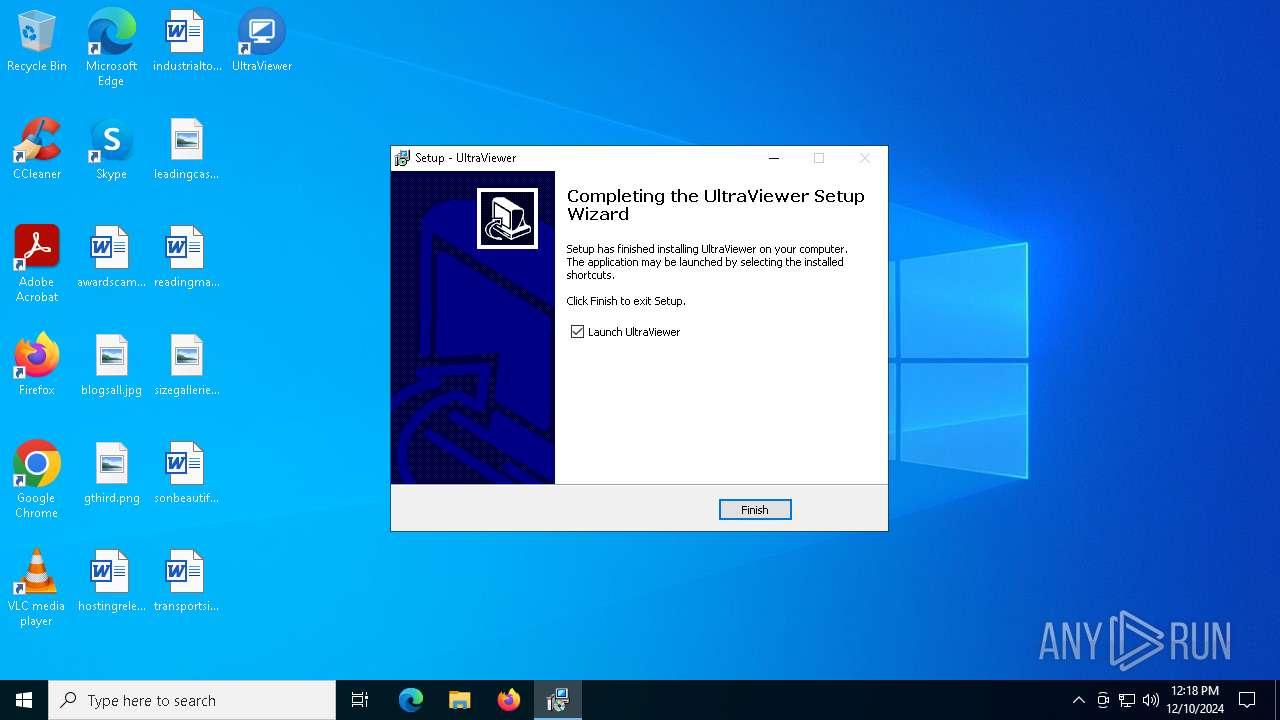
| File name: | UltraViewer_setup_6.6.110_en.exe |
| Full analysis: | https://app.any.run/tasks/5f55c7b6-5ff5-4cf7-8e44-5ce9924a3d34 |
| Verdict: | Malicious activity |
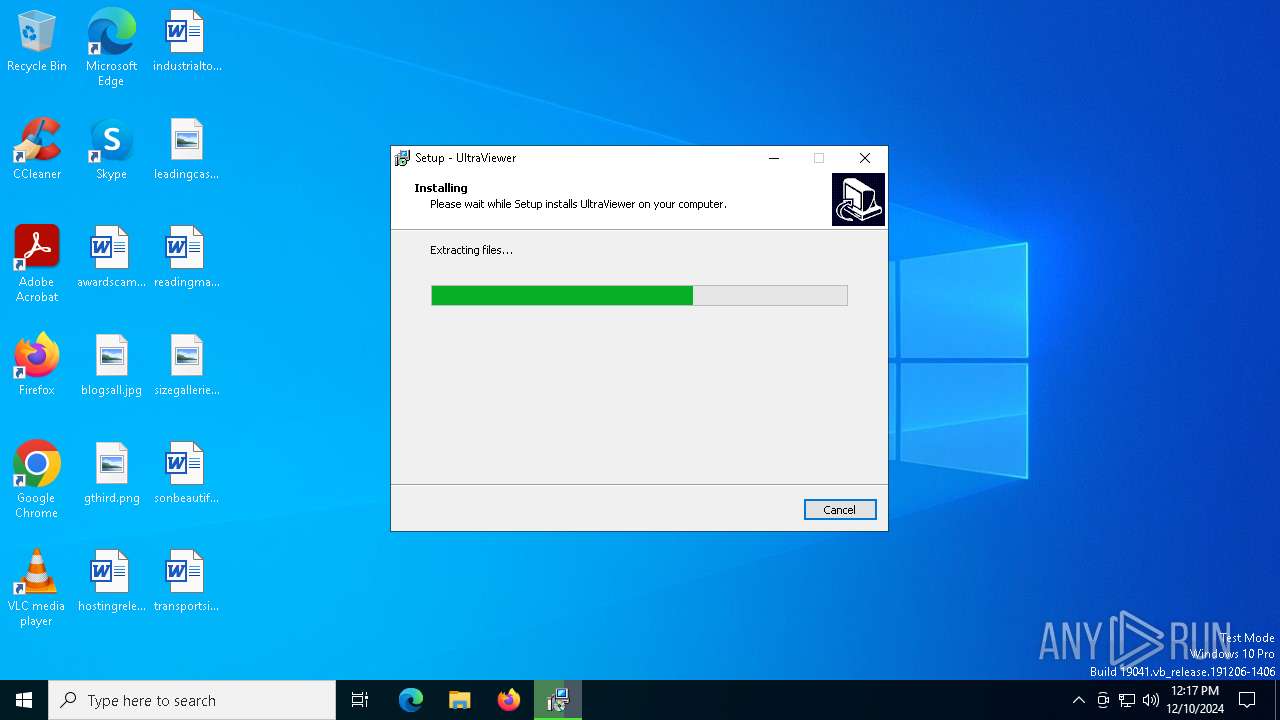
| Analysis date: | December 10, 2024, 12:17:02 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | C1E396984655DDFD2AB324E92045771D |
| SHA1: | C574637B50049FE391D2449FDFD79E6C1F76C1DC |
| SHA256: | F710BF1CE08B158FDF0278F0F4942C10E85D1CA329FCABB44C4F11233EAAD36B |
| SSDEEP: | 98304:IggAtDi7PImpRp7TCCI/Skb5FQTXN2MY0bqOsTiWgrKeCYotkk2qxcdDaJu/fsLx:C23YF8 |
MALICIOUS
Executing a file with an untrusted certificate
- UltraViewer_setup_6.6.110_en.exe (PID: 6176)
- UltraViewer_Desktop.exe (PID: 1016)
- UltraViewer_Desktop.exe (PID: 6240)
- UltraViewer_Service.exe (PID: 6004)
- UltraViewer_Desktop.exe (PID: 5684)
- UltraViewer_Desktop.exe (PID: 6628)
- UltraViewer_Desktop.exe (PID: 6892)
- UltraViewer_setup_6.6.110_en.exe (PID: 6520)
Starts NET.EXE for service management
- net.exe (PID: 440)
- UltraViewer_setup_6.6.110_en.tmp (PID: 6556)
- net.exe (PID: 396)
SUSPICIOUS
Reads the Windows owner or organization settings
- UltraViewer_setup_6.6.110_en.tmp (PID: 6556)
Executable content was dropped or overwritten
- UltraViewer_setup_6.6.110_en.exe (PID: 6520)
- UltraViewer_setup_6.6.110_en.tmp (PID: 6556)
- UltraViewer_setup_6.6.110_en.exe (PID: 6176)
Process drops legitimate windows executable
- UltraViewer_setup_6.6.110_en.tmp (PID: 6556)
Reads Internet Explorer settings
- UltraViewer_Desktop.exe (PID: 1016)
- UltraViewer_Desktop.exe (PID: 6628)
Reads security settings of Internet Explorer
- UltraViewer_Desktop.exe (PID: 1016)
- UltraViewer_Service.exe (PID: 6004)
- RegAsm.exe (PID: 2212)
- UltraViewer_Desktop.exe (PID: 6628)
- UltraViewer_setup_6.6.110_en.tmp (PID: 6288)
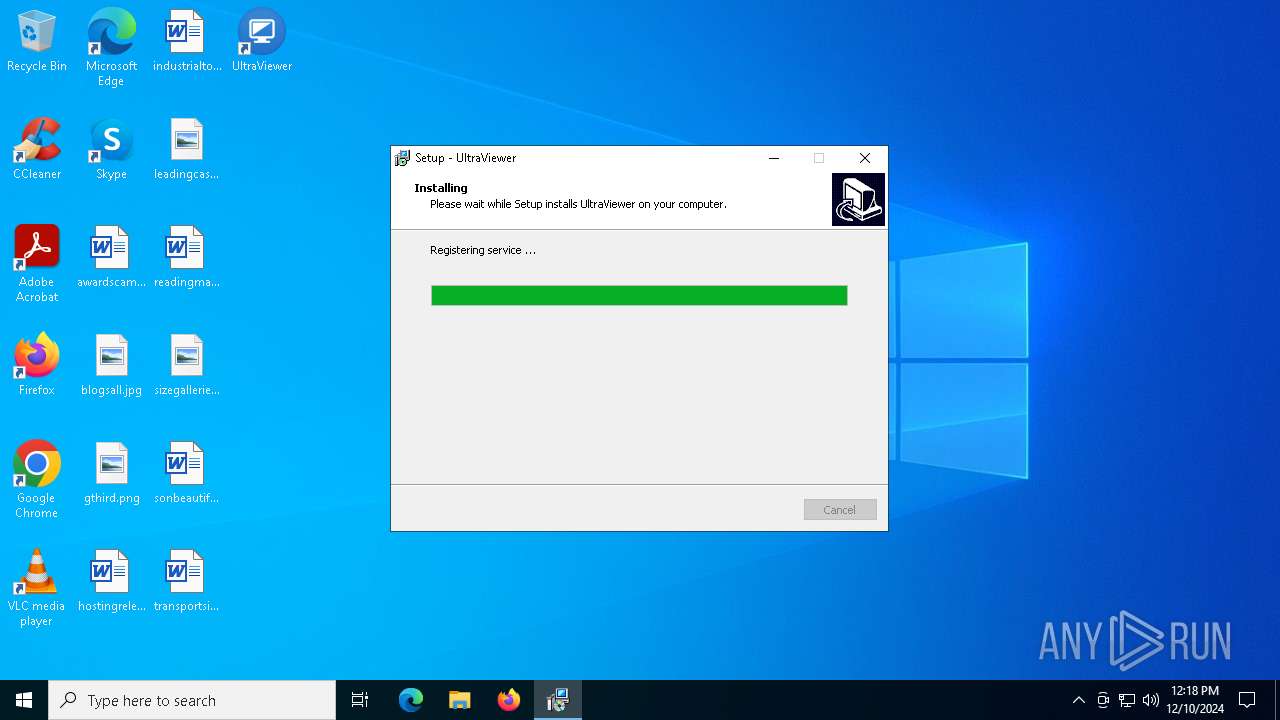
Executes as Windows Service
- UltraViewer_Service.exe (PID: 6004)
Uses TASKKILL.EXE to kill process
- UltraViewer_setup_6.6.110_en.tmp (PID: 6556)
Creates/Modifies COM task schedule object
- RegAsm.exe (PID: 2212)
- RegAsm.exe (PID: 6636)
Reads Microsoft Outlook installation path
- UltraViewer_Desktop.exe (PID: 6628)
Checks Windows Trust Settings
- uv_x64.exe (PID: 4684)
INFO
Process checks computer location settings
- UltraViewer_setup_6.6.110_en.tmp (PID: 6288)
Reads the computer name
- UltraViewer_setup_6.6.110_en.tmp (PID: 6556)
- UVUninstallHelper.exe (PID: 6500)
- RegAsm.exe (PID: 6636)
- UltraViewer_Desktop.exe (PID: 5684)
- RegAsm.exe (PID: 6652)
- RegAsm.exe (PID: 2212)
- RegAsm.exe (PID: 6740)
- uv_x64.exe (PID: 4684)
- UltraViewer_setup_6.6.110_en.tmp (PID: 6288)
Checks supported languages
- UltraViewer_setup_6.6.110_en.exe (PID: 6520)
- UVUninstallHelper.exe (PID: 6500)
- UltraViewer_setup_6.6.110_en.tmp (PID: 6556)
- UltraViewer_setup_6.6.110_en.exe (PID: 6176)
- RegAsm.exe (PID: 6636)
- RegAsm.exe (PID: 2212)
- UltraViewer_Service.exe (PID: 6004)
- RegAsm.exe (PID: 6740)
- UltraViewer_Desktop.exe (PID: 6628)
- RegAsm.exe (PID: 7004)
- uv_x64.exe (PID: 4684)
- RegAsm.exe (PID: 6652)
- UltraViewer_setup_6.6.110_en.tmp (PID: 6288)
Create files in a temporary directory
- UltraViewer_setup_6.6.110_en.exe (PID: 6520)
- UltraViewer_setup_6.6.110_en.exe (PID: 6176)
The sample compiled with english language support
- UltraViewer_setup_6.6.110_en.tmp (PID: 6556)
Reads the machine GUID from the registry
- UltraViewer_Desktop.exe (PID: 1016)
- UltraViewer_Service.exe (PID: 6004)
- RegAsm.exe (PID: 2212)
- UltraViewer_Desktop.exe (PID: 6892)
- UltraViewer_Desktop.exe (PID: 6628)
- uv_x64.exe (PID: 4684)
Checks proxy server information
- UltraViewer_Desktop.exe (PID: 1016)
- UltraViewer_Desktop.exe (PID: 6628)
Creates files in the program directory
- UltraViewer_setup_6.6.110_en.tmp (PID: 6556)
Reads the software policy settings
- uv_x64.exe (PID: 4684)
- UltraViewer_Service.exe (PID: 6004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 14:39:04+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | DucFabulous |
| FileDescription: | UltraViewer Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | UltraViewer |
| ProductVersion: | 6.6.110 |
Total processes
558
Monitored processes
429
Malicious processes
9
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8 | "taskkill.exe" /f /im "UltraViewer_Service.exe" | C:\Windows\SysWOW64\taskkill.exe | — | UltraViewer_setup_6.6.110_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | "taskkill.exe" /f /im "UltraViewer_Service.exe" | C:\Windows\SysWOW64\taskkill.exe | — | UltraViewer_setup_6.6.110_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 244 | "taskkill.exe" /f /im "UltraViewer_Service.exe" | C:\Windows\SysWOW64\taskkill.exe | — | UltraViewer_setup_6.6.110_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 308 | "taskkill.exe" /f /im "UltraViewer_Desktop.exe" | C:\Windows\SysWOW64\taskkill.exe | — | UltraViewer_setup_6.6.110_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 396 | "net" stop UltraViewService | C:\Windows\SysWOW64\net.exe | — | UltraViewer_setup_6.6.110_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 396 | "taskkill.exe" /f /im "UltraViewer_Service.exe" | C:\Windows\SysWOW64\taskkill.exe | — | UltraViewer_setup_6.6.110_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 432 | "taskkill.exe" /f /im "UltraViewer_Desktop.exe" | C:\Windows\SysWOW64\taskkill.exe | — | UltraViewer_setup_6.6.110_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
33 359
Read events
31 837
Write events
1 522
Delete events
0
Modification events
| (PID) Process: | (6636) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{315D07B8-9F8F-3885-AB17-1C3D460CEE4E}\InprocServer32\1.0.0.0 |
| Operation: | write | Name: | Class |
Value: RemoteControl.ExtendTreeView | |||
| (PID) Process: | (6636) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{315D07B8-9F8F-3885-AB17-1C3D460CEE4E}\InprocServer32\1.0.0.0 |
| Operation: | write | Name: | Assembly |
Value: RemoteControl, Version=1.0.0.0, Culture=neutral, PublicKeyToken=null | |||
| (PID) Process: | (6636) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{315D07B8-9F8F-3885-AB17-1C3D460CEE4E}\InprocServer32\1.0.0.0 |
| Operation: | write | Name: | RuntimeVersion |
Value: v4.0.30319 | |||
| (PID) Process: | (6636) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{80DF76B9-AE4F-4405-8F98-023627E6724C}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (6636) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{80DF76B9-AE4F-4405-8F98-023627E6724C}\InprocServer32 |
| Operation: | write | Name: | Class |
Value: RemoteControl.VAutoUpdater | |||
| (PID) Process: | (6636) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{80DF76B9-AE4F-4405-8F98-023627E6724C}\InprocServer32 |
| Operation: | write | Name: | Assembly |
Value: RemoteControl, Version=1.0.0.0, Culture=neutral, PublicKeyToken=null | |||
| (PID) Process: | (6636) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{80DF76B9-AE4F-4405-8F98-023627E6724C}\InprocServer32 |
| Operation: | write | Name: | RuntimeVersion |
Value: v4.0.30319 | |||
| (PID) Process: | (6636) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{80DF76B9-AE4F-4405-8F98-023627E6724C}\InprocServer32\1.0.0.0 |
| Operation: | write | Name: | Class |
Value: RemoteControl.VAutoUpdater | |||
| (PID) Process: | (6636) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{80DF76B9-AE4F-4405-8F98-023627E6724C}\InprocServer32\1.0.0.0 |
| Operation: | write | Name: | Assembly |
Value: RemoteControl, Version=1.0.0.0, Culture=neutral, PublicKeyToken=null | |||
| (PID) Process: | (6636) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{80DF76B9-AE4F-4405-8F98-023627E6724C}\InprocServer32\1.0.0.0 |
| Operation: | write | Name: | RuntimeVersion |
Value: v4.0.30319 | |||
Executable files
39
Suspicious files
19
Text files
168
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6520 | UltraViewer_setup_6.6.110_en.exe | C:\Users\admin\AppData\Local\Temp\is-48TKU.tmp\UltraViewer_setup_6.6.110_en.tmp | executable | |
MD5:E845838D99D29C4BBA4AD35EE996DEA3 | SHA256:B727418174AD4F929AD9206E4DF51865DEF55C0D2874BDA487CBAE6F2946938D | |||
| 6556 | UltraViewer_setup_6.6.110_en.tmp | C:\Users\admin\AppData\Local\Temp\is-09FS3.tmp\isxdl.dll | executable | |
MD5:48AD1A1C893CE7BF456277A0A085ED01 | SHA256:B0CC4697B2FD1B4163FDDCA2050FC62A9E7D221864F1BD11E739144C90B685B3 | |||
| 6556 | UltraViewer_setup_6.6.110_en.tmp | C:\Users\admin\AppData\Local\Temp\is-09FS3.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 6556 | UltraViewer_setup_6.6.110_en.tmp | C:\Users\admin\AppData\Local\Temp\is-09FS3.tmp\idp.dll | executable | |
MD5:55C310C0319260D798757557AB3BF636 | SHA256:54E7E0AD32A22B775131A6288F083ED3286A9A436941377FC20F85DD9AD983ED | |||
| 6556 | UltraViewer_setup_6.6.110_en.tmp | C:\Users\admin\AppData\Local\Temp\is-09FS3.tmp\UVUninstallHelper.exe | executable | |
MD5:ECECB301656F5F8C6A46A8ABF8D928FE | SHA256:801BBE7A174CA09BB029AEDF54C3073D96C033FA01DCD68F4240983D2AD7CB6B | |||
| 6556 | UltraViewer_setup_6.6.110_en.tmp | C:\Program Files (x86)\UltraViewer\emotion.fan | text | |
MD5:5E28EF7C6FB2D23E9DF42B3355BDCEB7 | SHA256:F899D1C4F1B55BDFA9F4237CFC593BF8AEDE52AF4D5EB3CC2AAEF8B77CF5C519 | |||
| 6556 | UltraViewer_setup_6.6.110_en.tmp | C:\Program Files (x86)\UltraViewer\is-M52V3.tmp | text | |
MD5:5E28EF7C6FB2D23E9DF42B3355BDCEB7 | SHA256:F899D1C4F1B55BDFA9F4237CFC593BF8AEDE52AF4D5EB3CC2AAEF8B77CF5C519 | |||
| 6556 | UltraViewer_setup_6.6.110_en.tmp | C:\Program Files (x86)\UltraViewer\is-A83V4.tmp | text | |
MD5:1545270D0FF548C77A57D008223DB83E | SHA256:3E40C331E56BC35DF9C6341E05FAA41165F4E25718914248886295B7553A734C | |||
| 6556 | UltraViewer_setup_6.6.110_en.tmp | C:\Program Files (x86)\UltraViewer\is-8REL3.tmp | executable | |
MD5:00DC215CEE6BE49802295AD6802DA661 | SHA256:78750E7BD53ED088D8365FC2E69B74883A813B0EA0D461873AD61FD8059DBD31 | |||
| 6556 | UltraViewer_setup_6.6.110_en.tmp | C:\Program Files (x86)\UltraViewer\is-554IC.tmp | executable | |
MD5:5343A19C618BC515CEB1695586C6C137 | SHA256:2246B4FEAE199408EA66D4A90C1589026F4A5800CE5A28E583B94506A8A73DCE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
36
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1356 | svchost.exe | GET | 200 | 2.16.164.99:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.99:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1356 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6248 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7096 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7096 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4684 | uv_x64.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEB2iSDBvmyYY0ILgln0z02o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.11.168.232:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1356 | svchost.exe | 2.16.164.99:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.99:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1356 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.177:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
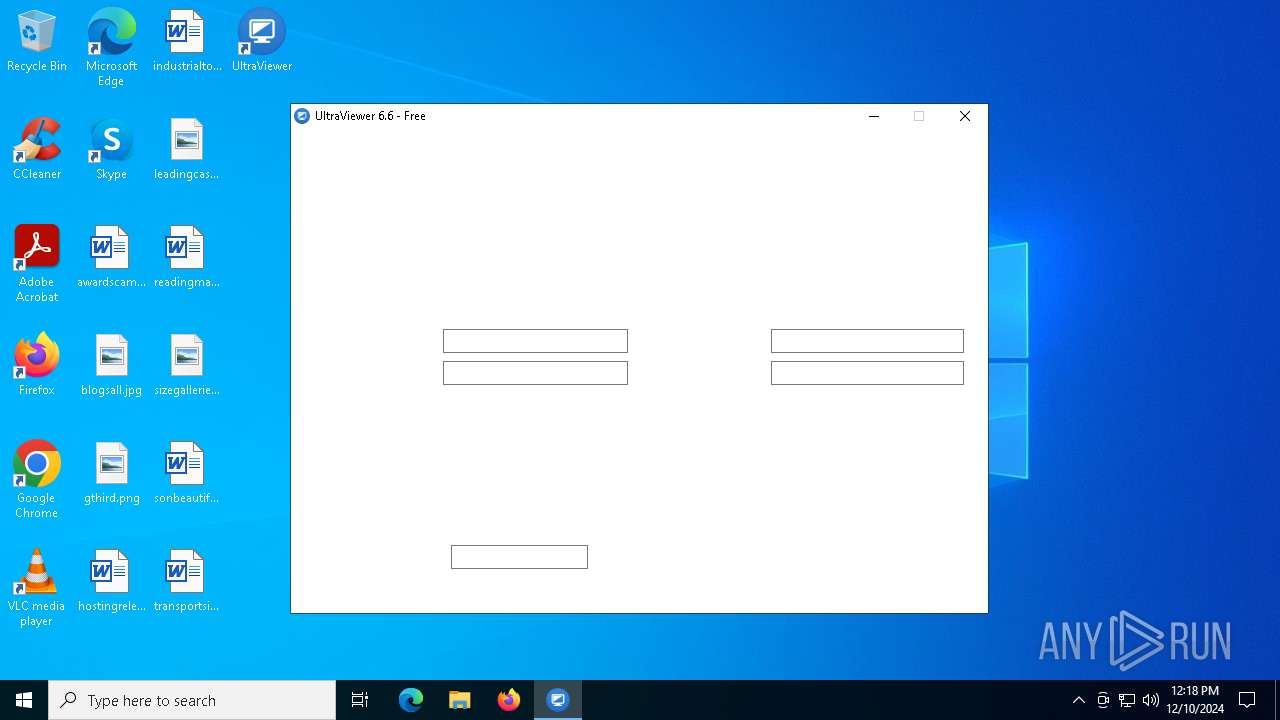
UltraViewer_Desktop.exe | uvh - 6628 - 131984
|