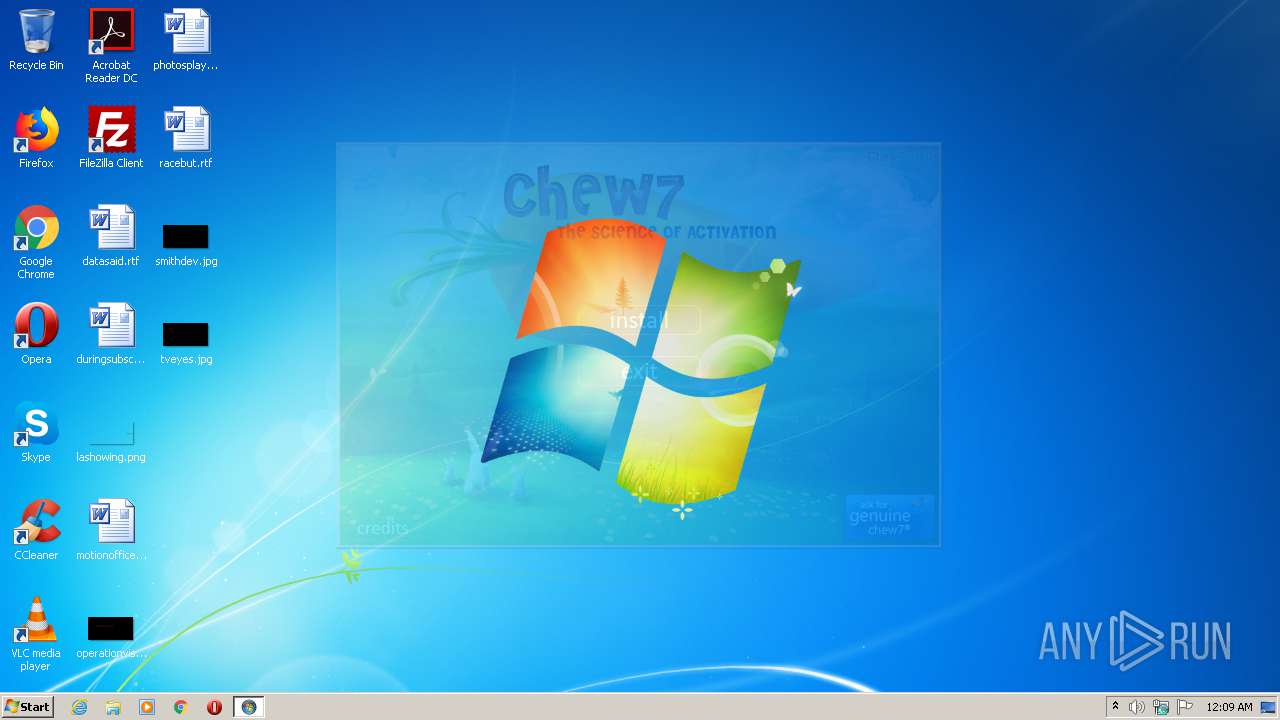
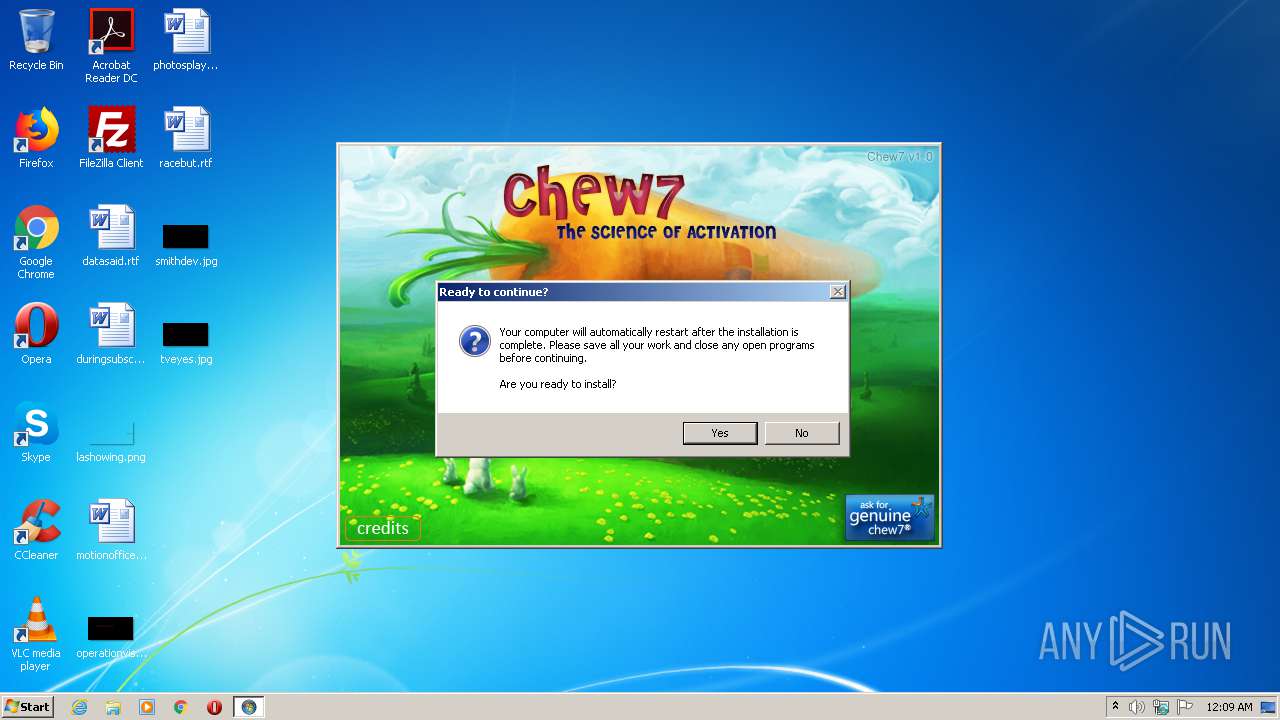
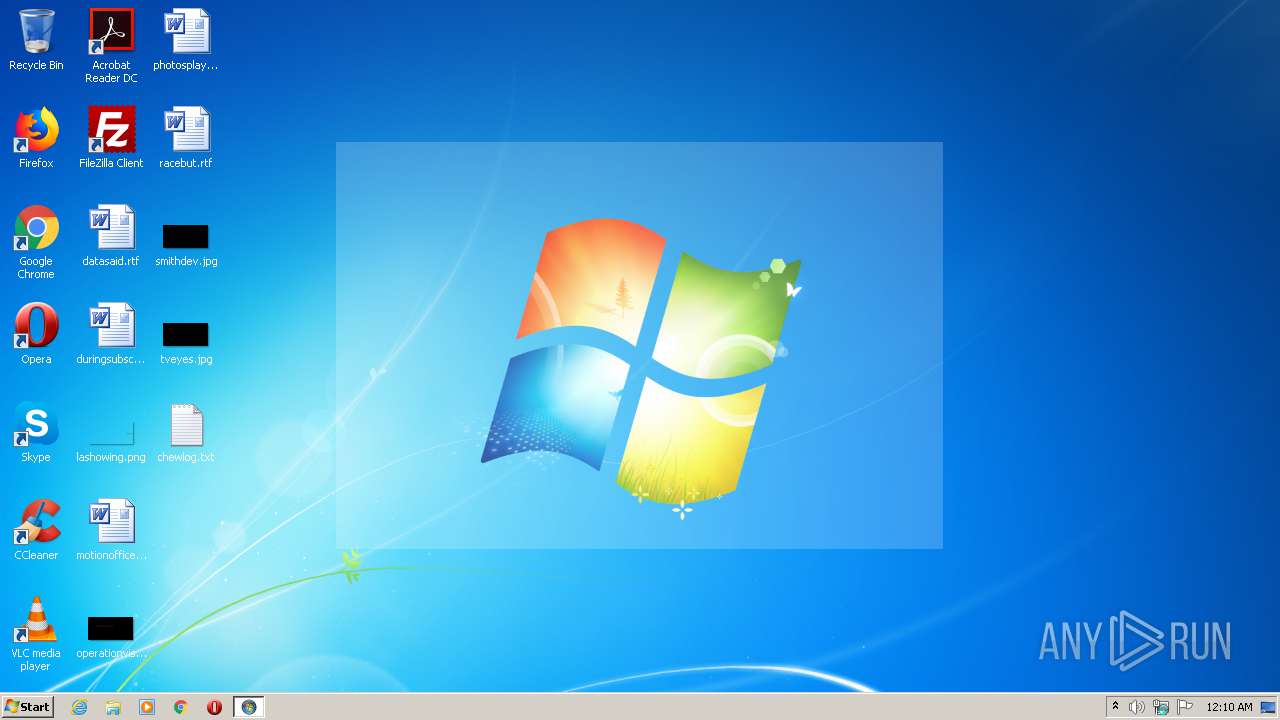
| File name: | Chew7.exe |
| Full analysis: | https://app.any.run/tasks/adbb37fc-b827-499f-99eb-1f66dd539413 |
| Verdict: | Malicious activity |
| Analysis date: | March 15, 2021, 00:09:04 |
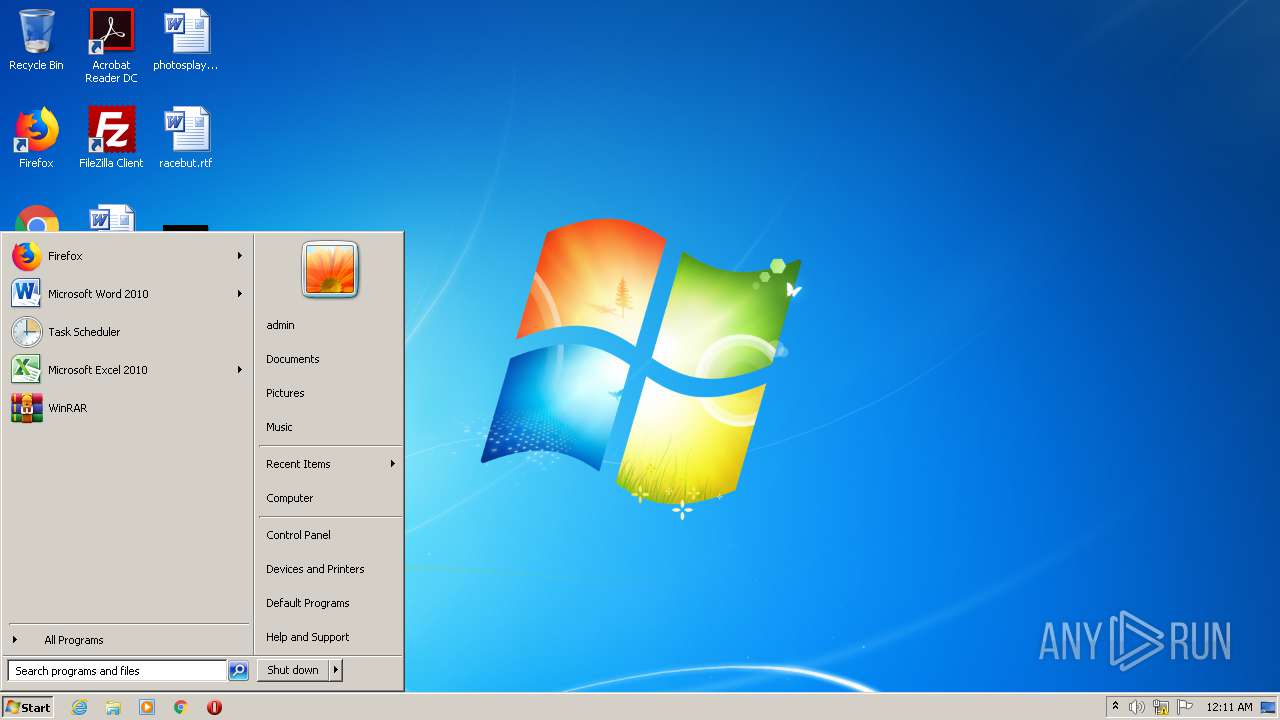
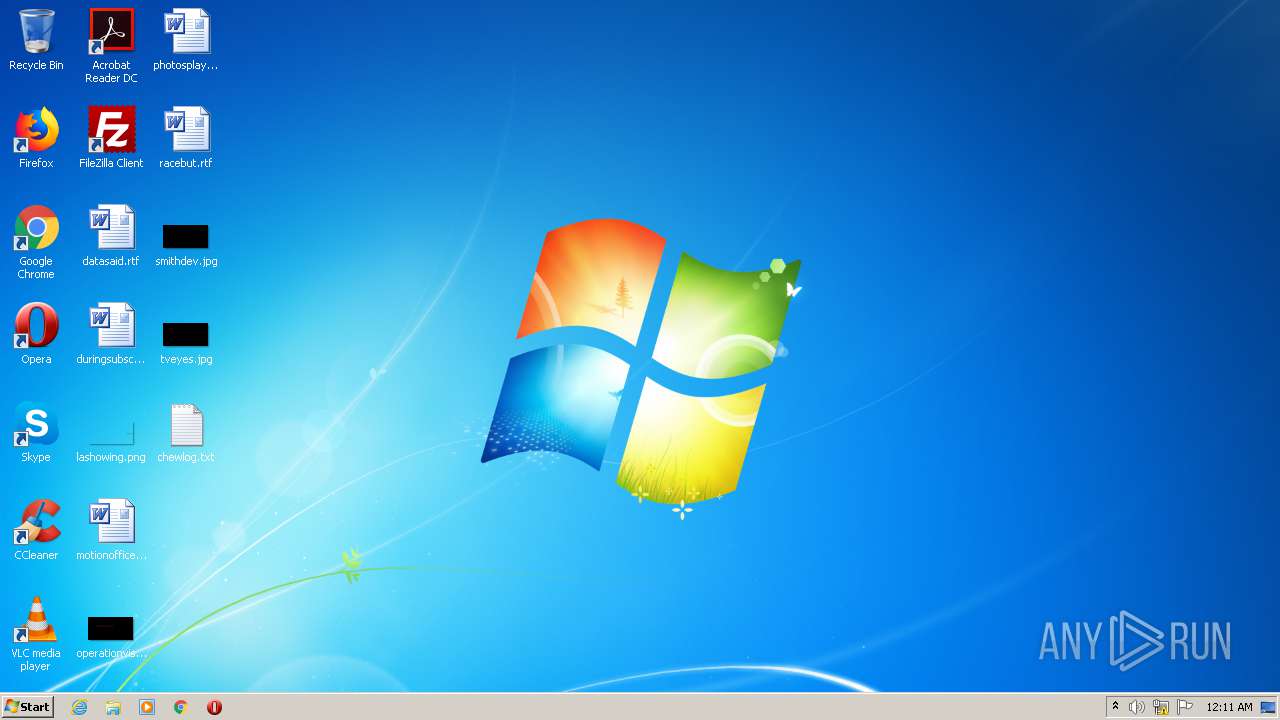
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 7E91139648B5A14B483486C053D5F4D0 |
| SHA1: | 78EC7FCB573D3EBB9B5110F9319380CC4B510B12 |
| SHA256: | F747A7679964D088E75FA60241238669104107280FEACF29CD0041F1F82E16B7 |
| SSDEEP: | 49152:jA3alq/Auj1YD/tmtPIr1PrYD/tmtPIr1Pu:jaY0tgrVY0tgr |
MALICIOUS
Uses Task Scheduler to run other applications
- Chew7.exe (PID: 3452)
- cmd.exe (PID: 4092)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2980)
- schtasks.exe (PID: 1388)
- schtasks.exe (PID: 3024)
- schtasks.exe (PID: 1752)
- schtasks.exe (PID: 2432)
Drops executable file immediately after starts
- hale.exe (PID: 3880)
- bump.exe (PID: 1700)
- bump.exe (PID: 1880)
- bump.exe (PID: 688)
- bump.exe (PID: 1536)
- bump.exe (PID: 3316)
- bump.exe (PID: 2636)
- bump.exe (PID: 2272)
- bump.exe (PID: 344)
- bump.exe (PID: 3792)
- bump.exe (PID: 1368)
- bump.exe (PID: 2124)
- bump.exe (PID: 2104)
- bump.exe (PID: 548)
- bump.exe (PID: 3976)
- bump.exe (PID: 4028)
- bump.exe (PID: 2472)
Application was dropped or rewritten from another process
- hale.exe (PID: 3880)
- bump.exe (PID: 2816)
- flick.exe (PID: 1844)
- bump.exe (PID: 1700)
- flick.exe (PID: 3148)
- bump.exe (PID: 4080)
- bump.exe (PID: 1344)
- flick.exe (PID: 2652)
- bump.exe (PID: 2204)
- bump.exe (PID: 1880)
- bump.exe (PID: 688)
- bump.exe (PID: 1452)
- bump.exe (PID: 1248)
- bump.exe (PID: 1536)
- bump.exe (PID: 3504)
- bump.exe (PID: 2784)
- bump.exe (PID: 3316)
- bump.exe (PID: 1768)
- bump.exe (PID: 3868)
- bump.exe (PID: 2636)
- flick.exe (PID: 3592)
- bump.exe (PID: 2272)
- bump.exe (PID: 3812)
- bump.exe (PID: 3404)
- bump.exe (PID: 3792)
- bump.exe (PID: 344)
- bump.exe (PID: 1940)
- flick.exe (PID: 756)
- flick.exe (PID: 444)
- bump.exe (PID: 1368)
- bump.exe (PID: 1332)
- bump.exe (PID: 2104)
- bump.exe (PID: 2052)
- bump.exe (PID: 2124)
- bump.exe (PID: 2528)
- flick.exe (PID: 3088)
- bump.exe (PID: 548)
- bump.exe (PID: 2712)
- bump.exe (PID: 4028)
- bump.exe (PID: 2696)
- bump.exe (PID: 3976)
- flick.exe (PID: 2192)
- bump.exe (PID: 2472)
- flick.exe (PID: 1344)
Loads dropped or rewritten executable
- schtasks.exe (PID: 1388)
- hale.exe (PID: 3880)
- conhost.exe (PID: 3420)
- conhost.exe (PID: 1000)
- find.exe (PID: 3816)
- wmiprvse.exe (PID: 3052)
- schtasks.exe (PID: 3024)
- find.exe (PID: 592)
- cmd.exe (PID: 3996)
- conhost.exe (PID: 3564)
- reg.exe (PID: 2728)
- schtasks.exe (PID: 2980)
- reg.exe (PID: 1780)
- reg.exe (PID: 1828)
- cmd.exe (PID: 4092)
- taskkill.exe (PID: 3020)
- taskkill.exe (PID: 2240)
- fc.exe (PID: 4000)
- reg.exe (PID: 760)
- find.exe (PID: 1760)
- find.exe (PID: 3004)
- Chew7.exe (PID: 3452)
- find.exe (PID: 2400)
- tasklist.exe (PID: 1512)
- cmd.exe (PID: 3520)
- conhost.exe (PID: 304)
- find.exe (PID: 3372)
- fc.exe (PID: 1512)
- takeown.exe (PID: 3004)
- reg.exe (PID: 3616)
- cmd.exe (PID: 1004)
- reg.exe (PID: 3304)
- takeown.exe (PID: 3588)
- reg.exe (PID: 2400)
- host.exe (PID: 4020)
- find.exe (PID: 2452)
- takeown.exe (PID: 2760)
- cmd.exe (PID: 3876)
- reg.exe (PID: 1860)
- fc.exe (PID: 3944)
- cmd.exe (PID: 3508)
- conhost.exe (PID: 1744)
- reg.exe (PID: 3936)
- find.exe (PID: 592)
- conhost.exe (PID: 1160)
- takeown.exe (PID: 3388)
- fc.exe (PID: 4052)
- fc.exe (PID: 2304)
- find.exe (PID: 496)
- find.exe (PID: 1504)
- find.exe (PID: 3456)
- find.exe (PID: 1504)
- find.exe (PID: 4040)
- takeown.exe (PID: 2132)
- find.exe (PID: 3796)
- find.exe (PID: 2548)
- find.exe (PID: 2708)
- fc.exe (PID: 2440)
- find.exe (PID: 960)
- fc.exe (PID: 960)
- takeown.exe (PID: 2120)
- find.exe (PID: 2160)
- find.exe (PID: 2664)
- find.exe (PID: 3808)
- find.exe (PID: 3520)
- takeown.exe (PID: 3056)
- fc.exe (PID: 3316)
- fc.exe (PID: 3800)
- find.exe (PID: 4040)
- find.exe (PID: 584)
- find.exe (PID: 2428)
- find.exe (PID: 3856)
- takeown.exe (PID: 2684)
- find.exe (PID: 3724)
- find.exe (PID: 2476)
- find.exe (PID: 944)
- find.exe (PID: 3148)
- find.exe (PID: 2328)
- fc.exe (PID: 4004)
- takeown.exe (PID: 2428)
- find.exe (PID: 2064)
- fc.exe (PID: 3724)
- takeown.exe (PID: 1480)
- cmd.exe (PID: 2364)
- find.exe (PID: 3552)
- schtasks.exe (PID: 1752)
- reg.exe (PID: 3152)
- schtasks.exe (PID: 2432)
- find.exe (PID: 3888)
- reg.exe (PID: 2800)
- reg.exe (PID: 3892)
- find.exe (PID: 4088)
- find.exe (PID: 2644)
- reg.exe (PID: 3840)
- DllHost.exe (PID: 2552)
- fc.exe (PID: 2708)
- reg.exe (PID: 3248)
- host.exe (PID: 4024)
- LogonUI.exe (PID: 1388)
- AUDIODG.EXE (PID: 1708)
Changes the autorun value in the registry
- reg.exe (PID: 3840)
SUSPICIOUS
Uses TASKKILL.EXE to kill process
- Chew7.exe (PID: 3452)
Creates files in the Windows directory
- Chew7.exe (PID: 3452)
- cmd.exe (PID: 4092)
Executable content was dropped or overwritten
- Chew7.exe (PID: 3452)
- hale.exe (PID: 3880)
- cmd.exe (PID: 4092)
- bump.exe (PID: 2816)
- bump.exe (PID: 1700)
- bump.exe (PID: 4080)
- bump.exe (PID: 1344)
- bump.exe (PID: 2204)
- bump.exe (PID: 1880)
- bump.exe (PID: 3504)
- bump.exe (PID: 688)
- bump.exe (PID: 2784)
- bump.exe (PID: 1452)
- bump.exe (PID: 1248)
- bump.exe (PID: 1536)
- bump.exe (PID: 3316)
- bump.exe (PID: 3868)
- bump.exe (PID: 2636)
- bump.exe (PID: 2272)
- bump.exe (PID: 1768)
- bump.exe (PID: 3812)
- bump.exe (PID: 3404)
- bump.exe (PID: 3792)
- bump.exe (PID: 344)
- bump.exe (PID: 1940)
- bump.exe (PID: 1368)
- bump.exe (PID: 1332)
- bump.exe (PID: 2528)
- bump.exe (PID: 2124)
- bump.exe (PID: 2104)
- bump.exe (PID: 2052)
- bump.exe (PID: 548)
- bump.exe (PID: 2712)
- bump.exe (PID: 4028)
- bump.exe (PID: 3976)
- bump.exe (PID: 2472)
- bump.exe (PID: 2696)
Drops a file with too old compile date
- Chew7.exe (PID: 3452)
- hale.exe (PID: 3880)
- cmd.exe (PID: 4092)
- bump.exe (PID: 4080)
- bump.exe (PID: 1344)
- bump.exe (PID: 1700)
- bump.exe (PID: 1368)
- bump.exe (PID: 1332)
- bump.exe (PID: 2528)
- bump.exe (PID: 2052)
- bump.exe (PID: 2124)
- bump.exe (PID: 2104)
Drops a file that was compiled in debug mode
- hale.exe (PID: 3880)
- cmd.exe (PID: 4092)
- bump.exe (PID: 2816)
- bump.exe (PID: 1700)
- bump.exe (PID: 4080)
- bump.exe (PID: 1344)
- bump.exe (PID: 2204)
- bump.exe (PID: 1880)
- bump.exe (PID: 1248)
- bump.exe (PID: 1452)
- bump.exe (PID: 688)
- bump.exe (PID: 2784)
- bump.exe (PID: 1536)
- bump.exe (PID: 3504)
- bump.exe (PID: 3316)
- bump.exe (PID: 3868)
- bump.exe (PID: 1768)
- bump.exe (PID: 2636)
- bump.exe (PID: 3812)
- bump.exe (PID: 2272)
- bump.exe (PID: 3404)
- bump.exe (PID: 344)
- bump.exe (PID: 3792)
- bump.exe (PID: 1940)
- bump.exe (PID: 1332)
- bump.exe (PID: 1368)
- bump.exe (PID: 2528)
- bump.exe (PID: 2052)
- bump.exe (PID: 2124)
- bump.exe (PID: 2104)
- bump.exe (PID: 2712)
- bump.exe (PID: 548)
- bump.exe (PID: 3976)
- bump.exe (PID: 2696)
- bump.exe (PID: 4028)
- bump.exe (PID: 2472)
Starts CMD.EXE for commands execution
- hale.exe (PID: 3880)
- cmd.exe (PID: 4092)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 4092)
- cmd.exe (PID: 1004)
- cmd.exe (PID: 3508)
- cmd.exe (PID: 3996)
- cmd.exe (PID: 3520)
Application launched itself
- cmd.exe (PID: 4092)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 4092)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 4092)
Creates files in the program directory
- icacls.exe (PID: 3792)
- cmd.exe (PID: 4092)
- icacls.exe (PID: 2476)
- icacls.exe (PID: 2432)
- icacls.exe (PID: 3720)
- icacls.exe (PID: 2220)
- icacls.exe (PID: 3200)
- icacls.exe (PID: 2292)
- icacls.exe (PID: 3592)
- icacls.exe (PID: 1828)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (43.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (16.2) |
| .exe | | | UPX compressed Win32 Executable (15.9) |
| .exe | | | Win32 EXE Yoda's Crypter (15.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:07:14 08:31:36+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 1565184 |
| InitializedDataSize: | 108032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x18017e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.6.7.3 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | The Science of Activation |
| FileVersion: | 0.6.7.3 |
| InternalName: | Chew7.exe |
| LegalCopyright: | © Chew7. All rights reserved. |
| OriginalFileName: | Chew7.exe |
| ProductName: | Chew7 v1.0 |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jul-2010 06:31:36 |
| FileDescription: | The Science of Activation |
| FileVersion: | 0.6.7.3 |
| InternalName: | Chew7.exe |
| LegalCopyright: | © Chew7. All rights reserved. |
| OriginalFilename: | Chew7.exe |
| ProductName: | Chew7 v1.0 |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 0.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 14-Jul-2010 06:31:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0017E184 | 0x0017E200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.9847 |
.rsrc | 0x00182000 | 0x0001A3B8 | 0x0001A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.79041 |
.reloc | 0x0019E000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92305 | 1141 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 6.21266 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 7.99412 | 88576 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 5.49495 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.65126 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.57475 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.57444 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
219
Monitored processes
181
Malicious processes
23
Suspicious processes
41
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | \??\C:\Windows\system32\conhost.exe "-12627258831763359859-1983815570-1808791818-1746300248544117490106755955293262070" | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 344 | bump -s:xC3:x74:x61 -r:xC3:x90:x90 -o 32\systemcpl.dll | C:\Users\admin\AppData\Local\Temp\B518.tmp\bump.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 352 | ICACLS "C:\Windows\System32" /restore "C:\ProgramData\Microsoft\Windows\Pending\slmgr.vbs.acl" | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 444 | flick.exe /h /q /c /m /r "C:\ProgramData\Microsoft\Windows\Pending\5883.lck" "C:\Windows\System32\slui.exe" | C:\Users\admin\AppData\Local\Temp\B518.tmp\flick.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 496 | FIND "changed" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 496 | FIND "changed" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 548 | bump -s:xFF:x15:x78:x10:x2E:x02 -r:xFF:x15:x5C:x10:x2E:x02 -o 32\sppuinotify.dll | C:\Users\admin\AppData\Local\Temp\B518.tmp\bump.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 | |||||||||||||||
| 572 | ICACLS "C:\Windows\winsxs\Temp\PendingRenames" /GRANT *S-1-1-0:F | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | FIND "changed" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 592 | FIND "Chew7.exe" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
668
Read events
636
Write events
32
Delete events
0
Modification events
| (PID) Process: | (4020) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (4020) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (4020) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (4020) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (4020) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (4020) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (4020) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (4020) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (4020) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENESW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (4020) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
71
Suspicious files
9
Text files
41
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3880 | hale.exe | C:\Users\admin\AppData\Local\Temp\B518.tmp\hale.cmd | text | |
MD5:1F44D34DE408D88C7C7C430D9C07F0FE | SHA256:499A44E0A92AE348567408E3331BB636899B415657B02C4C94CF2AB41DD7EF07 | |||
| 3452 | Chew7.exe | C:\Windows\system32\hale.exe | executable | |
MD5:F8546857FA2D2E6C9D377D0A840BB1B2 | SHA256:8DF72CE39B0192FA76A5FFDCC9E82B7E58703116158613DF5A12E7E2B8BABA94 | |||
| 3880 | hale.exe | C:\Users\admin\AppData\Local\Temp\B518.tmp\godo.cmd | text | |
MD5:0A9D51896A1A3735884221794A7C65F1 | SHA256:2341170D3FC76A5BBEB2A795C2974ECB42FE20BDF89C01BB0326651D1CFCCC5D | |||
| 3880 | hale.exe | C:\Users\admin\AppData\Local\Temp\B518.tmp\tick.cmd | text | |
MD5:574014049E0ED8FF74182FA96F2D1AB3 | SHA256:C3148A2F9B901F67E63EDD03F256BCB7A8EA071564EE31EC0D602DE0F5219699 | |||
| 3880 | hale.exe | C:\Users\admin\AppData\Local\Temp\B518.tmp\setv.cmd | text | |
MD5:D6C2C11867868F16C4BBD97EC106474E | SHA256:809D5FB8D05569815FF67E9AD520CA64E7C8998E035993CF9CA7F5216E5572DB | |||
| 3880 | hale.exe | C:\Users\admin\AppData\Local\Temp\B518.tmp\mtmp.cmd | text | |
MD5:02D7EBAD35B5624A751243D101A540CE | SHA256:7686C1B97D3F80D042AAC35D82B5E5B558A494AE3E0E35DE81A47C413D9020AC | |||
| 3880 | hale.exe | C:\Users\admin\AppData\Local\Temp\B518.tmp\tran.cmd | text | |
MD5:08D050C91F916DD562A7E9EF9F0E9815 | SHA256:196701833B1E0C5C7217A2CD92ED70722E7D91F7CFF6877CFF21E4BE5B0AF4C9 | |||
| 3880 | hale.exe | C:\Users\admin\AppData\Local\Temp\B518.tmp\undo.cmd | text | |
MD5:85A546F23A7ED21CAFD045A1B5F064AC | SHA256:AFD79AC6D48544C272F4570F32AA654A5F69497B5DB7D543ACF72883C6804A0A | |||
| 3880 | hale.exe | C:\Users\admin\AppData\Local\Temp\B518.tmp\plat.cmd | text | |
MD5:FE8A397E3064F711BA04B6BABD10558D | SHA256:EF709FE236DFEFC40D2AB9C51A27E10914E5E3C316388CC8F937CF3CD09E622F | |||
| 3880 | hale.exe | C:\Users\admin\AppData\Local\Temp\B518.tmp\postw.cmd | text | |
MD5:1277B2E3A1771D53D7E83777008EE705 | SHA256:88149562312E09F1B34D65919891AAA5C0992462468A2FE5C10968BB9618D312 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report