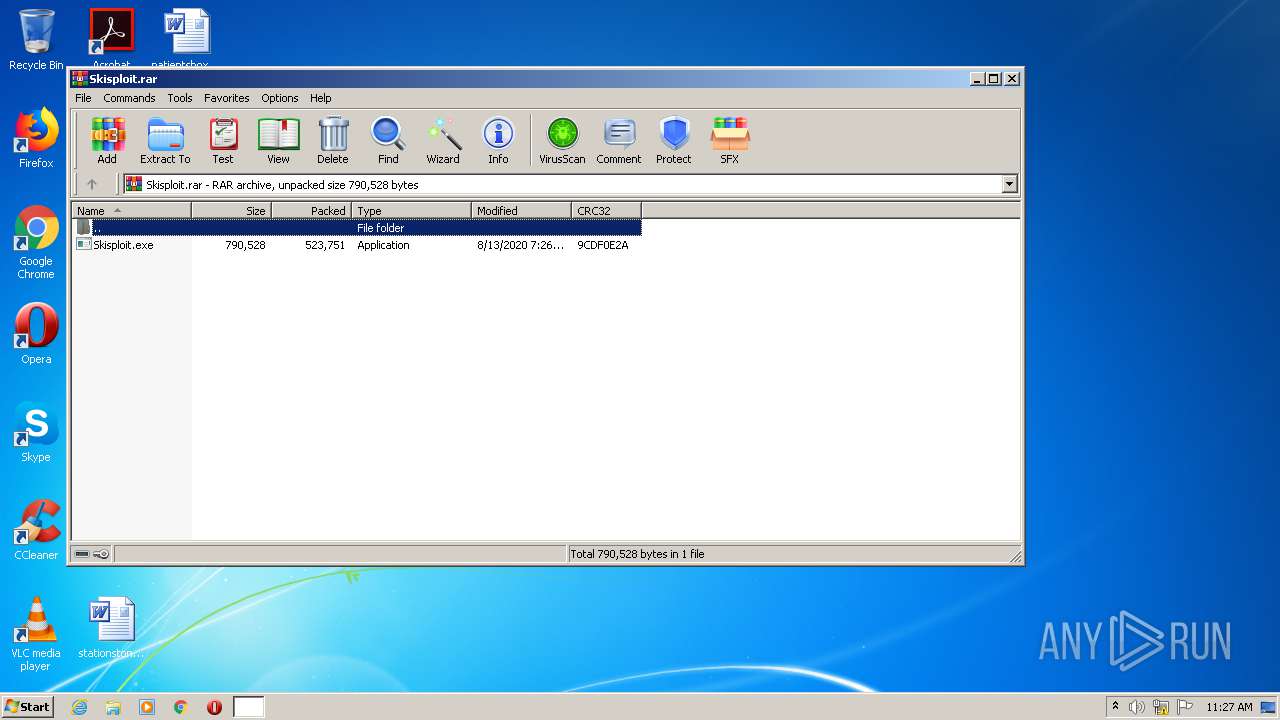
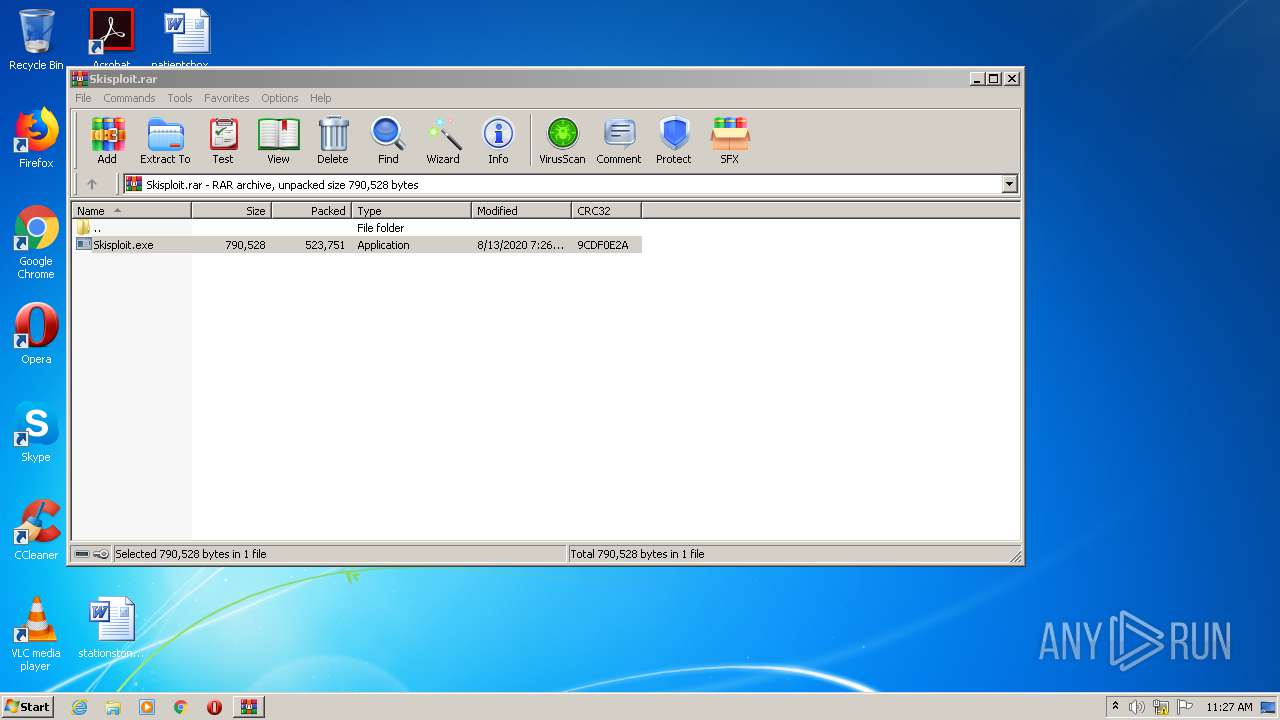
| File name: | Skisploit.rar |
| Full analysis: | https://app.any.run/tasks/7c88cb5d-78fd-4e1e-b625-506a47ac818b |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 11:26:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 5CFD7593357656A86C36842CBECDA744 |
| SHA1: | 8577064920CFCBA5EF0D1606BE557307B2181B55 |
| SHA256: | F7BBA465958CE016E38201B921EA8B0D38E81B9D08C787944577DD27890DA2DC |
| SSDEEP: | 12288:DOS4vFsWo1qV/tM5rzXdw+KyRkvwv5aVp939orzLAhpKTCIgdv+p:v4SaCrztoyyP3urPAq21dWp |
MALICIOUS
Application was dropped or rewritten from another process
- Skisploit.exe (PID: 1800)
SUSPICIOUS
Reads Environment values
- Skisploit.exe (PID: 1800)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1952)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1952)
Drops a file with too old compile date
- WinRAR.exe (PID: 1952)
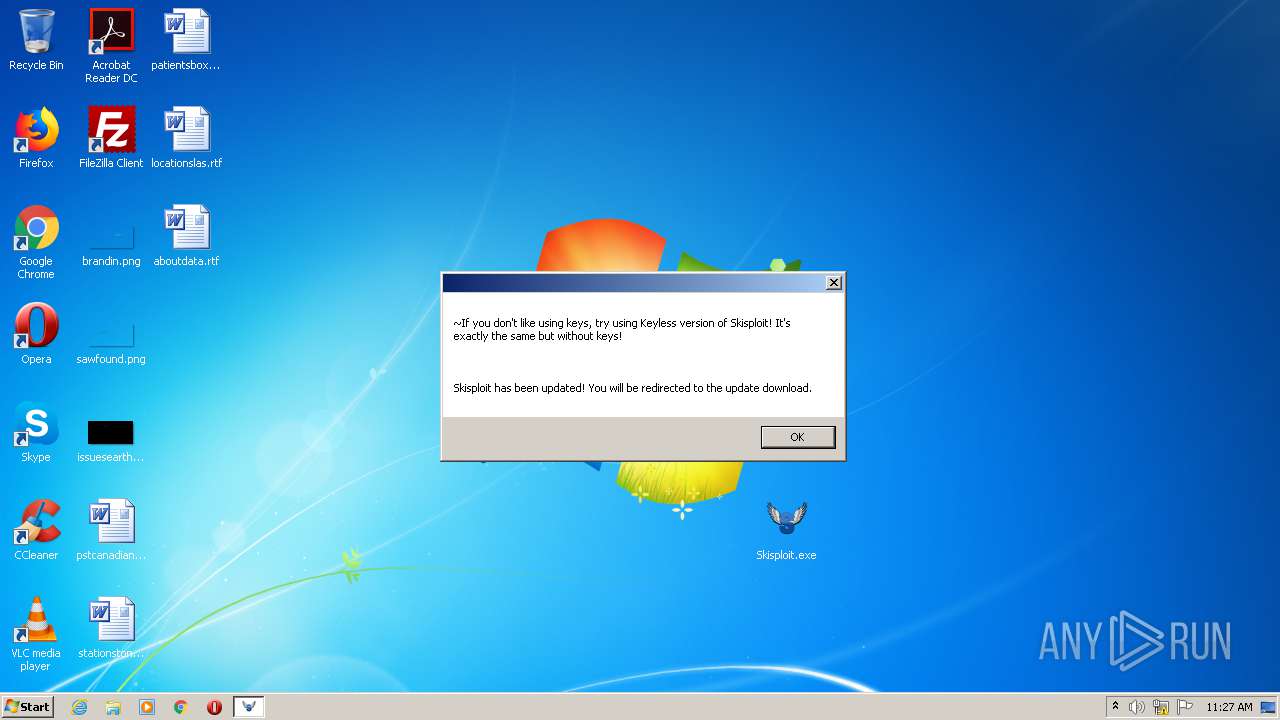
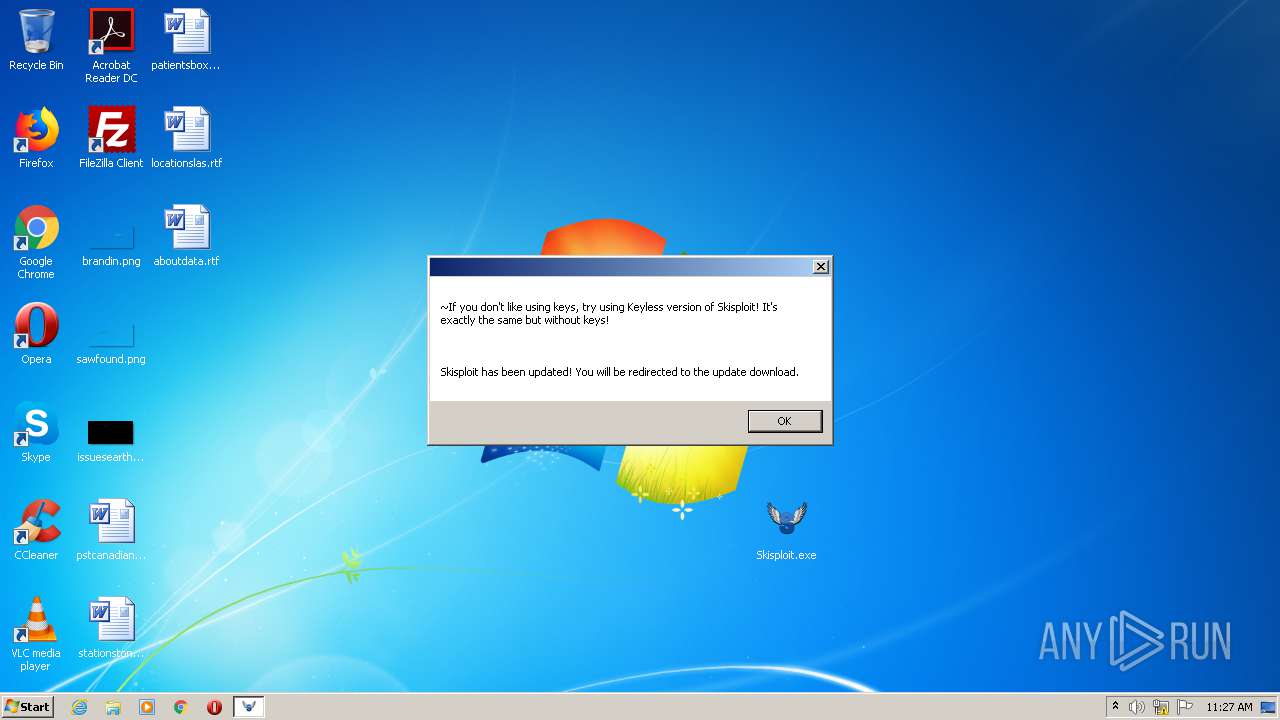
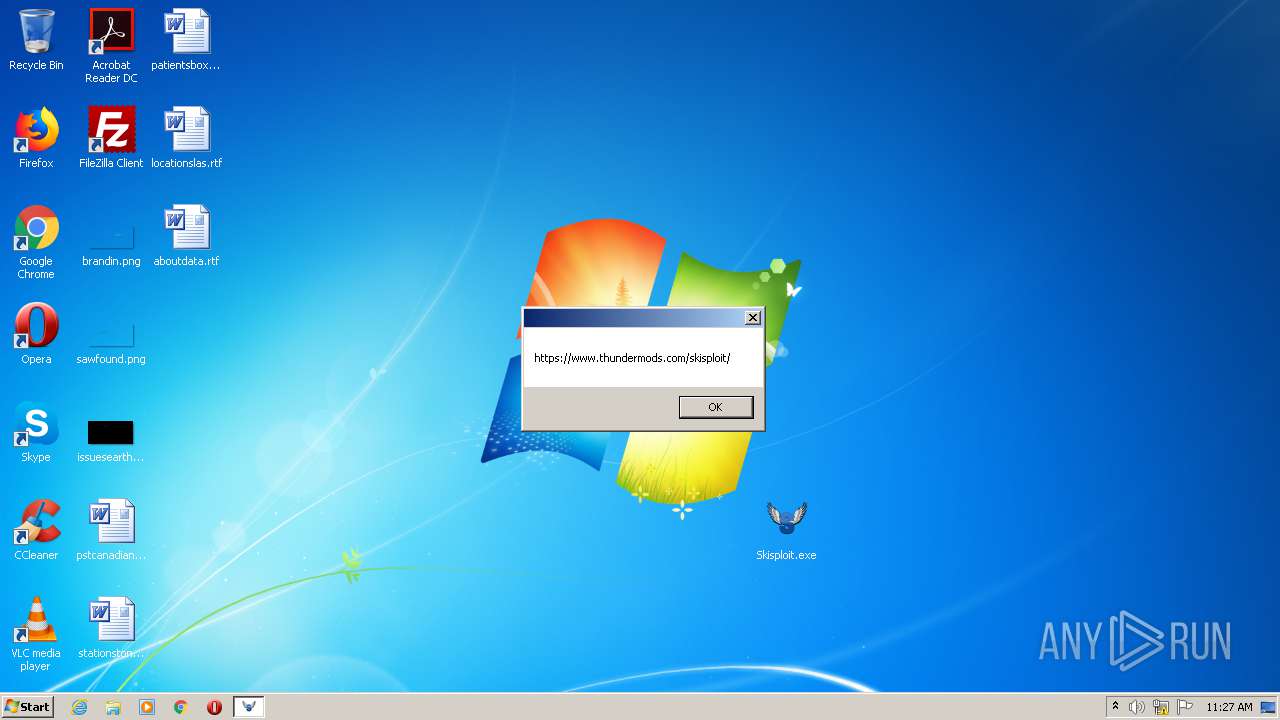
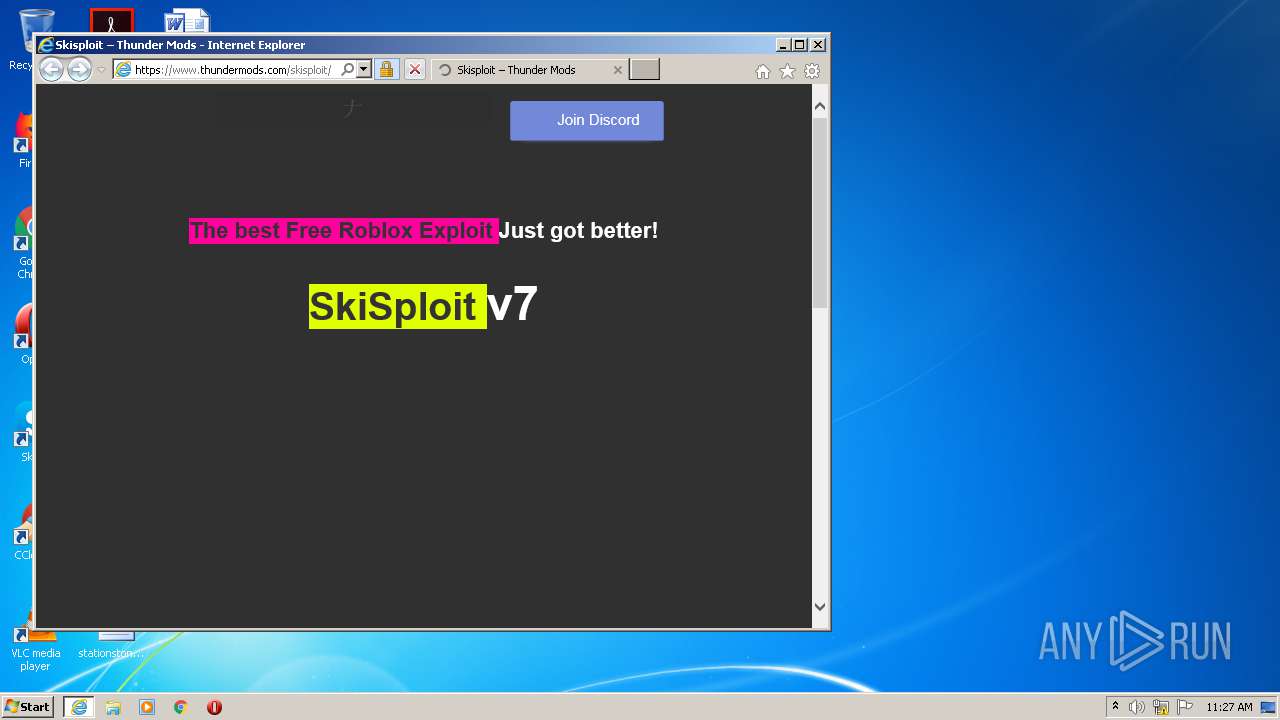
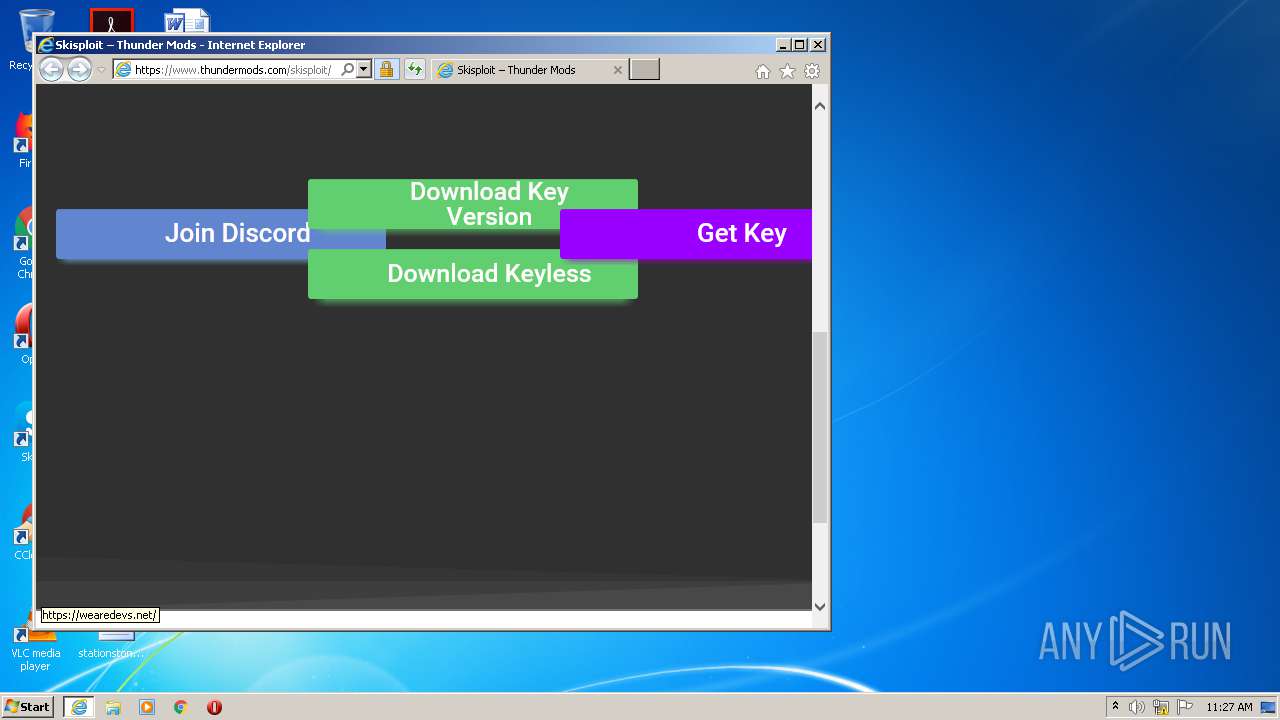
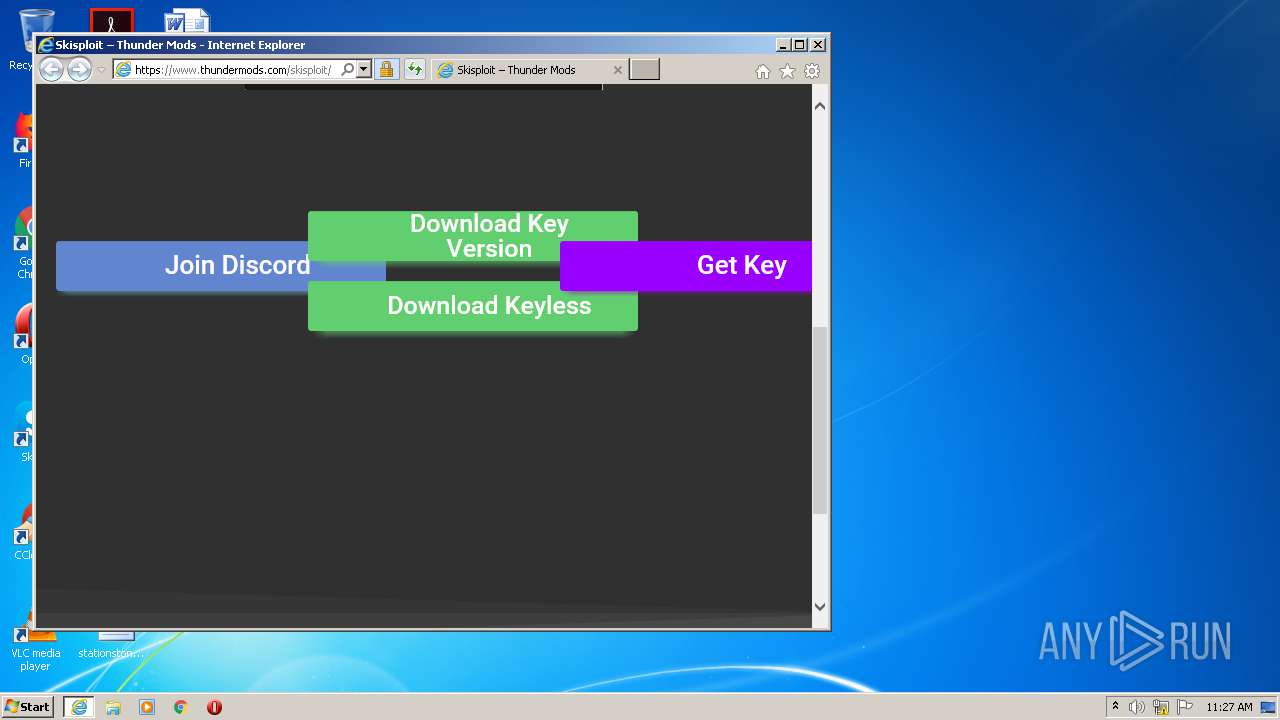
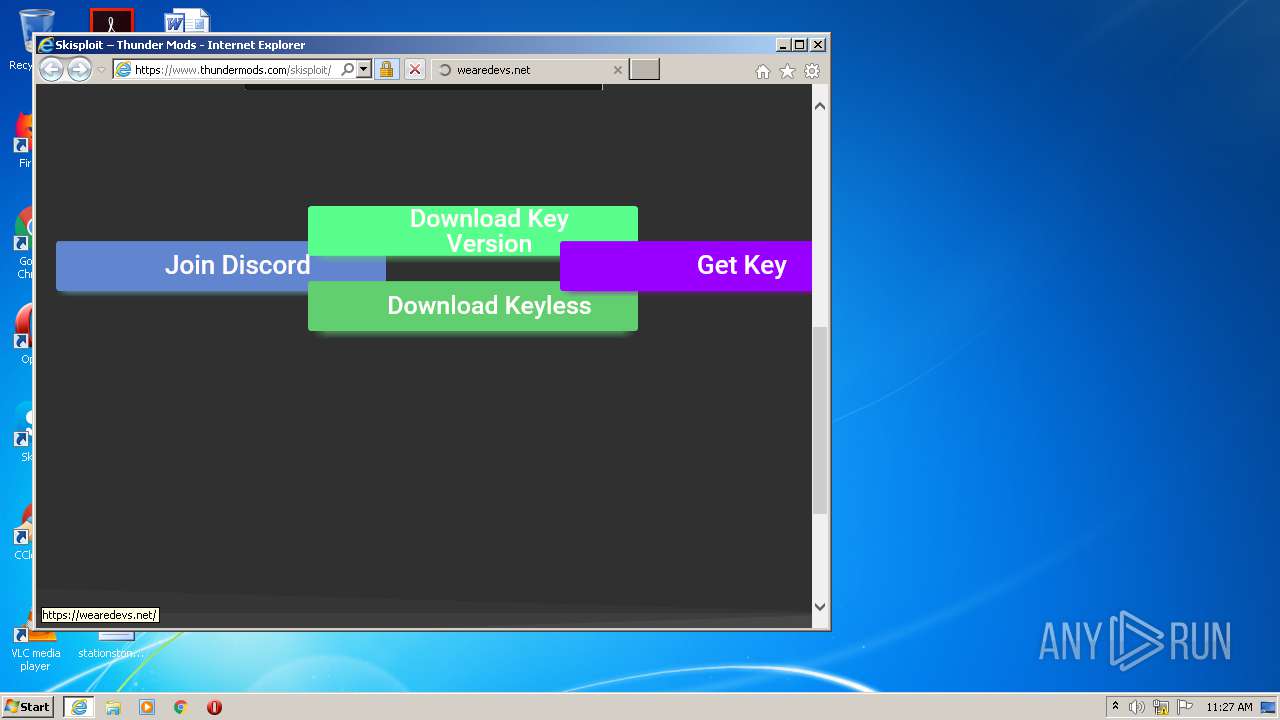
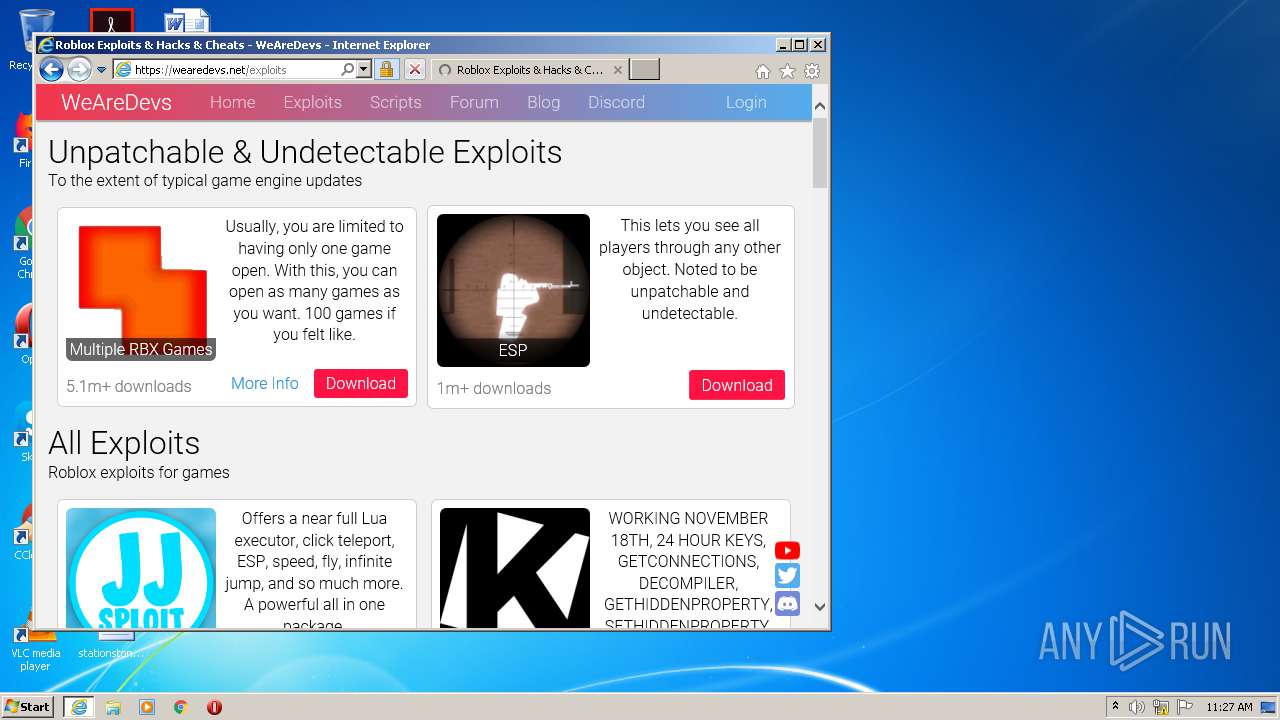
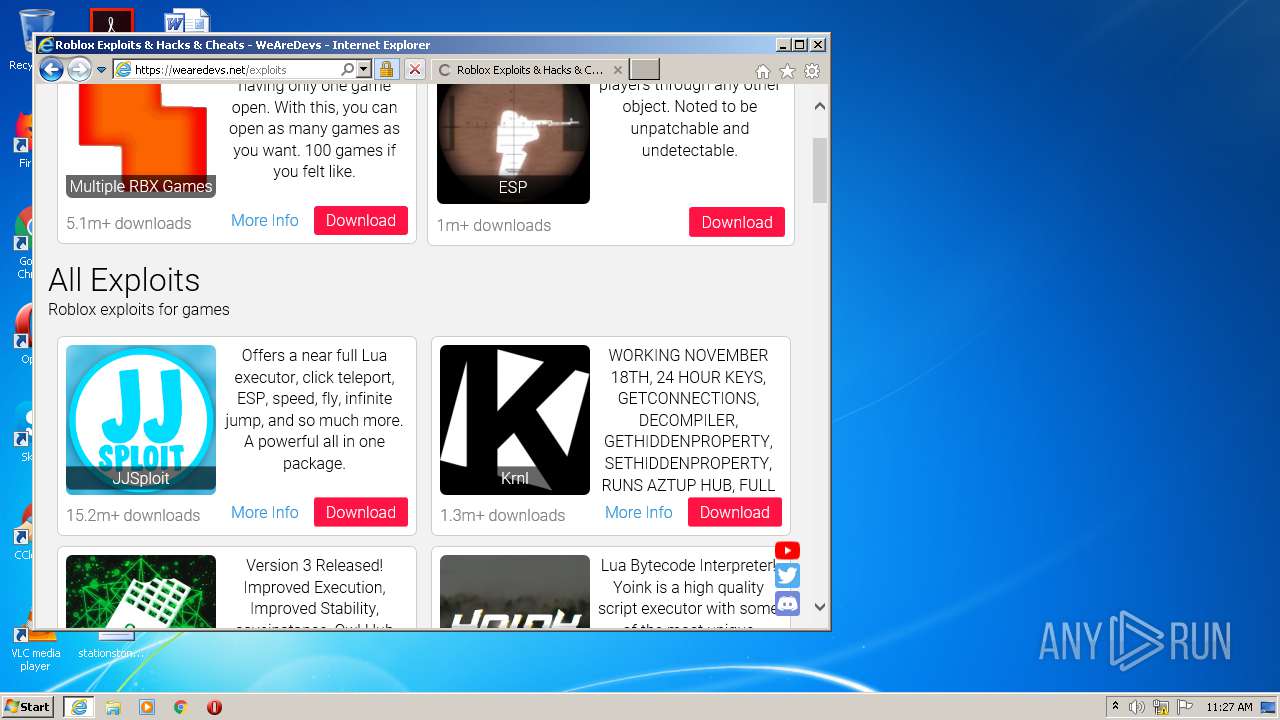
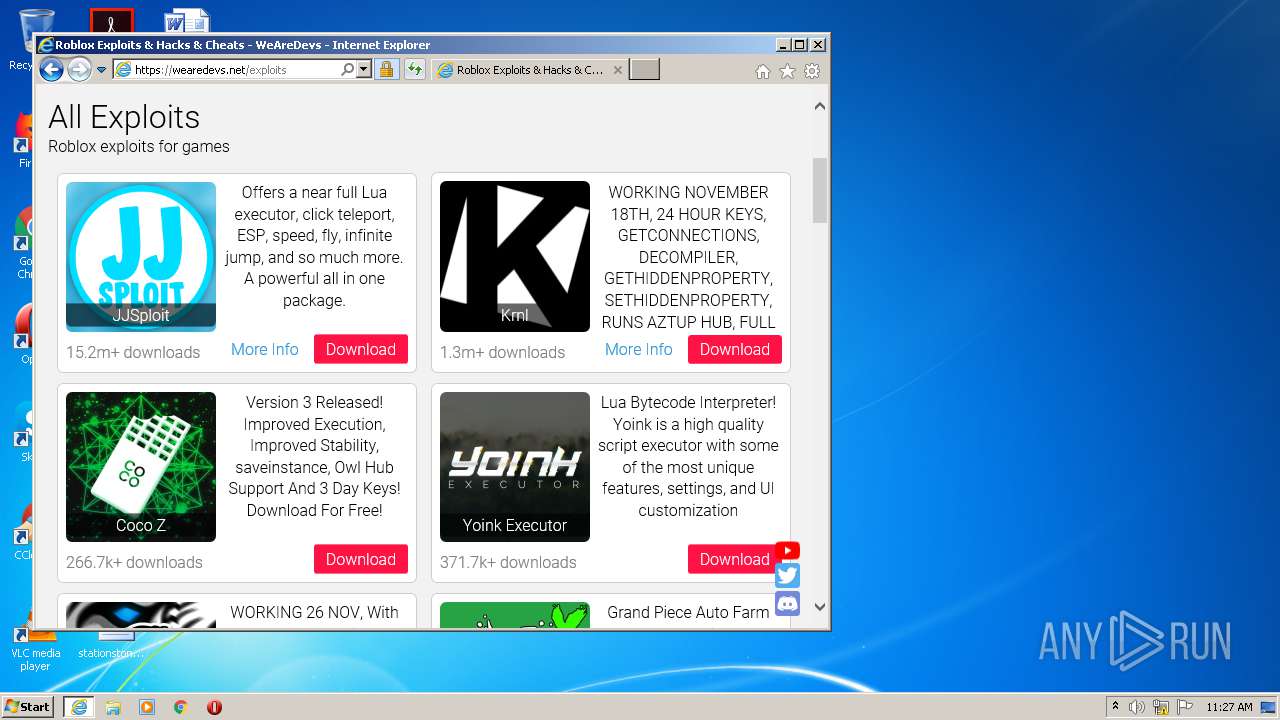
Starts Internet Explorer
- Skisploit.exe (PID: 1800)
INFO
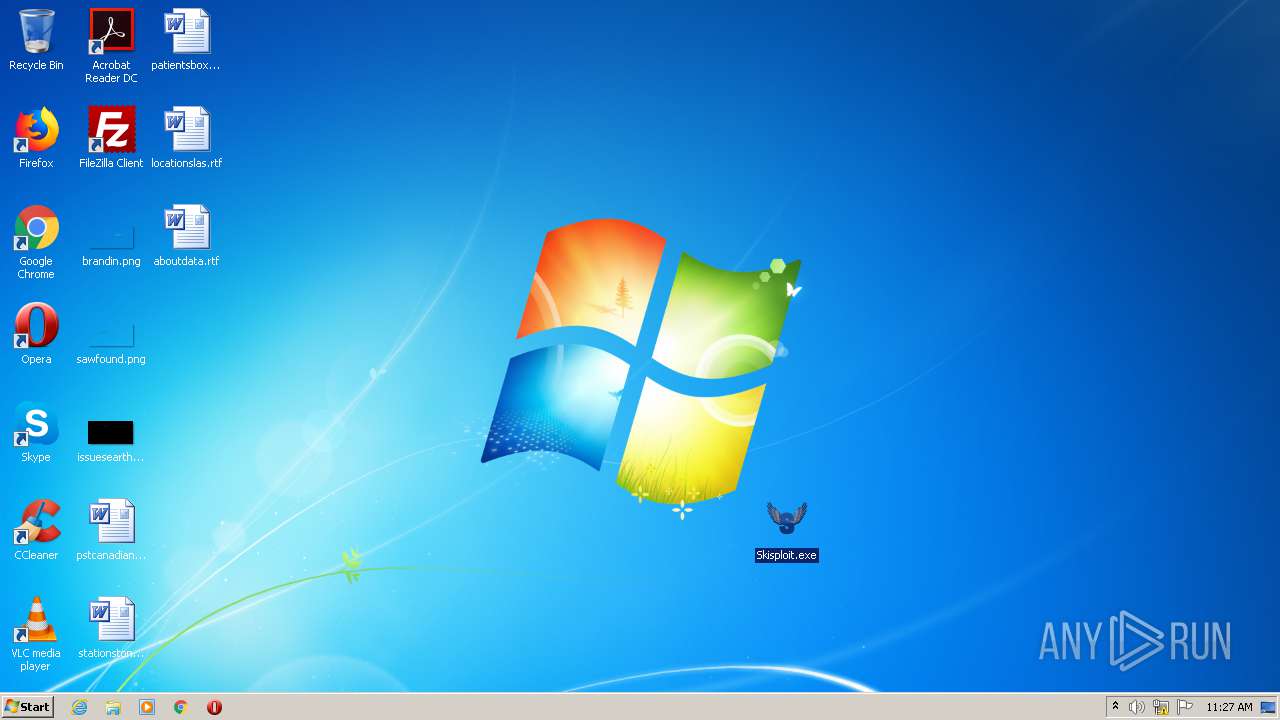
Manual execution by user
- Skisploit.exe (PID: 1800)
Changes internet zones settings
- iexplore.exe (PID: 2208)
Application launched itself
- iexplore.exe (PID: 2208)
Reads settings of System Certificates
- iexplore.exe (PID: 1920)
- iexplore.exe (PID: 2208)
Creates files in the user directory
- iexplore.exe (PID: 1920)
- iexplore.exe (PID: 2208)
Reads internet explorer settings
- iexplore.exe (PID: 1920)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2208)
Changes settings of System certificates
- iexplore.exe (PID: 2208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
38
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1800 | "C:\Users\admin\Desktop\Skisploit.exe" | C:\Users\admin\Desktop\Skisploit.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Skisploit Exit code: 0 Version: 2.0.0.5 Modules
| |||||||||||||||
| 1920 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2208 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1952 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Skisploit.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.thundermods.com/skisploit/ | C:\Program Files\Internet Explorer\iexplore.exe | Skisploit.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 341
Read events
1 089
Write events
251
Delete events
1
Modification events
| (PID) Process: | (1952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1952) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Skisploit.rar | |||
| (PID) Process: | (1952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (1952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
1
Suspicious files
118
Text files
142
Unknown types
73
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1920 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab97AA.tmp | — | |
MD5:— | SHA256:— | |||
| 1920 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar97AB.tmp | — | |
MD5:— | SHA256:— | |||
| 2208 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 1920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9FF67FB3141440EED32363089565AE60_E352512347F74186AC3F25D8D82AB077 | der | |
MD5:— | SHA256:— | |||
| 1920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CC197601BE0898B7B0FCC91FA15D8A69_20A41EFA74E592D2C51332C2C36EBF7F | der | |
MD5:— | SHA256:— | |||
| 1920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9FF67FB3141440EED32363089565AE60_E352512347F74186AC3F25D8D82AB077 | binary | |
MD5:— | SHA256:— | |||
| 1920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:— | SHA256:— | |||
| 1952 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1952.5945\Skisploit.exe | executable | |
MD5:— | SHA256:— | |||
| 1920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\skisploit[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
147
DNS requests
50
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1920 | iexplore.exe | GET | 200 | 92.122.214.147:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
1800 | Skisploit.exe | GET | 200 | 172.67.221.166:80 | http://api.thundermods.com/version.txt | US | text | 7 b | malicious |
1800 | Skisploit.exe | GET | 200 | 172.67.221.166:80 | http://api.thundermods.com/updatelink.txt | US | text | 38 b | malicious |
1920 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1920 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1800 | Skisploit.exe | GET | 200 | 172.67.221.166:80 | http://api.thundermods.com/updatemessage.txt | US | text | 189 b | malicious |
1920 | iexplore.exe | GET | 200 | 92.122.214.147:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgPbZyMWg7VeiWCef7Fm6c%2FSgA%3D%3D | unknown | der | 527 b | whitelisted |
1920 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEATXi7Ndo9ER0%2FY0D5NxnyM%3D | US | der | 278 b | whitelisted |
1920 | iexplore.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDgM%2F2Oalb9SggAAAAAYth0 | US | der | 472 b | whitelisted |
1920 | iexplore.exe | GET | 200 | 92.122.214.147:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgPbZyMWg7VeiWCef7Fm6c%2FSgA%3D%3D | unknown | der | 527 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1920 | iexplore.exe | 104.24.107.9:443 | api.thundermods.com | Cloudflare Inc | US | shared |
1800 | Skisploit.exe | 172.67.221.166:80 | api.thundermods.com | — | US | suspicious |
1920 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1920 | iexplore.exe | 216.58.206.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1920 | iexplore.exe | 172.217.18.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1920 | iexplore.exe | 139.45.196.84:443 | tharbadir.com | — | US | unknown |
1920 | iexplore.exe | 92.122.214.147:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | unknown |
1920 | iexplore.exe | 216.58.212.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2208 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 172.67.75.33:443 | static.lalaping.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.thundermods.com |
| malicious |
www.thundermods.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
tharbadir.com |
| malicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report