| File name: | locator.exe |
| Full analysis: | https://app.any.run/tasks/9a4c3f01-d6ce-4060-8d51-75fbc4ad4719 |
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2019, 20:06:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 9FEF8BFC026DDF7DCBC4BFE1D60762A7 |
| SHA1: | 50AC09382822CA065757B94F1FCC83CB80817D52 |
| SHA256: | F77B3069CC28B8C4EDBFFF935DC83EE701821E529A509DA7F157B5DE52B39863 |
| SSDEEP: | 98304:BSNgdeDvyMTcDa5LeRmzn17hJf+Dj/PuUyV:bedkmVmD+V |
MALICIOUS
Changes the autorun value in the registry
- qbXePHV:EYm (PID: 2076)
SUSPICIOUS
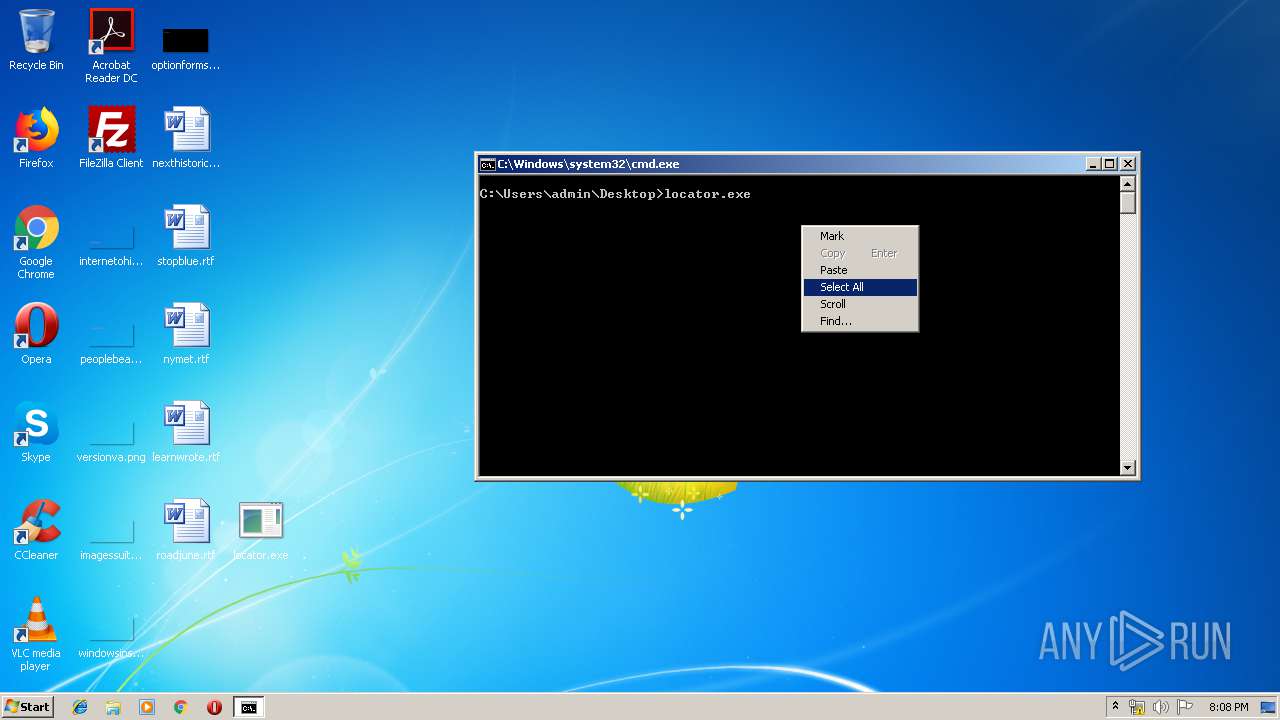
Starts application with an unusual extension
- locator.exe (PID: 3932)
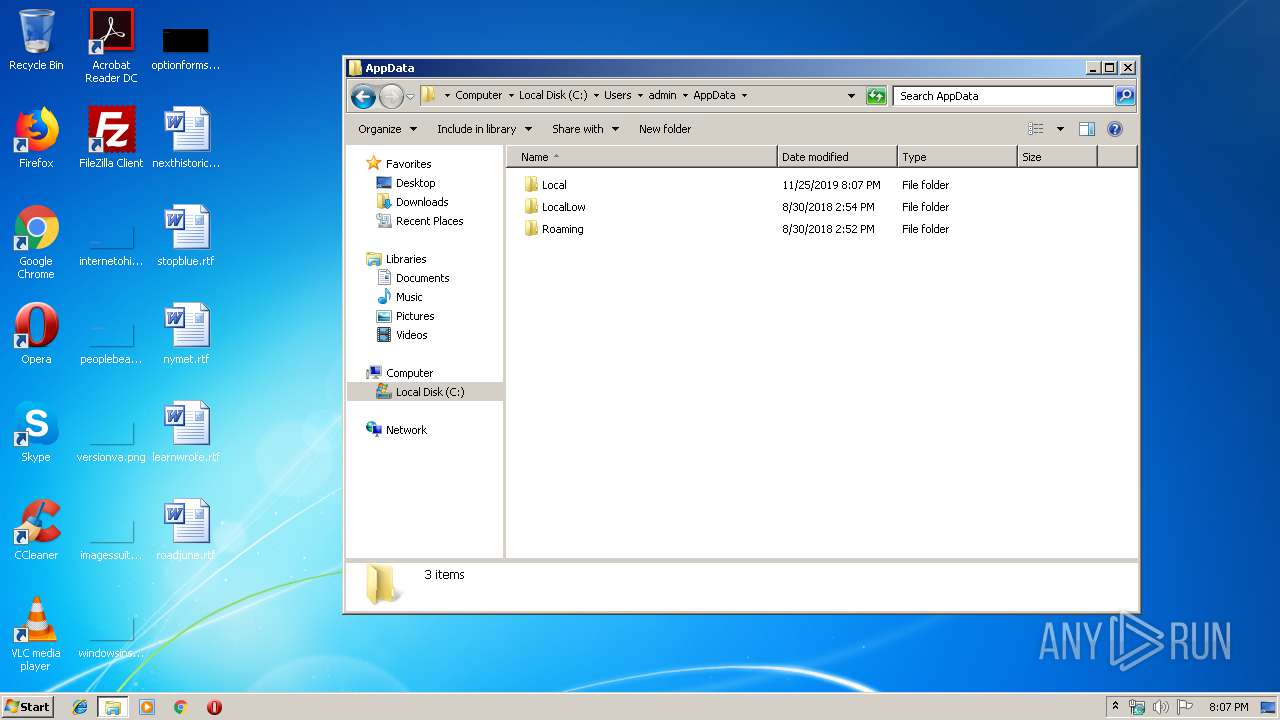
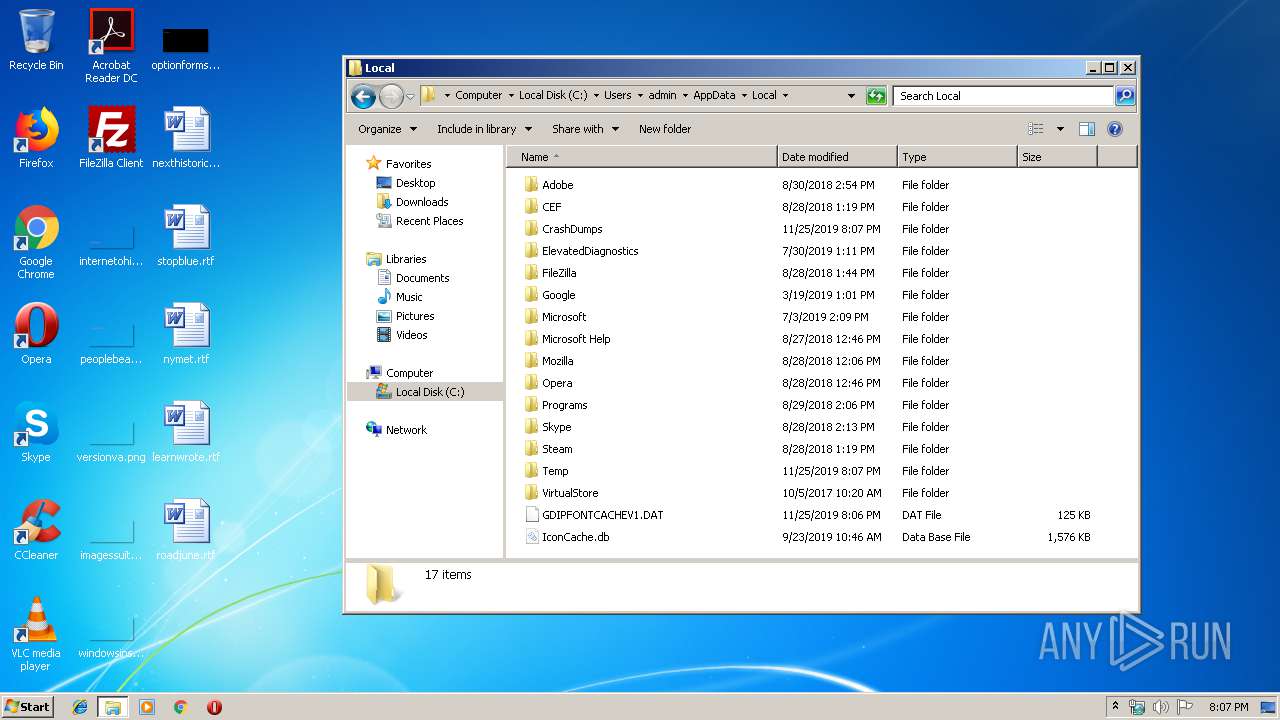
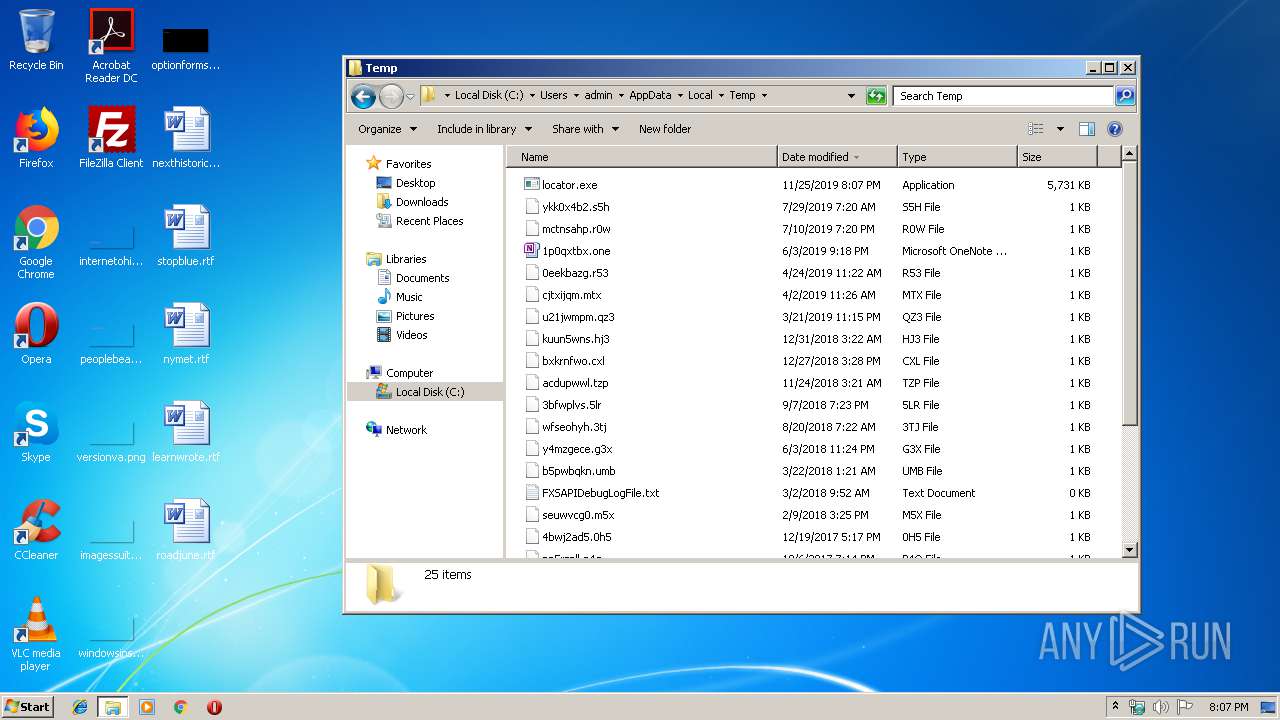
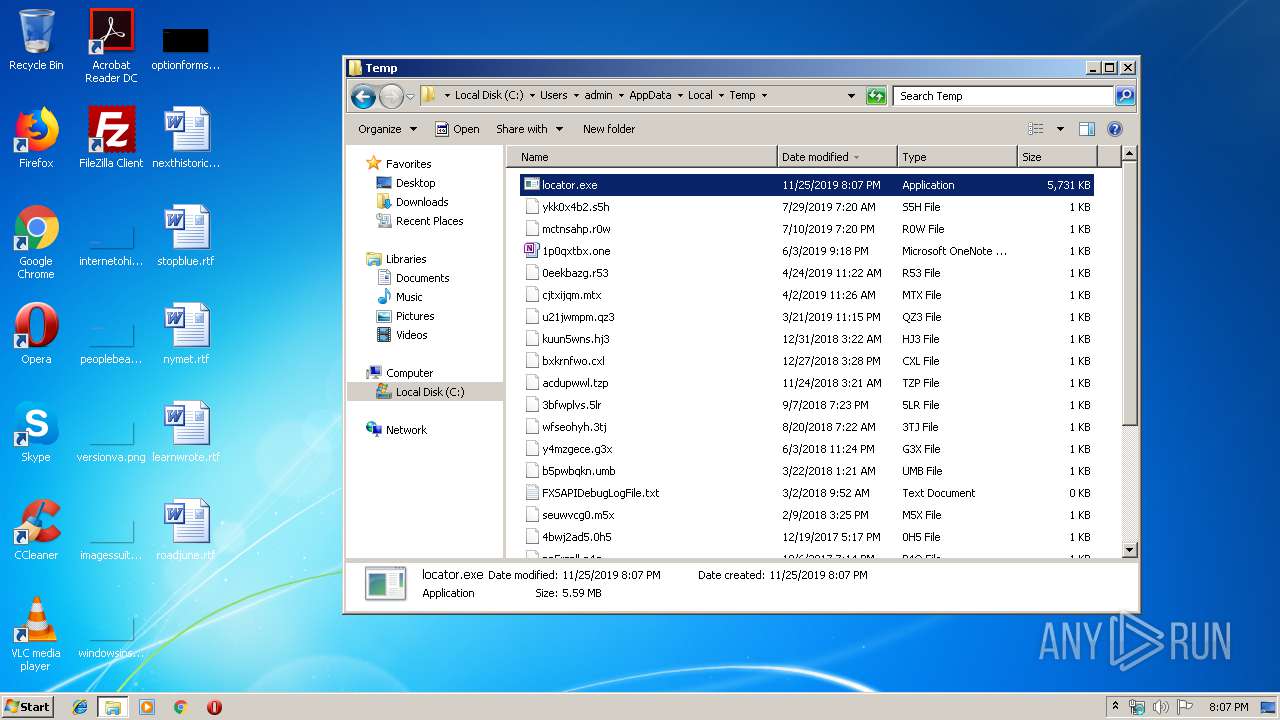
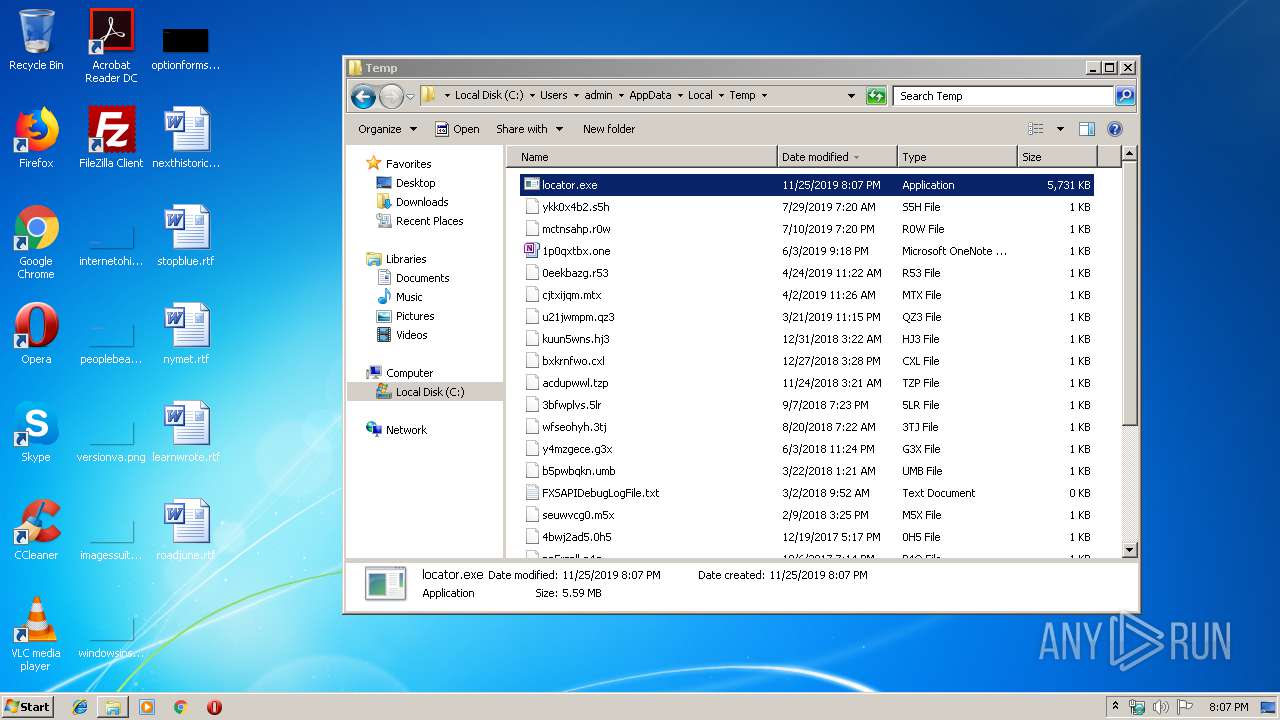
Executable content was dropped or overwritten
- locator.exe (PID: 3932)
- qbXePHV:EYm (PID: 2076)
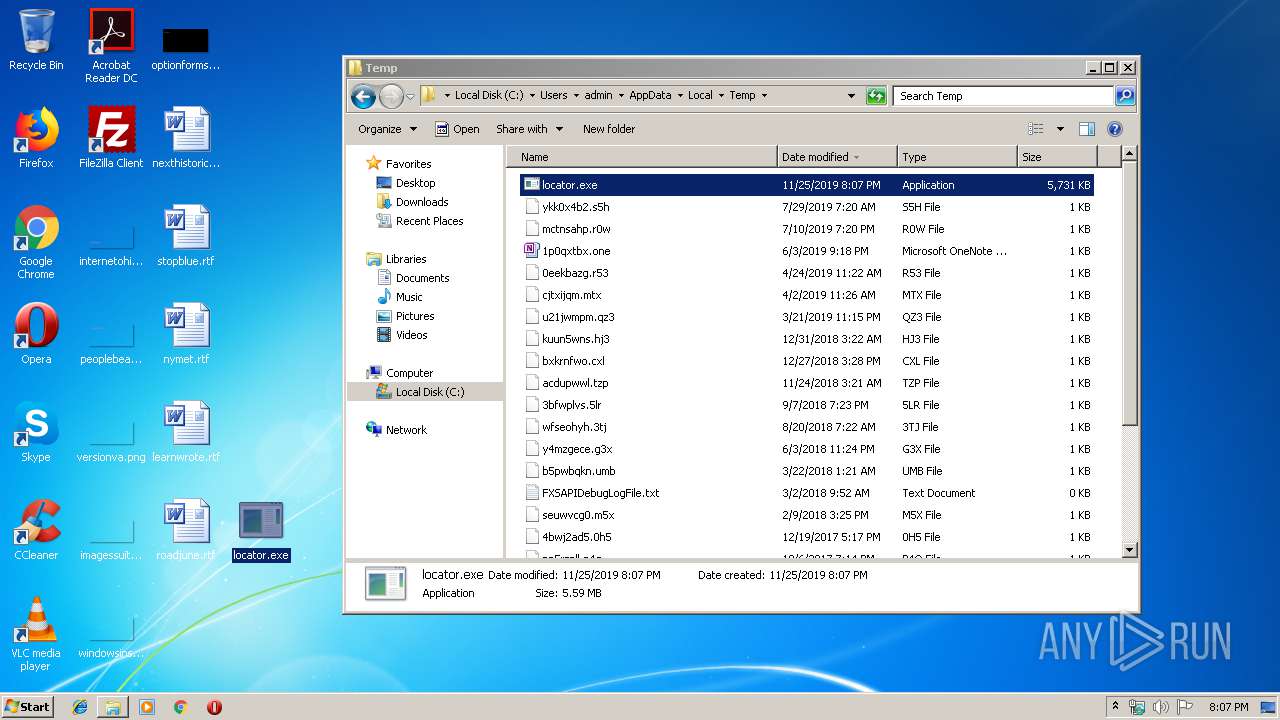
Starts itself from another location
- locator.exe (PID: 3932)
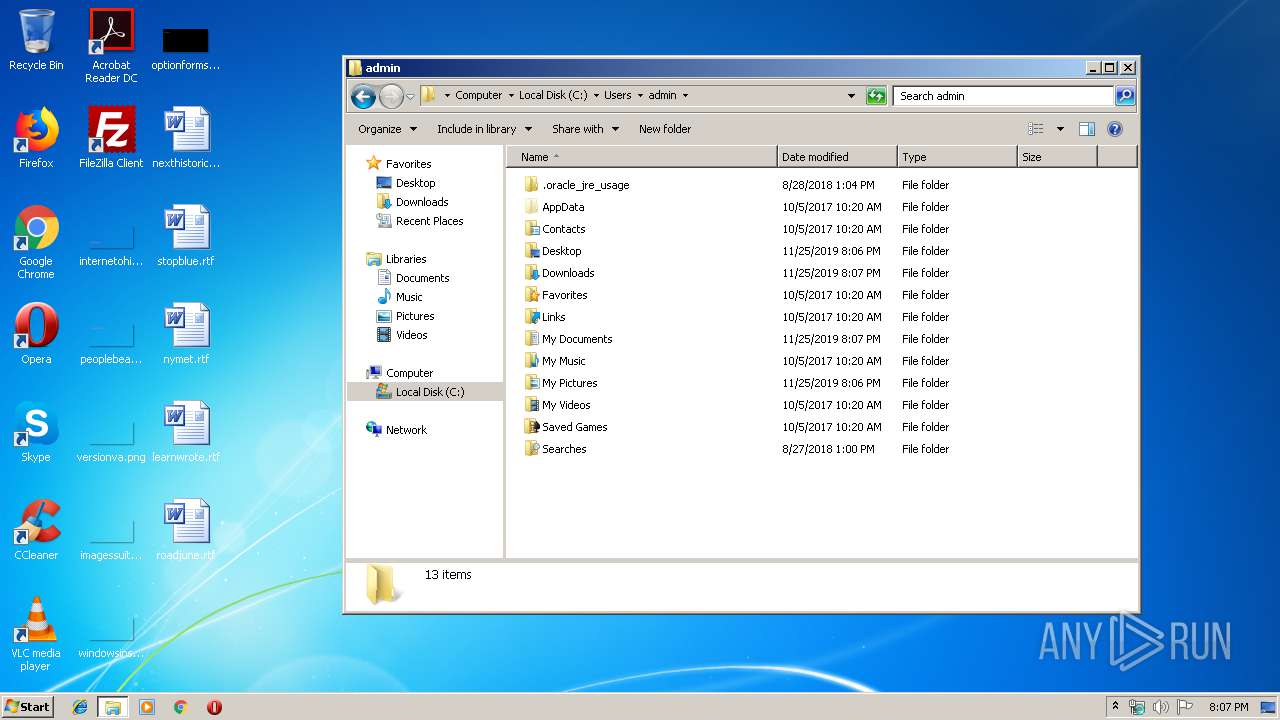
Creates files in the user directory
- locator.exe (PID: 3932)
- qbXePHV:EYm (PID: 2076)
Uses ICACLS.EXE to modify access control list
- qbXePHV:EYm (PID: 2076)
Starts NET.EXE for network exploration
- qbXePHV:EYm (PID: 2076)
Creates files in the program directory
- qbXePHV:EYm (PID: 2076)
INFO
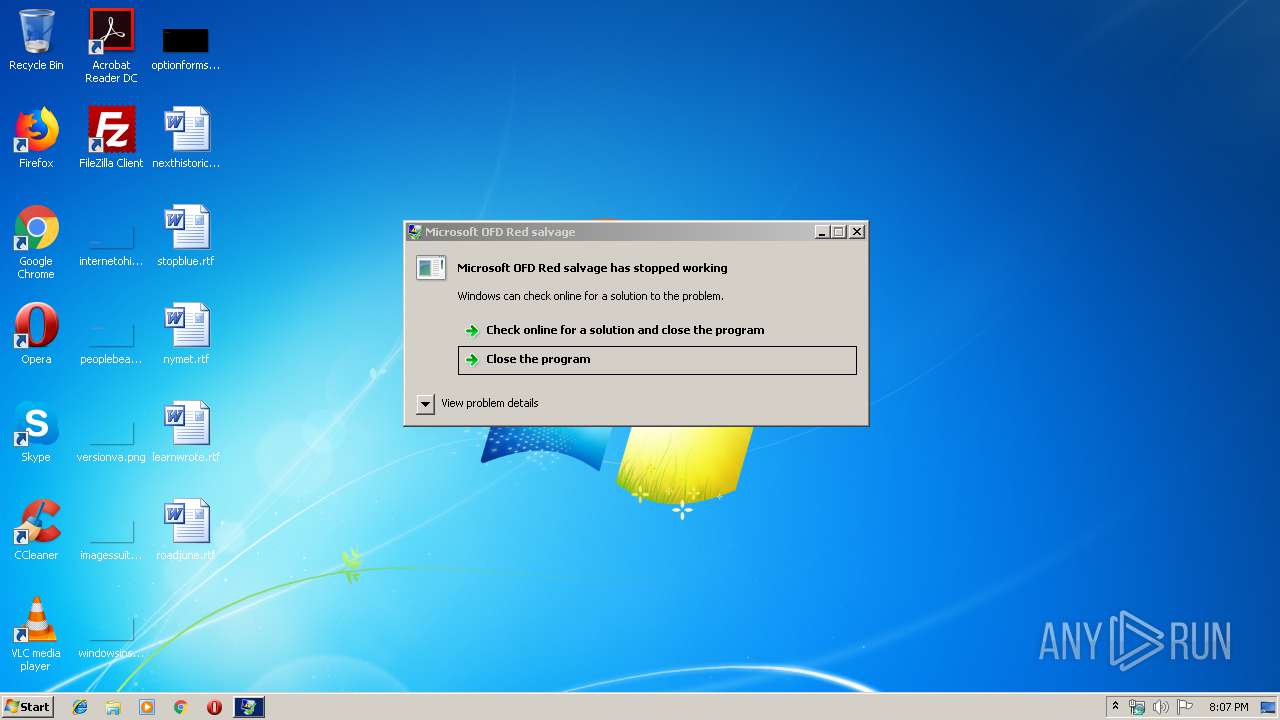
Application was crashed
- locator.exe (PID: 2092)
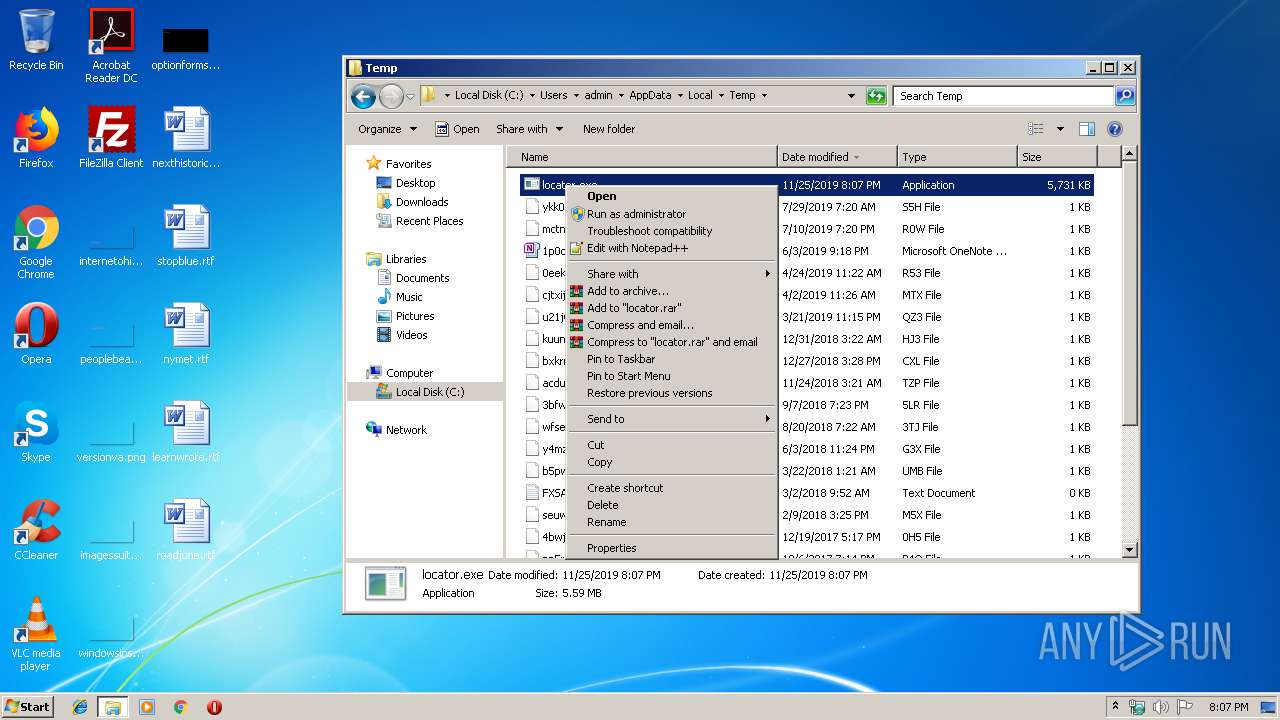
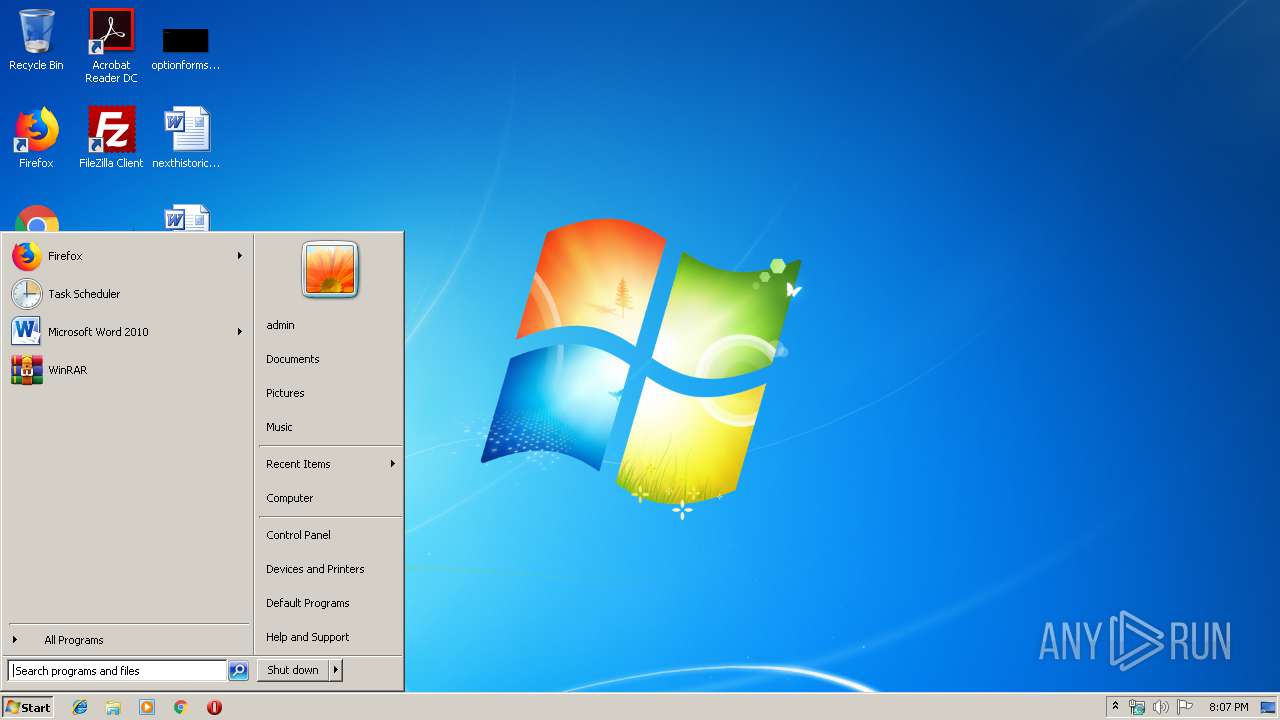
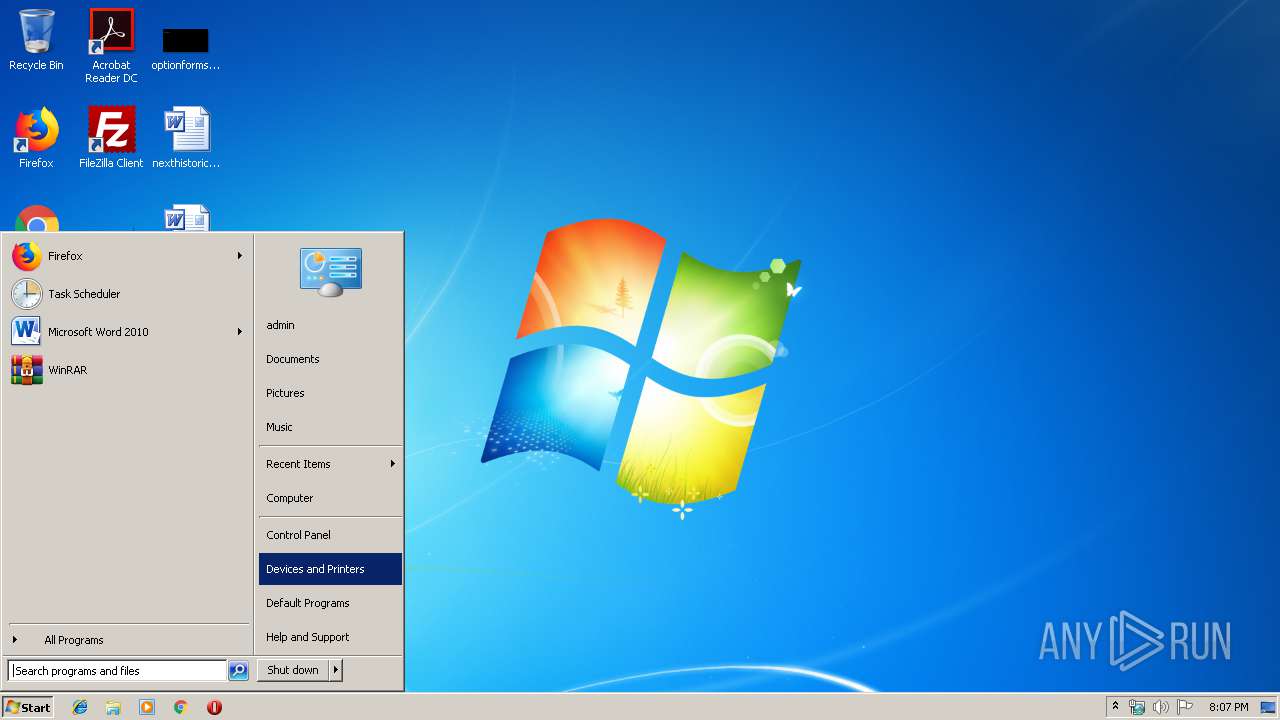
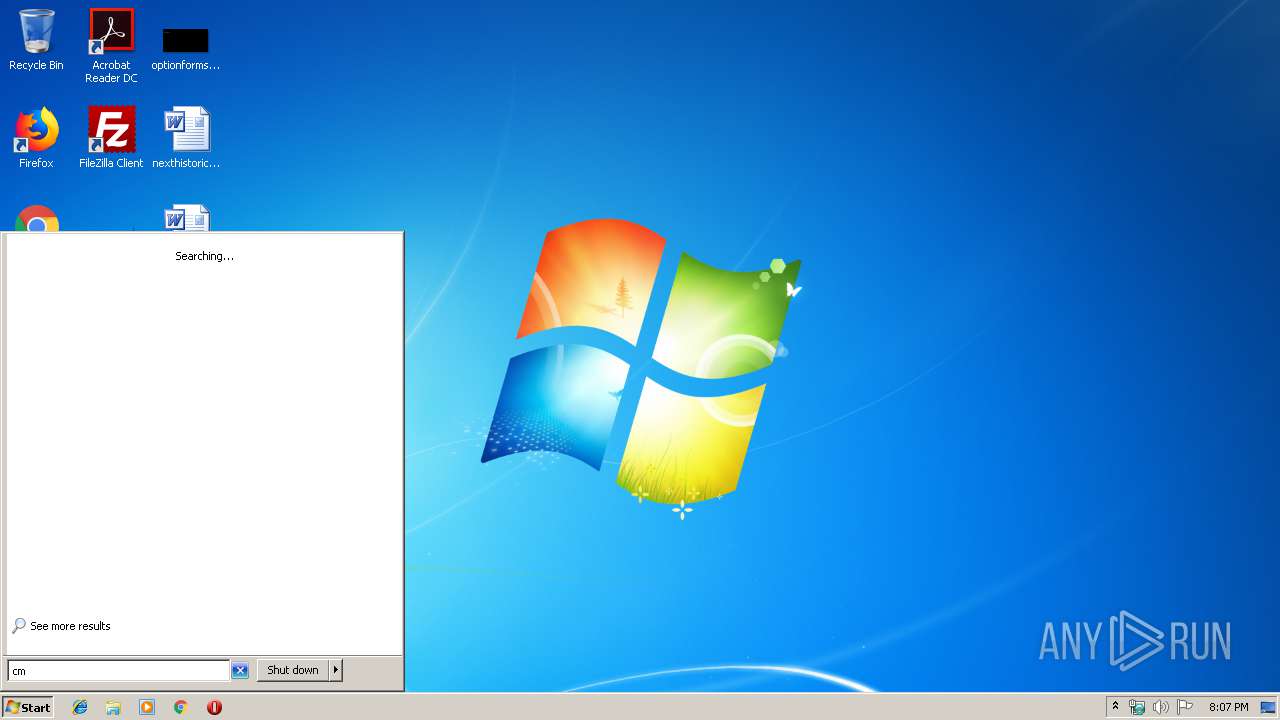
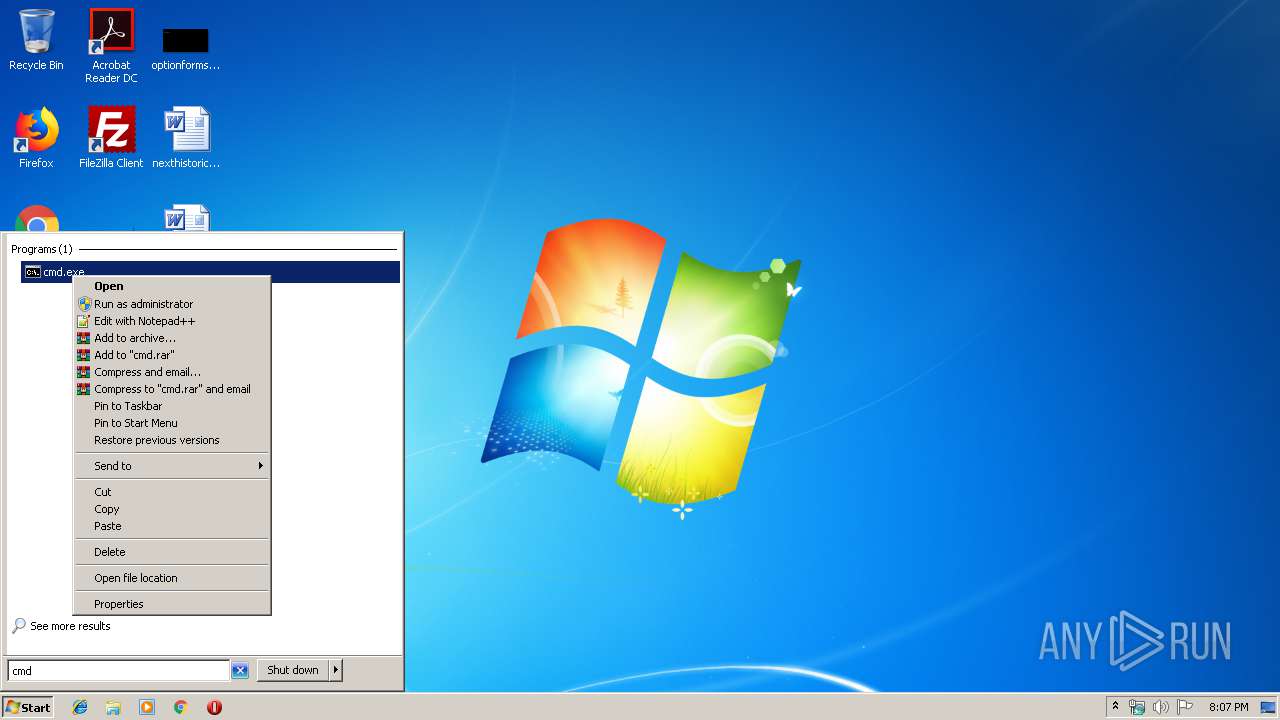
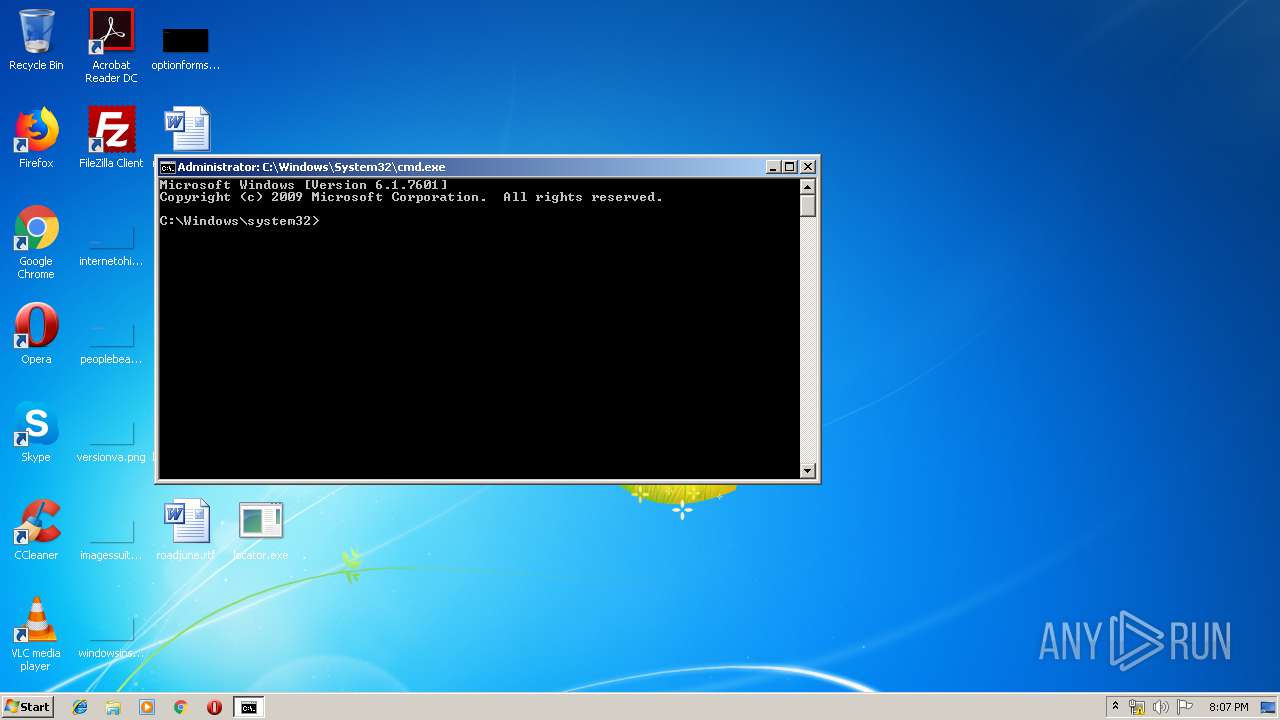
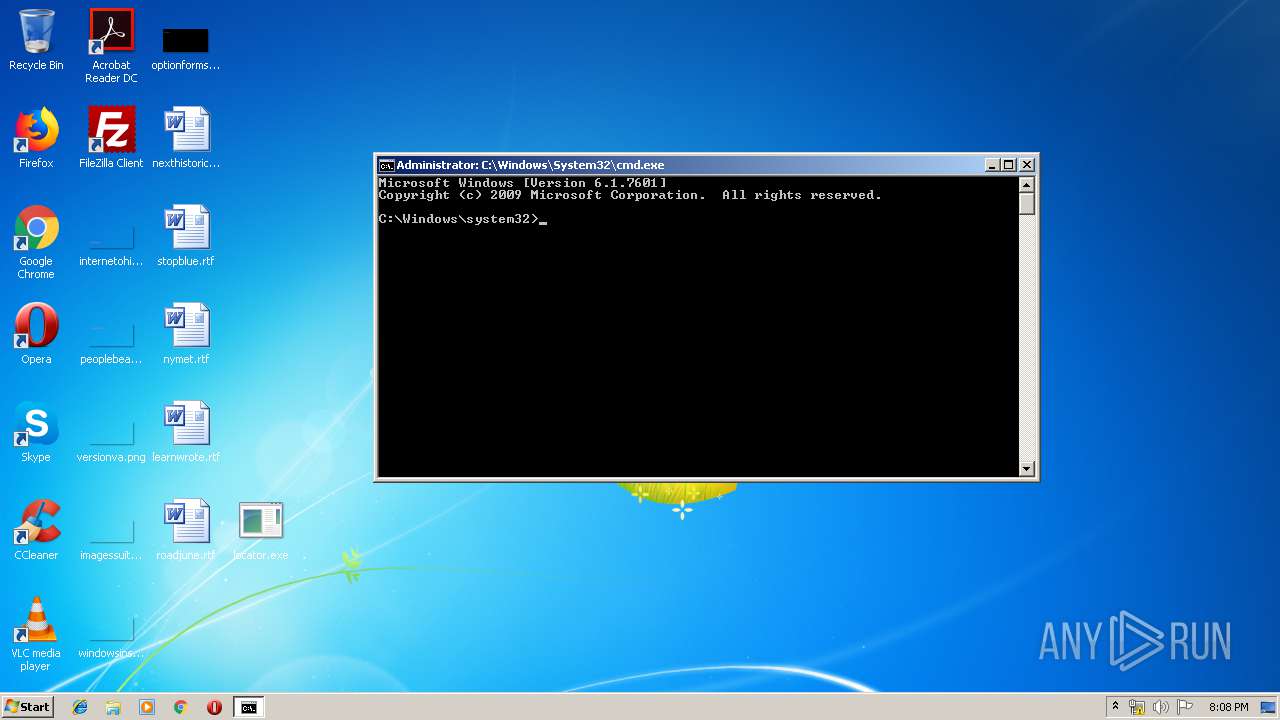
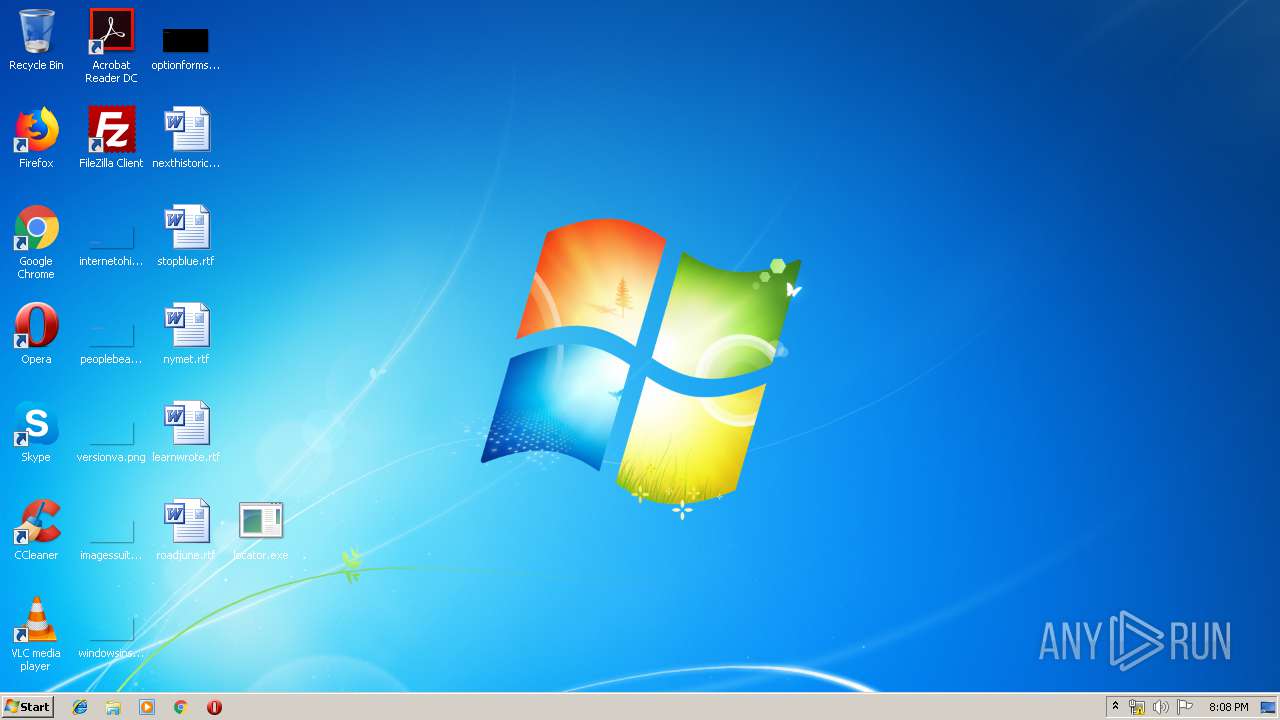
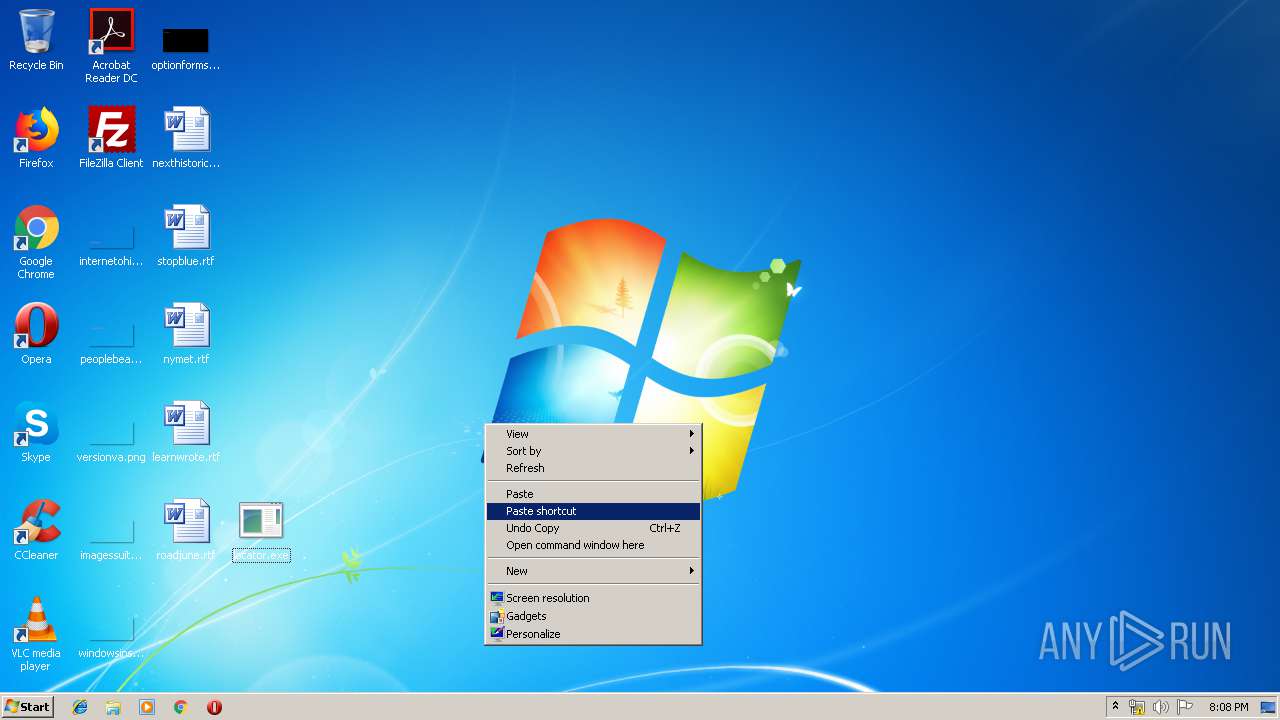
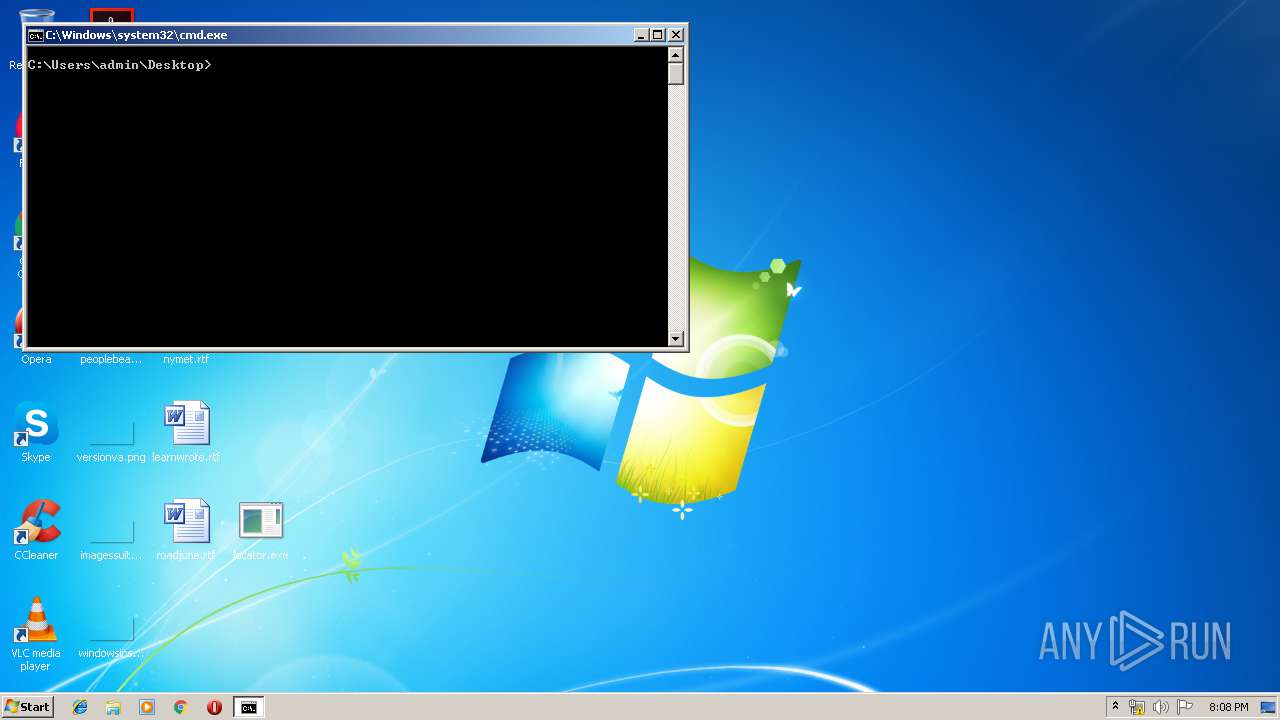
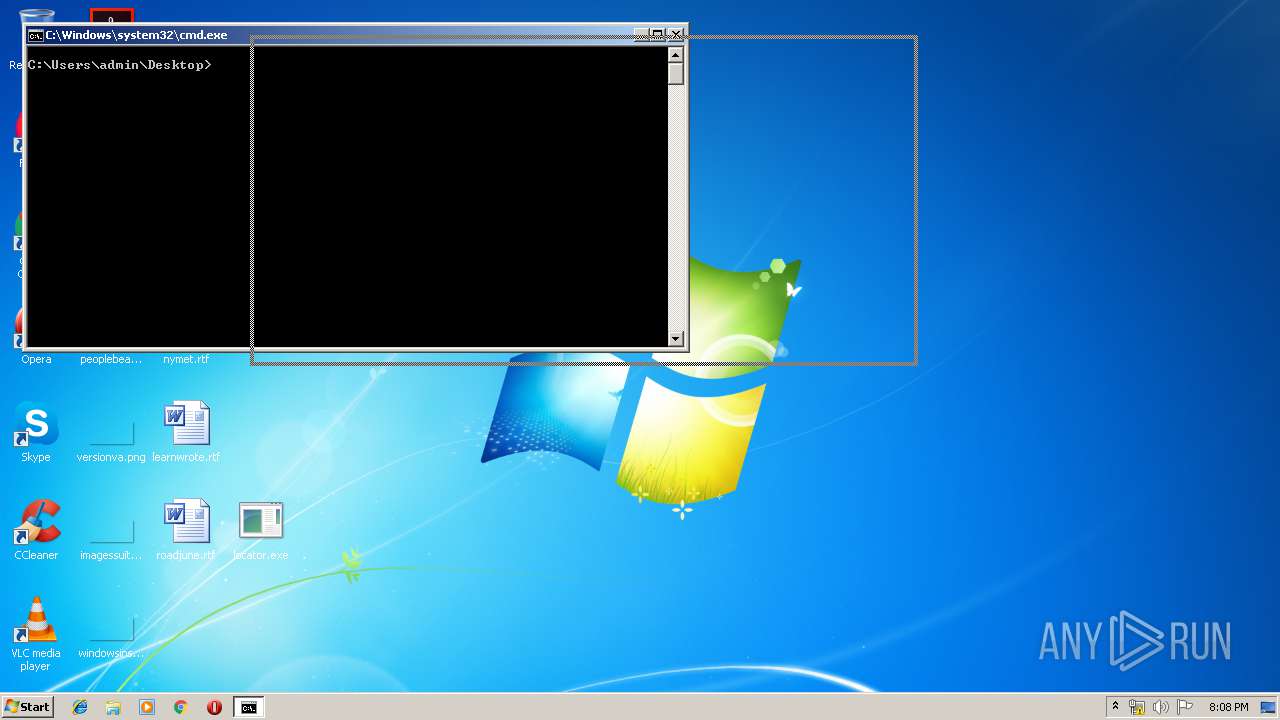
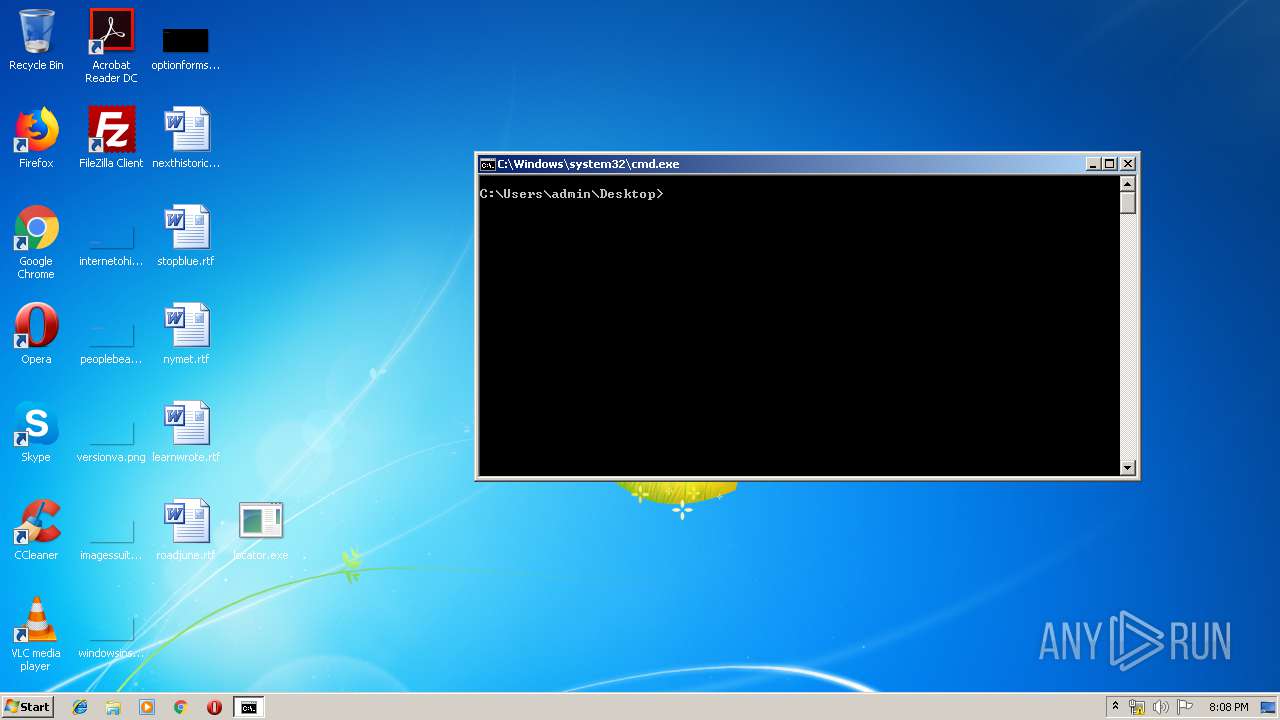
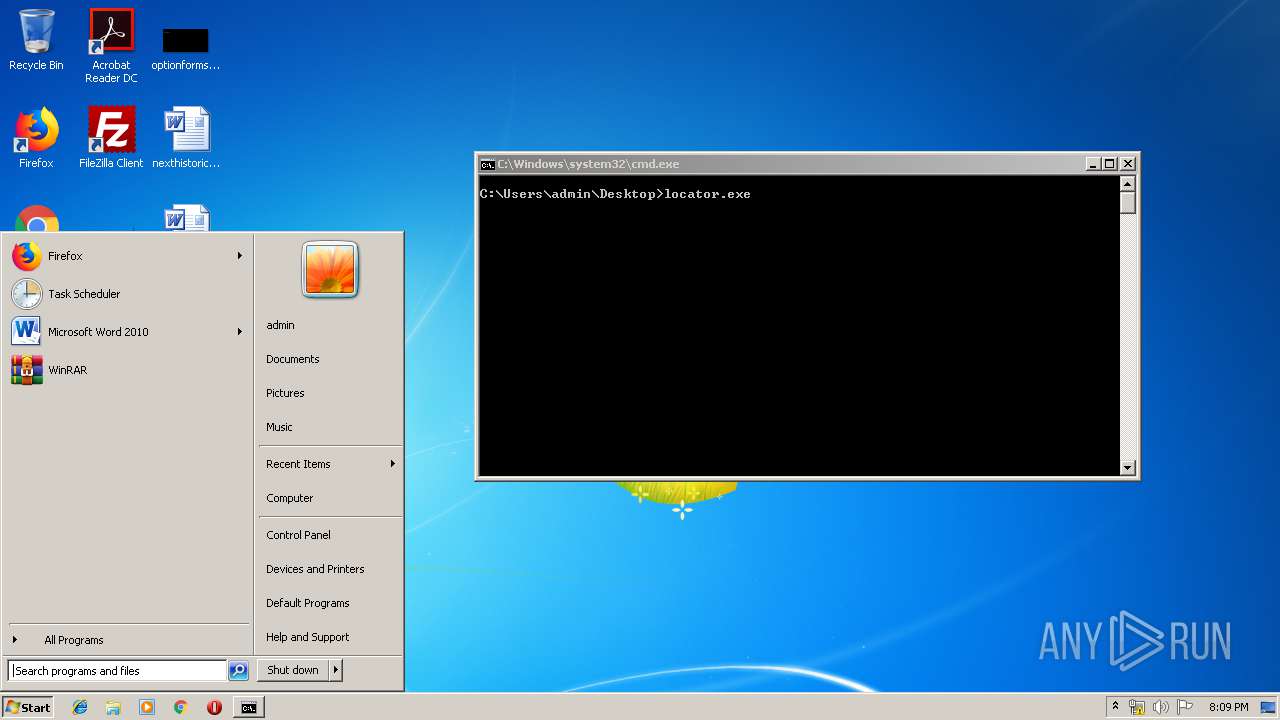
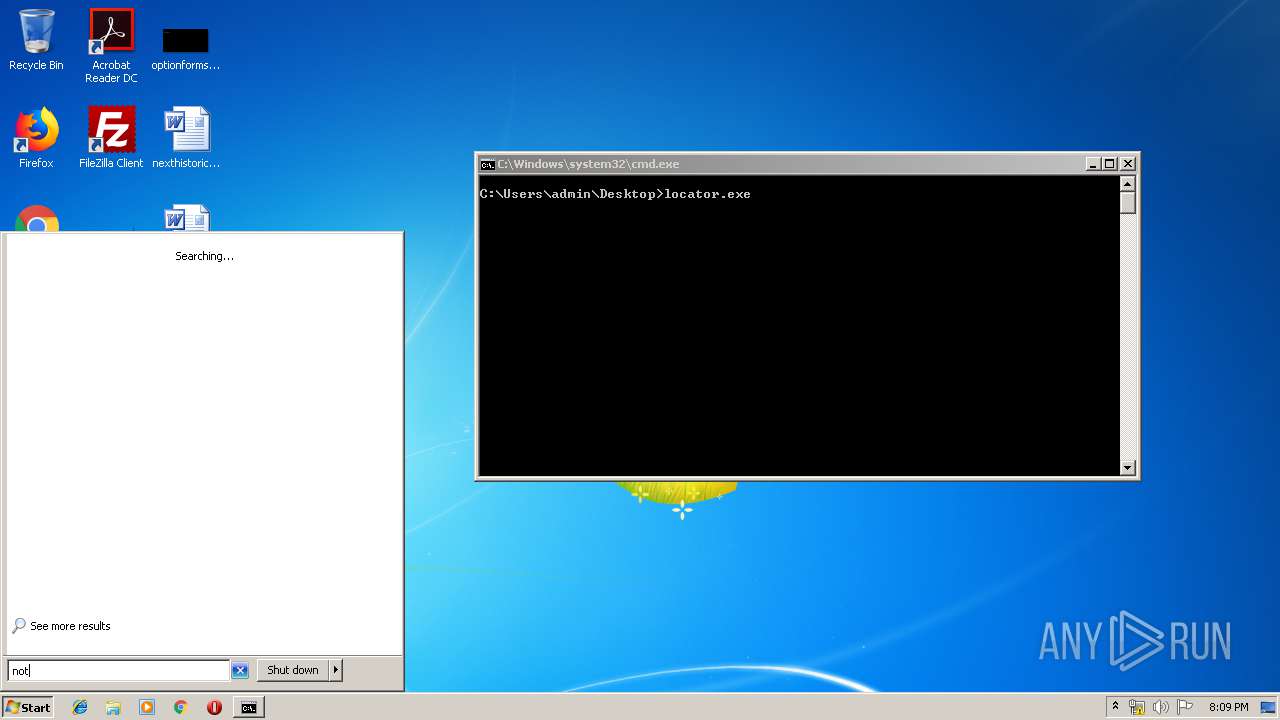
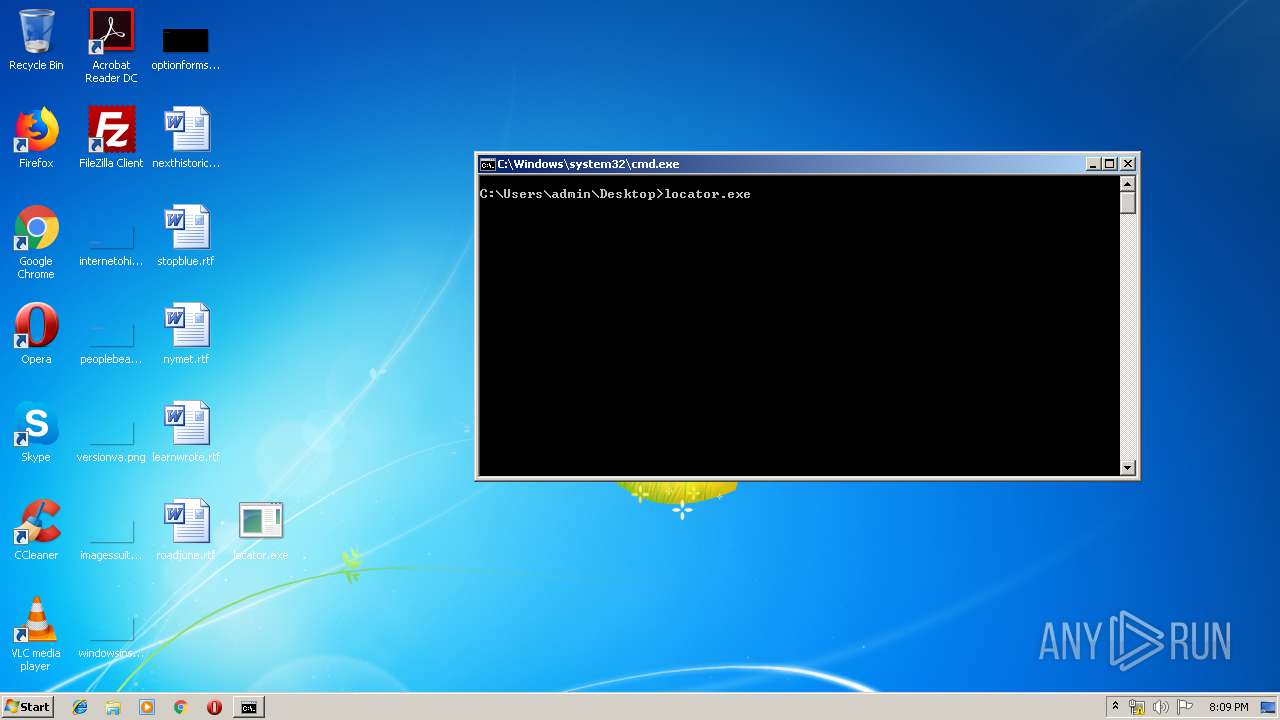
Manual execution by user
- notepad.exe (PID: 3852)
- explorer.exe (PID: 3172)
- cmd.exe (PID: 1780)
- cmd.exe (PID: 3356)
Dropped object may contain Bitcoin addresses
- qbXePHV:EYm (PID: 2076)
Dropped object may contain URL to Tor Browser
- qbXePHV:EYm (PID: 2076)
Dropped object may contain TOR URL's
- qbXePHV:EYm (PID: 2076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:09 16:05:20+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 40960 |
| InitializedDataSize: | 5820416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1005 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 11.0.0.716 |
| ProductVersionNumber: | 11.0.0.716 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft OFD Red salvage |
| FileVersion: | 11.00.0716 |
| InternalName: | RSalv |
| LegalCopyright: | Copyright (C) Microsoft Corp. 1990-2001. All rights reserved. |
| OriginalFileName: | RSalv.DLL |
| ProductName: | Microsoft Money |
| ProductVersion: | 11.00.0716 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 09-Nov-2018 15:05:20 |
| Detected languages: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft OFD Red salvage |
| FileVersion: | 11.00.0716 |
| InternalName: | RSalv |
| LegalCopyright: | Copyright (C) Microsoft Corp. 1990-2001. All rights reserved. |
| OriginalFilename: | RSalv.DLL |
| ProductName: | Microsoft Money |
| ProductVersion: | 11.00.0716 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 09-Nov-2018 15:05:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000099D6 | 0x0000A000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.044 |
.data | 0x0020D000 | 0x00372328 | 0x00373000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.28777 |
.idata | 0x0020C000 | 0x00000B80 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_READ, IMAGE_SCN_TYPE_COPY, IMAGE_SCN_TYPE_DSECT, IMAGE_SCN_TYPE_GROUP, IMAGE_SCN_TYPE_NOLOAD, IMAGE_SCN_TYPE_NO_PAD | 2.30265 |
.CRT | 0x00580000 | 0x0000031C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0131269 |
.rsrc | 0x00581000 | 0x00000C56 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.05482 |
.reloc | 0x00582000 | 0x00015817 | 0x00016000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.11211 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.45917 | 836 | UNKNOWN | English - United States | RT_VERSION |
126 | 3.23237 | 1020 | UNKNOWN | English - United States | RT_STRING |
127 | 2.45048 | 122 | UNKNOWN | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHLWAPI.dll |
USER32.dll |
msi.dll |
Total processes
88
Monitored processes
25
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | C:\Windows\system32\takeown.exe /F "C:\Documents and Settings" | C:\Windows\system32\takeown.exe | — | qbXePHV:EYm | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Takes ownership of a file Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1772 | C:\Windows\system32\icacls.exe C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-500 /reset | C:\Windows\system32\icacls.exe | — | qbXePHV:EYm | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1780 | "cmd.exe" /s /k pushd "C:\Users\admin\Desktop" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1892 | C:\Windows\system32\\nslookup.exe 224.0.0.252 | C:\Windows\system32\nslookup.exe | qbXePHV:EYm | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1916 | C:\Windows\system32\\nslookup.exe 224.0.0.22 | C:\Windows\system32\nslookup.exe | qbXePHV:EYm | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1944 | C:\Windows\system32\\nslookup.exe 192.168.100.2 | C:\Windows\system32\nslookup.exe | qbXePHV:EYm | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2076 | C:\Users\admin\AppData\Roaming\qbXePHV:EYm rj57cs9dmafYKN5BqK8OouDC C:\Users\admin\Desktop\locator.exe | C:\Users\admin\AppData\Roaming\qbXePHV:EYm | locator.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2092 | "C:\Users\admin\AppData\Local\Temp\locator.exe" | C:\Users\admin\AppData\Local\Temp\locator.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OFD Red salvage Exit code: 3221225477 Version: 11.00.0716 Modules
| |||||||||||||||
| 2192 | C:\Windows\system32\\net.exe view igmp.mcast.net | C:\Windows\system32\net.exe | — | qbXePHV:EYm | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2244 | C:\Windows\system32\\nslookup.exe 239.255.255.250 | C:\Windows\system32\nslookup.exe | qbXePHV:EYm | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
82
Read events
77
Write events
5
Delete events
0
Modification events
| (PID) Process: | (3852) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 44 | |||
| (PID) Process: | (3852) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 44 | |||
| (PID) Process: | (3852) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (3852) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
| (PID) Process: | (2076) qbXePHV:EYm | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | f9bmLJM9l9rK7G |
Value: C:\Users\admin\AppData\Roaming\FVVEFW~1\UDX2WB~1.EXE | |||
Executable files
3
Suspicious files
3
Text files
4 022
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2076 | qbXePHV:EYm | C:\Users\admin\AppData\Local\Temp\QnB0ED.tmp | — | |
MD5:— | SHA256:— | |||
| 2076 | qbXePHV:EYm | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Benioku.htm | — | |
MD5:— | SHA256:— | |||
| 2076 | qbXePHV:EYm | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Benioku.htm.locked | — | |
MD5:— | SHA256:— | |||
| 2076 | qbXePHV:EYm | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Berime.htm | — | |
MD5:— | SHA256:— | |||
| 2076 | qbXePHV:EYm | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Berime.htm.locked | — | |
MD5:— | SHA256:— | |||
| 2076 | qbXePHV:EYm | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\IrakHau.htm | — | |
MD5:— | SHA256:— | |||
| 2076 | qbXePHV:EYm | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\IrakHau.htm.locked | — | |
MD5:— | SHA256:— | |||
| 2076 | qbXePHV:EYm | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Leame.htm | — | |
MD5:— | SHA256:— | |||
| 2076 | qbXePHV:EYm | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Leame.htm.locked | — | |
MD5:— | SHA256:— | |||
| 2076 | qbXePHV:EYm | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\LeesMij.htm | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
igmp.mcast.net |
| whitelisted |