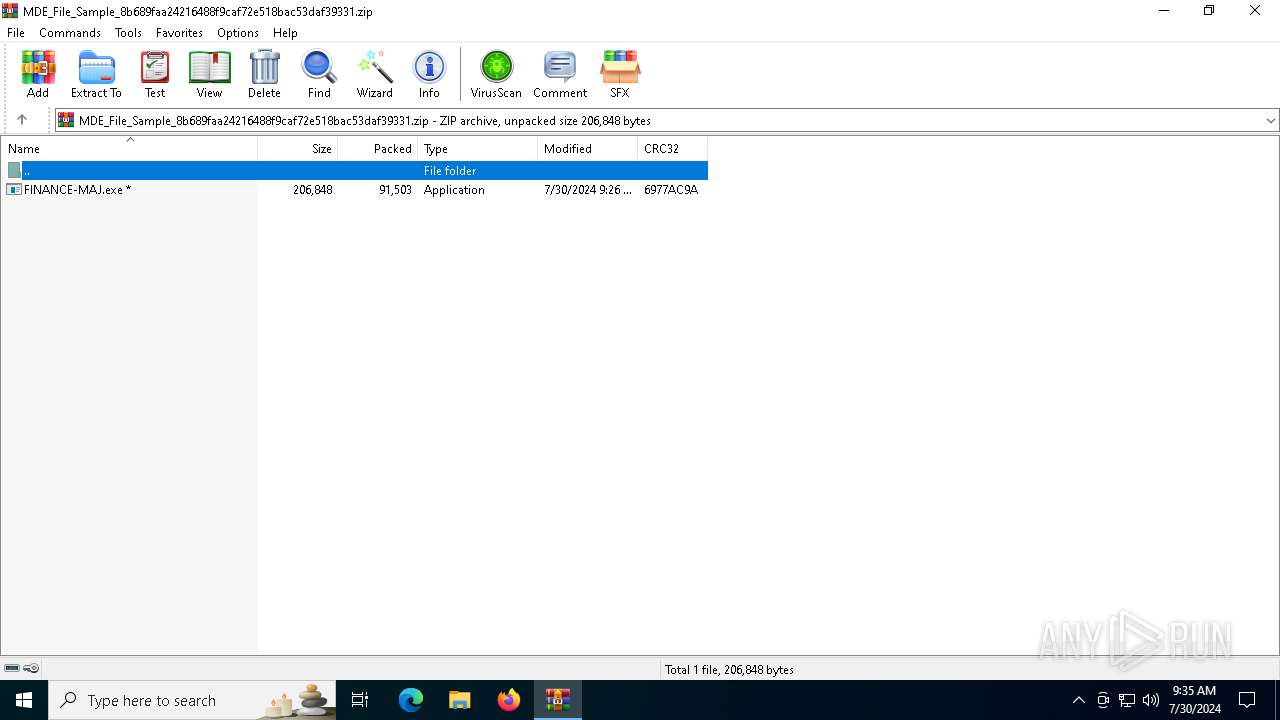
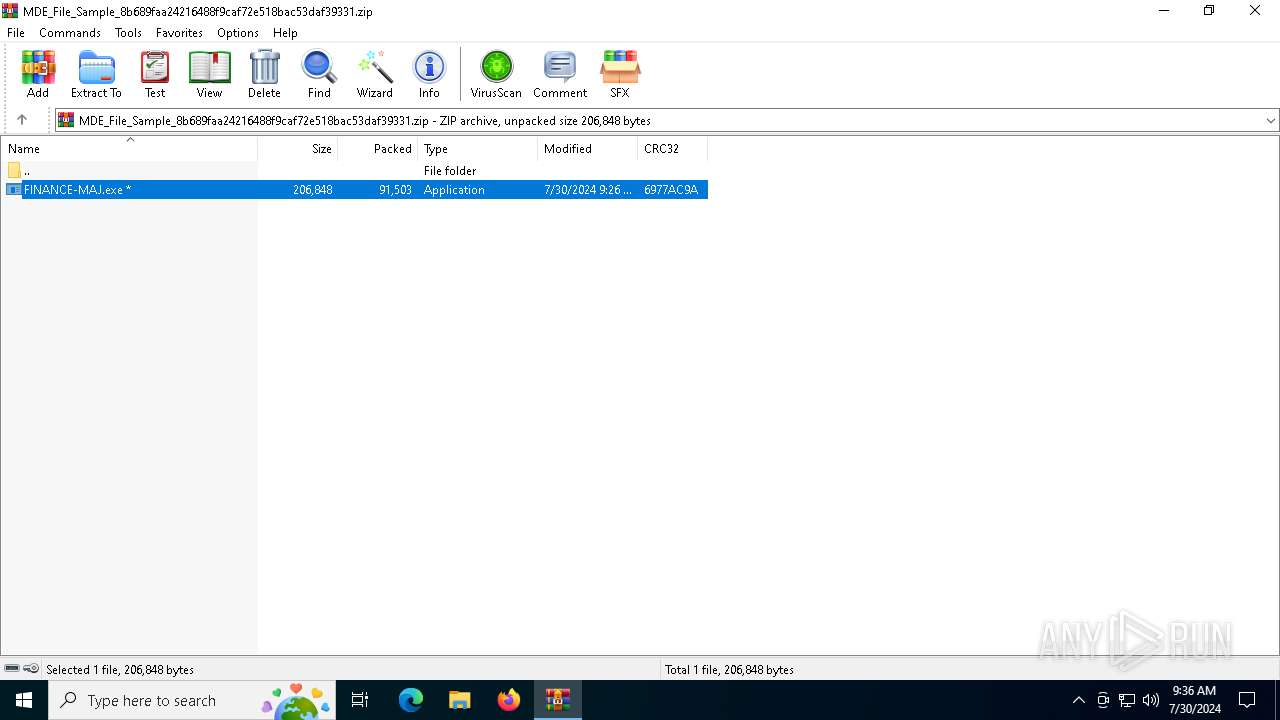
| File name: | MDE_File_Sample_8b689faa24216488f9caf72e518bac53daf39331.zip |
| Full analysis: | https://app.any.run/tasks/31a7a2bb-414d-4b2d-ab91-d56a8d4c1f42 |
| Verdict: | Malicious activity |
| Analysis date: | July 30, 2024, 09:35:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 0AC74B6D22D7E336ED13455CFB719D7C |
| SHA1: | 0571D6FE0A86368DA30B39E70E21064127B78F00 |
| SHA256: | F6ED9AA4C095183BB1695FD1D85E0B0464C1374B1FE14AC39F3768A25A6E7C57 |
| SSDEEP: | 1536:3dSuwmh9/DW9JZ3eEL9P8GQt18qb86ejW+/AuTK/7WUKtkYBrKhXuVpbY3PDGXDP:3dSyh9a9JZ3eENStxGShuTkKlr4+7JD/ |
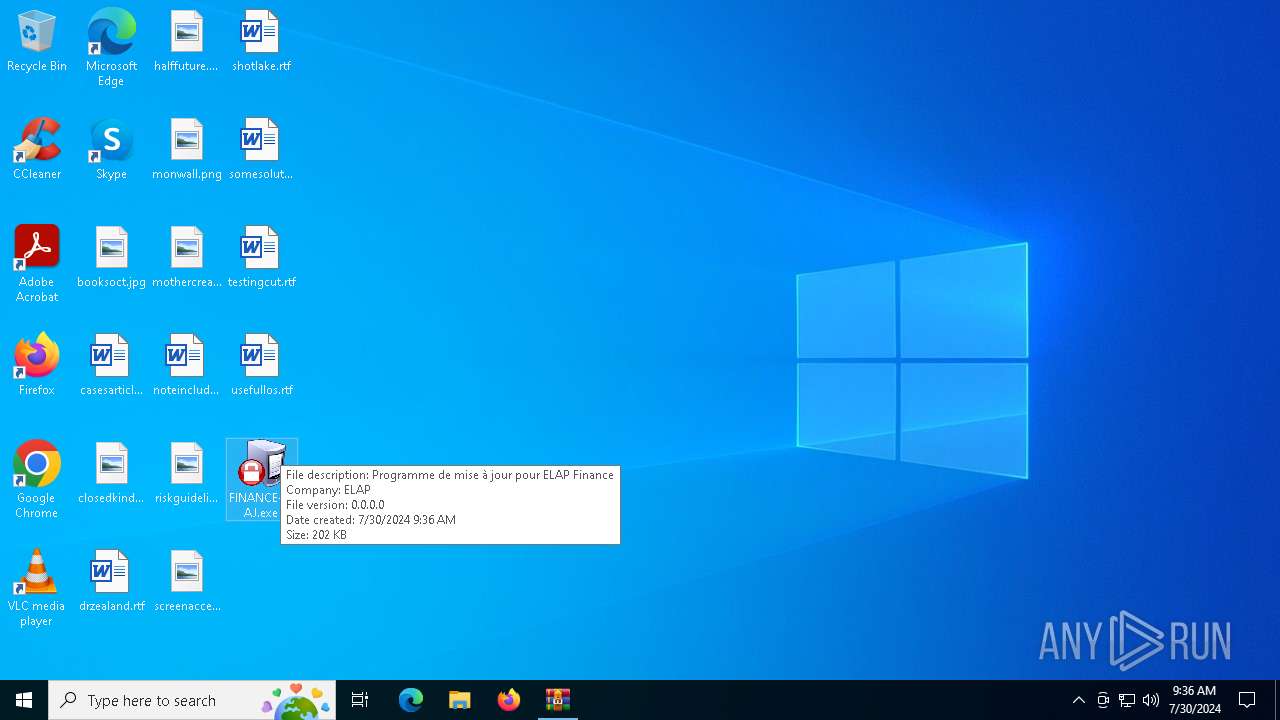
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 5624)
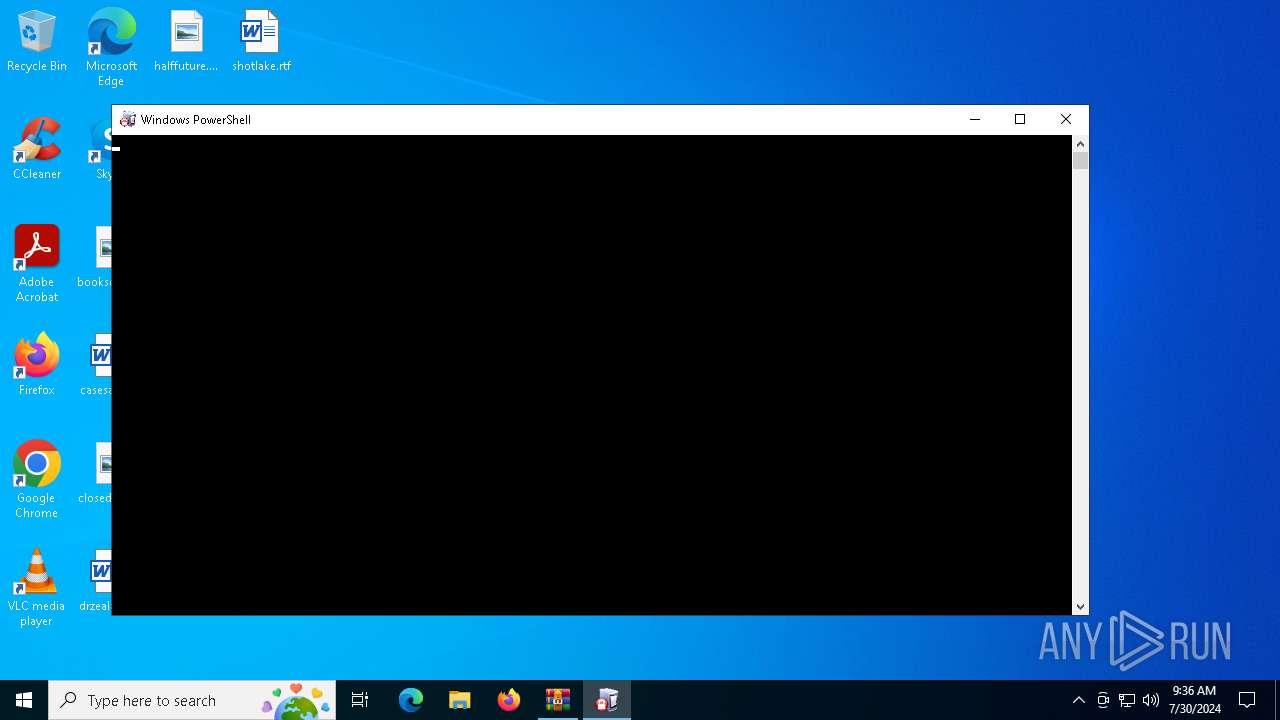
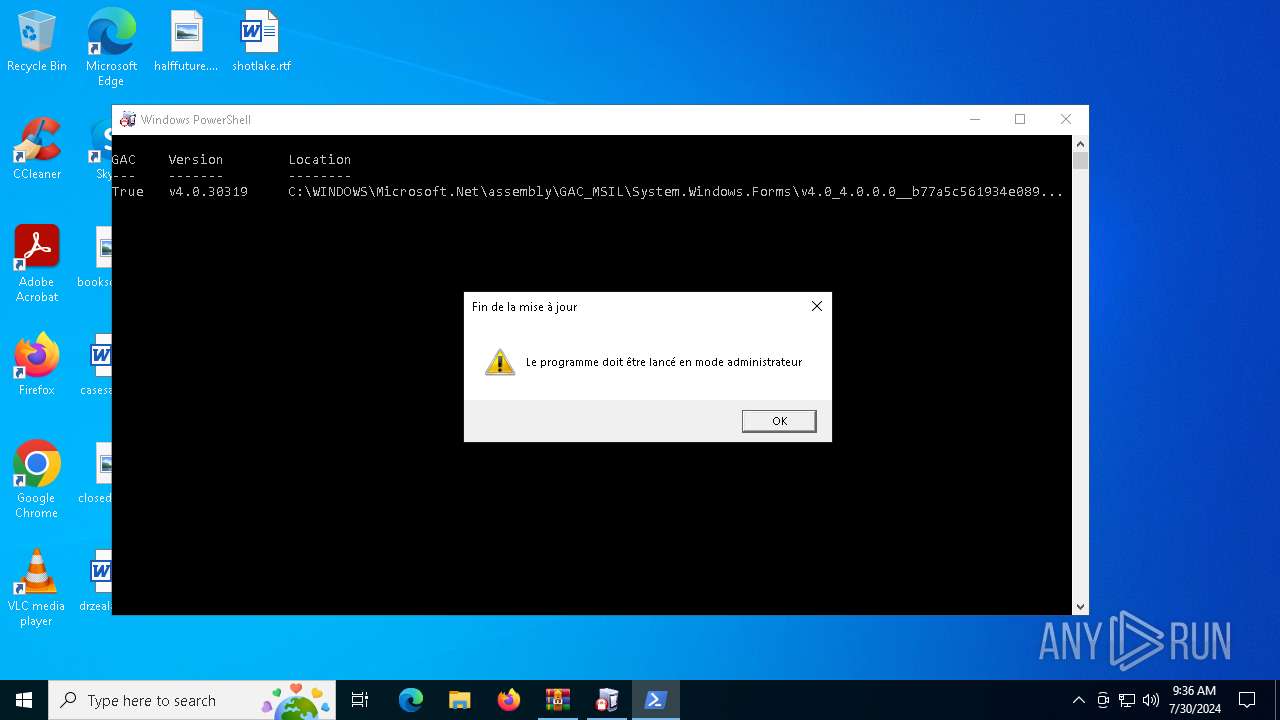
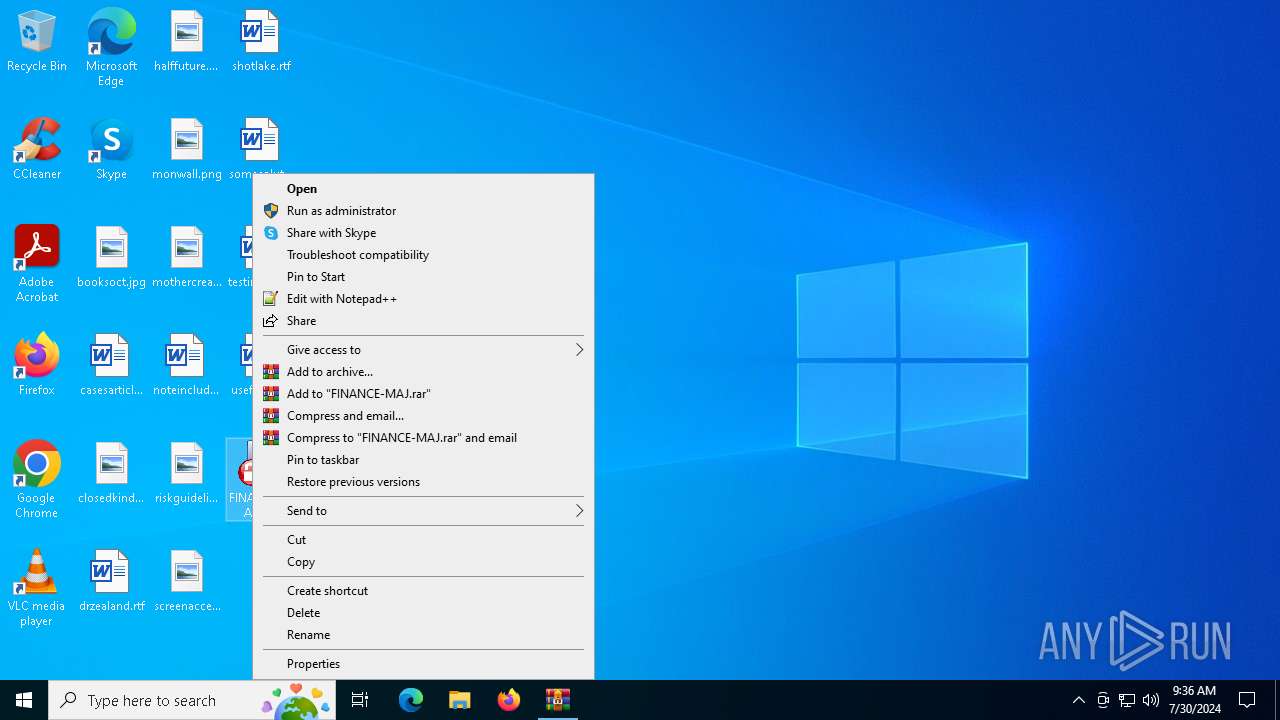
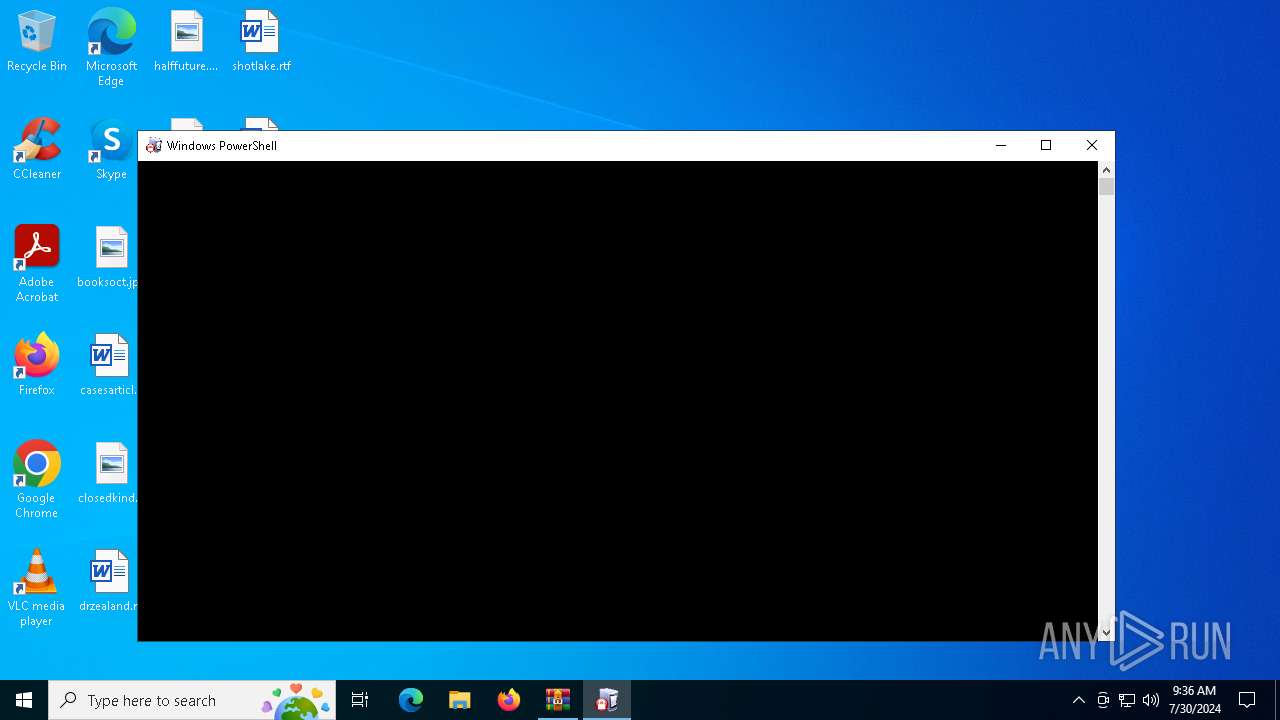
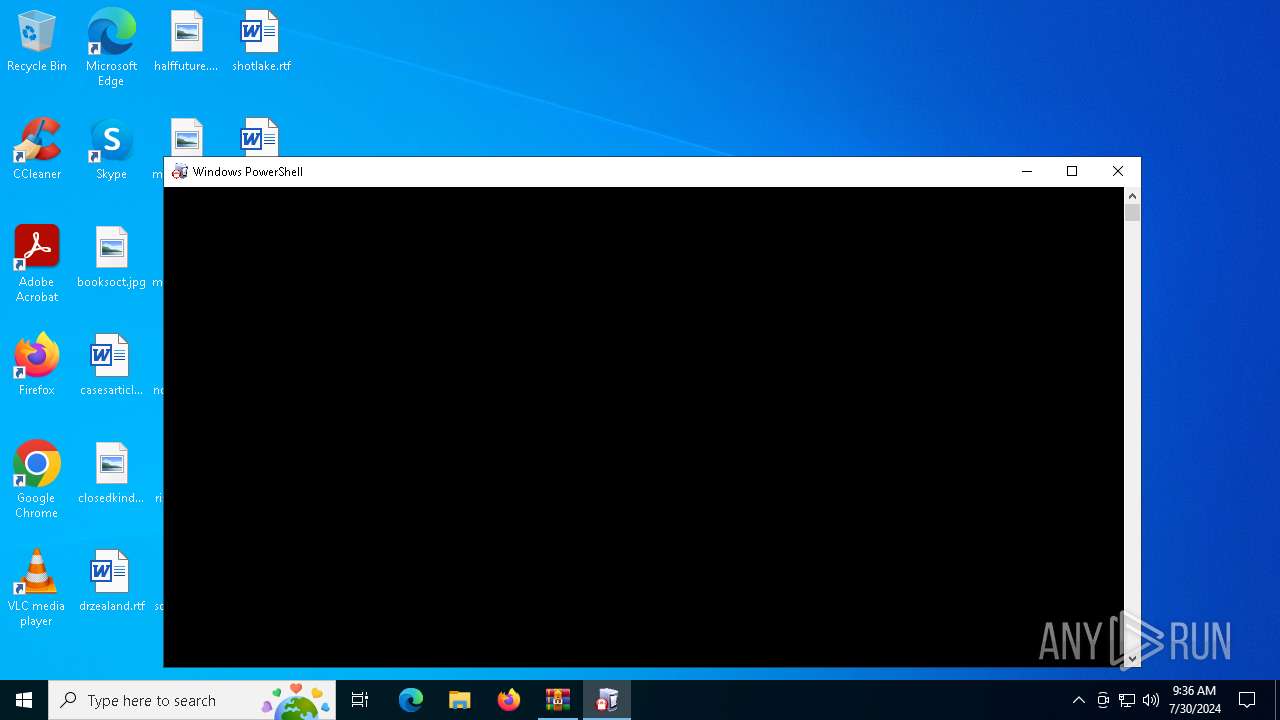
Bypass execution policy to execute commands
- powershell.exe (PID: 4180)
- powershell.exe (PID: 6220)
- powershell.exe (PID: 528)
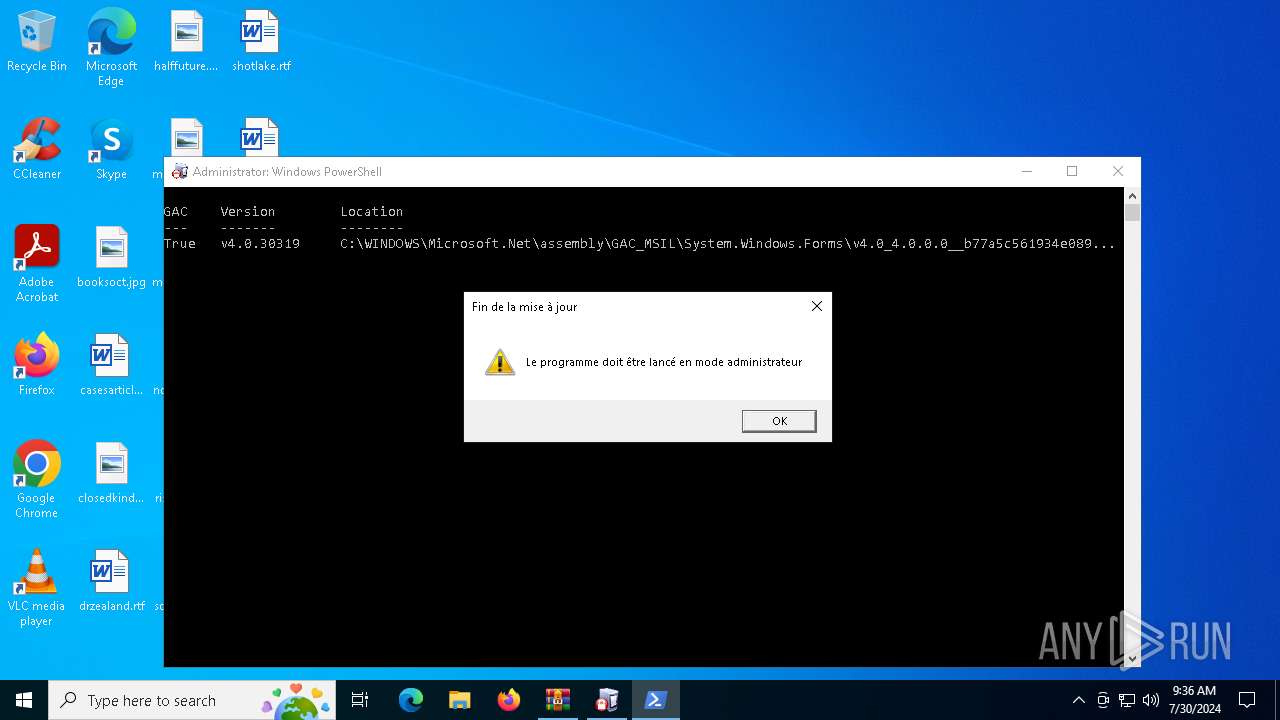
Changes powershell execution policy (Bypass)
- FINANCE-MAJ.exe (PID: 1156)
- FINANCE-MAJ.exe (PID: 4608)
- FINANCE-MAJ.exe (PID: 968)
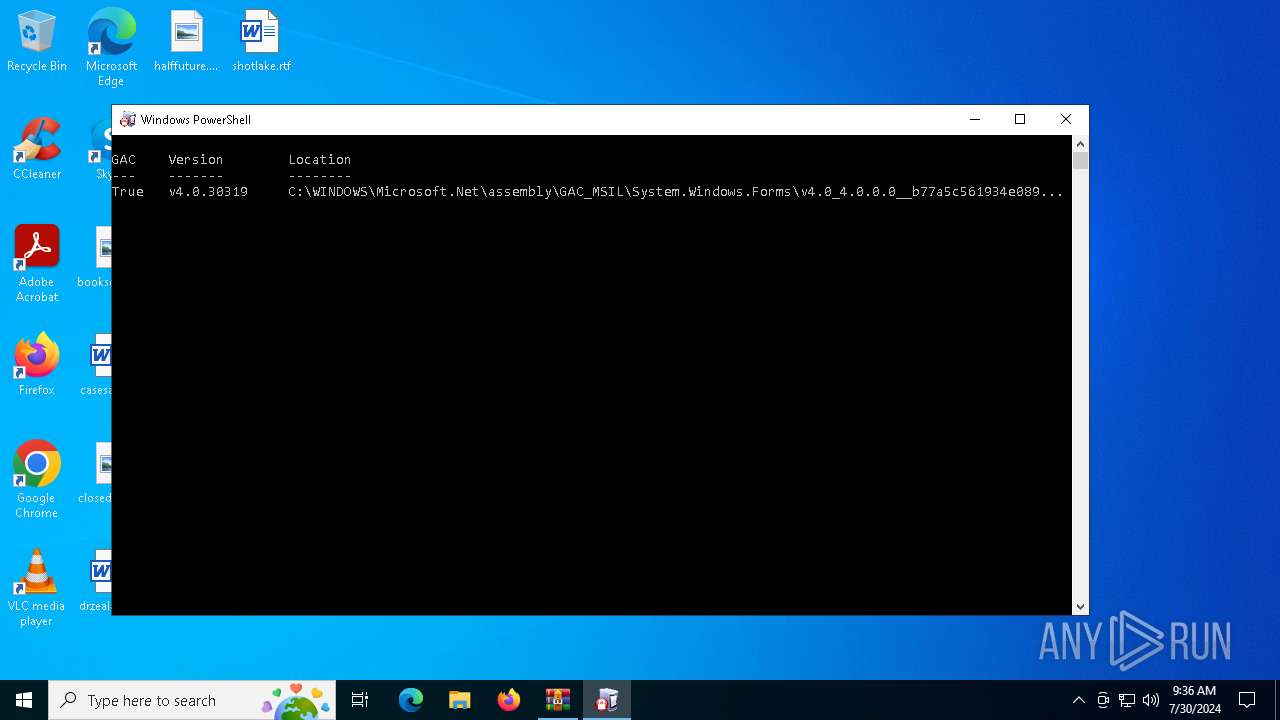
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 4180)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- FINANCE-MAJ.exe (PID: 1156)
- FINANCE-MAJ.exe (PID: 4608)
- FINANCE-MAJ.exe (PID: 968)
The process executes Powershell scripts
- FINANCE-MAJ.exe (PID: 1156)
- FINANCE-MAJ.exe (PID: 4608)
- FINANCE-MAJ.exe (PID: 968)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5624)
Create files in a temporary directory
- FINANCE-MAJ.exe (PID: 1156)
- FINANCE-MAJ.exe (PID: 4608)
Checks supported languages
- FINANCE-MAJ.exe (PID: 1156)
- FINANCE-MAJ.exe (PID: 4608)
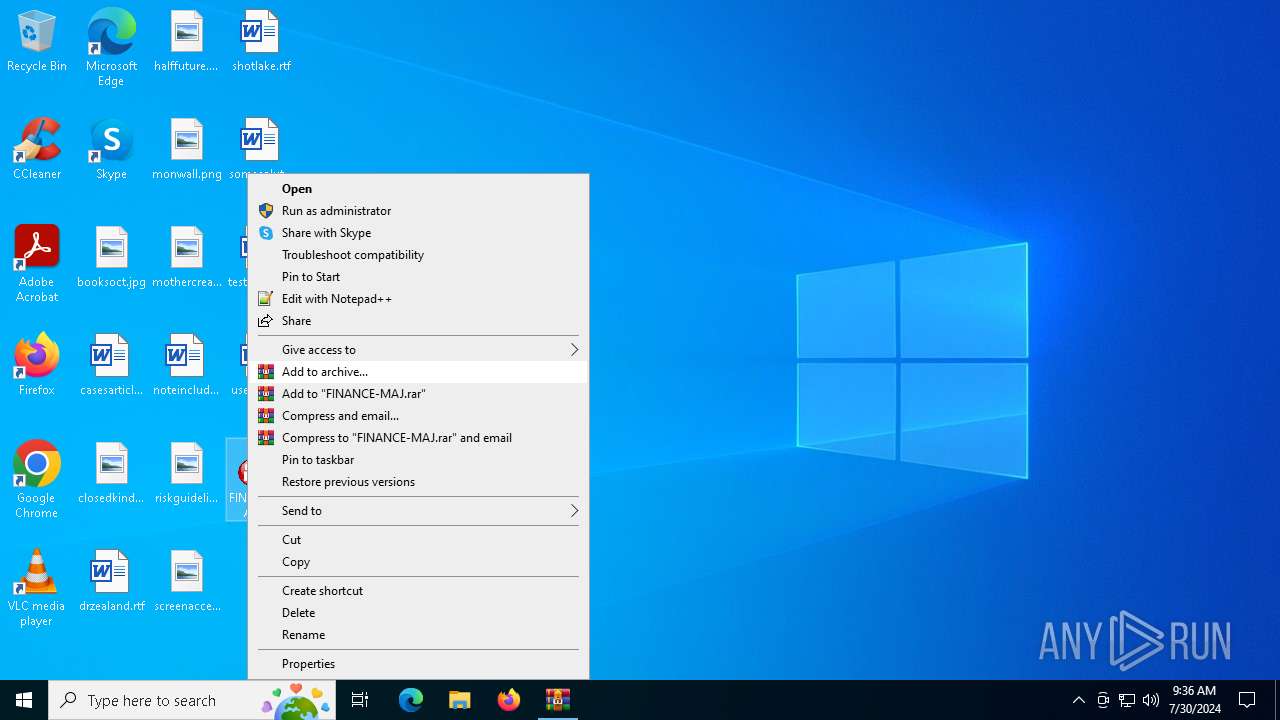
Manual execution by a user
- FINANCE-MAJ.exe (PID: 1156)
- FINANCE-MAJ.exe (PID: 4608)
- FINANCE-MAJ.exe (PID: 968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:07:30 09:26:30 |
| ZipCRC: | 0x6977ac9a |
| ZipCompressedSize: | 91503 |
| ZipUncompressedSize: | 206848 |
| ZipFileName: | FINANCE-MAJ.exe |
Total processes
153
Monitored processes
11
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | "powershell" –NoProfile -ExecutionPolicy Bypass -File C:\Users\admin\AppData\Local\Temp\D3A3.tmp\D3A4.tmp\D3A5.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | FINANCE-MAJ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 968 | "C:\Users\admin\Desktop\FINANCE-MAJ.exe" | C:\Users\admin\Desktop\FINANCE-MAJ.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH | |||||||||||||||
| 1156 | "C:\Users\admin\Desktop\FINANCE-MAJ.exe" | C:\Users\admin\Desktop\FINANCE-MAJ.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2952 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | FINANCE-MAJ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4180 | "powershell" –NoProfile -ExecutionPolicy Bypass -File C:\Users\admin\AppData\Local\Temp\76AE.tmp\76AF.tmp\76B0.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | FINANCE-MAJ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | FINANCE-MAJ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4476 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4608 | "C:\Users\admin\Desktop\FINANCE-MAJ.exe" | C:\Users\admin\Desktop\FINANCE-MAJ.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
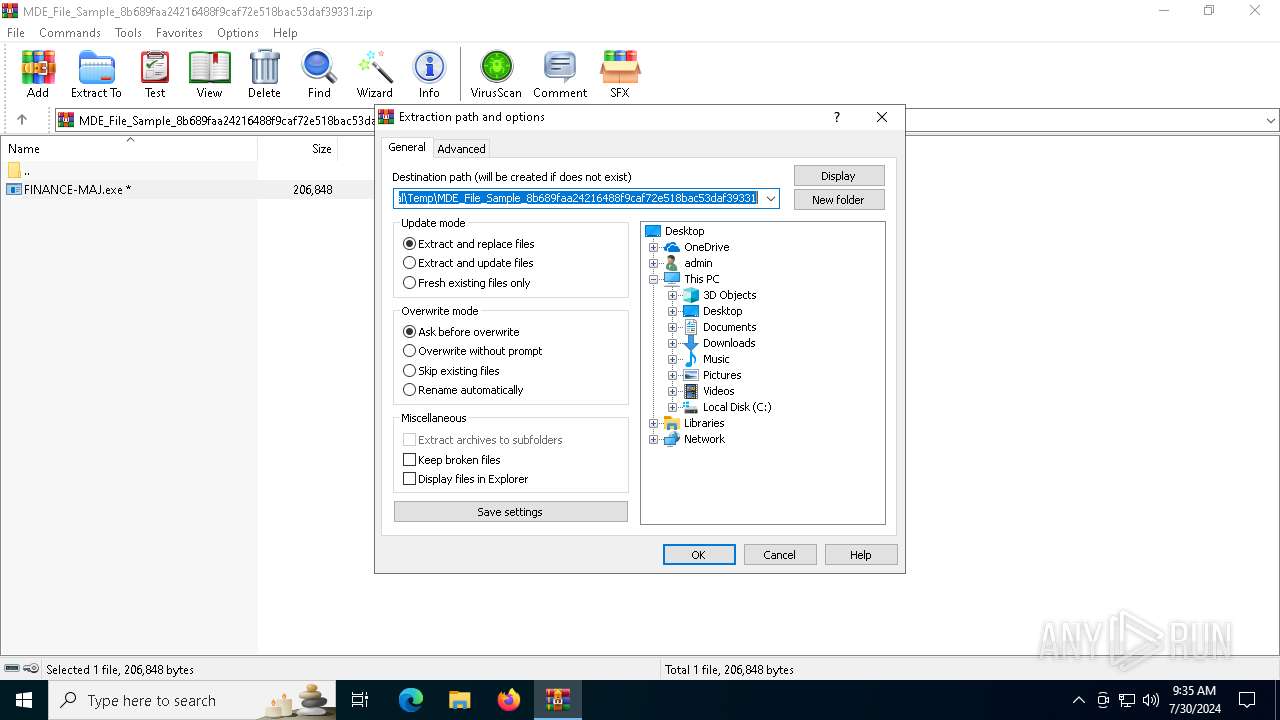
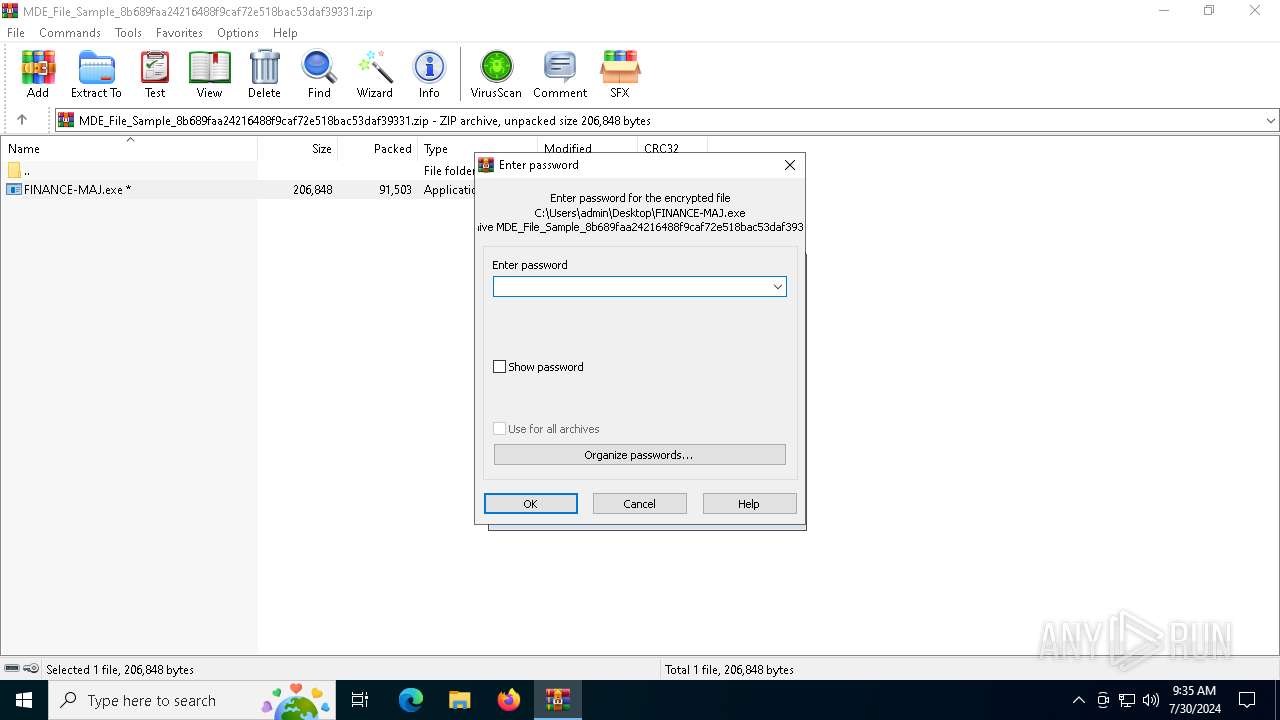
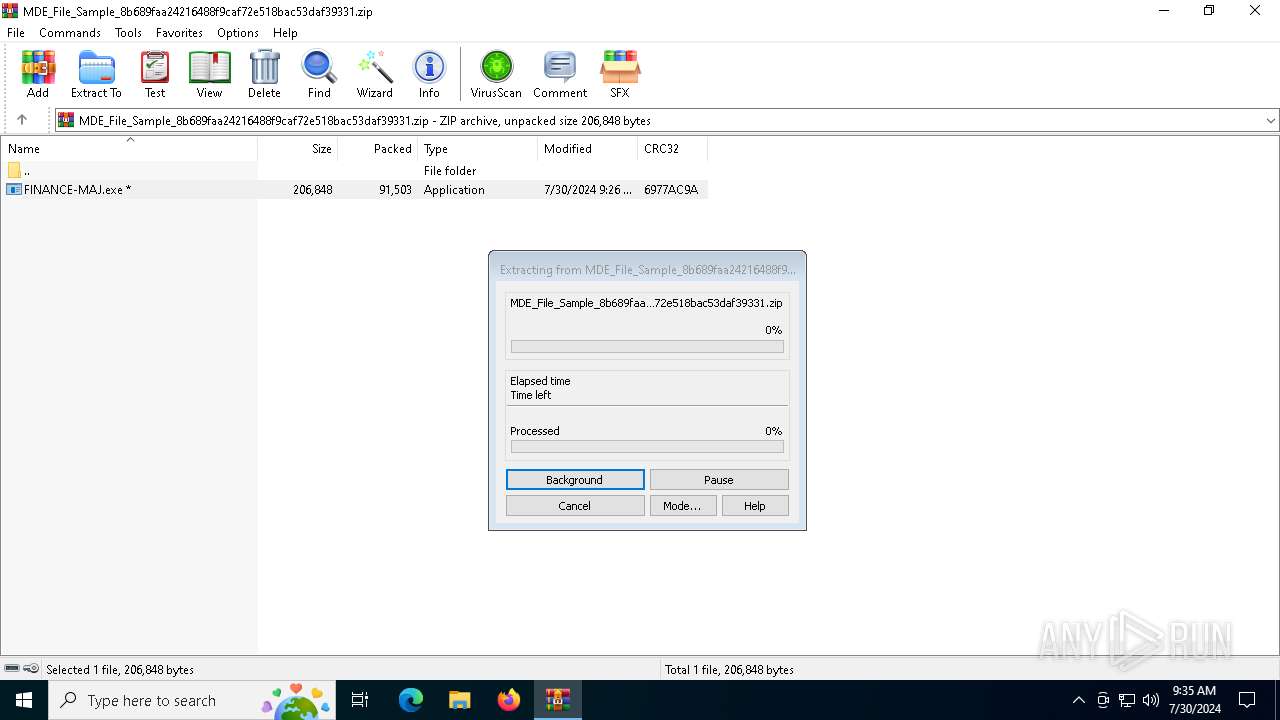
| 5624 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\MDE_File_Sample_8b689faa24216488f9caf72e518bac53daf39331.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6220 | "powershell" –NoProfile -ExecutionPolicy Bypass -File C:\Users\admin\AppData\Local\Temp\B86A.tmp\B86B.tmp\B86C.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | FINANCE-MAJ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
19 494
Read events
19 484
Write events
10
Delete events
0
Modification events
| (PID) Process: | (5624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (5624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (5624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (5624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MDE_File_Sample_8b689faa24216488f9caf72e518bac53daf39331.zip | |||
| (PID) Process: | (5624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (5624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
1
Suspicious files
10
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5624 | WinRAR.exe | C:\Users\admin\Desktop\FINANCE-MAJ.exe | executable | |
MD5:386397E56F66A38983AA176555A3A6C1 | SHA256:53135659CAAB7F07E597A293D3108B089FA03989A3FE67CD1C4950A3E7D239AD | |||
| 4180 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:10D39437AA9600F650C6D7A39AB0B89A | SHA256:5EF4C9CCA6954CC1CA5BD5C0ED9D2C2A35A50B8DCA5959A18F36F1999B890A70 | |||
| 6220 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1cb907.TMP | binary | |
MD5:10D39437AA9600F650C6D7A39AB0B89A | SHA256:5EF4C9CCA6954CC1CA5BD5C0ED9D2C2A35A50B8DCA5959A18F36F1999B890A70 | |||
| 1156 | FINANCE-MAJ.exe | C:\Users\admin\AppData\Local\Temp\76AE.tmp\76AF.tmp\76B0.ps1 | text | |
MD5:63E9D742E641C4BDCFD66EC728194E10 | SHA256:1E45A7E44F08B3EED7E666F77DDEB433BA28EB0228C7E913D84875B1F5155603 | |||
| 4180 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jfjydkv1.gw0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4180 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lk1v2jeo.lhn.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4180 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1c7779.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 4180 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\X303NJN8SVKDA6ZNRTY8.temp | binary | |
MD5:10D39437AA9600F650C6D7A39AB0B89A | SHA256:5EF4C9CCA6954CC1CA5BD5C0ED9D2C2A35A50B8DCA5959A18F36F1999B890A70 | |||
| 6220 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NR6U60FALS6G55ALM0JU.temp | binary | |
MD5:3A279869FDF1F6BC95AE38450F3F623D | SHA256:E6B05523906315A384BEE731BF4325717073EE2669BCECB27D9F3A0B433B8259 | |||
| 968 | FINANCE-MAJ.exe | C:\Users\admin\AppData\Local\Temp\D3A3.tmp\D3A4.tmp\D3A5.ps1 | text | |
MD5:63E9D742E641C4BDCFD66EC728194E10 | SHA256:1E45A7E44F08B3EED7E666F77DDEB433BA28EB0228C7E913D84875B1F5155603 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
42
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
504 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4340 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5368 | SearchApp.exe | 95.100.146.16:443 | www.bing.com | Akamai International B.V. | CZ | unknown |
5368 | SearchApp.exe | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
5464 | slui.exe | 20.83.72.98:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6012 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4236 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
488 | slui.exe | 20.83.72.98:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t-ring-fdv2.msedge.net |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
a-ring-fallback.msedge.net |
| unknown |
google.com |
| whitelisted |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |