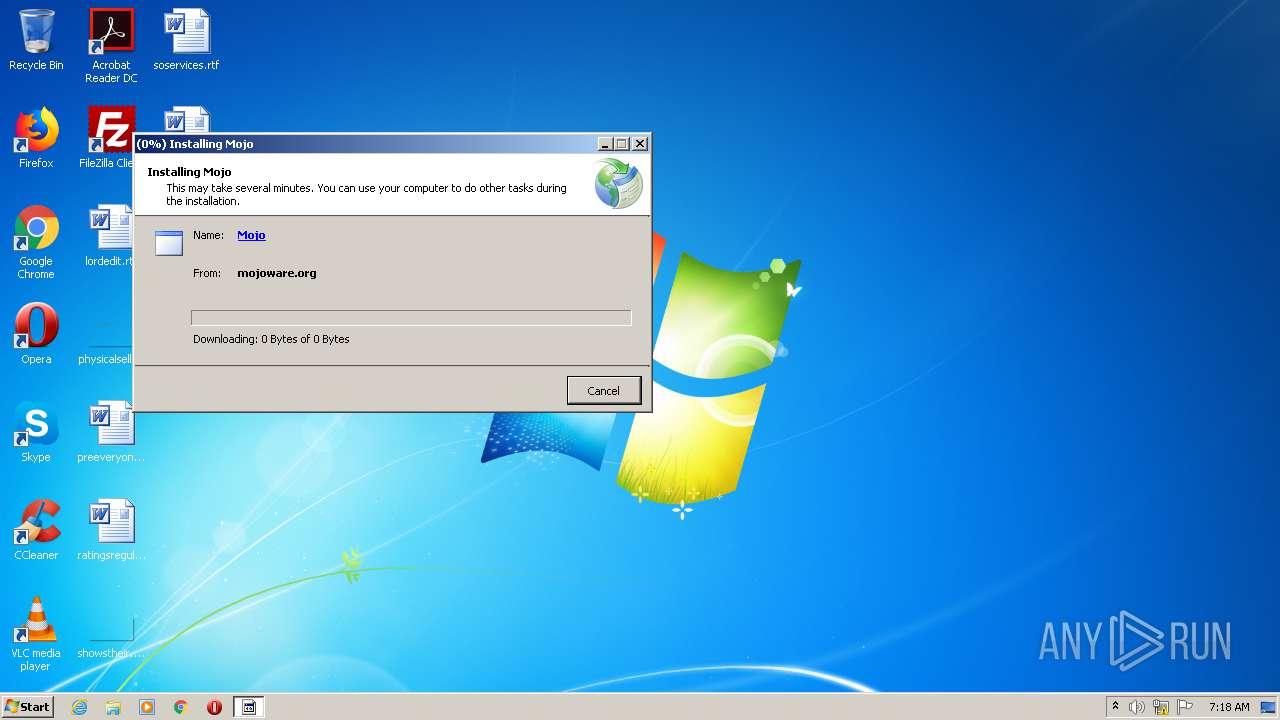
Loads dropped or rewritten executable
- mojo.exe (PID: 2212)
SUSPICIOUS
Creates files in the user directory
- dfsvc.exe (PID: 1548)
Reads Environment values
- dfsvc.exe (PID: 1548)
Reads Internet Cache Settings
- Mojo.setup.exe (PID: 944)
- dfsvc.exe (PID: 1548)
Executable content was dropped or overwritten
- dfsvc.exe (PID: 1548)
Creates a software uninstall entry
- dfsvc.exe (PID: 1548)
Reads internet explorer settings
- dfsvc.exe (PID: 1548)
INFO
Reads settings of System Certificates
- dfsvc.exe (PID: 1548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (54.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (34.8) |
| .exe | | | Win32 Executable (generic) (5.6) |
| .exe | | | Generic Win/DOS Executable (2.5) |
| .exe | | | DOS Executable Generic (2.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:10:07 03:29:19+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 321024 |
| InitializedDataSize: | 171520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e04d |
| OSVersion: | 5 |
| ImageVersion: | 10 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.0.21006.1 |
| ProductVersionNumber: | 10.0.21006.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileDescription: | Setup |
| FileVersion: | 10.0.21006.1 built by: B2Rel |
| InternalName: | setup.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | setup.exe |
| ProductName: | - |
| ProductVersion: | 10.0.21006.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Oct-2009 01:29:19 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | - |
| FileDescription: | Setup |
| FileVersion: | 10.0.21006.1 built by: B2Rel |
| InternalName: | setup.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | setup.exe |
| ProductName: | - |
| ProductVersion: | 10.0.21006.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 07-Oct-2009 01:29:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0004E528 | 0x0004E600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41817 |
.data | 0x00050000 | 0x000040AC | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.87108 |
.rsrc | 0x00055000 | 0x00023978 | 0x00023A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.51959 |
.reloc | 0x00079000 | 0x0000470C | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.12348 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05021 | 783 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.34688 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.08356 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 6.5129 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.72198 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.61913 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.11499 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.62416 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 6.05238 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 2.44951 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll (delay-loaded) |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
Secur32.dll |
USER32.dll |
WININET.dll |
msi.dll |
ole32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
_DecodePointerInternal@4 | 1 | 0x00019D13 |
_EncodePointerInternal@4 | 2 | 0x00019CF1 |
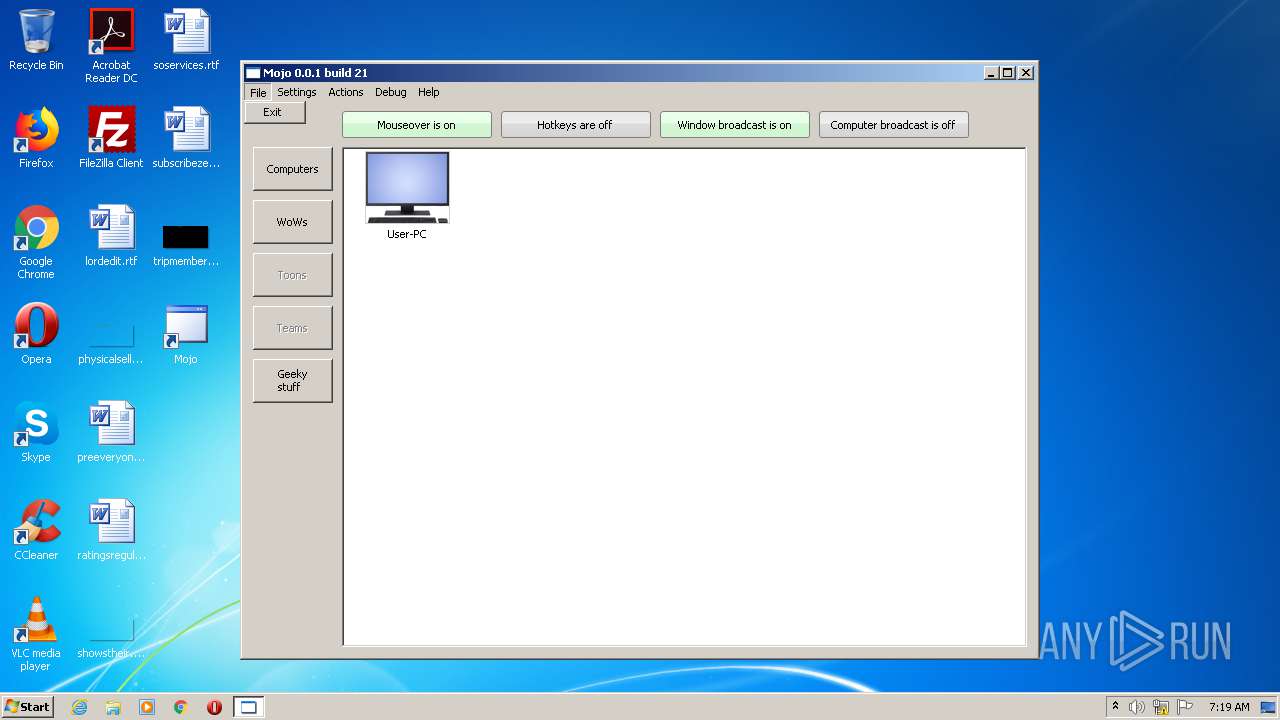
Total processes
42
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 944 | "C:\Users\admin\AppData\Local\Temp\Mojo.setup.exe" | C:\Users\admin\AppData\Local\Temp\Mojo.setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Exit code: 0 Version: 10.0.21006.1 built by: B2Rel Modules
| |||||||||||||||
| 1548 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe | Mojo.setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ClickOnce Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
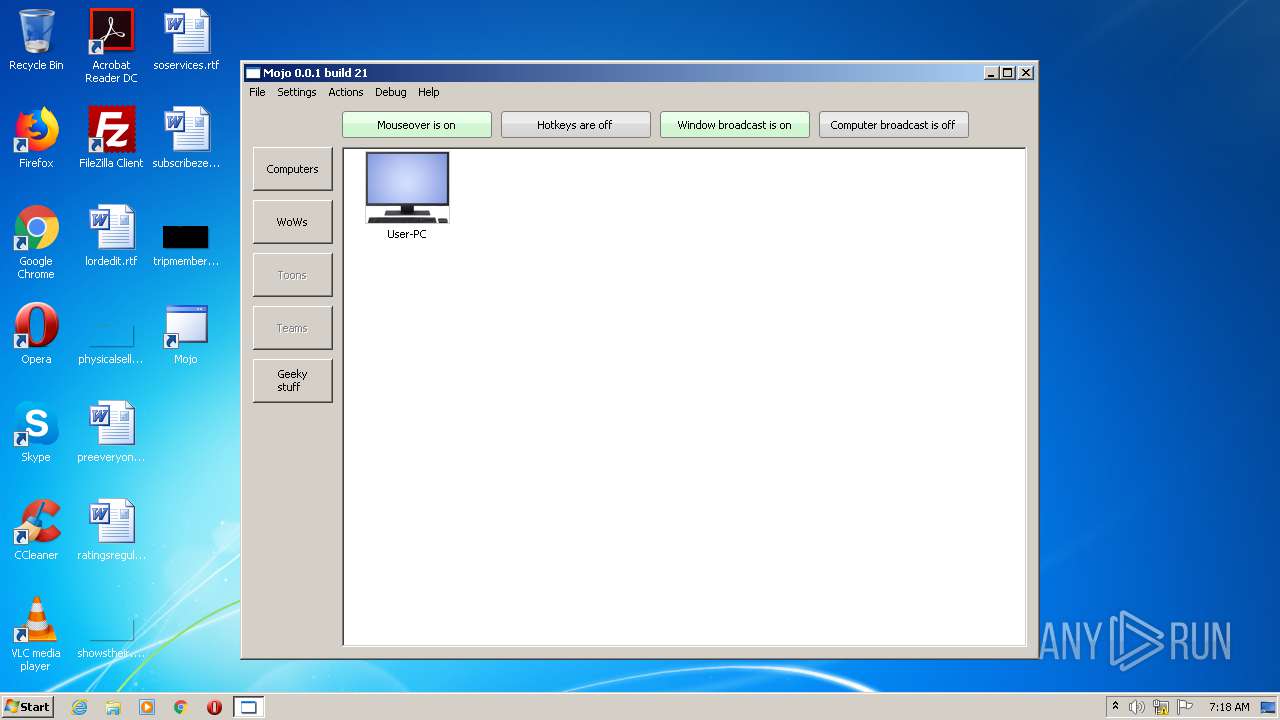
| 2212 | "C:\Users\admin\AppData\Local\Apps\2.0\TJLT5R2T.TM9\1ZMKQ76C.RRB\mojo..tion_c6b5d4e845ecfd15_0000.0000_cebb028b0c92818a\mojo.exe" | C:\Users\admin\AppData\Local\Apps\2.0\TJLT5R2T.TM9\1ZMKQ76C.RRB\mojo..tion_c6b5d4e845ecfd15_0000.0000_cebb028b0c92818a\mojo.exe | MojoInstaller.exe | ||||||||||||
User: admin Company: Mojoware -- see www.mojoware.org Integrity Level: HIGH Description: Mojo Exit code: 0 Version: 0.0.21 Modules
| |||||||||||||||
| 2236 | "C:\Users\admin\AppData\Local\Apps\2.0\TJLT5R2T.TM9\1ZMKQ76C.RRB\mojo..tion_c6b5d4e845ecfd15_0000.0000_cebb028b0c92818a\mojo.exe" | C:\Users\admin\AppData\Local\Apps\2.0\TJLT5R2T.TM9\1ZMKQ76C.RRB\mojo..tion_c6b5d4e845ecfd15_0000.0000_cebb028b0c92818a\mojo.exe | — | MojoInstaller.exe | |||||||||||
User: admin Company: Mojoware -- see www.mojoware.org Integrity Level: MEDIUM Description: Mojo Exit code: 3221226540 Version: 0.0.21 Modules
| |||||||||||||||
| 3000 | "C:\Users\admin\AppData\Local\Apps\2.0\TJLT5R2T.TM9\1ZMKQ76C.RRB\mojo..tion_c6b5d4e845ecfd15_0000.0000_cebb028b0c92818a\MojoInstaller.exe" | C:\Users\admin\AppData\Local\Apps\2.0\TJLT5R2T.TM9\1ZMKQ76C.RRB\mojo..tion_c6b5d4e845ecfd15_0000.0000_cebb028b0c92818a\MojoInstaller.exe | — | dfsvc.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: MojoInstaller Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
712
Read events
554
Write events
147
Delete events
11
Modification events
| (PID) Process: | (944) Mojo.setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (944) Mojo.setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (944) Mojo.setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (944) Mojo.setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (944) Mojo.setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (944) Mojo.setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (944) Mojo.setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (944) Mojo.setup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1548) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: V9EK0J4Q17HX4H1KAZVKQ0D8 | |||
| (PID) Process: | (1548) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete value | Name: | ComponentStore_RandomString |
Value: V9EK0J4Q17HX4H1KAZVKQ0D8 | |||
Executable files
8
Suspicious files
12
Text files
77
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 944 | Mojo.setup.exe | C:\Users\admin\AppData\Local\Temp\CabB57C.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | Mojo.setup.exe | C:\Users\admin\AppData\Local\Temp\TarB57D.tmp | — | |
MD5:— | SHA256:— | |||
| 1548 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\CabC058.tmp | — | |
MD5:— | SHA256:— | |||
| 1548 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\TarC069.tmp | — | |
MD5:— | SHA256:— | |||
| 1548 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\CabC079.tmp | — | |
MD5:— | SHA256:— | |||
| 1548 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\TarC07A.tmp | — | |
MD5:— | SHA256:— | |||
| 1548 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\CabC147.tmp | — | |
MD5:— | SHA256:— | |||
| 1548 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\TarC148.tmp | — | |
MD5:— | SHA256:— | |||
| 1548 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\CabC1A6.tmp | — | |
MD5:— | SHA256:— | |||
| 1548 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\TarC1A7.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
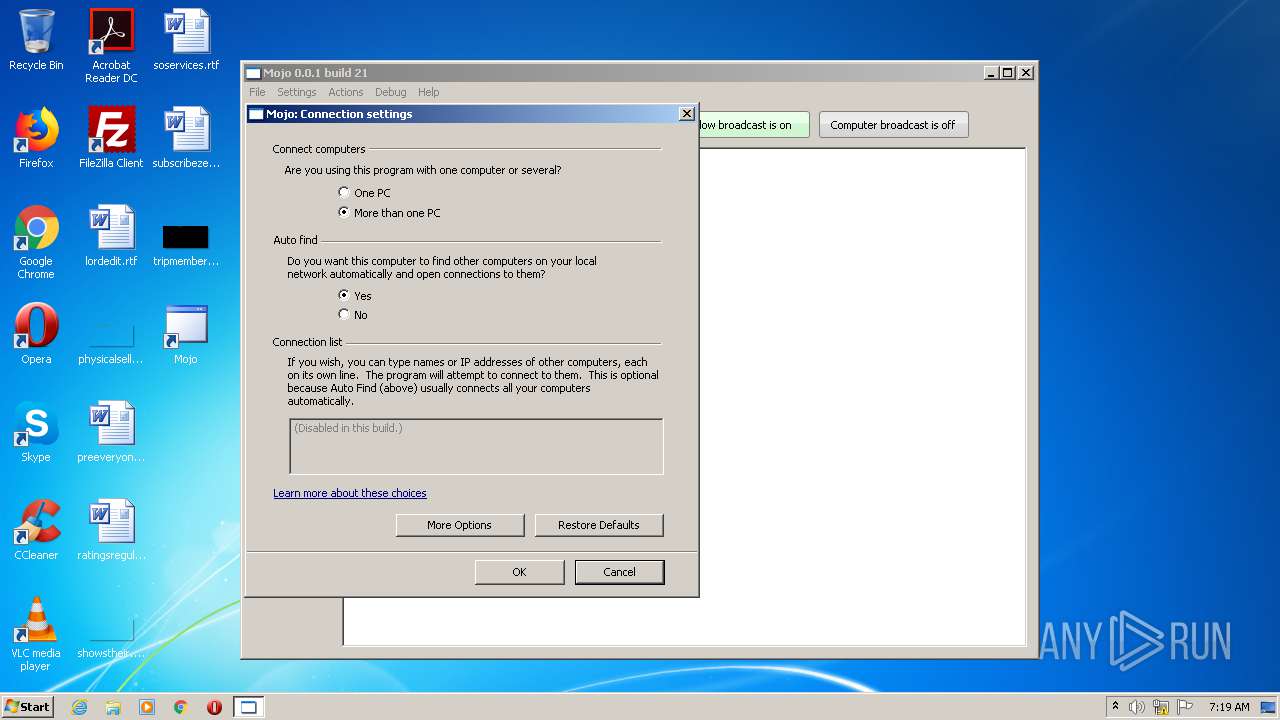
9
TCP/UDP connections
8
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
944 | Mojo.setup.exe | GET | 301 | 132.148.139.81:80 | http://mojoware.org/clickonce/MojoInstaller.application | US | html | 264 b | unknown |
944 | Mojo.setup.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | US | der | 471 b | whitelisted |
944 | Mojo.setup.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEQDwHUvue3yjezwFZqwFlyRY | US | der | 728 b | whitelisted |
1548 | dfsvc.exe | GET | 301 | 132.148.139.81:80 | http://mojoware.org/clickonce/MojoInstaller.application | US | html | 264 b | unknown |
1548 | dfsvc.exe | GET | 301 | 132.148.139.81:80 | http://mojoware.org/clickonce/MojoInstaller.application | US | html | 264 b | unknown |
1548 | dfsvc.exe | GET | 200 | 23.55.161.142:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
1548 | dfsvc.exe | GET | 304 | 23.55.161.142:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
1052 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1052 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEA7yTSbUNi7CXXtef0luXqk%3D | US | der | 279 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
944 | Mojo.setup.exe | 132.148.139.81:80 | mojoware.org | GoDaddy.com, LLC | US | unknown |
944 | Mojo.setup.exe | 132.148.139.81:443 | mojoware.org | GoDaddy.com, LLC | US | unknown |
944 | Mojo.setup.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
1548 | dfsvc.exe | 132.148.139.81:80 | mojoware.org | GoDaddy.com, LLC | US | unknown |
1548 | dfsvc.exe | 132.148.139.81:443 | mojoware.org | GoDaddy.com, LLC | US | unknown |
1548 | dfsvc.exe | 23.55.161.142:80 | www.download.windowsupdate.com | Akamai International B.V. | US | suspicious |
1052 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mojoware.org |
| unknown |
ocsp.comodoca.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
dns.msftncsi.com |
| shared |
Threats
Process | Message |
|---|---|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status Originated: -1073741772
*** Source File: d:\iso_whid\x86fre\base\isolation\win32\isoreg_direct.cpp, line 1127
|