| File name: | Bokusatsu Tenshi Full Anime Watch.exe |
| Full analysis: | https://app.any.run/tasks/2ff5ec5e-3bde-40a2-802f-c84a911b511e |
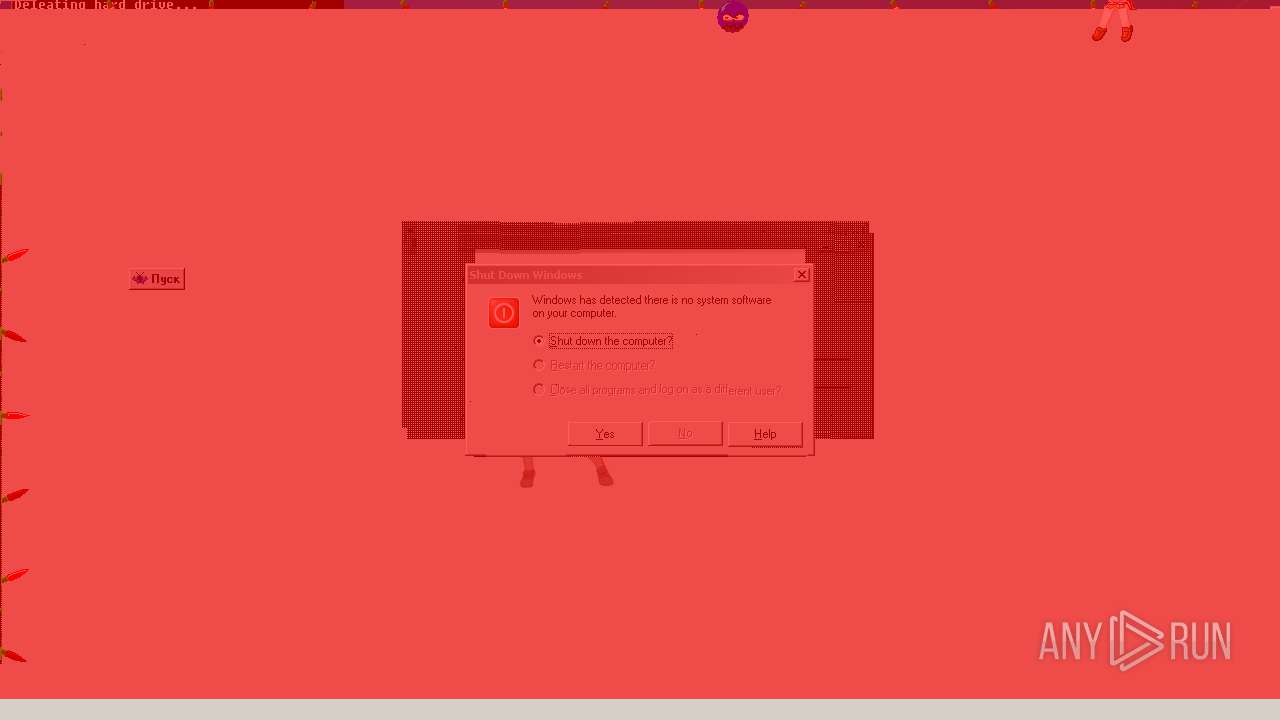
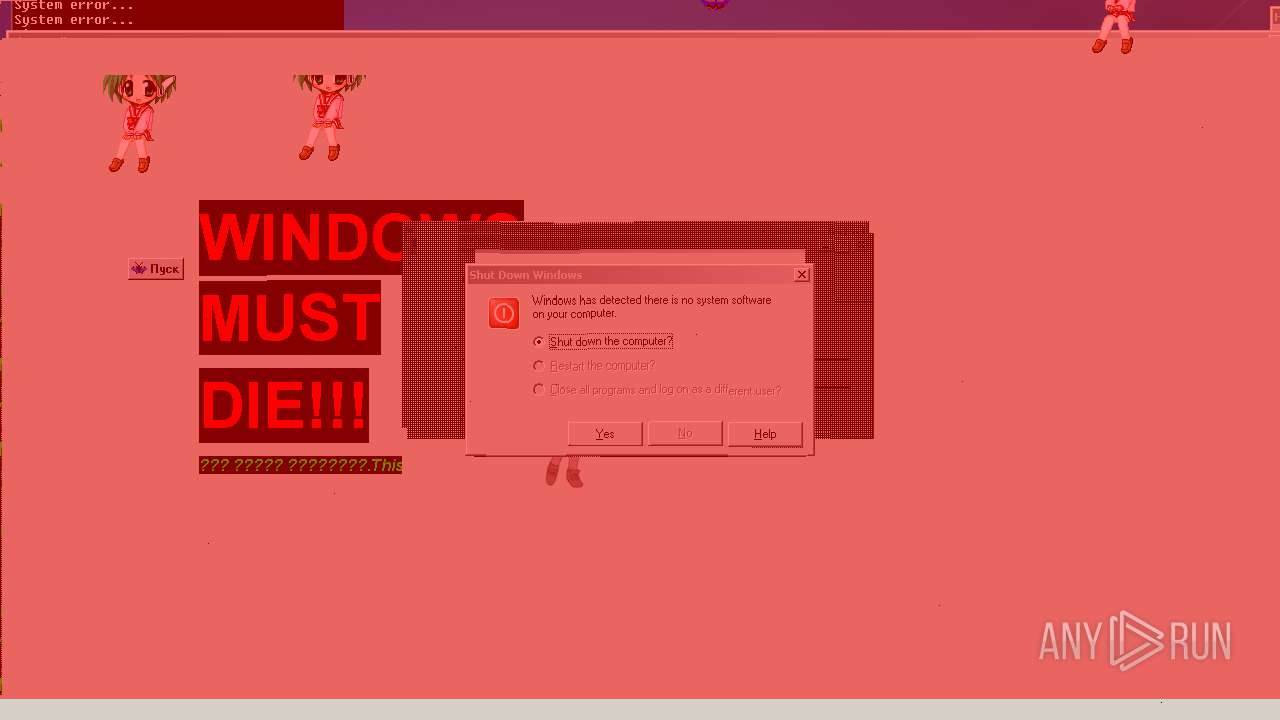
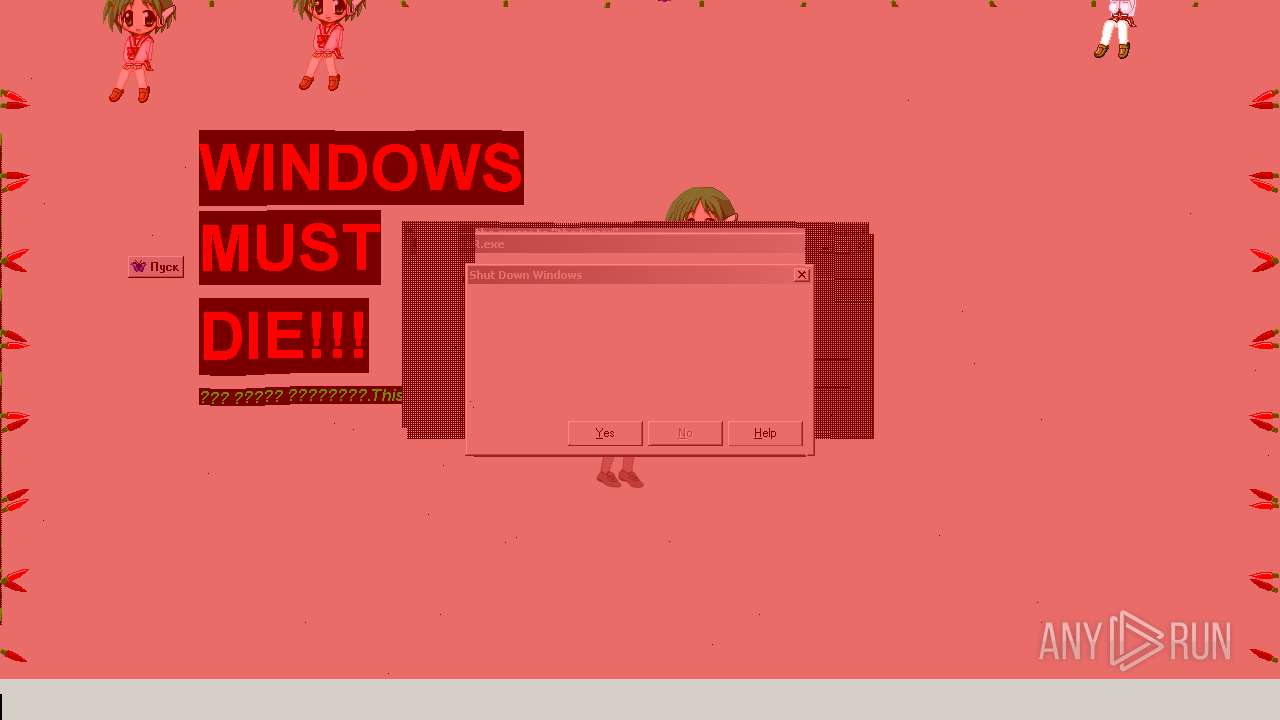
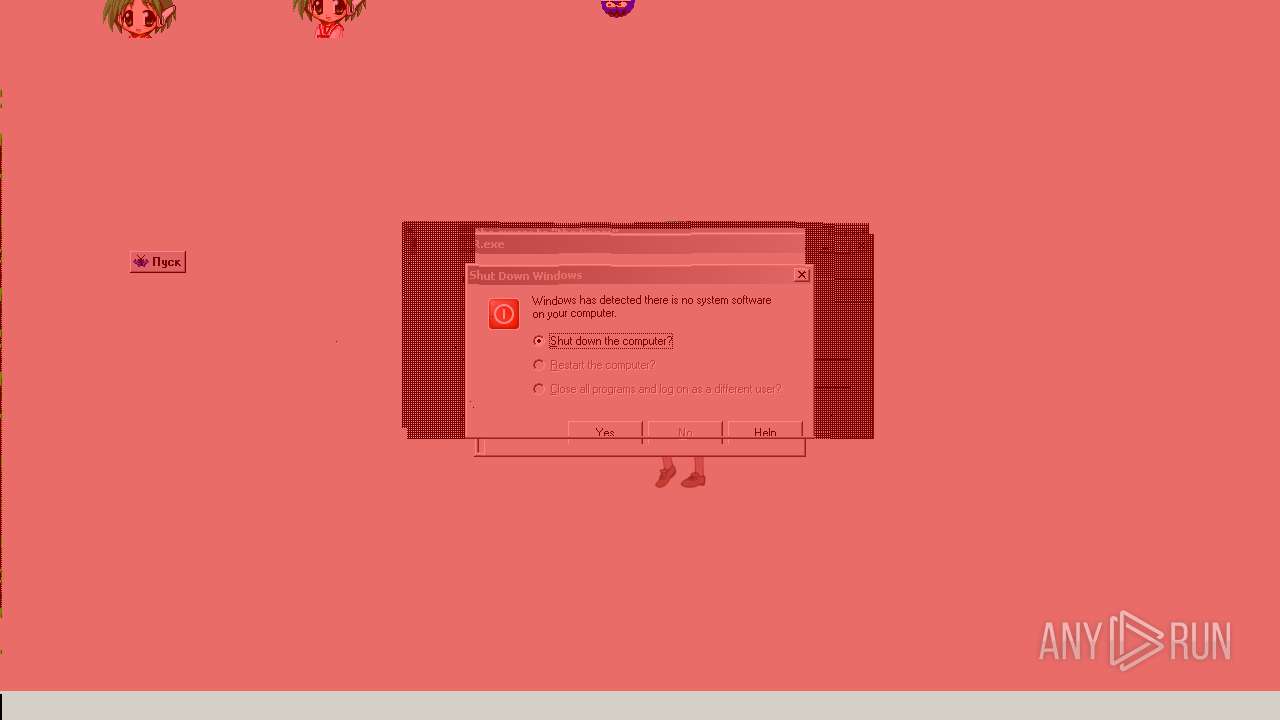
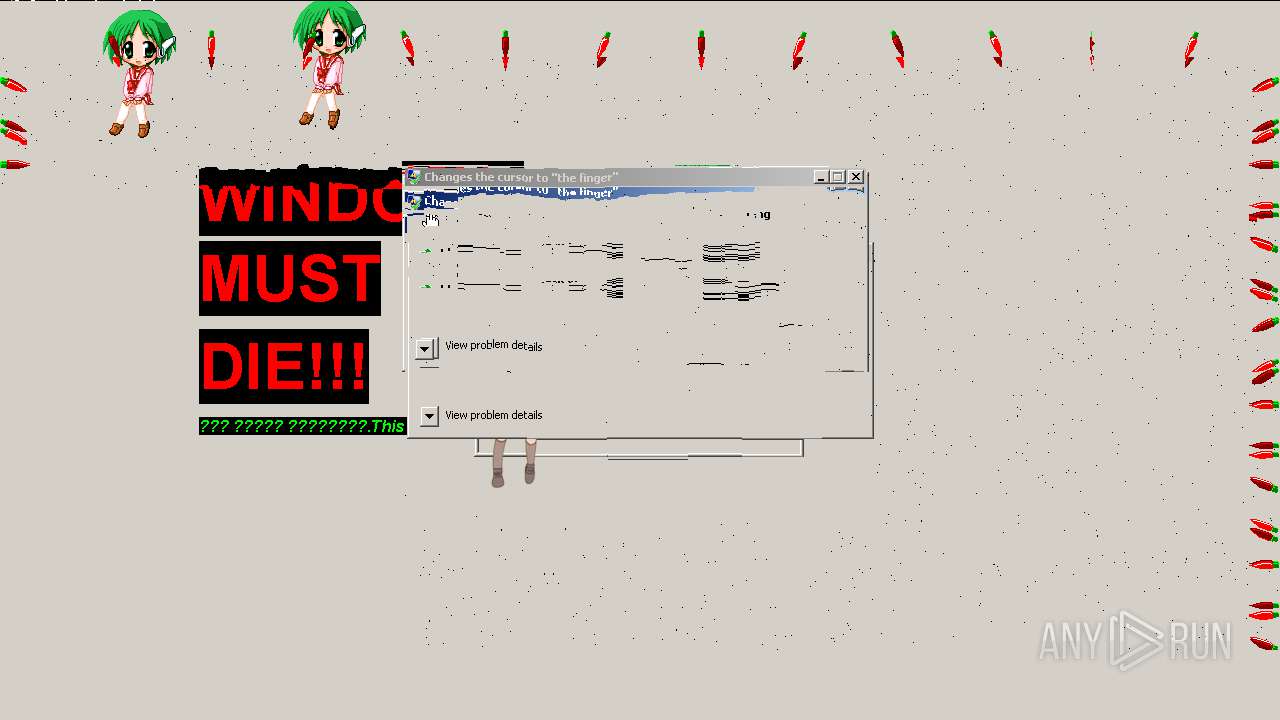
| Verdict: | Malicious activity |
| Analysis date: | October 08, 2021, 12:20:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 428B5352D8A6BB681CE65E172FE16C29 |
| SHA1: | 98DCC5C0FF63470B11FBB16578C378809FFEE5FC |
| SHA256: | F73D30F3CD4FBDD7D47FC89C85D4D1657026D52542A064DE6DCA67683FFFDDAF |
| SSDEEP: | 196608:kATMpri181qIboq/VCYb7PoJjKCppPT2Diq14GbgbWbfi4r+uSijIrtTkuKy:NTMpaIbooVBPoJdpUGGU+fFyNFkA |
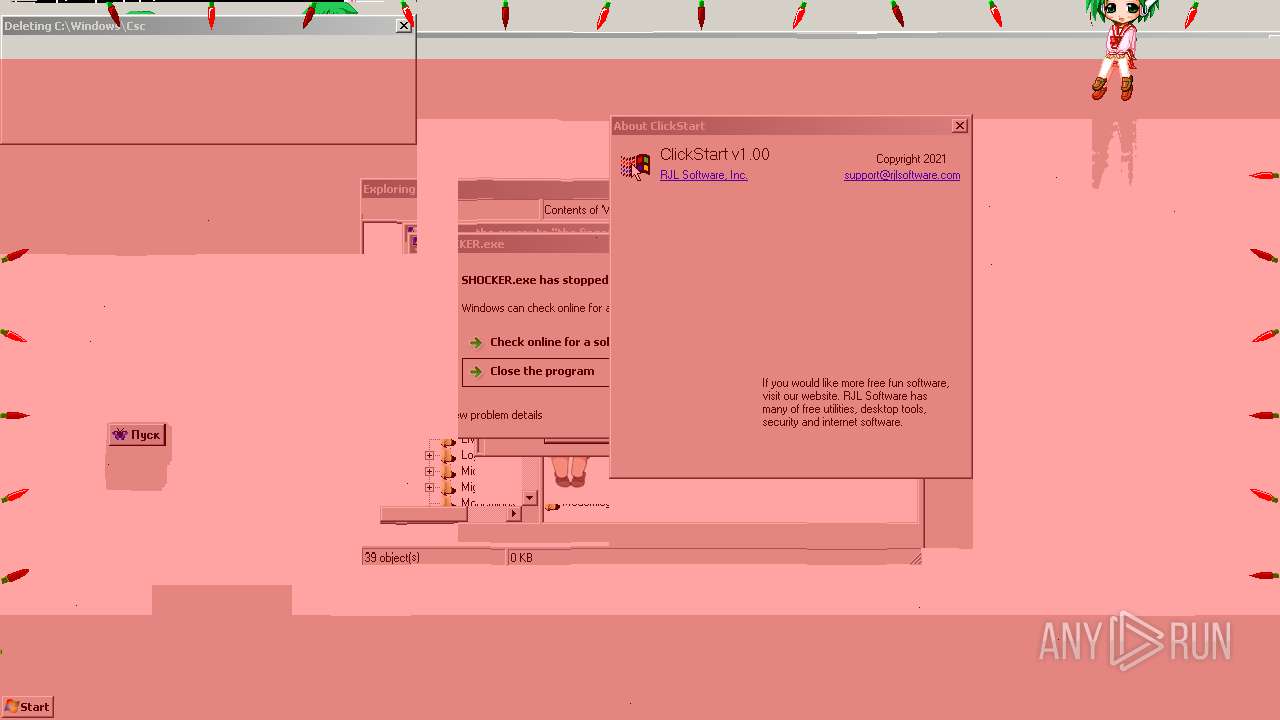
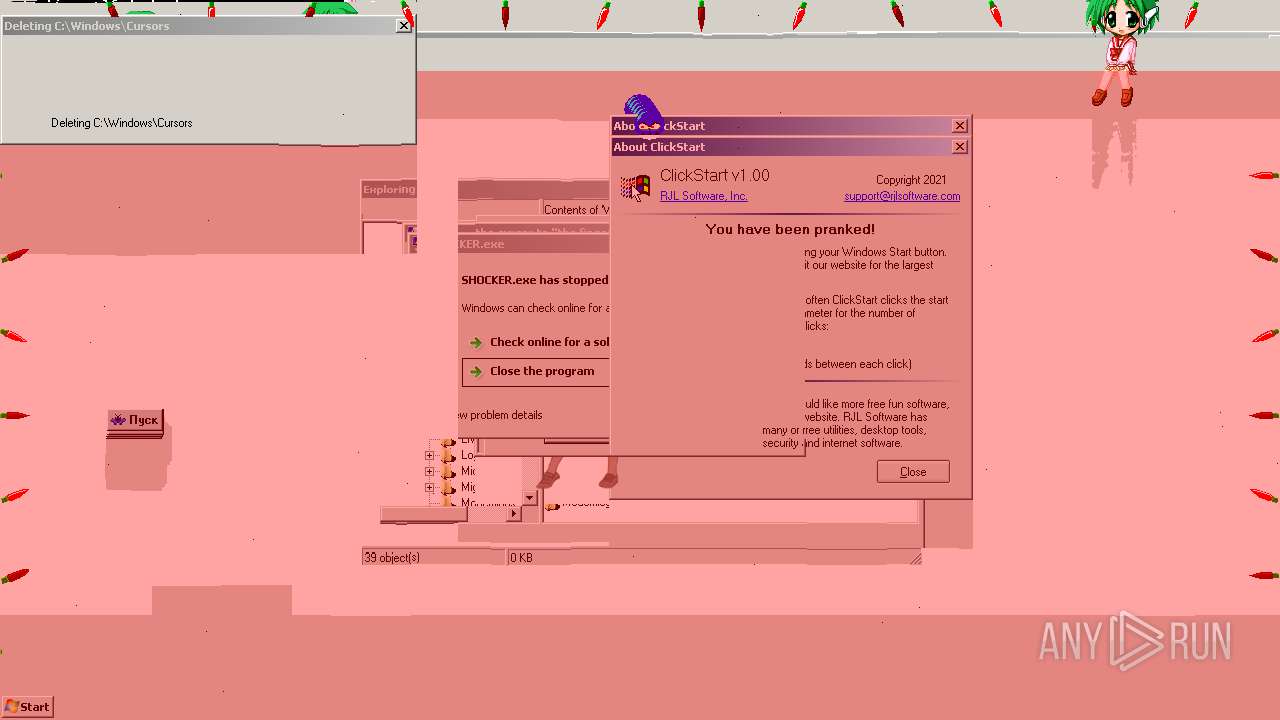
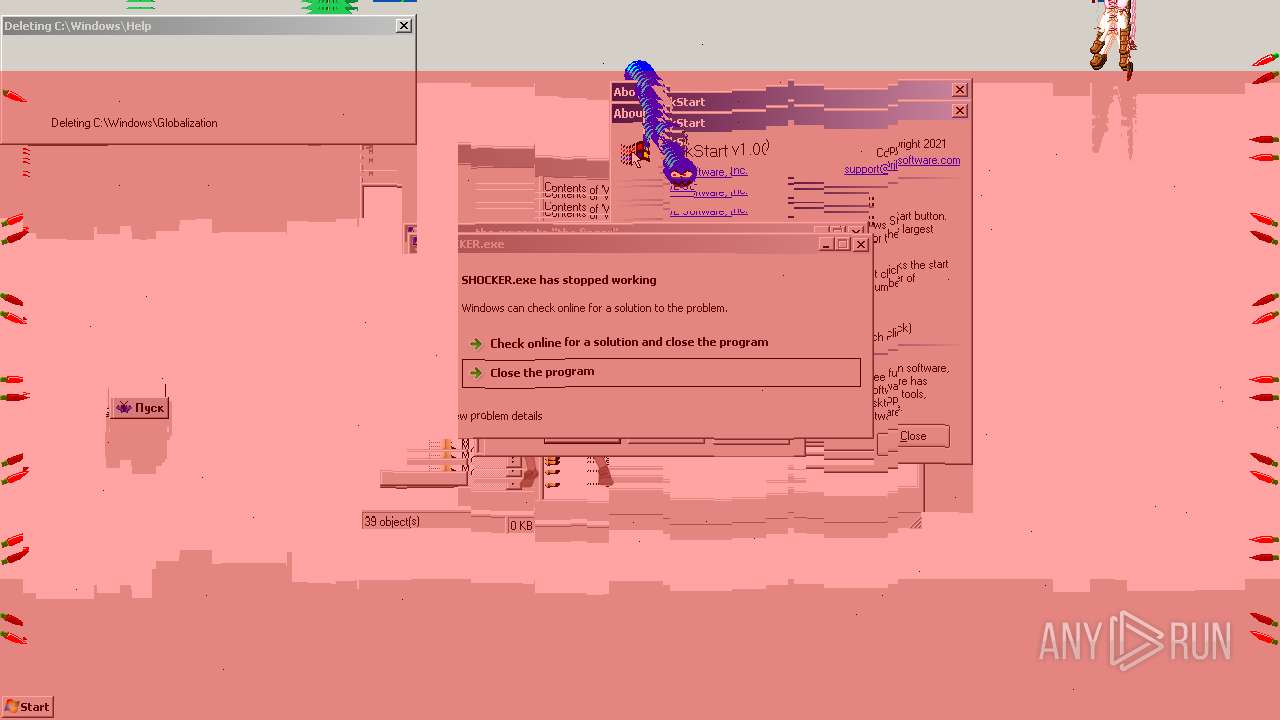
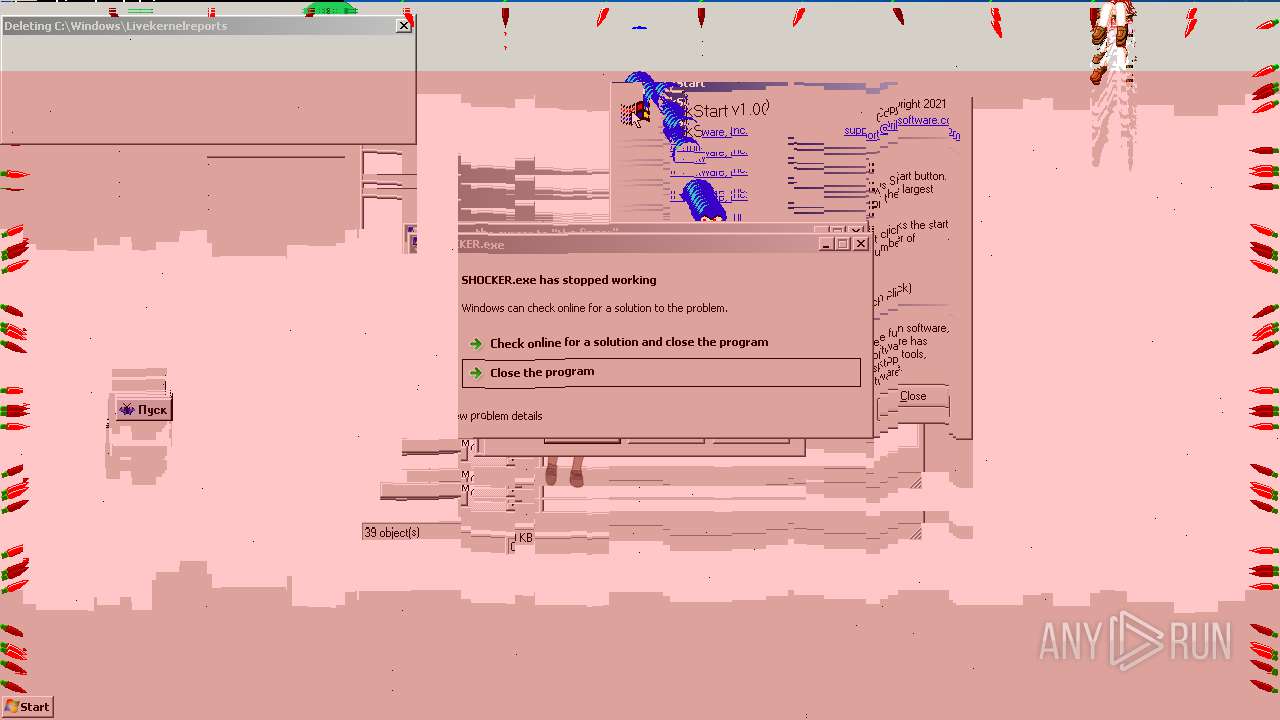
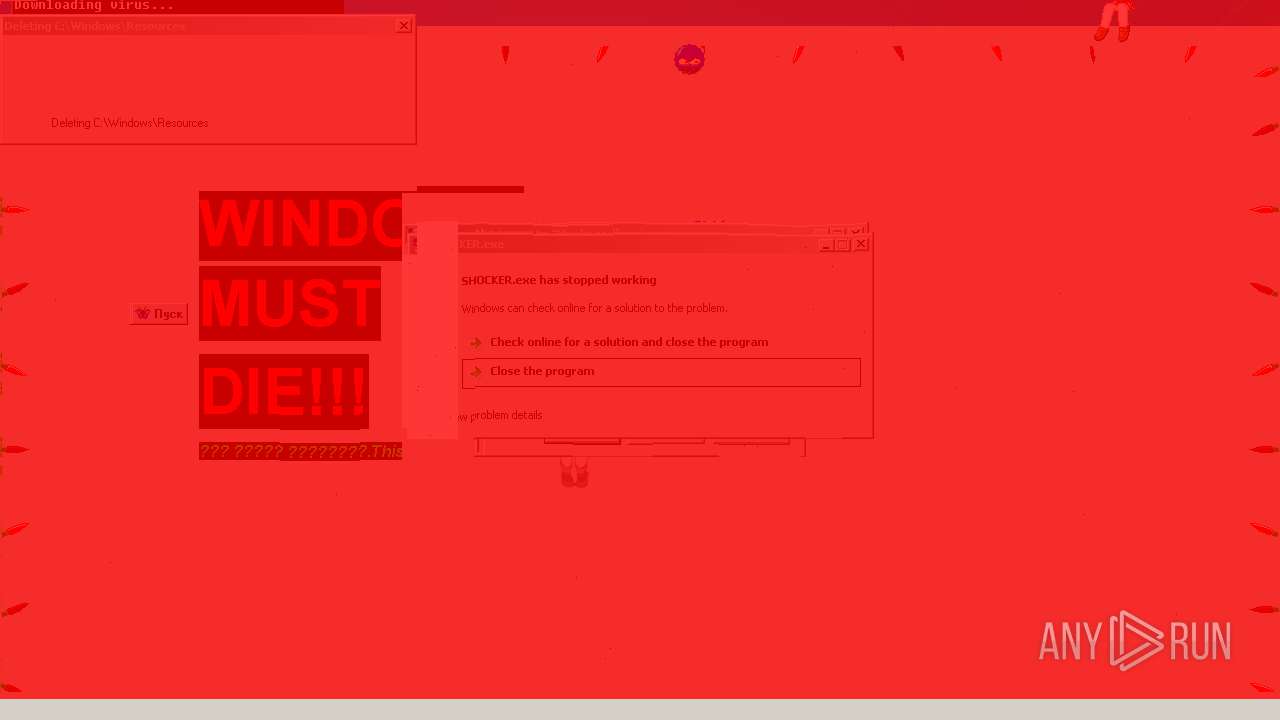
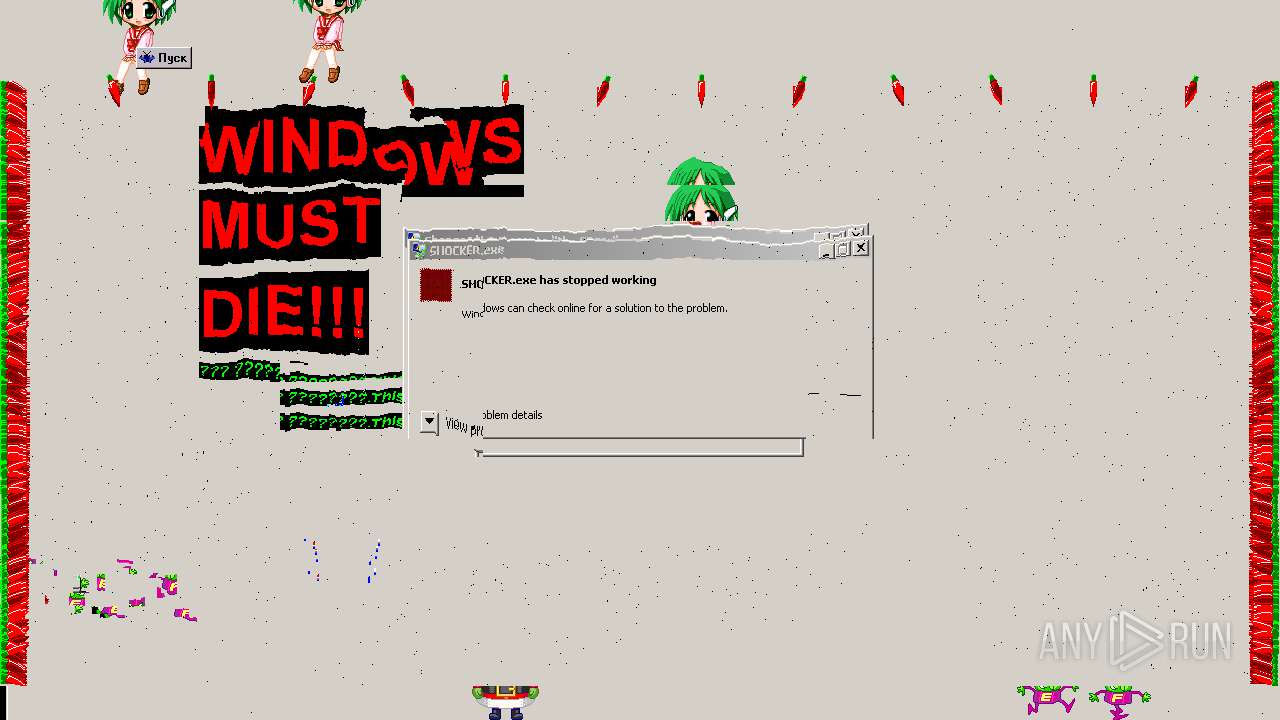
MALICIOUS
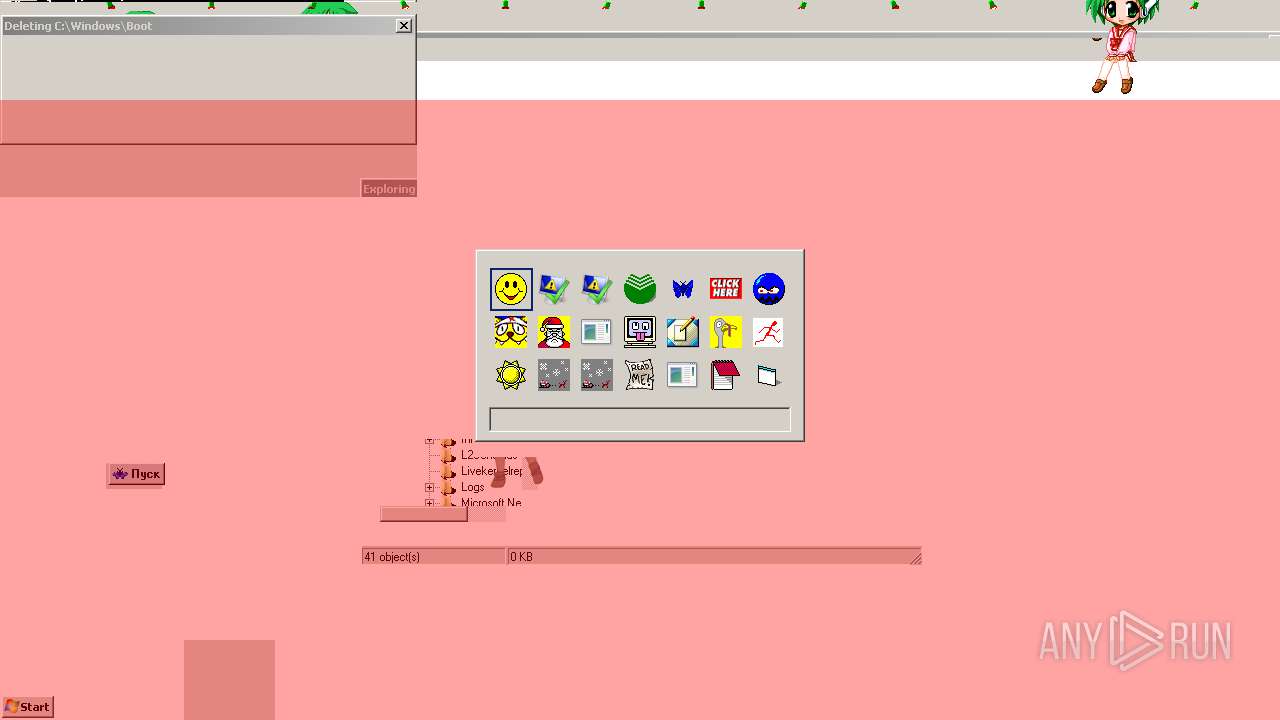
Drops executable file immediately after starts
- Bokusatsu Tenshi Full Anime Watch.exe (PID: 916)
- kona_dancer.exe (PID: 2224)
Application was dropped or rewritten from another process
- melter.exe (PID: 3688)
- ReadMe.exe (PID: 3748)
- ILoveYou.exe (PID: 3332)
- KorOvki.exe (PID: 4072)
- blast button.exe (PID: 1868)
- Snow for Windows.exe (PID: 2808)
- Evil's Crazy Mouse....exe (PID: 476)
- BURP.EXE (PID: 2708)
- MIGHTY FUCKER.exe (PID: 1008)
- Deathwishdog.exe (PID: 3488)
- ELVES.EXE (PID: 2236)
- australia.exe (PID: 2492)
- kona_dancer.exe (PID: 2224)
- Reverse.exe (PID: 3940)
- CrazyMouse.exe (PID: 3356)
- ????_original.exe (PID: 3304)
- come too me.exe (PID: 3204)
- ???????? ??????? ????????.exe (PID: 3436)
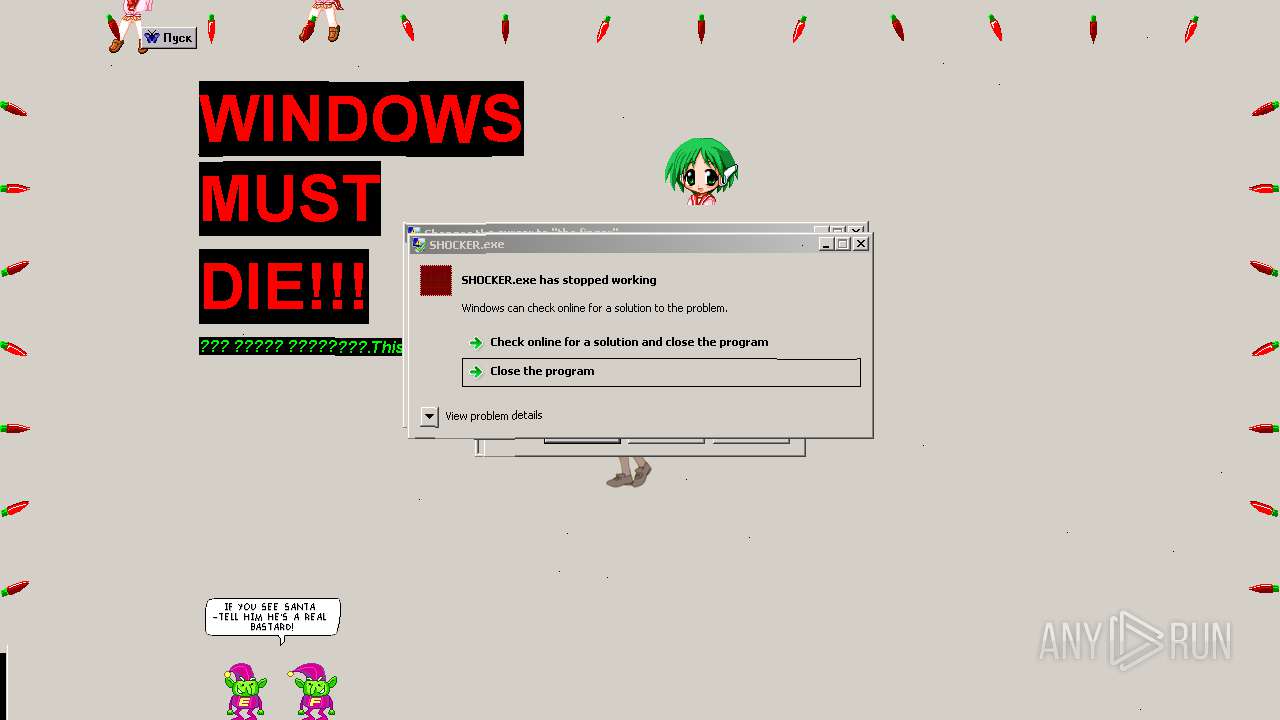
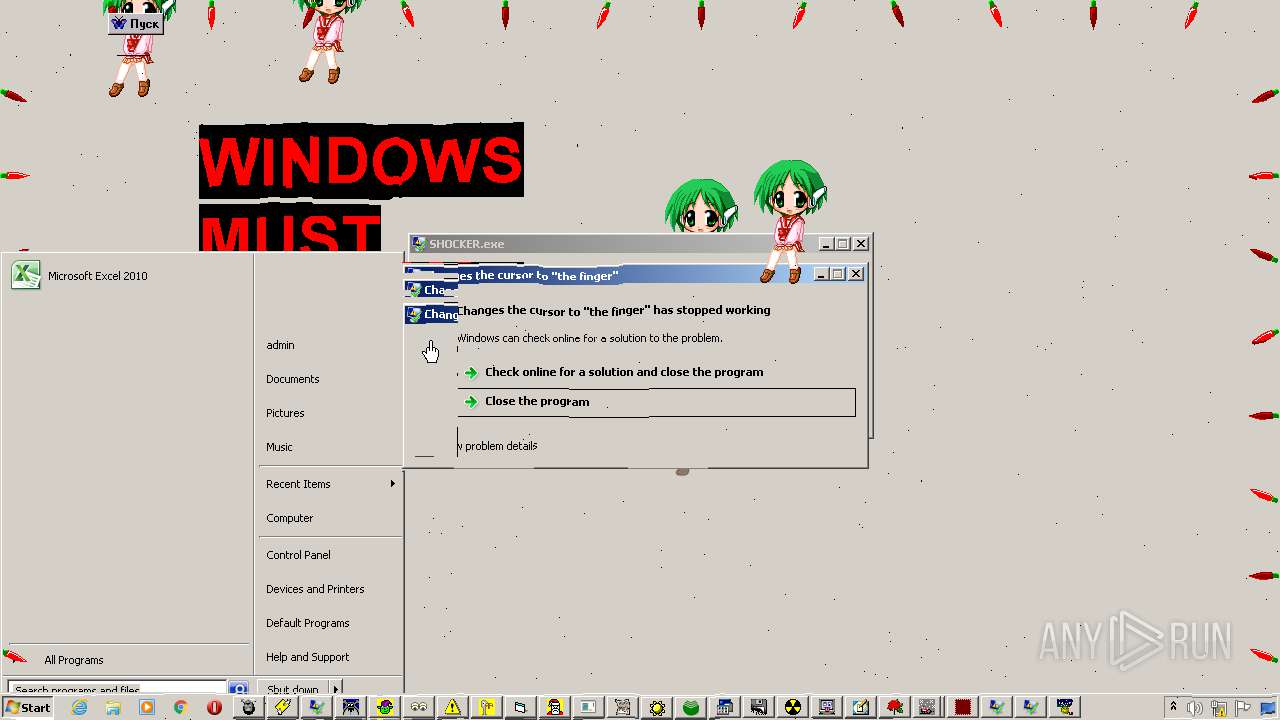
- SHOCKERR.exe (PID: 1016)
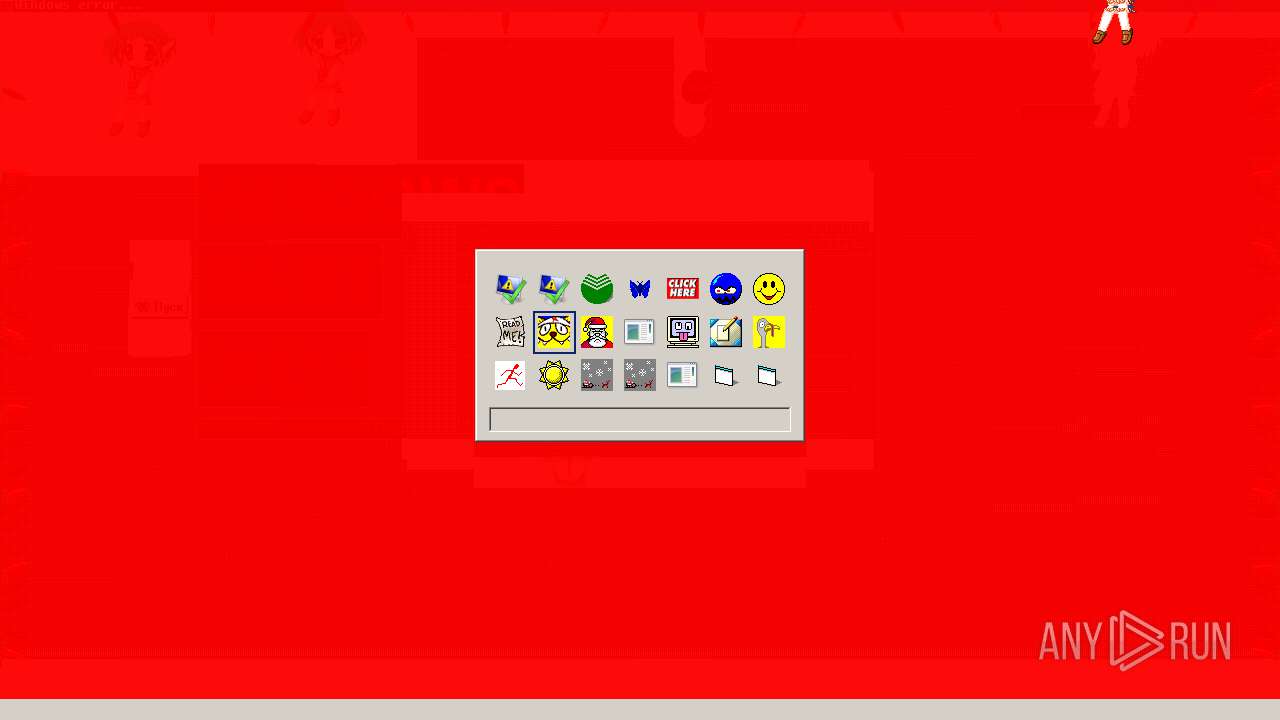
- Icons.exe (PID: 2856)
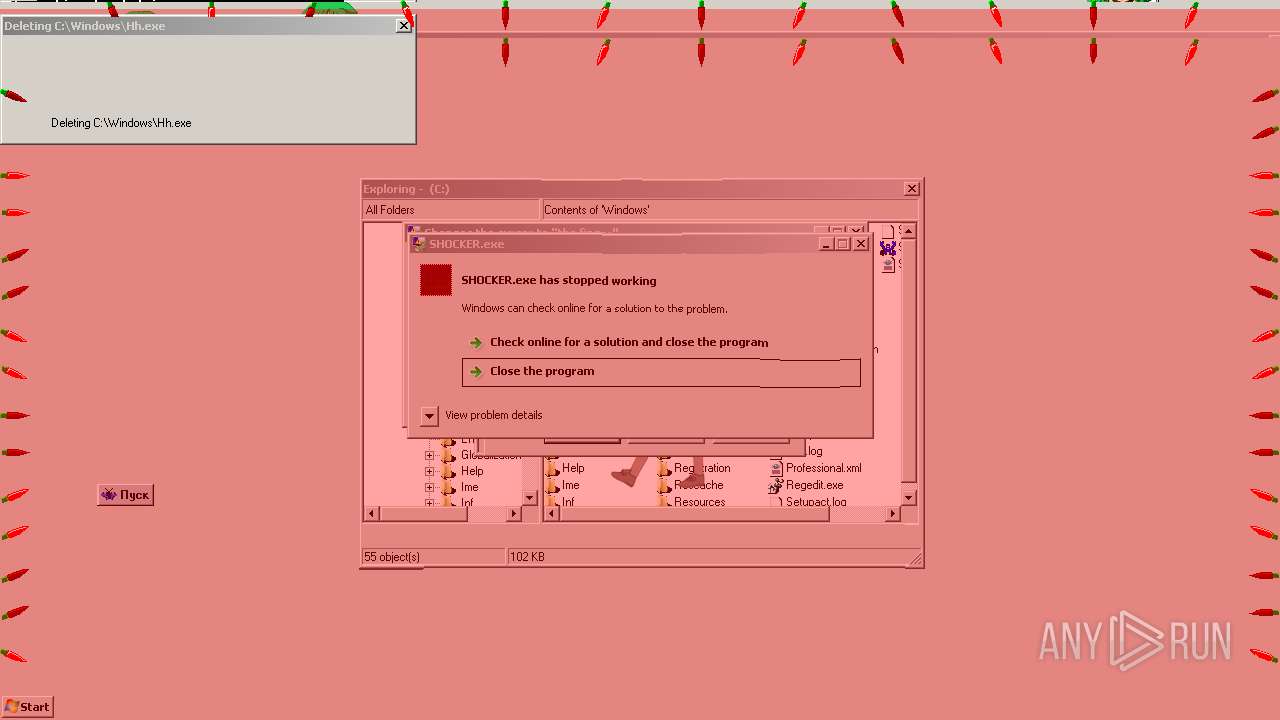
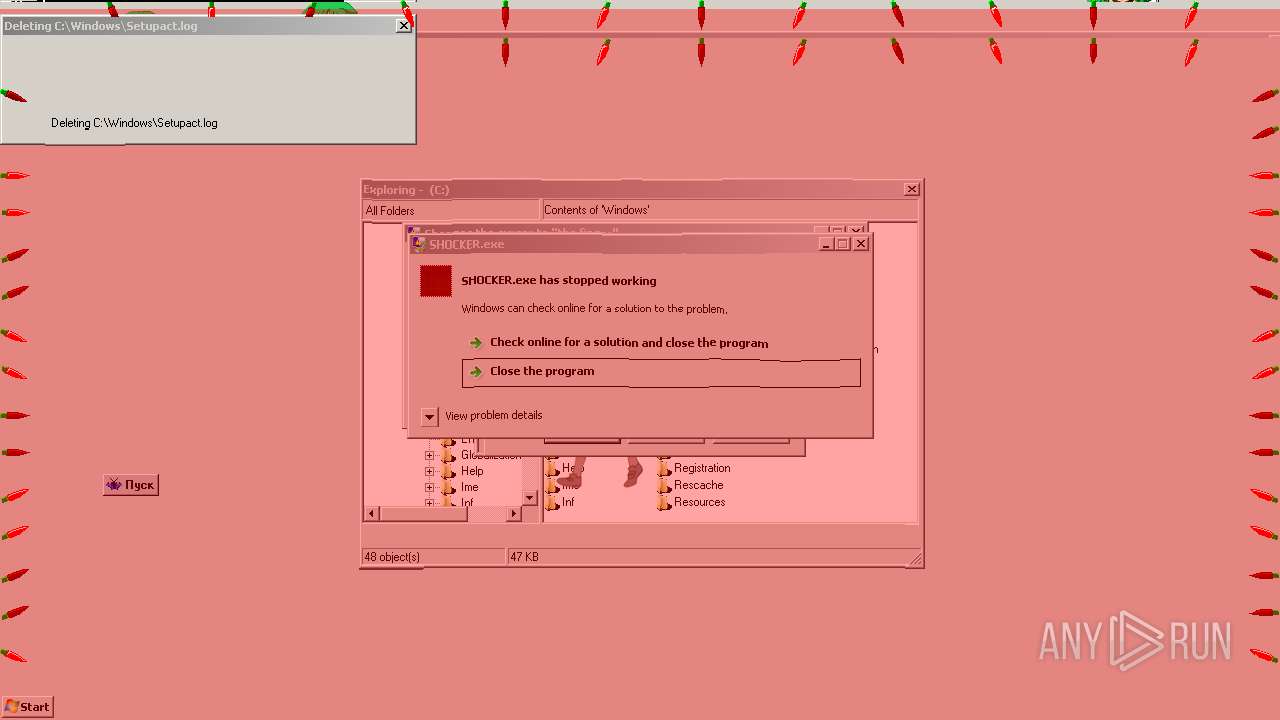
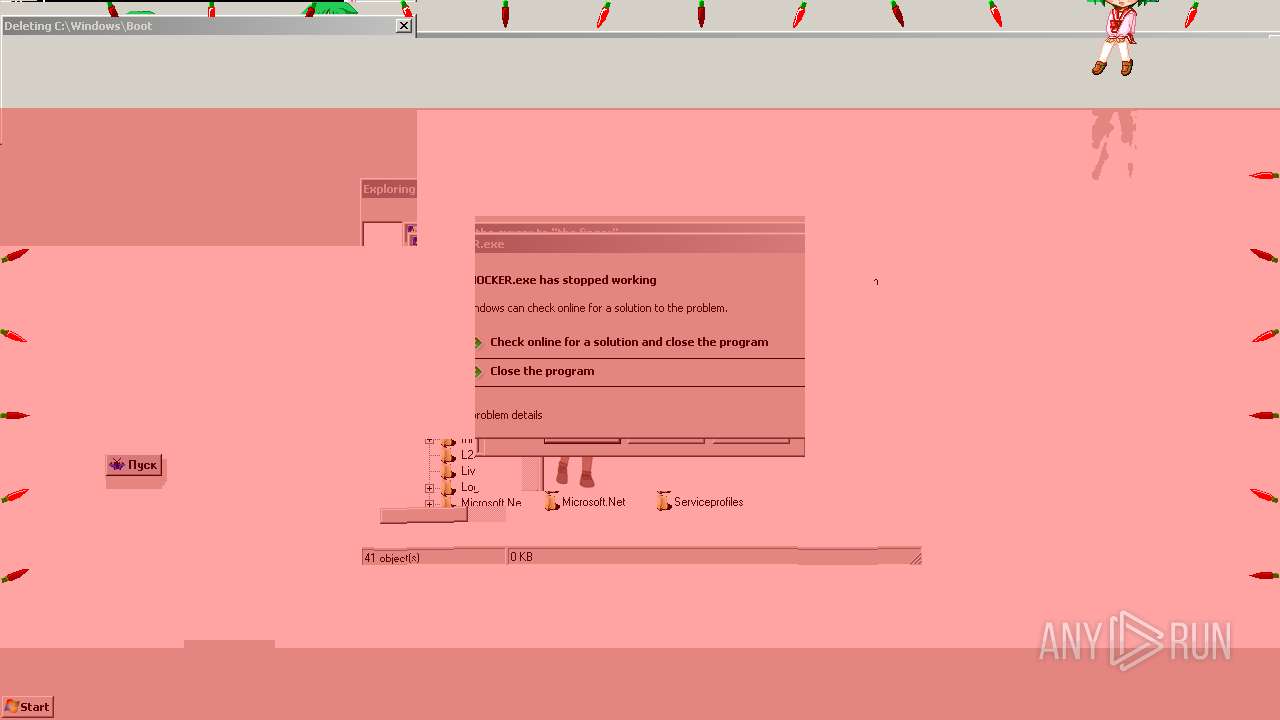
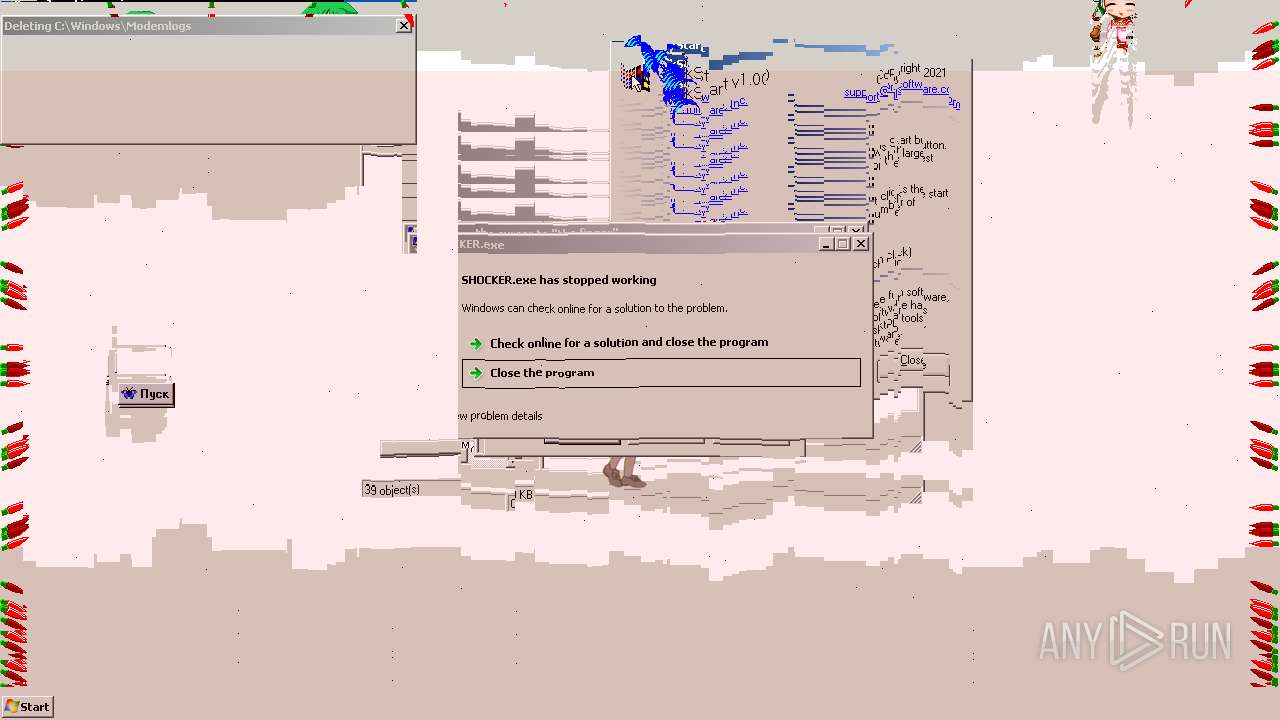
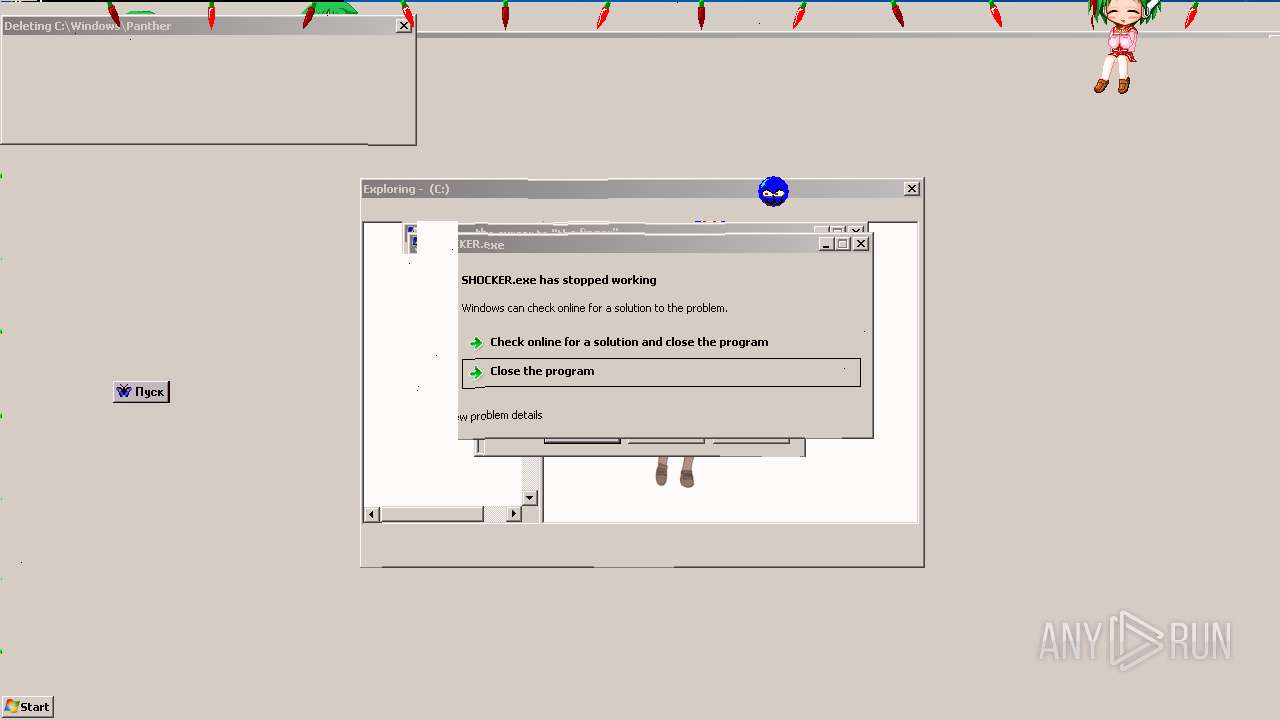
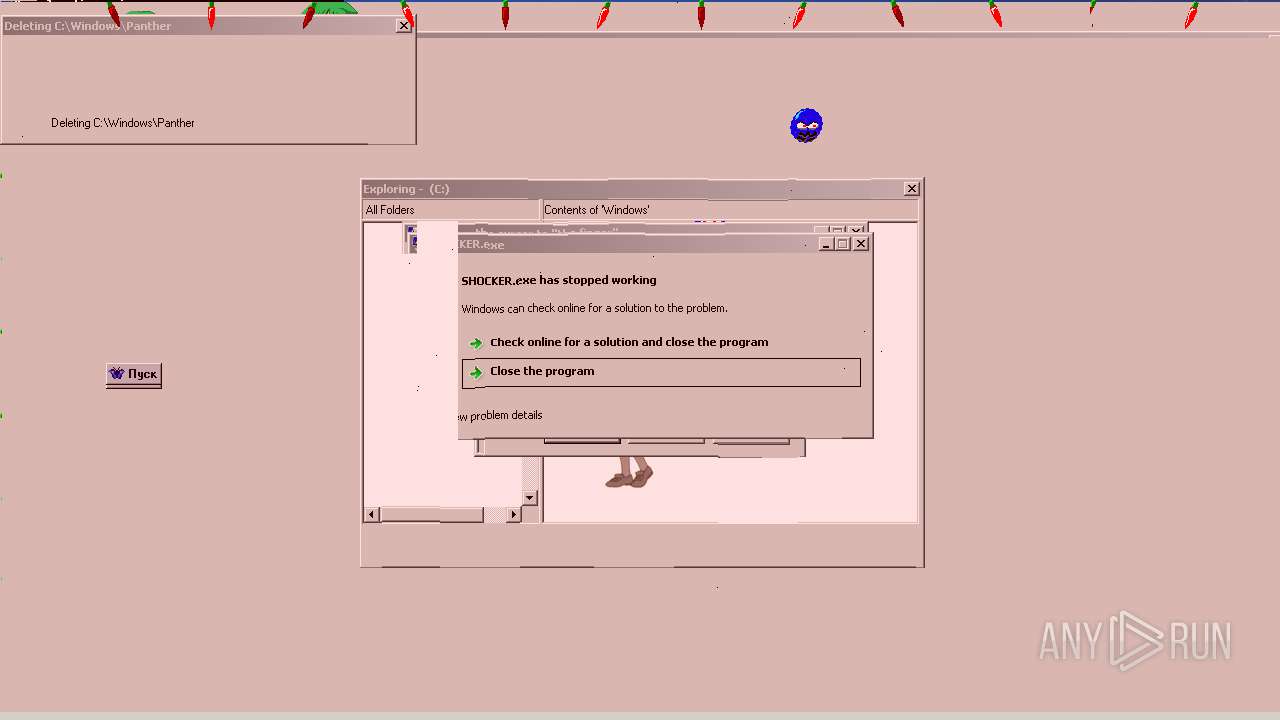
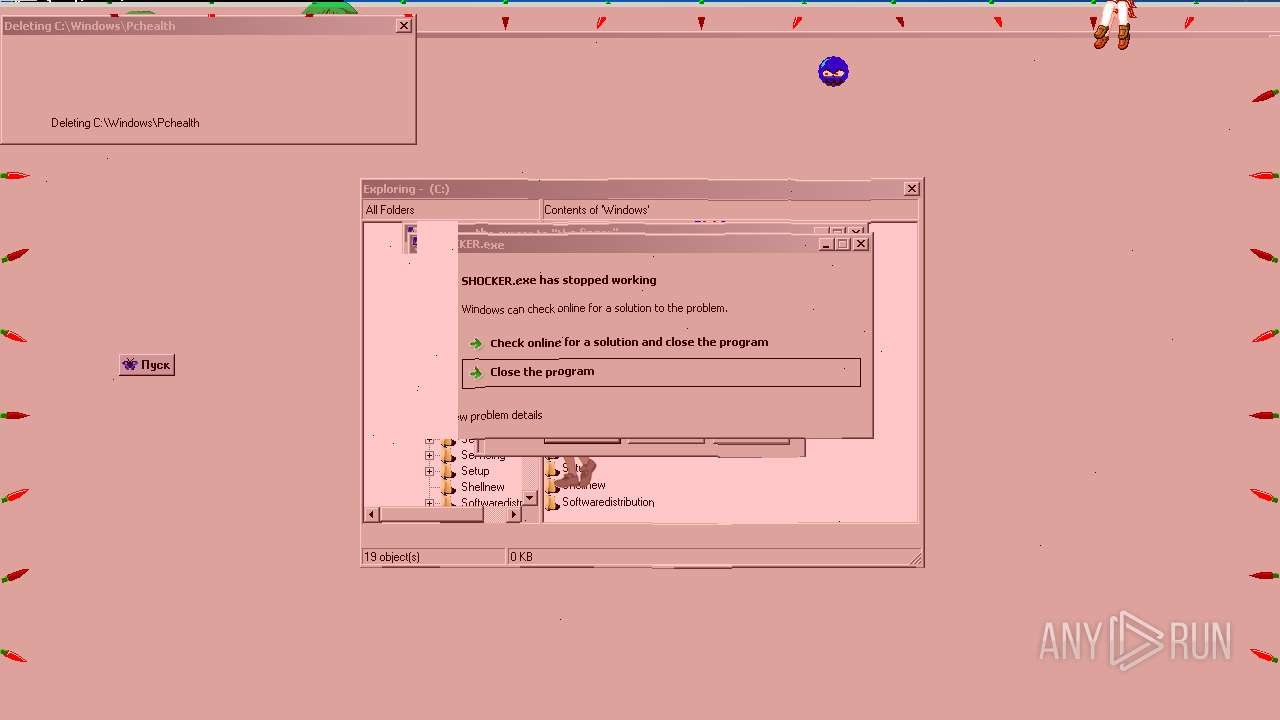
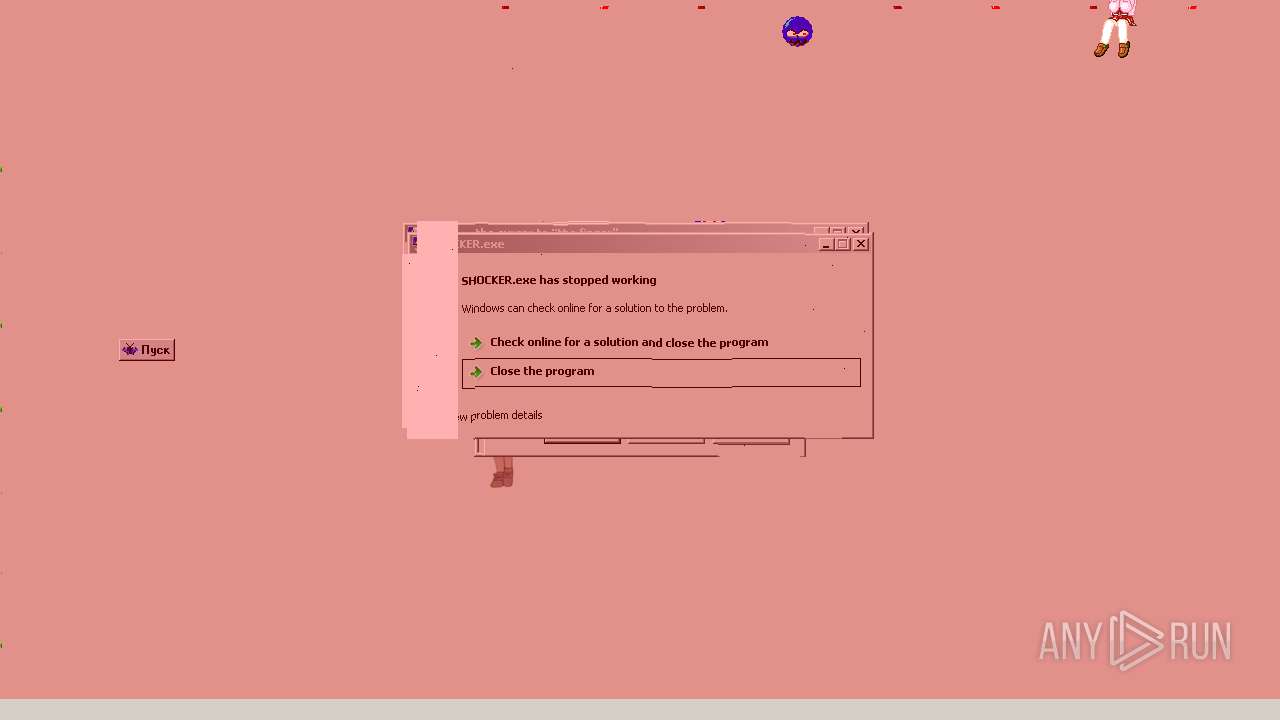
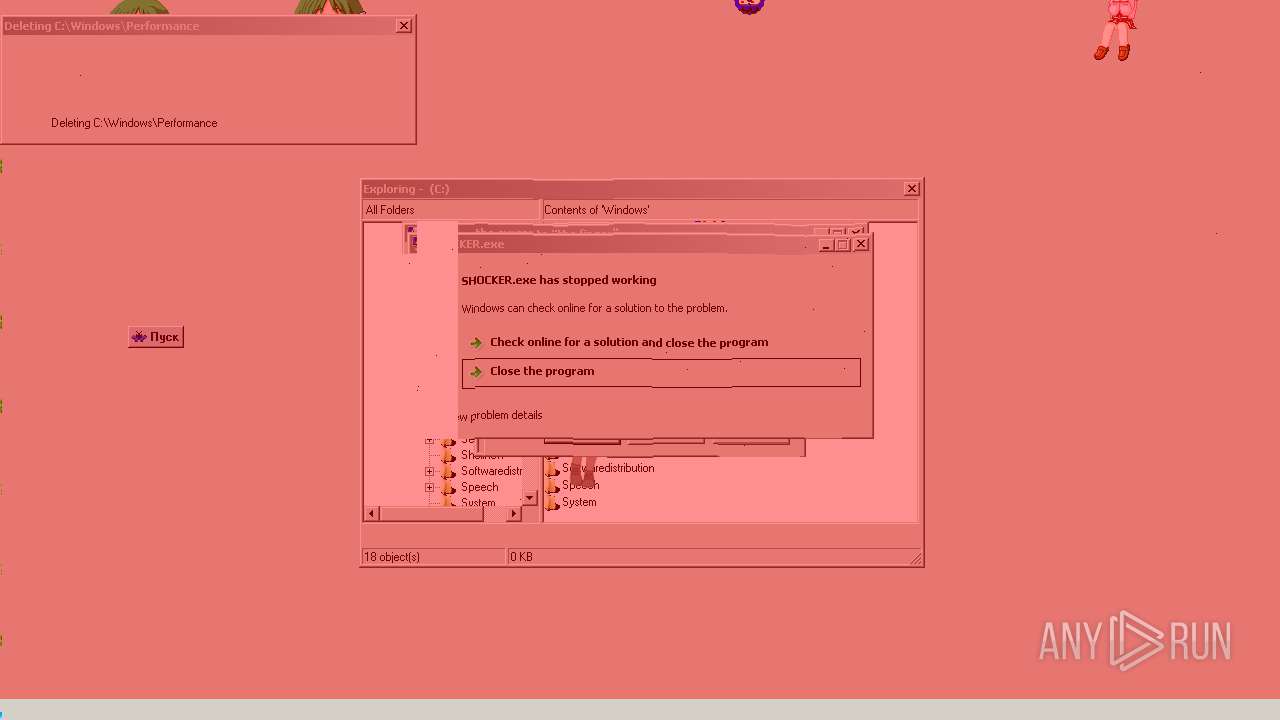
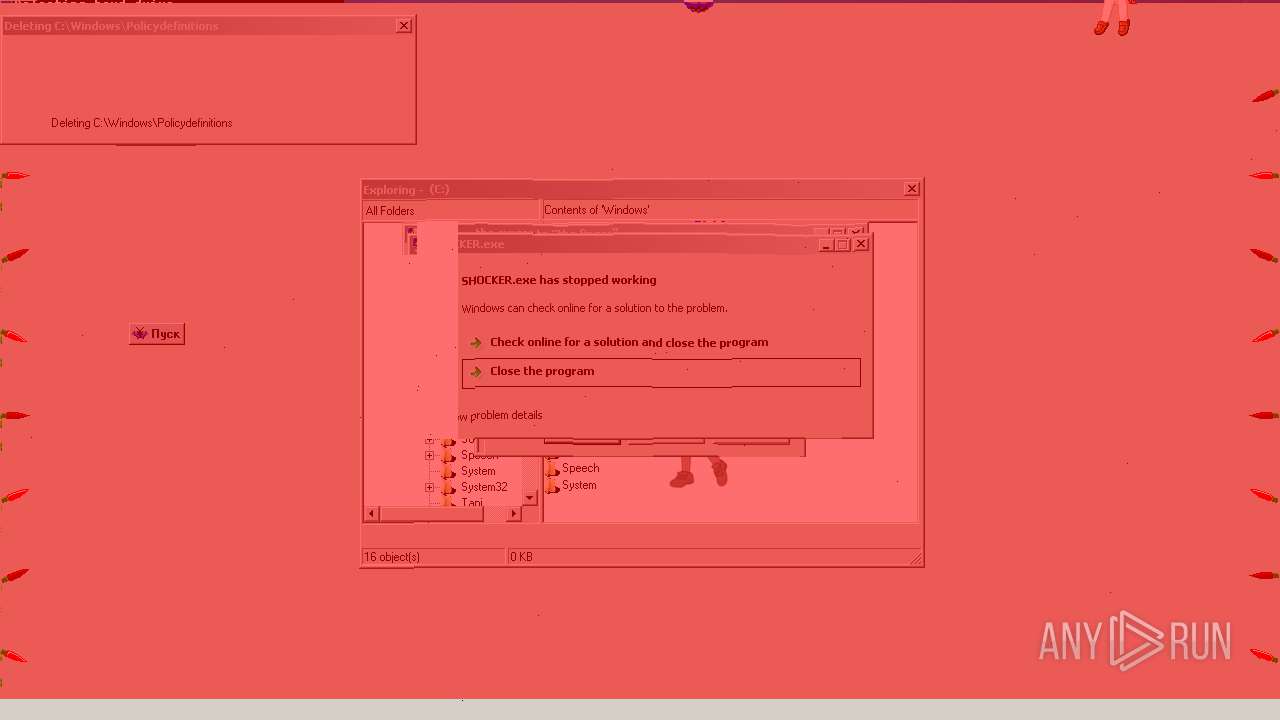
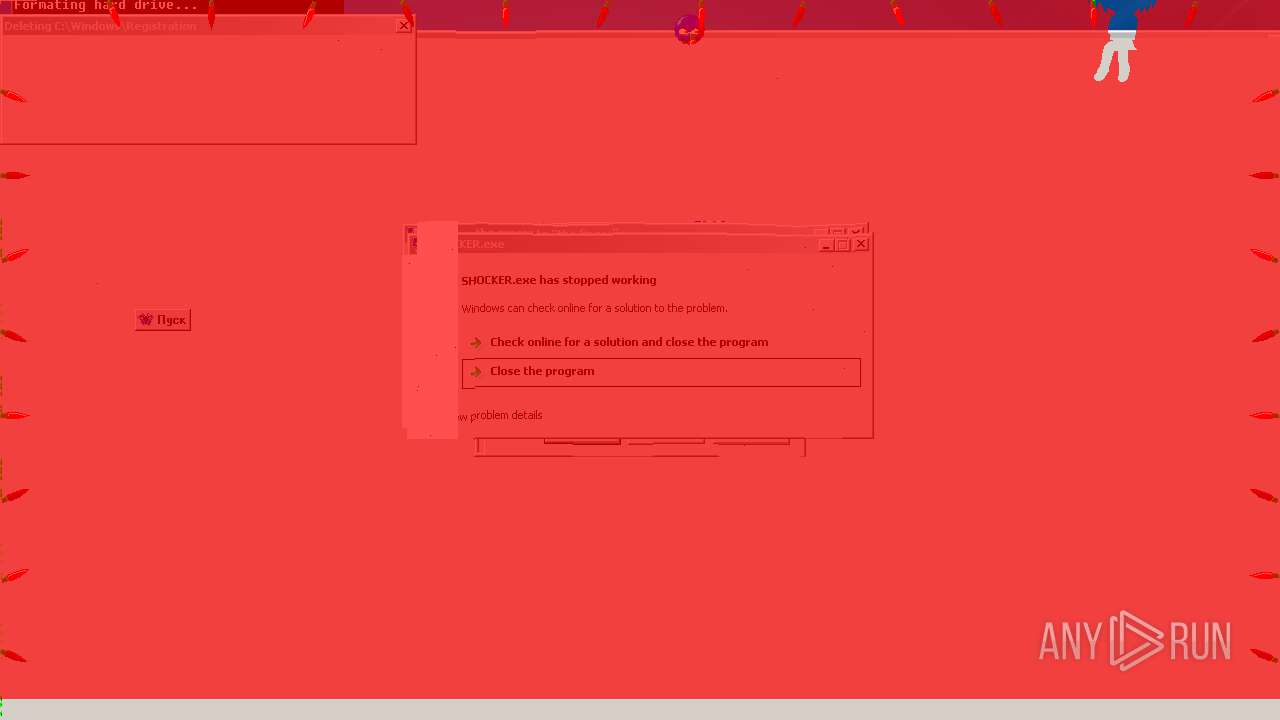
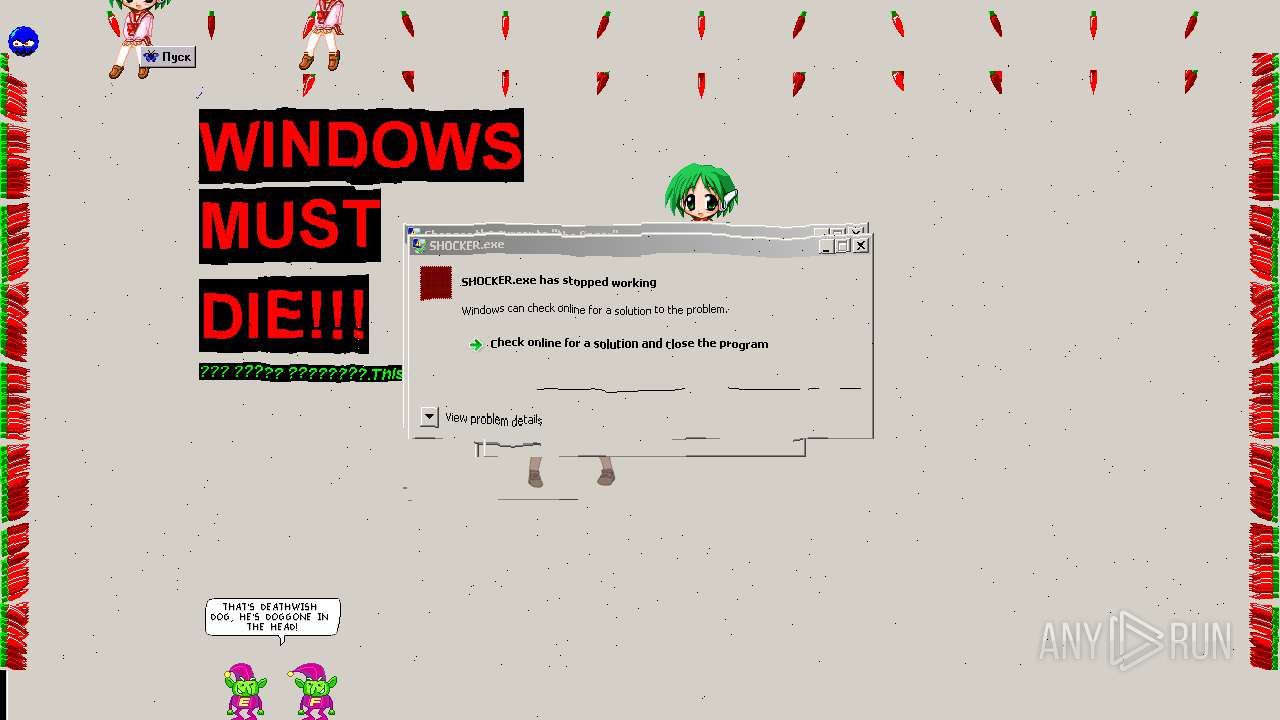
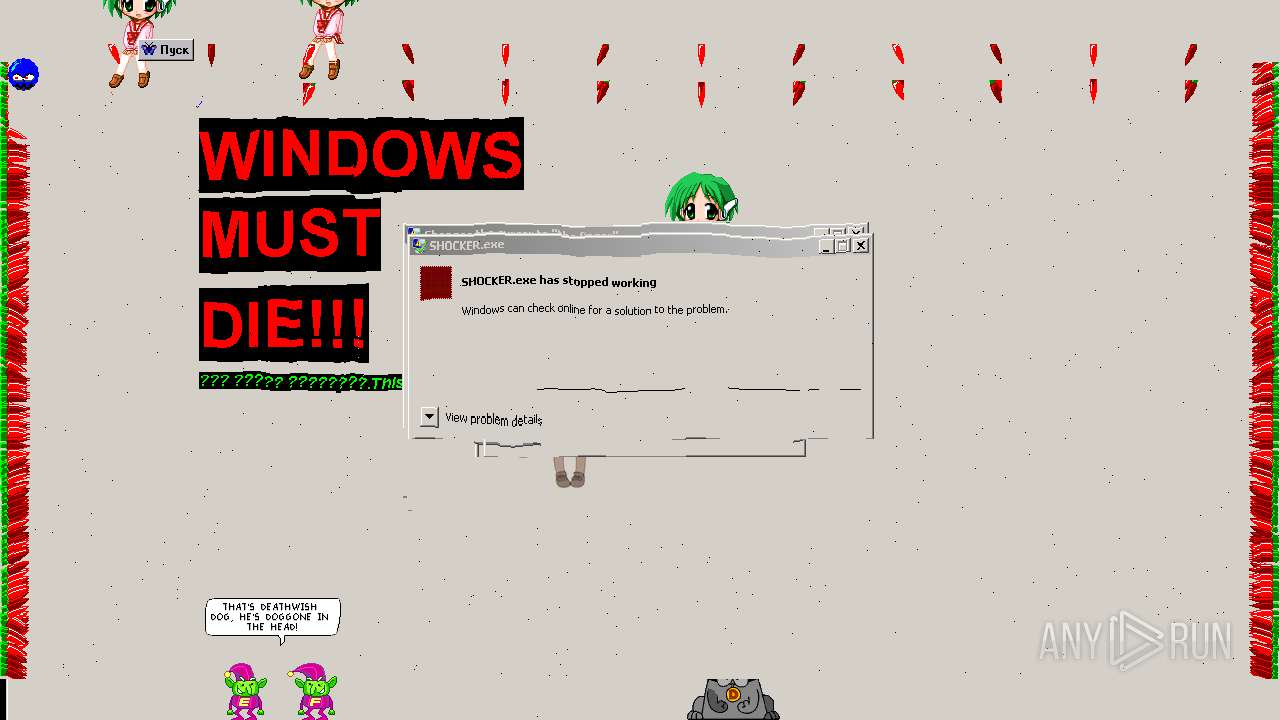
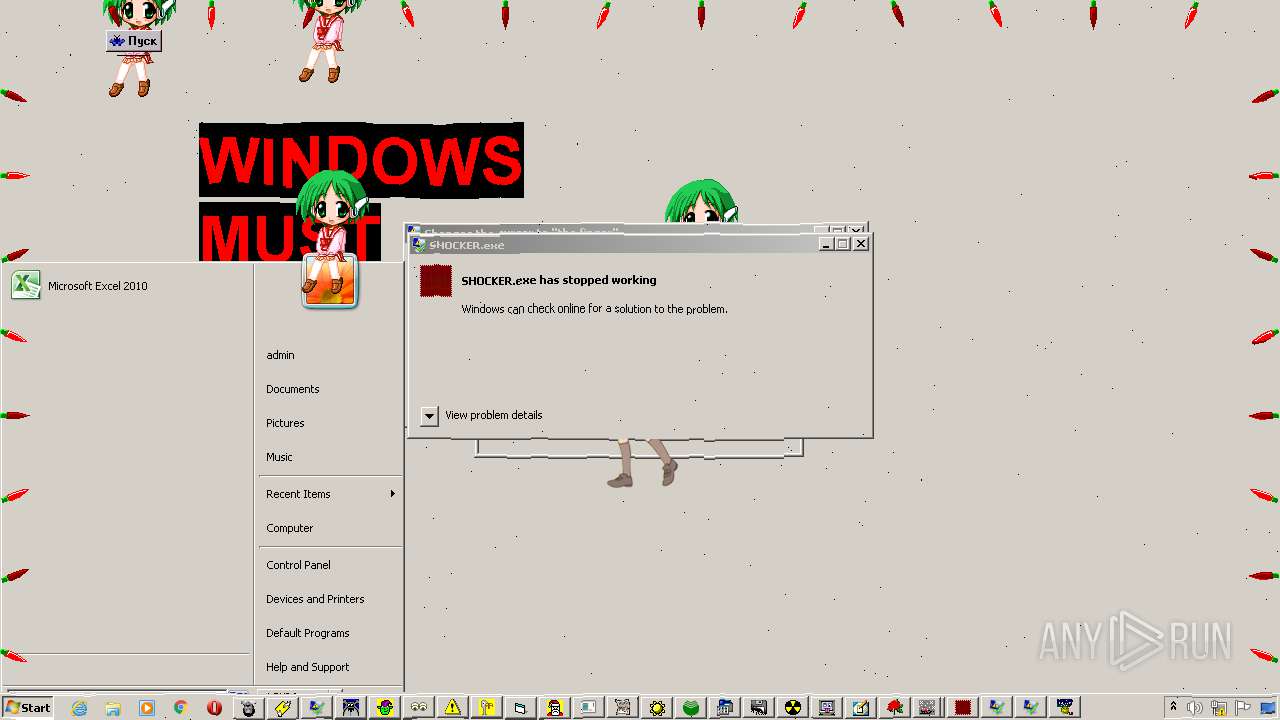
- SHOCKER.exe (PID: 1192)
- BUG.EXE (PID: 2444)
- Icons 2.exe (PID: 3148)
- Crazy Mouse v1.2.exe (PID: 3336)
- SANTA.EXE (PID: 2356)
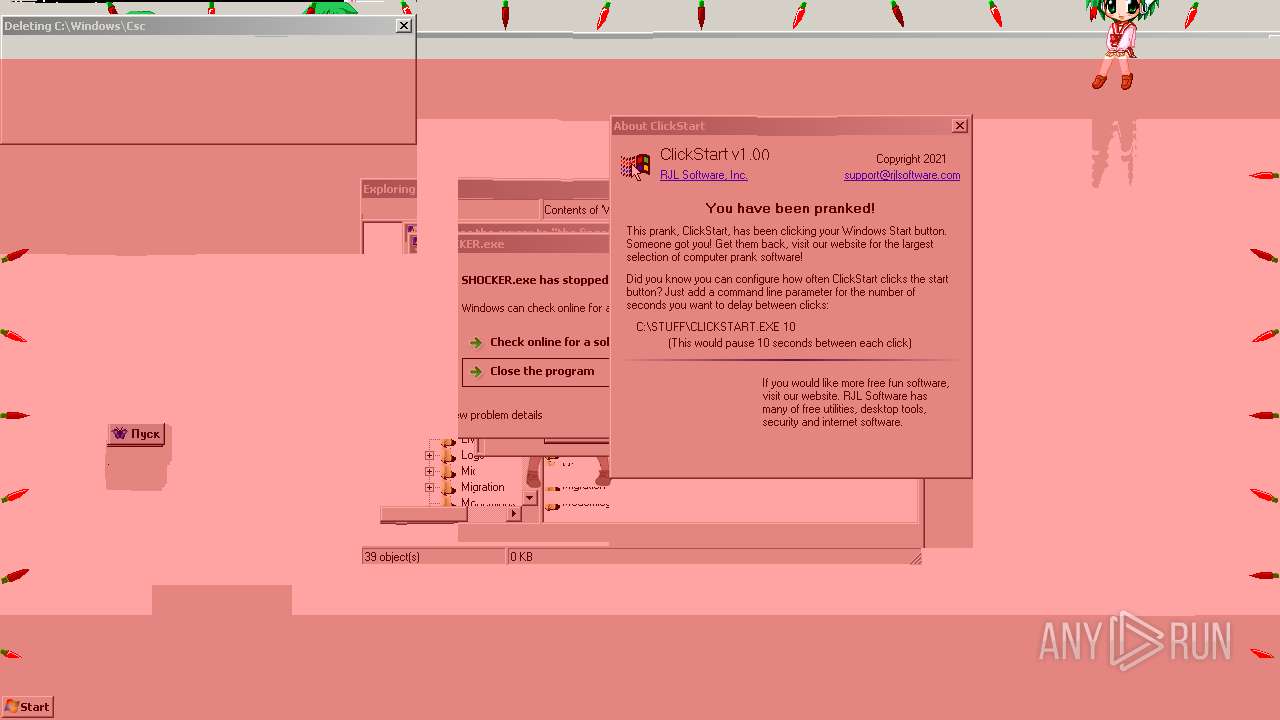
- starter.exe (PID: 3008)
- ??????? ????????.exe (PID: 1444)
- IDIOT.exe (PID: 2920)
- Close Programs.exe (PID: 4012)
- bonce.exe (PID: 2620)
- MoveMouse.exe (PID: 3864)
- Virus1.exe (PID: 3096)
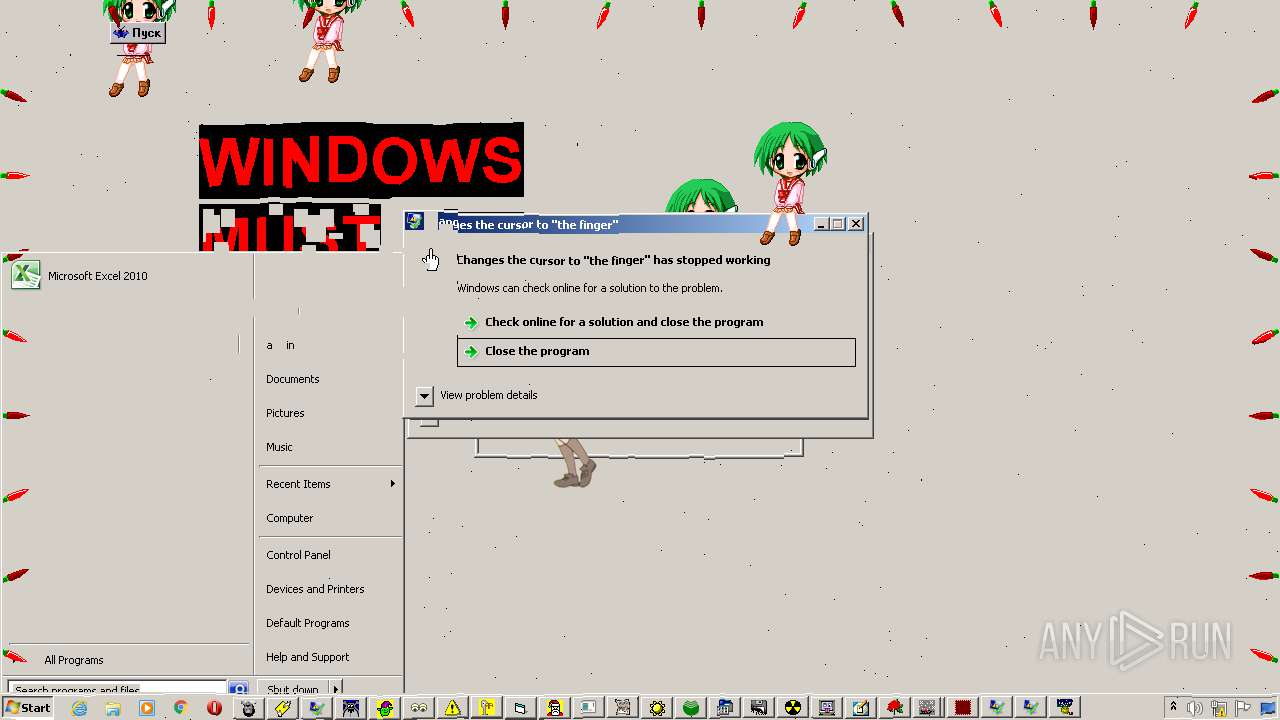
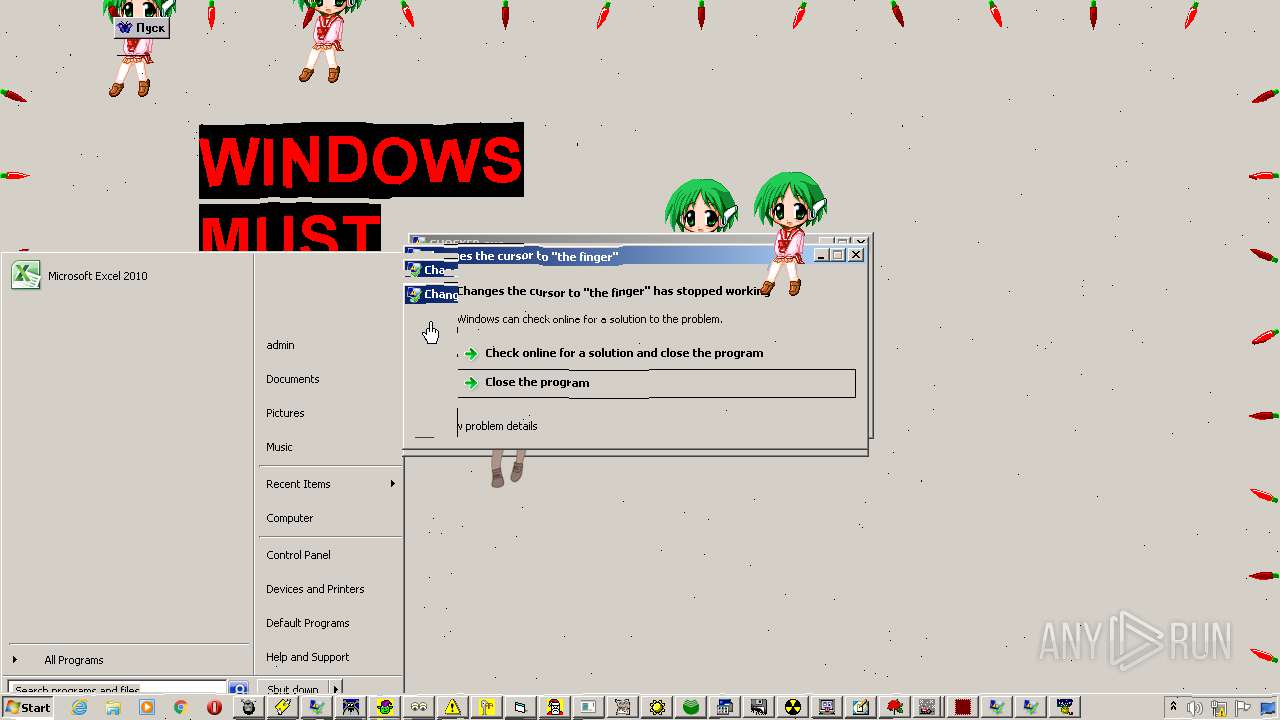
- middlefinger.exe (PID: 928)
- randomness.exe (PID: 1812)
- InvertMouse.exe (PID: 3500)
- LIZ.EXE (PID: 1864)
- float.exe (PID: 1856)
- jeprus.exe (PID: 3572)
- sante clous for window.EXE (PID: 2496)
- restat.exe (PID: 3788)
- Mouse Overheat.exe (PID: 3056)
- LARRY.EXE (PID: 1992)
- Kamika.exe (PID: 3752)
- MousePad.exe (PID: 872)
- Free porn.exe (PID: 3992)
- Ghost.exe (PID: 4060)
- hidder.exe (PID: 2144)
- pen.exe (PID: 3320)
- harddrive.exe (PID: 2296)
- GhostMouse.exe (PID: 748)
- PUSK4U.EXE (PID: 3592)
- anywork.exe (PID: 2568)
- XMASLTS.EXE (PID: 3584)
- brisk.exe (PID: 2608)
- HildaTurkey.exe (PID: 3448)
- AWMULTI3.EXE (PID: 3860)
- Realistic Format Virus.exe (PID: 924)
- Suprise.exe (PID: 3136)
- click here.exe (PID: 2924)
- HEADACHE.EXE (PID: 1636)
- Poltergeist.exe (PID: 3416)
Loads dropped or rewritten executable
- kona_dancer.exe (PID: 2224)
SUSPICIOUS
Checks supported languages
- Bokusatsu Tenshi Full Anime Watch.exe (PID: 916)
- cmd.exe (PID: 2112)
- AWMULTI3.EXE (PID: 3860)
- bonce.exe (PID: 2620)
- anywork.exe (PID: 2568)
- australia.exe (PID: 2492)
- brisk.exe (PID: 2608)
- click here.exe (PID: 2924)
- BUG.EXE (PID: 2444)
- Close Programs.exe (PID: 4012)
- blast button.exe (PID: 1868)
- come too me.exe (PID: 3204)
- Deathwishdog.exe (PID: 3488)
- Crazy Mouse v1.2.exe (PID: 3336)
- CrazyMouse.exe (PID: 3356)
- BURP.EXE (PID: 2708)
- ELVES.EXE (PID: 2236)
- float.exe (PID: 1856)
- Ghost.exe (PID: 4060)
- Icons 2.exe (PID: 3148)
- Evil's Crazy Mouse....exe (PID: 476)
- HEADACHE.EXE (PID: 1636)
- hidder.exe (PID: 2144)
- HildaTurkey.exe (PID: 3448)
- Icons.exe (PID: 2856)
- harddrive.exe (PID: 2296)
- GhostMouse.exe (PID: 748)
- Free porn.exe (PID: 3992)
- IDIOT.exe (PID: 2920)
- InvertMouse.exe (PID: 3500)
- jeprus.exe (PID: 3572)
- ILoveYou.exe (PID: 3332)
- LIZ.EXE (PID: 1864)
- Kamika.exe (PID: 3752)
- kona_dancer.exe (PID: 2224)
- KorOvki.exe (PID: 4072)
- LARRY.EXE (PID: 1992)
- MousePad.exe (PID: 872)
- middlefinger.exe (PID: 928)
- MIGHTY FUCKER.exe (PID: 1008)
- Mouse Overheat.exe (PID: 3056)
- melter.exe (PID: 3688)
- MoveMouse.exe (PID: 3864)
- pen.exe (PID: 3320)
- Poltergeist.exe (PID: 3416)
- PUSK4U.EXE (PID: 3592)
- ReadMe.exe (PID: 3748)
- restat.exe (PID: 3788)
- randomness.exe (PID: 1812)
- Reverse.exe (PID: 3940)
- SANTA.EXE (PID: 2356)
- sante clous for window.EXE (PID: 2496)
- SHOCKER.exe (PID: 1192)
- Realistic Format Virus.exe (PID: 924)
- SHOCKERR.exe (PID: 1016)
- Snow for Windows.exe (PID: 2808)
- Suprise.exe (PID: 3136)
- XMASLTS.EXE (PID: 3584)
- starter.exe (PID: 3008)
- Virus1.exe (PID: 3096)
- ???????? ??????? ????????.exe (PID: 3436)
- ????_original.exe (PID: 3304)
- ??????? ????????.exe (PID: 1444)
Drops a file that was compiled in debug mode
- Bokusatsu Tenshi Full Anime Watch.exe (PID: 916)
Reads the computer name
- Bokusatsu Tenshi Full Anime Watch.exe (PID: 916)
- Icons 2.exe (PID: 3148)
- Icons.exe (PID: 2856)
- BURP.EXE (PID: 2708)
- SHOCKERR.exe (PID: 1016)
- KorOvki.exe (PID: 4072)
- jeprus.exe (PID: 3572)
- kona_dancer.exe (PID: 2224)
- Poltergeist.exe (PID: 3416)
- SHOCKER.exe (PID: 1192)
- blast button.exe (PID: 1868)
- MIGHTY FUCKER.exe (PID: 1008)
Drops a file with too old compile date
- Bokusatsu Tenshi Full Anime Watch.exe (PID: 916)
- kona_dancer.exe (PID: 2224)
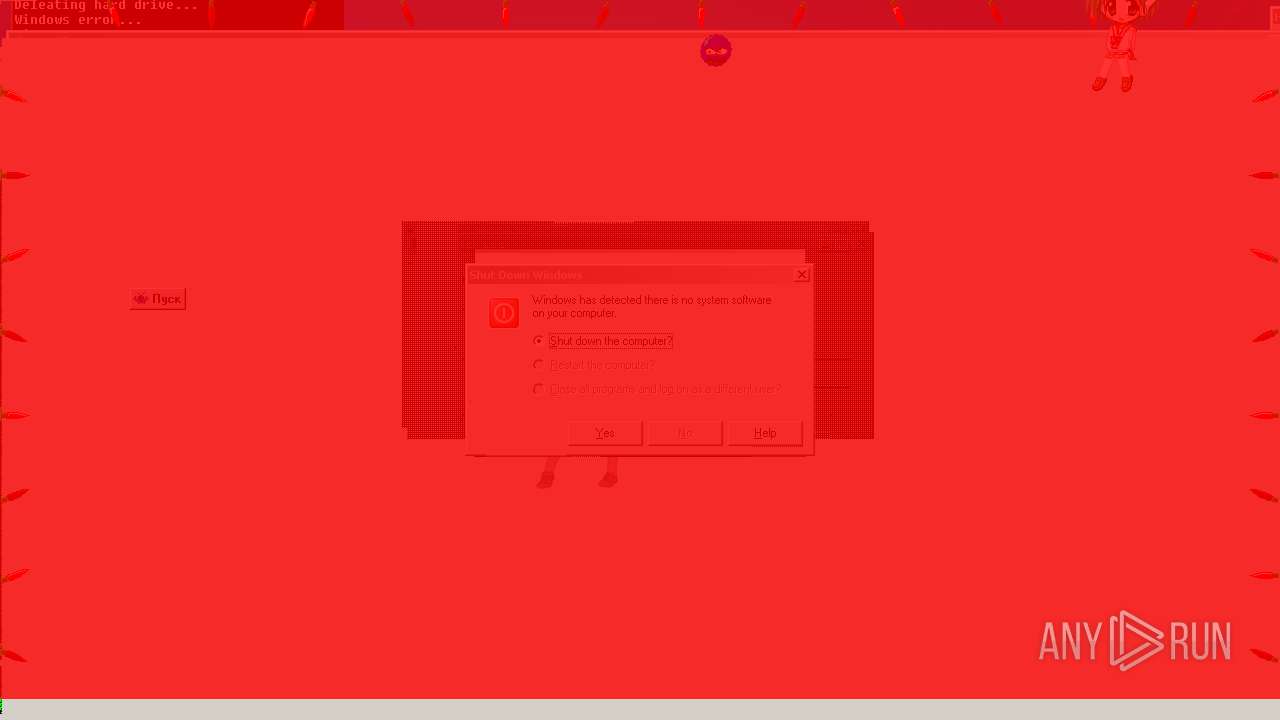
Executable content was dropped or overwritten
- Bokusatsu Tenshi Full Anime Watch.exe (PID: 916)
- kona_dancer.exe (PID: 2224)
Starts CMD.EXE for commands execution
- Bokusatsu Tenshi Full Anime Watch.exe (PID: 916)
Drops a file with a compile date too recent
- Bokusatsu Tenshi Full Anime Watch.exe (PID: 916)
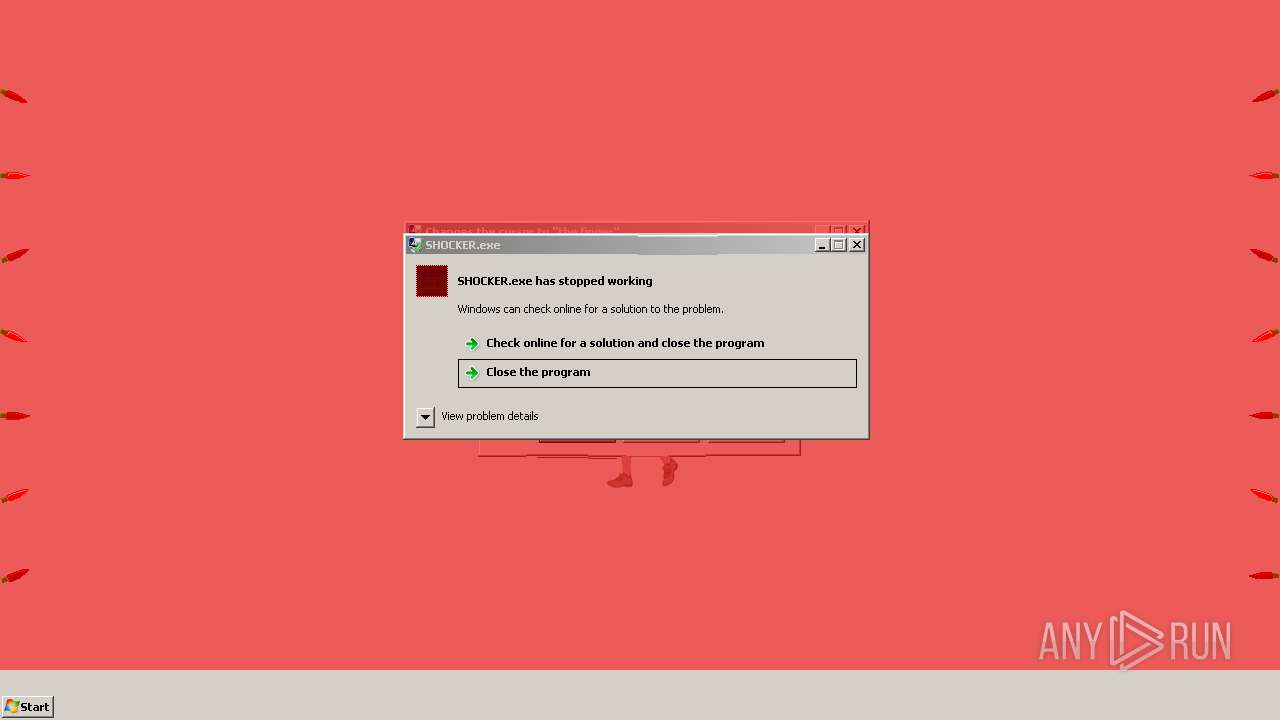
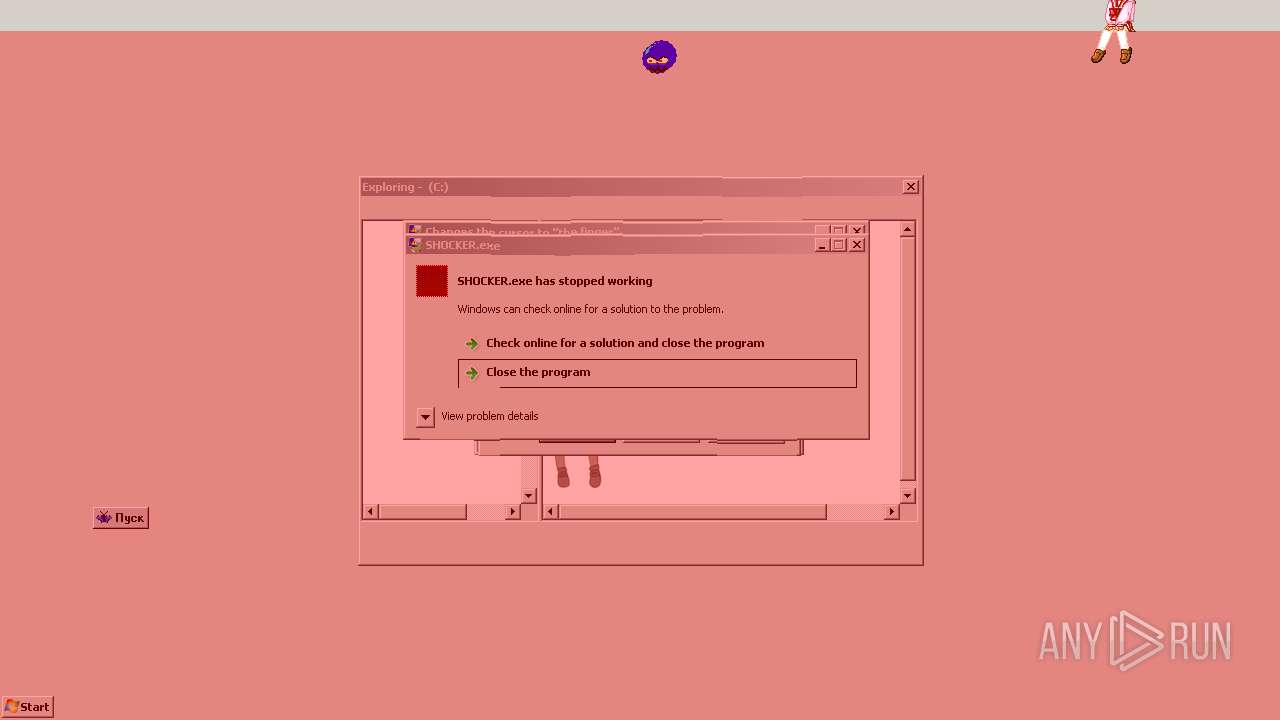
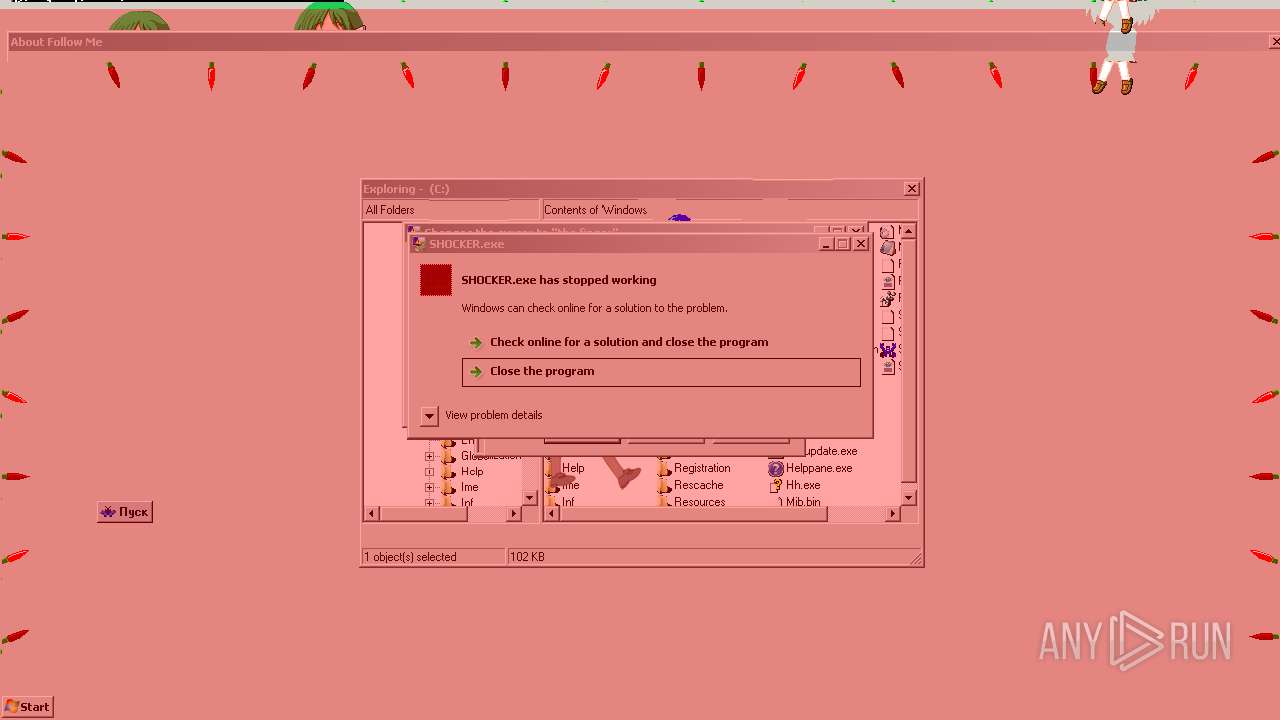
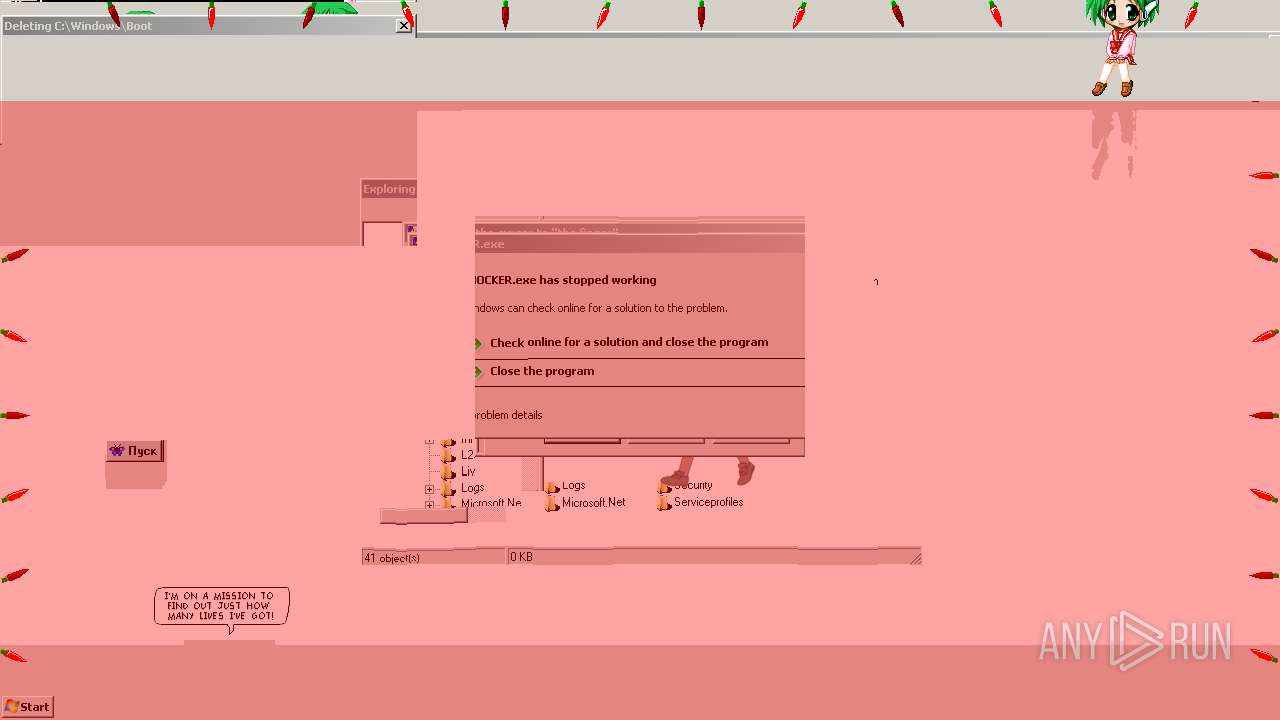
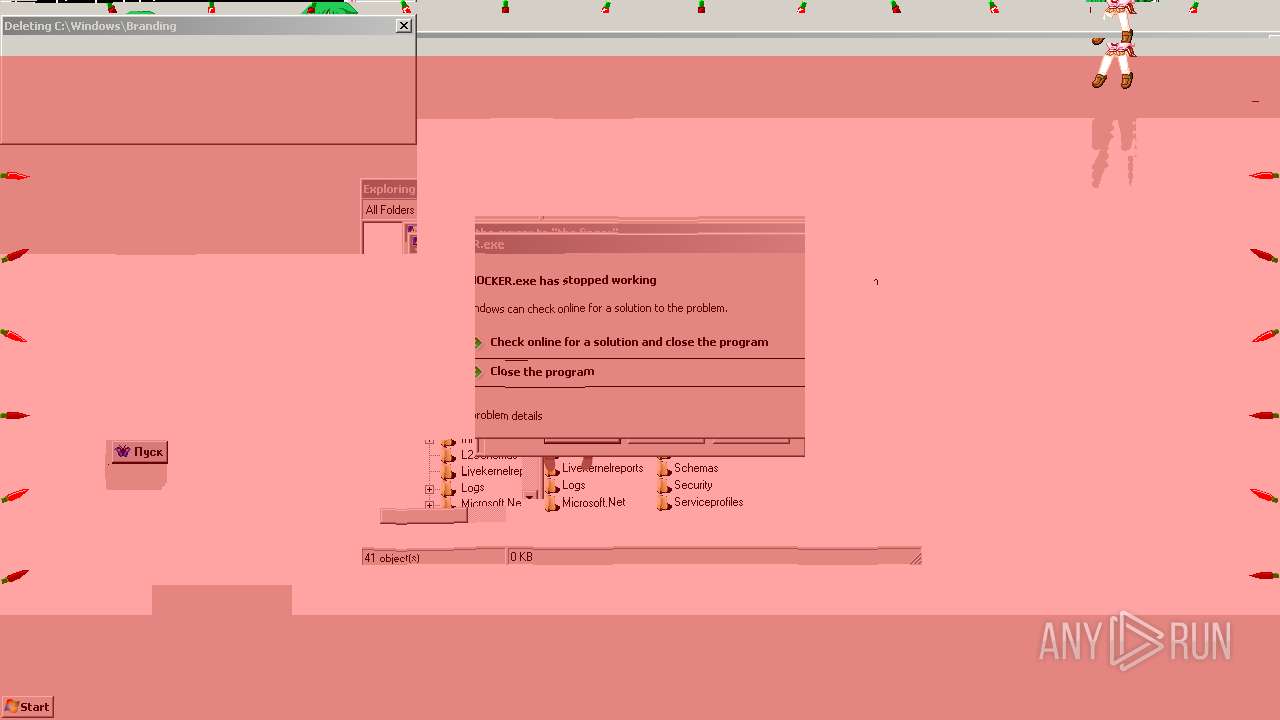
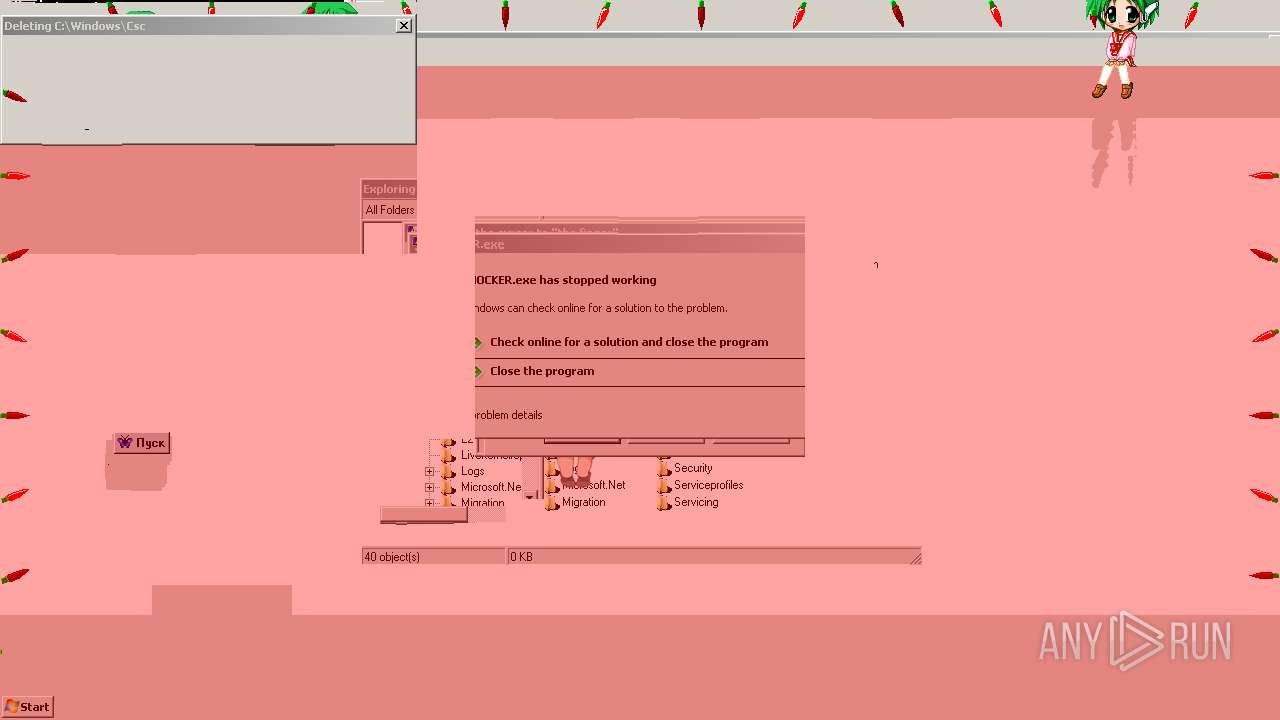
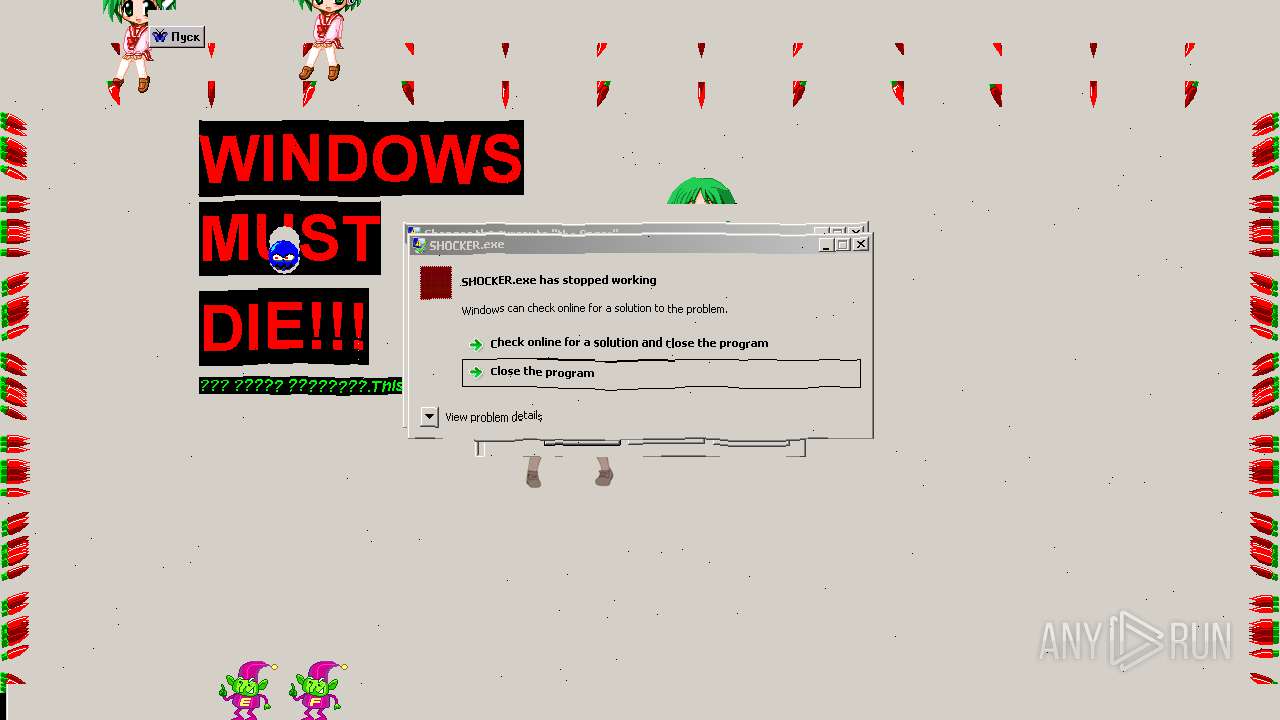
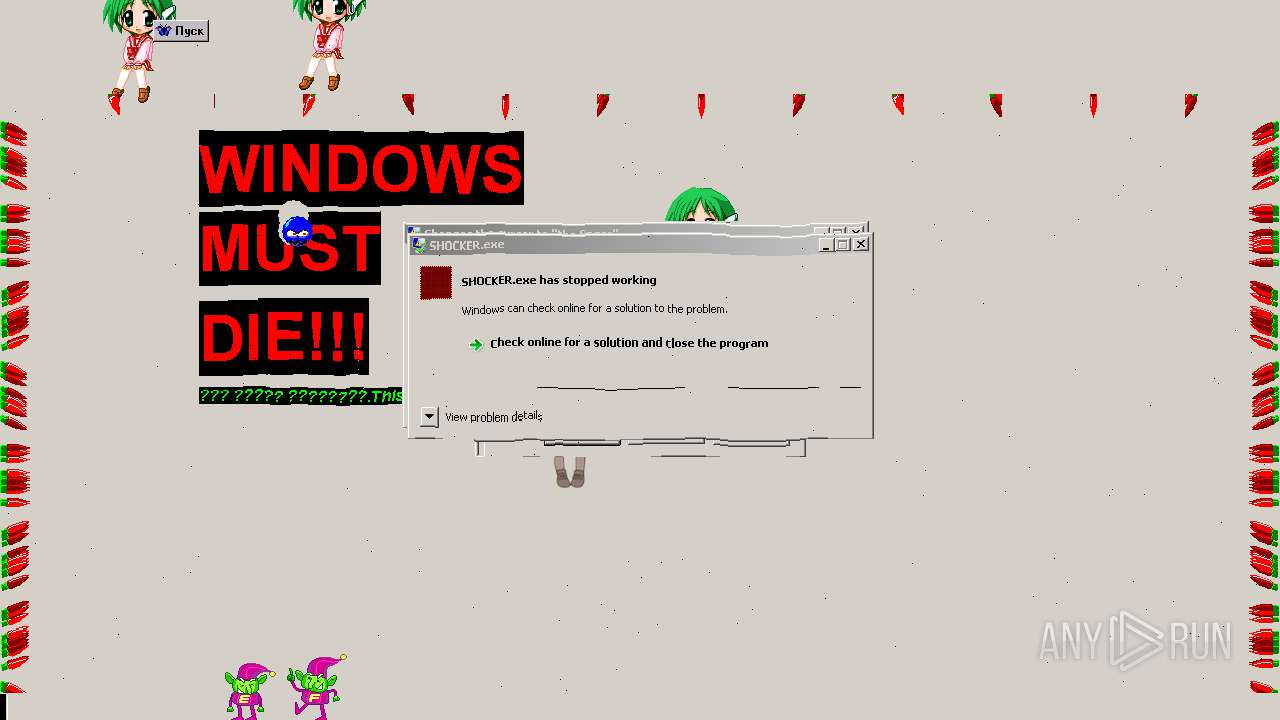
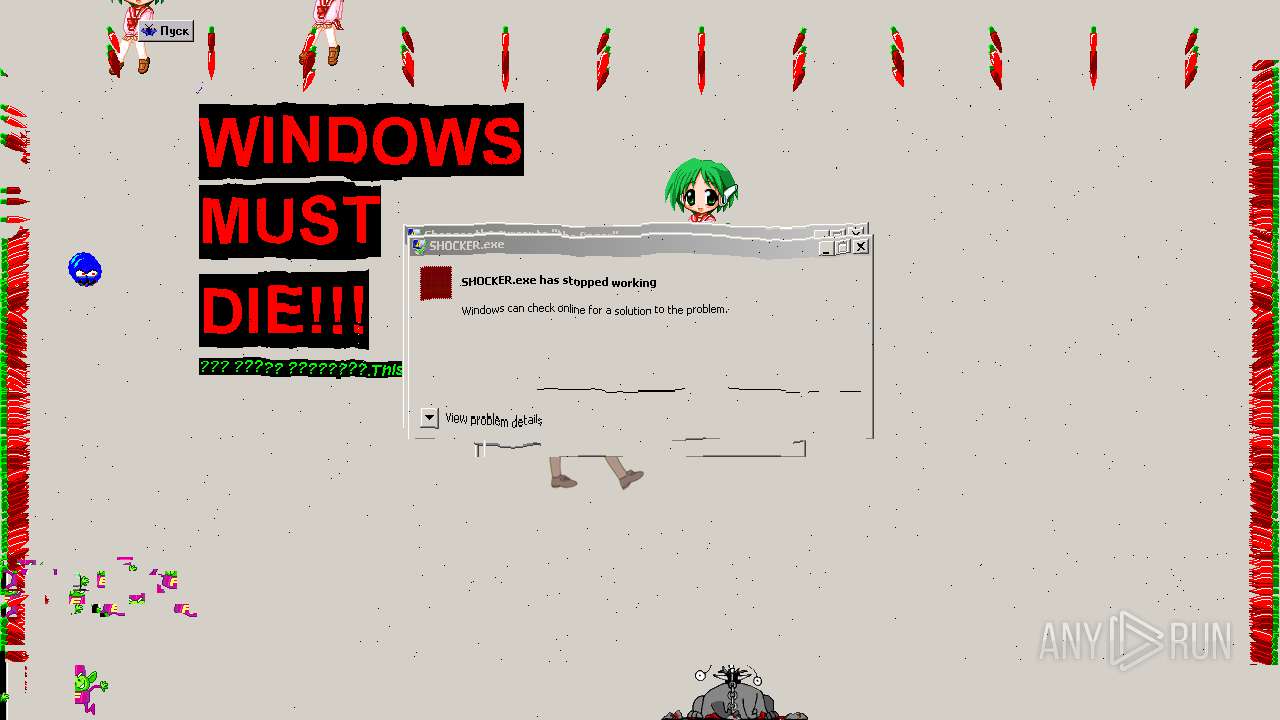
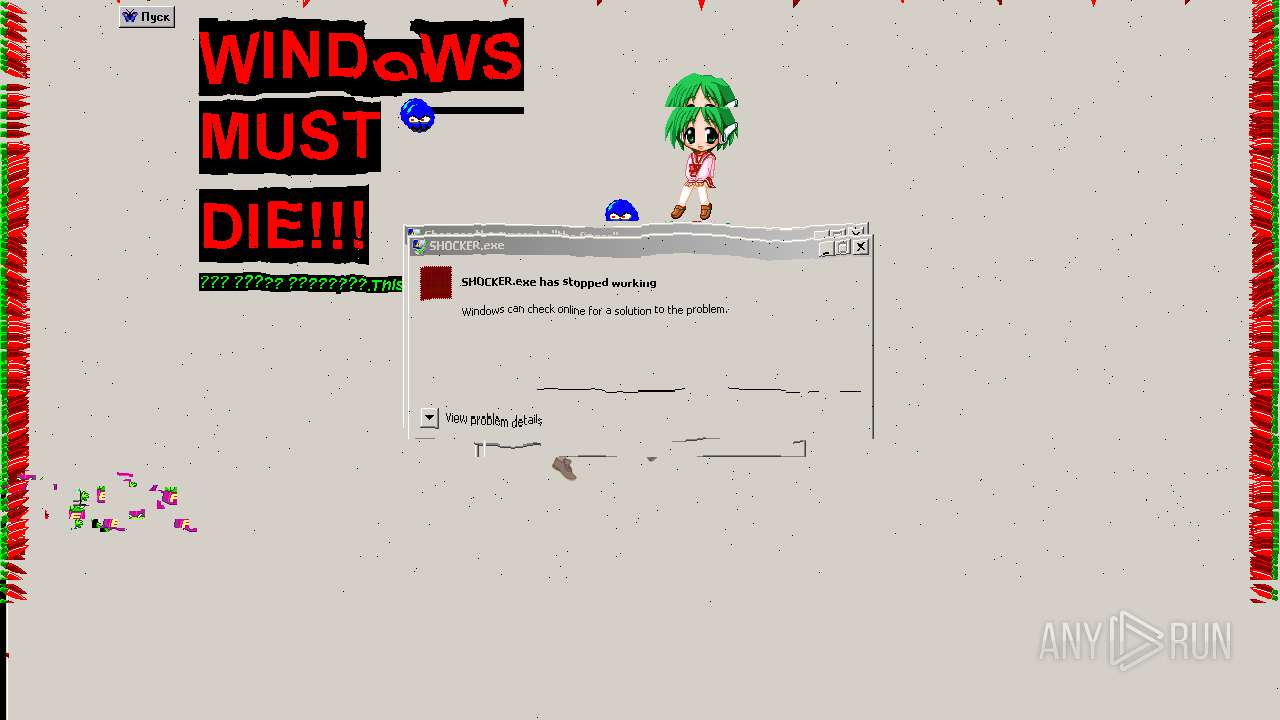
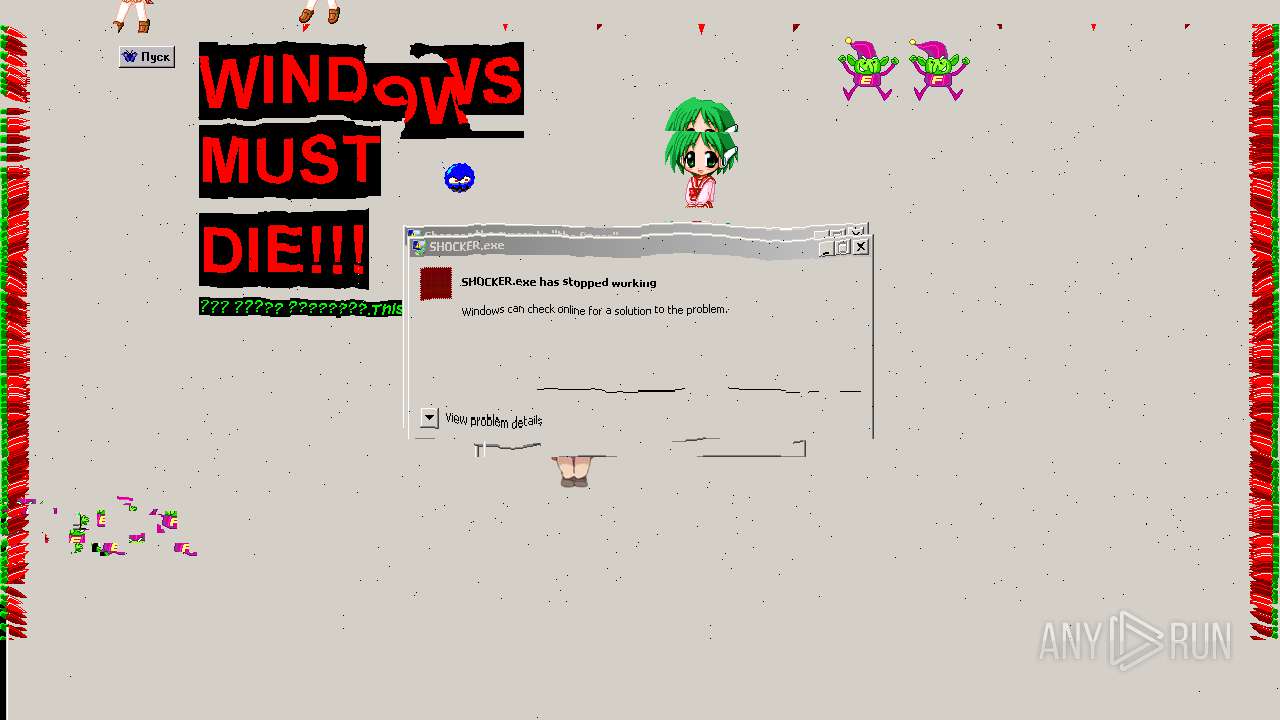
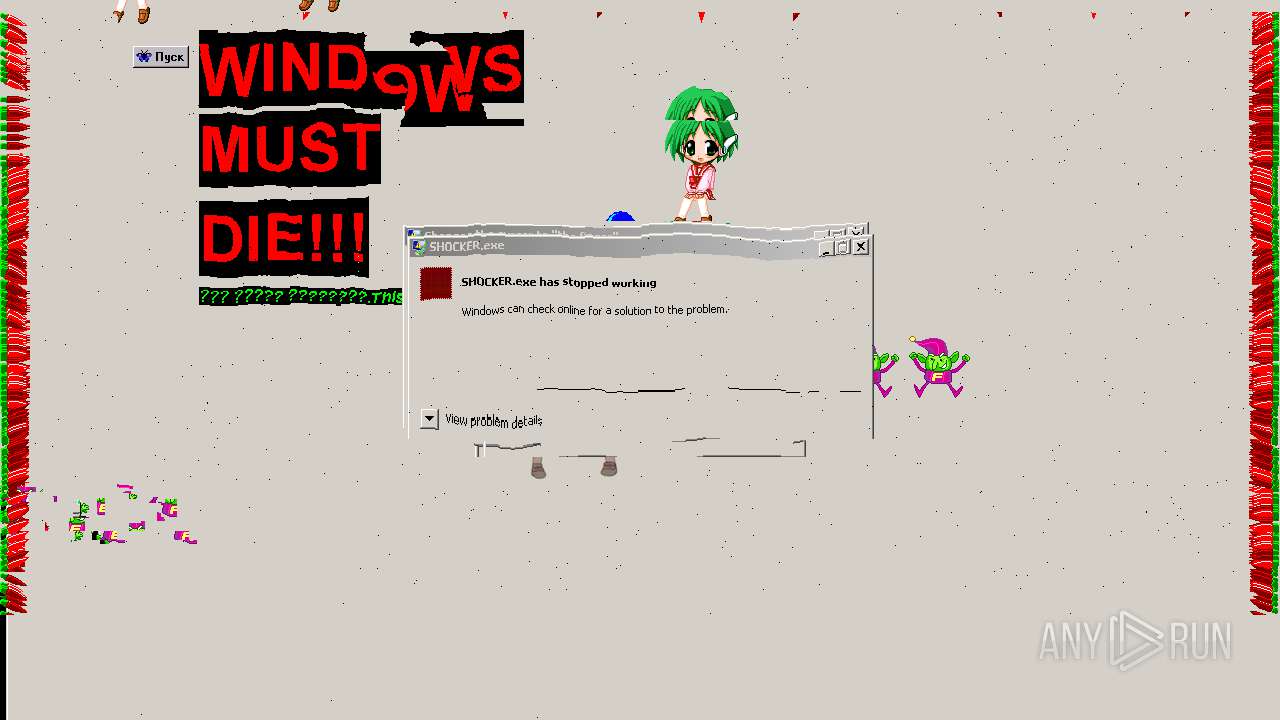
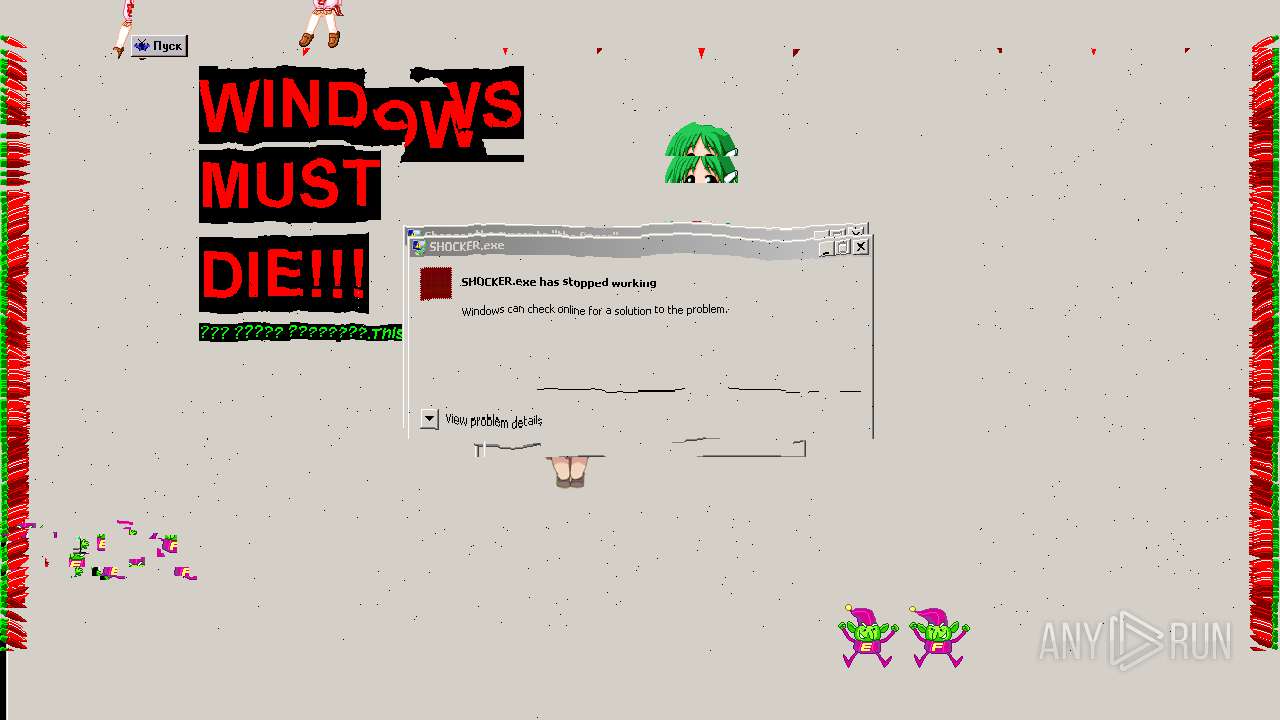
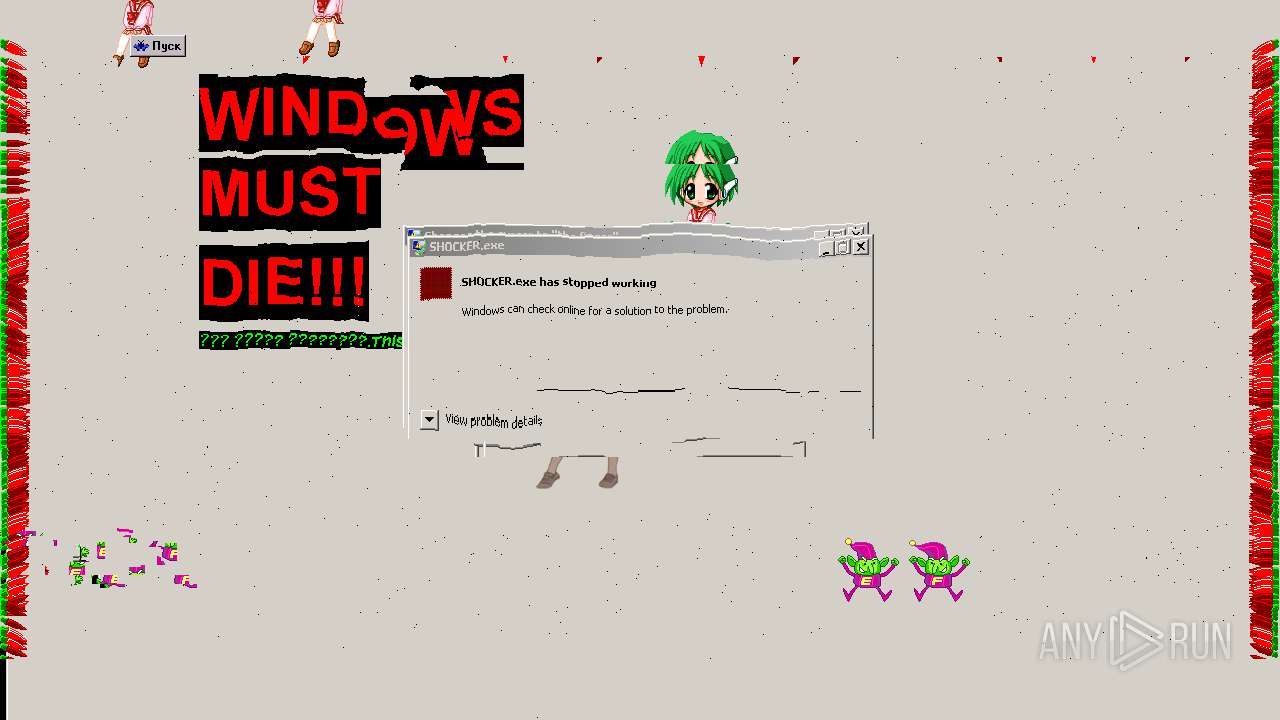
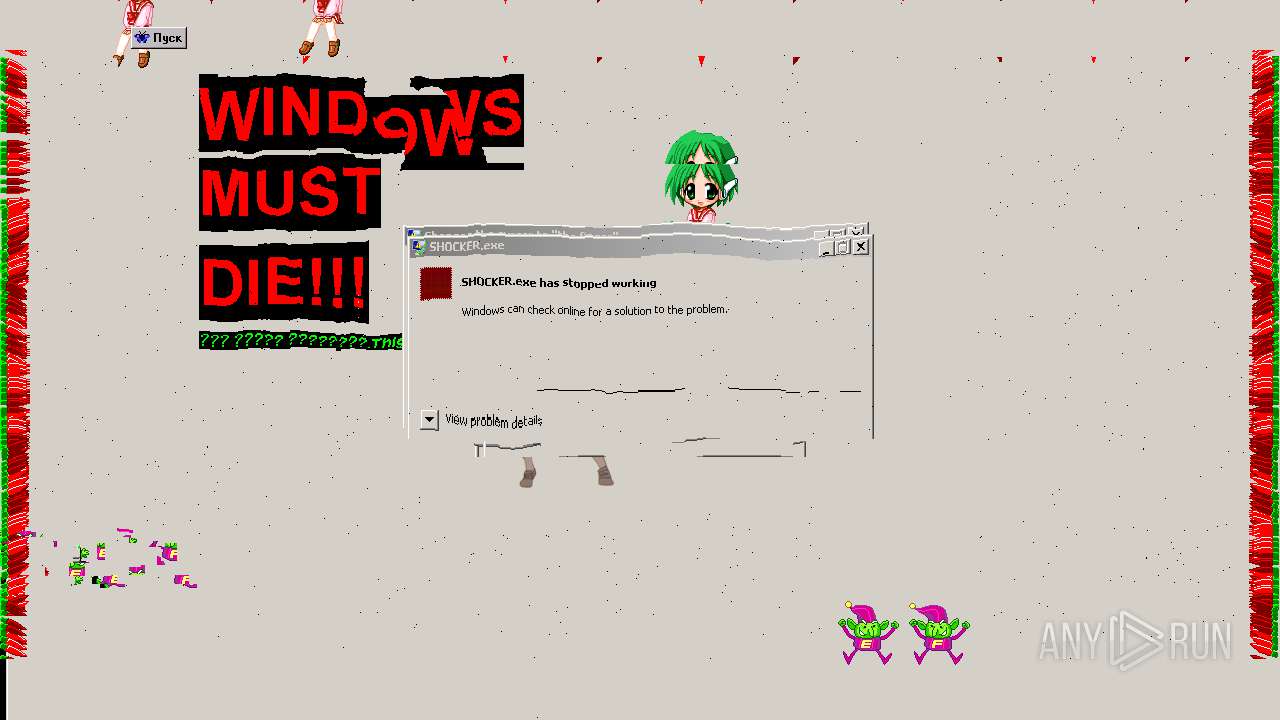
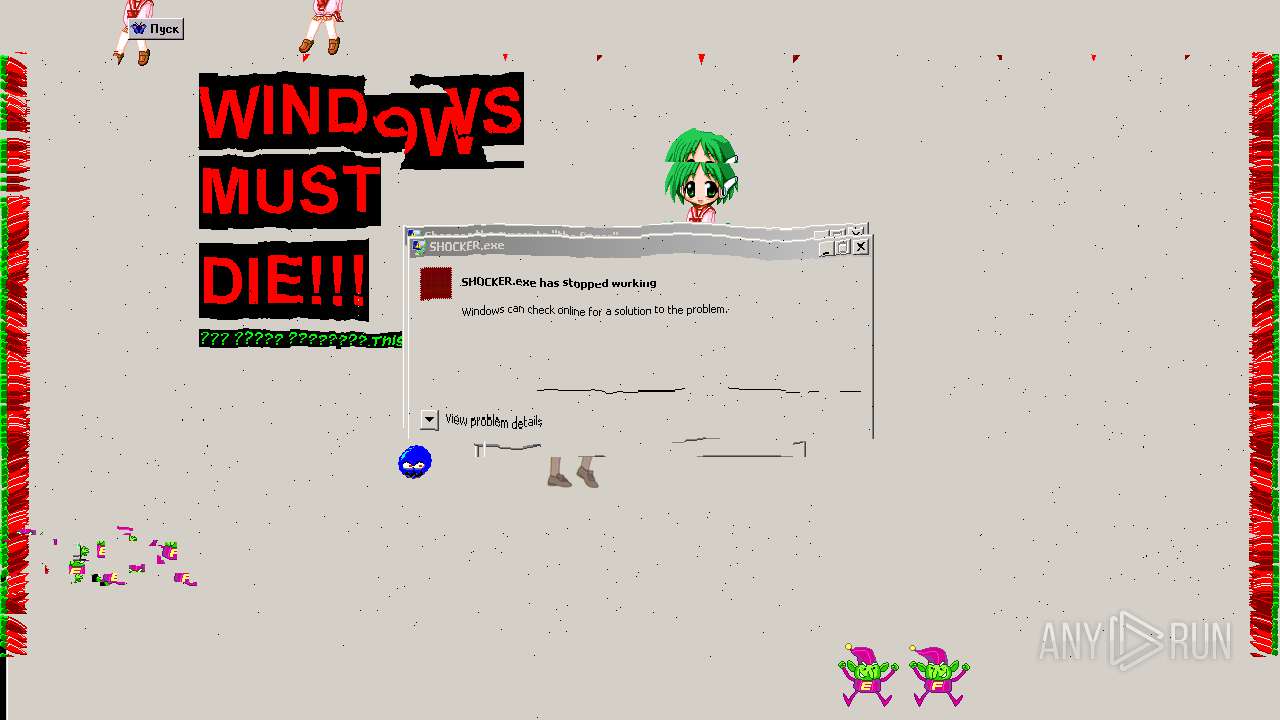
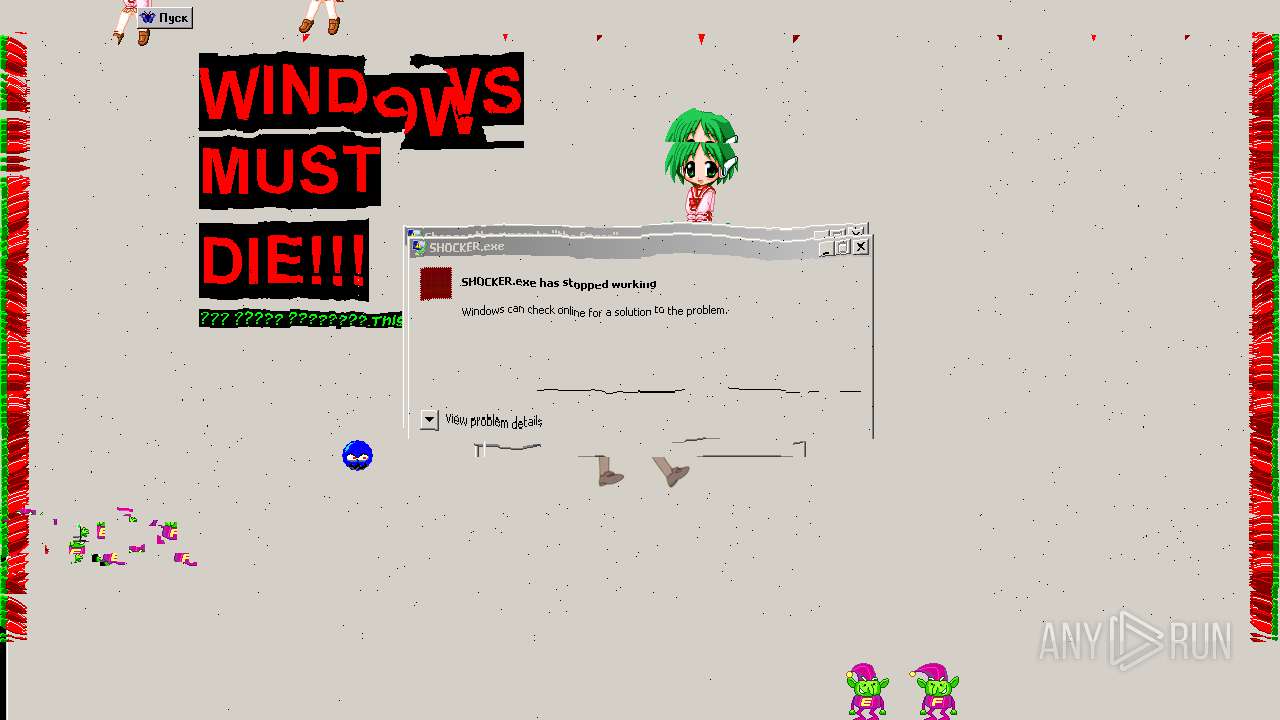
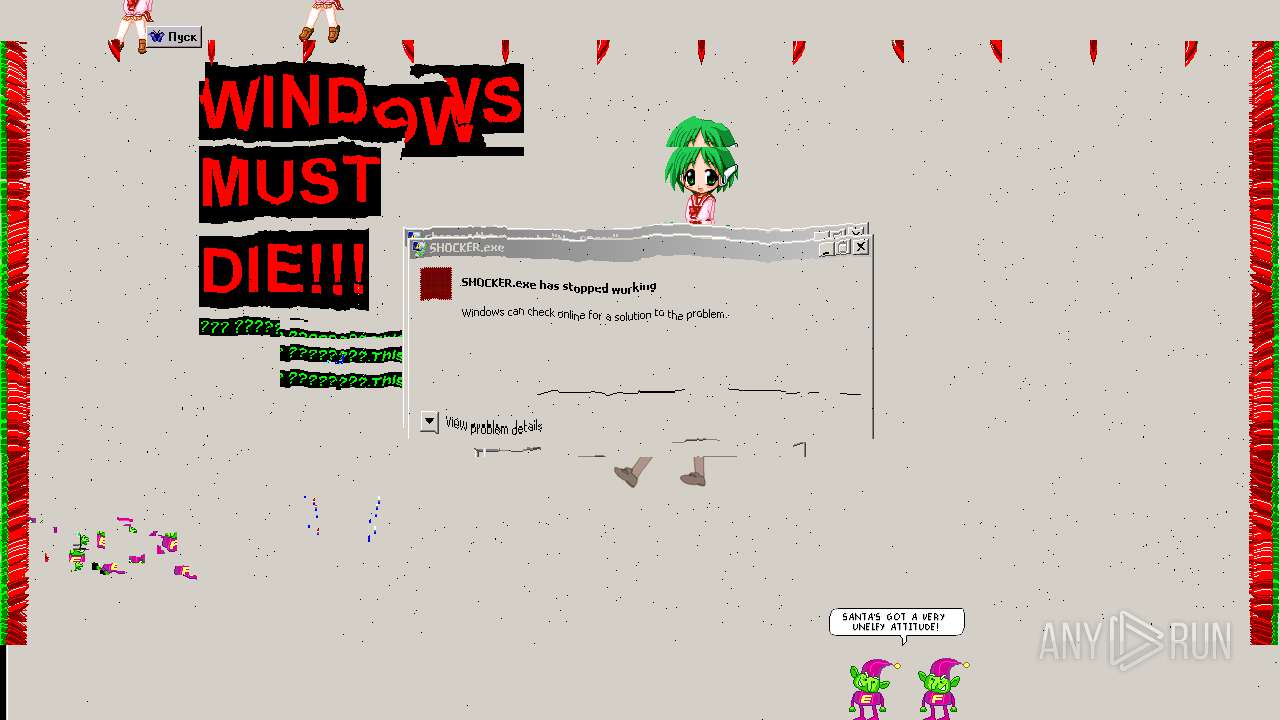
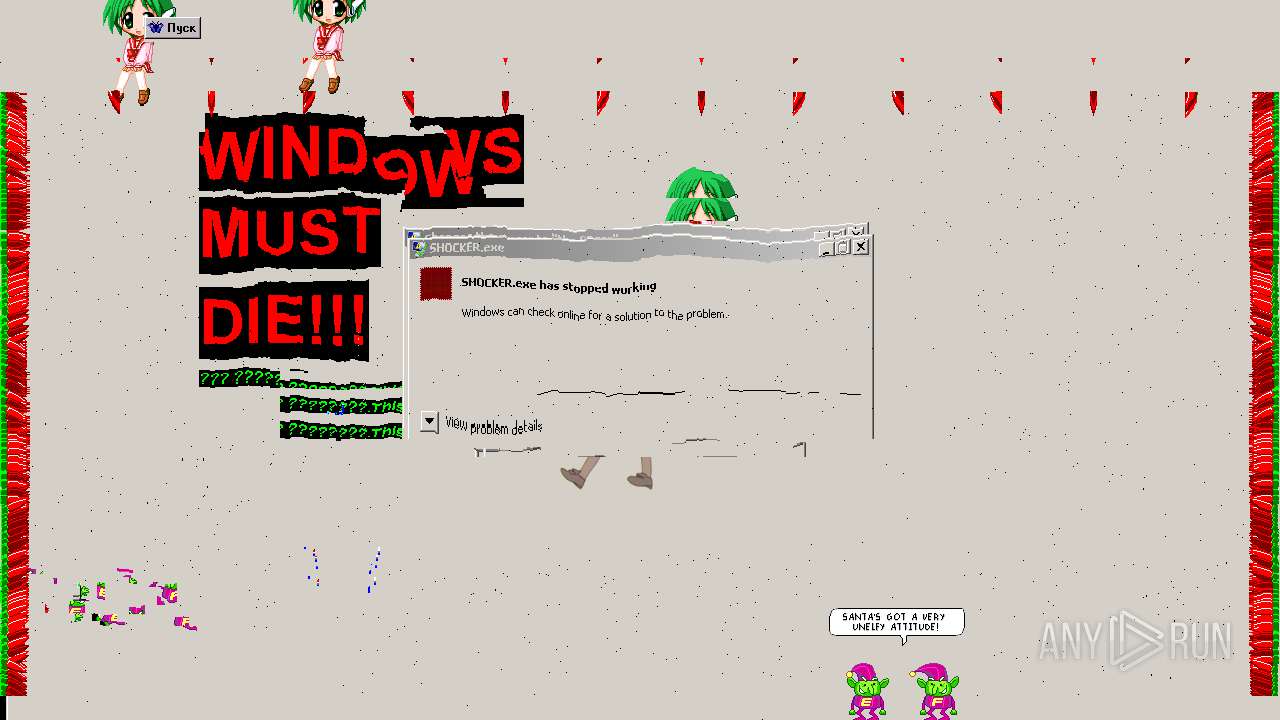
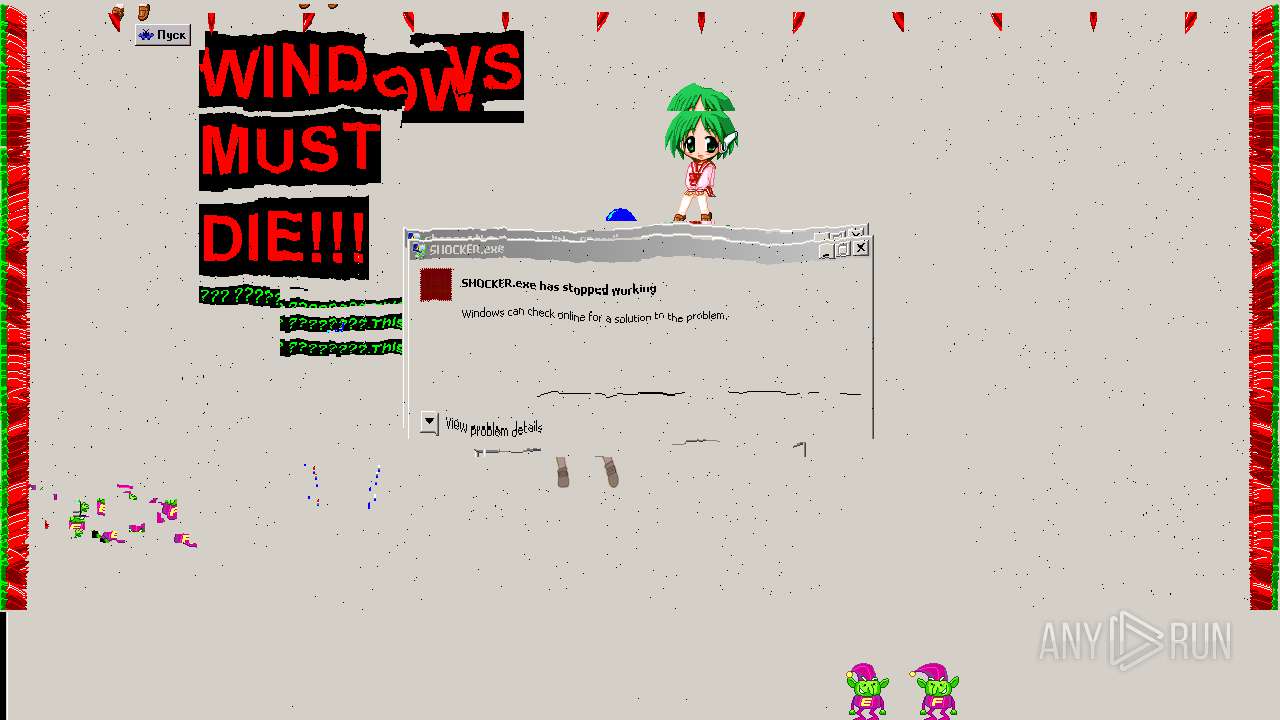
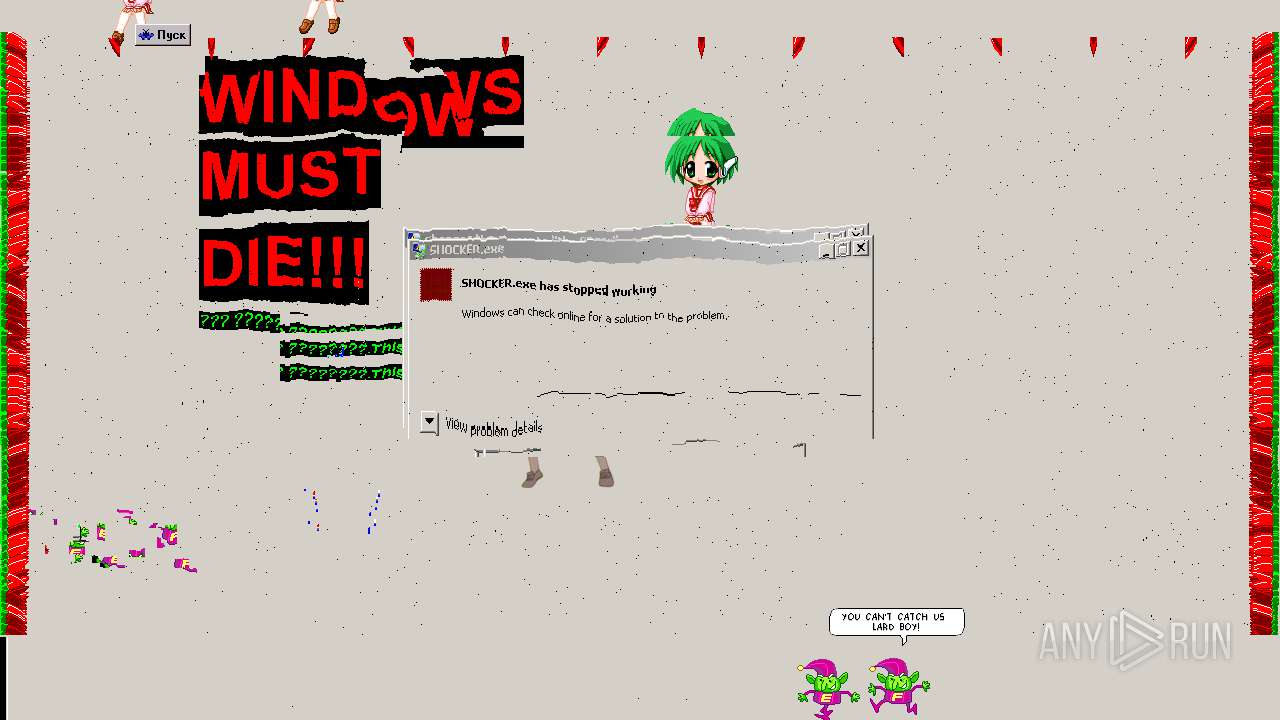
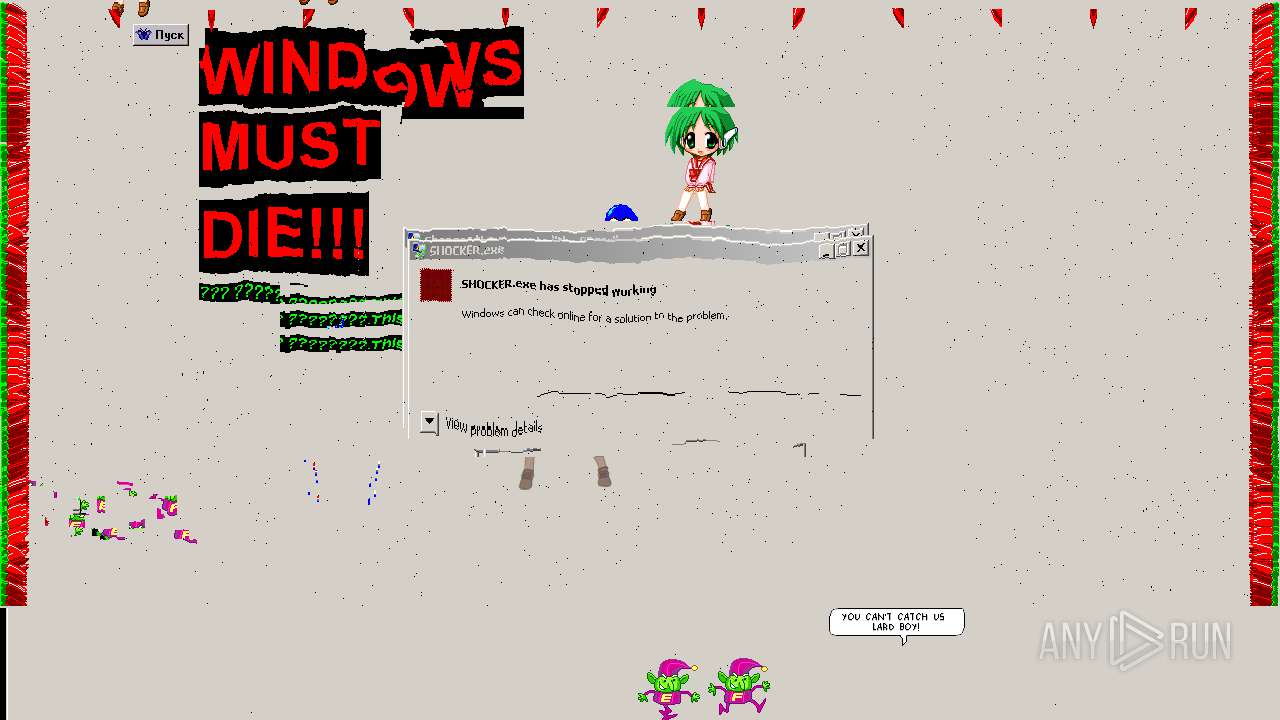
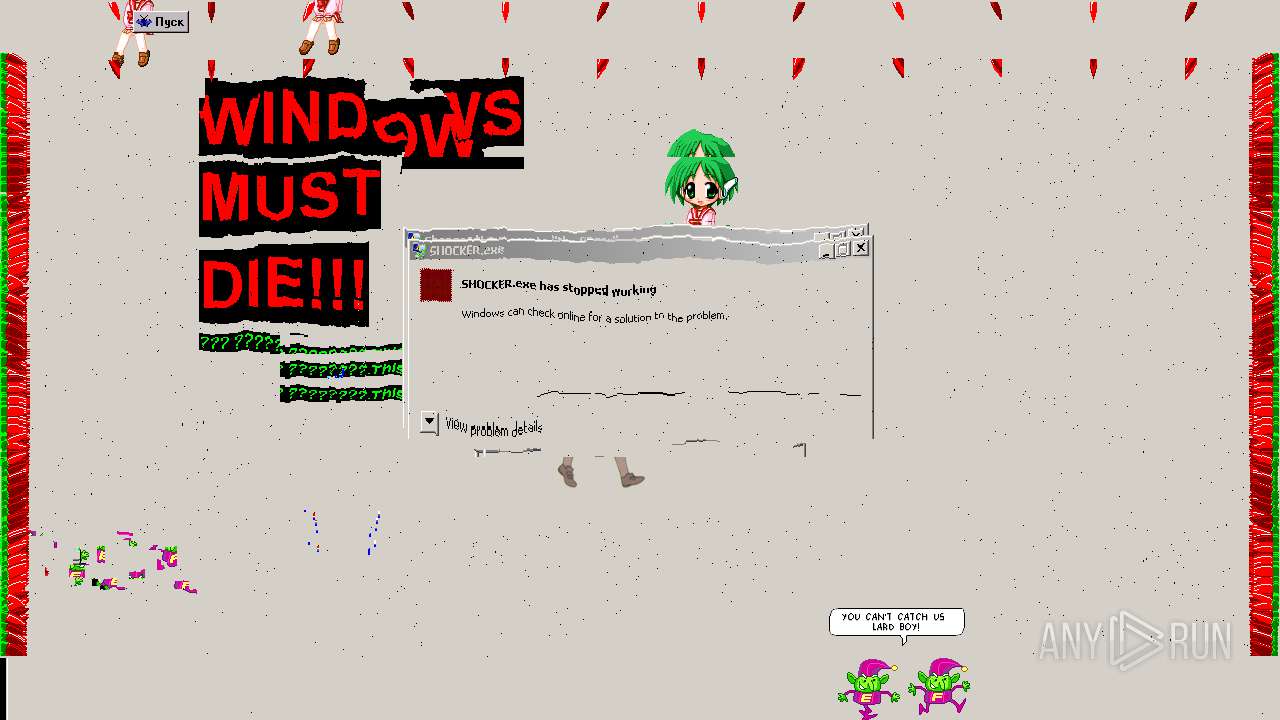
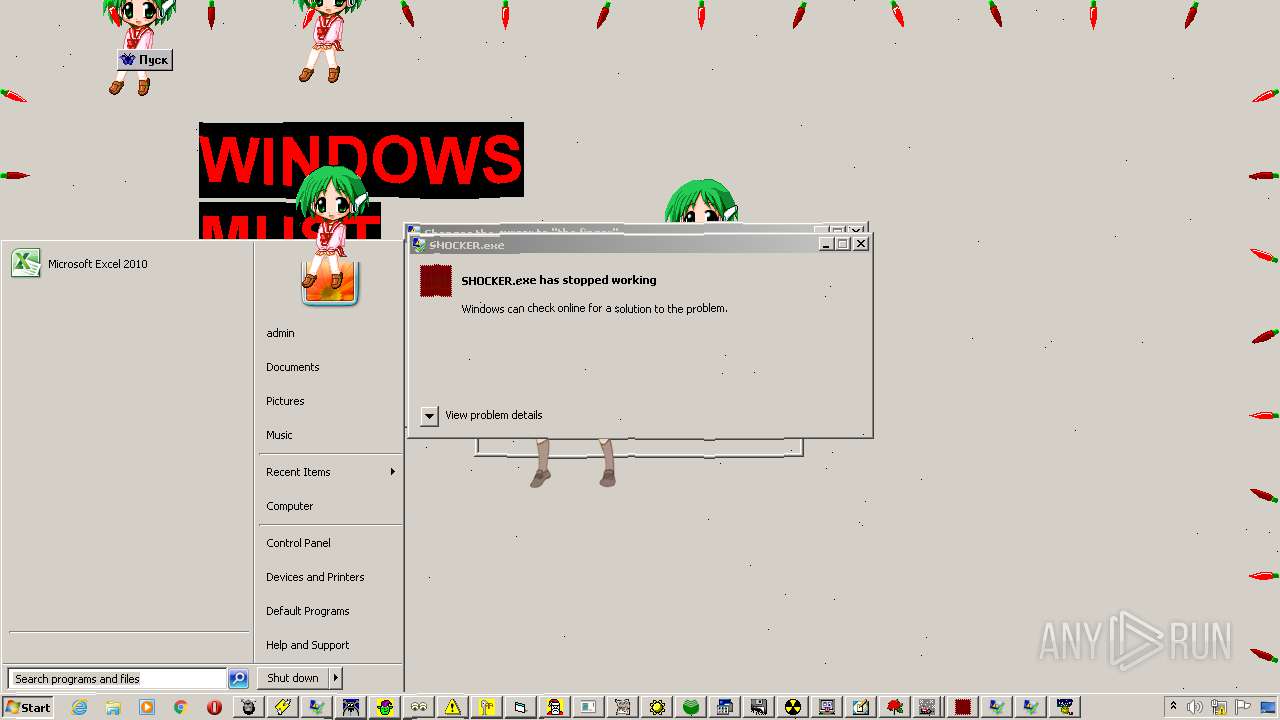
Executes application which crashes
- cmd.exe (PID: 2112)
Reads mouse settings
- Realistic Format Virus.exe (PID: 924)
Creates files in the user directory
- kona_dancer.exe (PID: 2224)
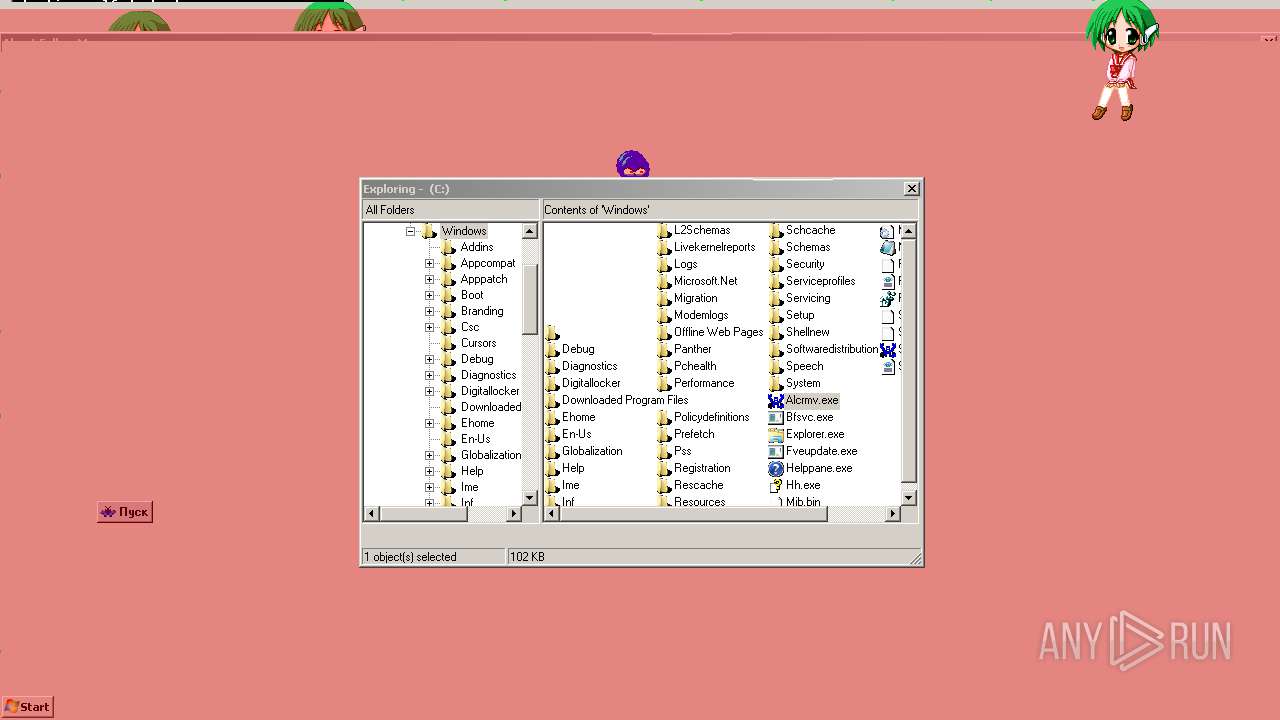
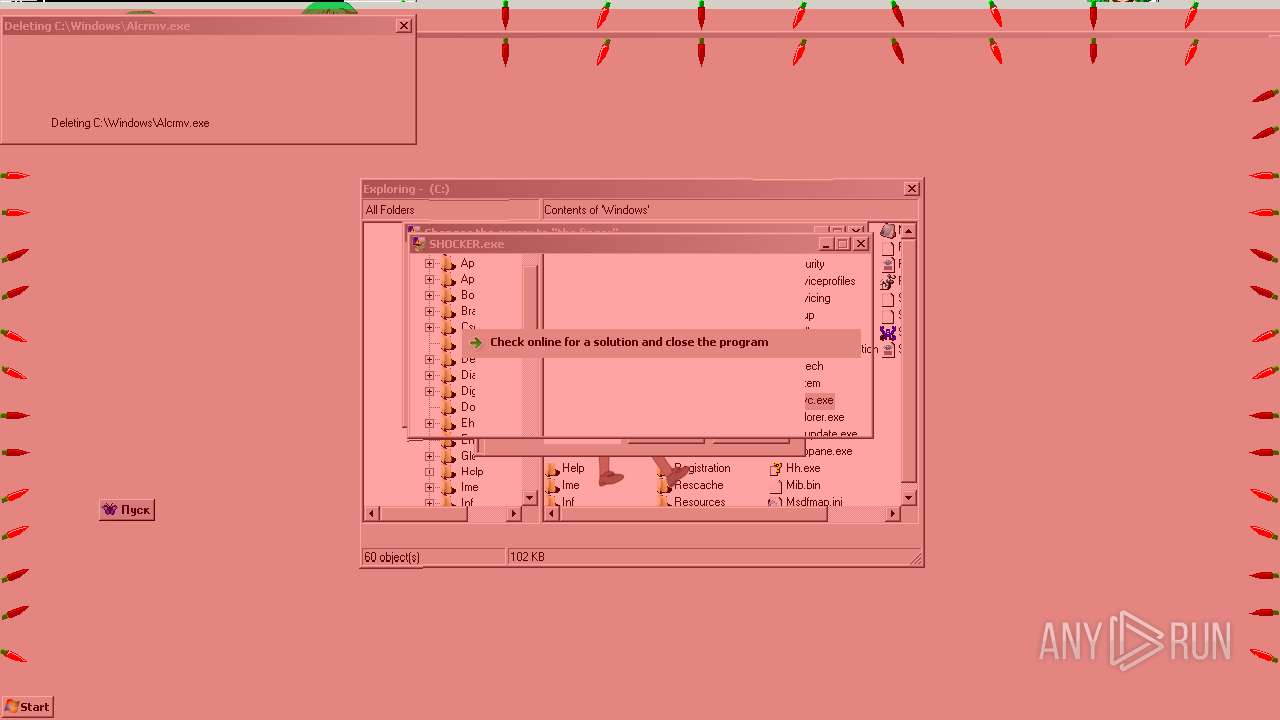
Creates files in the Windows directory
- Realistic Format Virus.exe (PID: 924)
INFO
Dropped object may contain Bitcoin addresses
- Bokusatsu Tenshi Full Anime Watch.exe (PID: 916)
Checks supported languages
- ntvdm.exe (PID: 764)
Reads Microsoft Office registry keys
- Realistic Format Virus.exe (PID: 924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:04:07 16:39:28+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 156160 |
| InitializedDataSize: | 349696 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x13f30 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Apr-2021 14:39:28 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 07-Apr-2021 14:39:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000261FA | 0x00026200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70212 |
.rdata | 0x00028000 | 0x00009C24 | 0x00009E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.21587 |
.data | 0x00032000 | 0x00034DA8 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.80741 |
.didat | 0x00067000 | 0x0000015C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.98928 |
.rsrc | 0x00068000 | 0x00047CAC | 0x00047E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.17056 |
.reloc | 0x000B0000 | 0x00002820 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.61325 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.03775 | 67624 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 6.30964 | 38056 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 6.1989 | 21640 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 6.1871 | 16936 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 6.39685 | 9640 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.11236 | 440 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
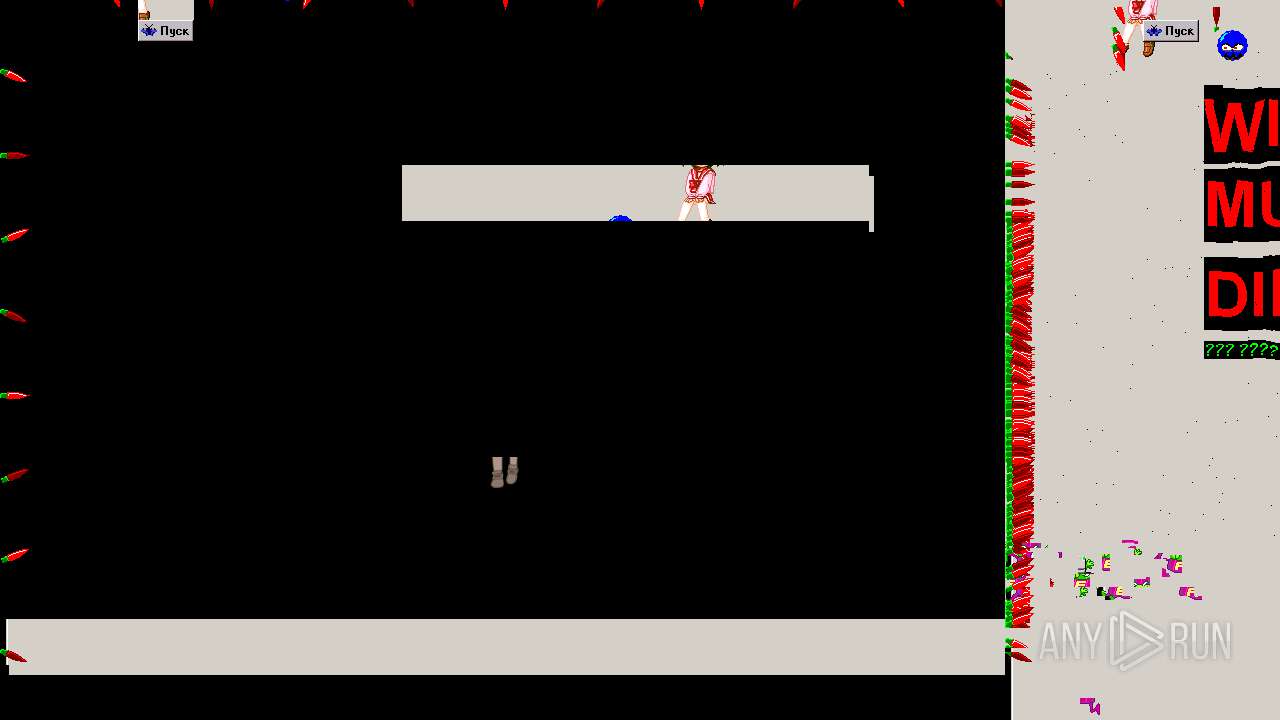
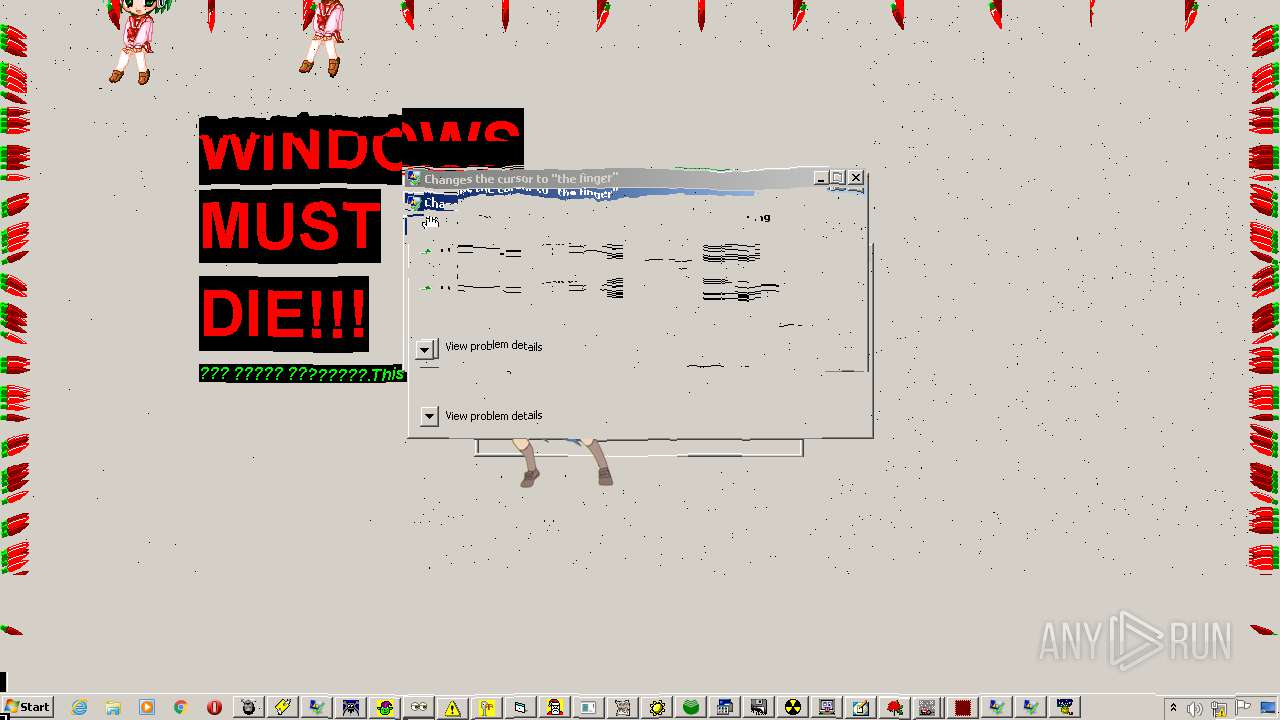
Total processes
101
Monitored processes
64
Malicious processes
8
Suspicious processes
22
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 476 | "Evil's Crazy Mouse....exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Evil's Crazy Mouse....exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 748 | "GhostMouse.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\GhostMouse.exe | — | cmd.exe | |||||||||||
User: admin Company: BSG Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 764 | "C:\Windows\system32\ntvdm.exe" -i1 -w | C:\Windows\system32\ntvdm.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 872 | "MousePad.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\MousePad.exe | — | cmd.exe | |||||||||||
User: admin Company: EN Soft Integrity Level: MEDIUM Exit code: 0 Version: 2.00 Modules
| |||||||||||||||
| 916 | "C:\Users\admin\AppData\Local\Temp\Bokusatsu Tenshi Full Anime Watch.exe" | C:\Users\admin\AppData\Local\Temp\Bokusatsu Tenshi Full Anime Watch.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 924 | "Realistic Format Virus.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Realistic Format Virus.exe | — | cmd.exe | |||||||||||
User: admin Company: BSG Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
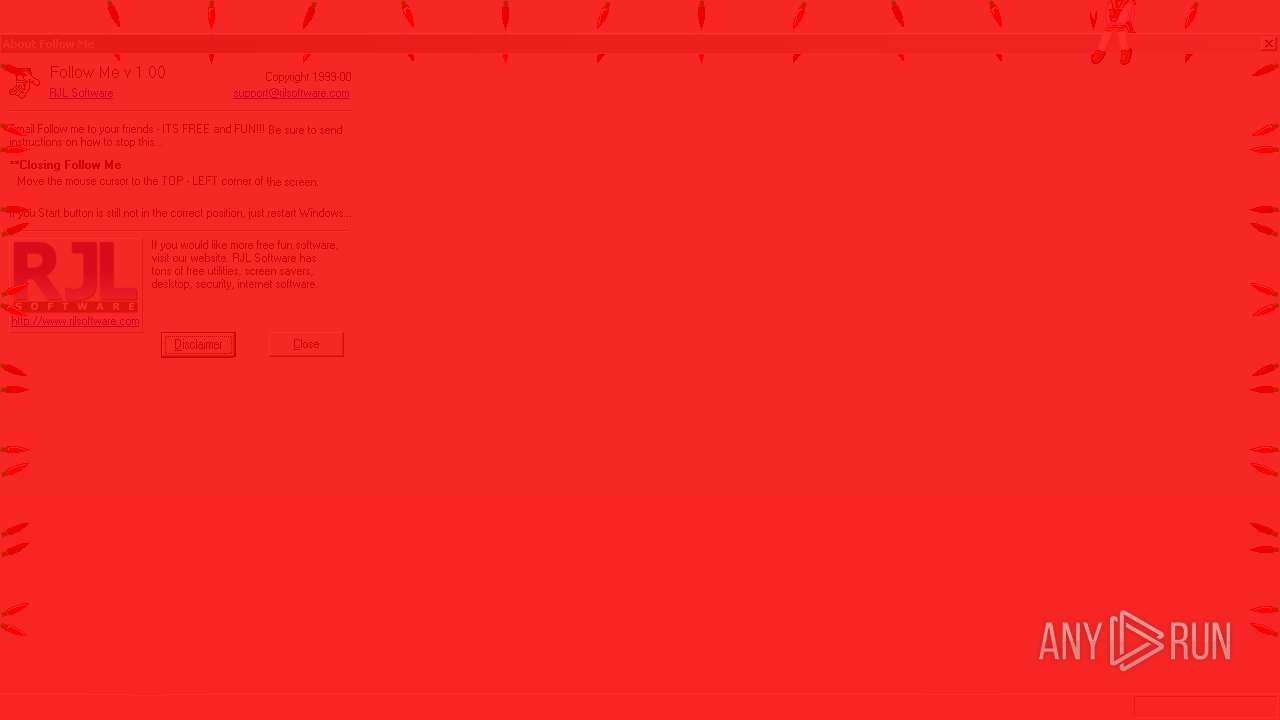
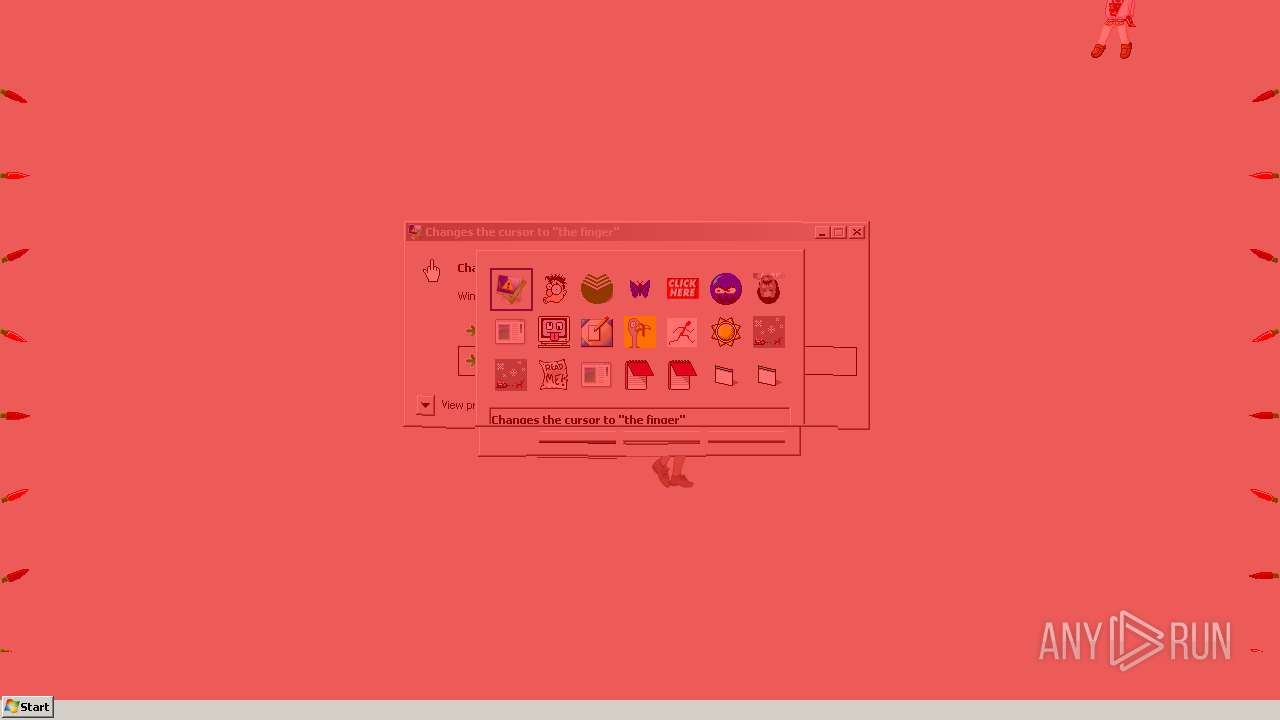
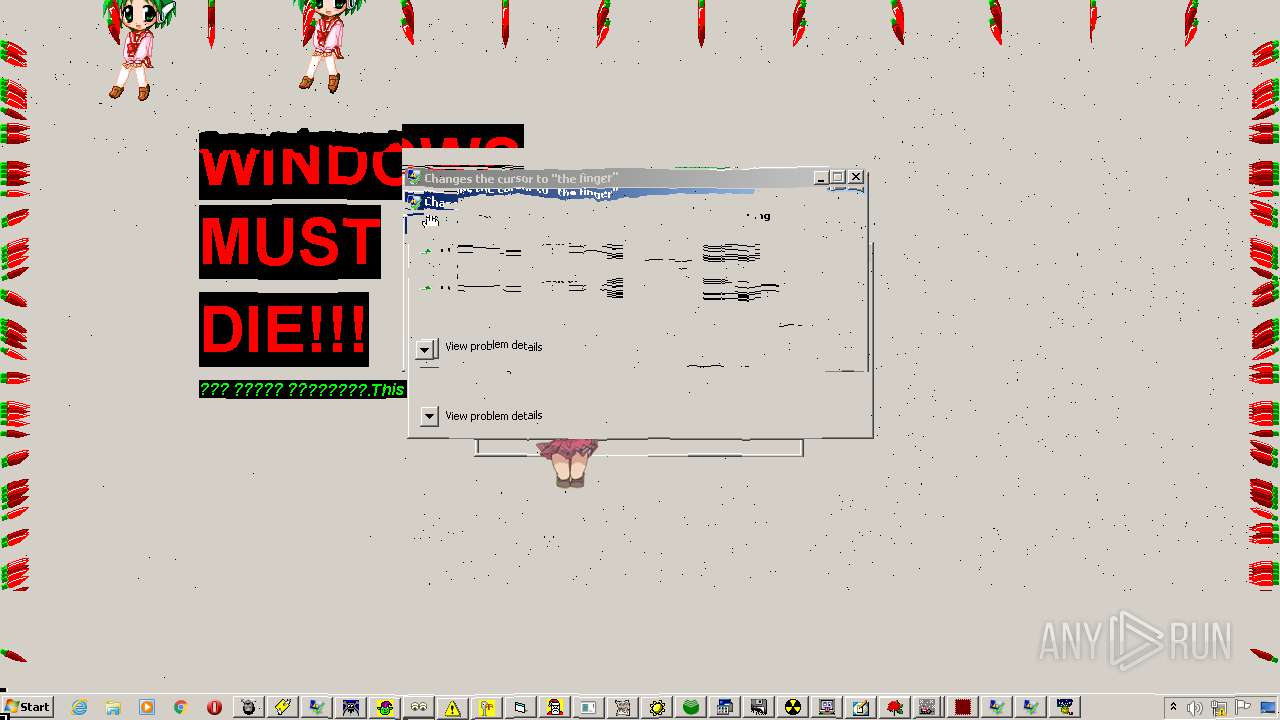
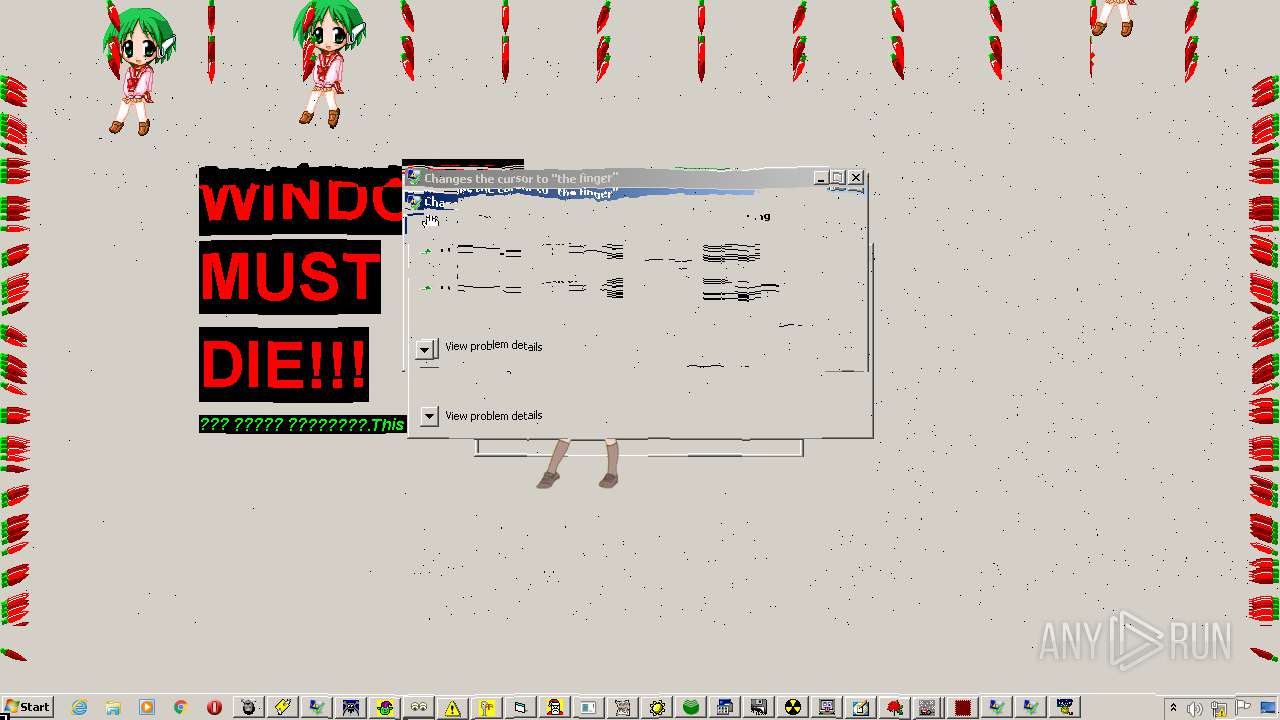
| 928 | "middlefinger.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\middlefinger.exe | cmd.exe | ||||||||||||
User: admin Company: RJL Software Integrity Level: MEDIUM Description: Changes the cursor to "the finger" Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1008 | "MIGHTY FUCKER.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\MIGHTY FUCKER.exe | — | cmd.exe | |||||||||||
User: admin Company: As your Ass Integrity Level: MEDIUM Description: Human nerve system collaptor Exit code: 0 Version: 1.2.0.0 Modules
| |||||||||||||||
| 1016 | "SHOCKERR.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\SHOCKERR.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
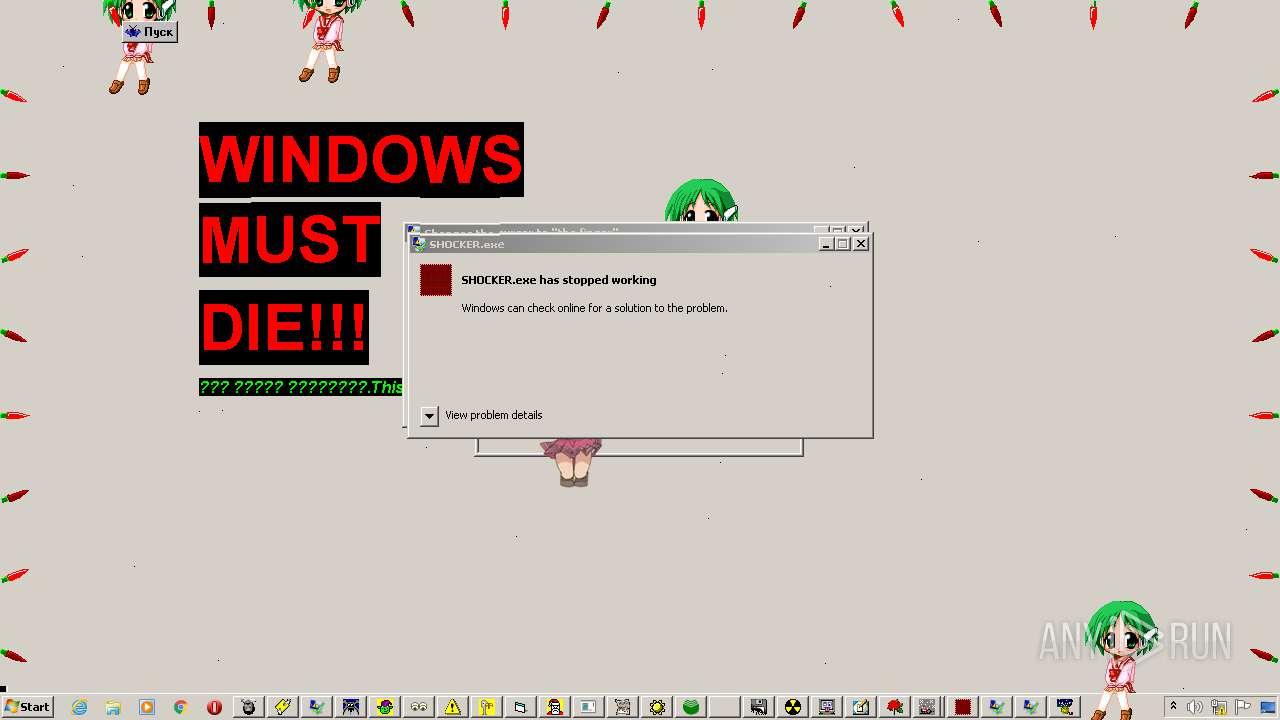
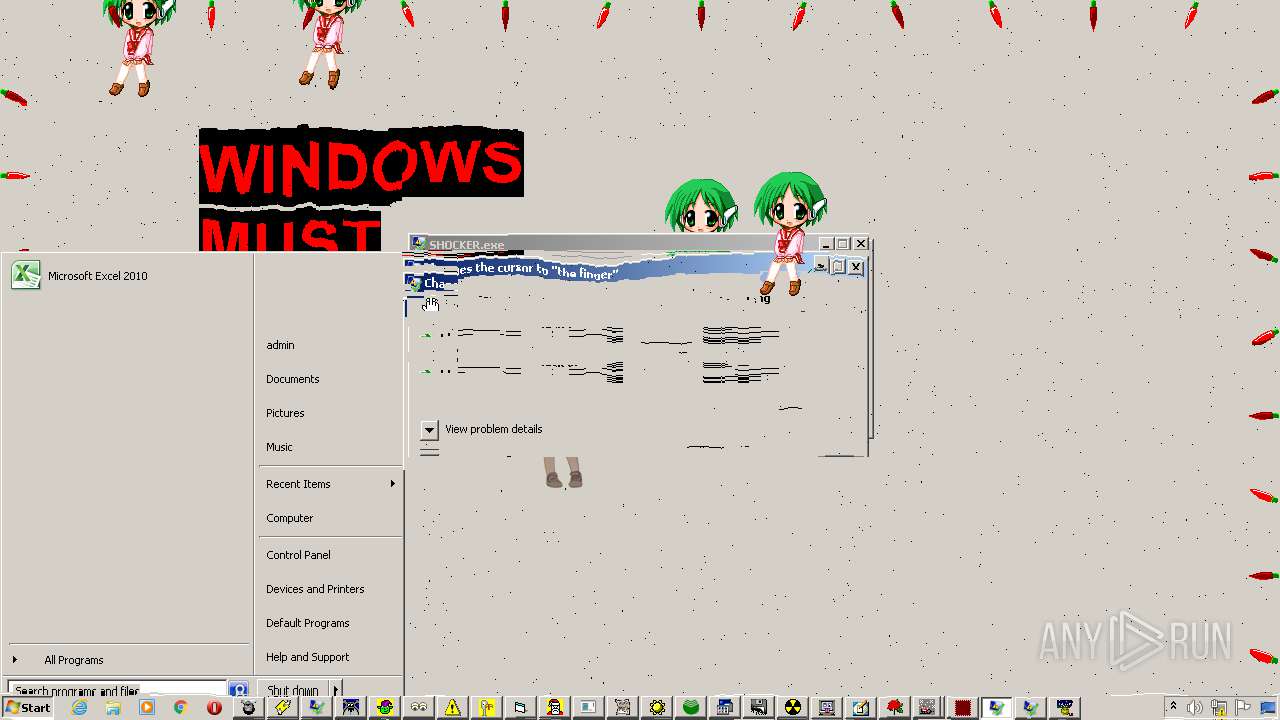
| 1192 | "SHOCKER.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\SHOCKER.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
4 317
Read events
4 300
Write events
17
Delete events
0
Modification events
| (PID) Process: | (916) Bokusatsu Tenshi Full Anime Watch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (916) Bokusatsu Tenshi Full Anime Watch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (916) Bokusatsu Tenshi Full Anime Watch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (916) Bokusatsu Tenshi Full Anime Watch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (924) Realistic Format Virus.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductNonBootFiles |
Value: | |||
| (PID) Process: | (2224) kona_dancer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2224) kona_dancer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2224) kona_dancer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2224) kona_dancer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
70
Suspicious files
1
Text files
10
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 916 | Bokusatsu Tenshi Full Anime Watch.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KorOvki.exe | executable | |
MD5:441E5C95C800C38201DF17A6A4D126B2 | SHA256:DD4376F06BBD24B56B45C133EA6D815D656F0D9C7FB4BF4FDA822CEFF7E00594 | |||
| 916 | Bokusatsu Tenshi Full Anime Watch.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\??????? ????????.exe | executable | |
MD5:DB4E99E23C916C6D1D37BC495F5203C2 | SHA256:89FB1B4D8A44508B02005771B1CE66E57CB90FD307C03F98E14AF01C64AB45B0 | |||
| 916 | Bokusatsu Tenshi Full Anime Watch.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\jeprus.exe | executable | |
MD5:76ED7878D30D403EFDCA73BD86CB7295 | SHA256:D3FDD7BB7F1C2EB57FAF04C6E018D96629E251BE2CEBA05814BD8153006AAC11 | |||
| 916 | Bokusatsu Tenshi Full Anime Watch.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\kona_dancer.exe | executable | |
MD5:78AE653289AB3169ECD0C76215999C6D | SHA256:565693B546AD31AFAE5B00AB2F54DB4211949665FF22A09AA769689D852C736D | |||
| 916 | Bokusatsu Tenshi Full Anime Watch.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\melter.exe | executable | |
MD5:D9BAAC374CC96E41C9F86C669E53F61C | SHA256:A1D883577BCB6C4F9DE47B06FE97C370C09BDDFFB6569B6CF93576371BDBC412 | |||
| 916 | Bokusatsu Tenshi Full Anime Watch.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\coringa.bat | text | |
MD5:1196BF85A0D23C2B7D48A7CA81520D13 | SHA256:34B0133BDCAC0B35135776D35456E2CB097695463CB21928755B7622EFC89DD8 | |||
| 916 | Bokusatsu Tenshi Full Anime Watch.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\australia.exe | executable | |
MD5:D6F2C877D32FBB92C67E768677485997 | SHA256:E2C93316C5D09EFCEDA9951B17952AC4F599620748BB684AC9A8C47D268969B2 | |||
| 916 | Bokusatsu Tenshi Full Anime Watch.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\MIGHTY FUCKER.exe | executable | |
MD5:54F28560DF75C4A658E38347B516C80B | SHA256:0C992F87DE865047F430D65C5E7355747DFE01F6BD684AA8138621B8D2F50DC4 | |||
| 916 | Bokusatsu Tenshi Full Anime Watch.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ILoveYou.exe | executable | |
MD5:A561D27EC9FA02532B5C9A3166F8C8EE | SHA256:B090838B451D1E72245D41CB0558F5687E2A900D3C9D77DBD1709109045D5B95 | |||
| 916 | Bokusatsu Tenshi Full Anime Watch.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Crazy Mouse v1.2.exe | executable | |
MD5:016A4B534577B183868BF6E7D534CA6B | SHA256:3888FBB6685DE35177C42F9F4F770308D09DDD97FBB6B537AAD14F181FF49C58 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report