| File name: | Amazon Costumer Service #110799.docx |
| Full analysis: | https://app.any.run/tasks/03eb718b-722a-42d5-8661-42465c1e4826 |
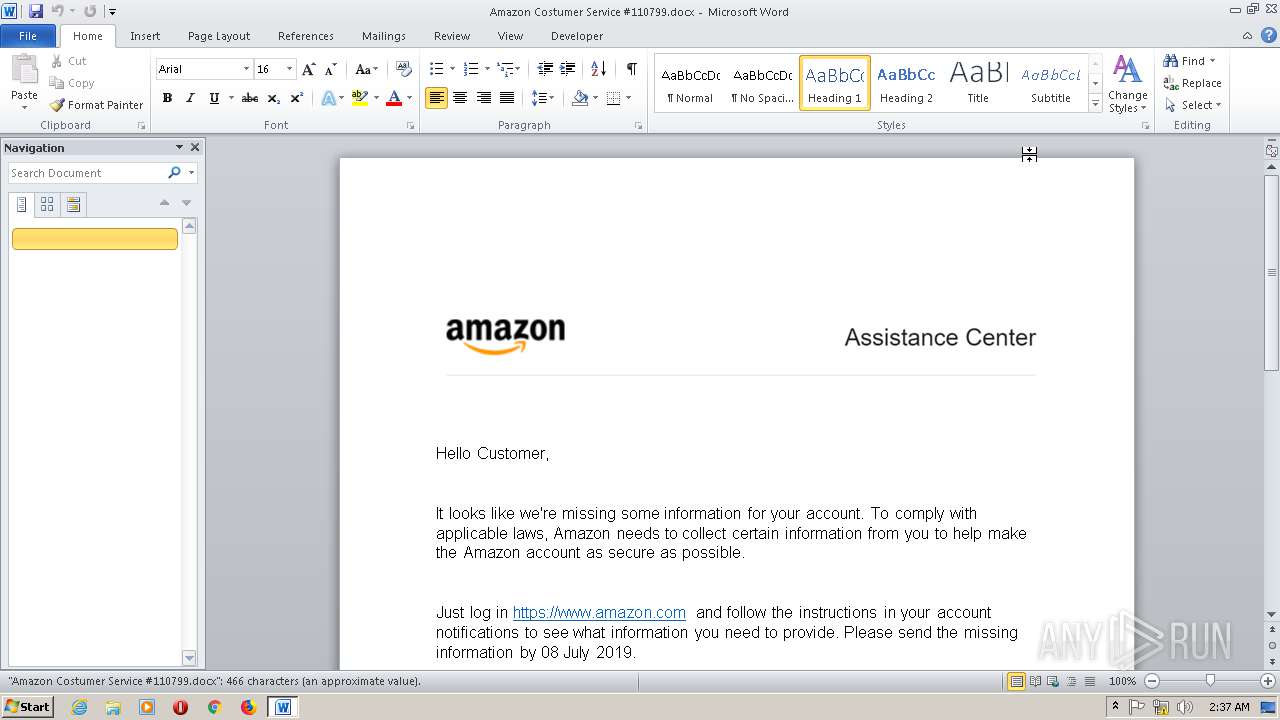
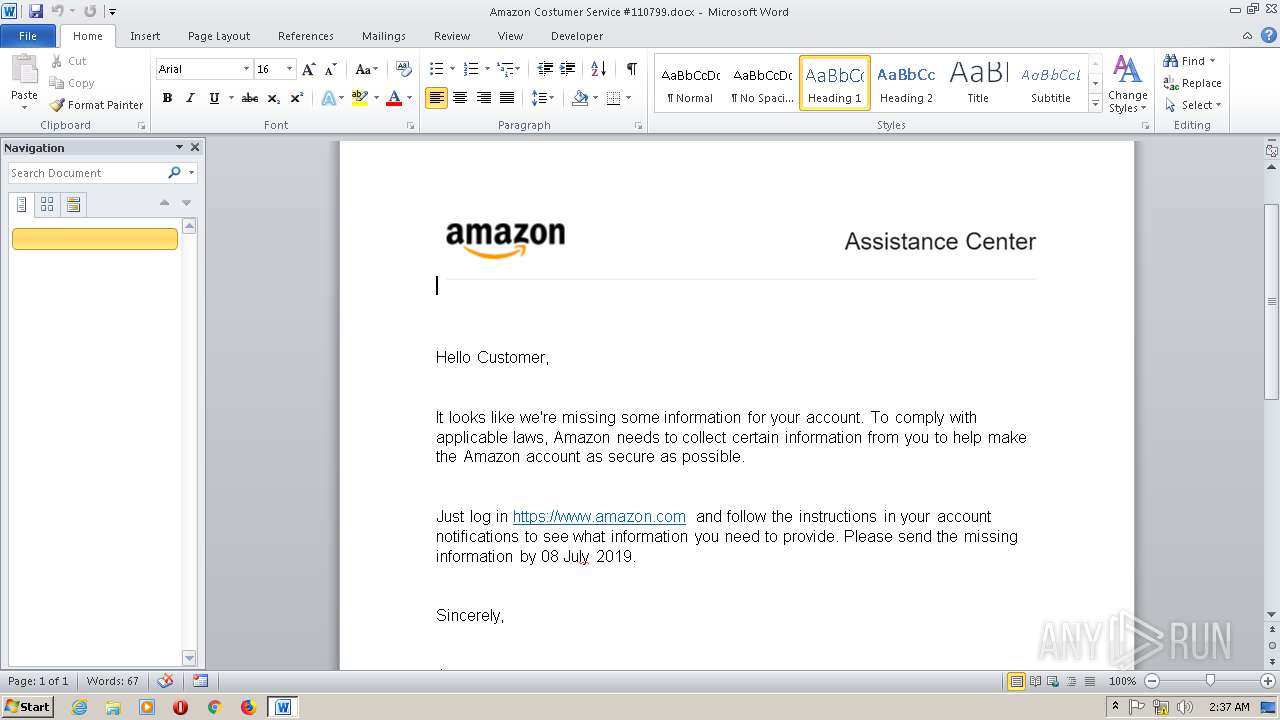
| Verdict: | Malicious activity |
| Analysis date: | July 09, 2019, 02:36:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | EA5BCBE140B93003111AE02FDC3A899A |
| SHA1: | F3843C9B541D632C8171D28FB5D859CCF5538438 |
| SHA256: | F7CA41C73A608996918AB6873789933EA9123AF0C3BB569D2F393EA2E779A83F |
| SSDEEP: | 1536:rAMoLwcU9aCzhR5LjD9Gq4ULwF2JgCB4A:rAJLCB7DTEF83B5 |
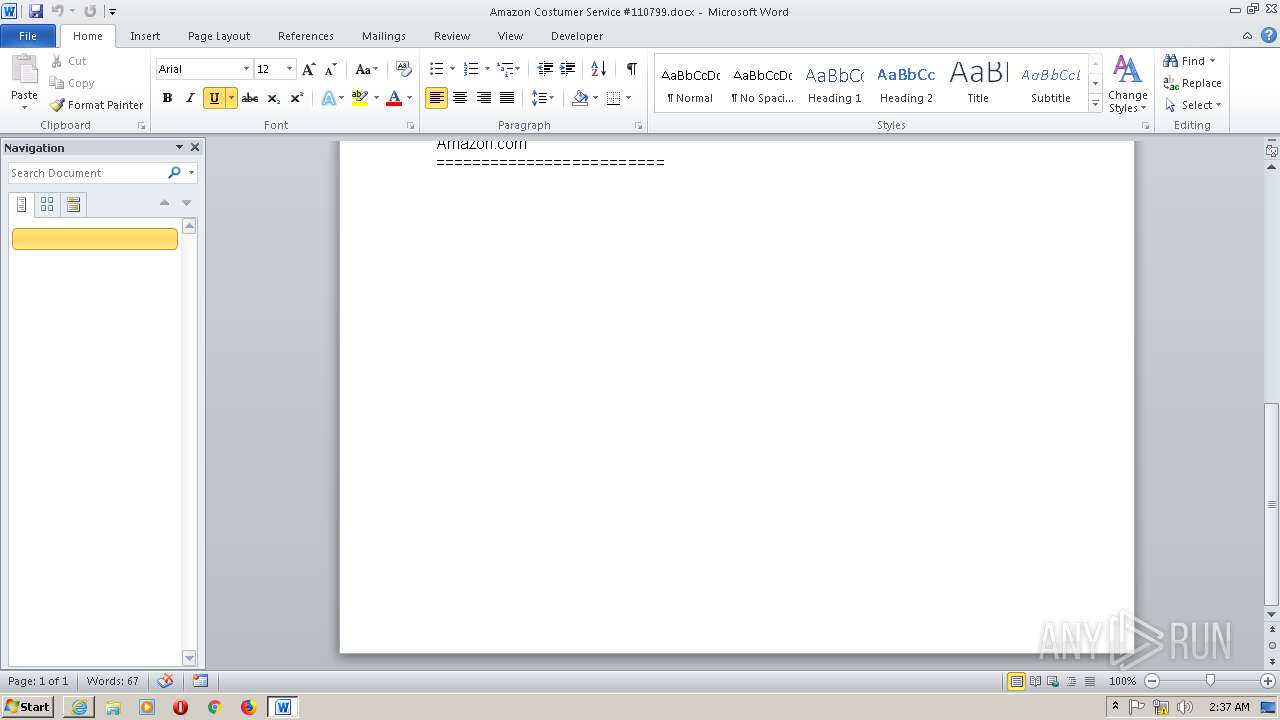
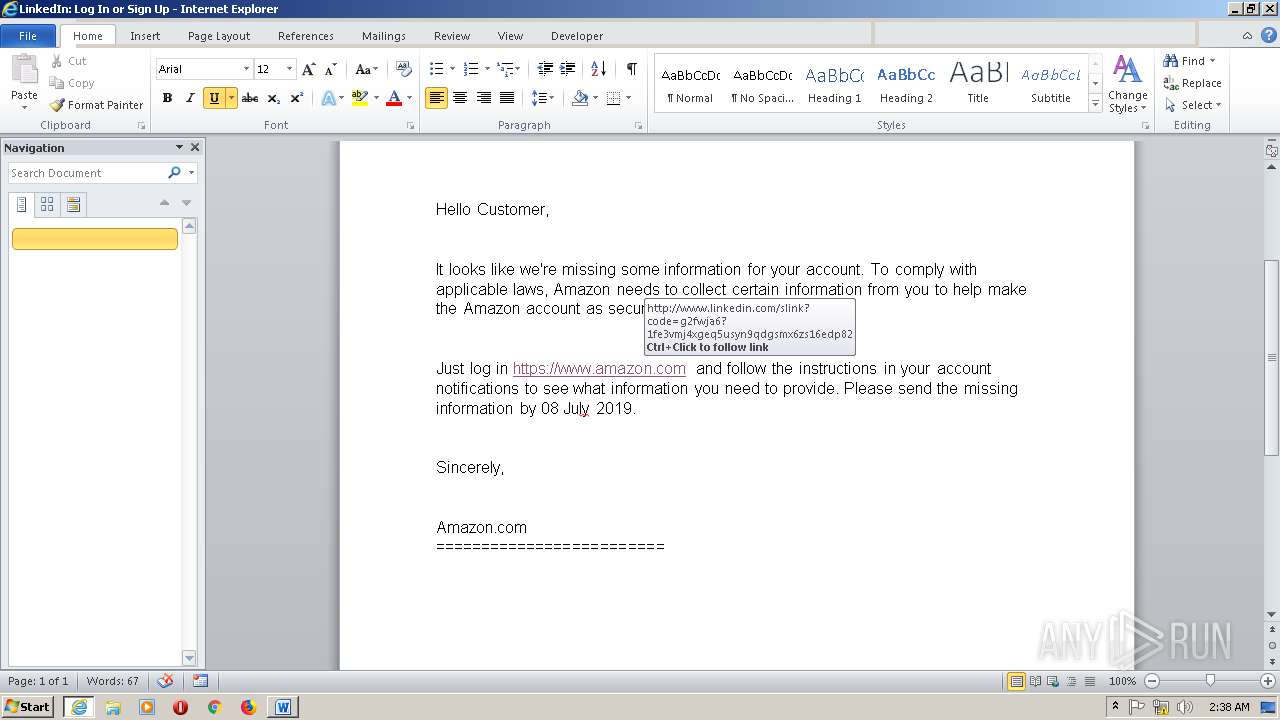
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2840)
SUSPICIOUS
Reads Internet Cache Settings
- WINWORD.EXE (PID: 2840)
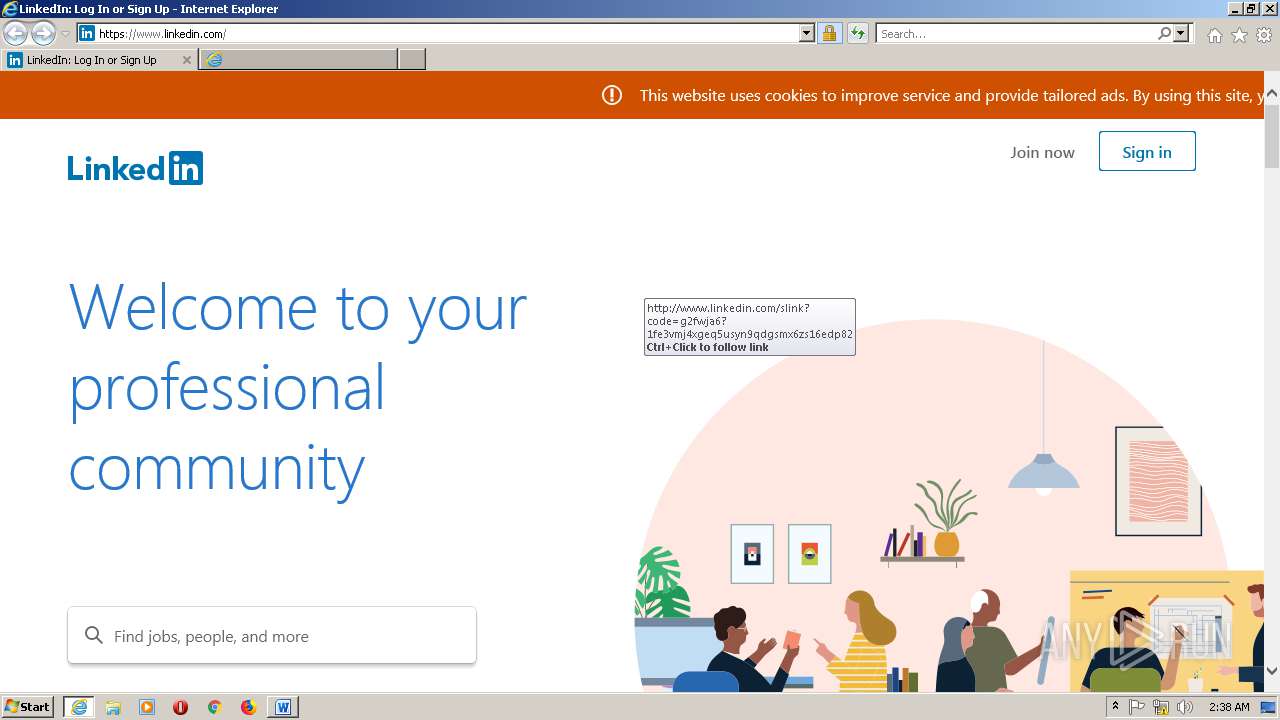
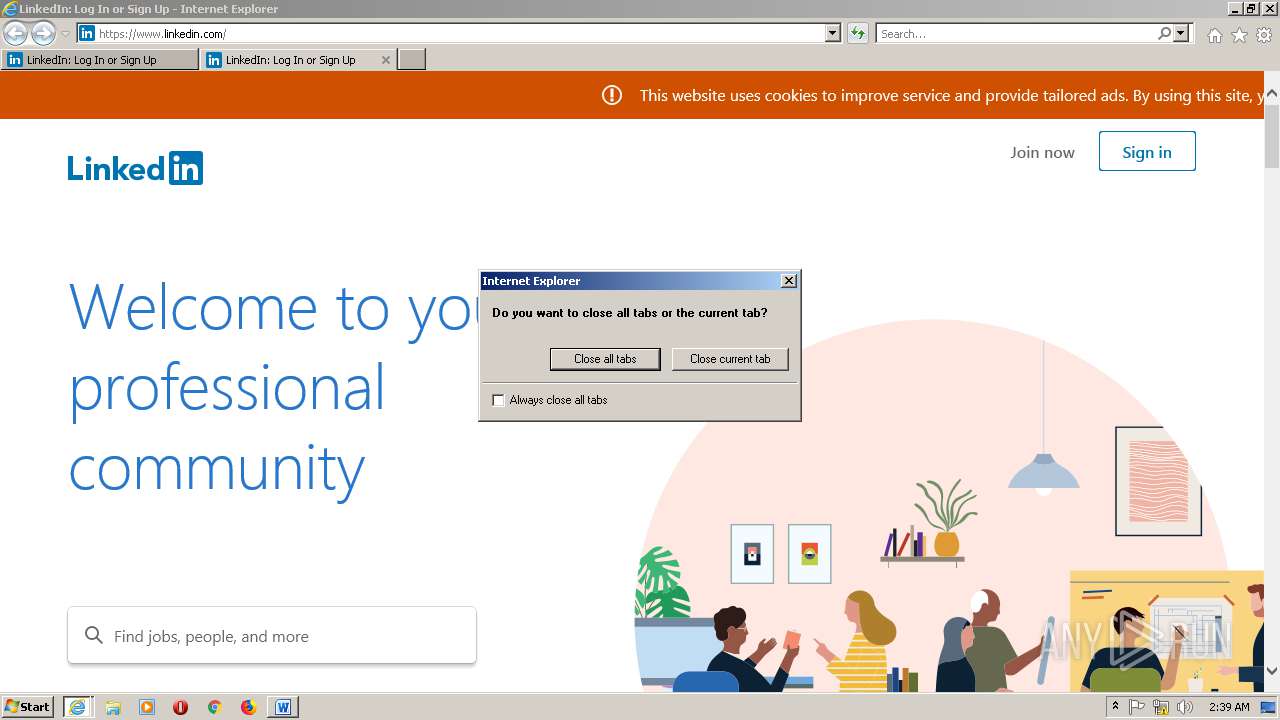
Starts Internet Explorer
- WINWORD.EXE (PID: 2840)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2840)
- IEXPLORE.EXE (PID: 2708)
- iexplore.exe (PID: 3004)
- IEXPLORE.EXE (PID: 2784)
Reads settings of System Certificates
- WINWORD.EXE (PID: 2840)
- IEXPLORE.EXE (PID: 2708)
- iexplore.exe (PID: 3004)
- IEXPLORE.EXE (PID: 2784)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 2840)
- iexplore.exe (PID: 3004)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2840)
Reads Internet Cache Settings
- iexplore.exe (PID: 3004)
Changes internet zones settings
- iexplore.exe (PID: 3004)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 2708)
- IEXPLORE.EXE (PID: 2784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x1dbbefa3 |
| ZipCompressedSize: | 357 |
| ZipUncompressedSize: | 1362 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | user |
| Description: | - |
XML
| Keywords: | - |
|---|---|
| LastModifiedBy: | Jaka Taruna |
| RevisionNumber: | 10 |
| CreateDate: | 2019:07:02 11:46:00Z |
| ModifyDate: | 2019:07:07 10:28:00Z |
| Template: | Costumer Service #8724365dot |
| TotalEditTime: | 12 minutes |
| Pages: | 1 |
| Words: | 84 |
| Characters: | 482 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 4 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 565 |
| SharedDoc: | No |
| HLinks: |
|
| HyperlinksChanged: | No |
| AppVersion: | 16 |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2708 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:3004 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2784 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:3004 CREDAT:1578250 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Amazon Costumer Service #110799.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.5123.5000 Modules
| |||||||||||||||
| 3004 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.linkedin.com/ | C:\Program Files\Internet Explorer\iexplore.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
2 361
Read events
1 827
Write events
526
Delete events
8
Modification events
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | i/> |
Value: 692F3E00180B0000010000000000000000000000 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1323892778 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1323892862 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1323892863 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 180B000060E2412EFF35D50100000000 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | #5> |
Value: 23353E00180B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | #5> |
Value: 23353E00180B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
16
Text files
53
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9369.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\I0M9A1NP.txt | — | |
MD5:— | SHA256:— | |||
| 2708 | IEXPLORE.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5M8YURQS.txt | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\Desktop\~$azon Costumer Service #110799.docx | pgc | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\SM2GLP5J.txt | text | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\EKGBQM0V.txt | text | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Amazon Costumer Service #110799.docx.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2708 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UJFUX3OG\IB88SRMI.htm | html | |
MD5:— | SHA256:— | |||
| 2708 | IEXPLORE.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\IQ2UV6GN.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
79
TCP/UDP connections
79
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
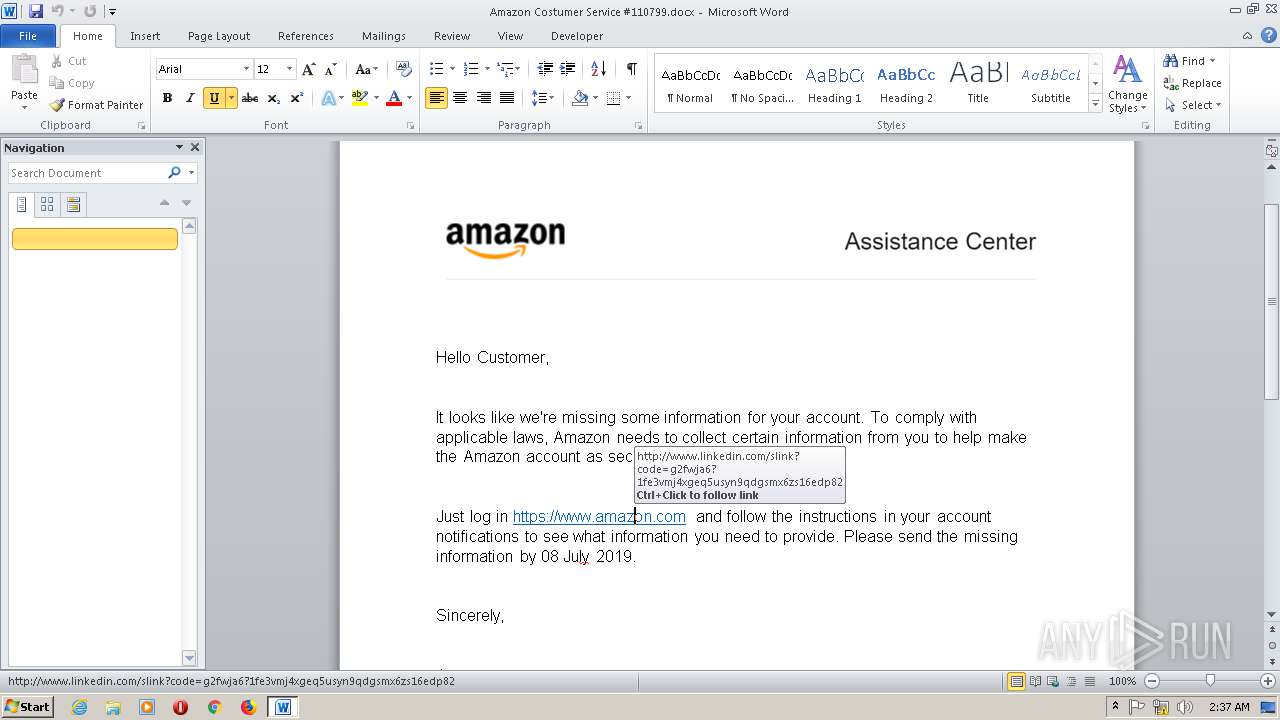
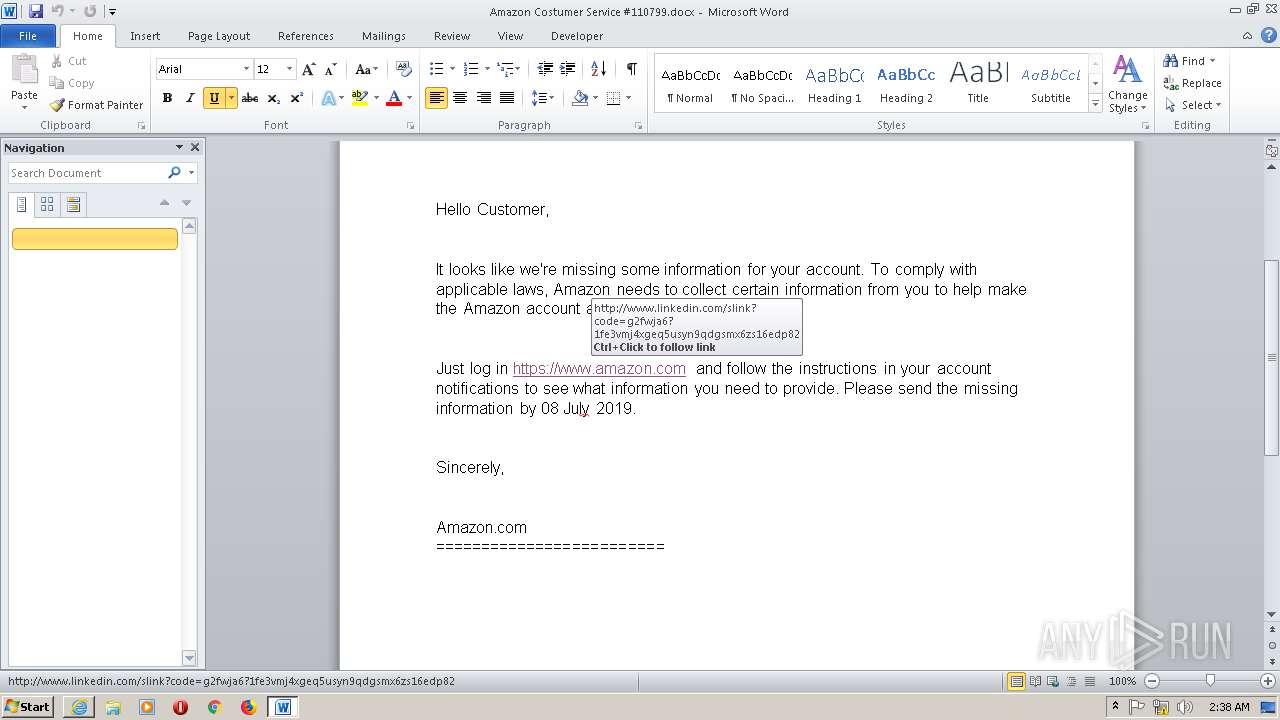
2840 | WINWORD.EXE | GET | 301 | 185.63.144.1:80 | http://www.linkedin.com/slink?code=g2fWJA6?1FE3VMJ4XGEq5UsYN9qDgSmX6zS16edP82 | IE | — | — | whitelisted |
2840 | WINWORD.EXE | GET | 301 | 185.63.144.1:443 | https://www.linkedin.com/slink?code=g2fWJA6?1FE3VMJ4XGEq5UsYN9qDgSmX6zS16edP82 | IE | — | — | whitelisted |
2708 | IEXPLORE.EXE | HEAD | 200 | 2.18.234.132:443 | https://static.licdn.com/sc/h/crs2l0612uc5z8wksw2hfq2ke | unknown | — | — | whitelisted |
2708 | IEXPLORE.EXE | GET | 200 | 2.18.234.132:443 | https://static.licdn.com/sc/h/1hbr6t0oqhf2avswaaruivxtl | unknown | image | 98.8 Kb | whitelisted |
2708 | IEXPLORE.EXE | GET | 200 | 185.63.144.1:443 | https://www.linkedin.com/ | IE | html | 66.4 Kb | whitelisted |
2708 | IEXPLORE.EXE | GET | 200 | 2.18.234.132:443 | https://static.licdn.com/sc/h/d80ave0ov78t6vlt7maud1pwd | unknown | image | 49.9 Kb | whitelisted |
2708 | IEXPLORE.EXE | GET | 200 | 2.18.234.132:443 | https://static.licdn.com/sc/h/crs2l0612uc5z8wksw2hfq2ke | unknown | text | 241 Kb | whitelisted |
2840 | WINWORD.EXE | GET | 200 | 185.63.144.1:443 | https://www.linkedin.com/ | IE | html | 69.3 Kb | whitelisted |
2708 | IEXPLORE.EXE | GET | 200 | 2.18.234.132:443 | https://static.licdn.com/sc/h/8nm52m62nktkly1ph06vzs8my | unknown | text | 115 Kb | whitelisted |
2708 | IEXPLORE.EXE | GET | 200 | 2.18.234.132:443 | https://static.licdn.com/sc/h/3odehi5uaegaqbi445ha14tnq | unknown | text | 62.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2840 | WINWORD.EXE | 185.63.144.1:80 | www.linkedin.com | LinkedIn Corporation | IE | unknown |
2840 | WINWORD.EXE | 185.63.144.1:443 | www.linkedin.com | LinkedIn Corporation | IE | unknown |
2708 | IEXPLORE.EXE | 185.63.144.1:443 | www.linkedin.com | LinkedIn Corporation | IE | unknown |
2708 | IEXPLORE.EXE | 2.18.234.132:443 | static.licdn.com | Akamai International B.V. | — | whitelisted |
2708 | IEXPLORE.EXE | 23.38.59.114:443 | platform.linkedin.com | Akamai International B.V. | NL | whitelisted |
2708 | IEXPLORE.EXE | 172.217.16.174:443 | www.youtube.com | Google Inc. | US | whitelisted |
2708 | IEXPLORE.EXE | 172.217.16.142:443 | www.youtube.com | Google Inc. | US | whitelisted |
2708 | IEXPLORE.EXE | 74.125.140.157:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3004 | iexplore.exe | 2.18.234.132:443 | static.licdn.com | Akamai International B.V. | — | whitelisted |
2708 | IEXPLORE.EXE | 172.217.16.194:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.linkedin.com |
| whitelisted |
static.licdn.com |
| whitelisted |
platform.linkedin.com |
| whitelisted |
www.youtube.com |
| whitelisted |
sb.scorecardresearch.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |