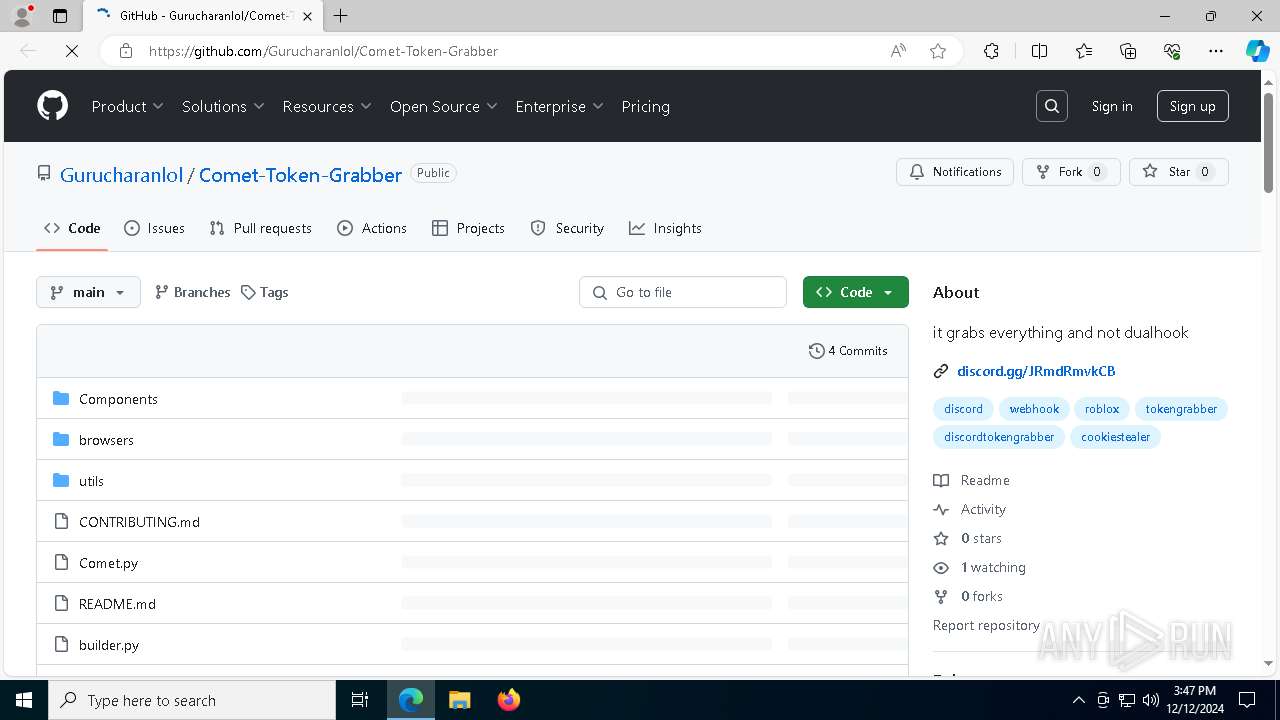
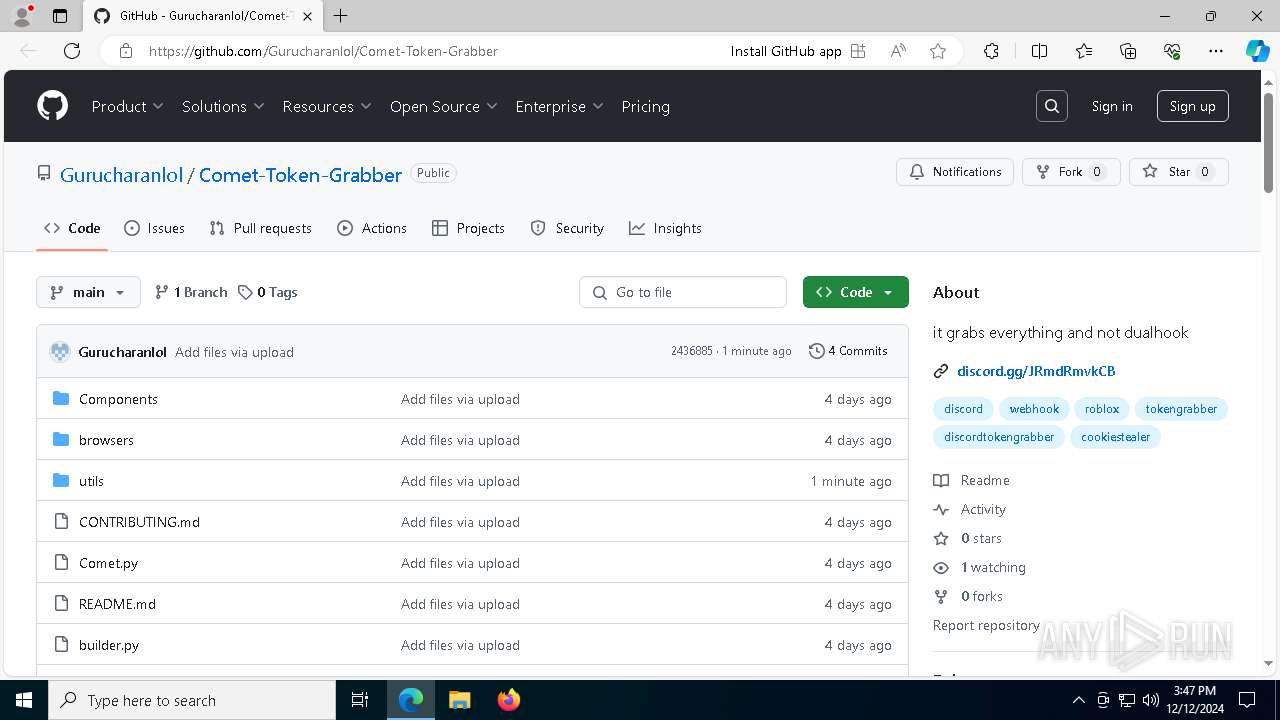
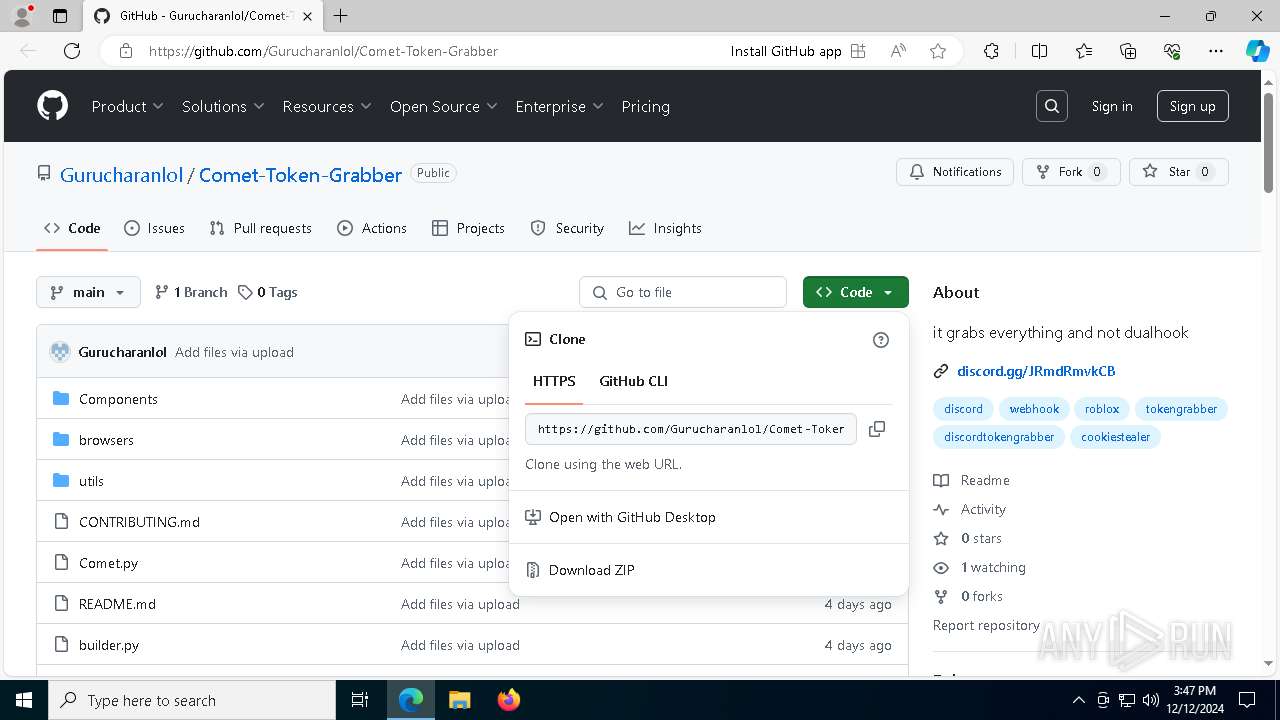
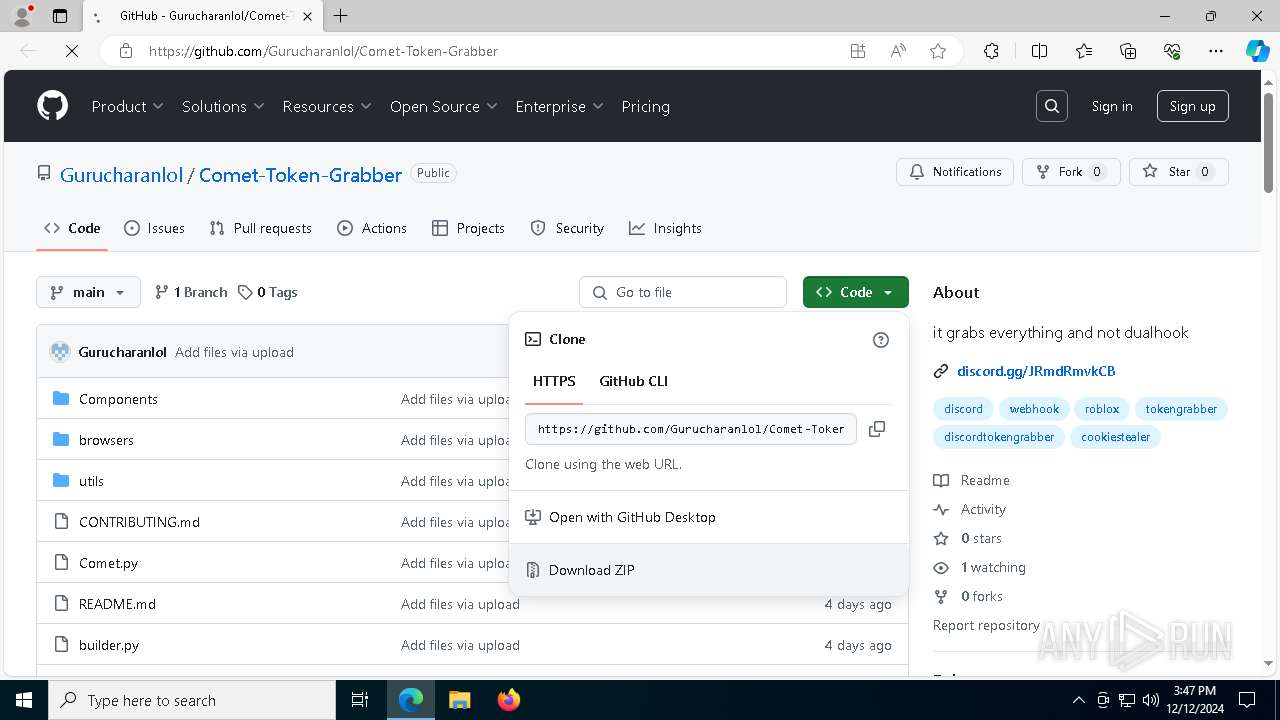
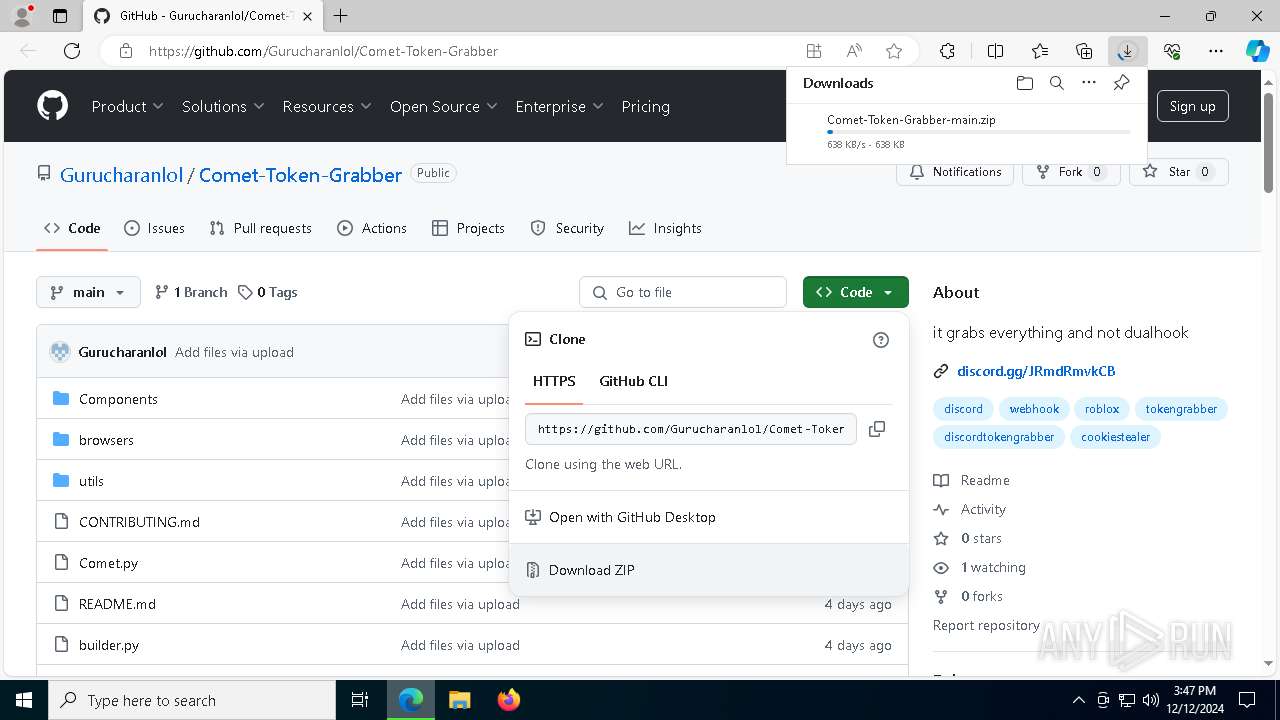
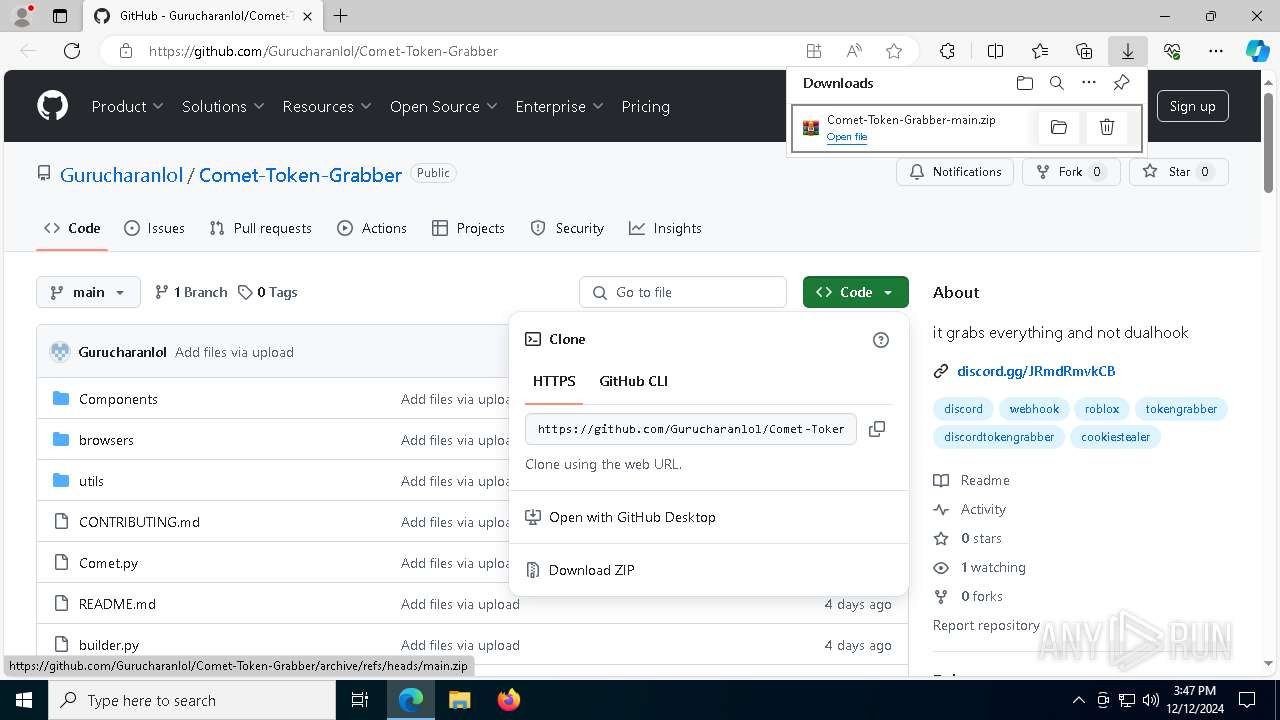
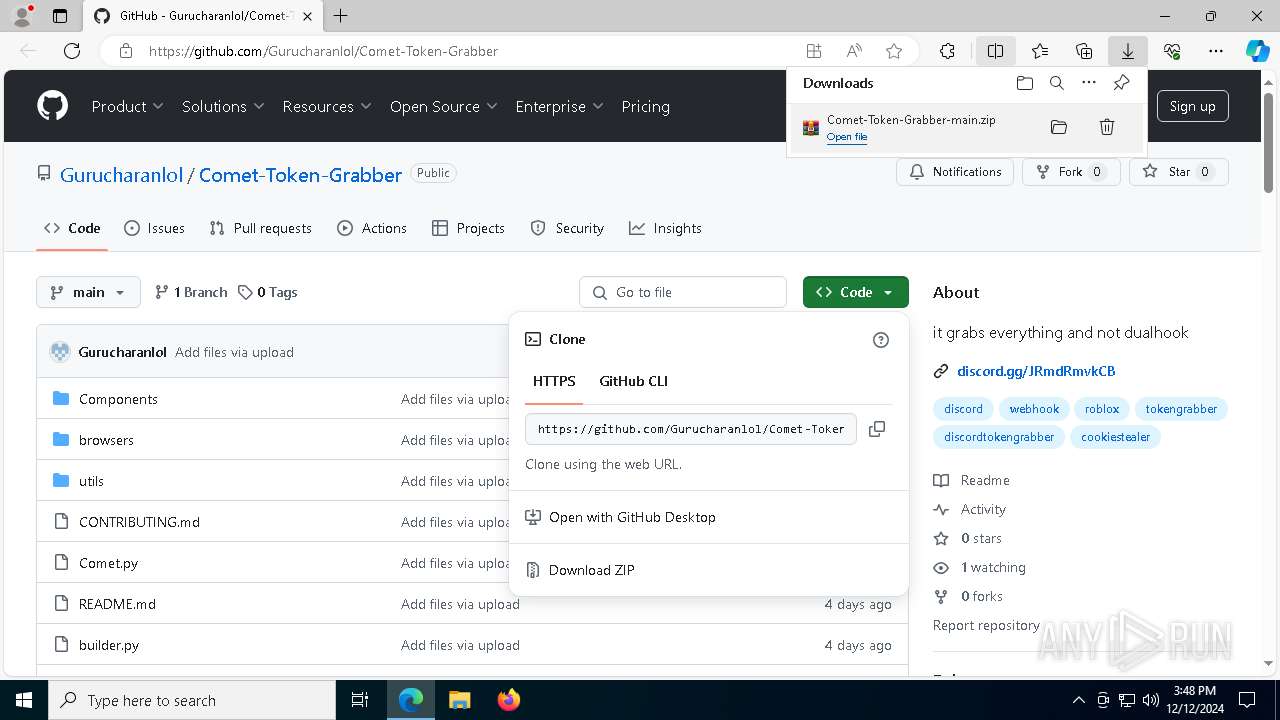
| URL: | https://github.com/Gurucharanlol/Comet-Token-Grabber |
| Full analysis: | https://app.any.run/tasks/b09a050e-c467-436d-85af-2343fcf57c87 |
| Verdict: | Malicious activity |
| Analysis date: | December 12, 2024, 15:47:33 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 39BE0D060360B8CC018B8494EDEC5600 |
| SHA1: | 5B29A8FAAF3278D8E4AF90F176A4CB1CEBD946BB |
| SHA256: | F6FDBD5924B0D0841C895667EC3EDDCB6D538FAE346761AC2A805430E1B9ADC6 |
| SSDEEP: | 3:N8tEdEvE9KJKVIxKOu/Enyn:2uepJqIxwMnyn |
MALICIOUS
Bypass User Account Control (fodhelper)
- fodhelper.exe (PID: 4388)
- fodhelper.exe (PID: 5400)
- fodhelper.exe (PID: 7832)
Changes the autorun value in the registry
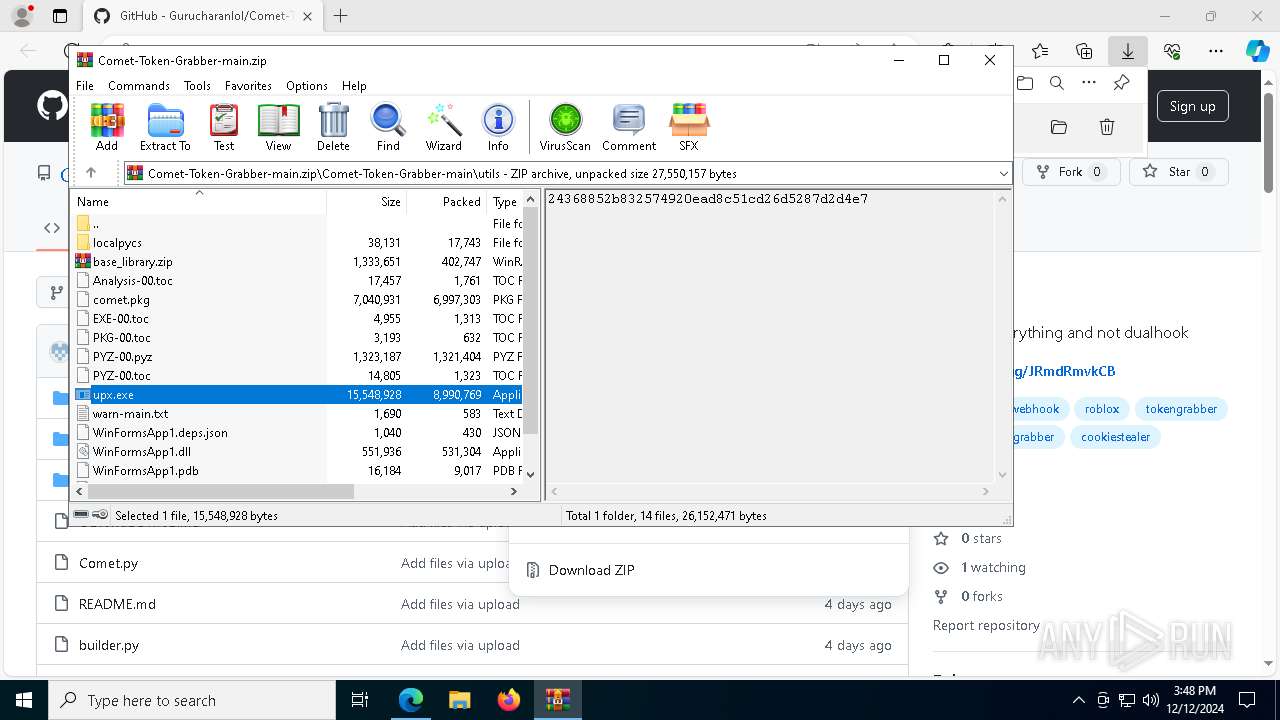
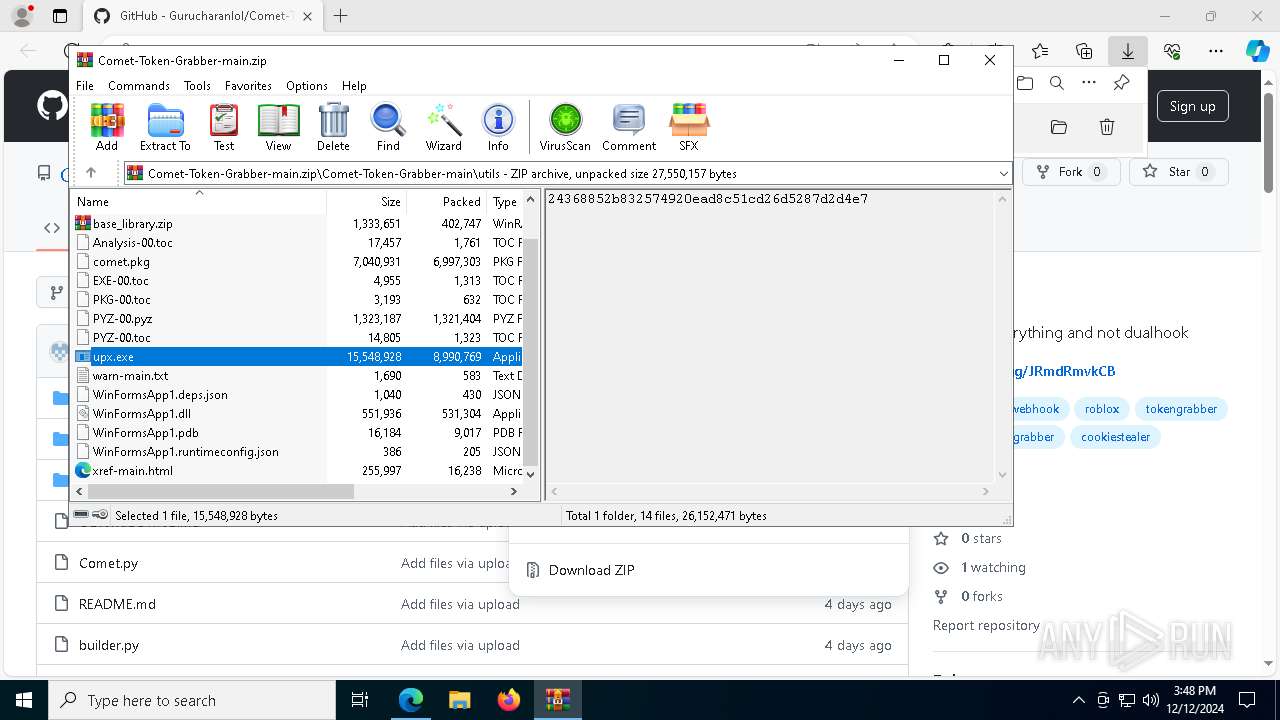
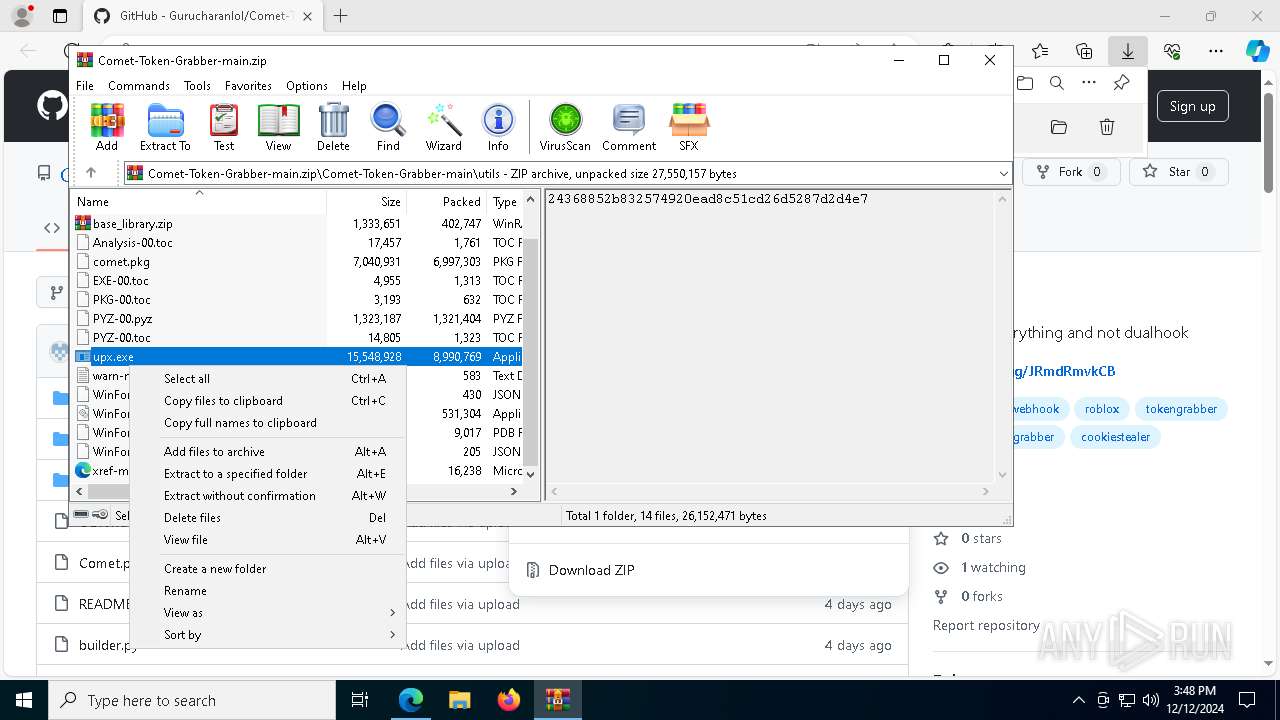
- upx.exe (PID: 7352)
SUSPICIOUS
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 3208)
- upx.exe (PID: 2728)
- upx.exe (PID: 7996)
- upx.exe (PID: 7540)
Uses ATTRIB.EXE to modify file attributes
- upx.exe (PID: 396)
- upx.exe (PID: 5488)
- upx.exe (PID: 7352)
Checks for external IP
- svchost.exe (PID: 2192)
- upx.exe (PID: 396)
- upx.exe (PID: 5488)
- upx.exe (PID: 7352)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 4976)
- WMIC.exe (PID: 3172)
- WMIC.exe (PID: 6536)
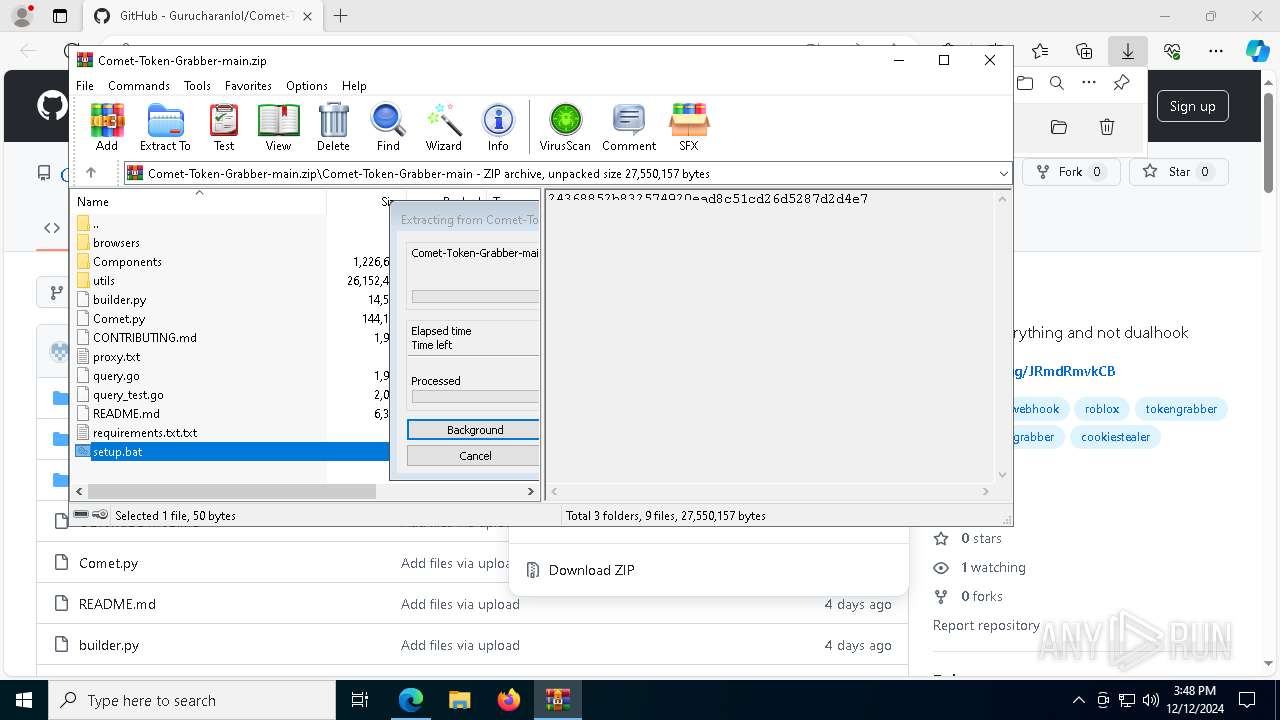
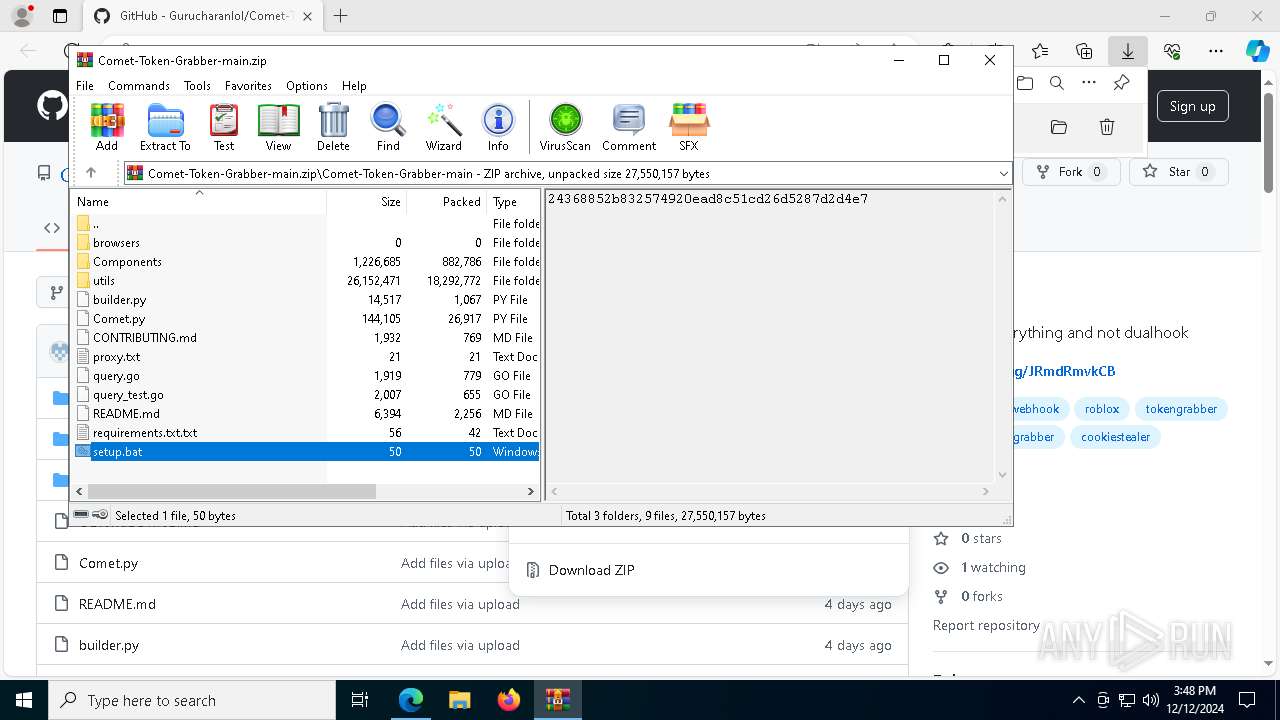
Executing commands from a ".bat" file
- WinRAR.exe (PID: 3208)
Creates or modifies Windows services
- upx.exe (PID: 5488)
Executable content was dropped or overwritten
- upx.exe (PID: 396)
- upx.exe (PID: 5488)
- upx.exe (PID: 7352)
Uses WMIC.EXE to obtain Windows Installer data
- upx.exe (PID: 396)
- upx.exe (PID: 5488)
- upx.exe (PID: 7352)
INFO
Application launched itself
- msedge.exe (PID: 6372)
Reads Environment values
- identity_helper.exe (PID: 7544)
The sample compiled with english language support
- msedge.exe (PID: 6372)
- msedge.exe (PID: 6764)
- WinRAR.exe (PID: 3208)
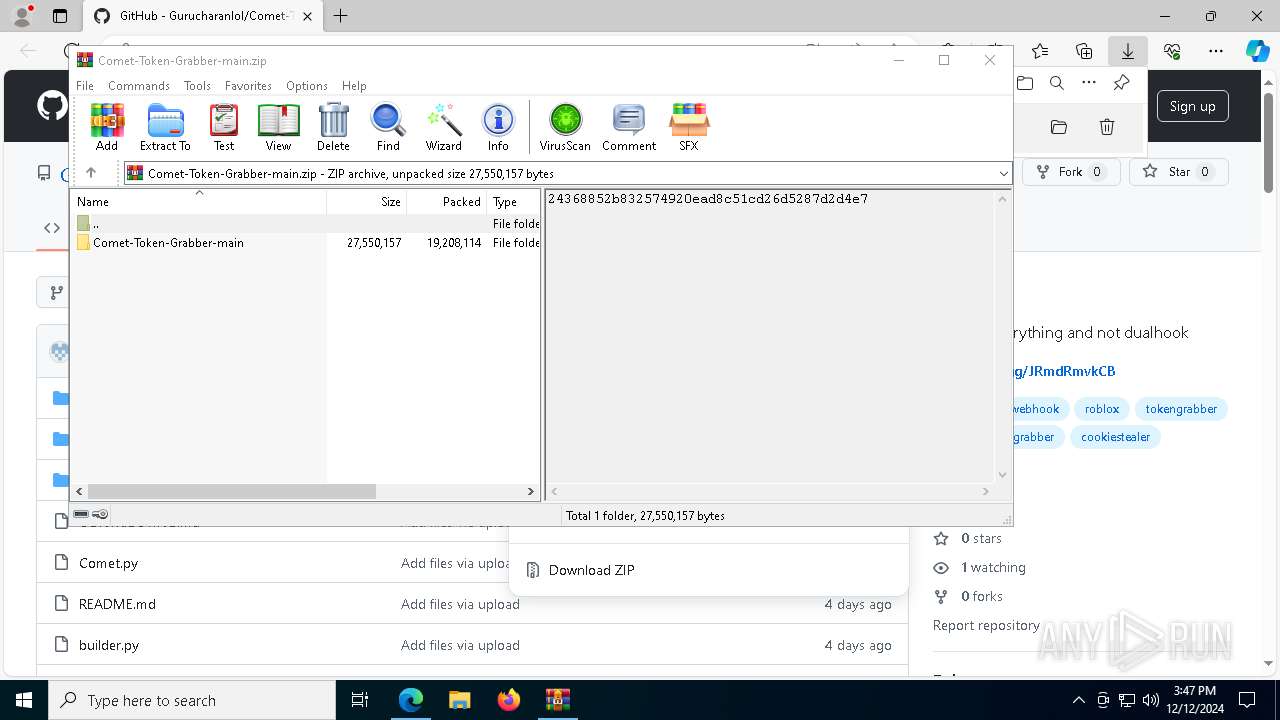
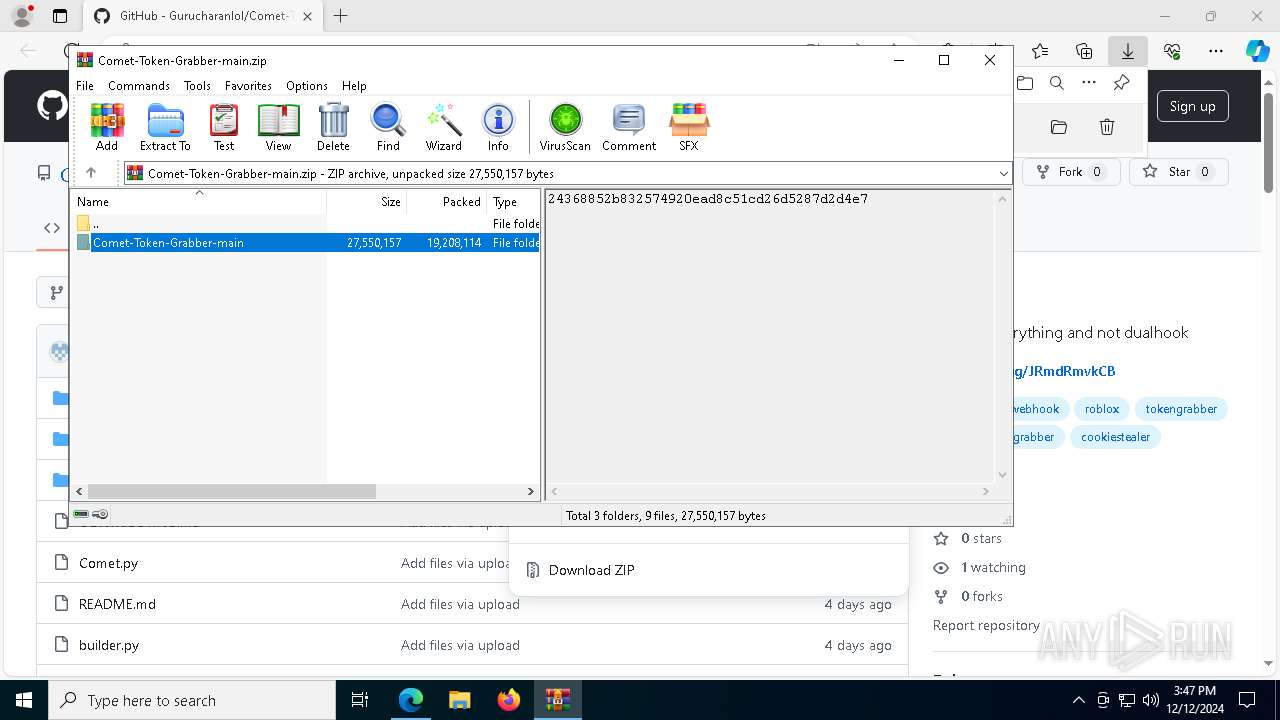
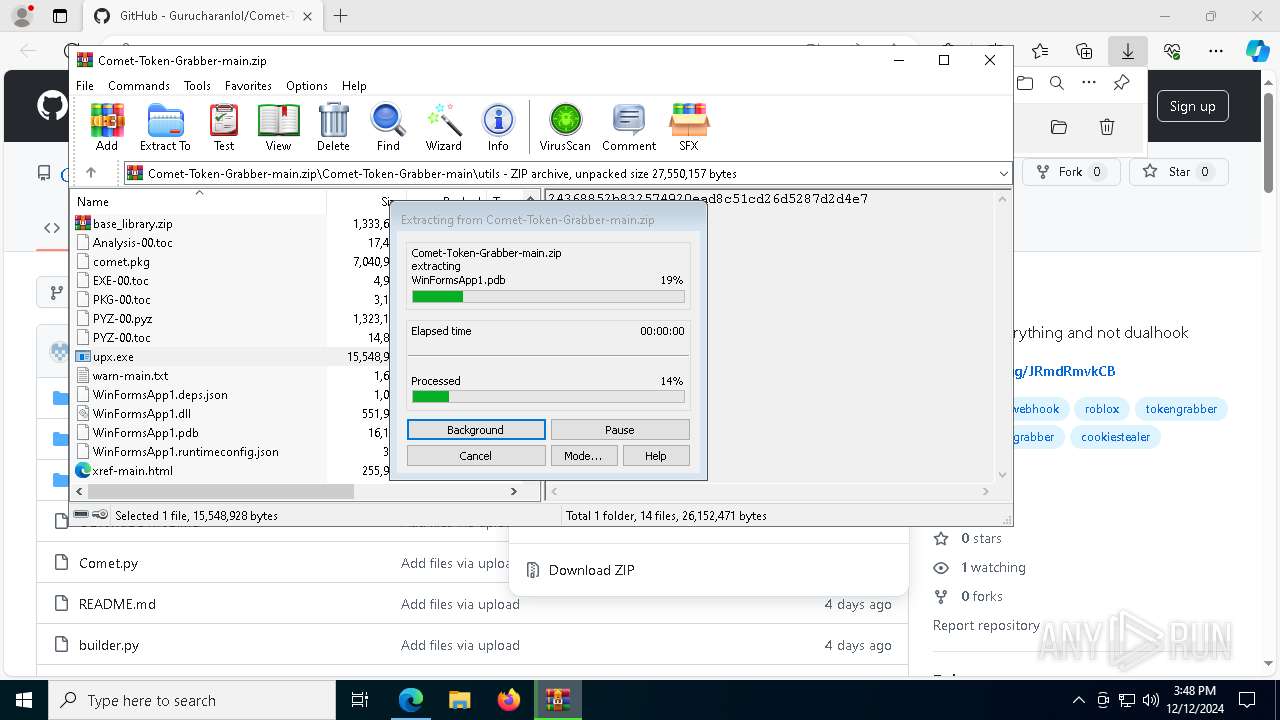
The process uses the downloaded file
- WinRAR.exe (PID: 3208)
Reads the machine GUID from the registry
- upx.exe (PID: 396)
Reads the software policy settings
- upx.exe (PID: 396)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3208)
Checks supported languages
- upx.exe (PID: 396)
- upx.exe (PID: 7540)
- upx.exe (PID: 7996)
- upx.exe (PID: 7352)
Reads the computer name
- upx.exe (PID: 5488)
- identity_helper.exe (PID: 7544)
Reads security settings of Internet Explorer
- fodhelper.exe (PID: 7832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
205
Monitored processes
74
Malicious processes
8
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
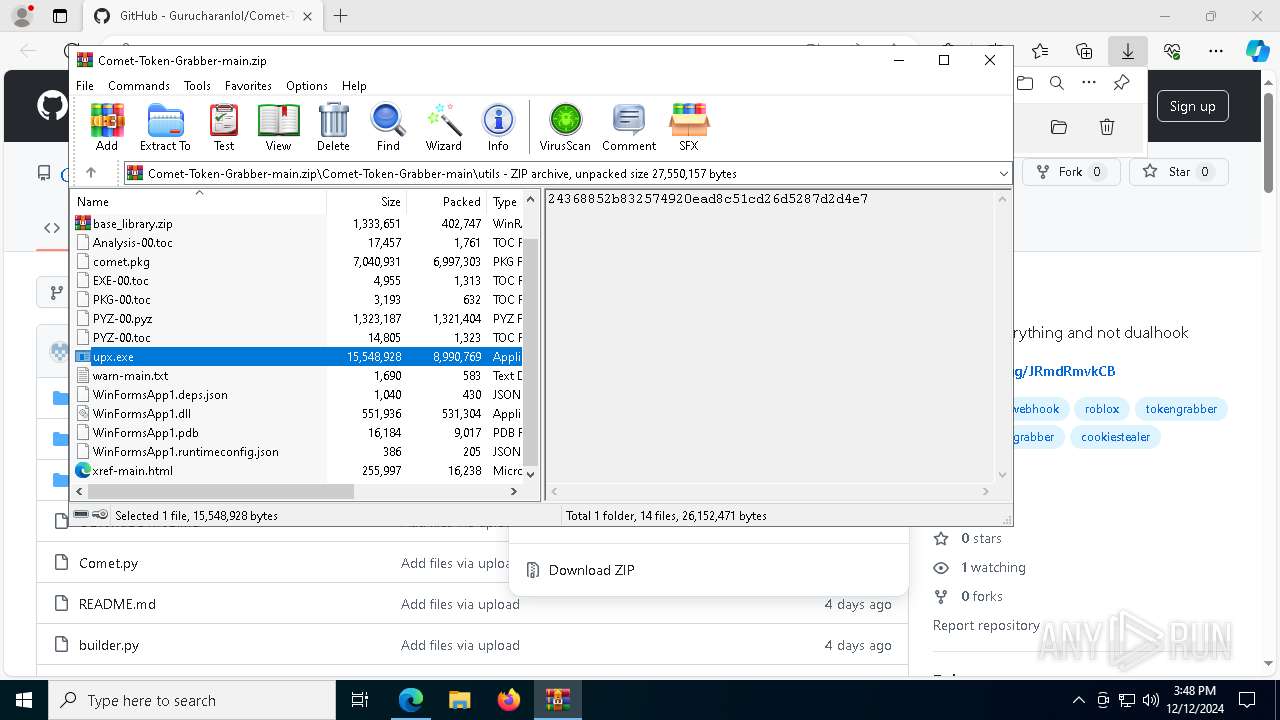
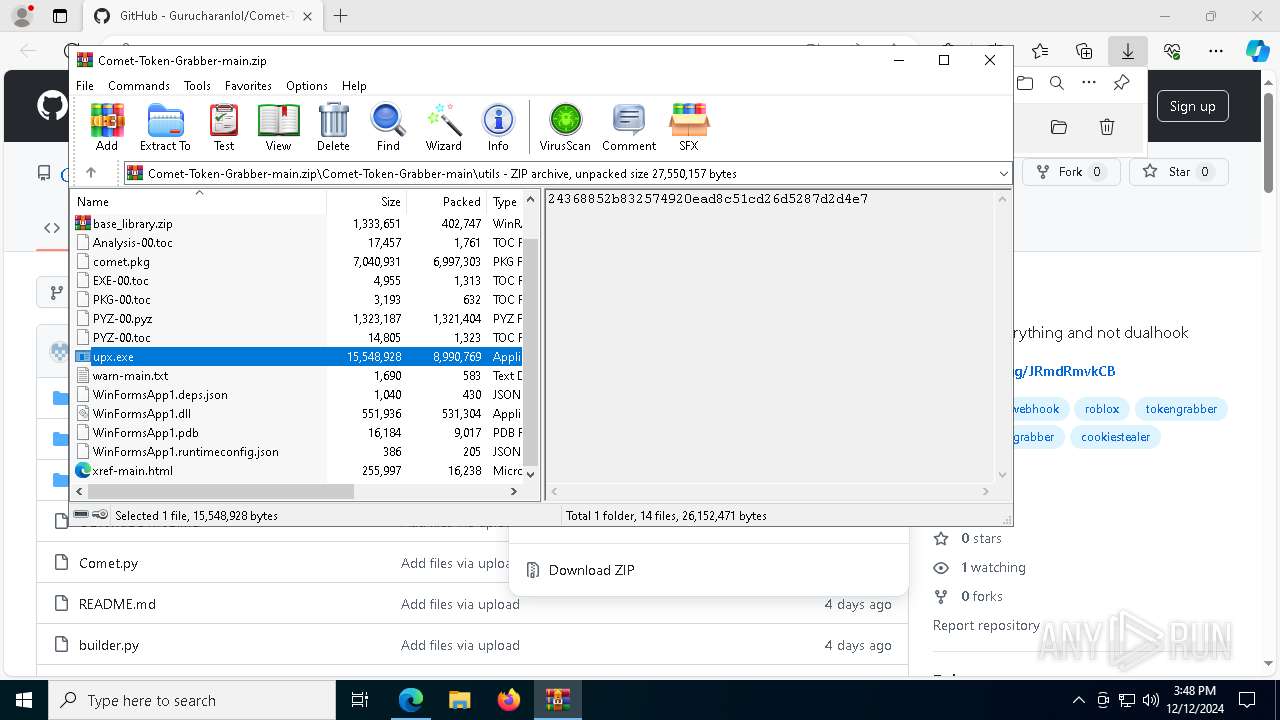
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
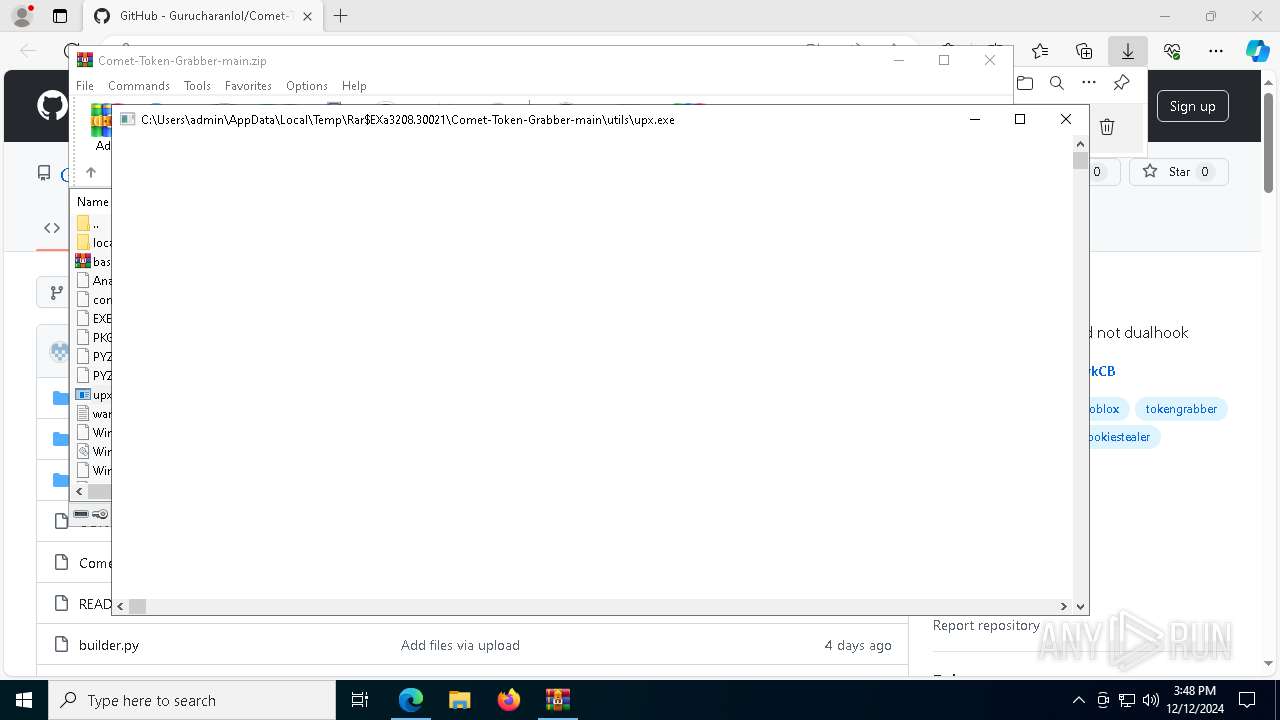
| 396 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3208.30021\Comet-Token-Grabber-main\utils\upx.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3208.30021\Comet-Token-Grabber-main\utils\upx.exe | fodhelper.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 420 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6828 --field-trial-handle=2352,i,13282490681882509605,2475304407627117102,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1576 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7264 --field-trial-handle=2352,i,13282490681882509605,2475304407627117102,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4164 --field-trial-handle=2352,i,13282490681882509605,2475304407627117102,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2076 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7672 --field-trial-handle=2352,i,13282490681882509605,2475304407627117102,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | attrib +h +s C:\Users\admin\AppData\Roaming\Microsoft\Protect\SecurityHealthSystray.exe | C:\Windows\System32\attrib.exe | — | upx.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | upx.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2728 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3208.30021\Comet-Token-Grabber-main\utils\upx.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3208.30021\Comet-Token-Grabber-main\utils\upx.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3060 | fodhelper | C:\Windows\System32\fodhelper.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Features On Demand Helper Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 369
Read events
21 301
Write events
63
Delete events
5
Modification events
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: FC52B1EAAA872F00 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: AFE7B9EAAA872F00 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328416 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5F1116B2-31FD-4D6E-915E-B904C3C85A39} | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328416 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {323CDF10-48C1-4407-958F-F9EEC372E0D9} | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328416 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7DC06D9F-9BBC-45E5-B0FE-31B59CFCF9F7} | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328416 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FE2267DE-FFA5-4068-ADA8-3C8953379439} | |||
Executable files
15
Suspicious files
346
Text files
125
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\0daa3115-eecb-4e89-b49b-f30d2ed28ab5.tmp | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135269.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135269.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135278.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135278.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
81
DNS requests
66
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.19.198.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.198.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.198.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4764 | SIHClient.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
396 | upx.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | shared |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4764 | SIHClient.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6300 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.19.198.194:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.19.198.194:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.215.121.133:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.215.121.133:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6764 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6372 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6764 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| shared |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
396 | upx.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
396 | upx.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
396 | upx.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
5488 | upx.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
5488 | upx.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
5488 | upx.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
7352 | upx.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |