| File name: | kolhoz — копия.exe |
| Full analysis: | https://app.any.run/tasks/5ec2f7b2-c650-4b03-9717-e352c2df94fa |
| Verdict: | Malicious activity |
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | June 18, 2025, 07:38:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | DD1BF9C2AE58B89EFE0818121701AB54 |
| SHA1: | A60D6D6E1745220B143BBFB6B214594CBD1CE8D8 |
| SHA256: | F70C8DFD406389CF8CFD27D3A9C9F0EBD25EB0CE39529CB3AD7A3206783786F4 |
| SSDEEP: | 3072:umhXodguLLDzaJ/A7z7zT73ShHECB4BSLbBk7a:Wfza6z7zyb7v+a |
MALICIOUS
Known privilege escalation attack
- dllhost.exe (PID: 188)
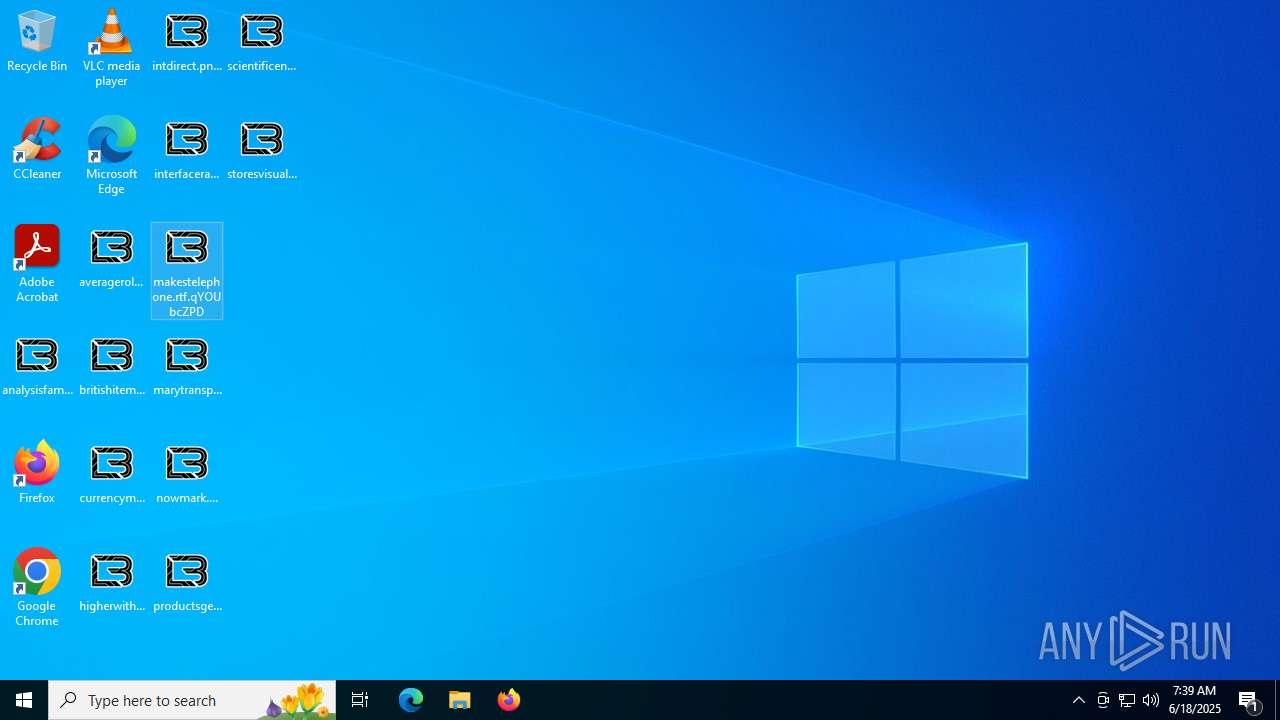
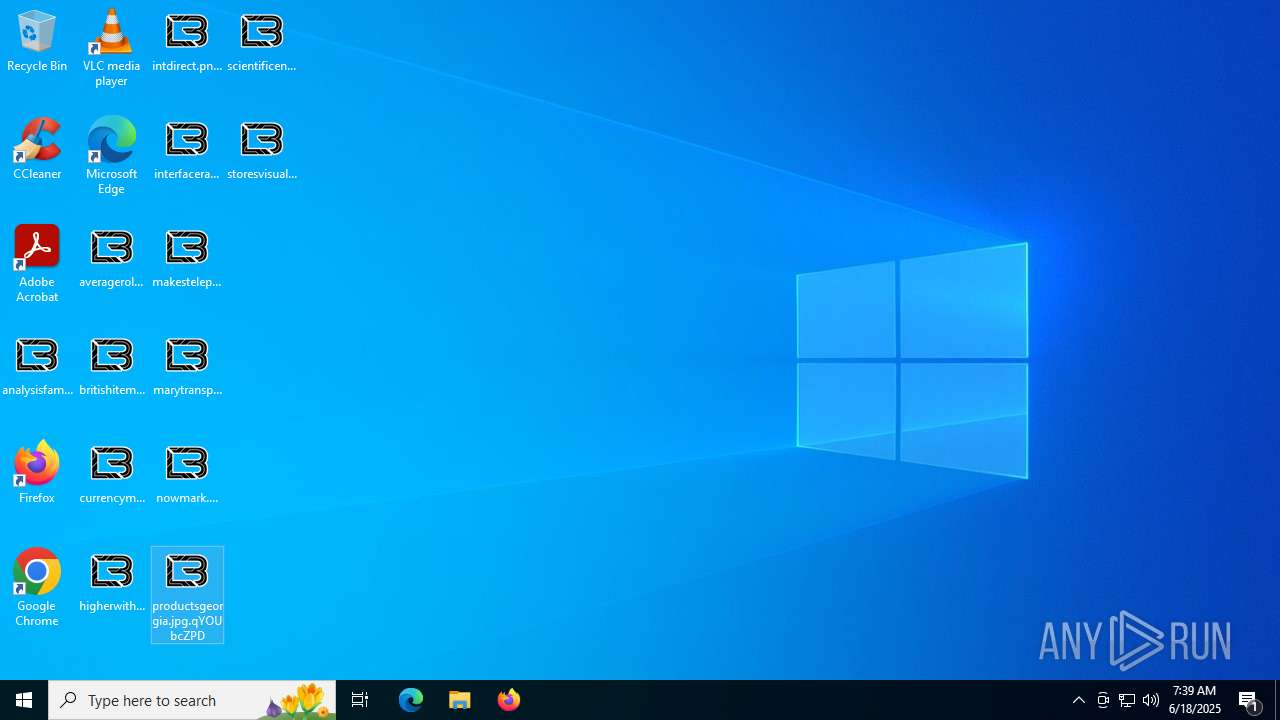
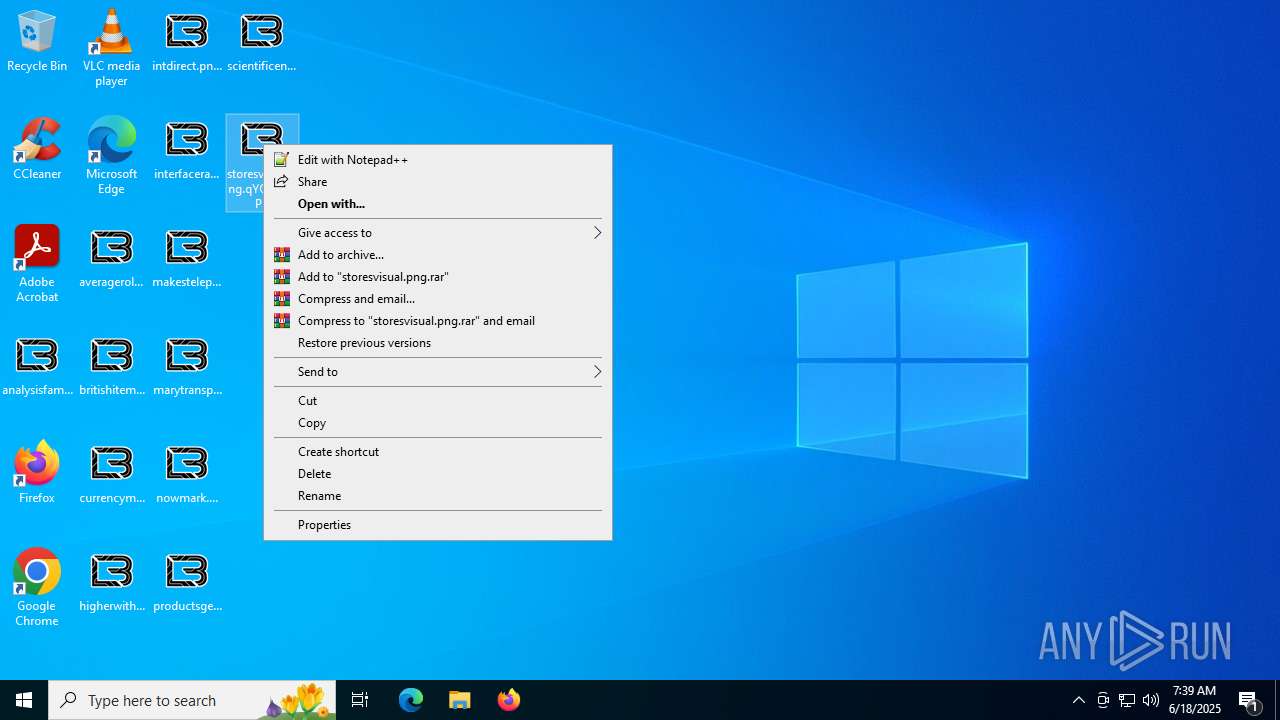
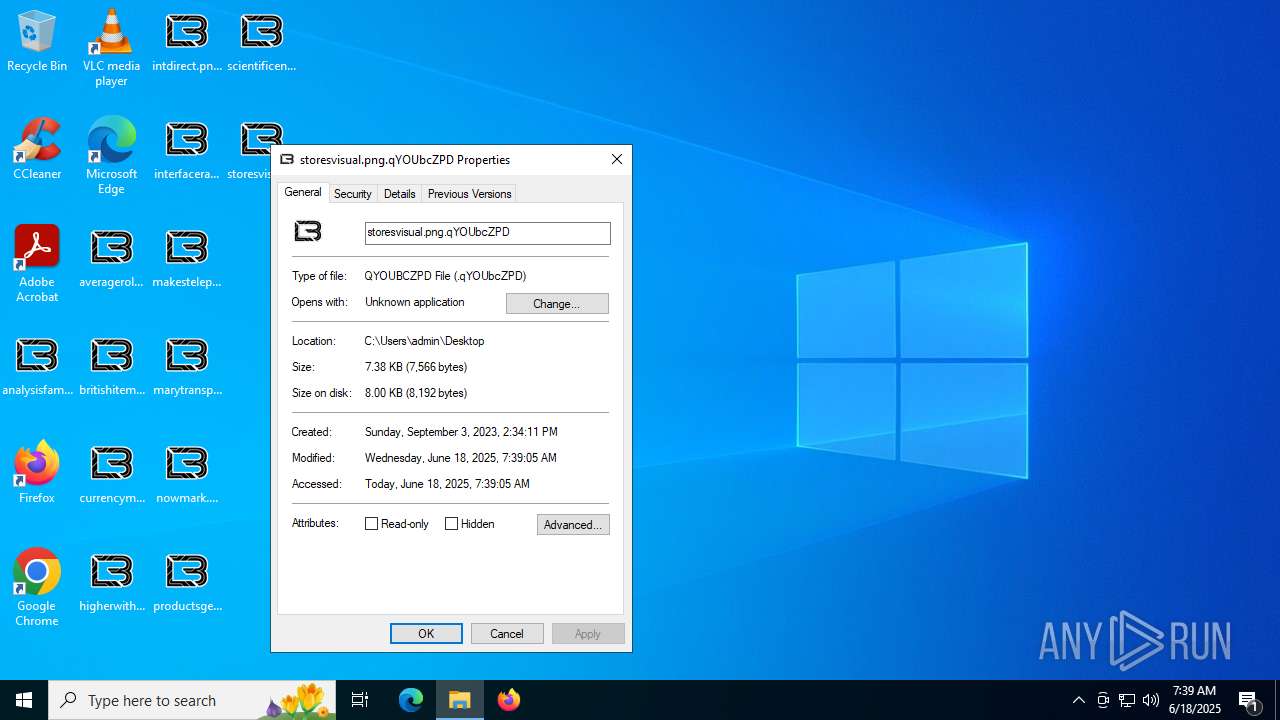
Renames files like ransomware
- kolhoz — копия.exe (PID: 5424)
[YARA] LockBit is detected
- kolhoz — копия.exe (PID: 5424)
SUSPICIOUS
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 2148)
There is functionality for taking screenshot (YARA)
- kolhoz — копия.exe (PID: 5424)
Write to the desktop.ini file (may be used to cloak folders)
- kolhoz — копия.exe (PID: 5424)
Executable content was dropped or overwritten
- kolhoz — копия.exe (PID: 5424)
INFO
Reads the computer name
- kolhoz — копия.exe (PID: 3780)
- kolhoz — копия.exe (PID: 5424)
- ShellExperienceHost.exe (PID: 2148)
- SearchApp.exe (PID: 3608)
Checks supported languages
- kolhoz — копия.exe (PID: 3780)
- kolhoz — копия.exe (PID: 5424)
- ShellExperienceHost.exe (PID: 2148)
- SearchApp.exe (PID: 3608)
Reads the machine GUID from the registry
- kolhoz — копия.exe (PID: 3780)
- SearchApp.exe (PID: 3608)
Creates files in the program directory
- kolhoz — копия.exe (PID: 5424)
Process checks computer location settings
- SearchApp.exe (PID: 3608)
Checks proxy server information
- SearchApp.exe (PID: 3608)
Reads the software policy settings
- SearchApp.exe (PID: 3608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:09:13 23:30:57+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.12 |
| CodeSize: | 99328 |
| InitializedDataSize: | 50688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1946f |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
141
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3608 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3780 | "C:\Users\admin\AppData\Roaming\kolhoz — копия.exe" | C:\Users\admin\AppData\Roaming\kolhoz — копия.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5424 | "C:\Users\admin\AppData\Roaming\kolhoz — копия.exe" | C:\Users\admin\AppData\Roaming\kolhoz — копия.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
8 485
Read events
8 397
Write events
87
Delete events
1
Modification events
| (PID) Process: | (188) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (188) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (188) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (188) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (188) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (5424) kolhoz — копия.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 13 | |||
| (PID) Process: | (2148) ShellExperienceHost.exe | Key: | \REGISTRY\A\{1bb1a326-9624-1467-354e-d219429ef4d6}\LocalState |
| Operation: | write | Name: | PeekBadges |
Value: 5B005D000000D4766A1124E0DB01 | |||
| (PID) Process: | (3608) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | SafeSearchMode |
Value: 1 | |||
| (PID) Process: | (3608) SearchApp.exe | Key: | \REGISTRY\A\{6ac31378-4ee7-a1f9-a219-a6400eb0b9f3}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_USEREMAIL |
Value: 00005A41D03024E0DB01 | |||
| (PID) Process: | (3608) SearchApp.exe | Key: | \REGISTRY\A\{6ac31378-4ee7-a1f9-a219-a6400eb0b9f3}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_ACCOUNTTYPETEXT |
Value: 00005A41D03024E0DB01 | |||
Executable files
14
Suspicious files
1 529
Text files
973
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5424 | kolhoz — копия.exe | C:\$Recycle.Bin\S-1-5-18\desktop.ini | binary | |
MD5:5C3941DFA950A7B94E022FC616C225A1 | SHA256:57536F00CE463E1EA73B23EFEBFD3B6D56B3A3DD5C4F7B9A18F394A0953E34A6 | |||
| 5424 | kolhoz — копия.exe | C:\ProgramData\qYOUbcZPD.ico | image | |
MD5:88D9337C4C9CFE2D9AFF8A2C718EC76B | SHA256:95E059EF72686460884B9AEA5C292C22917F75D56FE737D43BE440F82034F438 | |||
| 5424 | kolhoz — копия.exe | C:\$Recycle.Bin\S-1-5-18\AAAAAAAAAAA | binary | |
MD5:5C3941DFA950A7B94E022FC616C225A1 | SHA256:57536F00CE463E1EA73B23EFEBFD3B6D56B3A3DD5C4F7B9A18F394A0953E34A6 | |||
| 5424 | kolhoz — копия.exe | C:\$Recycle.Bin\S-1-5-18\JJJJJJJJJJJ | binary | |
MD5:5C3941DFA950A7B94E022FC616C225A1 | SHA256:57536F00CE463E1EA73B23EFEBFD3B6D56B3A3DD5C4F7B9A18F394A0953E34A6 | |||
| 5424 | kolhoz — копия.exe | C:\$Recycle.Bin\S-1-5-18\BBBBBBBBBBB | binary | |
MD5:5C3941DFA950A7B94E022FC616C225A1 | SHA256:57536F00CE463E1EA73B23EFEBFD3B6D56B3A3DD5C4F7B9A18F394A0953E34A6 | |||
| 5424 | kolhoz — копия.exe | C:\$Recycle.Bin\S-1-5-18\HHHHHHHHHHH | binary | |
MD5:5C3941DFA950A7B94E022FC616C225A1 | SHA256:57536F00CE463E1EA73B23EFEBFD3B6D56B3A3DD5C4F7B9A18F394A0953E34A6 | |||
| 5424 | kolhoz — копия.exe | C:\$Recycle.Bin\S-1-5-18\KKKKKKKKKKK | binary | |
MD5:5C3941DFA950A7B94E022FC616C225A1 | SHA256:57536F00CE463E1EA73B23EFEBFD3B6D56B3A3DD5C4F7B9A18F394A0953E34A6 | |||
| 5424 | kolhoz — копия.exe | C:\$Recycle.Bin\S-1-5-18\IIIIIIIIIII | binary | |
MD5:5C3941DFA950A7B94E022FC616C225A1 | SHA256:57536F00CE463E1EA73B23EFEBFD3B6D56B3A3DD5C4F7B9A18F394A0953E34A6 | |||
| 5424 | kolhoz — копия.exe | C:\$Recycle.Bin\S-1-5-18\LLLLLLLLLLL | binary | |
MD5:5C3941DFA950A7B94E022FC616C225A1 | SHA256:57536F00CE463E1EA73B23EFEBFD3B6D56B3A3DD5C4F7B9A18F394A0953E34A6 | |||
| 5424 | kolhoz — копия.exe | C:\$Recycle.Bin\S-1-5-18\MMMMMMMMMMM | binary | |
MD5:5C3941DFA950A7B94E022FC616C225A1 | SHA256:57536F00CE463E1EA73B23EFEBFD3B6D56B3A3DD5C4F7B9A18F394A0953E34A6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
30
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
724 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
724 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6320 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3608 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3108 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
724 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
724 | SIHClient.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |