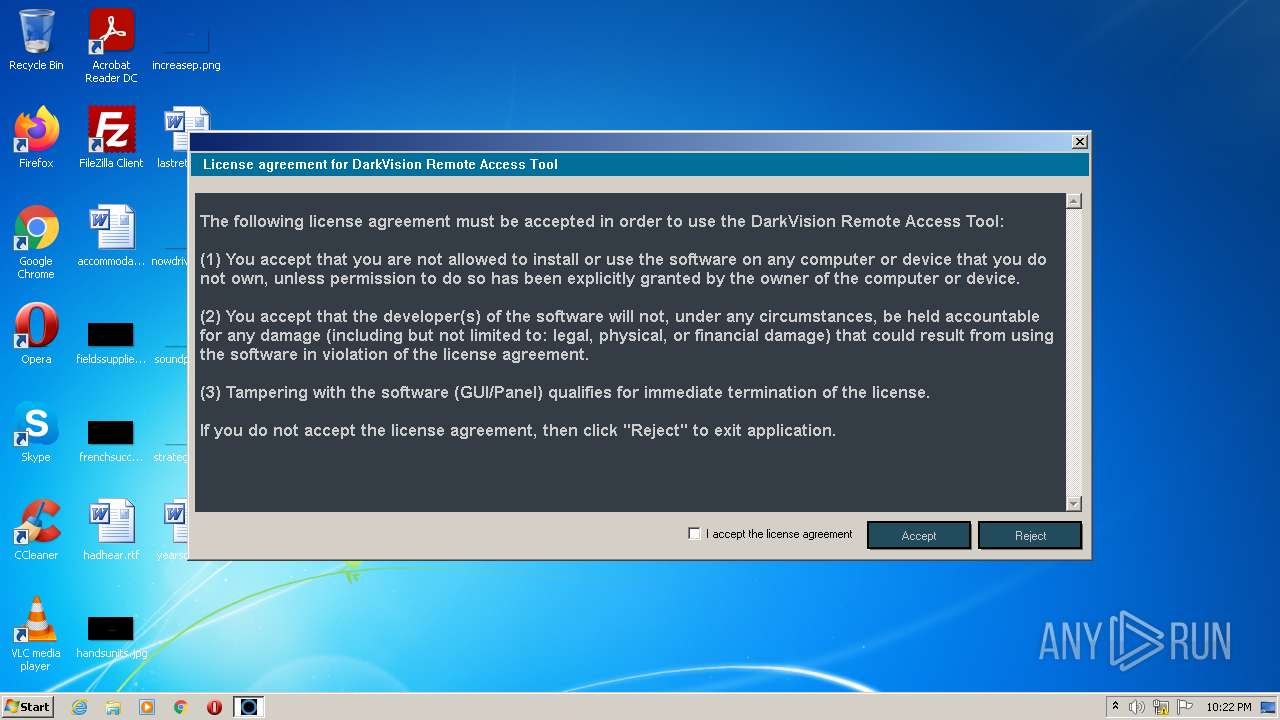
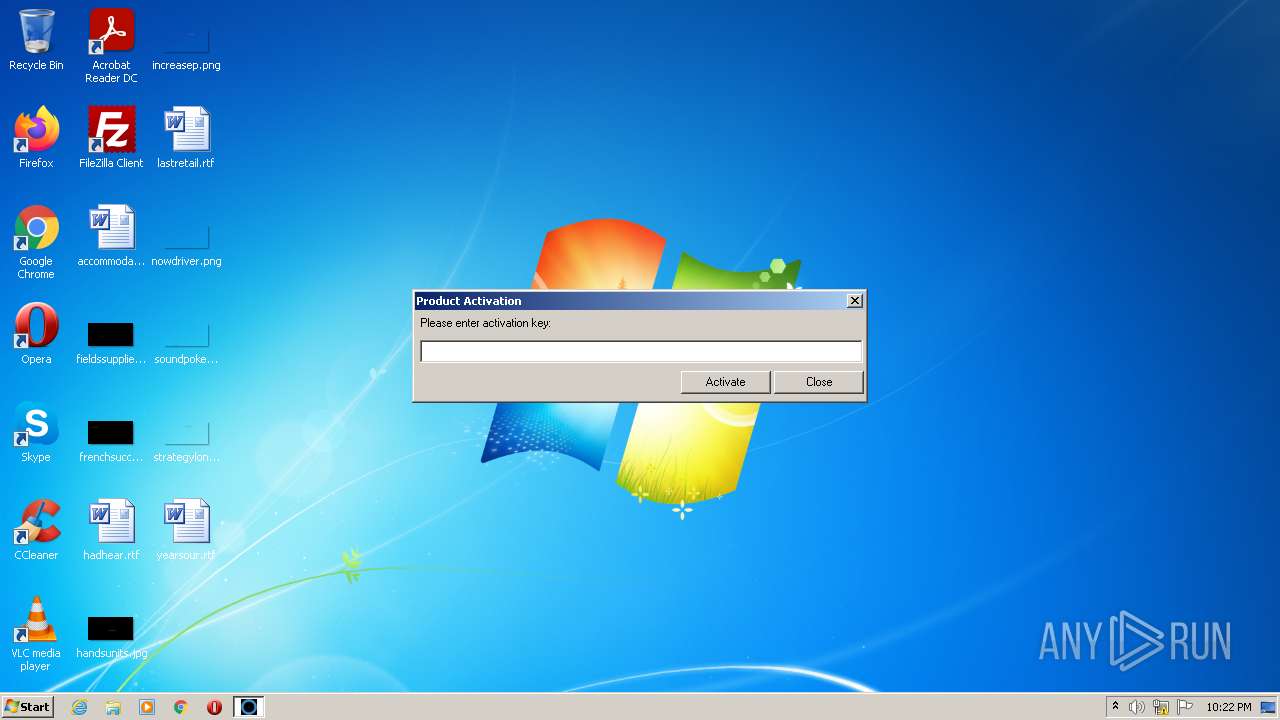
| File name: | DarkVision.exe |
| Full analysis: | https://app.any.run/tasks/50e16913-13f2-4809-9362-f8694aa4fc79 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 22:22:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C4436E385D44A2B187EFC3D2F5376773 |
| SHA1: | 6060577571CE93F9CC1822F1B9F244BD48F27E23 |
| SHA256: | F73466DDE9FEFD8E71F01D2A38A59FBD2E6C70A1B16955E265966143F22BF3EC |
| SSDEEP: | 49152:t847VJj/RTkzzfJIcPw2JxGyqLptWVo18LSSUmsGR/x91pufmI57r7MDqs:tpVV9GqclJ62q8OSNsGR1pufmI7r7m |
MALICIOUS
Drops executable file immediately after starts
- DarkVision.exe (PID: 1704)
Application was dropped or rewritten from another process
- DARKVISIONENCRYPTED_original.exe (PID: 2508)
- DARKVISIONENCRYPTED_original.exe (PID: 2852)
SUSPICIOUS
Reads the computer name
- DarkVision.exe (PID: 1704)
- DARKVISIONENCRYPTED_original.exe (PID: 2508)
Checks supported languages
- DarkVision.exe (PID: 1704)
- DARKVISIONENCRYPTED_original.exe (PID: 2508)
- DARKVISIONENCRYPTED_original.exe (PID: 2852)
Executable content was dropped or overwritten
- DarkVision.exe (PID: 1704)
Application launched itself
- DARKVISIONENCRYPTED_original.exe (PID: 2508)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1eef0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 255488 |
| CodeSize: | 201728 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2021:06:11 11:16:47+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Jun-2021 09:16:47 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 11-Jun-2021 09:16:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000313BA | 0x00031400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70981 |
.rdata | 0x00033000 | 0x0000A622 | 0x0000A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22268 |
.data | 0x0003E000 | 0x00023728 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.70882 |
.didat | 0x00062000 | 0x0000018C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.35543 |
.rsrc | 0x00063000 | 0x0000DFD0 | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.63675 |
.reloc | 0x00071000 | 0x0000227C | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56418 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.10026 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 5.25868 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.02609 | 1128 | UNKNOWN | English - United States | RT_ICON |
5 | 5.18109 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.04307 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.11236 | 440 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1704 | "C:\Users\admin\AppData\Local\Temp\DarkVision.exe" | C:\Users\admin\AppData\Local\Temp\DarkVision.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2508 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\DARKVISIONENCRYPTED_original.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\DARKVISIONENCRYPTED_original.exe | — | DarkVision.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\DARKVISIONENCRYPTED_original.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\DARKVISIONENCRYPTED_original.exe | DARKVISIONENCRYPTED_original.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 607
Read events
1 590
Write events
17
Delete events
0
Modification events
| (PID) Process: | (1704) DarkVision.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR SFX |
| Operation: | write | Name: | C%%ProgramData |
Value: C:\Users\admin\AppData\Local\Temp\RarSFX0 | |||
| (PID) Process: | (1704) DarkVision.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1704) DarkVision.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1704) DarkVision.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1704) DarkVision.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2508) DARKVISIONENCRYPTED_original.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2508) DARKVISIONENCRYPTED_original.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2508) DARKVISIONENCRYPTED_original.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2508) DARKVISIONENCRYPTED_original.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
41
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1704 | DarkVision.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\DROPPERPLUGIN32.DLL | executable | |
MD5:40CC4932320C65FBB5CF1B07CD6D42AB | SHA256:96454417229C3629BBAE5C909A1A15770F0AEA6BB633C28CE12AA3105E51A1DB | |||
| 1704 | DarkVision.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\HVNCPLUGIN32.DLL | executable | |
MD5:0441F3075DCCC3F870D5CF490E93312D | SHA256:02992774E9F3510617CA827CA112530AE565B073F088E72A9B7070503313B9F7 | |||
| 1704 | DarkVision.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\FILEPLUGIN64.DLL | executable | |
MD5:15F74A7350ED9A19D15BE88E965D77DE | SHA256:3EF8922F7BB2C456CB50B698EBD6B68561D3D74BBBA0CBA5B334F99497A97FF9 | |||
| 1704 | DarkVision.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\FILEPLUGIN32.DLL | executable | |
MD5:C35D2454860618AD9CE671A6081E6540 | SHA256:20C66FB1356518CFAEDB95CB3C7F8DD779A7EBA398280DFB916799C545D2DB82 | |||
| 1704 | DarkVision.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\HVNCPLUGIN64.DLL | executable | |
MD5:D8947667CD885C994FCD17D00A357197 | SHA256:55C347FE6766C3D23EF13335C66F22FB84F666DBF0956480BE7A5B95181AE53C | |||
| 1704 | DarkVision.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KILLSWITCHPLUGIN64.DLL | executable | |
MD5:3778830910DA7411F5FCF878F535A52E | SHA256:9F37EBB3F41C58C76700027BBC5B61010B86905841017FEFD51AB0173C651B86 | |||
| 1704 | DarkVision.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\DROPPERPLUGIN64.DLL | executable | |
MD5:5D2CED6944769633C1540E6D2462EFE0 | SHA256:353D6D894C5ABB8AF81D7B3DEFC327156CABDD8D9A9A2534D57ABAEC18D6999D | |||
| 1704 | DarkVision.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\MICROPHONECAPTUREPLUGIN64.DLL | executable | |
MD5:855673689DB2A4B1E29DCE0D0615F370 | SHA256:178B4B009987569E17A3679FA8DE419FCEAF628F3065F936EAFCAF0ADC133775 | |||
| 1704 | DarkVision.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\OFFLINEKEYLOGGERPLUGIN32.DLL | executable | |
MD5:80632C2EFD86C3448B3A323D02BAE6EE | SHA256:6F889406433E227CA285AC22D00C499F2610884EFAA70BBF1253C8E76B5586A2 | |||
| 1704 | DarkVision.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\MICROPHONECAPTUREPLUGIN32.DLL | executable | |
MD5:8E1C368870B371FF0E79A4D47E286176 | SHA256:13CCB540555127951C9EE7ECF7FAD8210A1A13DD43BB9C13D4F7EEE27E4EFE51 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report