| File name: | 2025-05-18_fadd4bb2d8a84763827c701643c7cedd_black-basta_elex_gcleaner_hijackloader |
| Full analysis: | https://app.any.run/tasks/73f6c01b-6da0-428c-bb79-5aa9fb73bd82 |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 22:13:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | FADD4BB2D8A84763827C701643C7CEDD |
| SHA1: | 57AC027F873007EFC8935341D5E9D1BDD0A30887 |
| SHA256: | F754AABDCB2E6EA31AA26C3CA75F606B8FC81690FA9D86AD48DC900300148399 |
| SSDEEP: | 98304:zSYpVEm5sn6gNEkdfaTgmHihuRB3FKFfpRBVnf9D0ks+Zo8Y1F2qaVhKffn7YAxr:taABbPzJKrmwX6hLZ |
MALICIOUS
CANBIS mutex has been found
- 2025-05-18_fadd4bb2d8a84763827c701643c7cedd_black-basta_elex_gcleaner_hijackloader.exe (PID: 7420)
SUSPICIOUS
Executable content was dropped or overwritten
- 2025-05-18_fadd4bb2d8a84763827c701643c7cedd_black-basta_elex_gcleaner_hijackloader.exe (PID: 7420)
Drops 7-zip archiver for unpacking
- 2025-05-18_fadd4bb2d8a84763827c701643c7cedd_black-basta_elex_gcleaner_hijackloader.exe (PID: 7420)
Reads security settings of Internet Explorer
- 2025-05-18_fadd4bb2d8a84763827c701643c7cedd_black-basta_elex_gcleaner_hijackloader.exe (PID: 7420)
INFO
The sample compiled with english language support
- 2025-05-18_fadd4bb2d8a84763827c701643c7cedd_black-basta_elex_gcleaner_hijackloader.exe (PID: 7420)
Reads the computer name
- 2025-05-18_fadd4bb2d8a84763827c701643c7cedd_black-basta_elex_gcleaner_hijackloader.exe (PID: 7420)
Checks supported languages
- 2025-05-18_fadd4bb2d8a84763827c701643c7cedd_black-basta_elex_gcleaner_hijackloader.exe (PID: 7420)
- 3074103123.exe (PID: 7484)
Process checks computer location settings
- 2025-05-18_fadd4bb2d8a84763827c701643c7cedd_black-basta_elex_gcleaner_hijackloader.exe (PID: 7420)
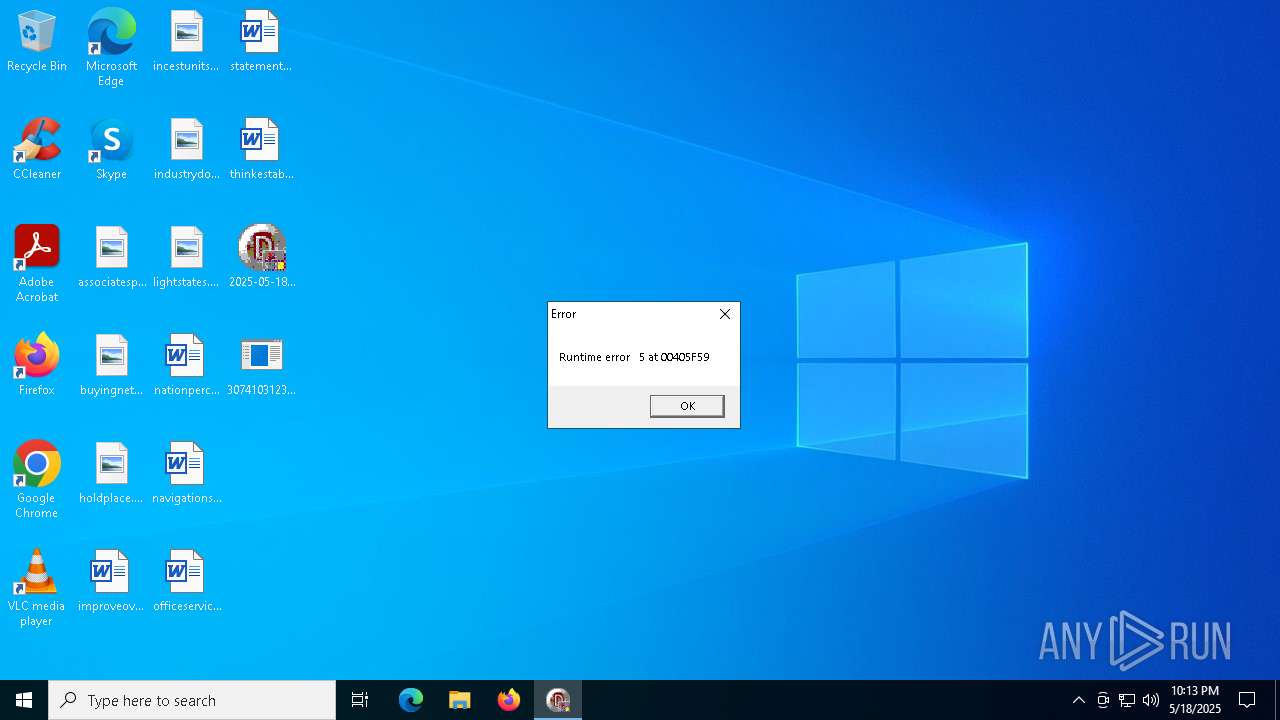
Failed to create an executable file in Windows directory
- 2025-05-18_fadd4bb2d8a84763827c701643c7cedd_black-basta_elex_gcleaner_hijackloader.exe (PID: 7420)
Checks proxy server information
- slui.exe (PID: 7816)
Reads the software policy settings
- slui.exe (PID: 7816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (57.2) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 5 (38.8) |
| .exe | | | Win32 Executable Delphi generic (1.2) |
| .scr | | | Windows screen saver (1.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 46080 |
| InitializedDataSize: | 7680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc254 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
123
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7420 | "C:\Users\admin\Desktop\2025-05-18_fadd4bb2d8a84763827c701643c7cedd_black-basta_elex_gcleaner_hijackloader.exe" | C:\Users\admin\Desktop\2025-05-18_fadd4bb2d8a84763827c701643c7cedd_black-basta_elex_gcleaner_hijackloader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 5 Modules
| |||||||||||||||
| 7484 | "C:\Users\admin\Desktop\3074103123.exe" | C:\Users\admin\Desktop\3074103123.exe | — | 2025-05-18_fadd4bb2d8a84763827c701643c7cedd_black-basta_elex_gcleaner_hijackloader.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 0 Version: 23.01 Modules
| |||||||||||||||
| 7492 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 3074103123.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7816 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 025
Read events
4 025
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7420 | 2025-05-18_fadd4bb2d8a84763827c701643c7cedd_black-basta_elex_gcleaner_hijackloader.exe | C:\Users\admin\Desktop\1942300141.exe | executable | |
MD5:FADD4BB2D8A84763827C701643C7CEDD | SHA256:F754AABDCB2E6EA31AA26C3CA75F606B8FC81690FA9D86AD48DC900300148399 | |||
| 7420 | 2025-05-18_fadd4bb2d8a84763827c701643c7cedd_black-basta_elex_gcleaner_hijackloader.exe | C:\Users\admin\Desktop\3074103123.exe | executable | |
MD5:9A1DD1D96481D61934DCC2D568971D06 | SHA256:8CEBB25E240DB3B6986FCAED6BC0B900FA09DAD763A56FB71273529266C5C525 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
20
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7272 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7816 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
uk.undernet.org |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |