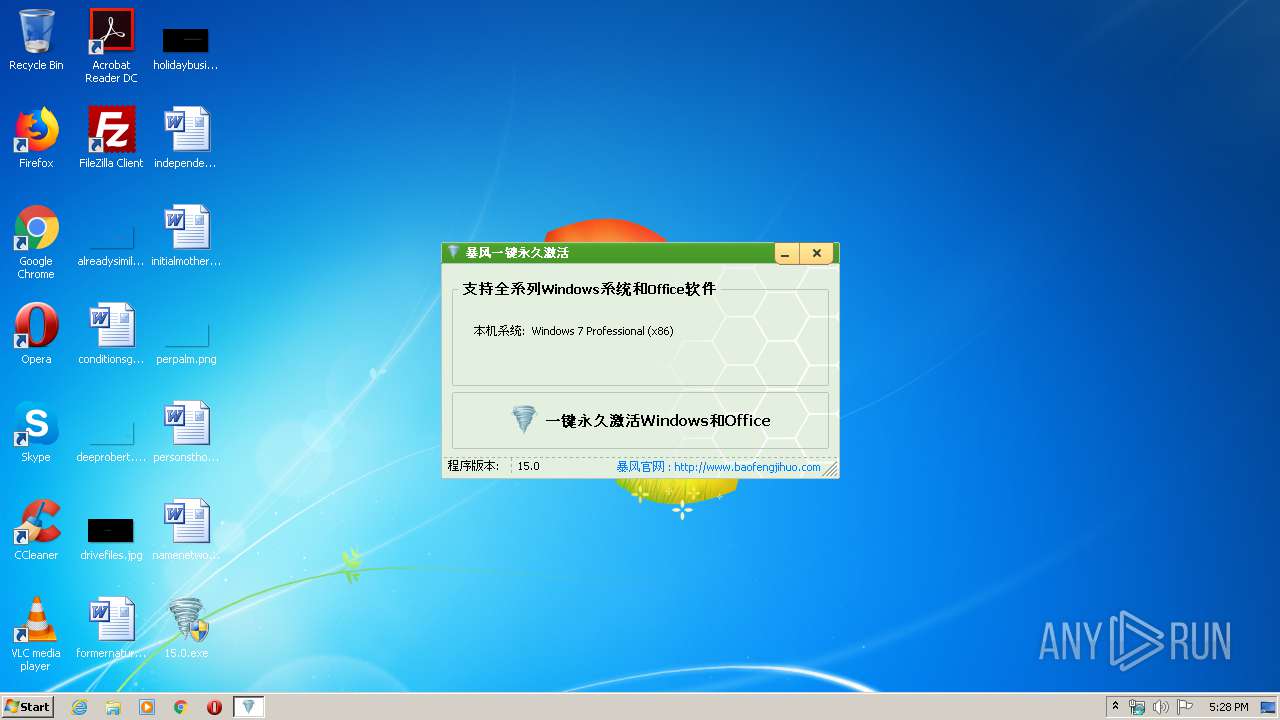
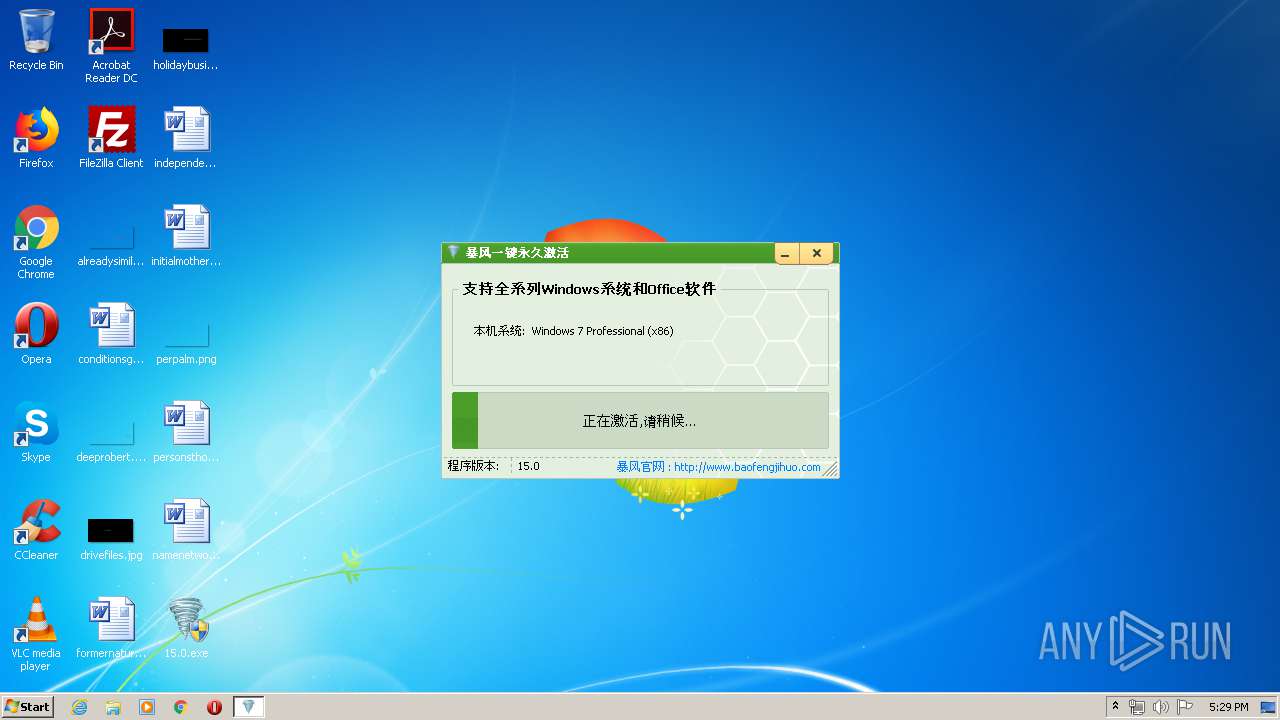
| File name: | 15.0.exe |
| Full analysis: | https://app.any.run/tasks/7f861edb-4406-4fec-bebe-f258c88c9db2 |
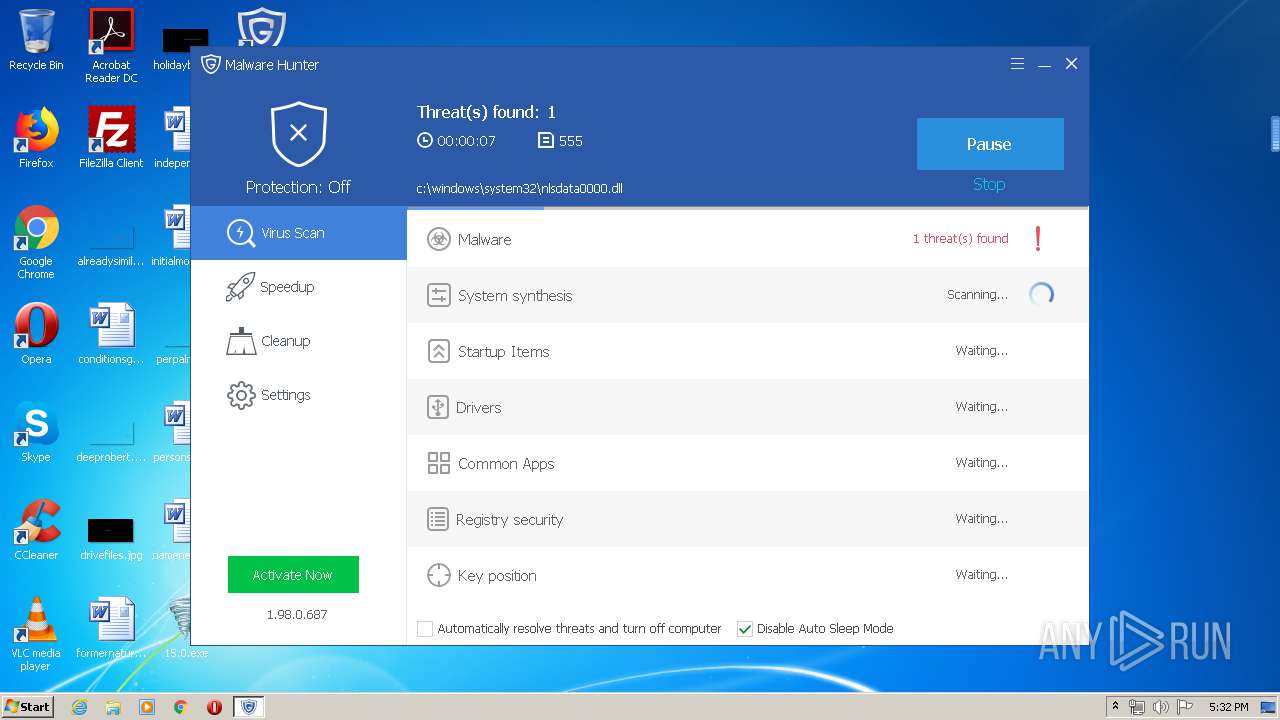
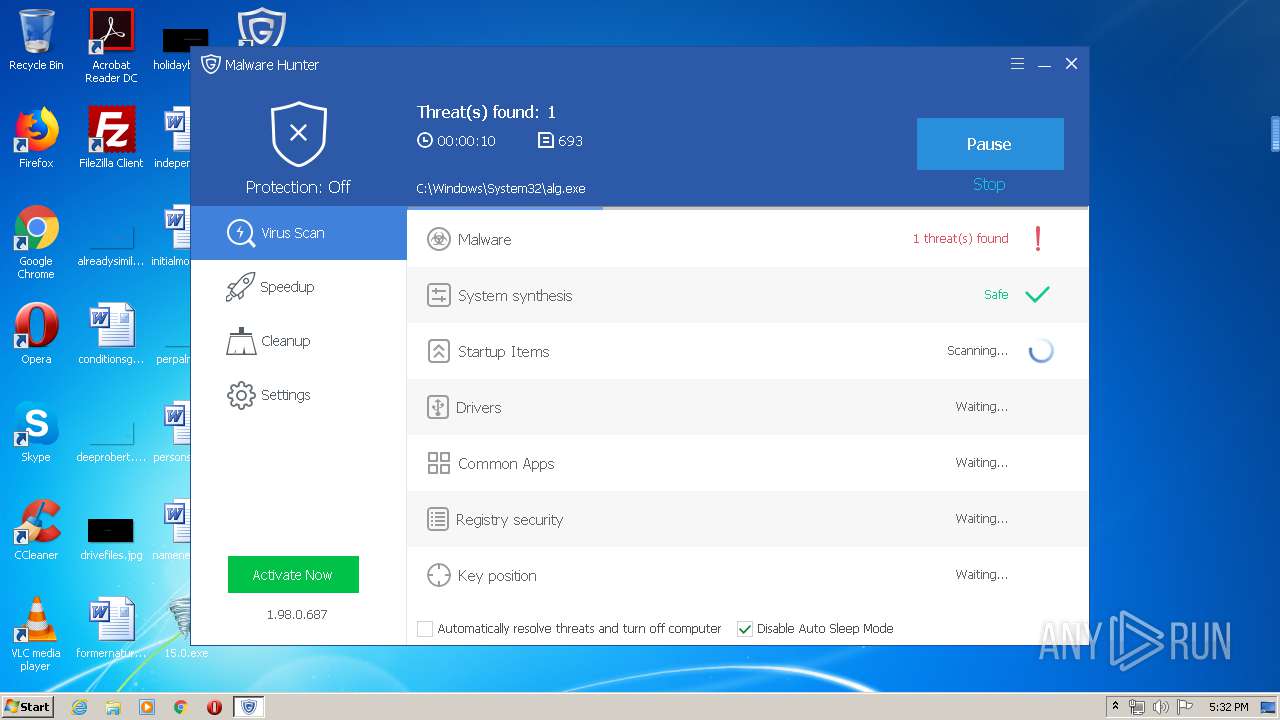
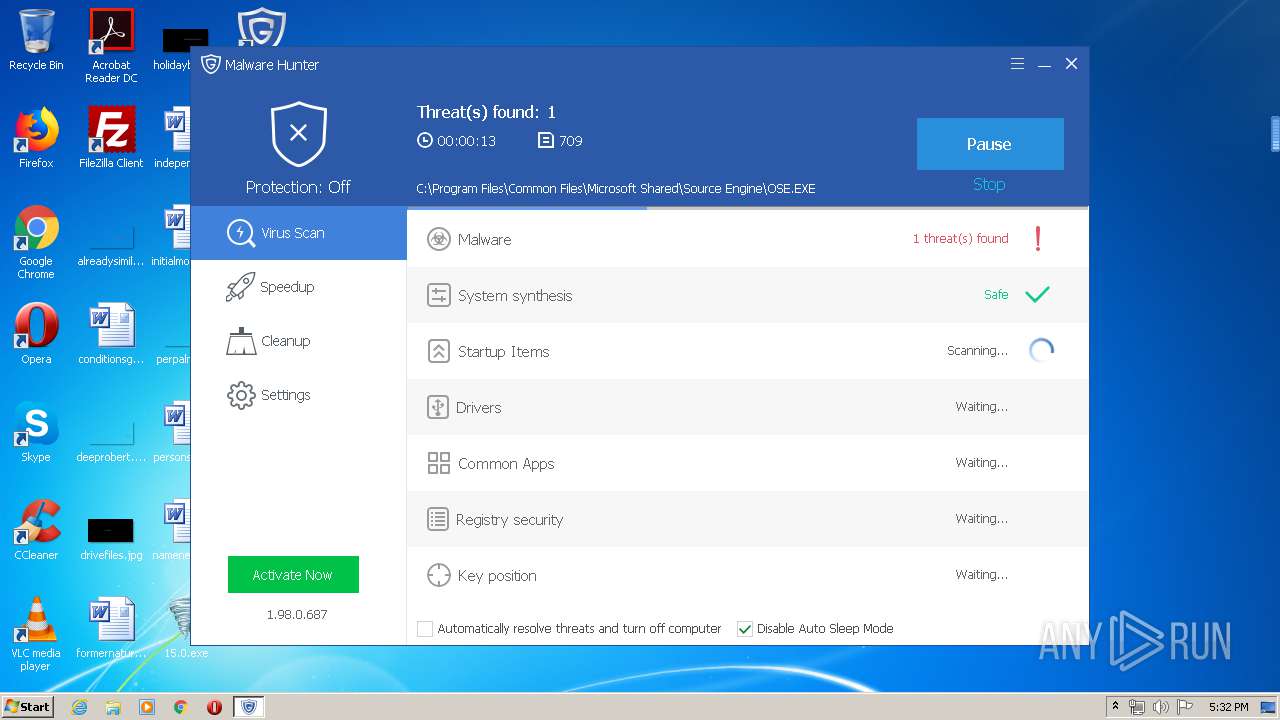
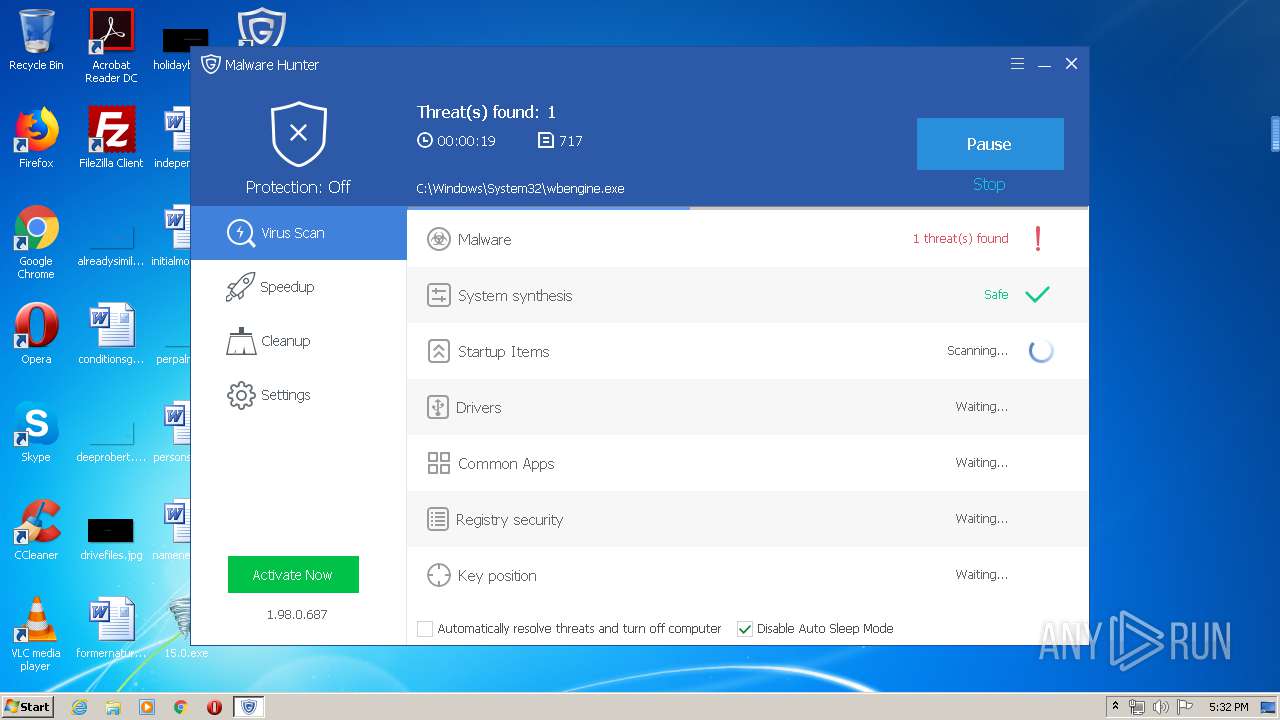
| Verdict: | Malicious activity |
| Analysis date: | March 23, 2020, 17:28:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | 44AAF63853E943A9E6F4C793EA791BE3 |
| SHA1: | C7764D7D204CF97F07F5F3FD8670775B77B76315 |
| SHA256: | F7240B2DD95ADB30D53B2F4421D2C934C7F293CF9DBA016A992E8C50F9011DA7 |
| SSDEEP: | 98304:vtnQe6thoMvYPJCNVG0FrpwTi2jDFcjjf6rrBjxveTlwwnk/2d7U/rJ0CLgGAtgX:vtyrvJVxBpFOhCYrFVeTKwI2dWJSxZ7q |
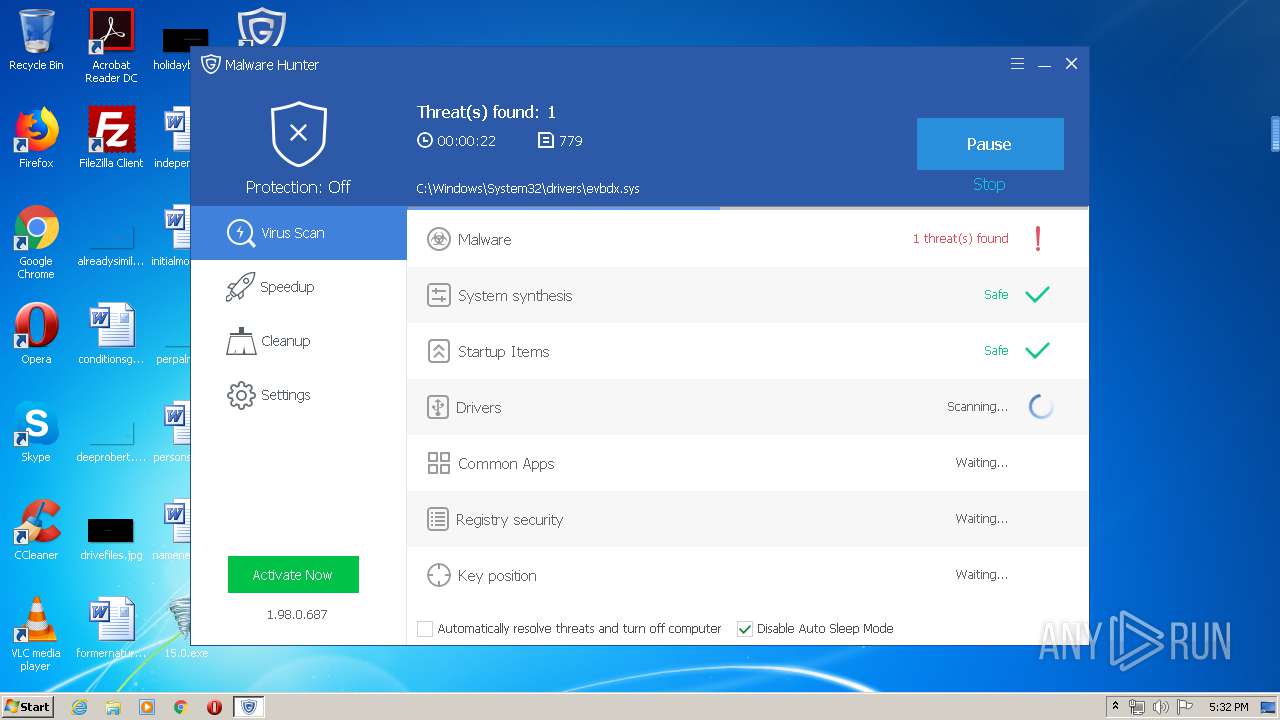
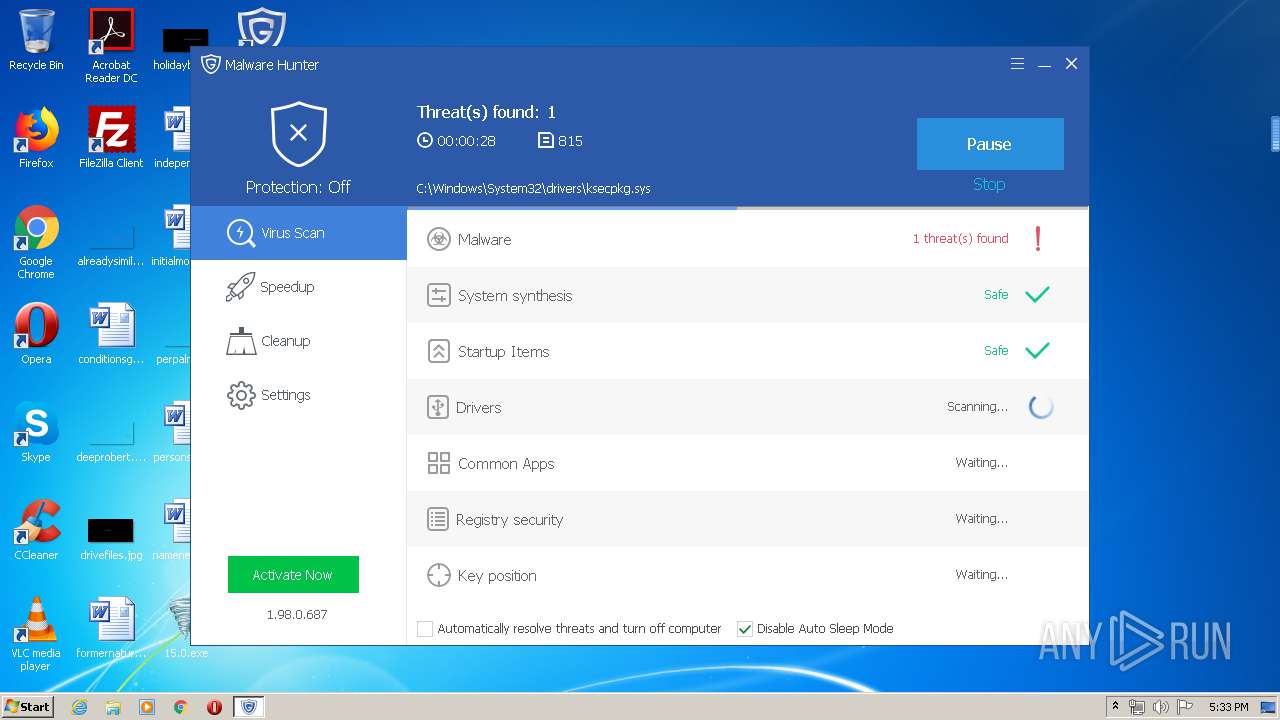
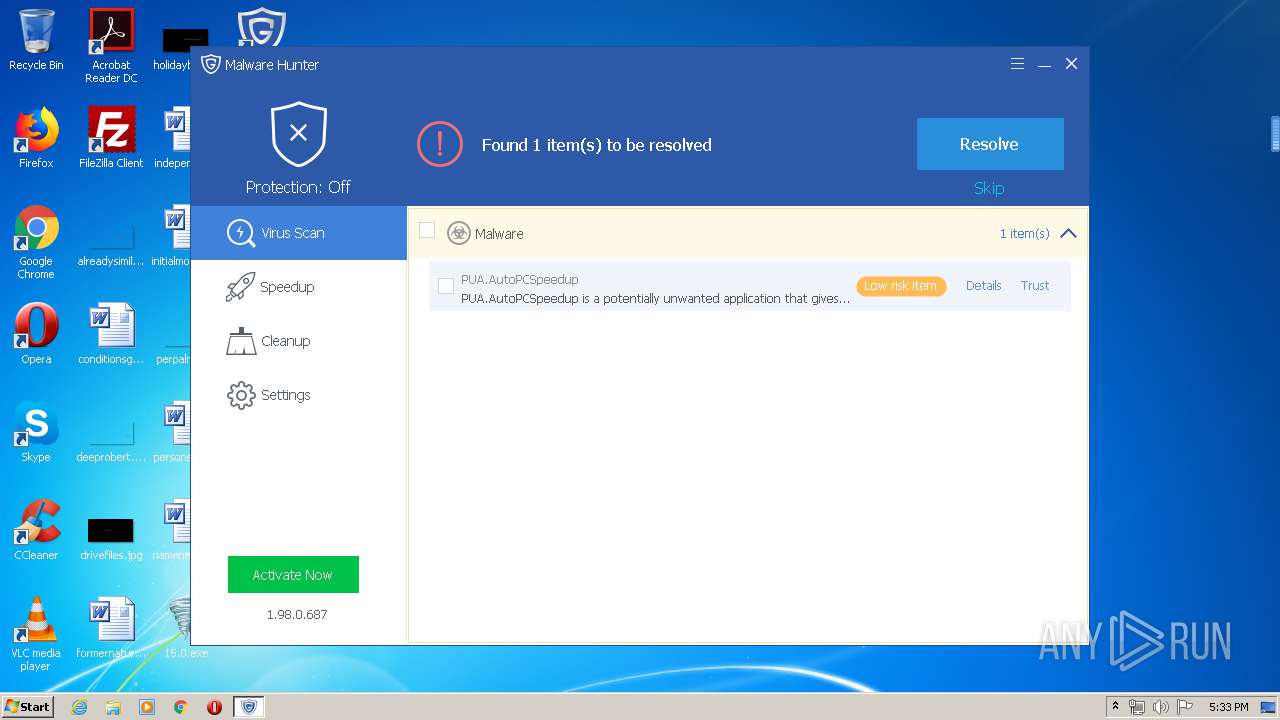
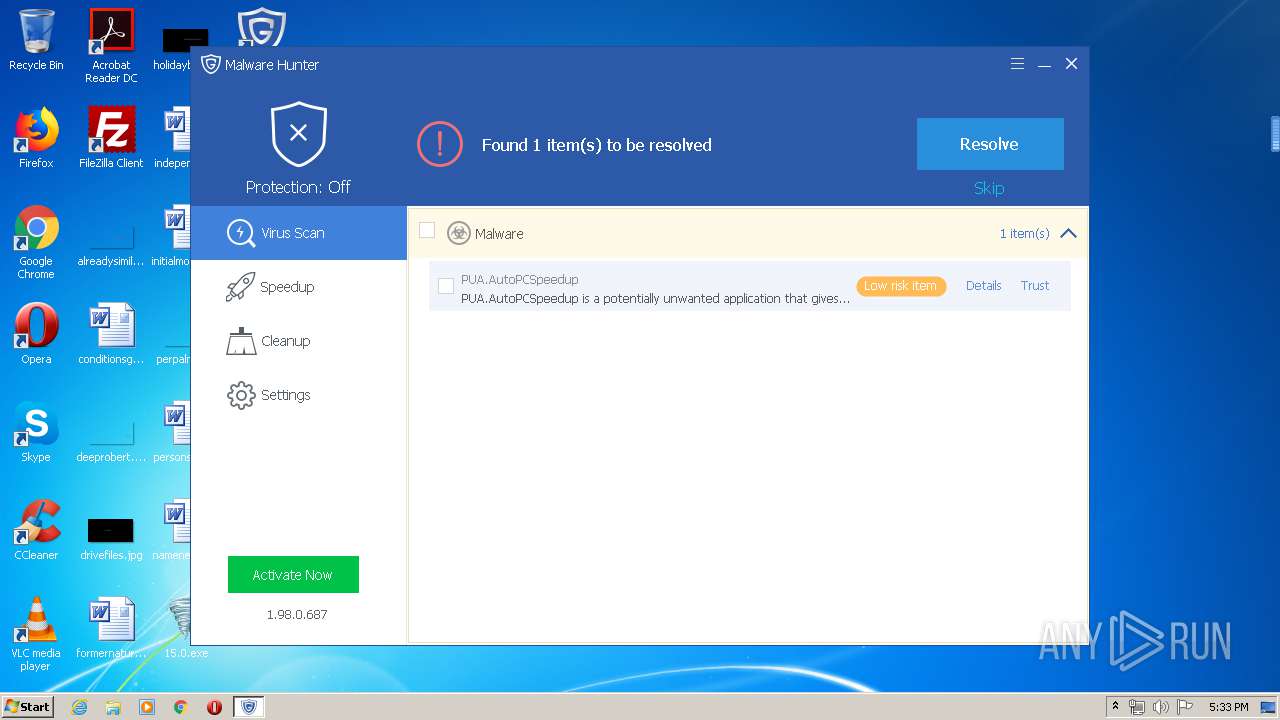
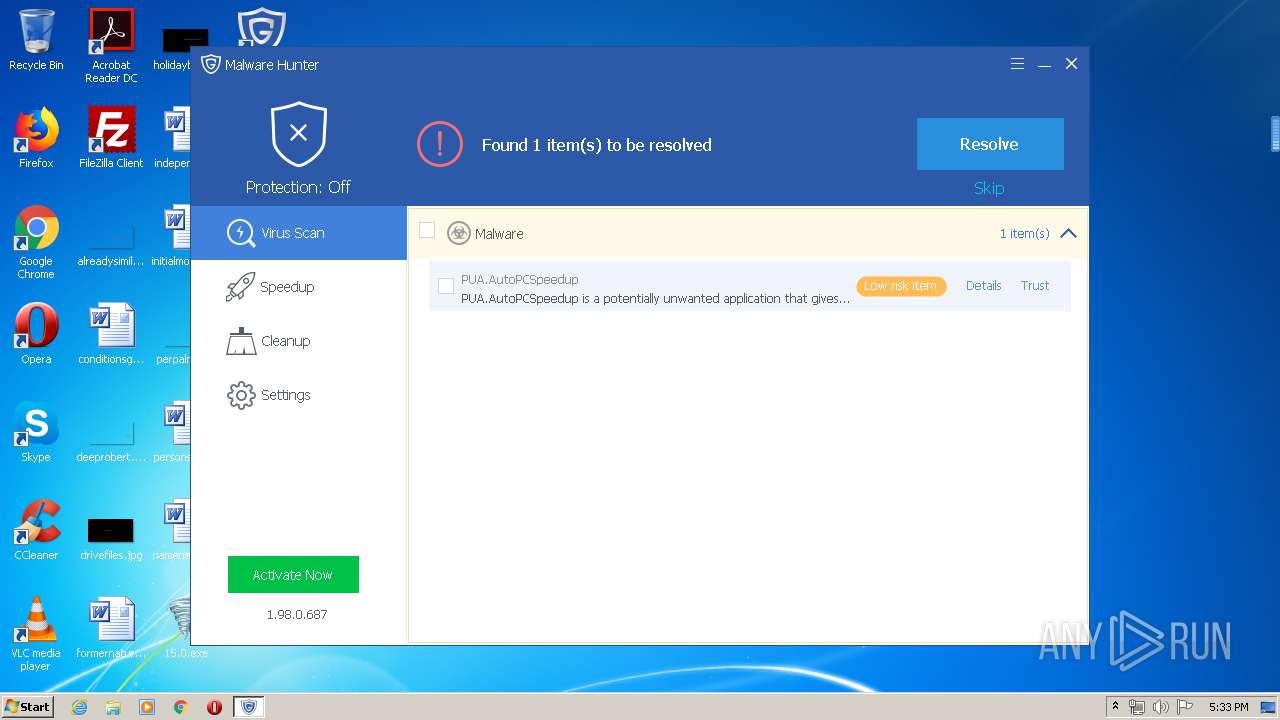
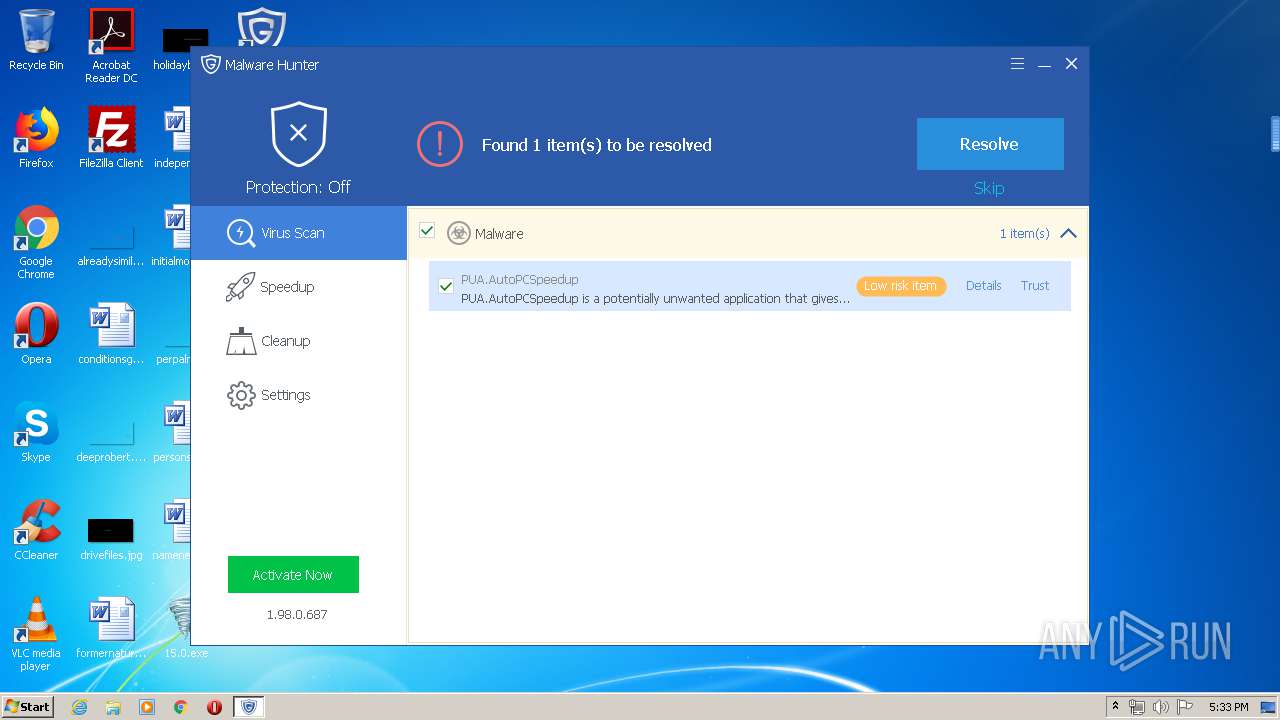
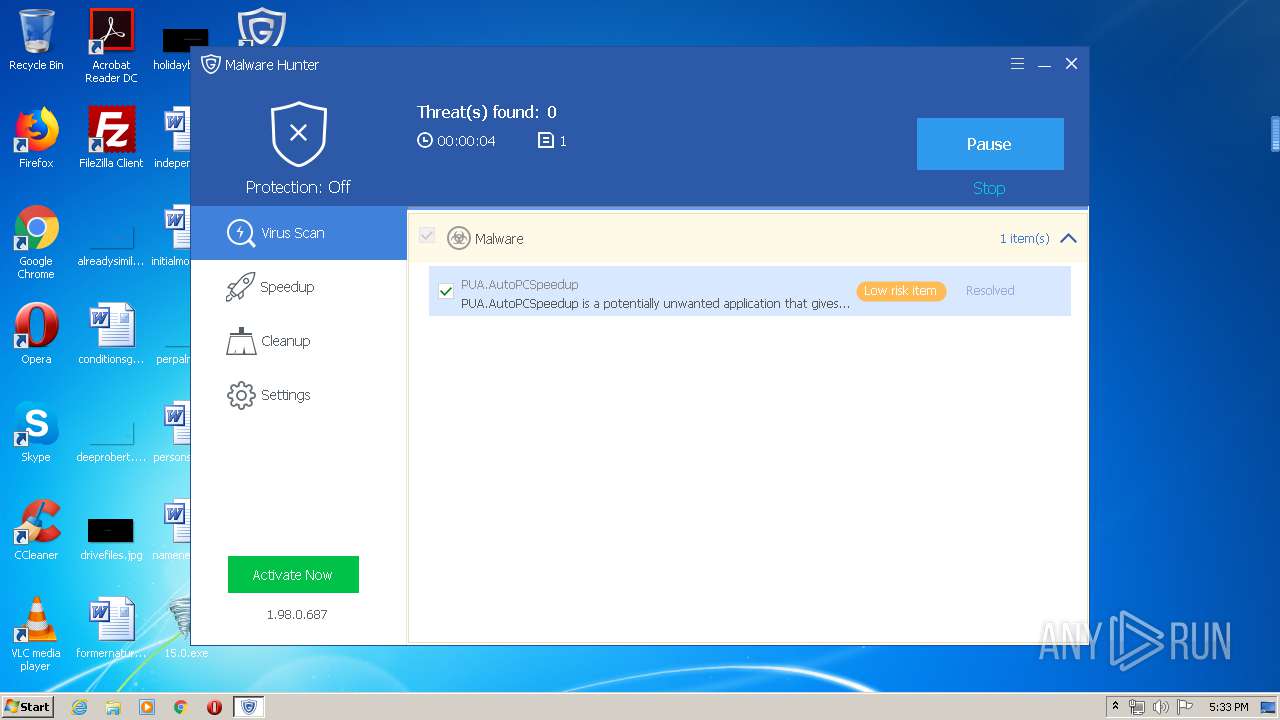
MALICIOUS
Application was dropped or rewritten from another process
- _¼¤»î¹¤¾ß8.exe (PID: 2596)
- ±©·ç¼¤»î15.0.exe (PID: 2644)
- ¼¤»î¹¤¾ß8.exe (PID: 3456)
- Windows Mobile User Experience Server.exe (PID: 3872)
- DvLayout.exe (PID: 3288)
- Windows Mobile User Experience Server.exe (PID: 3272)
- DvUpdate.exe (PID: 572)
- KMSService.exe (PID: 2248)
- DumpUp.exe (PID: 3032)
- SppExtComObjPatcher.exe (PID: 3640)
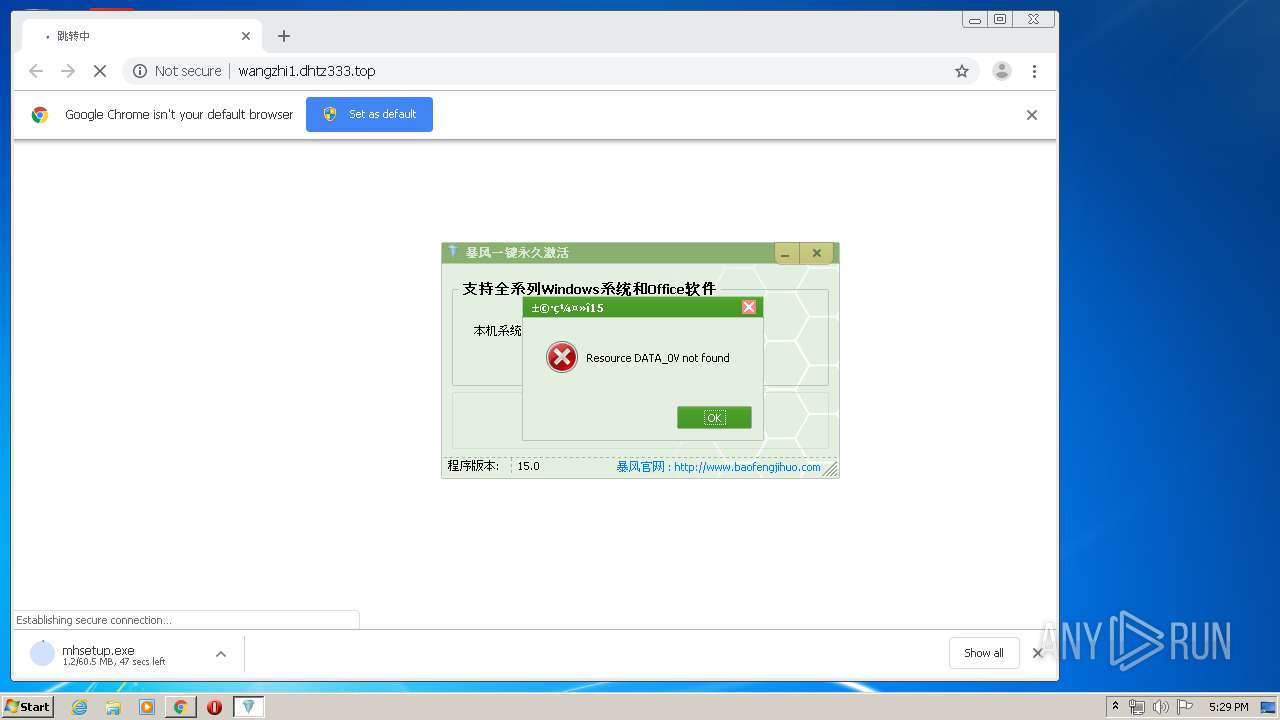
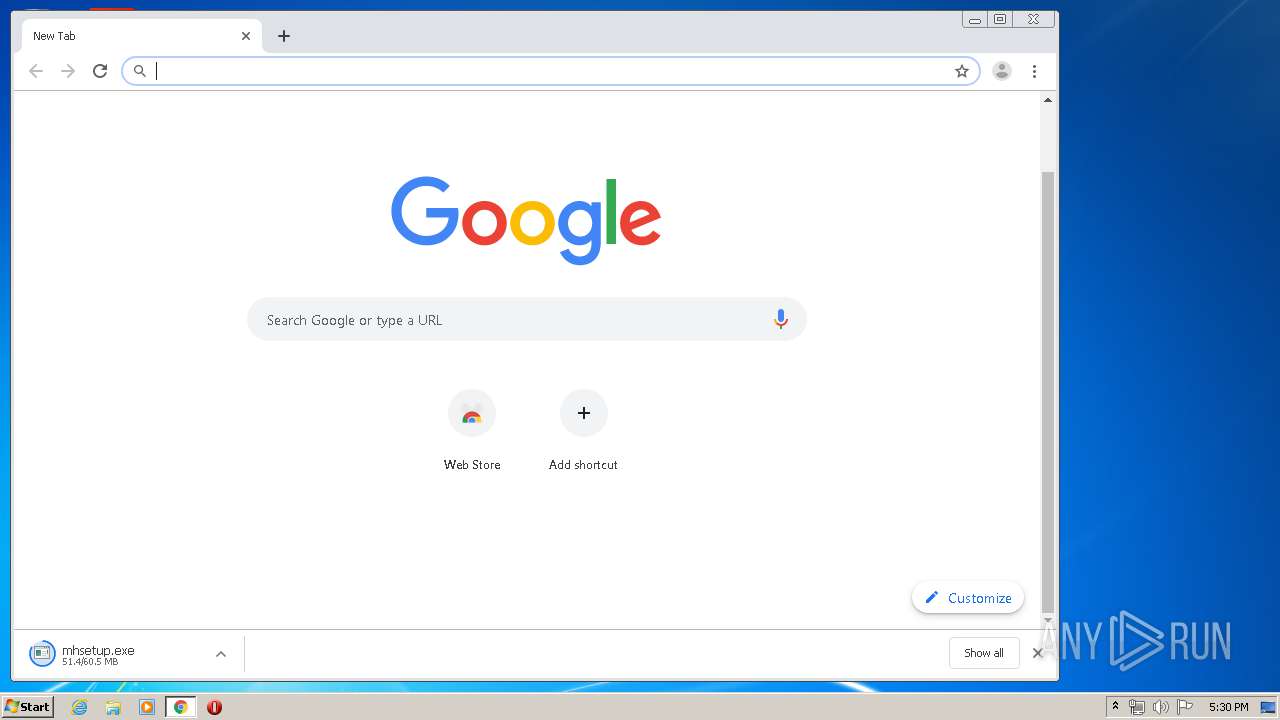
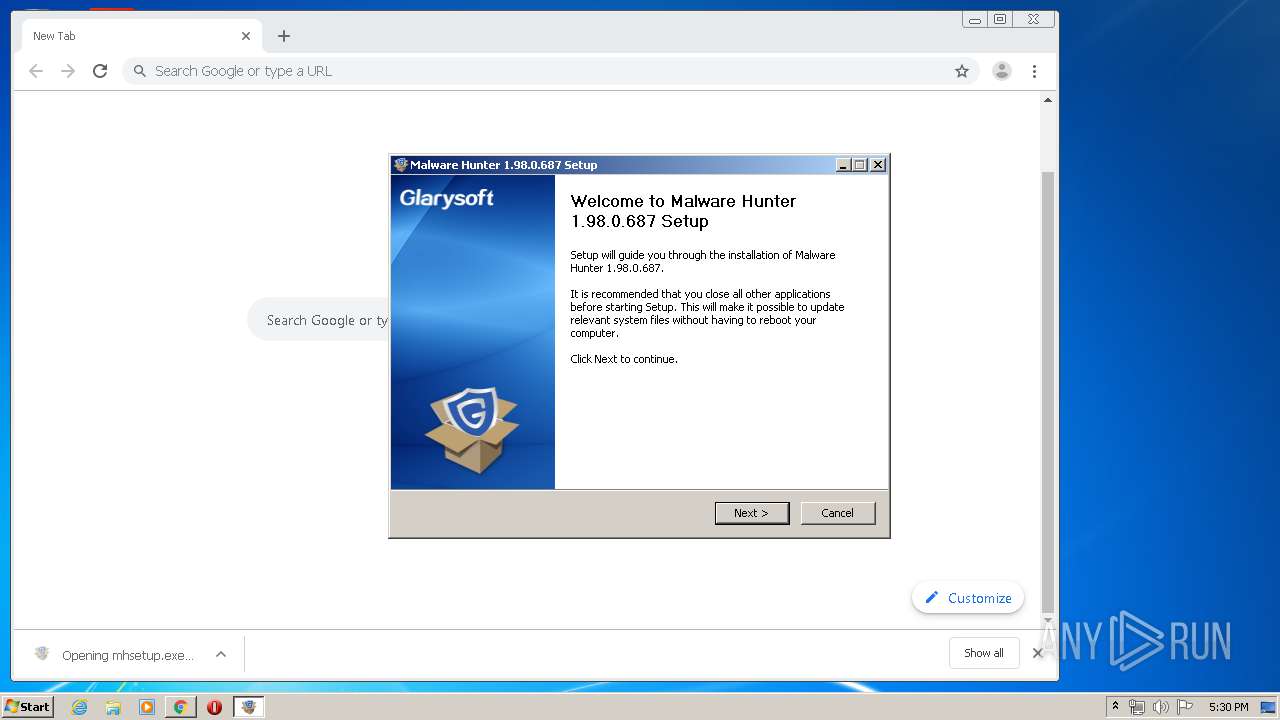
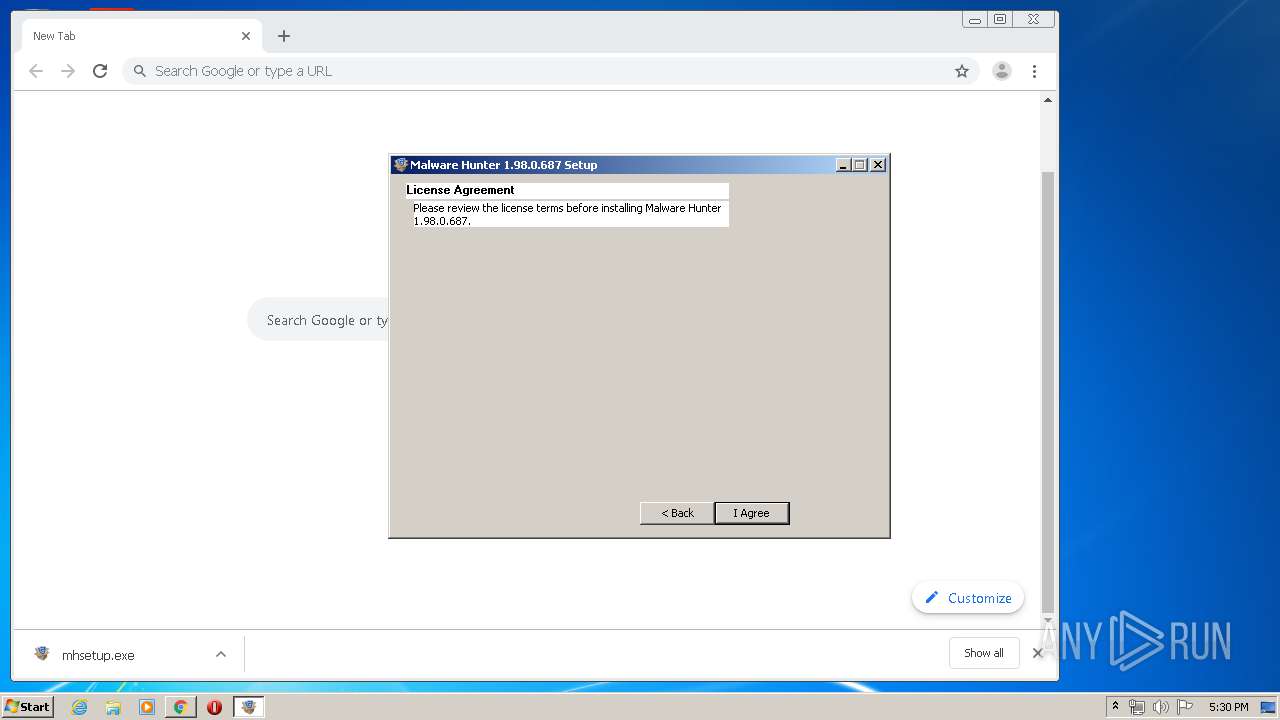
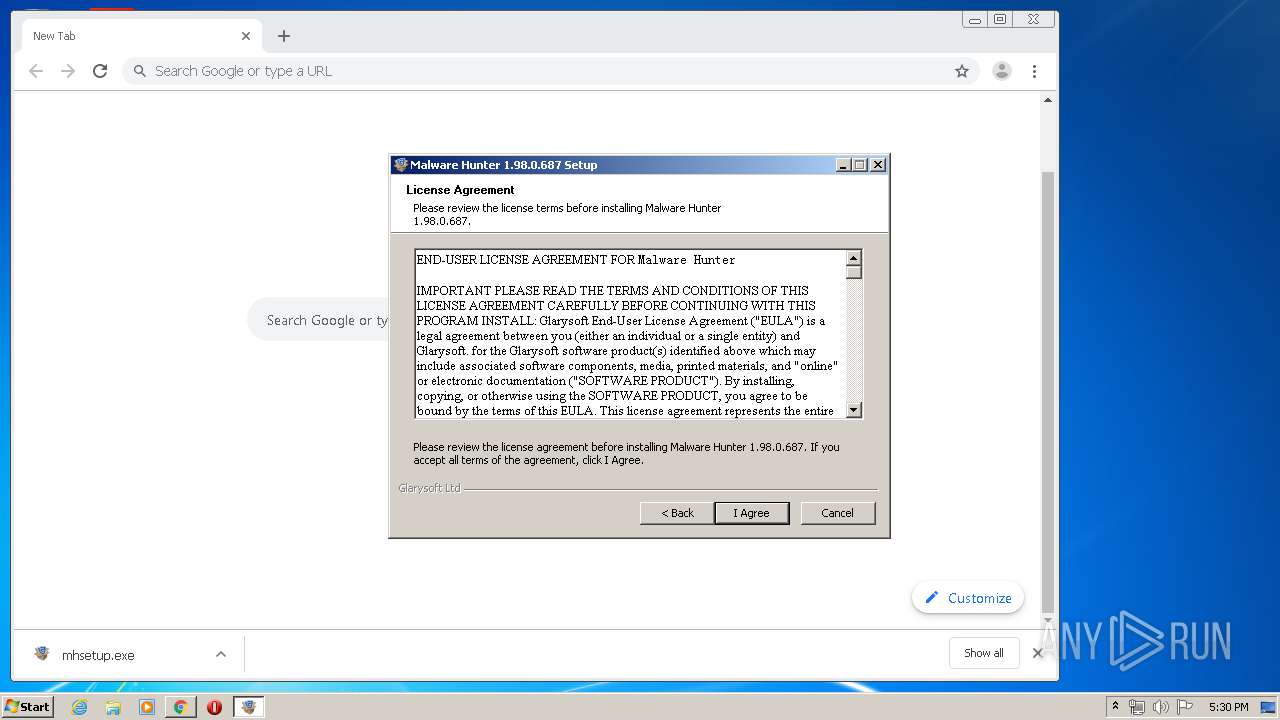
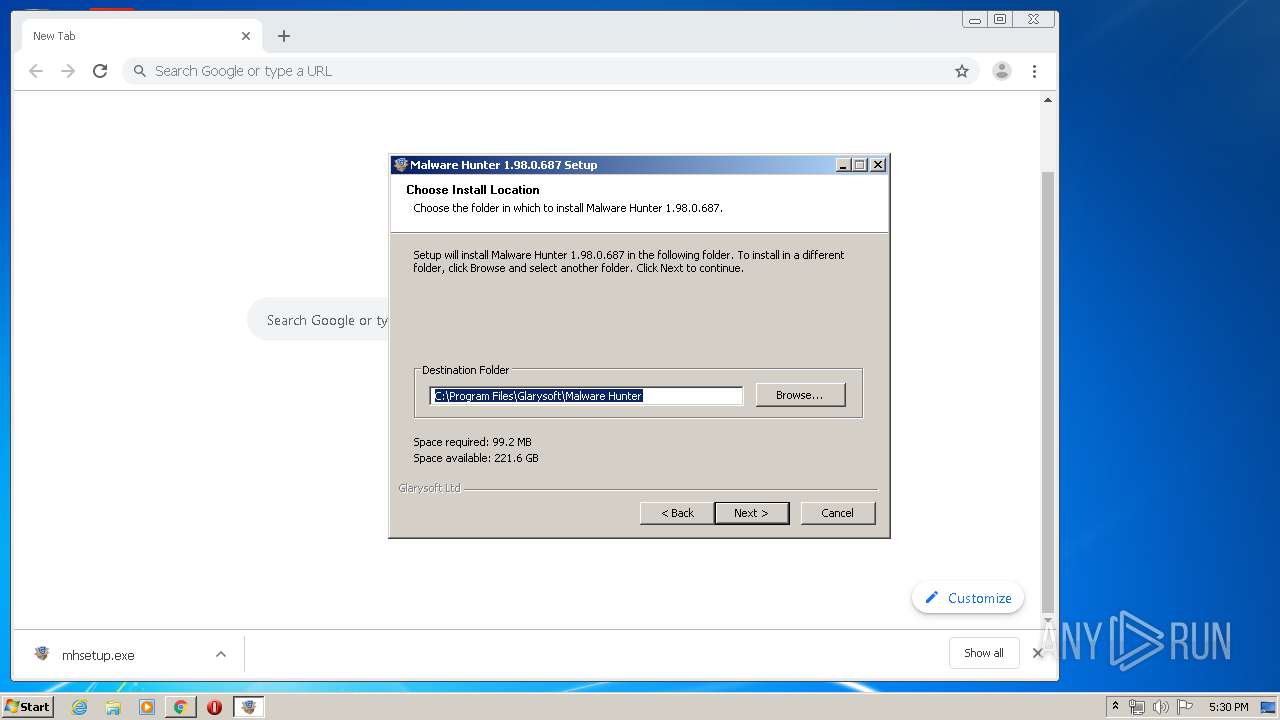
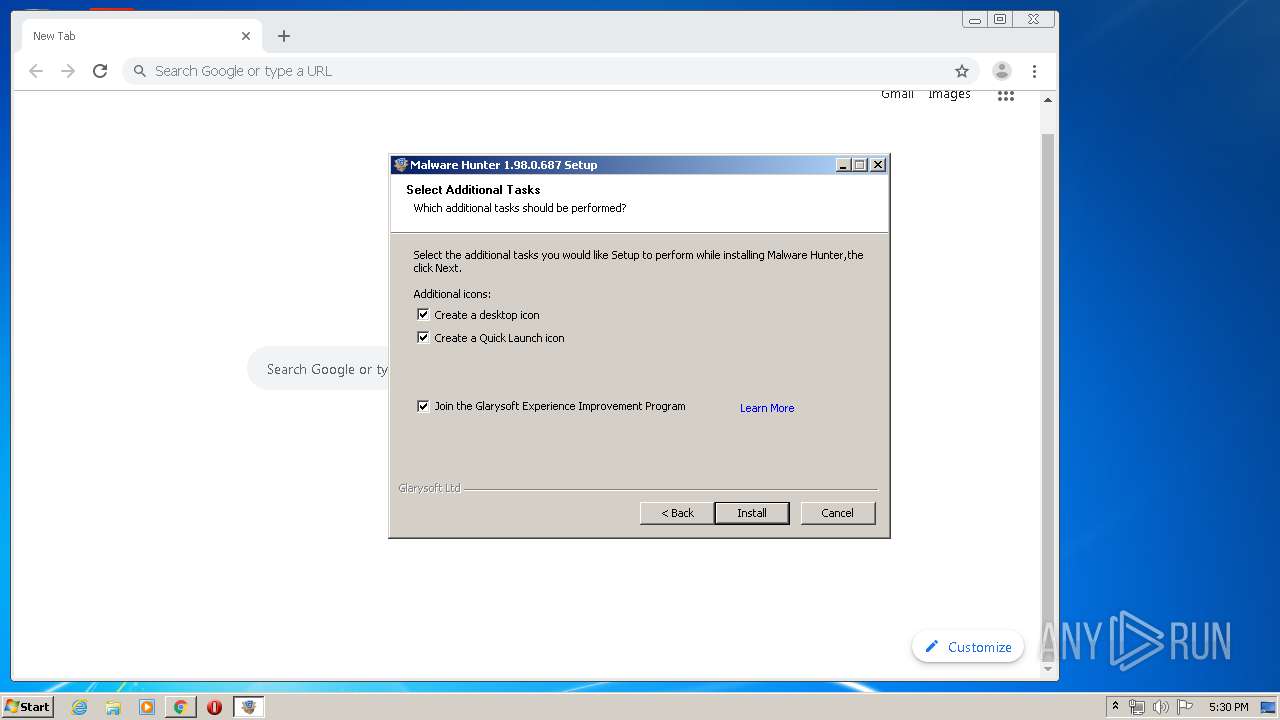
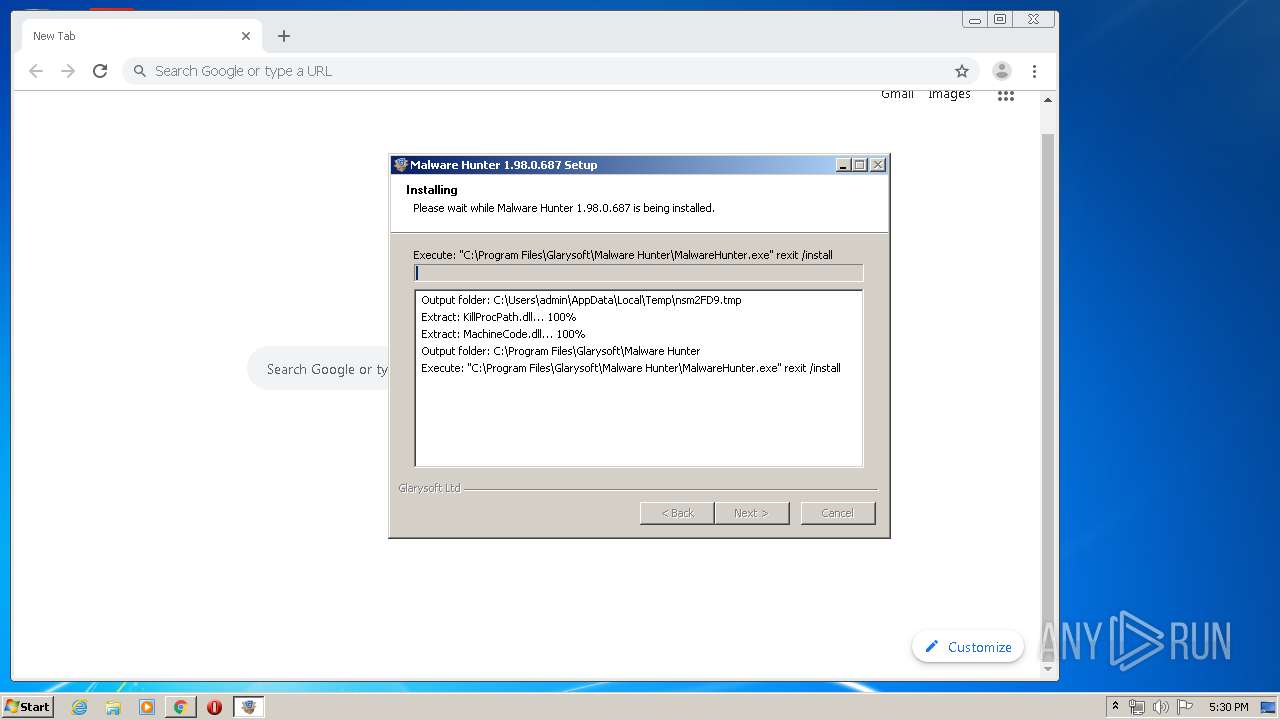
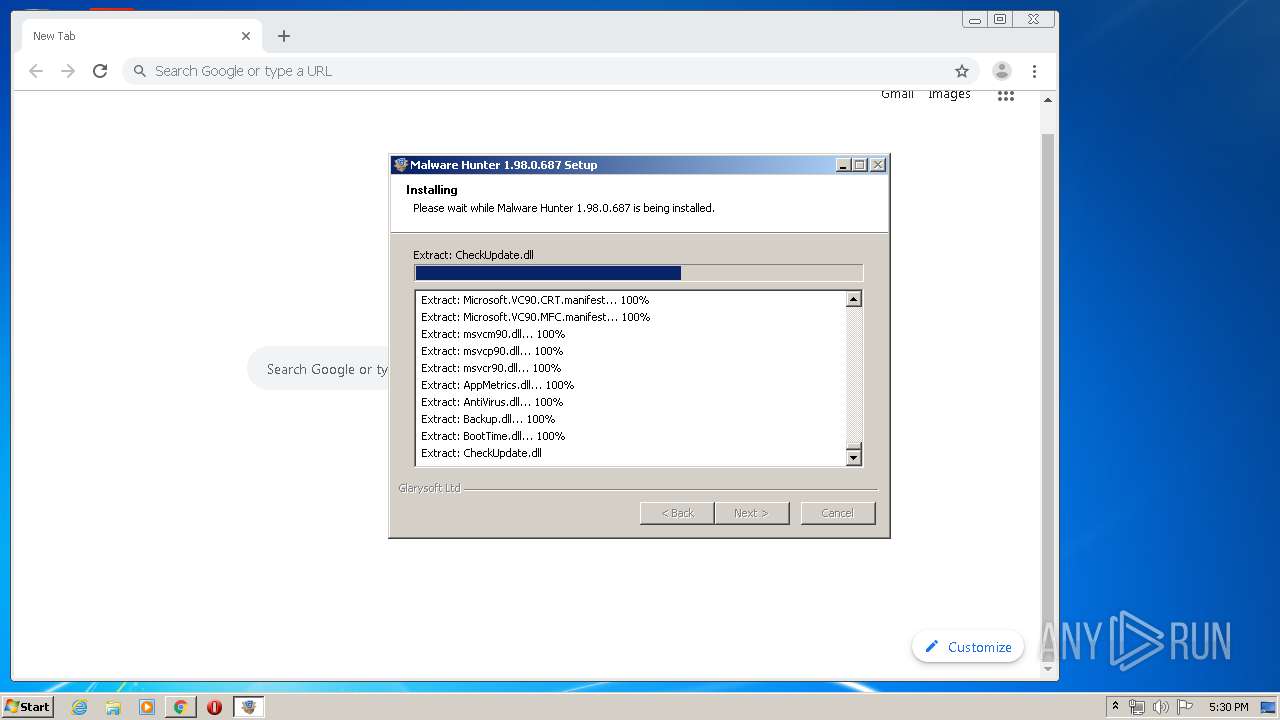
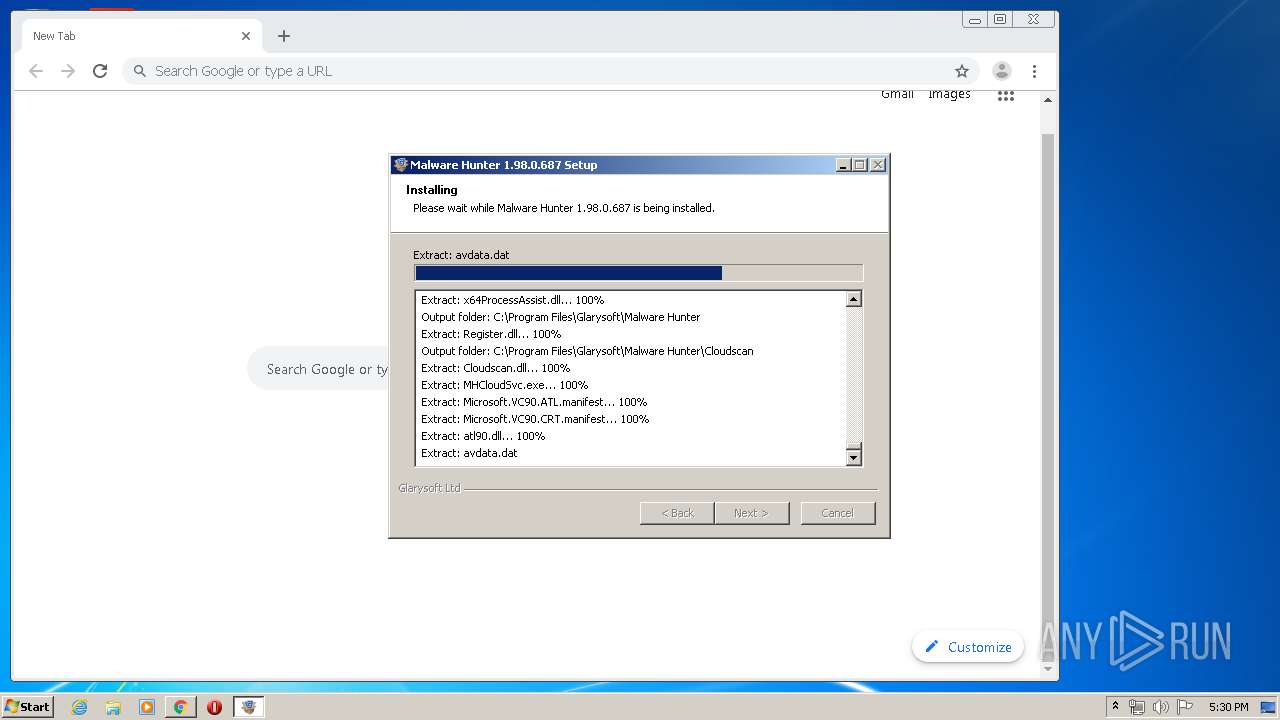
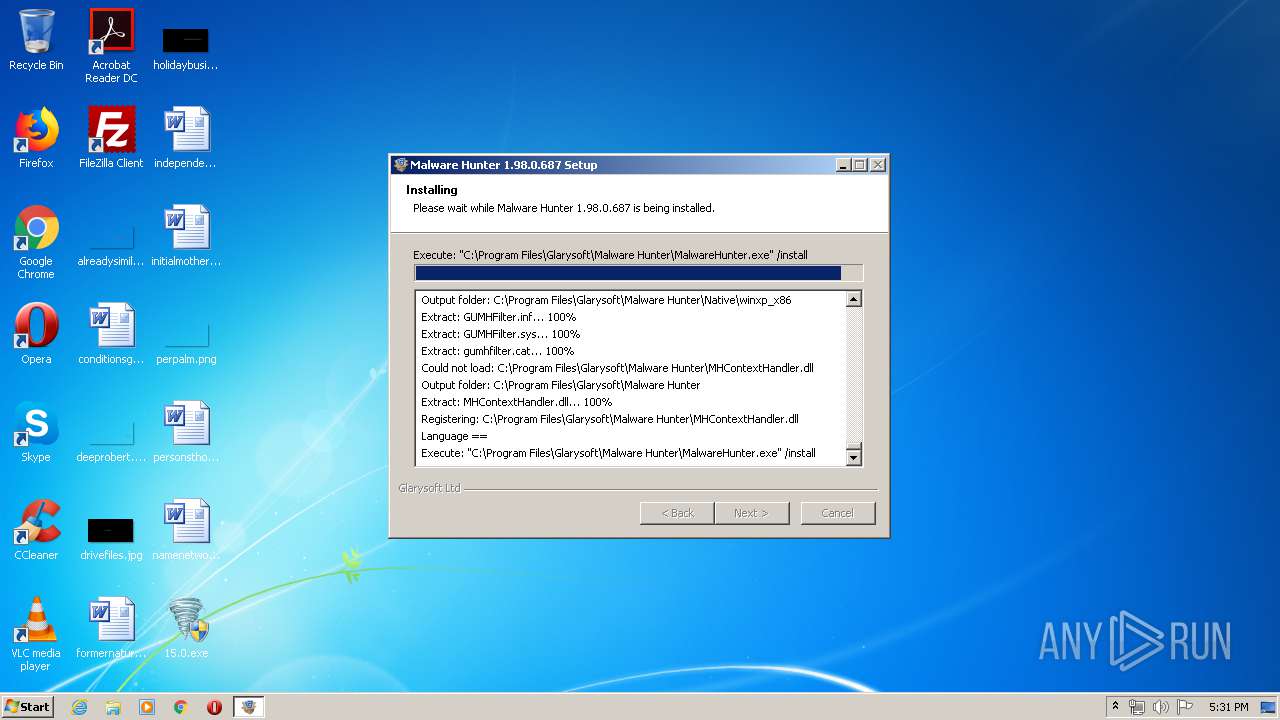
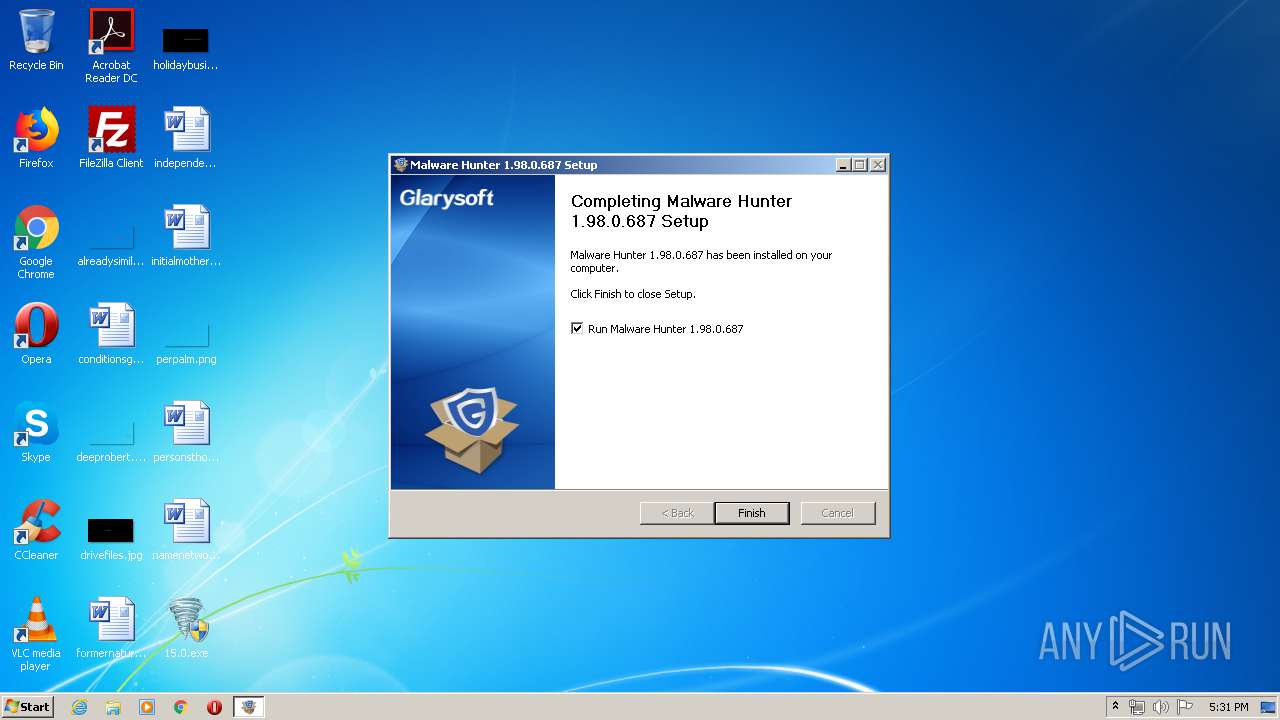
- mhsetup.exe (PID: 3508)
- mhsetup.exe (PID: 2064)
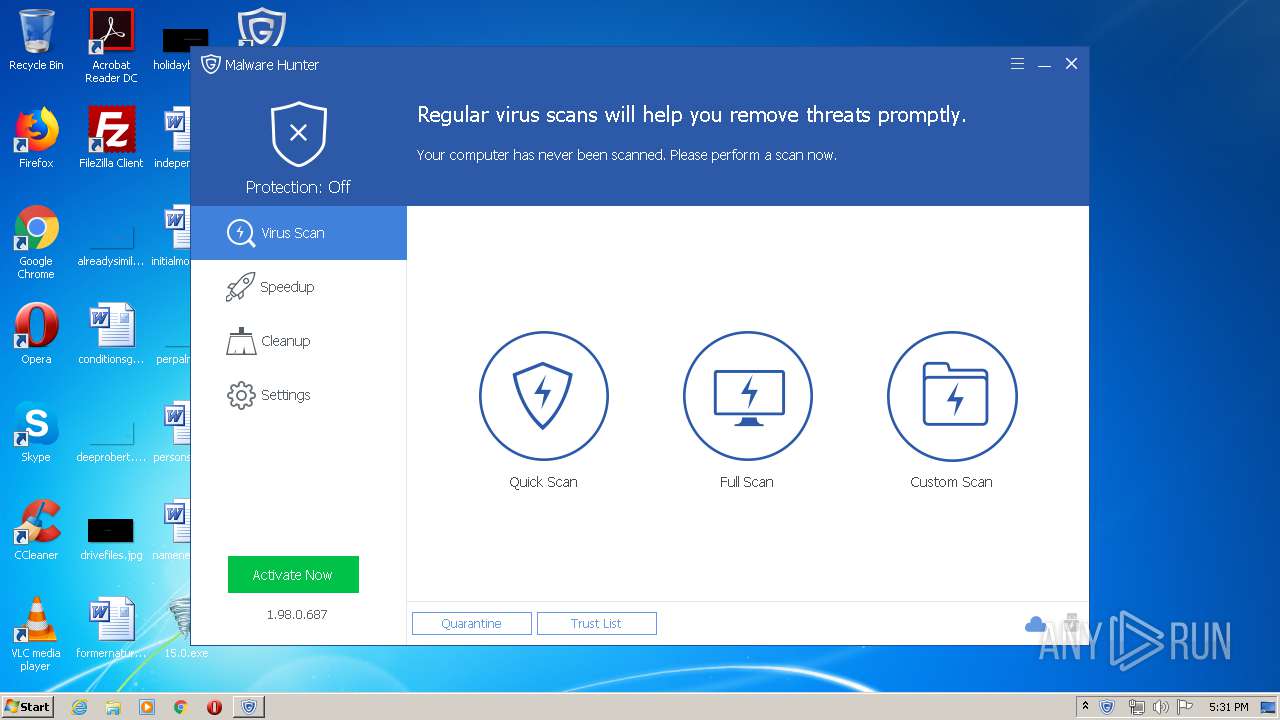
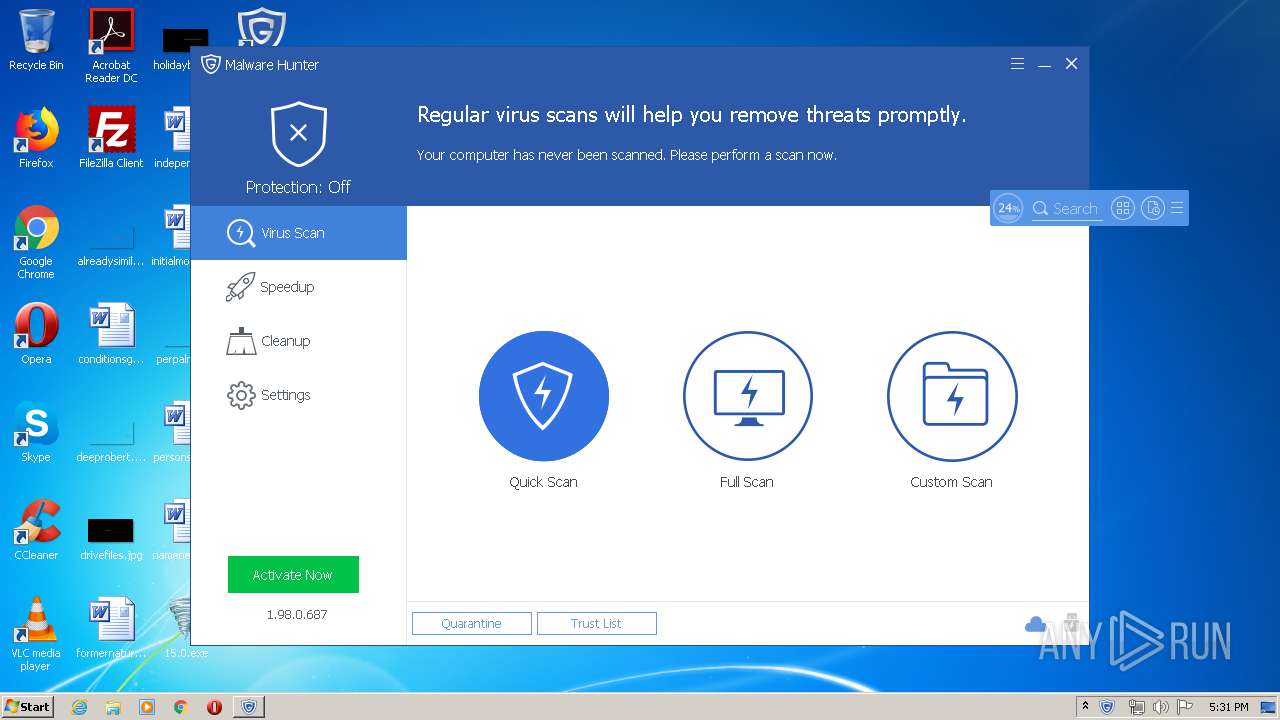
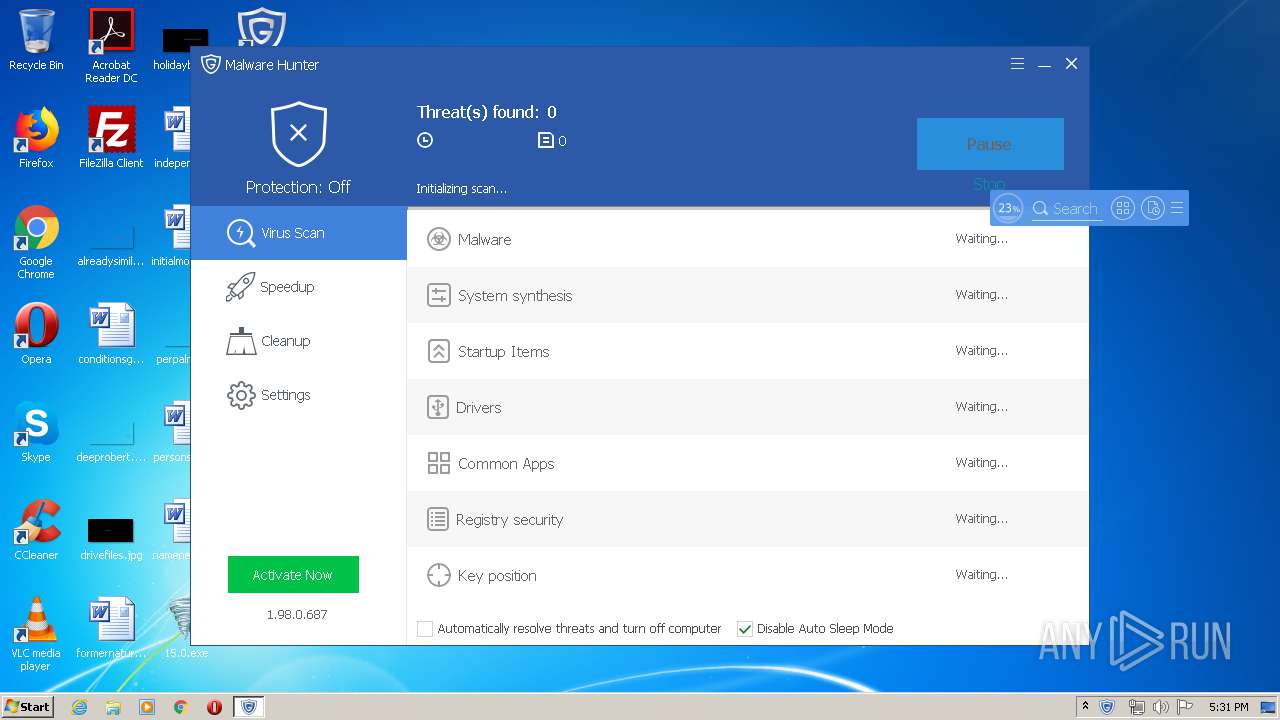
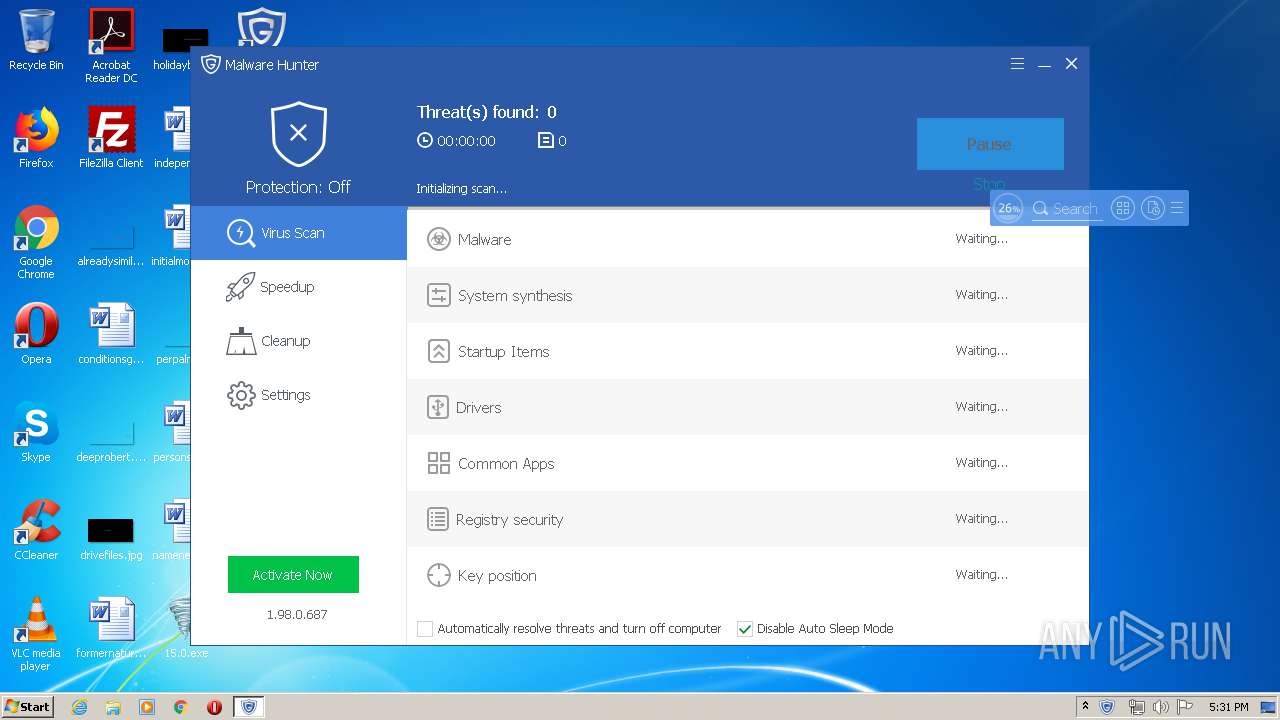
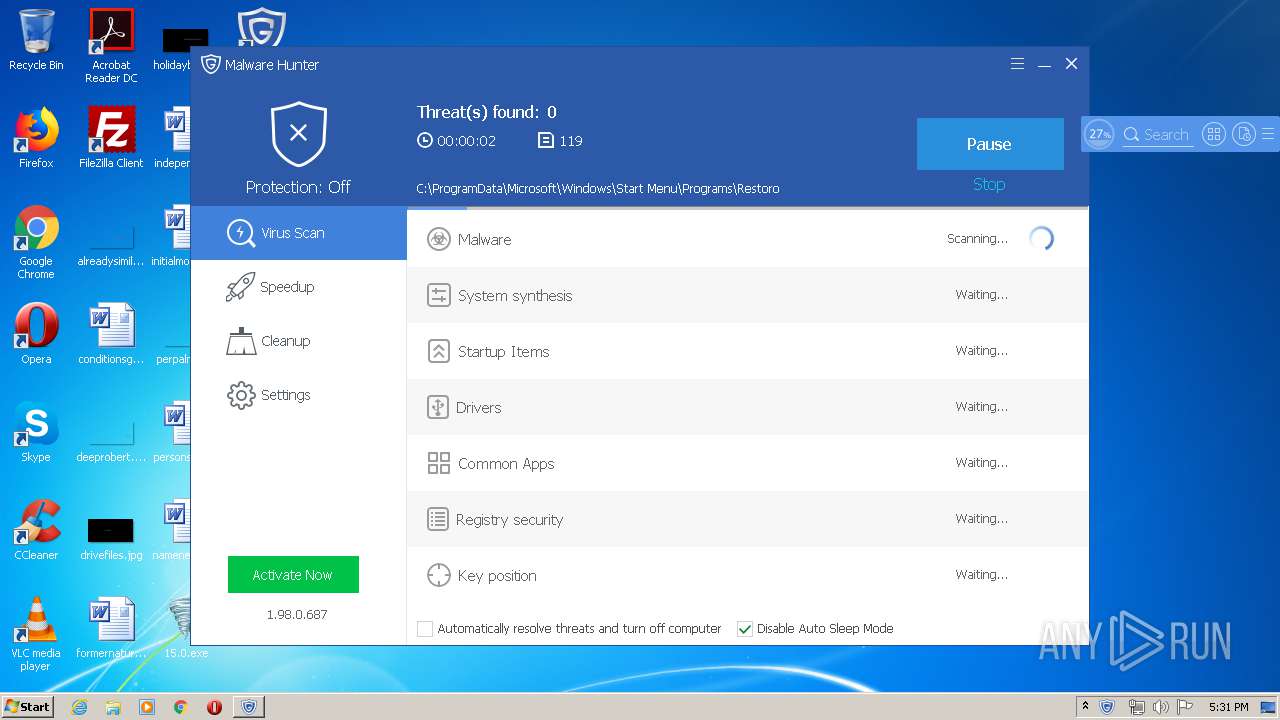
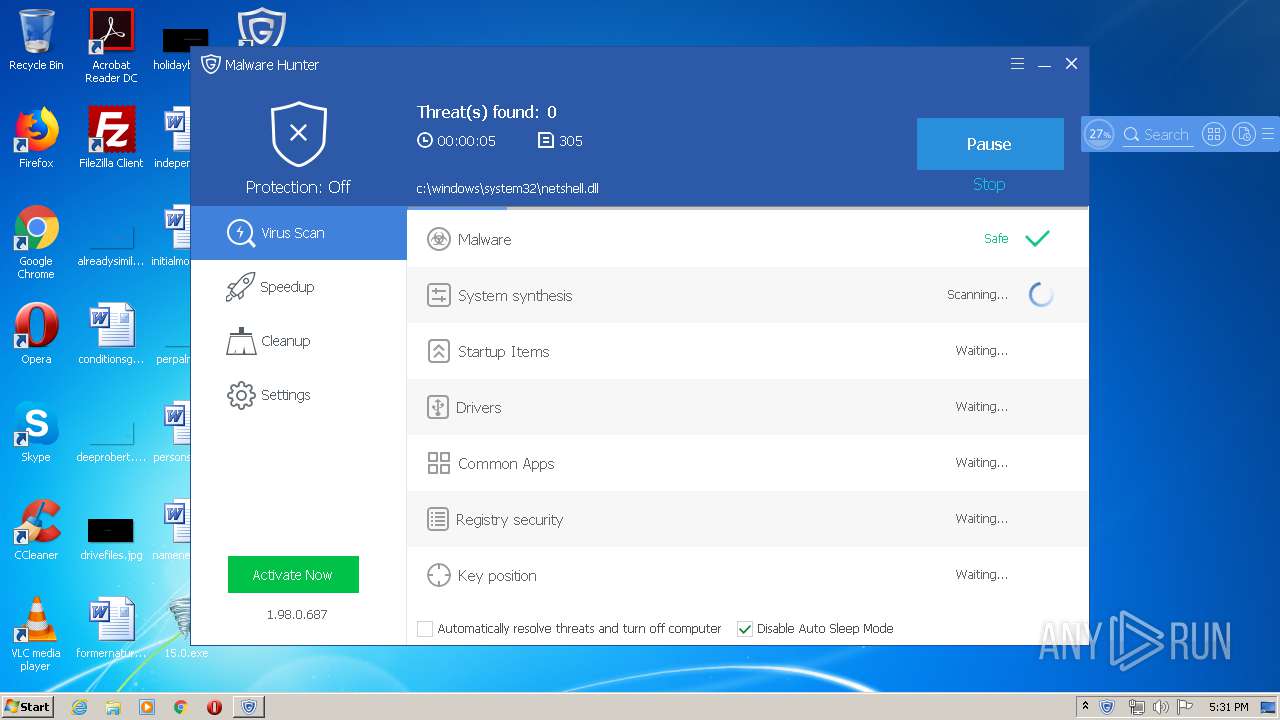
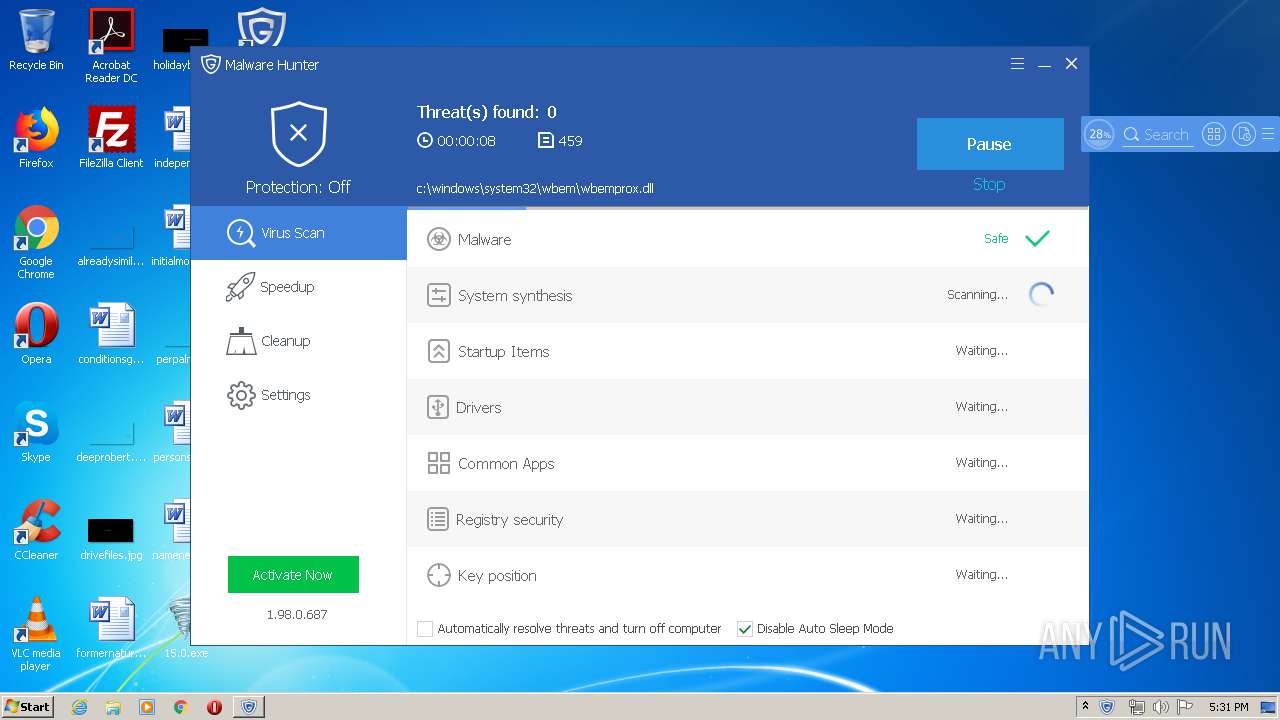
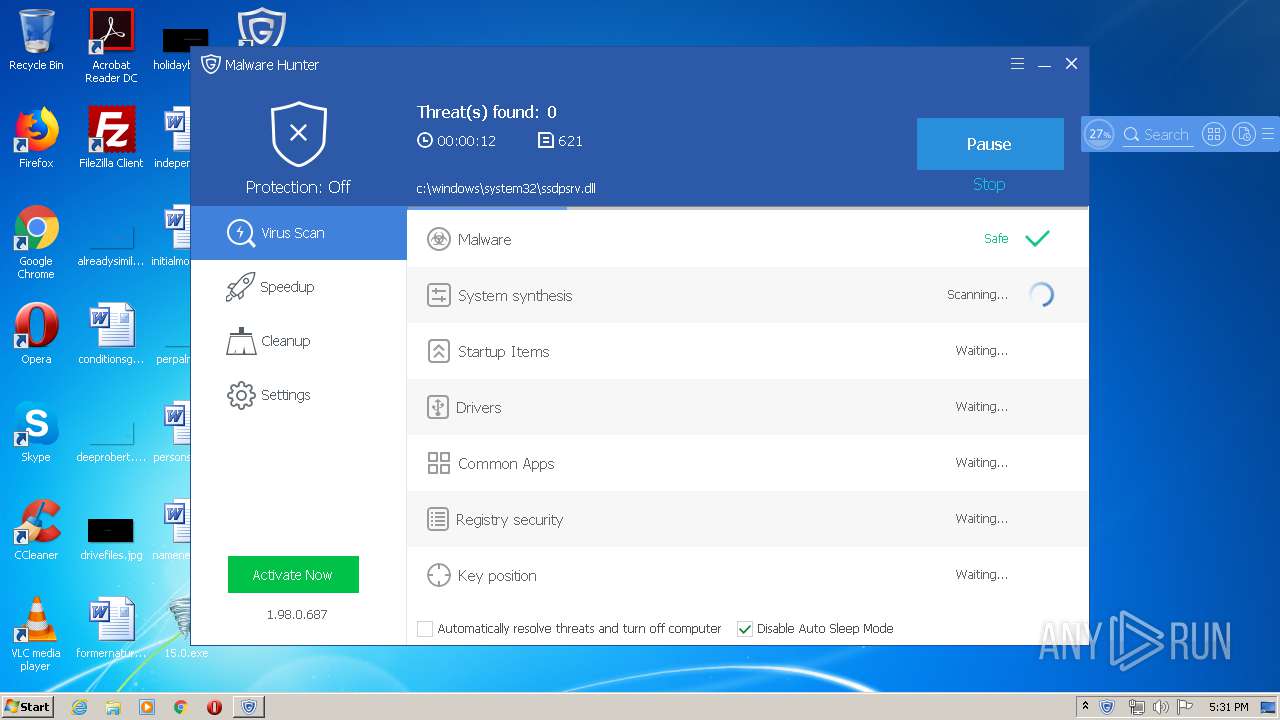
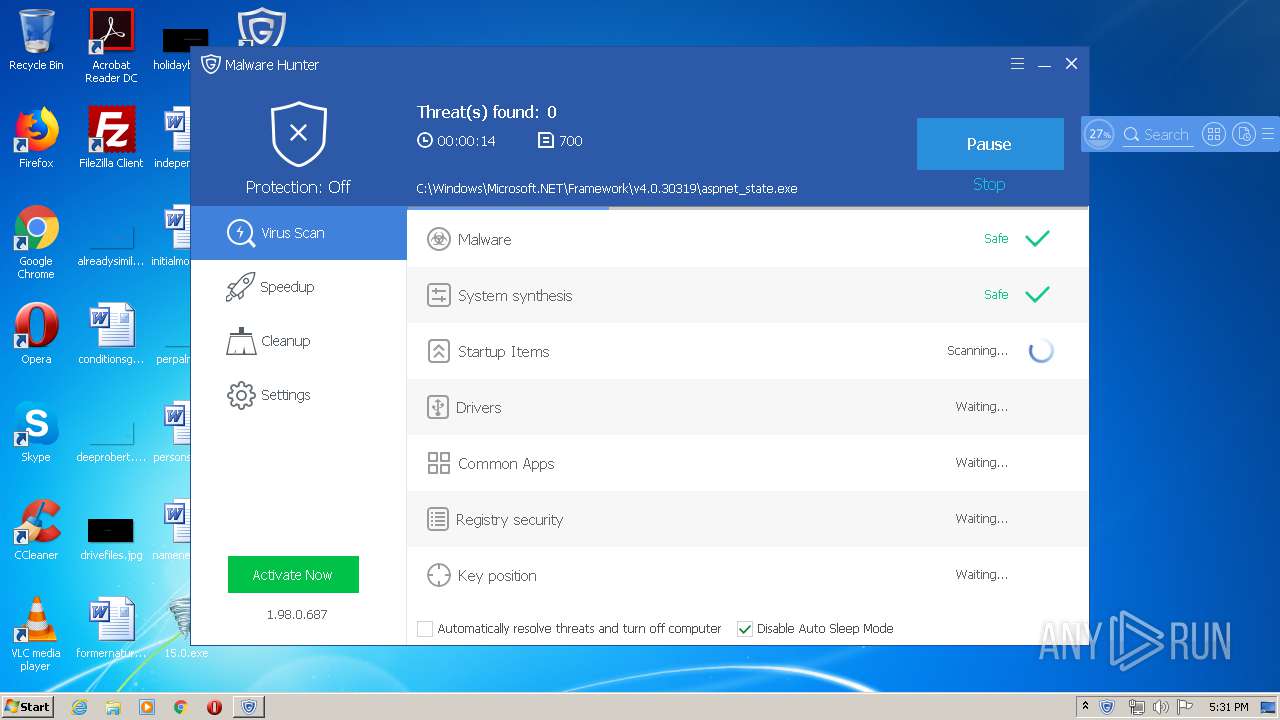
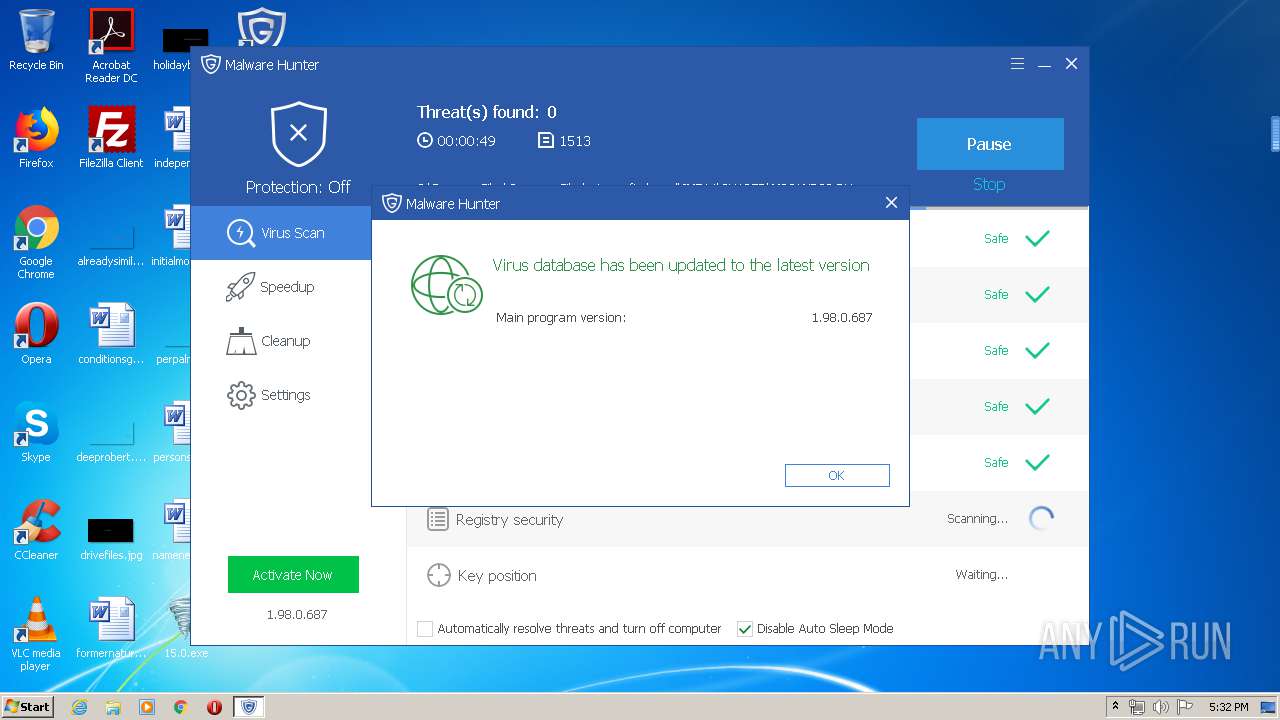
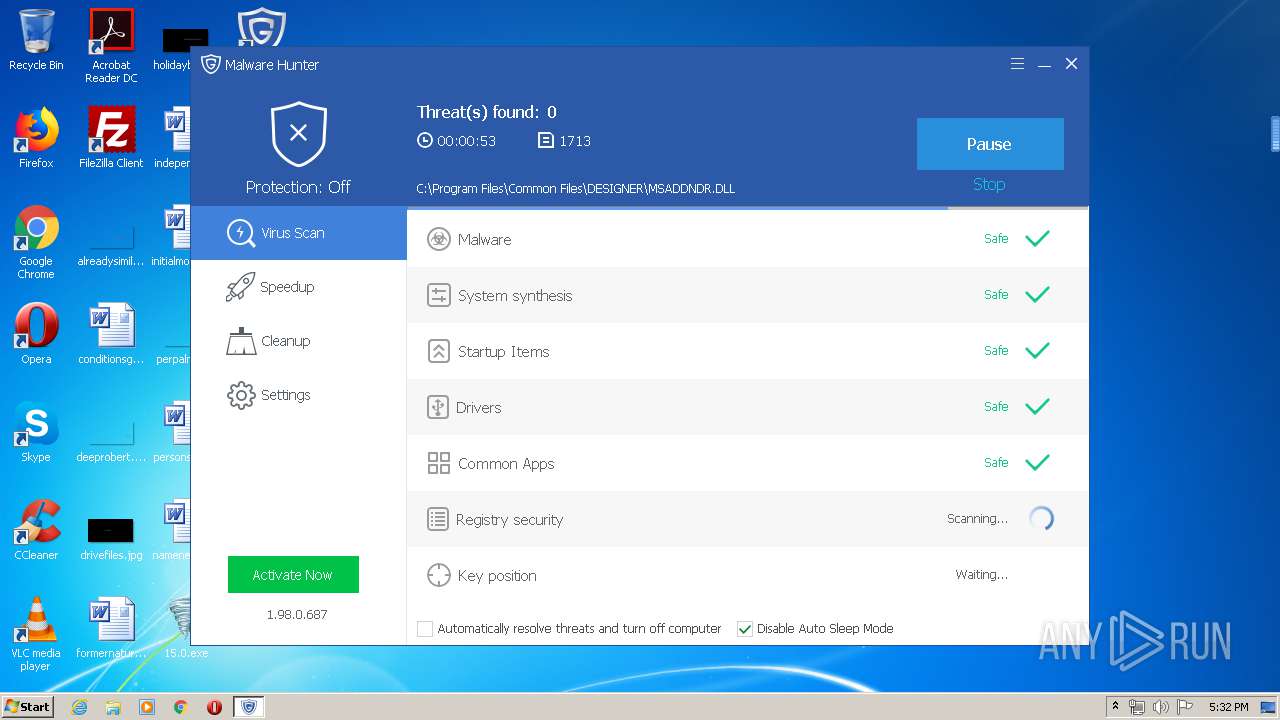
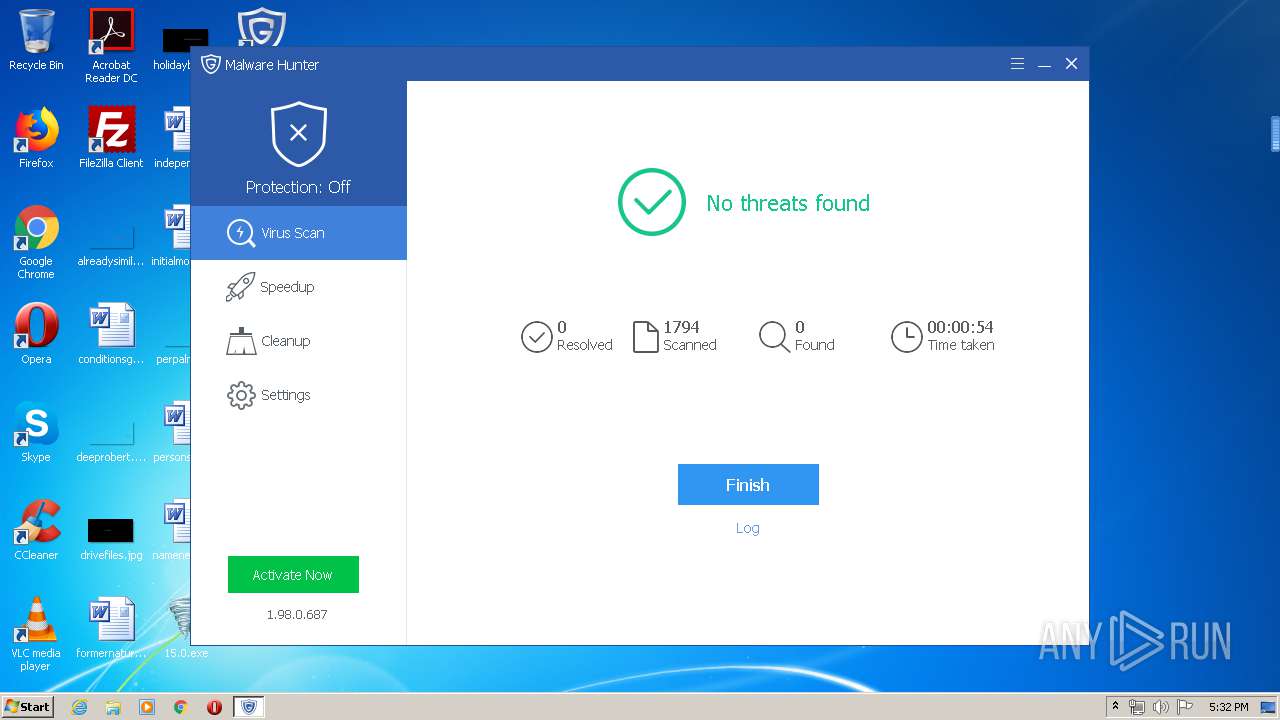
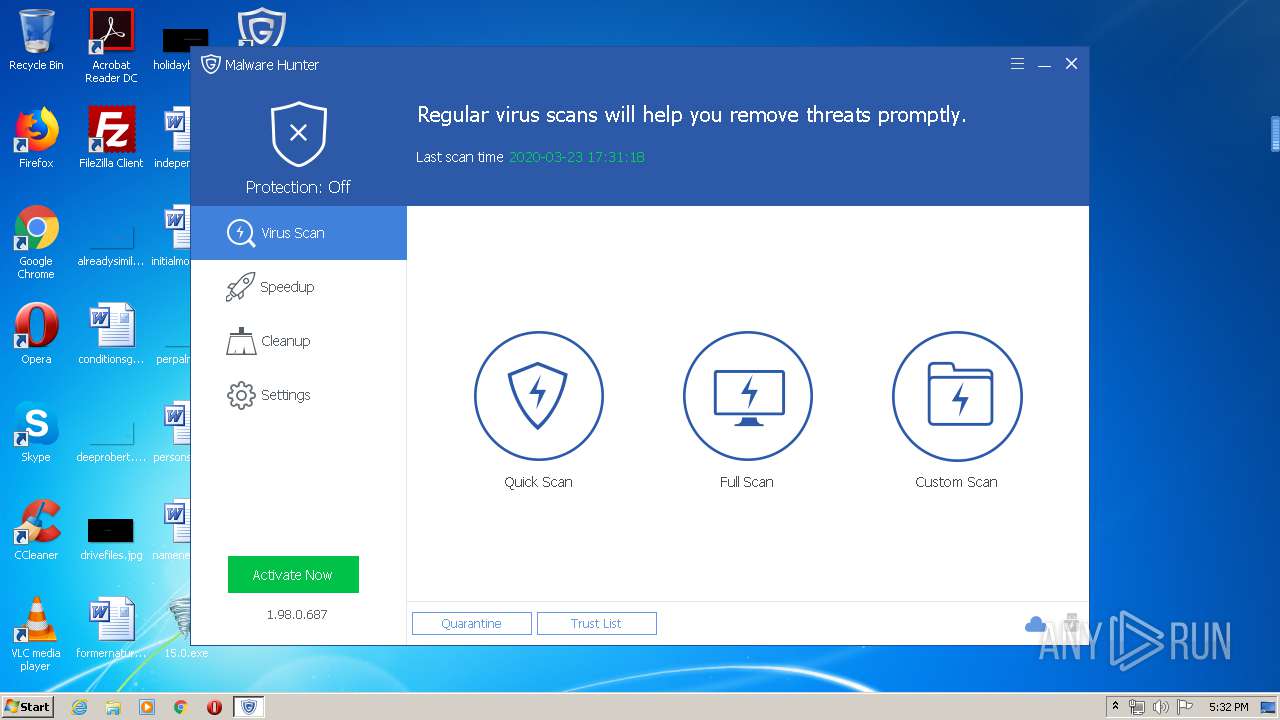
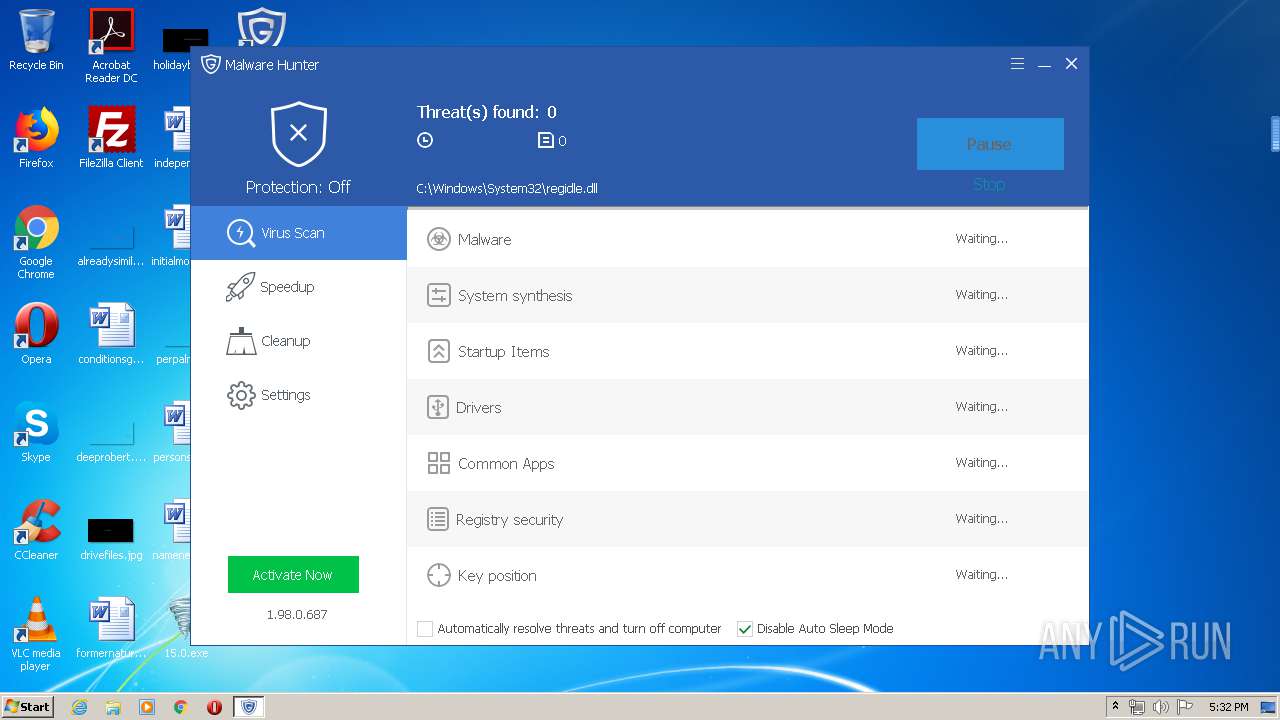
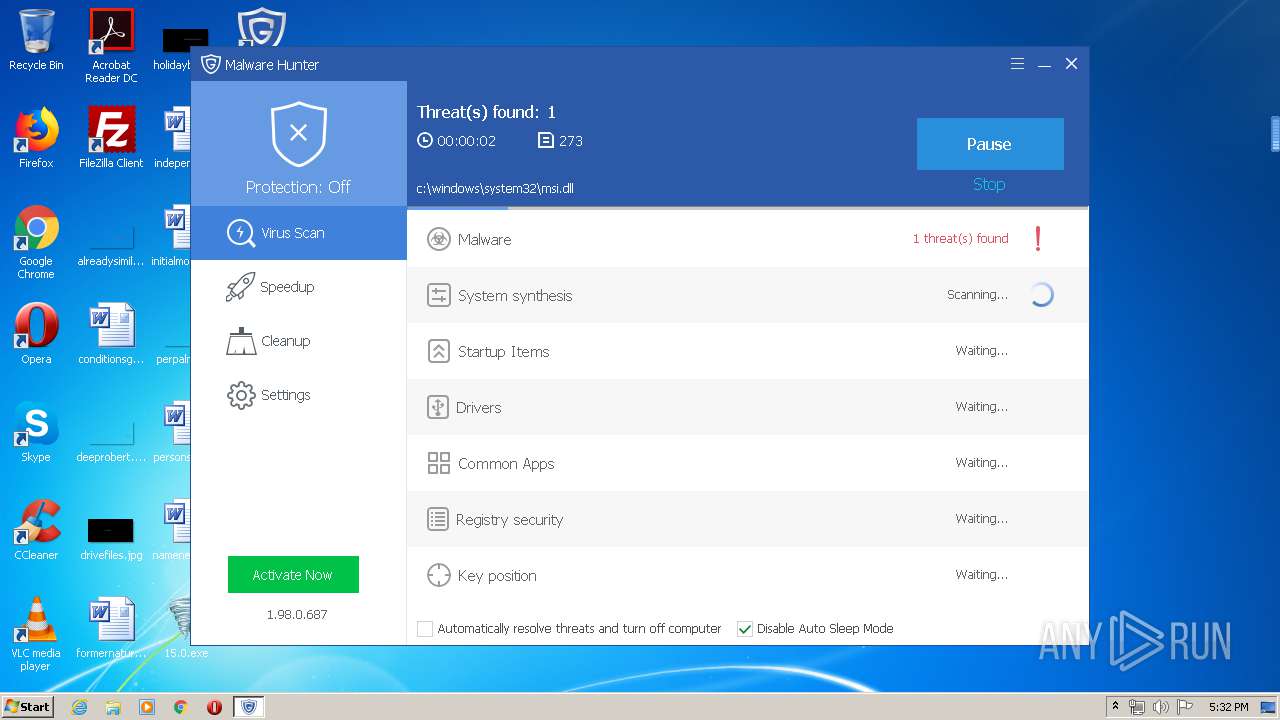
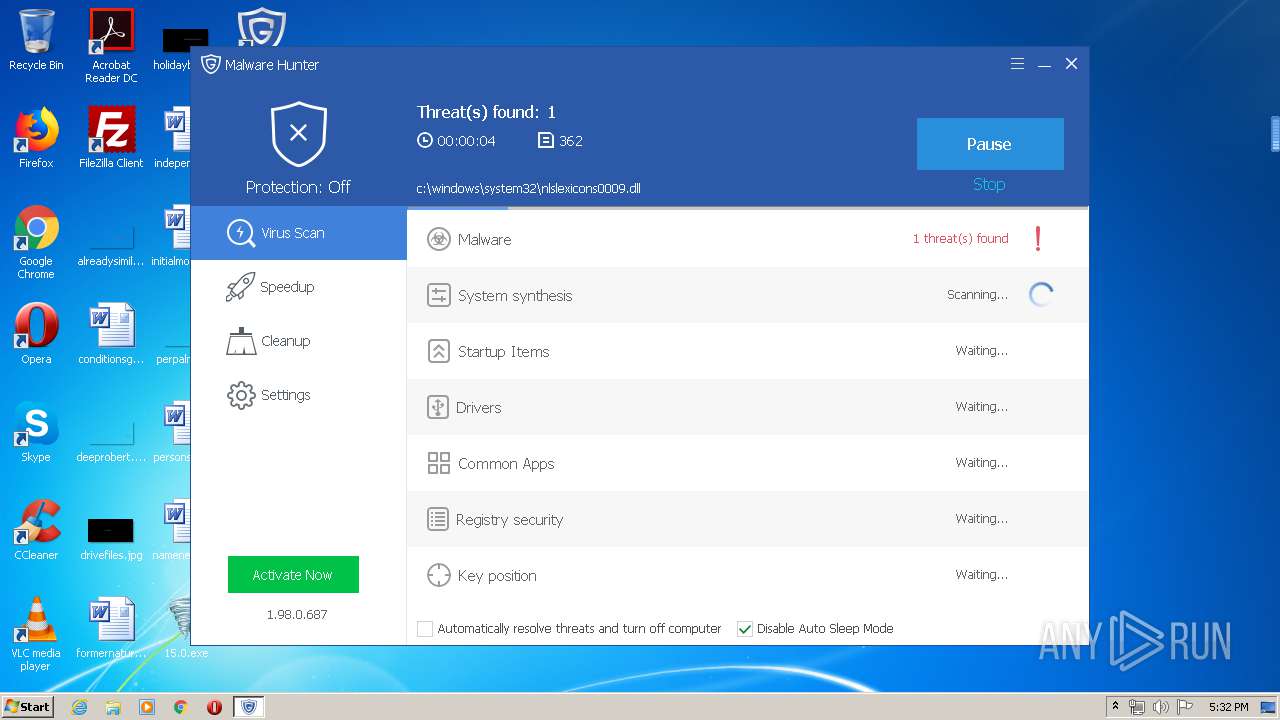
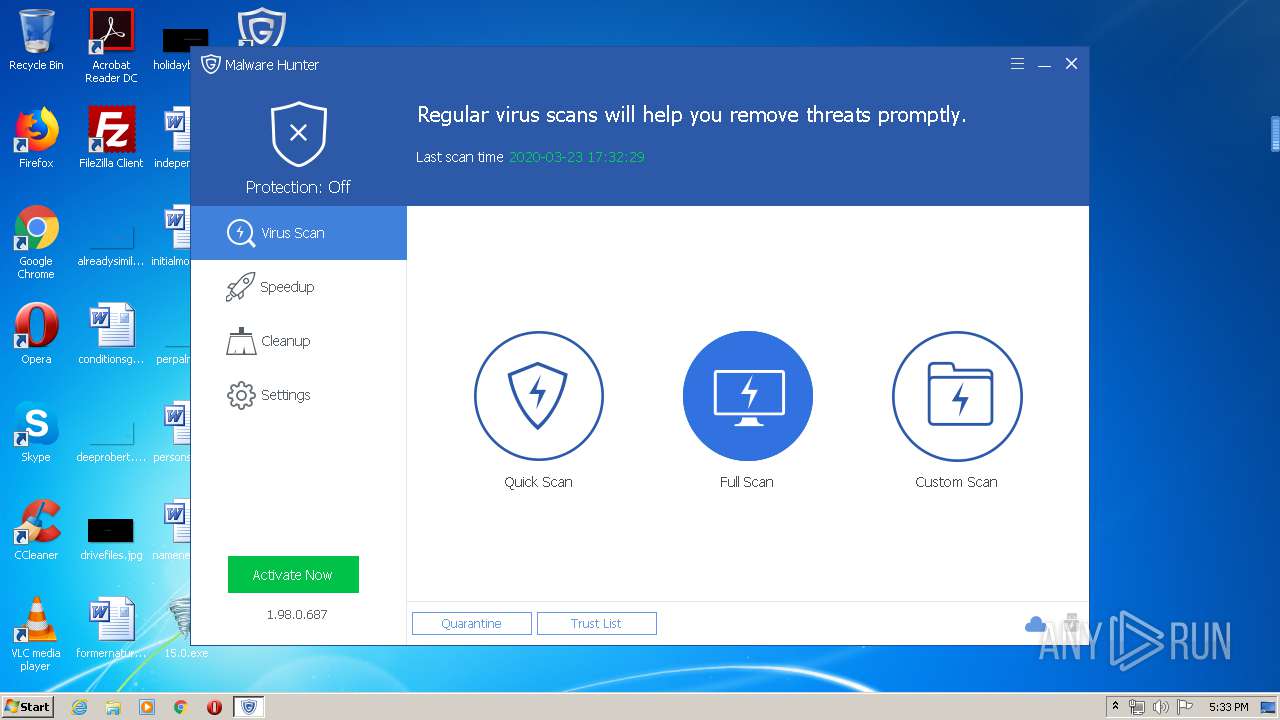
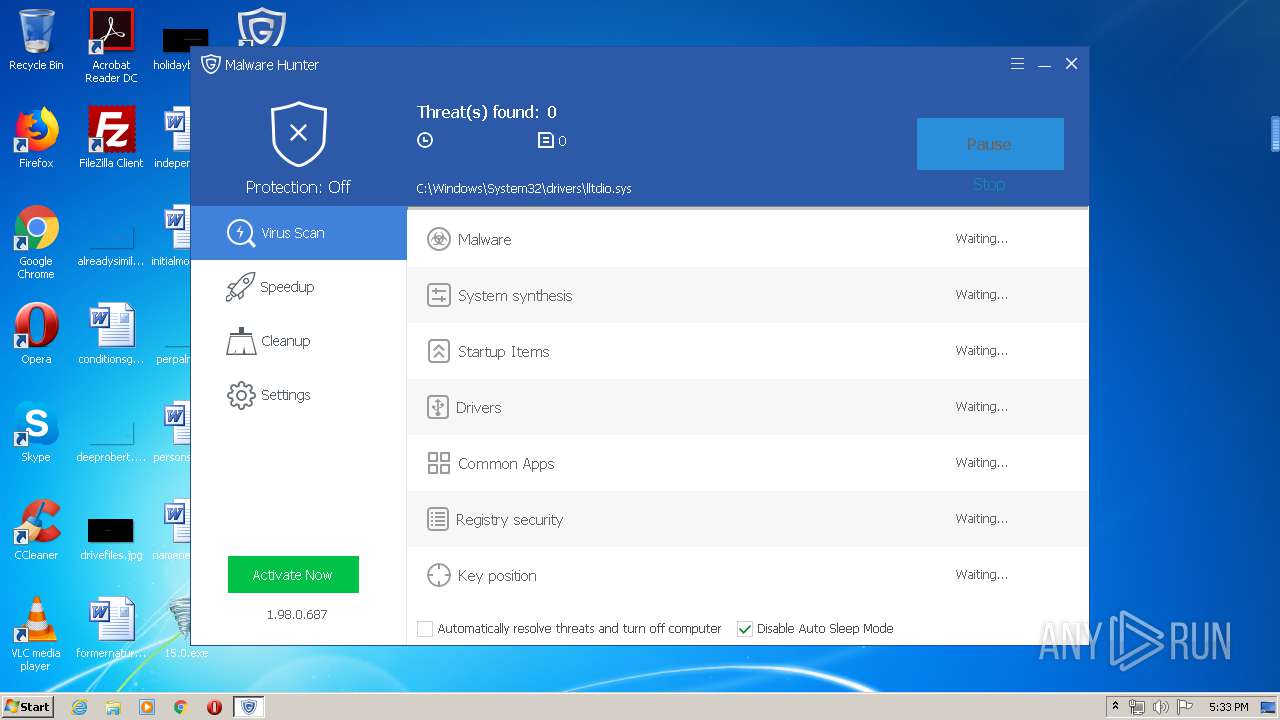
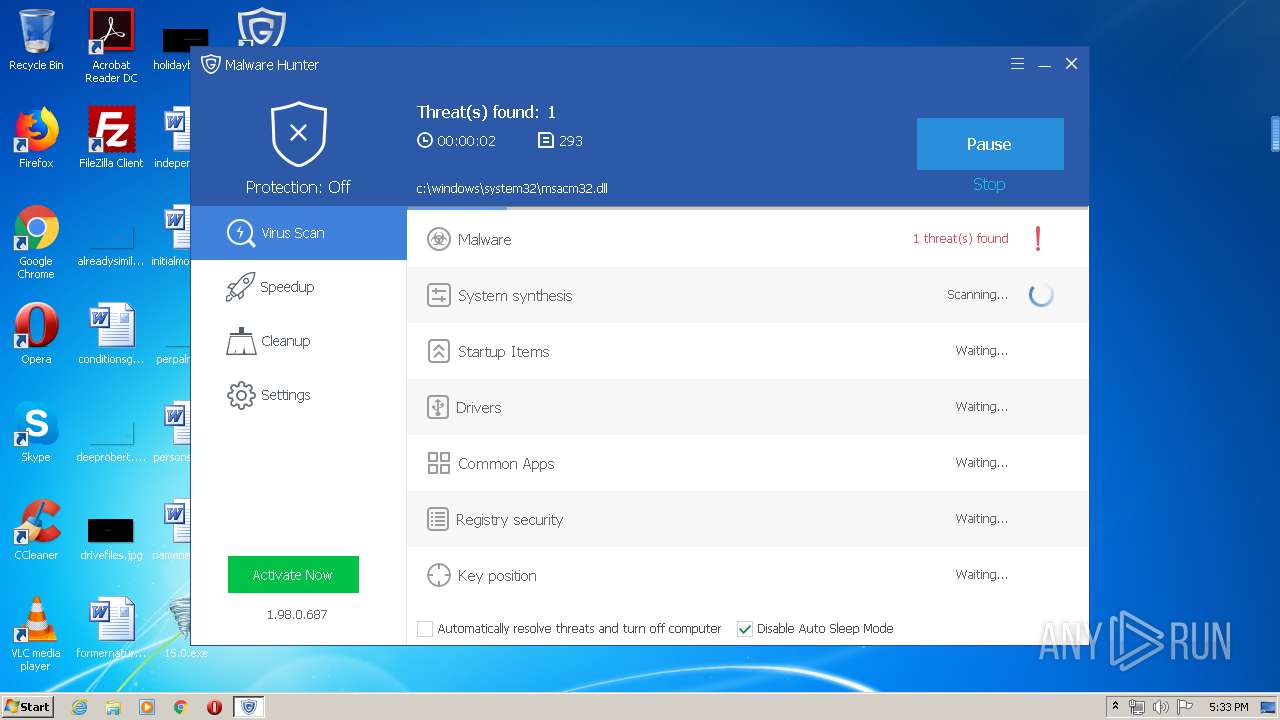
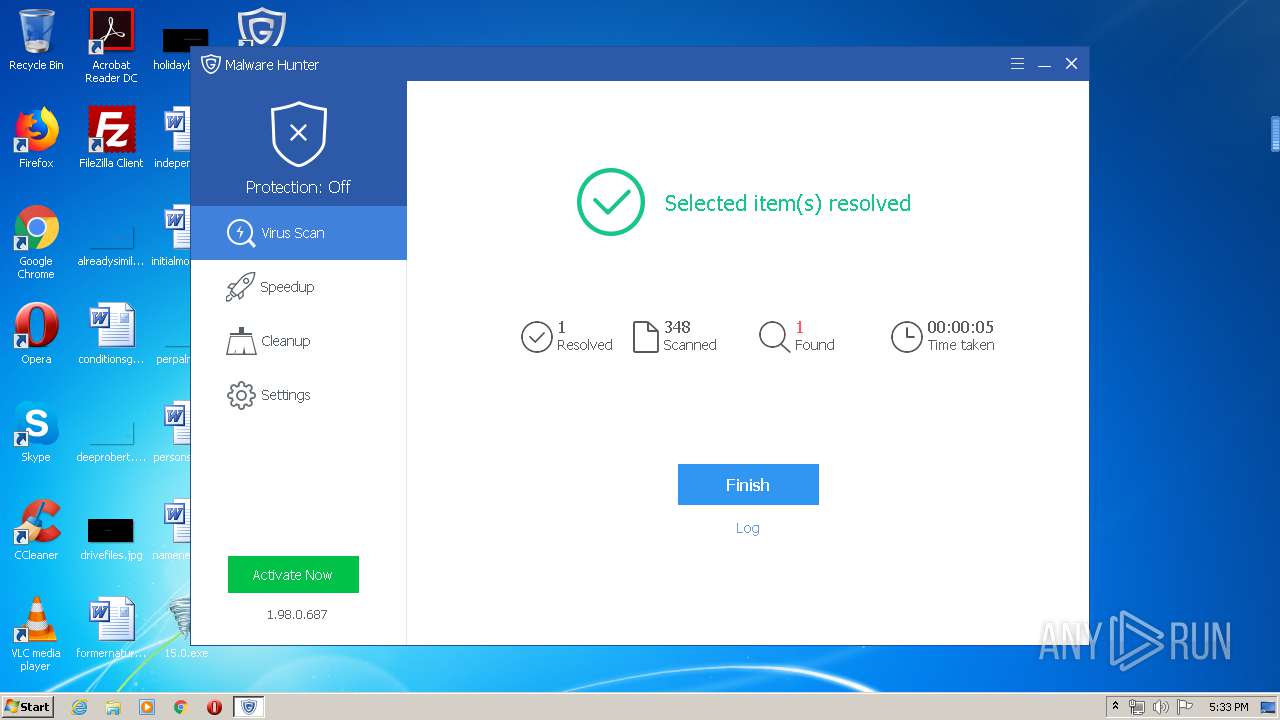
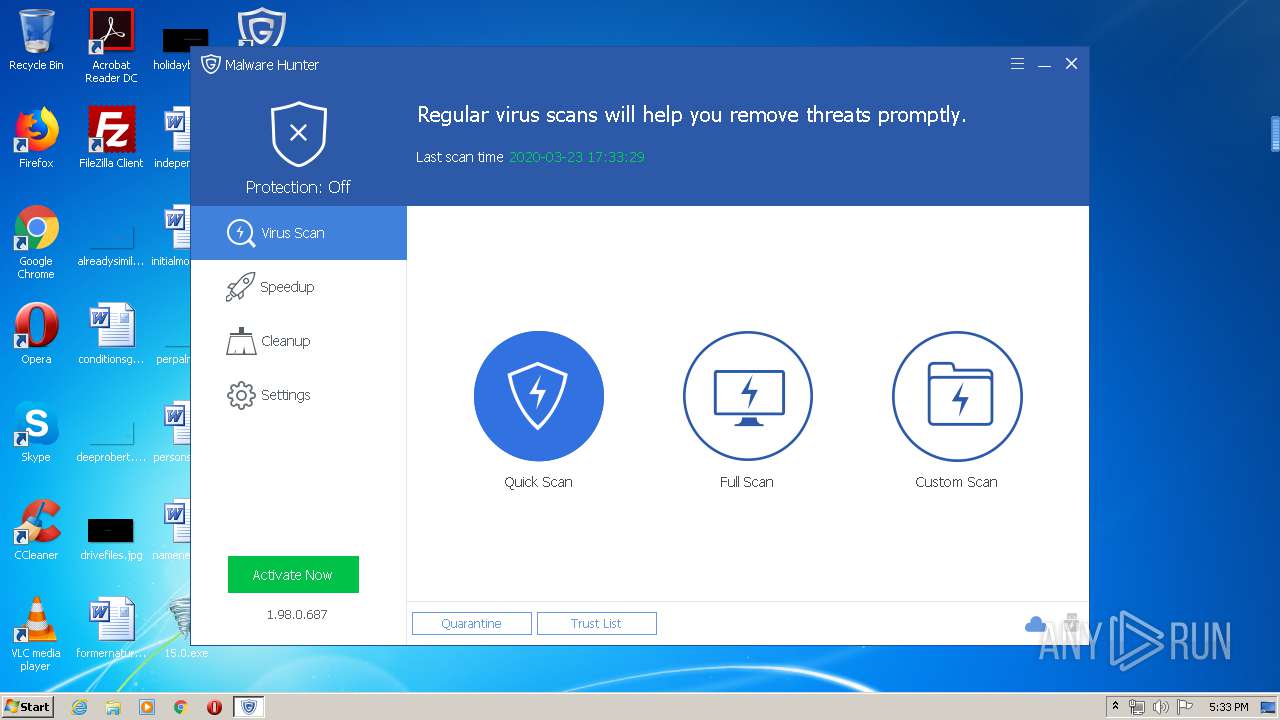
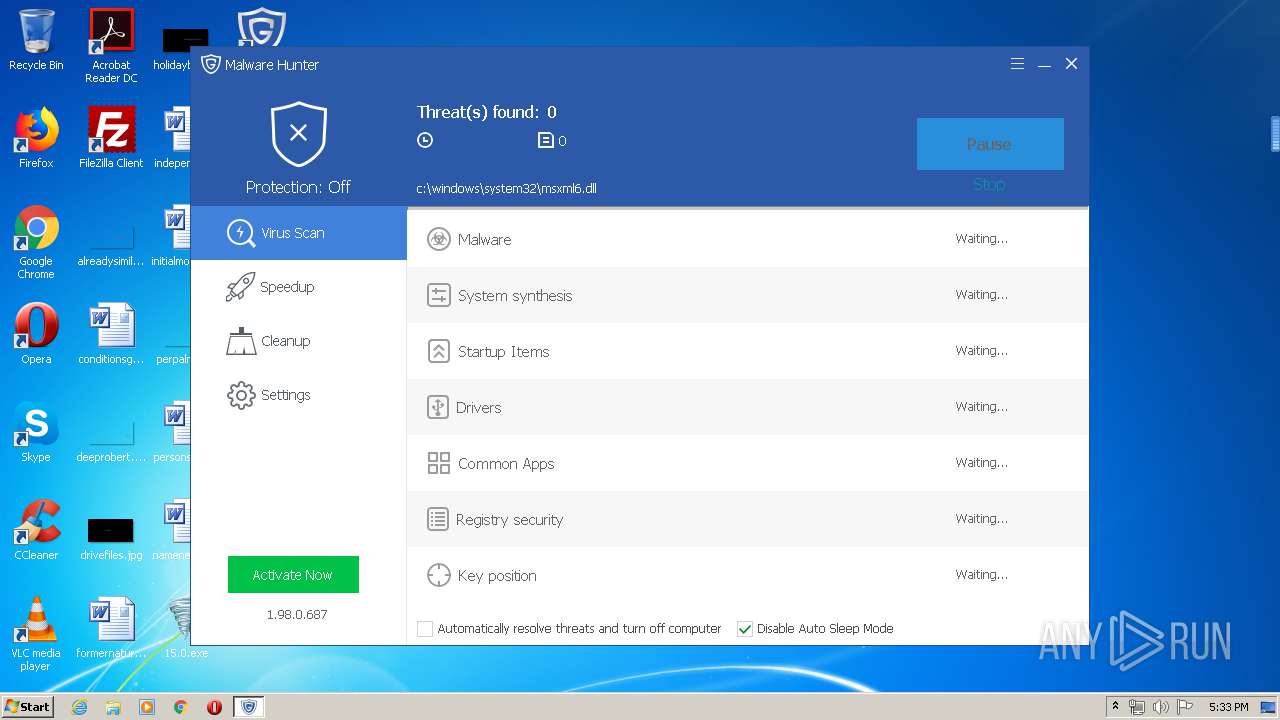
- MalwareHunter.exe (PID: 2972)
- MHCloudSvc.exe (PID: 3836)
- Initialize_Standalone_Pro.exe (PID: 3608)
- sendinfo.exe (PID: 2060)
- MalwareHunter.exe (PID: 3488)
- MHCloudSvc.exe (PID: 3328)
- mhtray.exe (PID: 3596)
- MalwareHunter.exe (PID: 2564)
- PCBooster.exe (PID: 2232)
- MemfilesService.exe (PID: 2356)
- QuickSearch.exe (PID: 1444)
Loads dropped or rewritten executable
- 15.0.exe (PID: 3900)
- OSPPSVC.EXE (PID: 2904)
- mhsetup.exe (PID: 2064)
- MalwareHunter.exe (PID: 2972)
- Initialize_Standalone_Pro.exe (PID: 3608)
- MHCloudSvc.exe (PID: 3836)
- MalwareHunter.exe (PID: 3488)
- sendinfo.exe (PID: 2060)
- mhtray.exe (PID: 3596)
- MHCloudSvc.exe (PID: 3328)
- PCBooster.exe (PID: 2232)
- MalwareHunter.exe (PID: 2564)
- QuickSearch.exe (PID: 1444)
- MemfilesService.exe (PID: 2356)
Changes Image File Execution Options
- ±©·ç¼¤»î15.0.exe (PID: 2644)
Loads the Task Scheduler COM API
- OSPPSVC.EXE (PID: 2904)
- MalwareHunter.exe (PID: 2972)
- MalwareHunter.exe (PID: 3488)
Changes settings of System certificates
- MalwareHunter.exe (PID: 2972)
- ¼¤»î¹¤¾ß8.exe (PID: 3456)
Changes the autorun value in the registry
- mhtray.exe (PID: 3596)
SUSPICIOUS
Executable content was dropped or overwritten
- _¼¤»î¹¤¾ß8.exe (PID: 2596)
- 15.0.exe (PID: 3900)
- DvLayout.exe (PID: 3288)
- ±©·ç¼¤»î15.0.exe (PID: 2644)
- chrome.exe (PID: 872)
- mhsetup.exe (PID: 2064)
- MalwareHunter.exe (PID: 2972)
- sendinfo.exe (PID: 2060)
Starts CMD.EXE for self-deleting
- _¼¤»î¹¤¾ß8.exe (PID: 2596)
Creates files in the Windows directory
- ¼¤»î¹¤¾ß8.exe (PID: 3456)
- ±©·ç¼¤»î15.0.exe (PID: 2644)
- MalwareHunter.exe (PID: 2972)
Executed as Windows Service
- ¼¤»î¹¤¾ß8.exe (PID: 3456)
- Windows Mobile User Experience Server.exe (PID: 3872)
- KMSService.exe (PID: 2248)
- SppExtComObjPatcher.exe (PID: 3640)
Starts CMD.EXE for commands execution
- _¼¤»î¹¤¾ß8.exe (PID: 2596)
- DvLayout.exe (PID: 3288)
Creates or modifies windows services
- Windows Mobile User Experience Server.exe (PID: 3872)
Removes files from Windows directory
- ¼¤»î¹¤¾ß8.exe (PID: 3456)
Uses WMIC.EXE to obtain a system information
- ¼¤»î¹¤¾ß8.exe (PID: 3456)
- ±©·ç¼¤»î15.0.exe (PID: 2644)
Uses NETSH.EXE for network configuration
- ±©·ç¼¤»î15.0.exe (PID: 2644)
Reads Environment values
- ¼¤»î¹¤¾ß8.exe (PID: 3456)
Low-level read access rights to disk partition
- ¼¤»î¹¤¾ß8.exe (PID: 3456)
Executes scripts
- ±©·ç¼¤»î15.0.exe (PID: 2644)
Modifies files in Chrome extension folder
- chrome.exe (PID: 872)
Creates COM task schedule object
- mhsetup.exe (PID: 2064)
Creates files in the driver directory
- MalwareHunter.exe (PID: 2972)
Creates files in the program directory
- MalwareHunter.exe (PID: 2972)
- mhsetup.exe (PID: 2064)
- MalwareHunter.exe (PID: 3488)
- MHCloudSvc.exe (PID: 3328)
- PCBooster.exe (PID: 2232)
- MemfilesService.exe (PID: 2356)
Adds / modifies Windows certificates
- MalwareHunter.exe (PID: 2972)
- ¼¤»î¹¤¾ß8.exe (PID: 3456)
Creates a software uninstall entry
- mhsetup.exe (PID: 2064)
- sendinfo.exe (PID: 2060)
Creates files in the user directory
- mhsetup.exe (PID: 2064)
- PCBooster.exe (PID: 2232)
Reads Internet Cache Settings
- sendinfo.exe (PID: 2060)
- MalwareHunter.exe (PID: 3488)
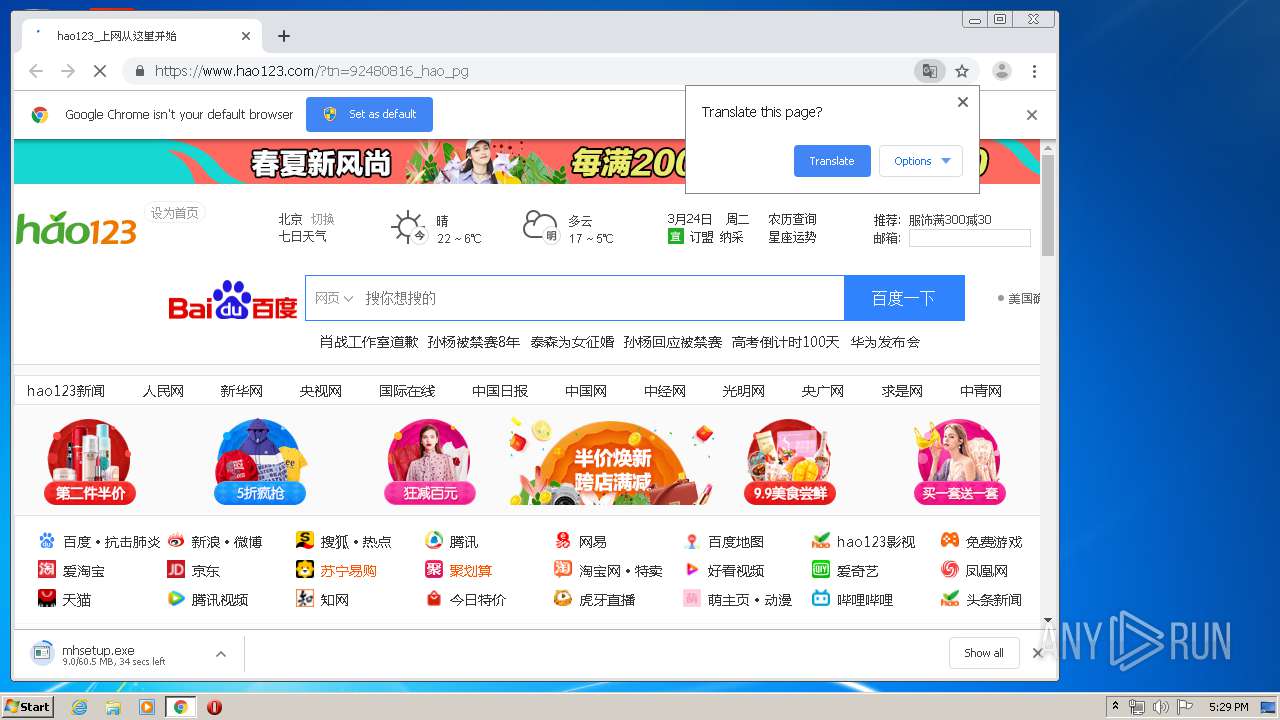
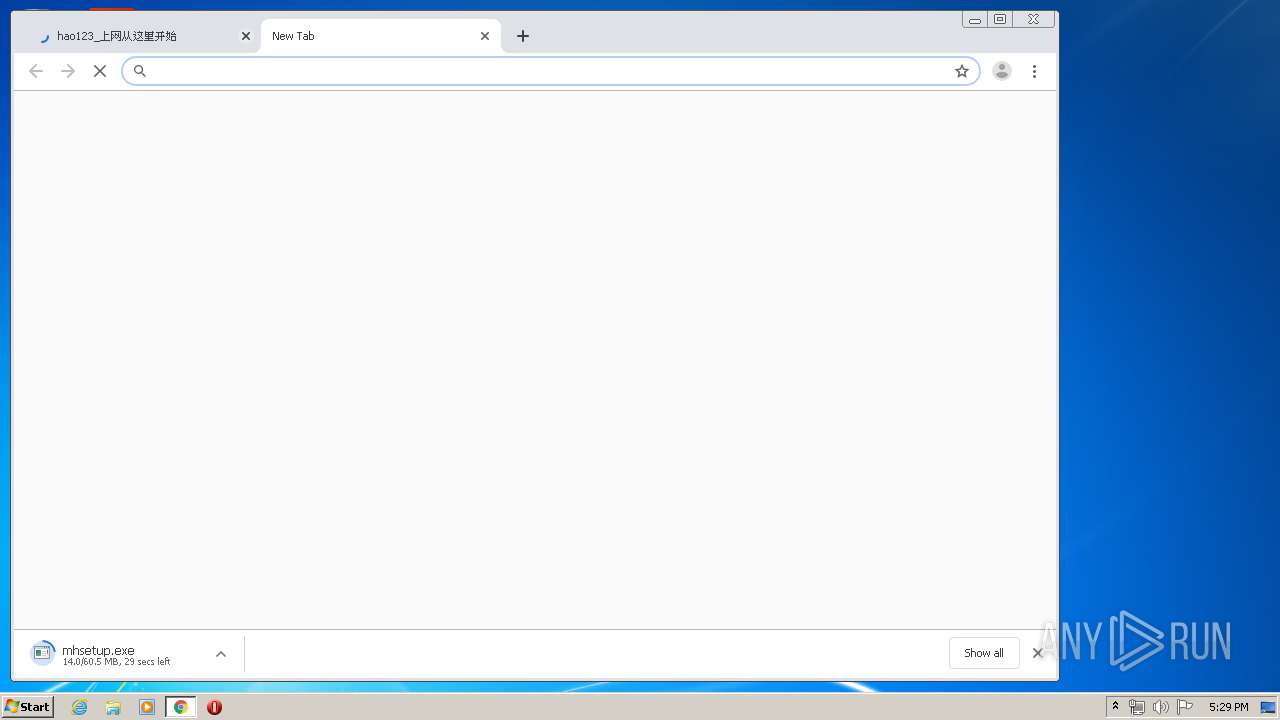
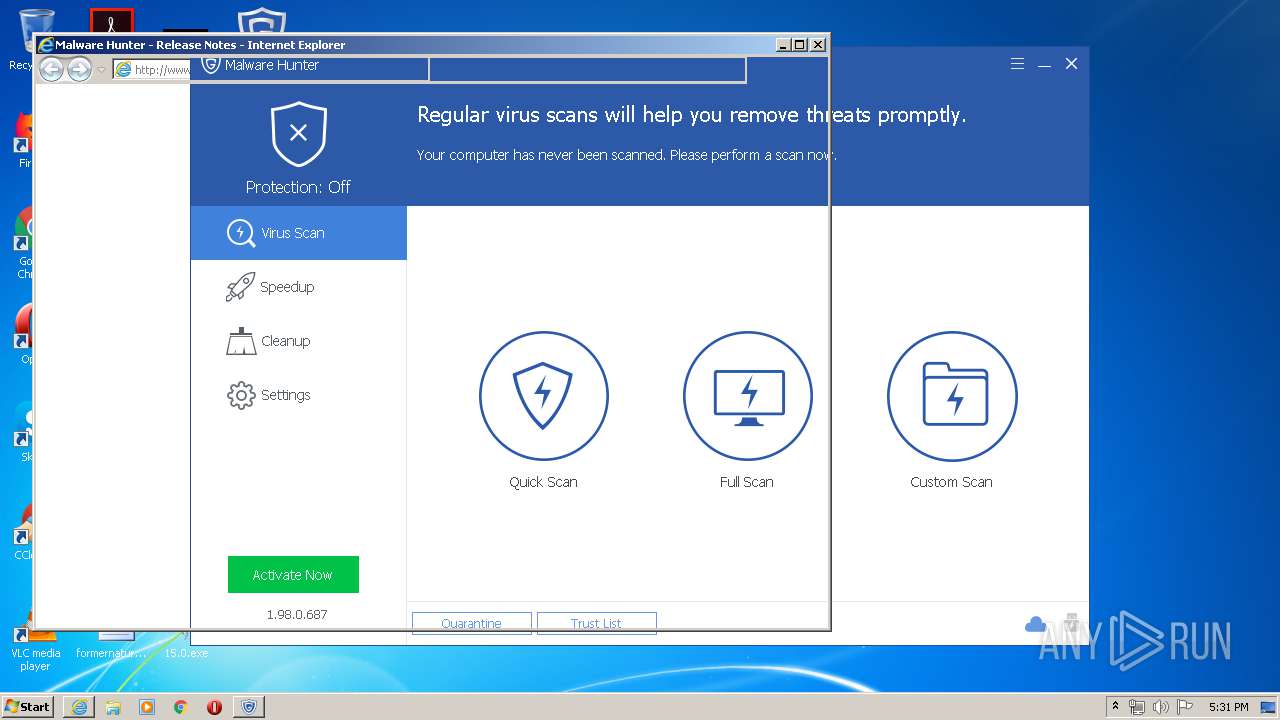
Starts Internet Explorer
- mhsetup.exe (PID: 2064)
Executed via COM
- MHCloudSvc.exe (PID: 3328)
Reads internet explorer settings
- QuickSearch.exe (PID: 1444)
INFO
Reads settings of System Certificates
- ¼¤»î¹¤¾ß8.exe (PID: 3456)
- chrome.exe (PID: 3164)
- iexplore.exe (PID: 3240)
Application launched itself
- chrome.exe (PID: 872)
- iexplore.exe (PID: 3020)
Reads the hosts file
- chrome.exe (PID: 3164)
- chrome.exe (PID: 872)
Manual execution by user
- chrome.exe (PID: 872)
Dropped object may contain Bitcoin addresses
- OSPPSVC.EXE (PID: 2904)
- mhsetup.exe (PID: 2064)
- chrome.exe (PID: 3164)
Reads Internet Cache Settings
- chrome.exe (PID: 872)
- iexplore.exe (PID: 3020)
- iexplore.exe (PID: 3240)
Changes internet zones settings
- iexplore.exe (PID: 3020)
Reads internet explorer settings
- iexplore.exe (PID: 3240)
Changes settings of System certificates
- iexplore.exe (PID: 3240)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:19 16:41:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 28160 |
| InitializedDataSize: | 267264 |
| UninitializedDataSize: | 8192 |
| EntryPoint: | 0x3961 |
| OSVersion: | 5.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Dec-2016 15:41:32 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 19-Dec-2016 15:41:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006C4E | 0x00006E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.31313 |
.rdata | 0x00008000 | 0x00001E3A | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.30616 |
.data | 0x0000A000 | 0x0003E0F8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.61647 |
.ndata | 0x00049000 | 0x00046000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0008F000 | 0x00013868 | 0x00013A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.42551 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29545 | 1081 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 0 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 4.41823 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68733 | 494 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.86626 | 228 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
133
Monitored processes
72
Malicious processes
15
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,15885712796242254436,6555140473145507001,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14770366456486979510 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 572 | C:\Users\admin\AppData\local\Mlxg_km\DvUpdate.exe | C:\Users\admin\AppData\local\Mlxg_km\DvUpdate.exe | Windows Mobile User Experience Server.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,15885712796242254436,6555140473145507001,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6953755456272615488 --mojo-platform-channel-handle=3912 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 880 | cscript "C:\Program Files\Microsoft Office\Office14\\ospp.vbs" /dstatus | C:\Windows\system32\cscript.exe | — | ±©·ç¼¤»î15.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,15885712796242254436,6555140473145507001,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2297765633278422737 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Glarysoft\Malware Hunter\QuickSearch.exe" /Mini 197370 | C:\Program Files\Glarysoft\Malware Hunter\QuickSearch.exe | — | PCBooster.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities QuickSearch Exit code: 0 Version: 5.35.0.124 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,15885712796242254436,6555140473145507001,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=99681544347175047 --mojo-platform-channel-handle=2816 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,15885712796242254436,6555140473145507001,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3467238809829615280 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3972 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,15885712796242254436,6555140473145507001,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16386281686991071116 --mojo-platform-channel-handle=3448 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
5 720
Read events
3 904
Write events
1 807
Delete events
9
Modification events
| (PID) Process: | (3456) ¼¤»î¹¤¾ß8.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3456) ¼¤»î¹¤¾ß8.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000002000000090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3288) DvLayout.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\MLXG |
| Operation: | write | Name: | Channel |
Value: dWcrnd2YL54HDo6u | |||
| (PID) Process: | (2596) _¼¤»î¹¤¾ß8.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2596) _¼¤»î¹¤¾ß8.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3872) Windows Mobile User Experience Server.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Windows Mobile User Experience Server |
| Operation: | write | Name: | version |
Value: 0.1 | |||
| (PID) Process: | (3288) DvLayout.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3288) DvLayout.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3456) ¼¤»î¹¤¾ß8.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | DefaultConnectionSettings |
Value: 460000000300000009000000000000000000000000000000040000000000000000000000000000000000000000000000000000000100000002000000C0A8645A000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3456) ¼¤»î¹¤¾ß8.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
84
Suspicious files
100
Text files
755
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3900 | 15.0.exe | C:\Users\admin\AppData\Local\Temp\nsr7306.tmp | — | |
MD5:— | SHA256:— | |||
| 3456 | ¼¤»î¹¤¾ß8.exe | C:\Windows\TEMP\CabC5B9.tmp | — | |
MD5:— | SHA256:— | |||
| 3456 | ¼¤»î¹¤¾ß8.exe | C:\Windows\TEMP\TarC5BA.tmp | — | |
MD5:— | SHA256:— | |||
| 3456 | ¼¤»î¹¤¾ß8.exe | C:\Windows\system32\config\systemprofile\AppData\Roaming\Microsoft\Windows\Cookies\BDN4UM0F.txt | — | |
MD5:— | SHA256:— | |||
| 3456 | ¼¤»î¹¤¾ß8.exe | C:\Users\admin\AppData\Local\Temp\time.txt | text | |
MD5:— | SHA256:— | |||
| 3456 | ¼¤»î¹¤¾ß8.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E7EC0C85688F4738F3BE49B104BA67 | der | |
MD5:— | SHA256:— | |||
| 3900 | 15.0.exe | C:\Users\admin\AppData\local\Mlxg_km\DvLayout.exe | executable | |
MD5:— | SHA256:— | |||
| 3288 | DvLayout.exe | C:\Users\admin\AppData\local\Mlxg_km\WBKENYVA.sys | executable | |
MD5:— | SHA256:— | |||
| 3872 | Windows Mobile User Experience Server.exe | C:\Users\admin\AppData\local\Mlxg_km\st.ini | text | |
MD5:— | SHA256:— | |||
| 3900 | 15.0.exe | C:\Users\admin\AppData\local\Mlxg_km\DvUpdate.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
110
DNS requests
69
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3456 | ¼¤»î¹¤¾ß8.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gsorganizationvalsha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQMnk2cPe3vhNiR6XLHz4QGvBl7BwQUlt5h8b0cFilTHMDMfTuDAEDmGnwCDDgHcwPJHmvTnYYYUg%3D%3D | US | der | 1.54 Kb | whitelisted |
2060 | sendinfo.exe | POST | 200 | 54.186.7.180:80 | http://metrics.glarysoft.com/install.php | US | — | — | whitelisted |
3164 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
3456 | ¼¤»î¹¤¾ß8.exe | GET | 200 | 104.18.20.226:80 | http://crl.globalsign.net/root.crl | US | der | 914 b | whitelisted |
3240 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/css/global.css?1912021231 | US | html | 259 b | whitelisted |
3456 | ¼¤»î¹¤¾ß8.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/MEwwSjBIMEYwRDAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCCwQAAAAAAURO8EJH | US | der | 1.49 Kb | whitelisted |
3240 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/css/content.css?18011003 | US | html | 258 b | whitelisted |
3456 | ¼¤»î¹¤¾ß8.exe | GET | 302 | 104.193.88.123:80 | http://www.baidu.com/s?ie=utf-8&wd=ip | US | html | 285 b | whitelisted |
3240 | iexplore.exe | GET | 200 | 54.243.205.134:80 | http://www.glarysoft.com/update/release-notes/mh/1.98.0.687 | US | html | 25.5 Kb | whitelisted |
3240 | iexplore.exe | GET | 200 | 172.217.23.106:80 | http://fonts.googleapis.com/css?family=Open+Sans:400,300,600,800,700 | US | text | 290 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3456 | ¼¤»î¹¤¾ß8.exe | 104.193.88.123:80 | www.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | US | malicious |
3456 | ¼¤»î¹¤¾ß8.exe | 103.235.46.250:443 | wappass.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | suspicious |
3456 | ¼¤»î¹¤¾ß8.exe | 104.18.20.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
3456 | ¼¤»î¹¤¾ß8.exe | 104.18.21.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
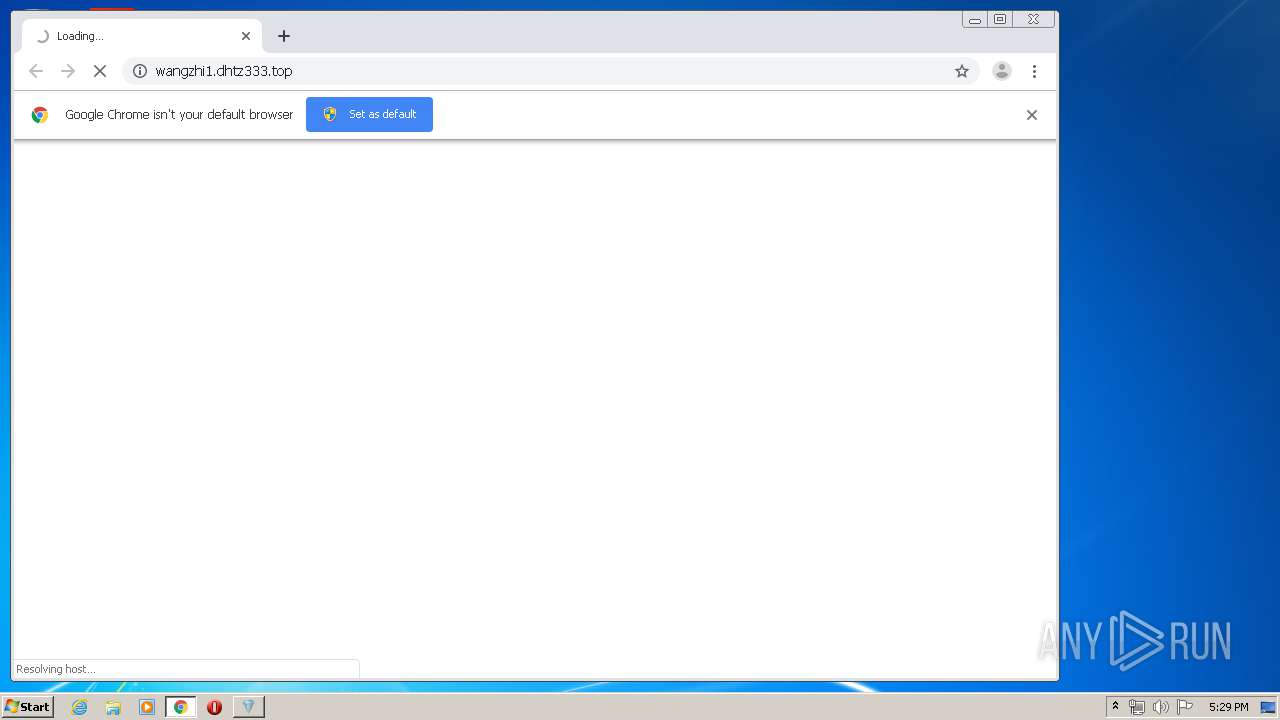
— | — | 152.32.215.234:8083 | du.testjj.com | MCNC | US | unknown |
572 | DvUpdate.exe | 152.32.215.234:8083 | du.testjj.com | MCNC | US | unknown |
3164 | chrome.exe | 216.239.34.117:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3164 | chrome.exe | 103.235.46.191:443 | hm.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | suspicious |
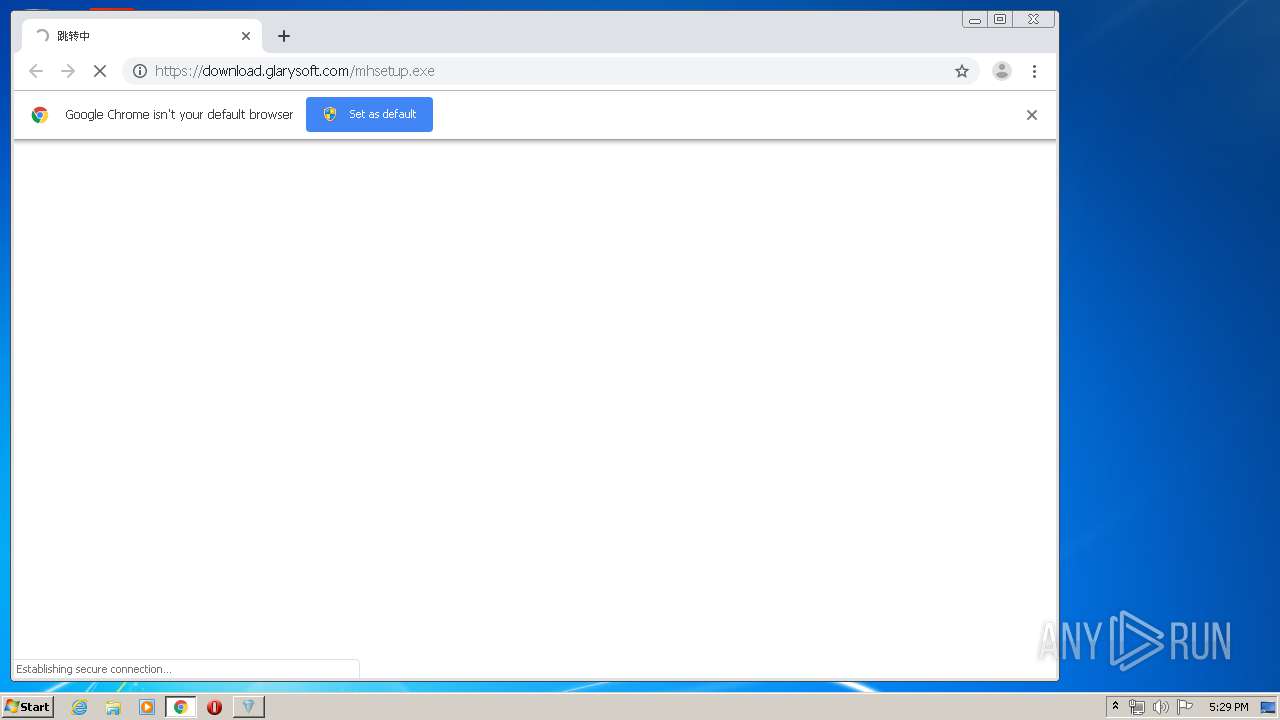
3164 | chrome.exe | 99.86.3.104:443 | download.glarysoft.com | AT&T Services, Inc. | US | malicious |
3164 | chrome.exe | 216.239.32.117:443 | www.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.baidu.com |
| whitelisted |
wappass.baidu.com |
| suspicious |
ocsp.globalsign.com |
| whitelisted |
crl.globalsign.net |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
du.testjj.com |
| malicious |
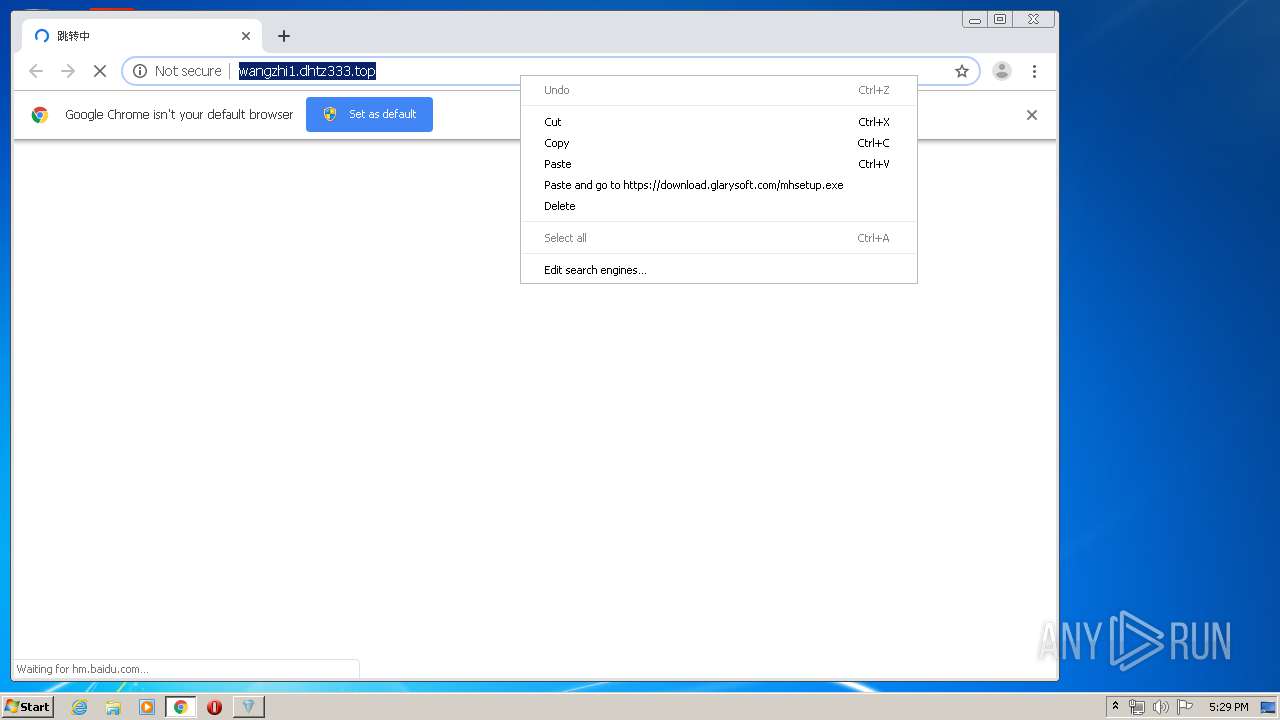
wangzhi1.dhtz333.top |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
hm.baidu.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3164 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2060 | sendinfo.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
2060 | sendinfo.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
_¼¤»î¹¤¾ß8.exe | Main in... |
_¼¤»î¹¤¾ß8.exe | install ... |
¼¤»î¹¤¾ß8.exe | Service :: Run |
¼¤»î¹¤¾ß8.exe | Main in... |
¼¤»î¹¤¾ß8.exe | GetInfo :: CollectAndReport |
¼¤»î¹¤¾ß8.exe | Service :: ServiceWorkerThread |
¼¤»î¹¤¾ß8.exe | Service :: Main |
DvLayout.exe | C:\Users\admin\AppData\local\Mlxg_km\KMDF_LOOK.sys |
DvLayout.exe | JXOBFOPI.sys |
DvLayout.exe | C:\Users\admin\AppData\local\Mlxg_km |