| File name: | Setup.exe |
| Full analysis: | https://app.any.run/tasks/ade11d65-accb-42bb-9ab3-d06b37ed0221 |
| Verdict: | Malicious activity |
| Analysis date: | September 16, 2019, 14:45:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8683003A4AC9F1B5B5C80A0158908341 |
| SHA1: | 4993D0E0FA9619AF20BFA4785CE22461A97A99EA |
| SHA256: | F7D6E5C98B49BDFAE8DDBA4B9C9FCFB69D0853958ABE8431BB12E2F2F2216C29 |
| SSDEEP: | 24576:U8bu5SIipR/EGGqhFi6hHX+RSRhJ1MLtwJOszme6LsEwymyfP4g:/DIwRcD76d+G6tiOsme6LuWfPj |
MALICIOUS
Loads dropped or rewritten executable
- FPSetup.exe (PID: 3388)
- KakapoWebInstallerdyb.exe (PID: 3304)
- FirePlayer.exe (PID: 3844)
- WerFault.exe (PID: 4028)
- FirePlayer.exe (PID: 2424)
- WerFault.exe (PID: 1108)
Application was dropped or rewritten from another process
- helper.exe (PID: 2728)
- KakapoWebInstallerdyb.exe (PID: 3304)
- FPSetup.exe (PID: 3388)
SUSPICIOUS
Application launched itself
- Setup.exe (PID: 3556)
- cmd.exe (PID: 2864)
Modifies the open verb of a shell class
- FPSetup.exe (PID: 3388)
Creates files in the program directory
- Setup.exe (PID: 3288)
- FPSetup.exe (PID: 3388)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2720)
- cmd.exe (PID: 2472)
- Setup.exe (PID: 3288)
- cmd.exe (PID: 2864)
Executable content was dropped or overwritten
- Setup.exe (PID: 3288)
- KakapoWebInstallerdyb.exe (PID: 3304)
- FPSetup.exe (PID: 3388)
Starts CMD.EXE for self-deleting
- Setup.exe (PID: 3288)
- cmd.exe (PID: 2864)
Creates a software uninstall entry
- FPSetup.exe (PID: 3388)
Creates files in the user directory
- FirePlayer.exe (PID: 3844)
- KakapoWebInstallerdyb.exe (PID: 3304)
Creates files in the Windows directory
- FPSetup.exe (PID: 3388)
INFO
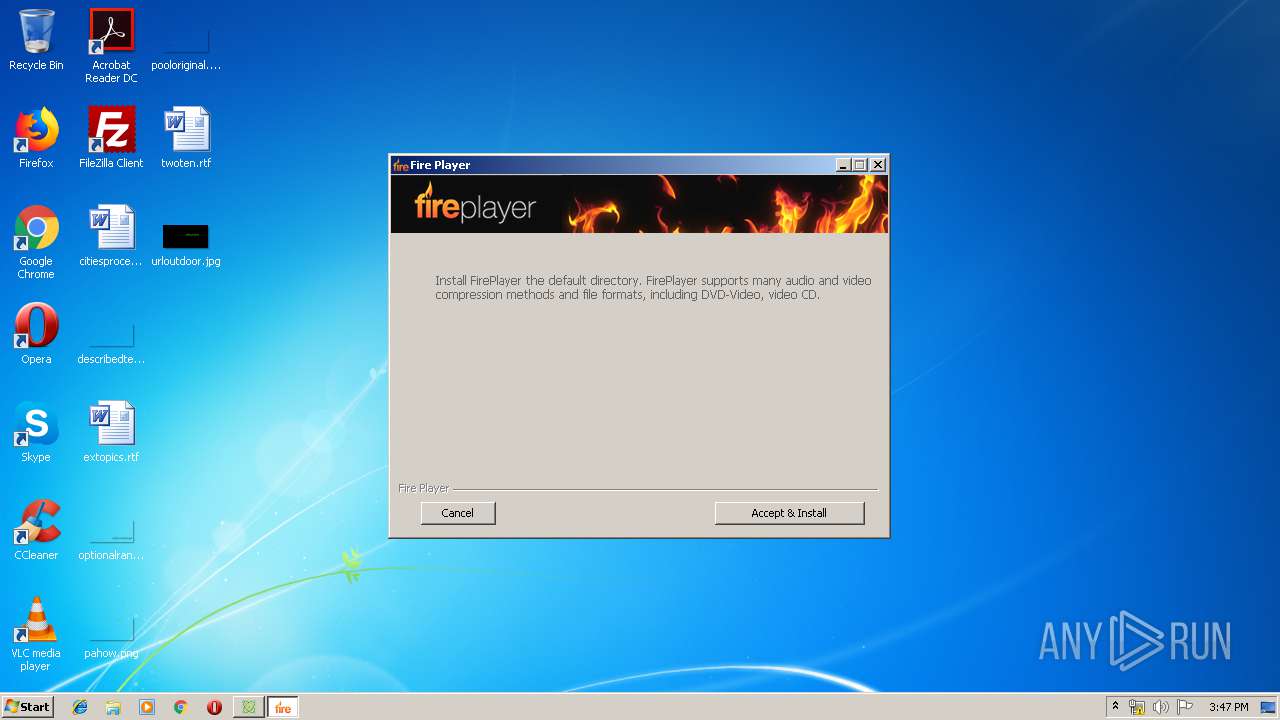
Manual execution by user
- FirePlayer.exe (PID: 3844)
- FirePlayer.exe (PID: 2424)
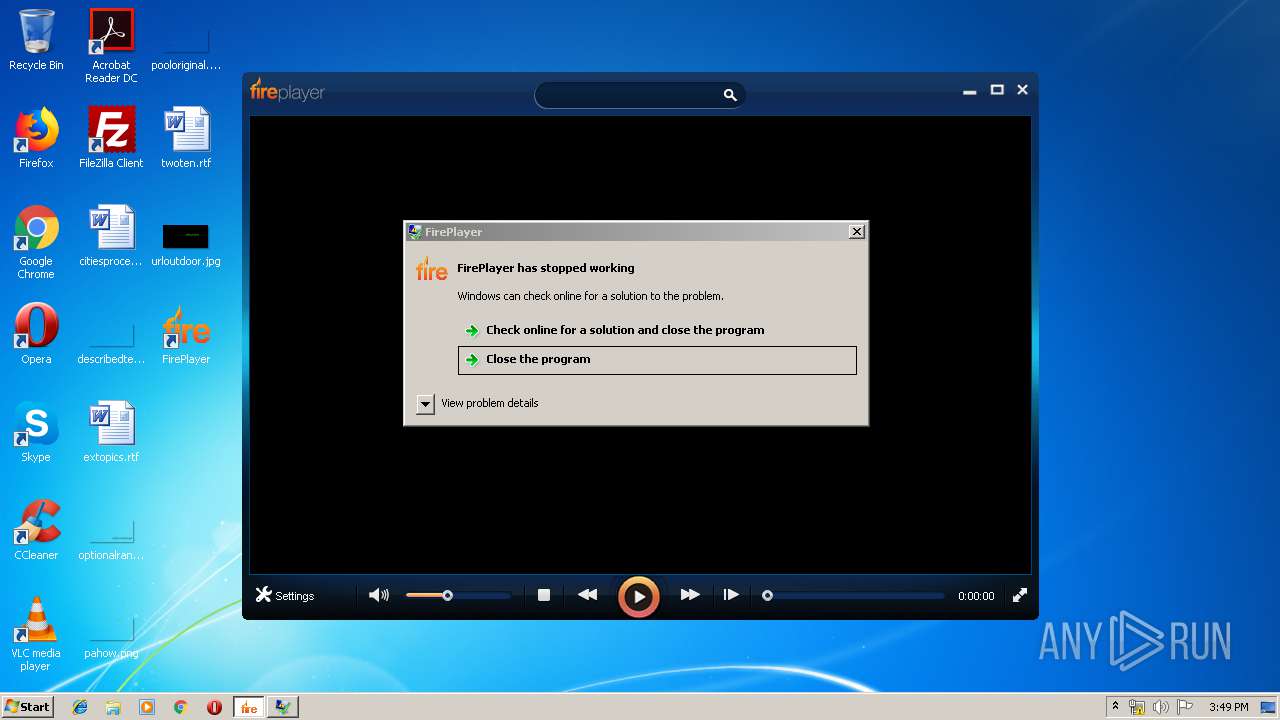
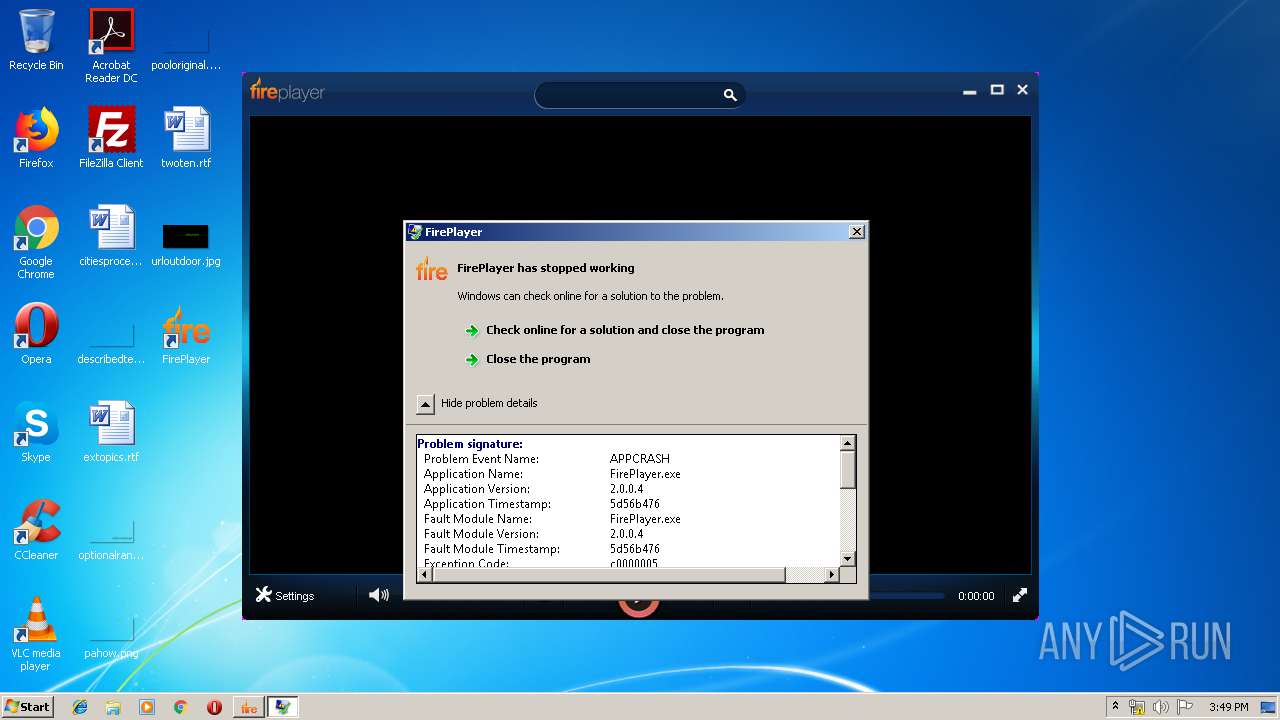
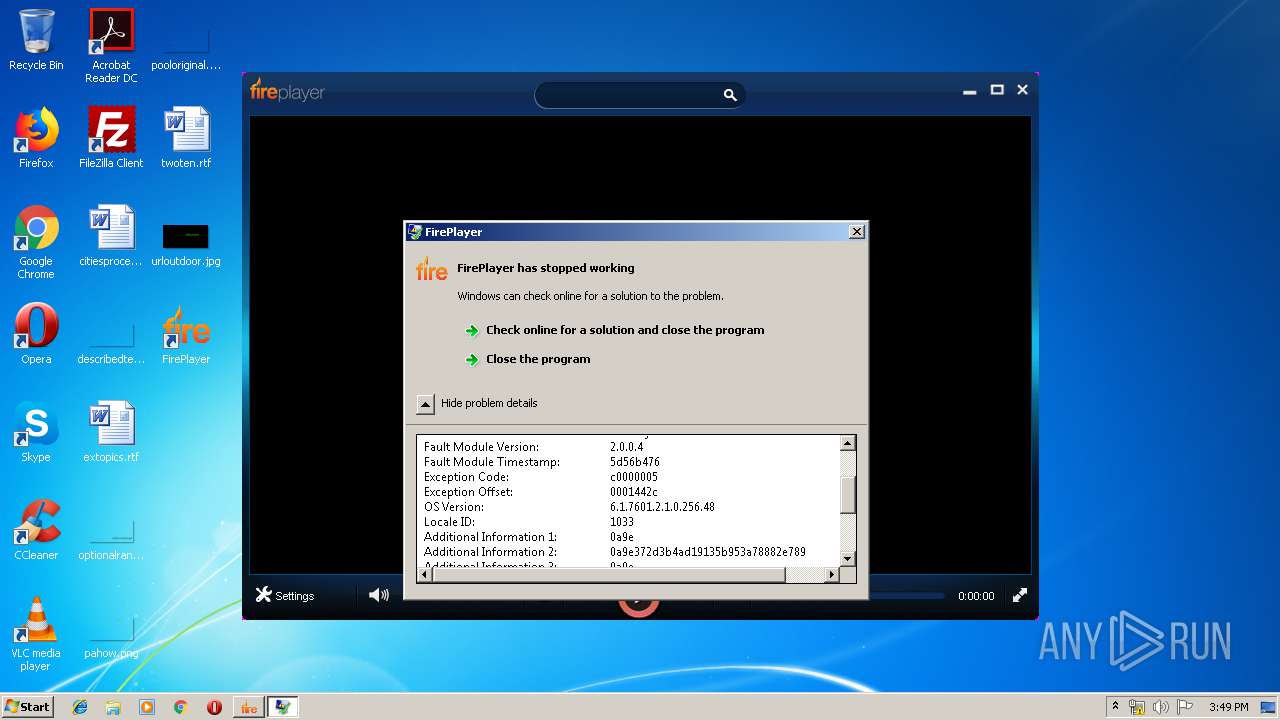
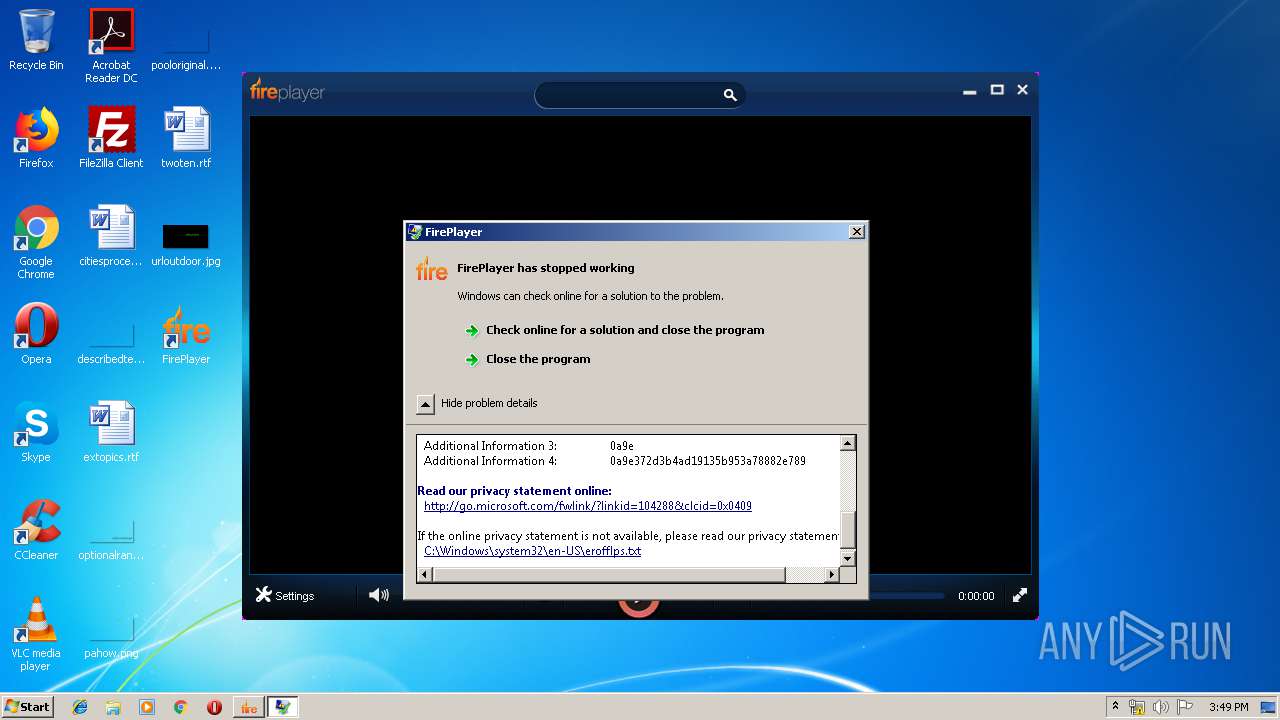
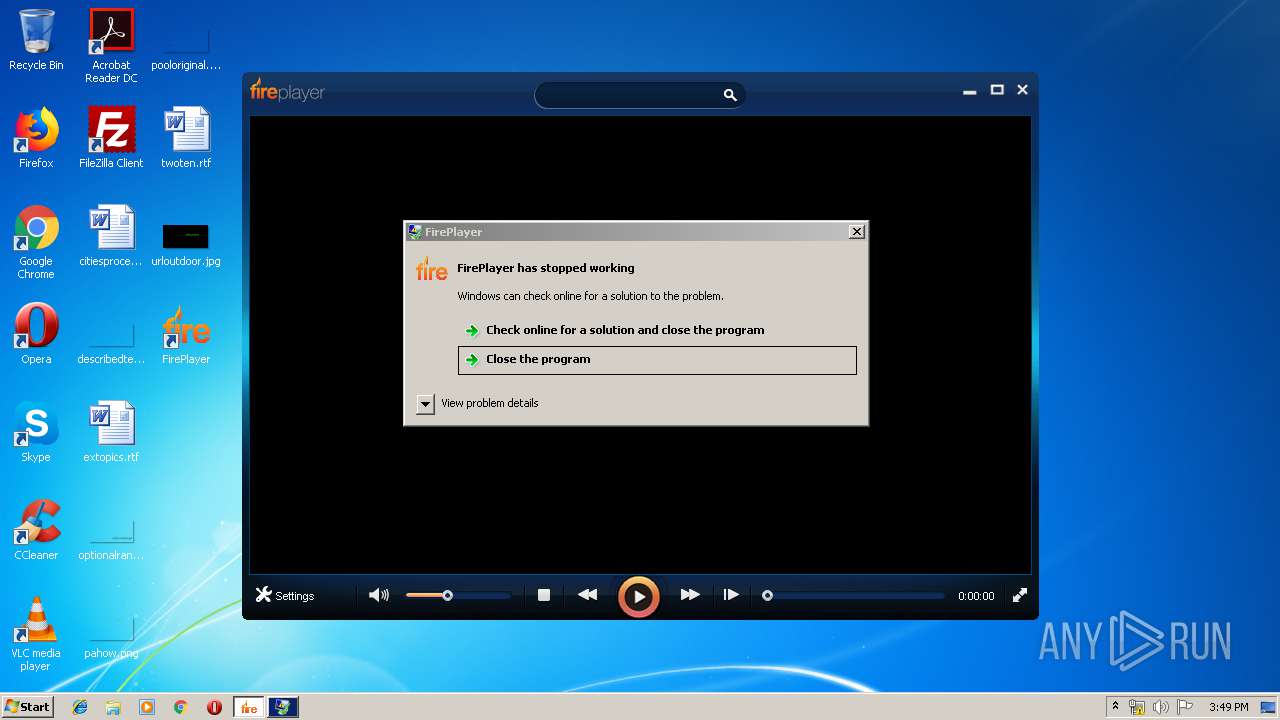
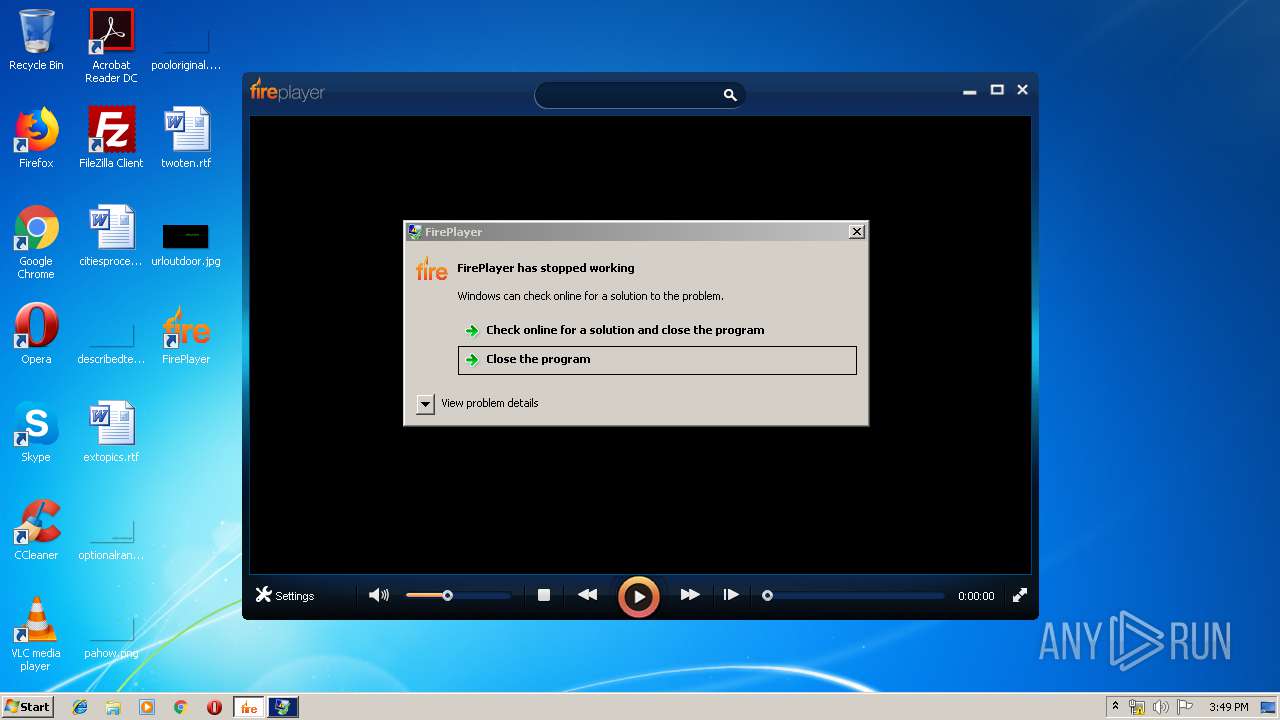
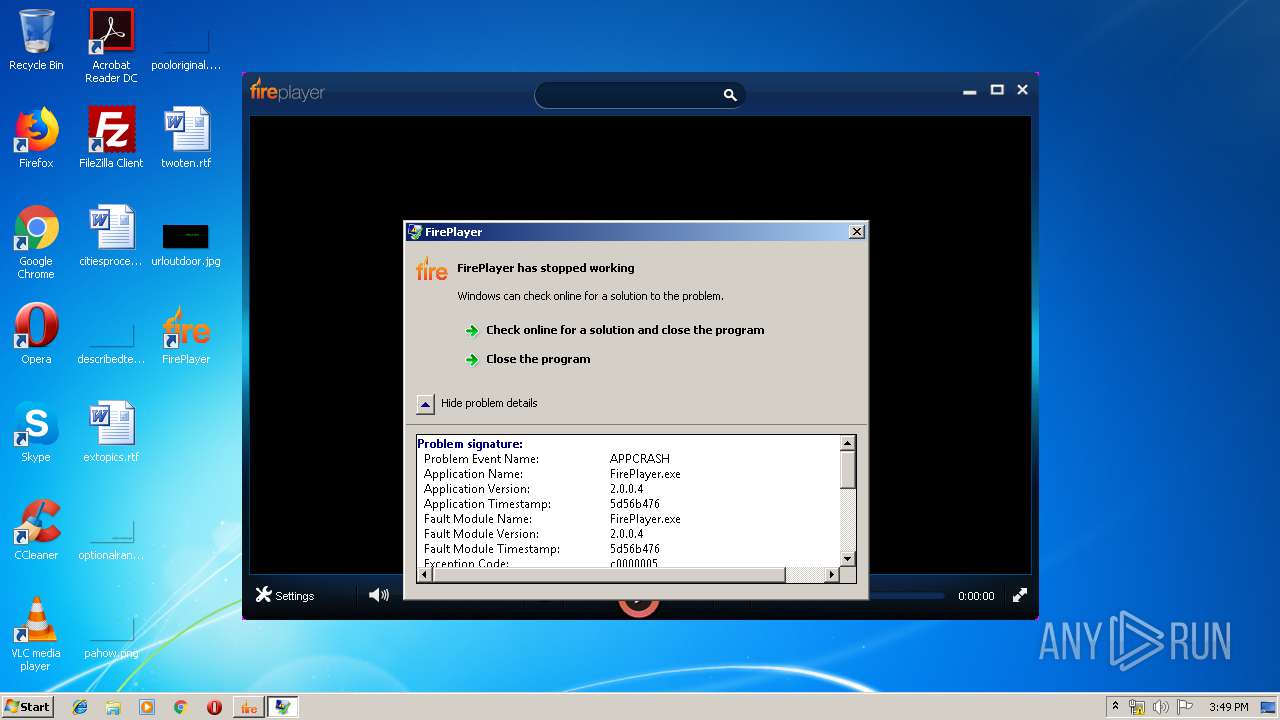
Application was crashed
- FirePlayer.exe (PID: 3844)
- FirePlayer.exe (PID: 2424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:09:13 09:51:18+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 400896 |
| InitializedDataSize: | 956416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x49f67 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.4.6 |
| ProductVersionNumber: | 1.4.4.6 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
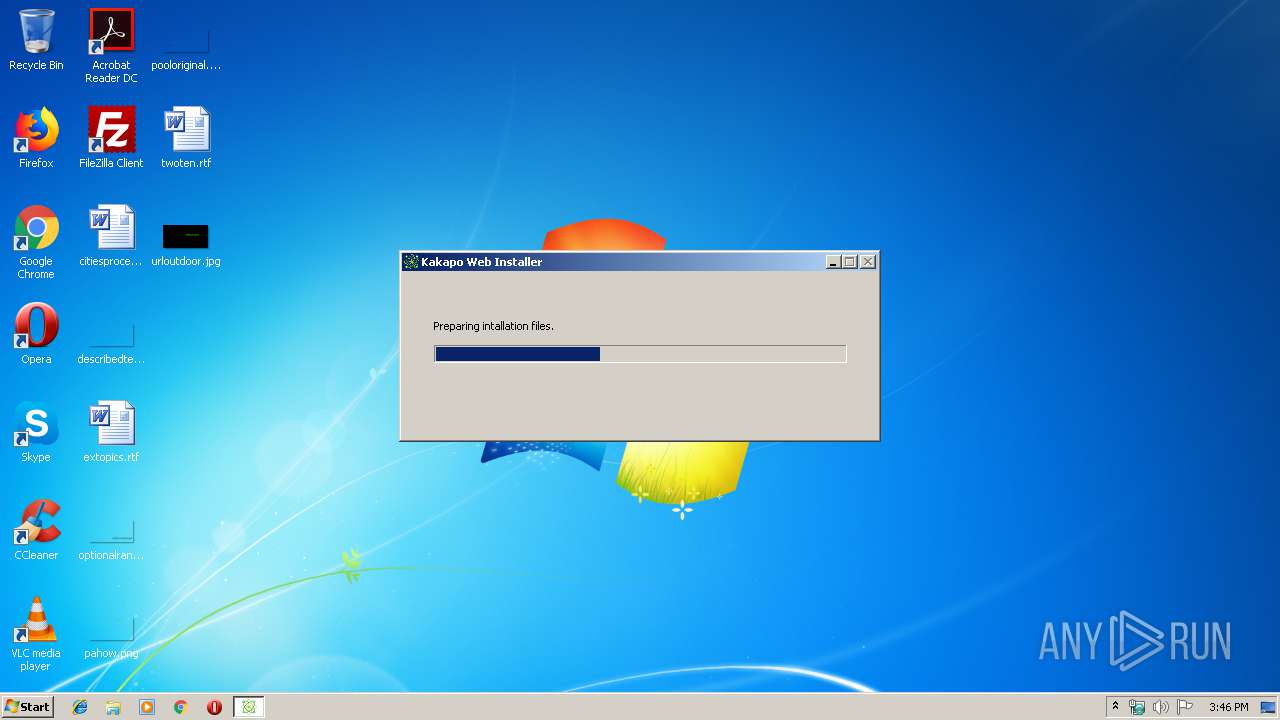
| FileDescription: | Kakapo Web Installer |
| FileVersion: | 1.4.4.6 |
| InternalName: | KakapoWebInstaller.exe |
| LegalCopyright: | Copyright 2019 |
| OriginalFileName: | KakapoWebInstaller.exe |
| ProductName: | KakapoWebInstaller |
| ProductVersion: | 1.4.4.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Sep-2019 07:51:18 |
| Detected languages: |
|
| FileDescription: | Kakapo Web Installer |
| FileVersion: | 1.4.4.6 |
| InternalName: | KakapoWebInstaller.exe |
| LegalCopyright: | Copyright 2019 |
| OriginalFilename: | KakapoWebInstaller.exe |
| ProductName: | KakapoWebInstaller |
| ProductVersion: | 1.4.4.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 13-Sep-2019 07:51:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000616B4 | 0x00061800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60131 |
.gfp4 | 0x00063000 | 0x0000042F | 0x00000600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.67387 |
.rdata | 0x00064000 | 0x00010A34 | 0x00010C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.50124 |
.data | 0x00075000 | 0x0000399C | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.80009 |
.rsrc | 0x00079000 | 0x000D1584 | 0x000D1600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.87343 |
.reloc | 0x0014B000 | 0x00005BD0 | 0x00005C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.6995 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.24655 | 881 | Latin 1 / Western European | English - United States | RT_MANIFEST |
107 | 1.98048 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
129 | 3.29147 | 256 | Latin 1 / Western European | English - United States | RT_DIALOG |
132 | 7.9524 | 787523 | Latin 1 / Western European | English - United States | JPG |
Imports
ADVAPI32.dll |
CRYPT32.dll |
KERNEL32.dll |
PSAPI.DLL |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WLDAP32.dll |
WS2_32.dll |
Total processes
57
Monitored processes
15
Malicious processes
11
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1108 | C:\Windows\system32\WerFault.exe -u -p 2424 -s 648 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2256 | cmd /d /c del /f /q "C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2424 | "C:\Program Files\FirePlayer\FirePlayer.exe" | C:\Program Files\FirePlayer\FirePlayer.exe | explorer.exe | ||||||||||||
User: admin Company: Prodigies Technology Co. Integrity Level: MEDIUM Description: FirePlayer Exit code: 3221225477 Version: 2.0.0.4 Modules
| |||||||||||||||
| 2472 | C:\Windows\system32\cmd.exe /d /c cmd /d /c cmd /d /c IF EXIST "C:\Program Files\KakapoWebqlbInstaller\KakapoWebInstallerdyb.exe" (start "" "C:\Program Files\KakapoWebqlbInstaller\KakapoWebInstallerdyb.exe" 44382953475016) | C:\Windows\system32\cmd.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2720 | cmd /d /c cmd /d /c IF EXIST "C:\Program Files\KakapoWebqlbInstaller\KakapoWebInstallerdyb.exe" (start "" "C:\Program Files\KakapoWebqlbInstaller\KakapoWebInstallerdyb.exe" 44382953475016) | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2728 | "C:\Program Files\FirePlayer\helper.exe" -fireplayer.exe | C:\Program Files\FirePlayer\helper.exe | — | FPSetup.exe | |||||||||||
User: admin Company: Prodigies Technology Co. Integrity Level: HIGH Description: FirePlayer Uninstall Component Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2864 | C:\Windows\system32\cmd.exe /d /c timeout 5 & cmd /d /c del /f /q "C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Windows\system32\cmd.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3080 | cmd /d /c IF EXIST "C:\Program Files\KakapoWebqlbInstaller\KakapoWebInstallerdyb.exe" (start "" "C:\Program Files\KakapoWebqlbInstaller\KakapoWebInstallerdyb.exe" 44382953475016) | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3288 | "C:\Users\admin\AppData\Local\Temp\Setup.exe" -uac | C:\Users\admin\AppData\Local\Temp\Setup.exe | Setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Kakapo Web Installer Exit code: 0 Version: 1.4.4.6 Modules
| |||||||||||||||
| 3304 | "C:\Program Files\KakapoWebqlbInstaller\KakapoWebInstallerdyb.exe" 44382953475016 | C:\Program Files\KakapoWebqlbInstaller\KakapoWebInstallerdyb.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: FirePlayer Exit code: 0 Version: 3.0.9.15 Modules
| |||||||||||||||
Total events
1 286
Read events
1 189
Write events
97
Delete events
0
Modification events
| (PID) Process: | (3556) Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3556) Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3304) KakapoWebInstallerdyb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\KakapoWebInstallerdyb_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3304) KakapoWebInstallerdyb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\KakapoWebInstallerdyb_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3304) KakapoWebInstallerdyb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\KakapoWebInstallerdyb_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3304) KakapoWebInstallerdyb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\KakapoWebInstallerdyb_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3304) KakapoWebInstallerdyb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\KakapoWebInstallerdyb_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3304) KakapoWebInstallerdyb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\KakapoWebInstallerdyb_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3304) KakapoWebInstallerdyb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\KakapoWebInstallerdyb_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3304) KakapoWebInstallerdyb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\KakapoWebInstallerdyb_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
21
Suspicious files
4
Text files
10
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
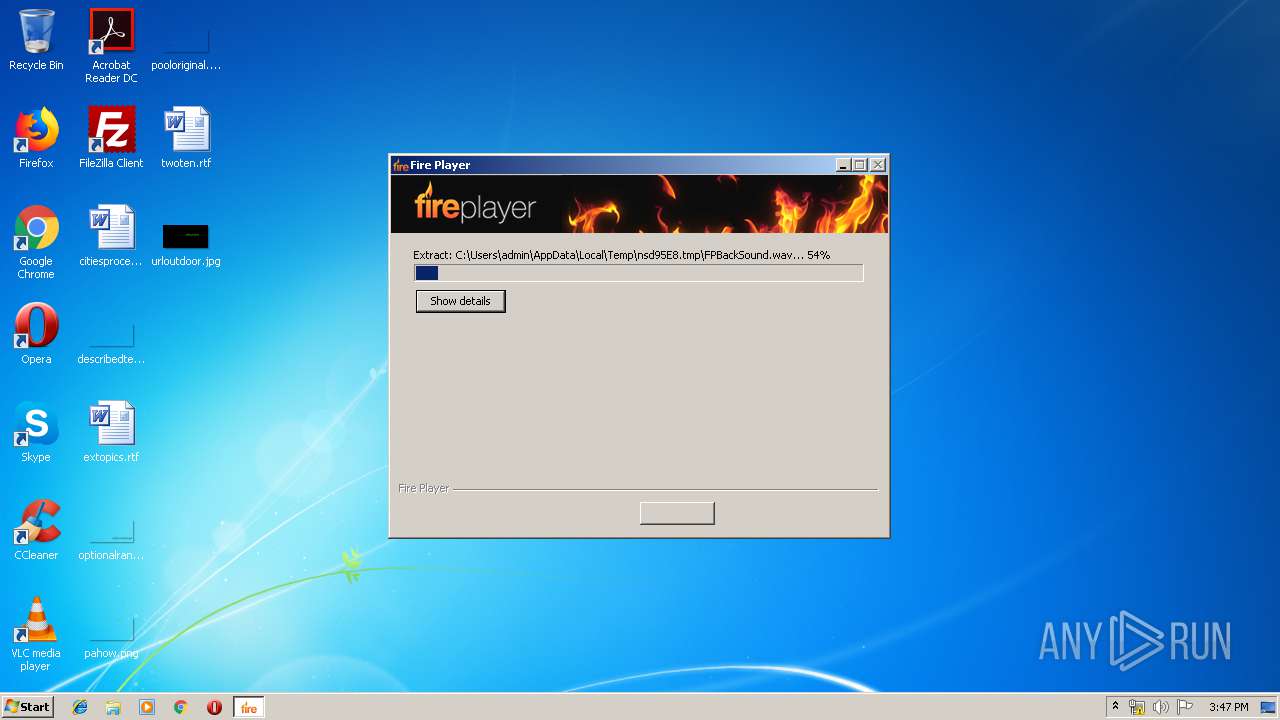
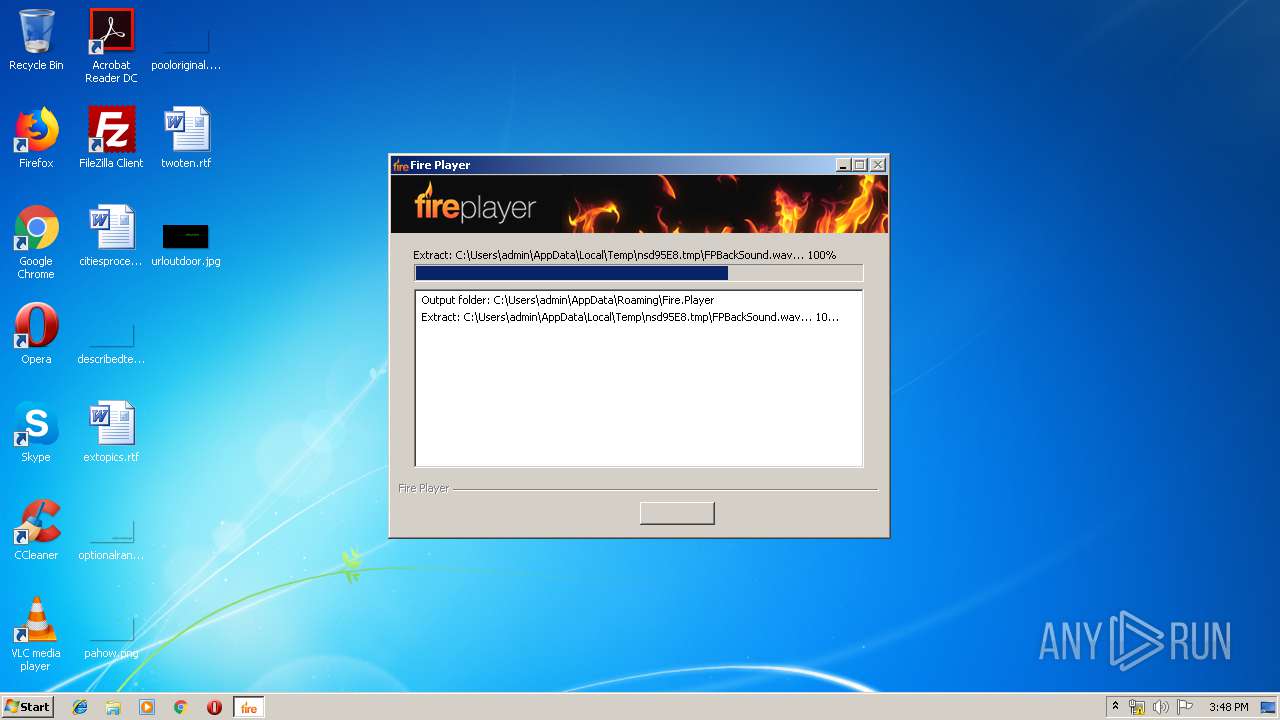
| 3304 | KakapoWebInstallerdyb.exe | C:\Users\admin\AppData\Local\Temp\nsd95E8.tmp\FPBackSound.wav | — | |
MD5:— | SHA256:— | |||
| 3304 | KakapoWebInstallerdyb.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\fireplayr_setup_component[1].exe | — | |
MD5:— | SHA256:— | |||
| 3304 | KakapoWebInstallerdyb.exe | C:\Users\admin\AppData\Roaming\Fire.Player\FPSetup.exe | — | |
MD5:— | SHA256:— | |||
| 3388 | FPSetup.exe | C:\Program Files\FirePlayer\FirePlayer.exe | — | |
MD5:— | SHA256:— | |||
| 3288 | Setup.exe | C:\Program Files\KakapoWebqlbInstaller\KakapoWebInstallerdyb.exe | executable | |
MD5:— | SHA256:— | |||
| 3304 | KakapoWebInstallerdyb.exe | C:\Users\admin\AppData\Local\Temp\nsd95E8.tmp\Logo.bmp | image | |
MD5:— | SHA256:— | |||
| 3304 | KakapoWebInstallerdyb.exe | C:\Users\admin\AppData\Local\Temp\nsd95E8.tmp\Banner.dll | executable | |
MD5:0116A50101C4107A138A588D1E46FCA5 | SHA256:AB80CF45070D936F0745F5E39B22E6E07BA90AA179B5EC4469EF6E2CB1B9EF6B | |||
| 3304 | KakapoWebInstallerdyb.exe | C:\Users\admin\AppData\Local\Temp\nsd95E8.tmp\System.dll | executable | |
MD5:56A321BD011112EC5D8A32B2F6FD3231 | SHA256:BB6DF93369B498EAA638B0BCDC4BB89F45E9B02CA12D28BCEDF4629EA7F5E0F1 | |||
| 3388 | FPSetup.exe | C:\Users\admin\AppData\Local\Temp\nsjA44A.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 3388 | FPSetup.exe | C:\Windows\Fonts\coolvetica_rg.ttf | ttf | |
MD5:4F9C46C1BDC961ED94EB04475BE1237C | SHA256:CE3E42173E236043D2D3EE8BF2EE5E68AF004A35177D0B83384ECC19C00D7496 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3556 | Setup.exe | 104.26.1.207:443 | softwaredeliverycdn.com | Cloudflare Inc | US | shared |
3556 | Setup.exe | 104.26.0.207:443 | softwaredeliverycdn.com | Cloudflare Inc | US | shared |
3288 | Setup.exe | 104.26.1.207:443 | softwaredeliverycdn.com | Cloudflare Inc | US | shared |
3304 | KakapoWebInstallerdyb.exe | 104.18.71.49:443 | installer.fireplayr.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
softwaredeliverycdn.com |
| malicious |
dns.msftncsi.com |
| shared |
installer.fireplayr.com |
| unknown |