| File name: | RUNDLG.EXE |
| Full analysis: | https://app.any.run/tasks/8ef2ce96-7140-4620-b475-9b0fa123be16 |
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2021, 11:33:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable, MZ for MS-DOS |
| MD5: | D4B2063C64737CCBD33DB7FE14FB8EFA |
| SHA1: | 90AEC895822DC6561963CF355FA45E76F9459283 |
| SHA256: | F756B34676BF480317044E572388043862BBD9813ECA7F7045F5D08FBF533515 |
| SSDEEP: | 24:tFnoCH63lNXvUrf63HNIPNaiThl3jVELrT6HQTw8b0bM03xhpeQuxT7ckFyqbeWA:voJxMfgtwaiqLrT6Qk84QghpeTNIqbe |
MALICIOUS
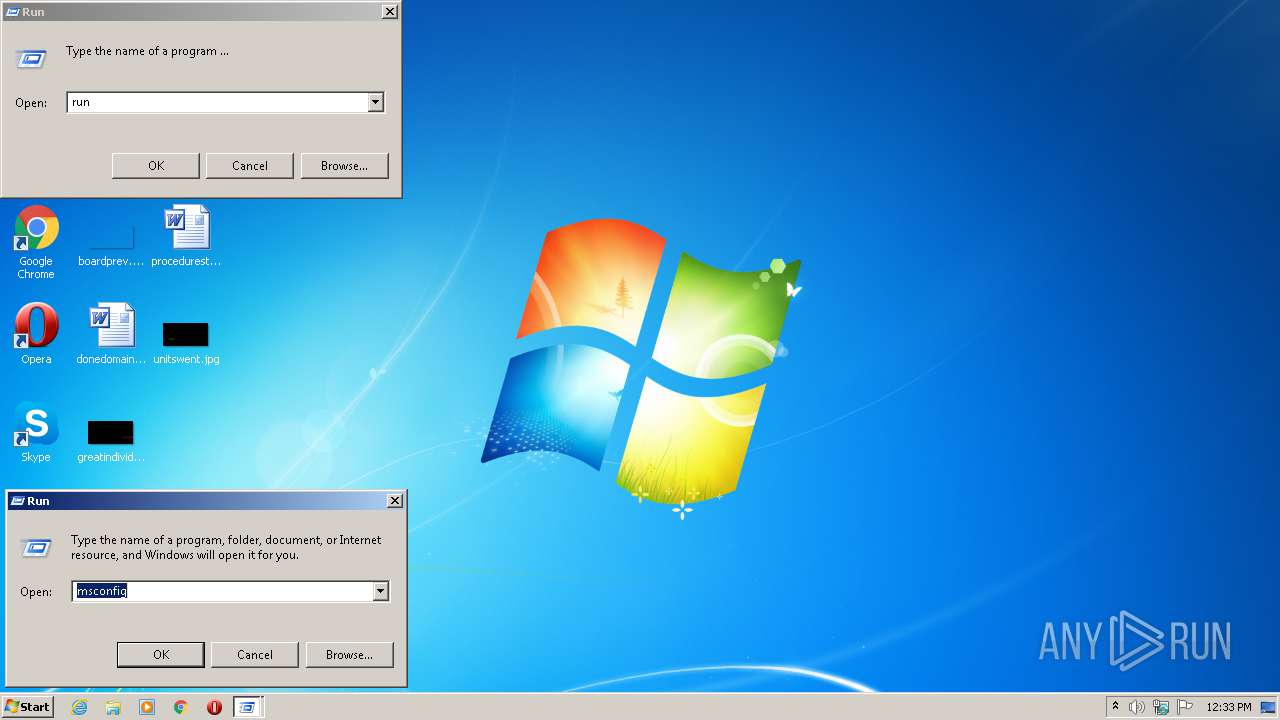
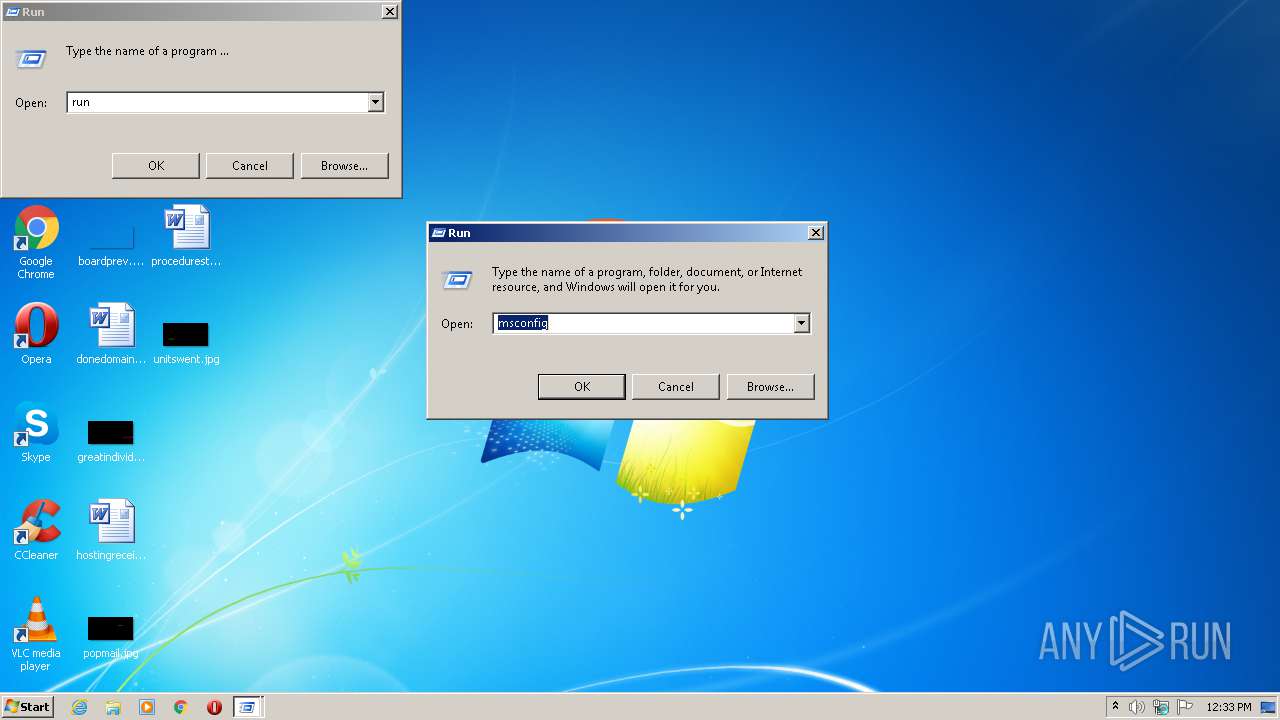
Runs app for hidden code execution
- RUNDLG.EXE (PID: 2168)
SUSPICIOUS
Checks supported languages
- RUNDLG.EXE (PID: 2168)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 744)
- cmd.exe (PID: 2968)
Reads the computer name
- RUNDLG.EXE (PID: 2168)
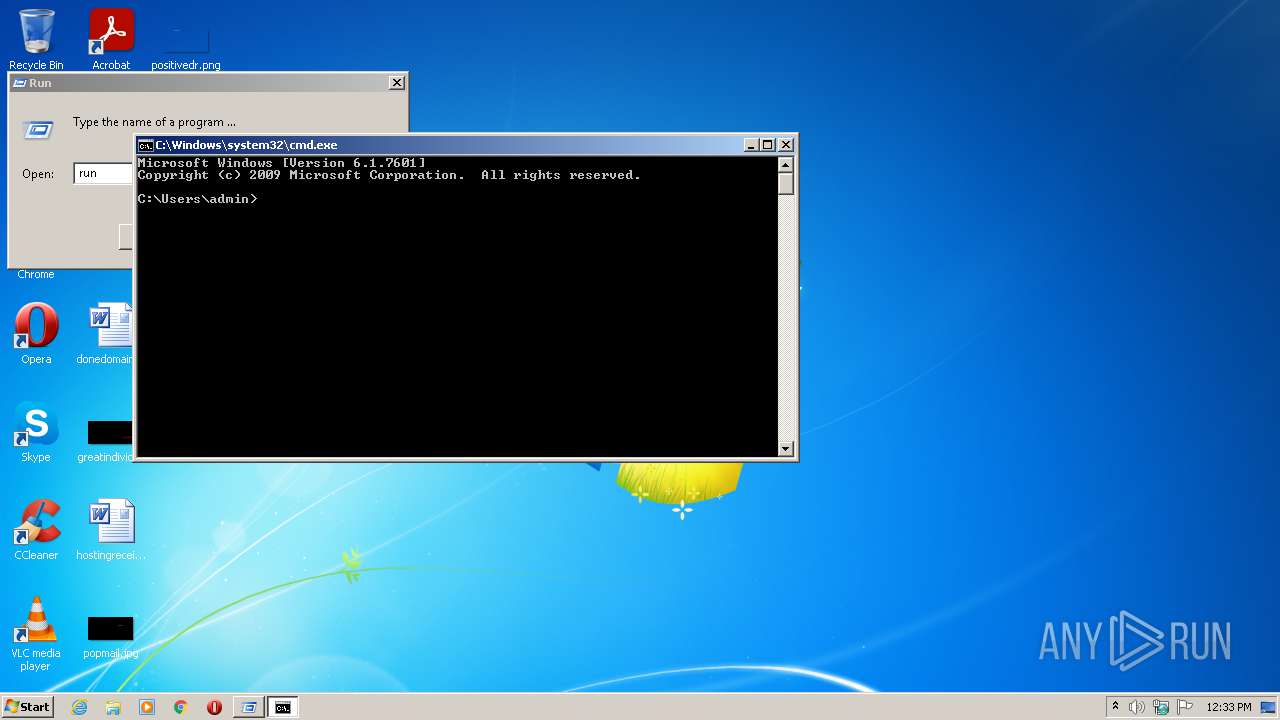
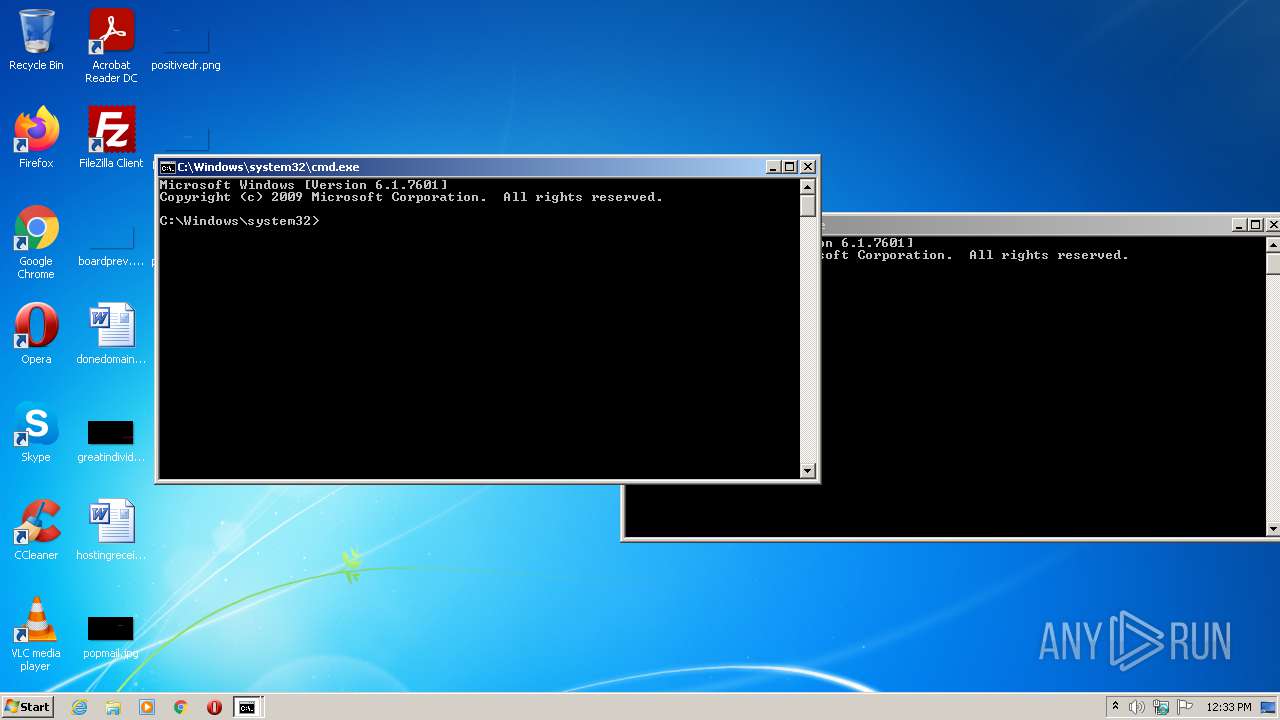
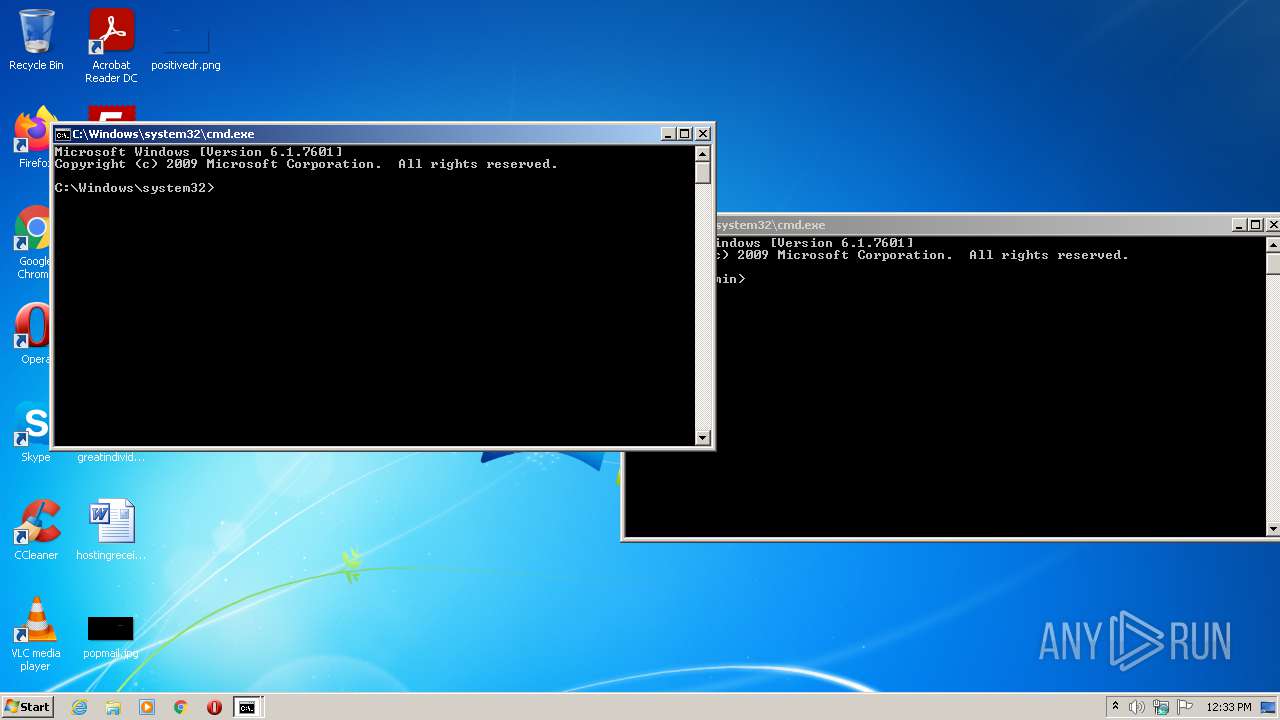
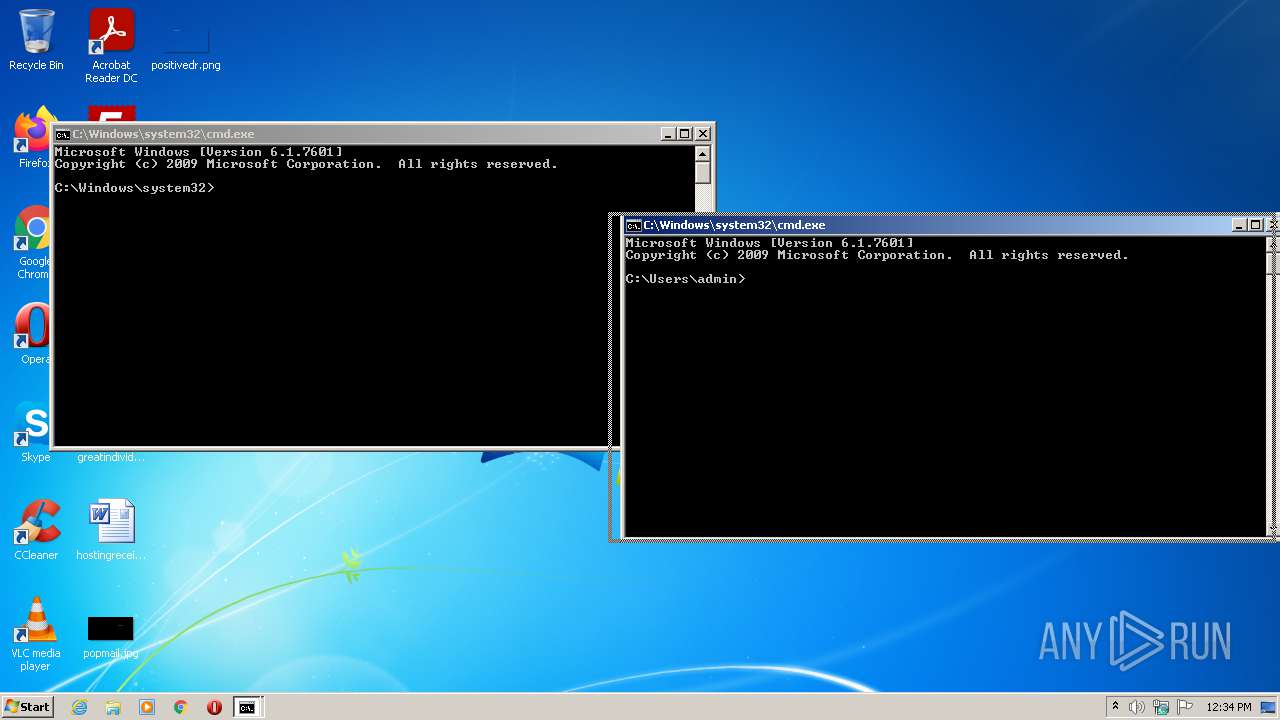
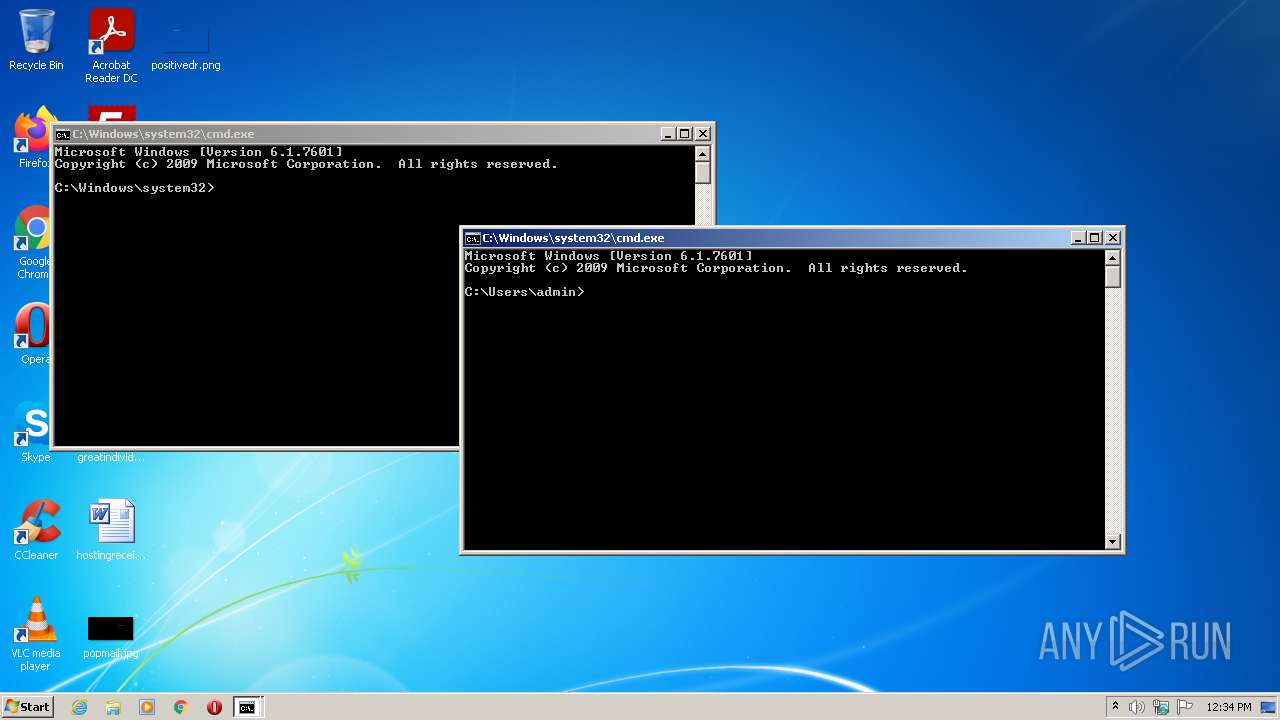
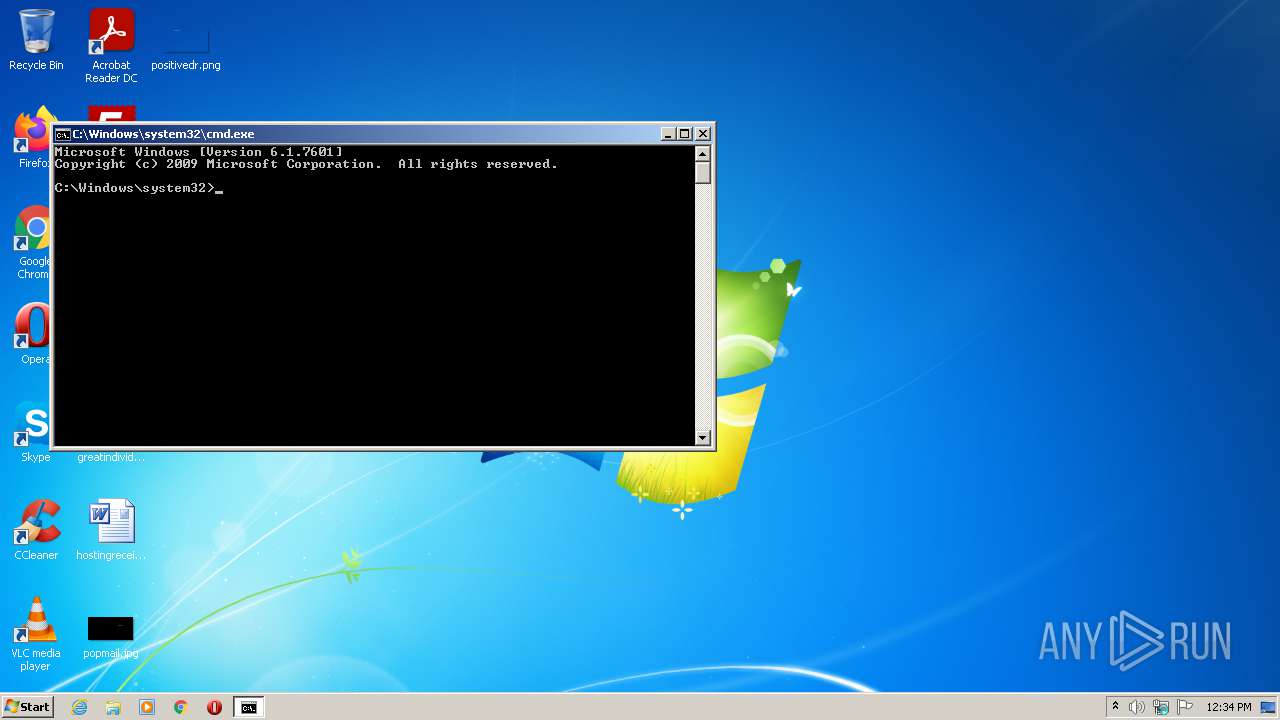
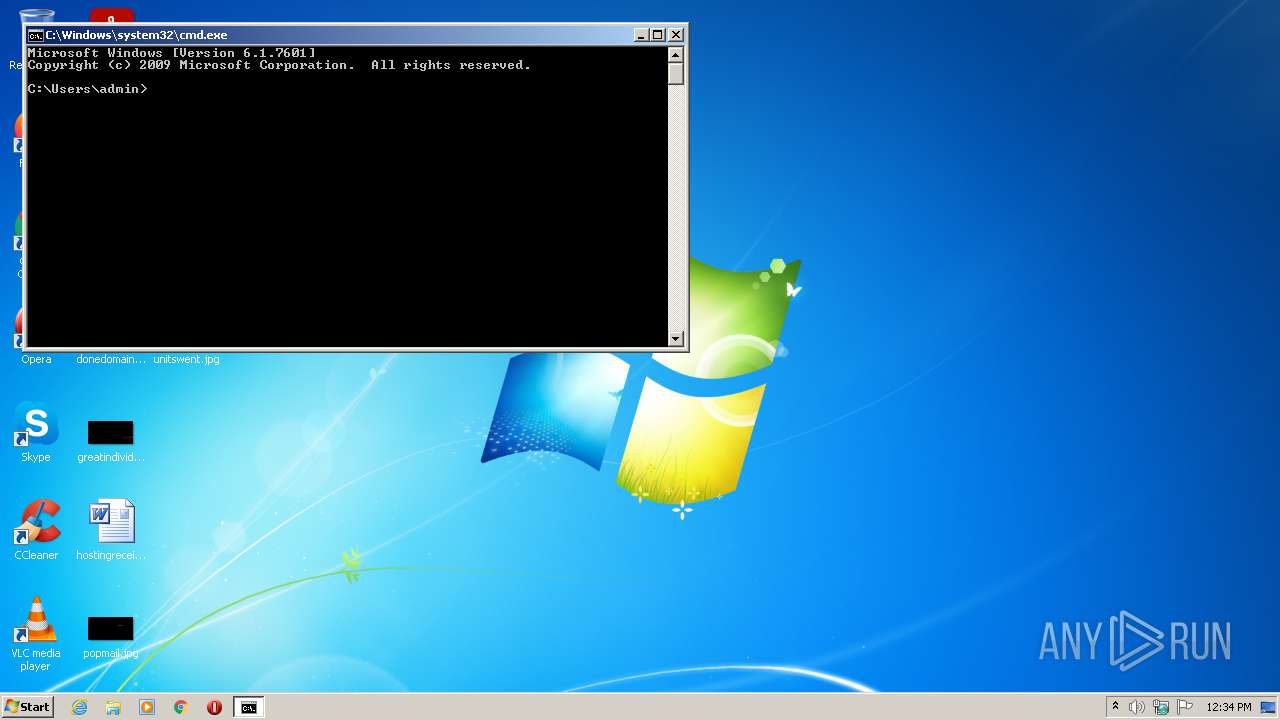
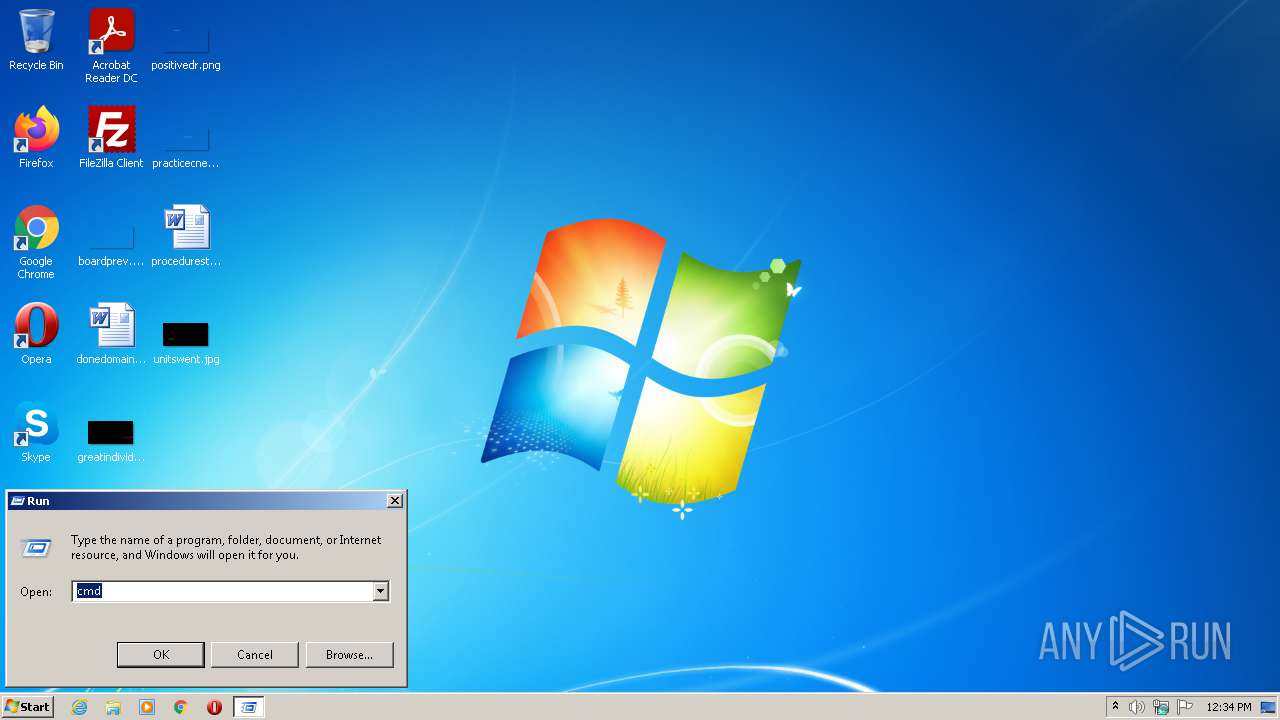
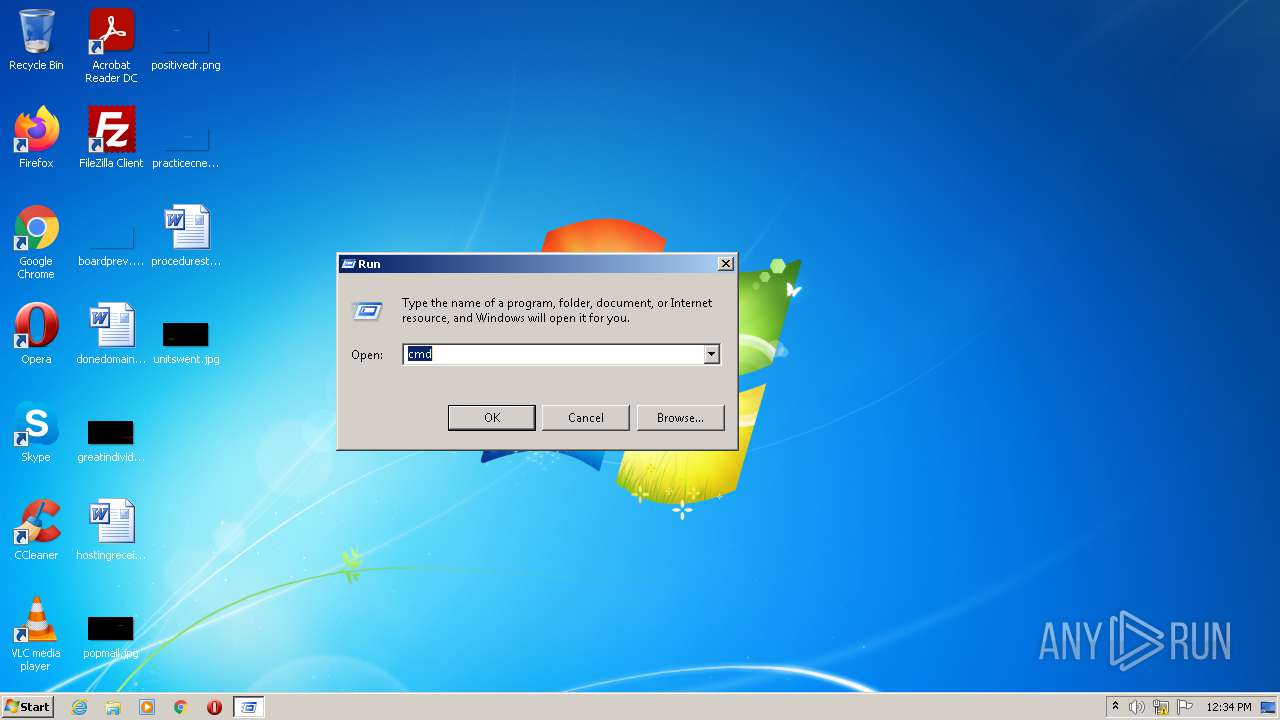
Starts CMD.EXE for commands execution
- RUNDLG.EXE (PID: 2168)
Reads the date of Windows installation
- RUNDLG.EXE (PID: 2168)
INFO
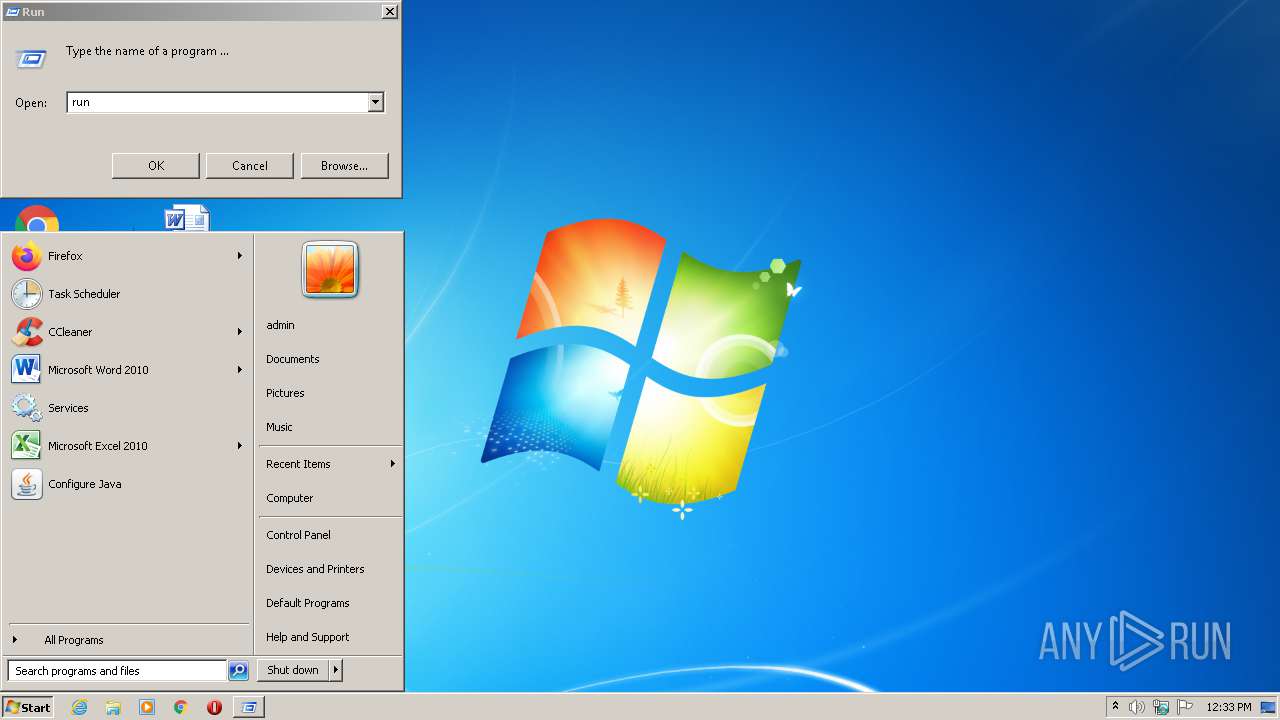
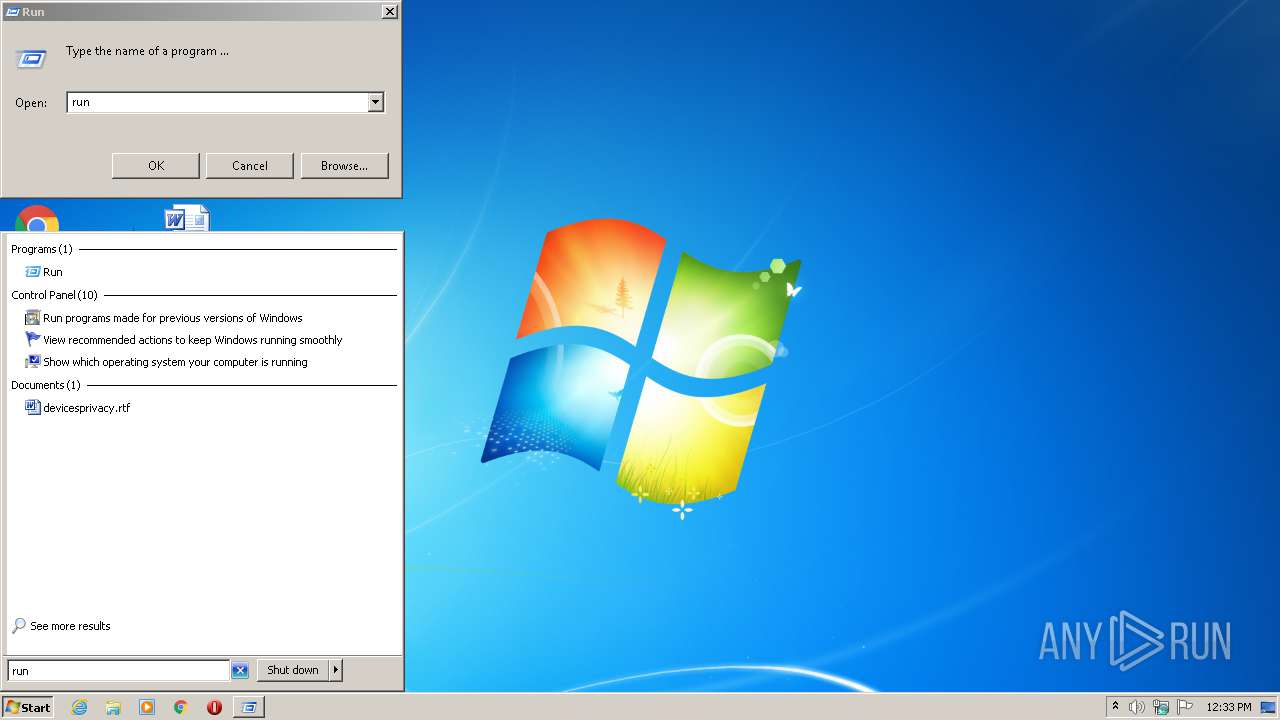
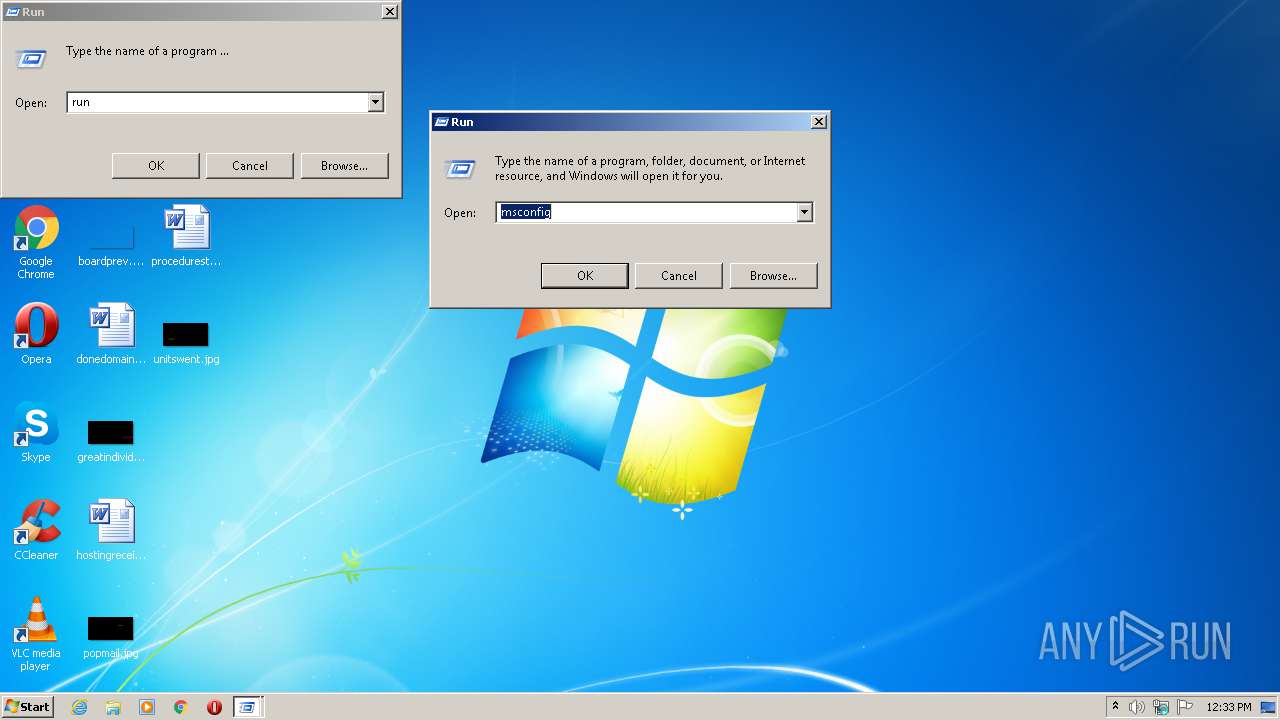
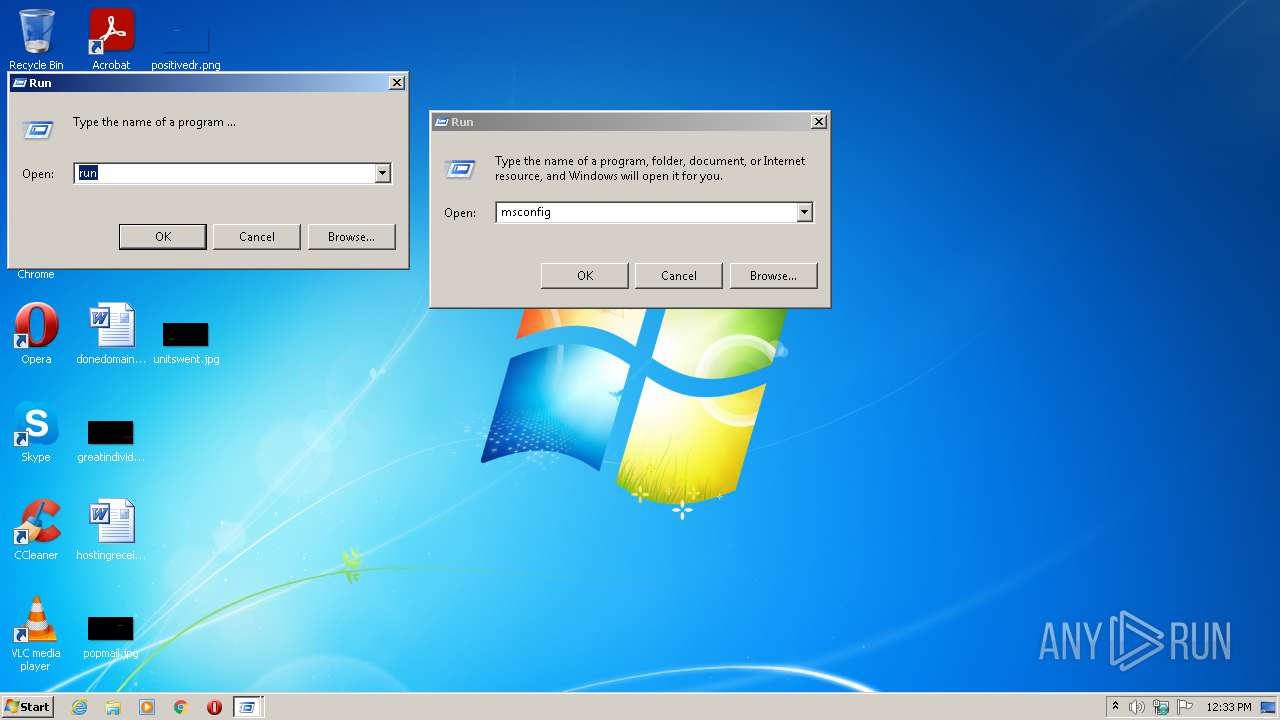
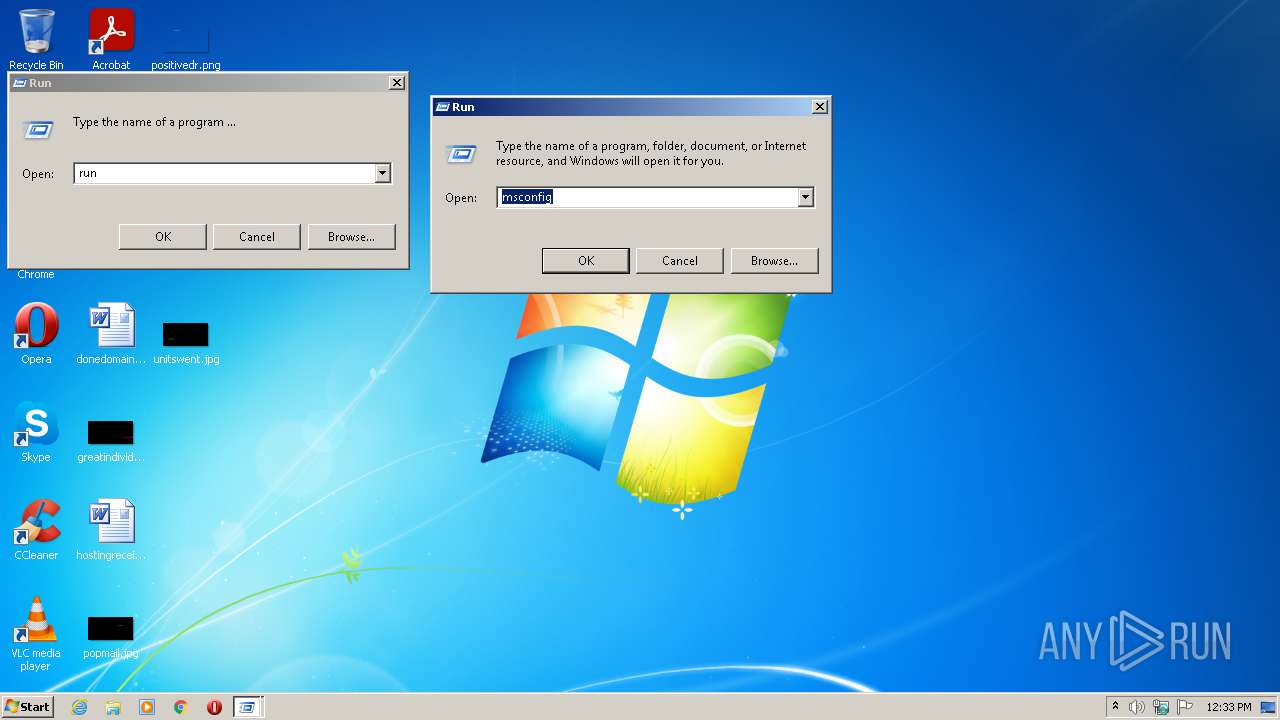
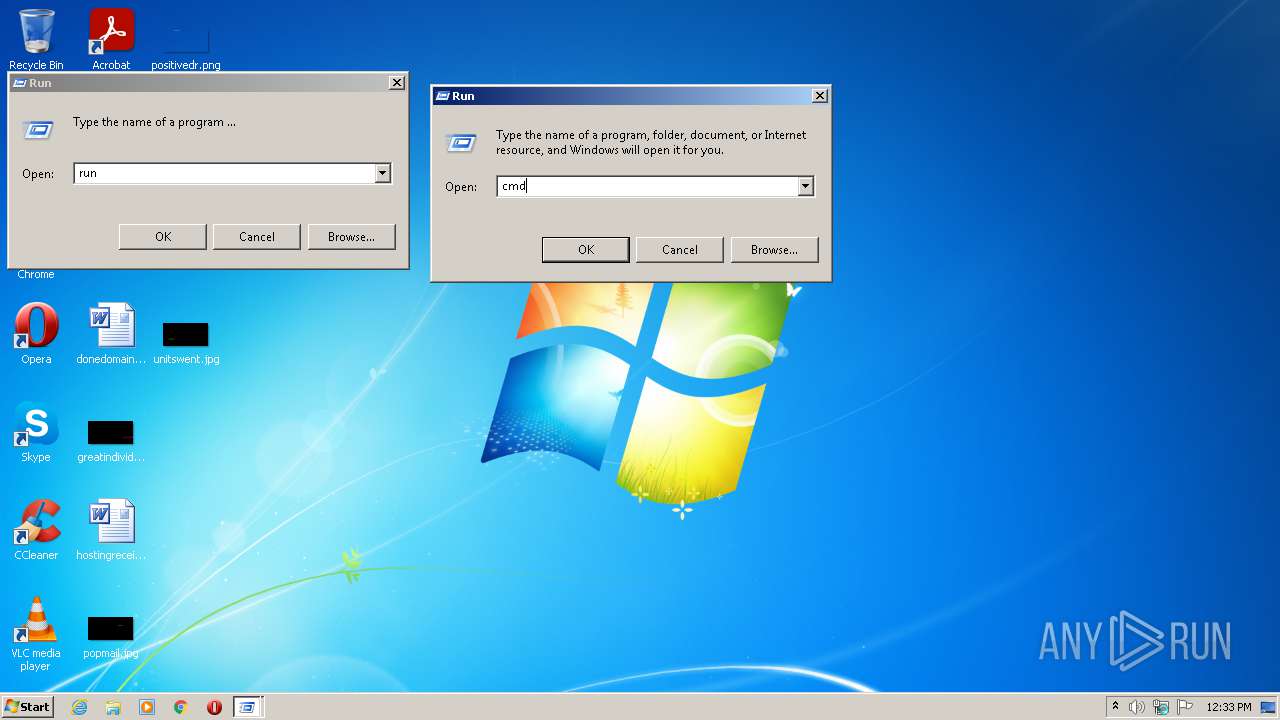
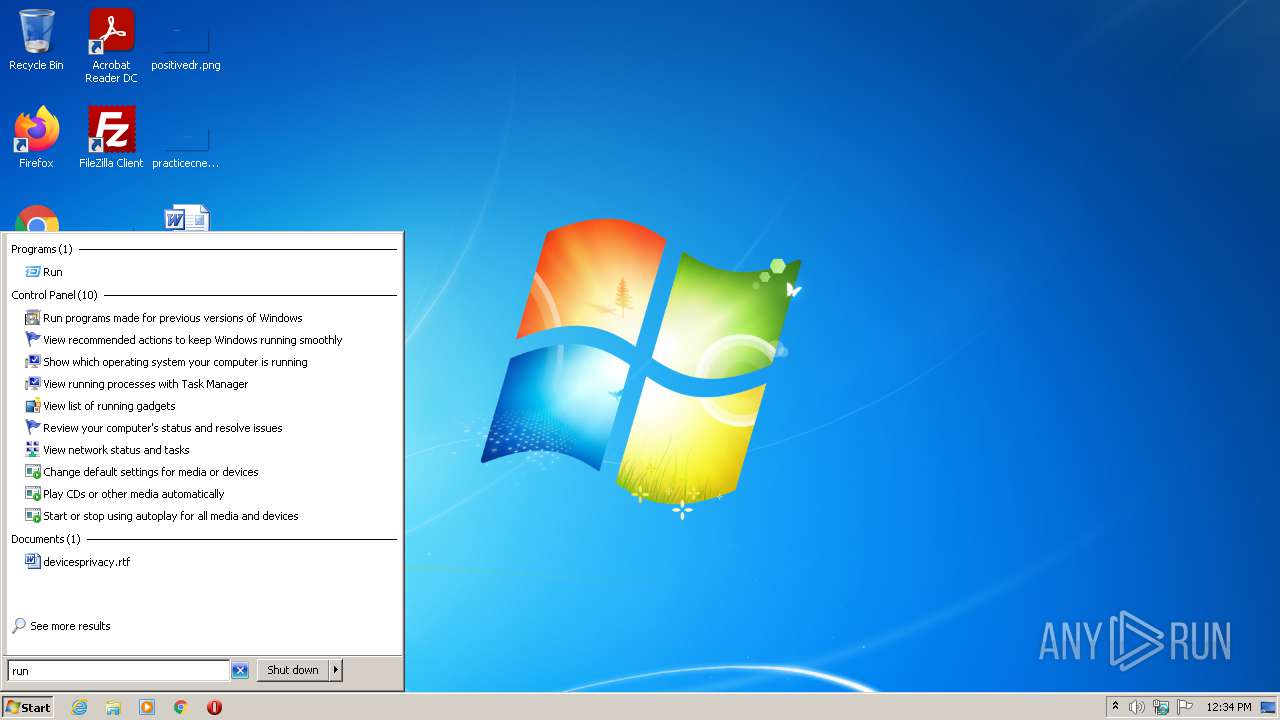
Manual execution by user
- cmd.exe (PID: 2708)
- cmd.exe (PID: 2968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x466f |
| UninitializedDataSize: | - |
| InitializedDataSize: | 8192 |
| CodeSize: | 4096 |
| LinkerVersion: | - |
| PEType: | PE32 |
| TimeStamp: | 1987:09:11 03:35:02+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Sep-1987 01:35:02 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0x4550 |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x014C |
| Checksum: | 0x0002 |
| Initial IP value: | 0x5346 |
| Initial CS value: | 0x2147 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x010B |
| OEM information: | 0x0000 |
| Address of NE header: | 0x0000000C |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 2 |
| Time date stamp: | 11-Sep-1987 01:35:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00004000 | 0x00001000 | 0x00000768 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.46667 |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 744 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | RUNDLG.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2168 | "C:\Users\admin\AppData\Local\Temp\RUNDLG.EXE" | C:\Users\admin\AppData\Local\Temp\RUNDLG.EXE | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2708 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2968 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
801
Read events
733
Write events
68
Delete events
0
Modification events
| (PID) Process: | (2168) RUNDLG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2168) RUNDLG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2168) RUNDLG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2168) RUNDLG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2168) RUNDLG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2168) RUNDLG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2168) RUNDLG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2168) RUNDLG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\pzq.rkr |
Value: 000000000F0000000B000000B3A20500000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF100FB1A96C63D70100000000 | |||
| (PID) Process: | (2168) RUNDLG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003701000063020000154A0D013F0000004A0000008E0F0D004D006900630072006F0073006F00660074002E0049006E007400650072006E00650074004500780070006C006F007200650072002E00440065006600610075006C007400000028003E004000A4E75102B8E651020000000000000000000000000000080274E45102000008026CE25102000000000000D26CFFFFFFFF705911750000000000000000A4E251027C900D75000400000000000008E35102FFFFFFFF38EA7000FFFFFFFF080A7400D80E740030EA7000D4E25102F7AF3D7680D0707614F05102081D3E76E4613E766820700008E351020000000071000000BBF2CB00E8E25102A1693E766820700008E351020000000014E551023F613E766820700008E3510200000400000000800400000026E4510298E351025DA5147726E45102D26E147779A51477D6794D7526E4510210E65102000100006400610072E3510226E451026F0061006D0069006E0067005C006D006900630072006F0073006F0066007400CCE351023400000080E35102DE70310033003300350033003800310030003000F8E551025A000000A0E351021DA71477D6610E02D4E351025A00000010E651025C00000011000000104F7000084F7000F8E55102C4E3510220E40000D7F3CB00D0E351025E903E7620E45102D4E3510203943E760000000064561802FCE35102A9933E7664561802A8E45102D8511802BD933E7600000000D8511802A8E4510204E45102000000006D0000001CC85C004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000094011CE4940100000000000000000000000000000000480B67020000000005000000D80B670200000000340C670230E4940178E494010000000000000000E8B9670205000000200000000100000064666C7464666C7400000000400000000459D8768805015E00000000000000000100000000000000000000000000000000000000E803000000000000FFFFFFFF000000000000000088FD68021CE4940105000000FFFFFFFF0000000000000000AC54D87600000000C054D8768805015E88FD68020000000088FD680205000000D80B67020000000090E6940198E69401E8B96702940A670220000000780B670200000000000000000000000000000000000000000500000000000000010000006C61746E64666C740000000011000000104F7B00084F7B0050E594016CE500004A6E853170E50000426E853124E594015E901D7670E594010CD400006E6E853138E59401929B1D7610D40A024C06000050E5940180CF0A025CE5940111000000104F7B00084F7B0050E59401A0CF0A02C0E50000166E853170E594015E901D76C0E5940174E5940103941D76000000000CD40A029CE59401A9931D760CD40A0248E6940180CF0A02BD931D760000000080CF0A0248E69401A4E59401000000006D0000001CC85C004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000094011CE4940100000000000000000000000000000000480B67020000000005000000D80B670200000000340C670230E4940178E494010000000000000000E8B9670205000000200000000100000064666C7464666C7400000000400000000459D8768805015E00000000000000000100000000000000000000000000000000000000E803000000000000FFFFFFFF000000000000000088FD68021CE4940105000000FFFFFFFF0000000000000000AC54D87600000000C054D8768805015E88FD68020000000088FD680205000000D80B67020000000090E6940198E69401E8B96702940A670220000000780B670200000000000000000000000000000000000000000500000000000000010000006C61746E64666C740000000011000000104F7B00084F7B0050E594016CE500004A6E853170E50000426E853124E594015E901D7670E594010CD400006E6E853138E59401929B1D7610D40A024C06000050E5940180CF0A025CE5940111000000104F7B00084F7B0050E59401A0CF0A02C0E50000166E853170E594015E901D76C0E5940174E5940103941D76000000000CD40A029CE59401A9931D760CD40A0248E6940180CF0A02BD931D760000000080CF0A0248E69401A4E59401 | |||
| (PID) Process: | (2168) RUNDLG.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report