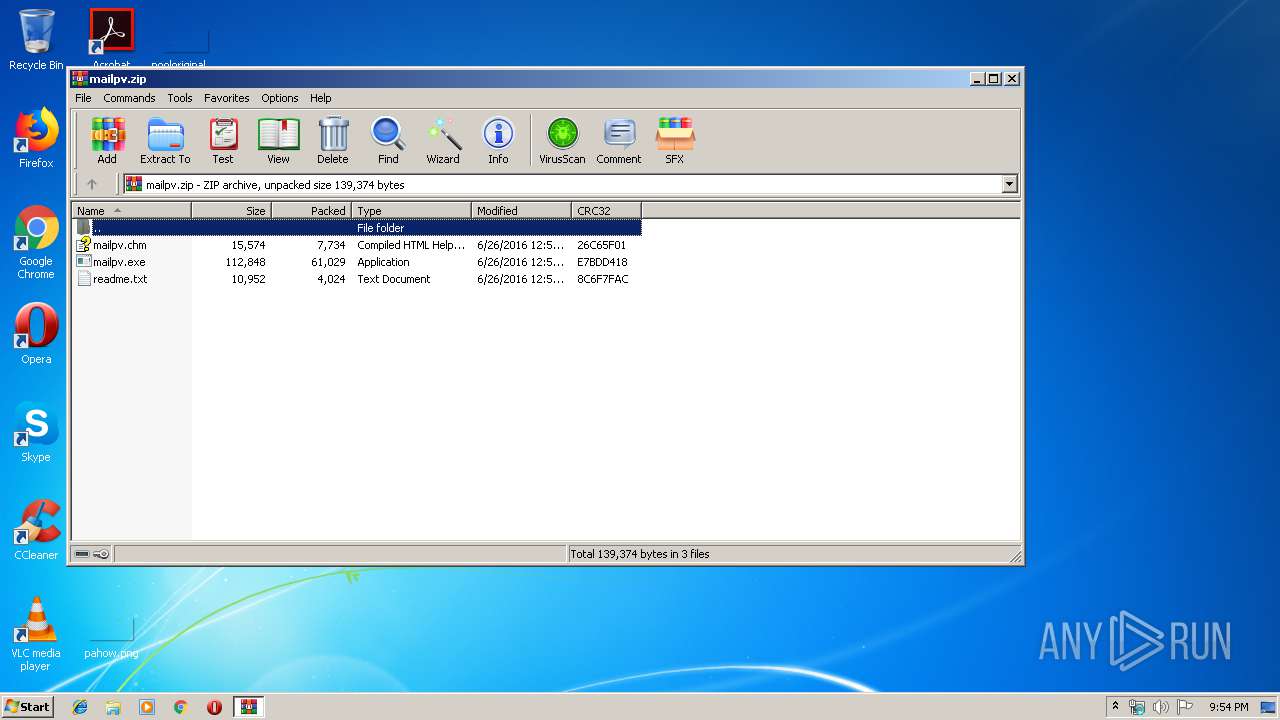
| File name: | mailpv.zip |
| Full analysis: | https://app.any.run/tasks/3d54ecbb-07cc-49bb-b2bc-e2fbe9548f8d |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2019, 20:54:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 720AEEB56DFE9FA9AB0D0D28E36EFAB0 |
| SHA1: | 6490EF83B9A61C7406E9C9FEB4363AAD603A5D83 |
| SHA256: | F6EC2FB60D5FB109B56C39D637599F3DD71F96E27AE4D33E46557C2D02A88504 |
| SSDEEP: | 1536:5pmqOPGjqVsLgarBIqZrIvrsTwaiujdstJY4WmuB:5YuumrBSsTwcdstJhG |
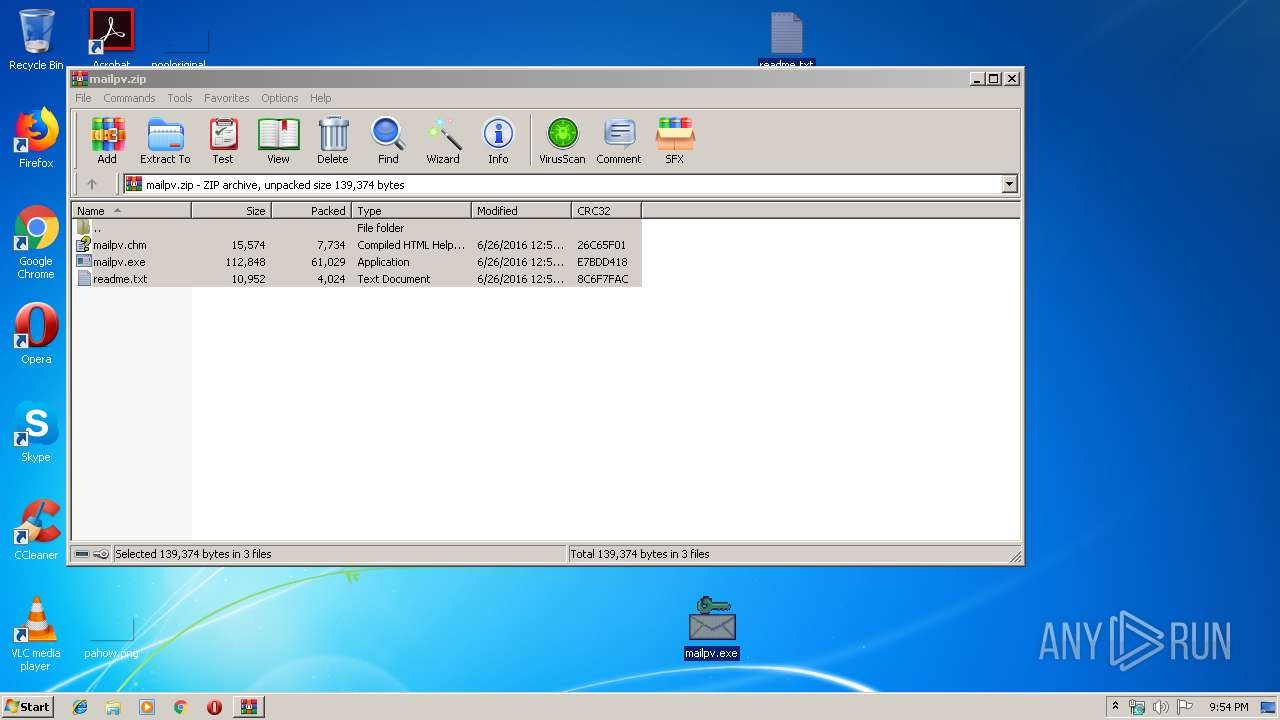
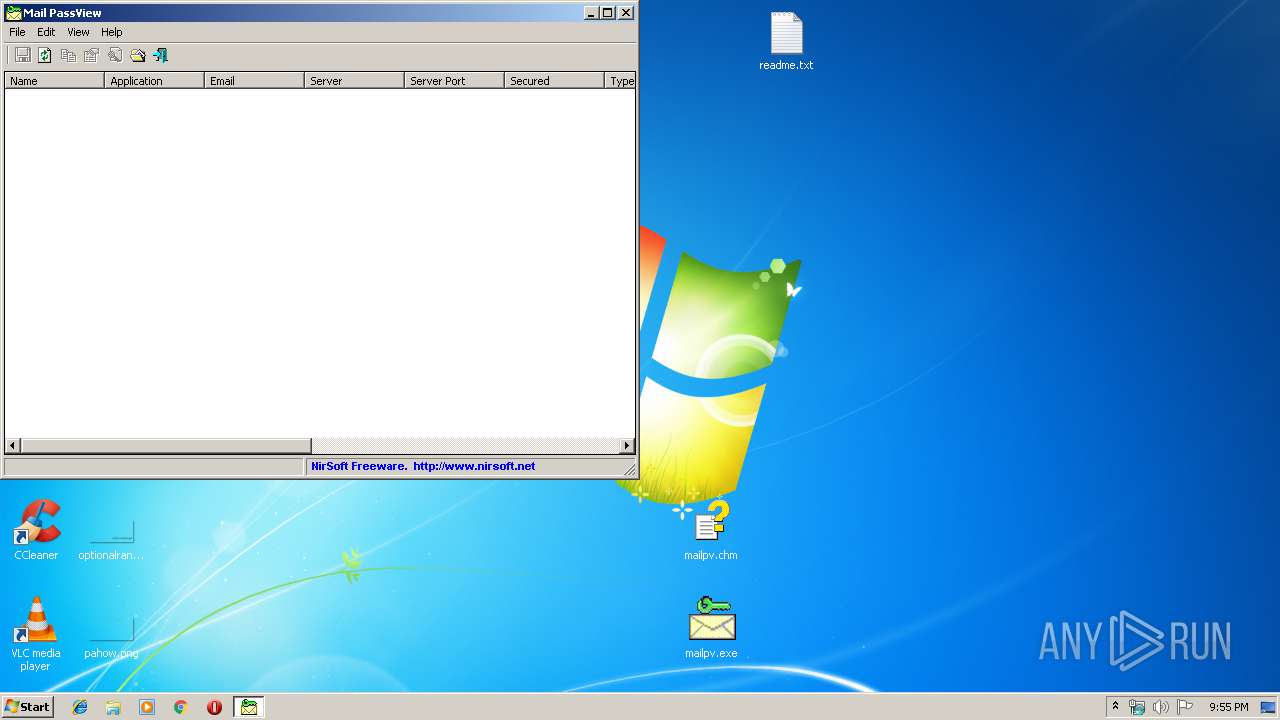
MALICIOUS
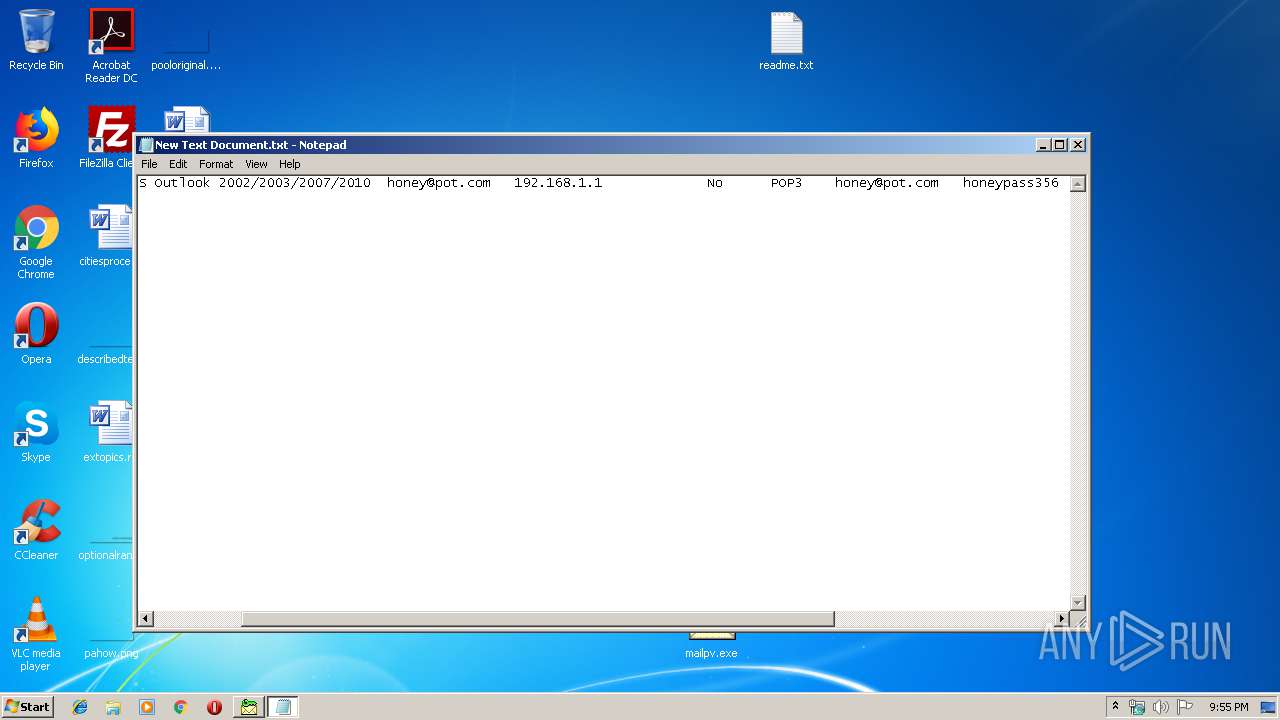
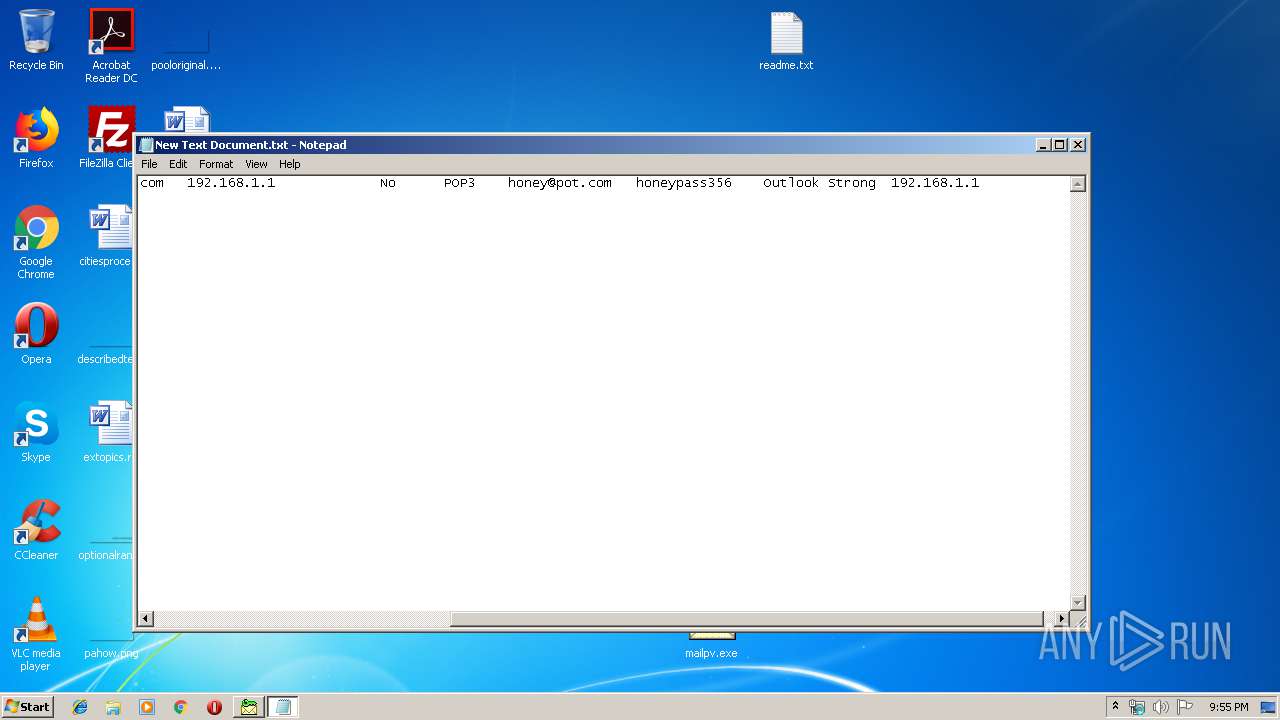
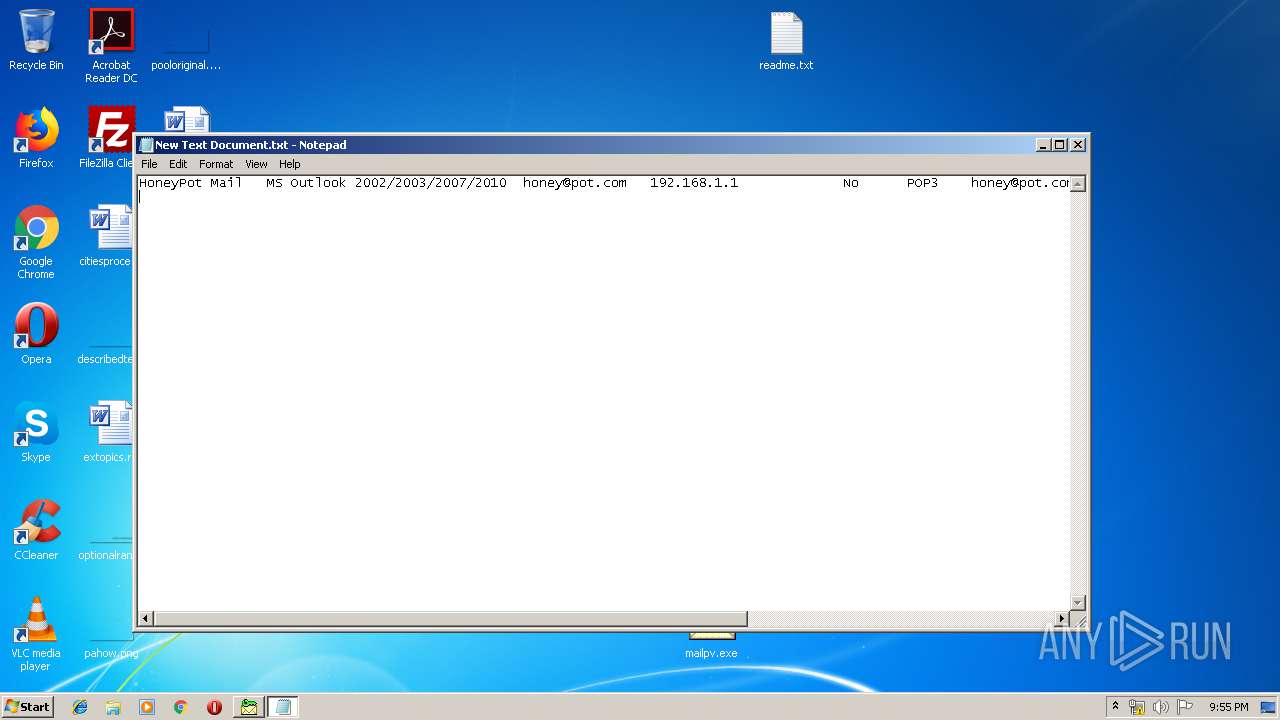
Application was dropped or rewritten from another process
- mailpv.exe (PID: 3932)
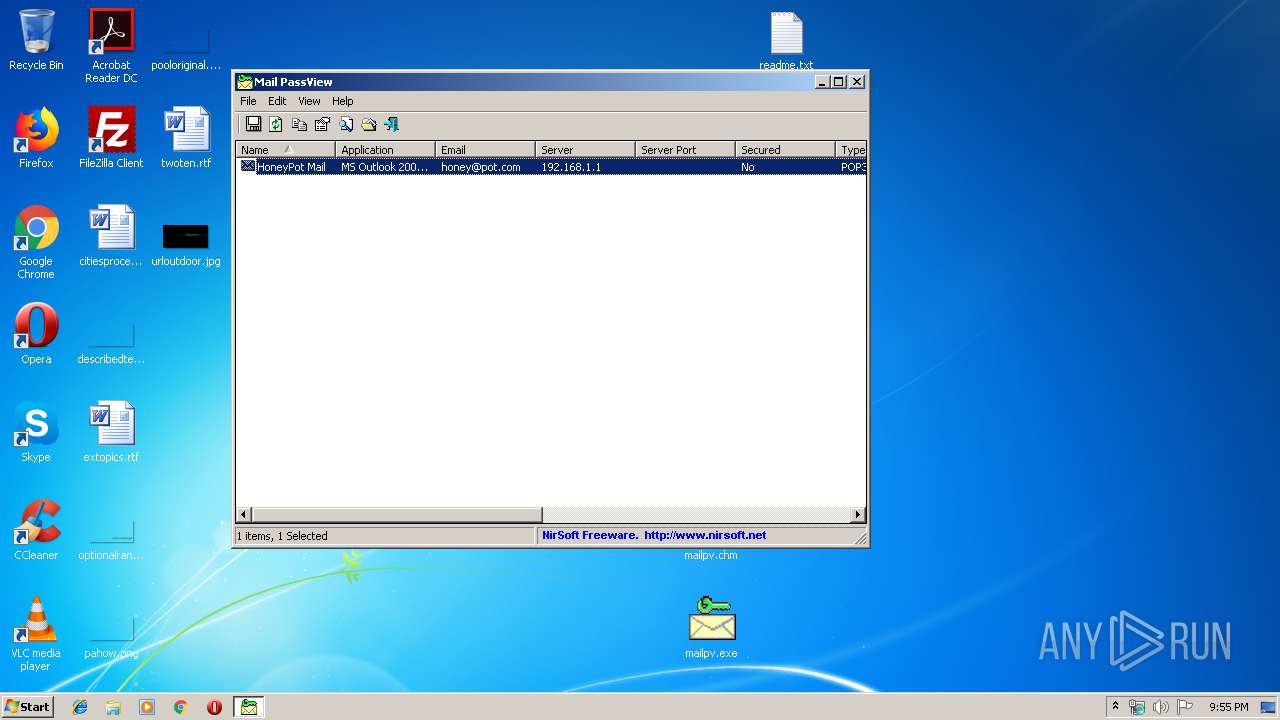
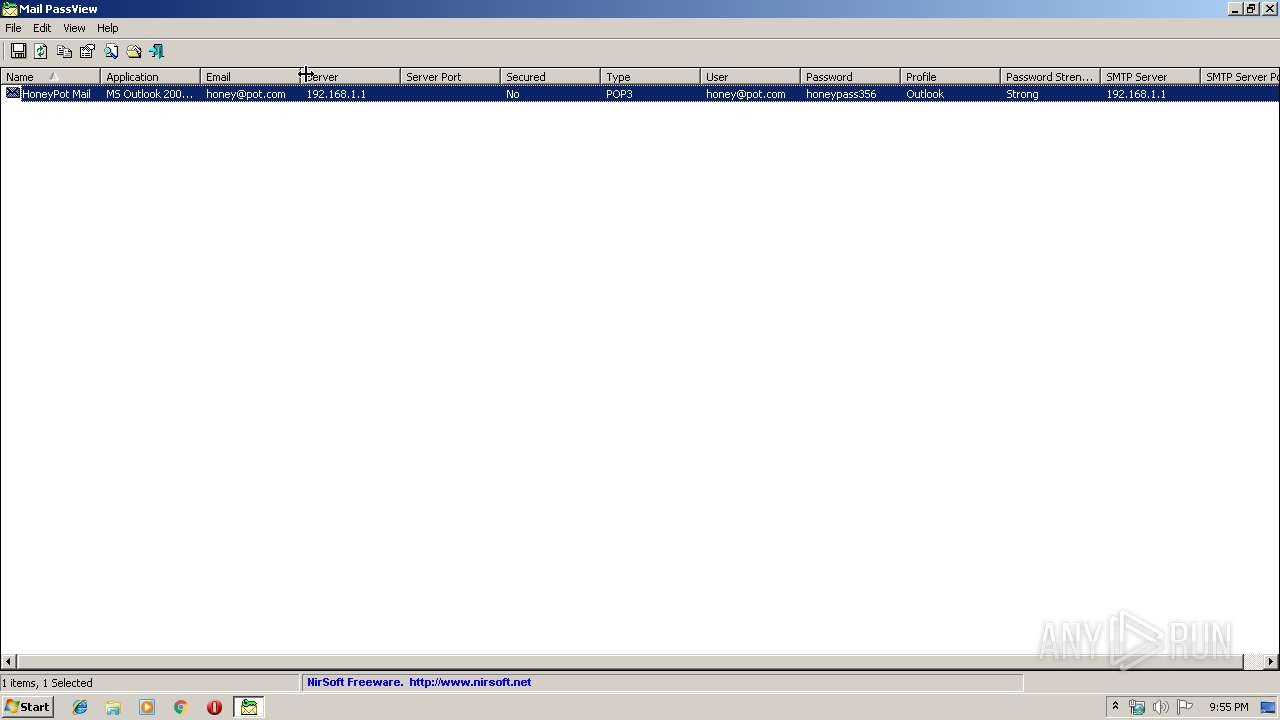
Actions looks like stealing of personal data
- mailpv.exe (PID: 3932)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2896)
INFO
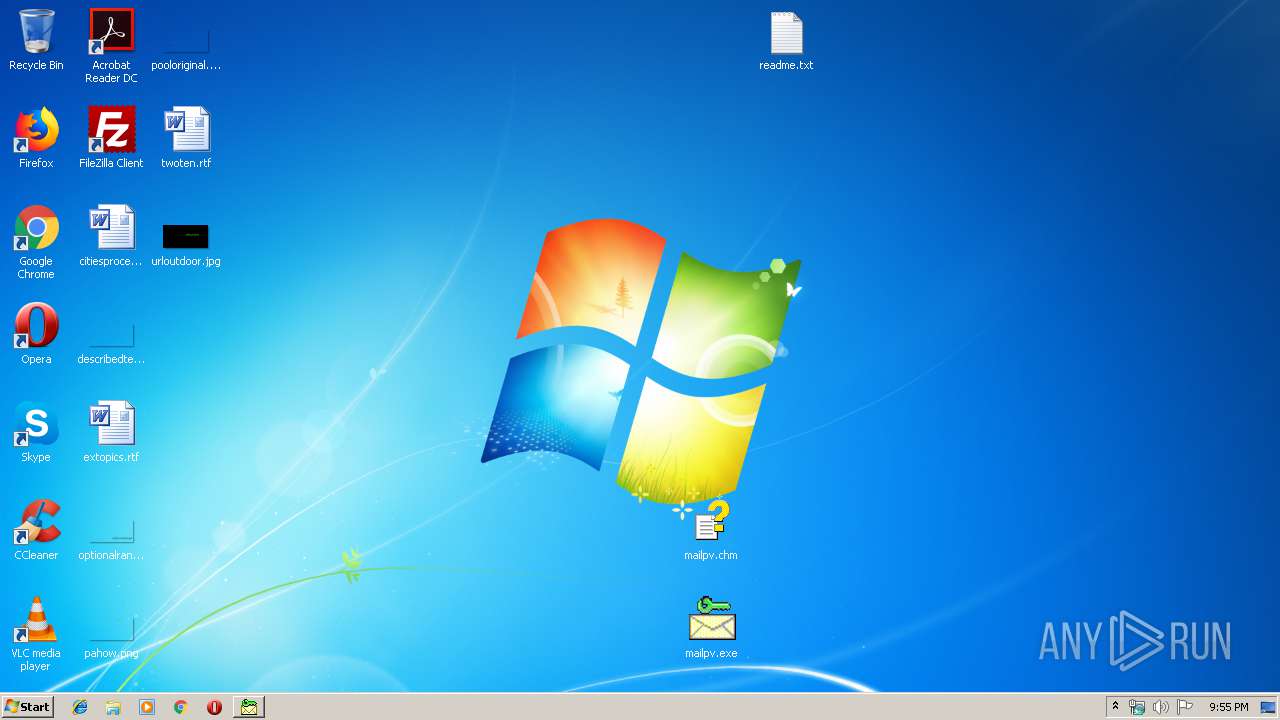
Manual execution by user
- mailpv.exe (PID: 3932)
- NOTEPAD.EXE (PID: 2372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2016:06:26 12:52:13 |
| ZipCRC: | 0xe7bdd418 |
| ZipCompressedSize: | 61029 |
| ZipUncompressedSize: | 112848 |
| ZipFileName: | mailpv.exe |
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
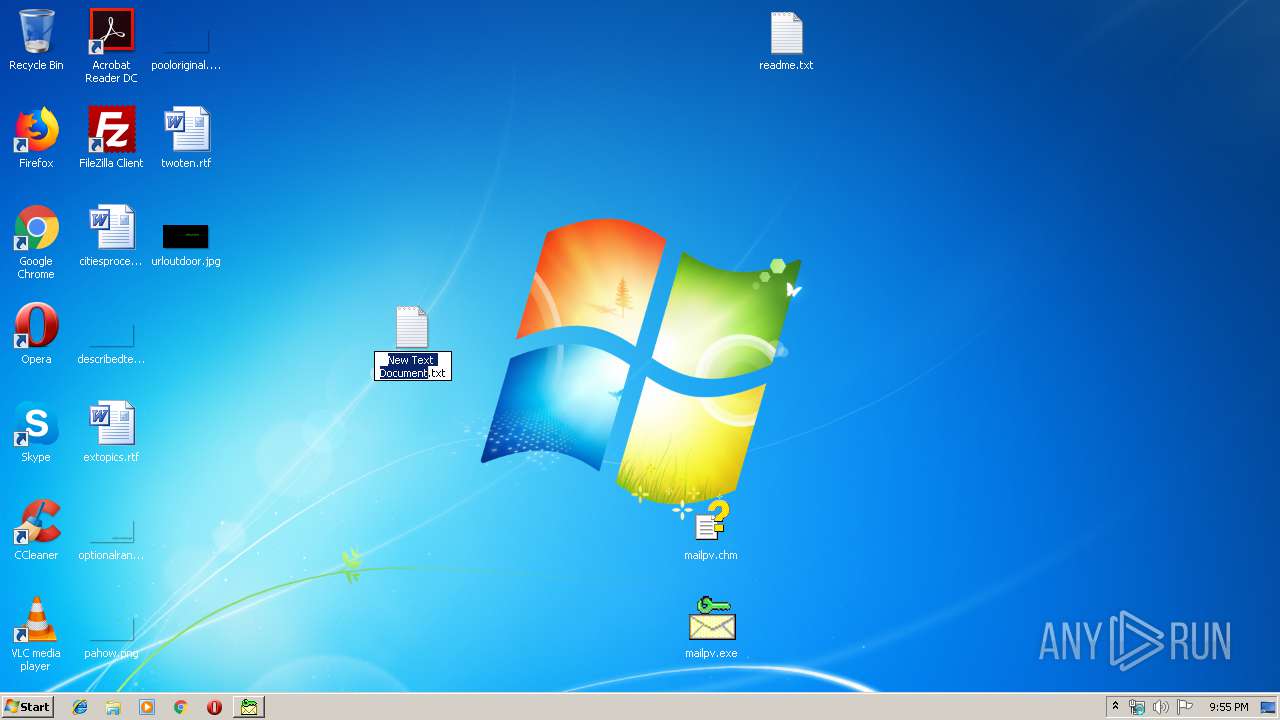
| 2372 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\New Text Document.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\mailpv.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3932 | "C:\Users\admin\Desktop\mailpv.exe" | C:\Users\admin\Desktop\mailpv.exe | explorer.exe | ||||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: Email Password-Recovery Exit code: 0 Version: 1.86 Modules
| |||||||||||||||
Total events
462
Read events
440
Write events
22
Delete events
0
Modification events
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\mailpv.zip | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\hhctrl.ocx,-452 |
Value: Compiled HTML Help file | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3932 | mailpv.exe | C:\Users\admin\AppData\Local\Temp\cp2819.tmp | — | |
MD5:— | SHA256:— | |||
| 2896 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2896.9856\readme.txt | text | |
MD5:932B6EBC19697B3B9DAFBA47902DF8B2 | SHA256:7D6B967D66E5216AD06986500A3FB891A132518387160B88E22A3B5DE9A2DA21 | |||
| 2896 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2896.9856\mailpv.exe | executable | |
MD5:782DD6152AB52361EBA2BAFD67771FA0 | SHA256:26A3395A4115355E897A7DAF04551EBA5E62DA661D8DBAE7C99205A2E74D24BA | |||
| 2896 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2896.9856\mailpv.chm | chi | |
MD5:7DCBCACEBCCCA4A9DD27732210D4B4AB | SHA256:CCC353CB42A241BDF9F425AF61471A045FE3F309B16FBE42826F10763CFDEA38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report